Note:
- This tutorial requires access to Oracle Cloud. To sign up for a free account, see Get started with Oracle Cloud Infrastructure Free Tier.
- It uses example values for Oracle Cloud Infrastructure credentials, tenancy, and compartments. When completing your lab, substitute these values with ones specific to your cloud environment.
Add OCI Load Balancer and OCI WAF to a Hub with Hub and Spoke VCN Routing Architecture
Introduction
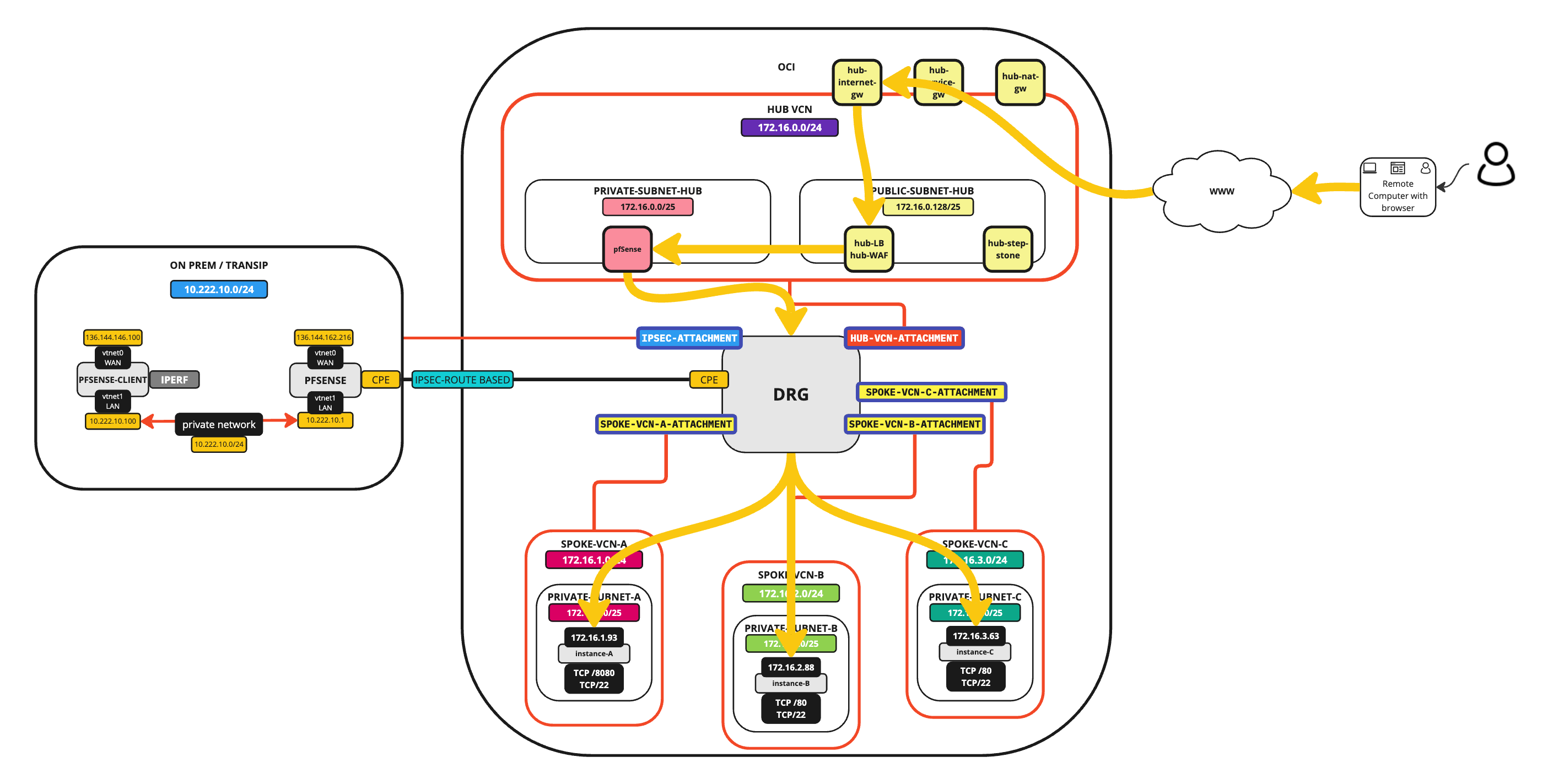
This tutorial will guide you through the tasks necessary to deploy and configure an Oracle Cloud Infrastructure (OCI) Load Balancer with OCI Web Application Firewall (WAF) in OCI and how this will operate in a Hub and Spoke VCN routing environment.
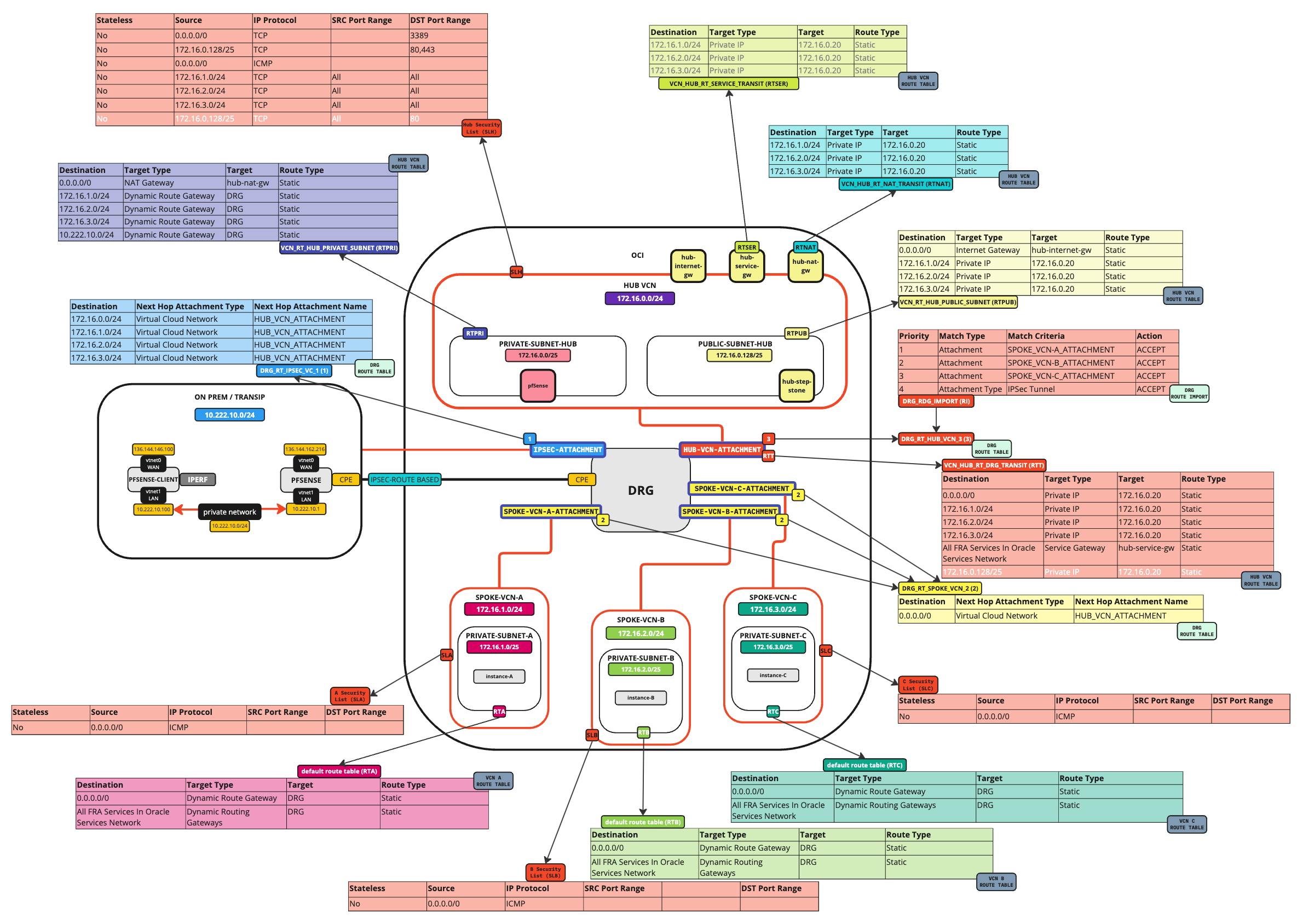
The following image illustrates the traffic flows.
External to Spoke connectivity using the Load Balancer and WAF
Objectives
- We will configure an OCI Load Balancer with OCI WAF policy in a Hub and Spoke network architecture. Additionally, we will set up the web servers to monitor and track how the load balancer distributes traffic.
Prerequisites
-
Ensure you complete the following tutorials if you want to recreate the content in this tutorial.
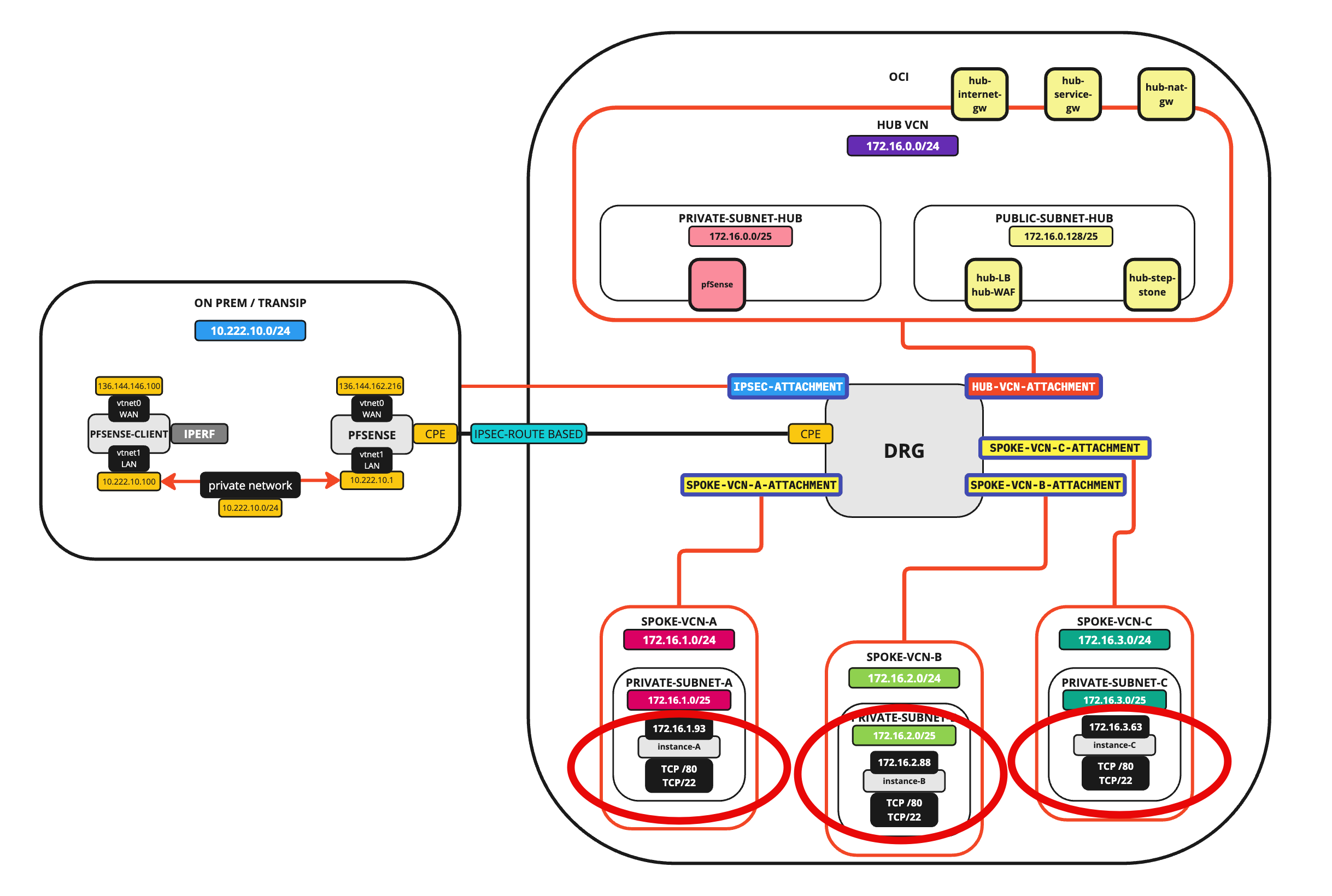
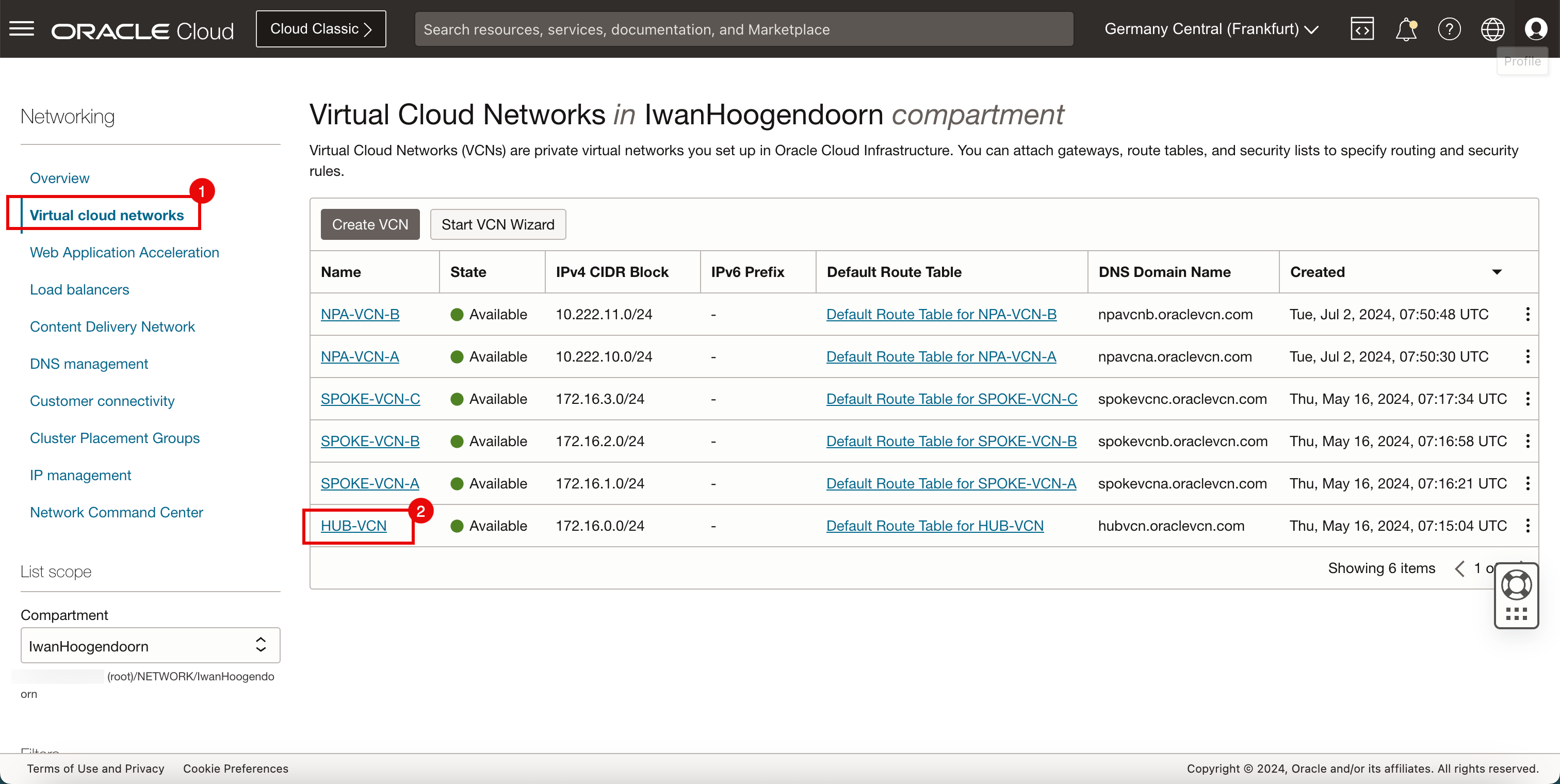
Task 1: Review the Current Hub and Spoke Network Architecture
To continue this tutorial we should have:
- 1 x Hub VCN (with a firewall, internet gateway, NAT gateway, and a service gateway)
- 3 x Spoke VCNs
- 1 x On-premises attached with an IPSec VPN Connection
In the Hub VCN, we have a Windows instance that we can use to connect to the spoke instances. Each spoke will have one instance that will be configured as a web server, these instances can be used as endpoints for the load balancer that we will deploy in this tutorial.
The following image illustrates the starting point.
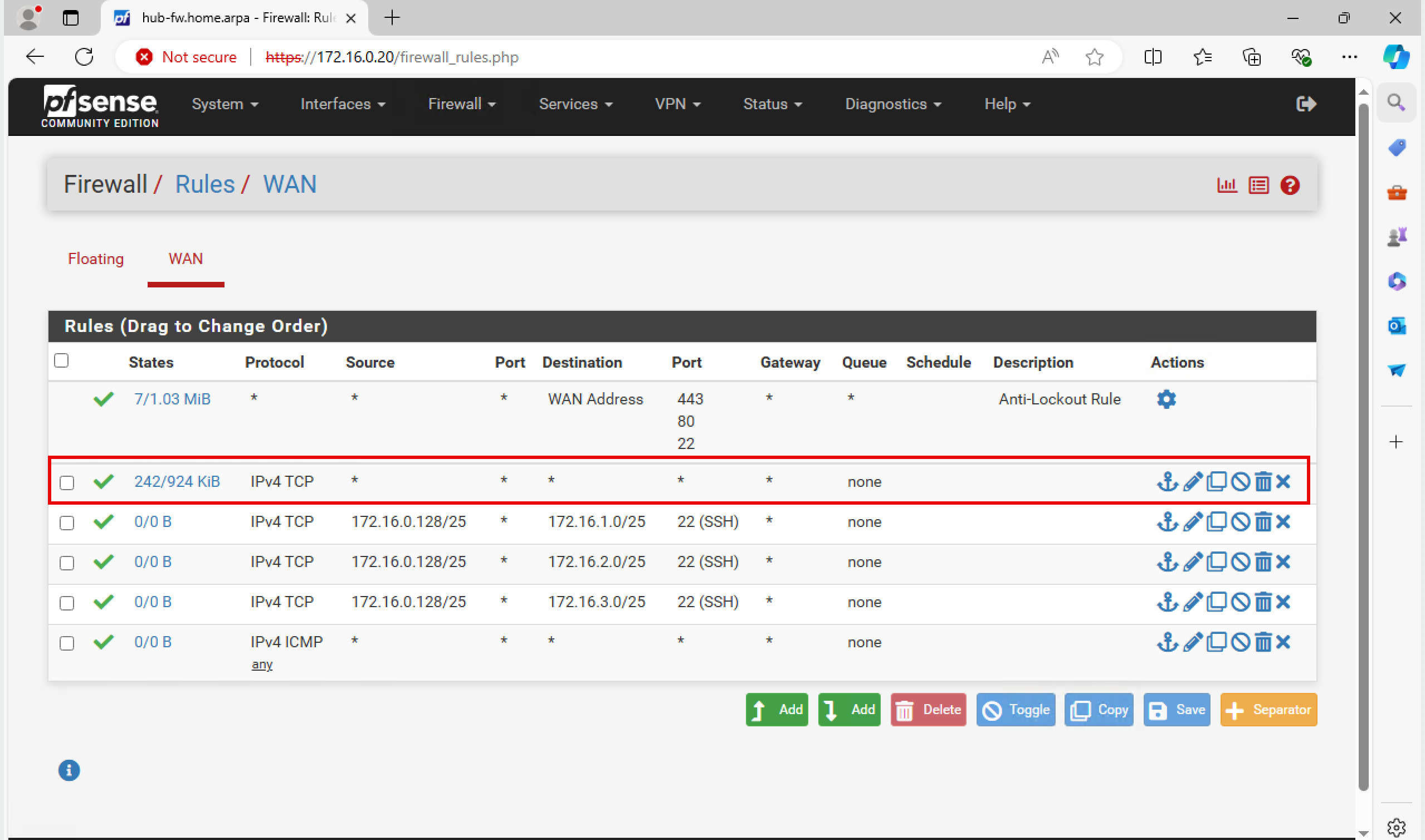
Task 2: Configure Routing in the Hub and Spoke Network Architecture between the OCI WAF and OCI Load Balancer, the Hub Firewall and the Spoke Instances
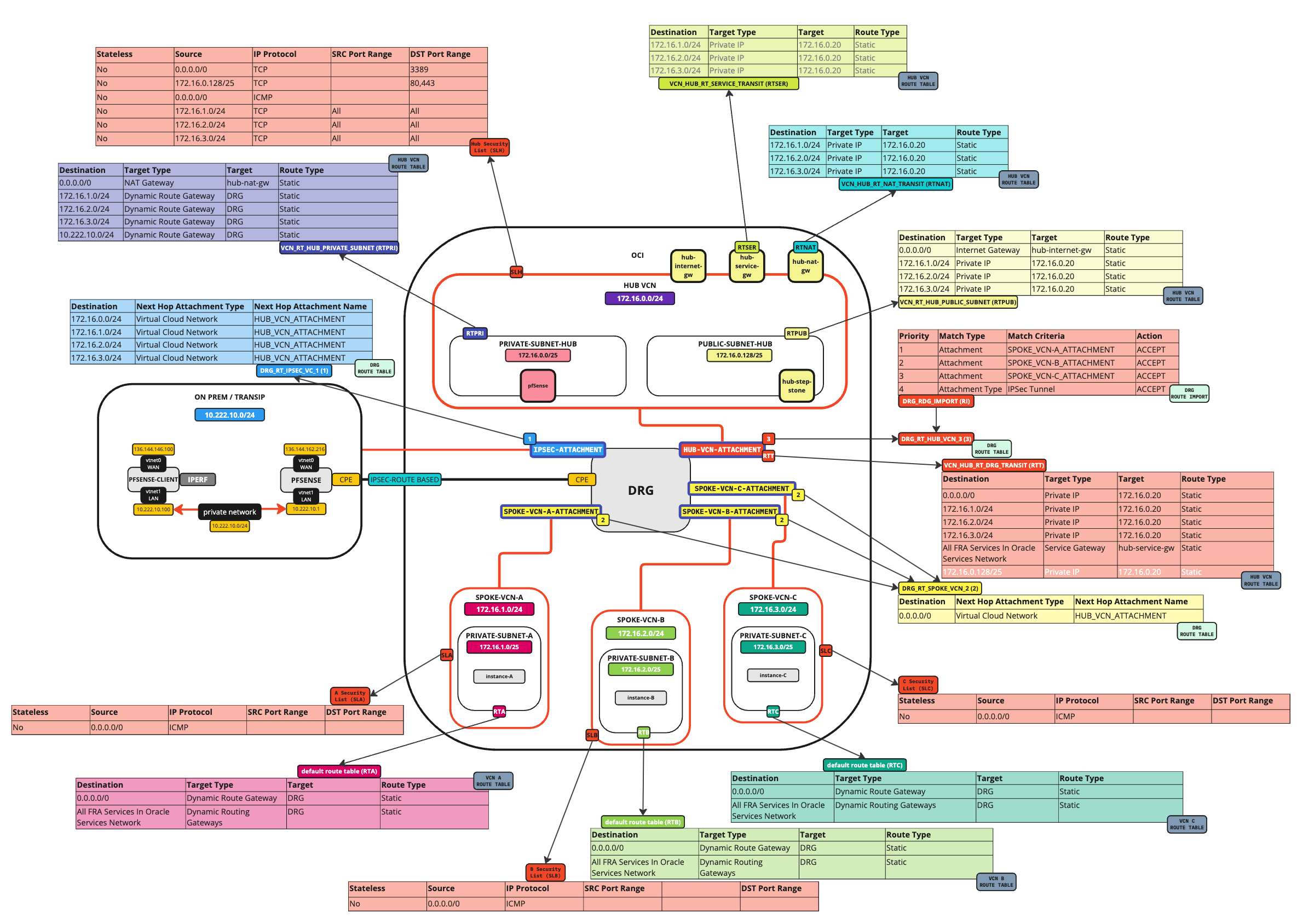
The following image illustrates the current Hub and Spoke network architecture with all the security lists and routing tables.
Before we add the OCI Load balancer, we want to make sure that traffic coming from the OCI Load Balancer subnet is routed to the hub firewall so that the traffic can be inspected on the hub firewall before it sends the traffic to the spoke instances.
While we already have a default routing rule doing this, it is still best practice to add this rule in to call it out explicitly as we did with the other networks as well.
-
Add the routing rule.
-
Log in to the OCI Console, navigate to Networking, Virtual Cloud Networks and Virtual Cloud Network.
-
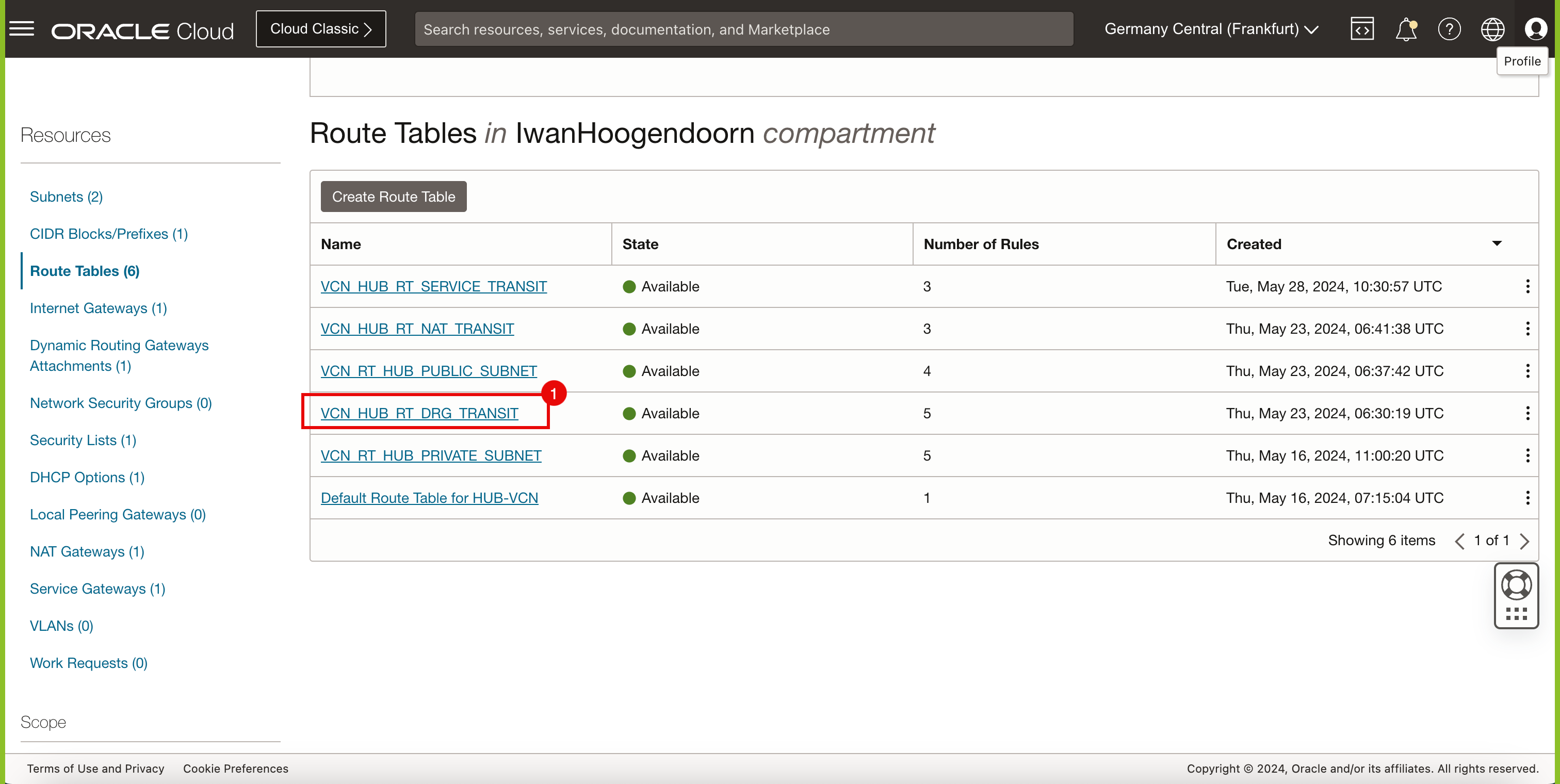
Click Route Tables.
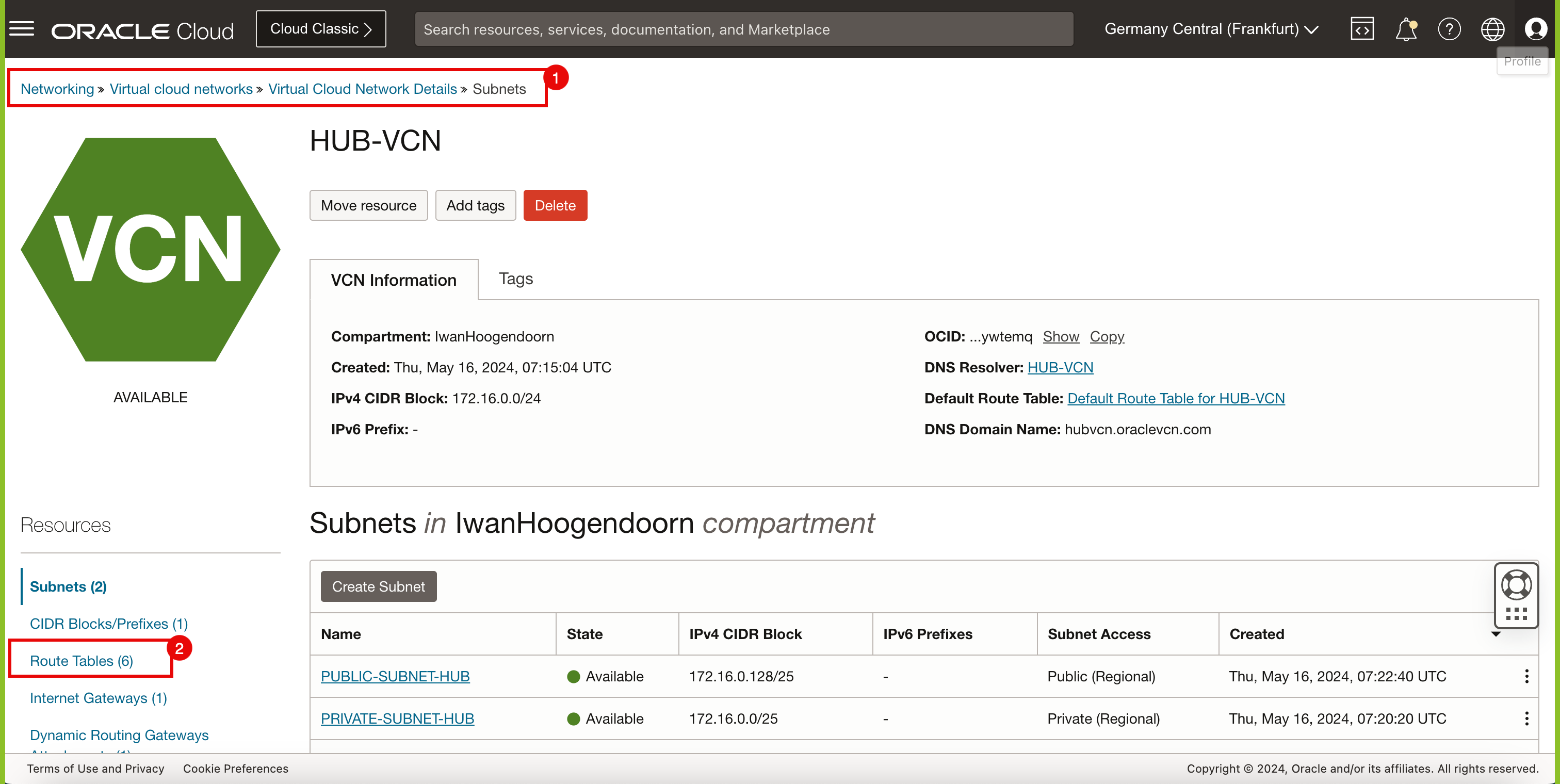
- Select the VCN_HUB_RT_DRG_TRANSIT route table.
-
-
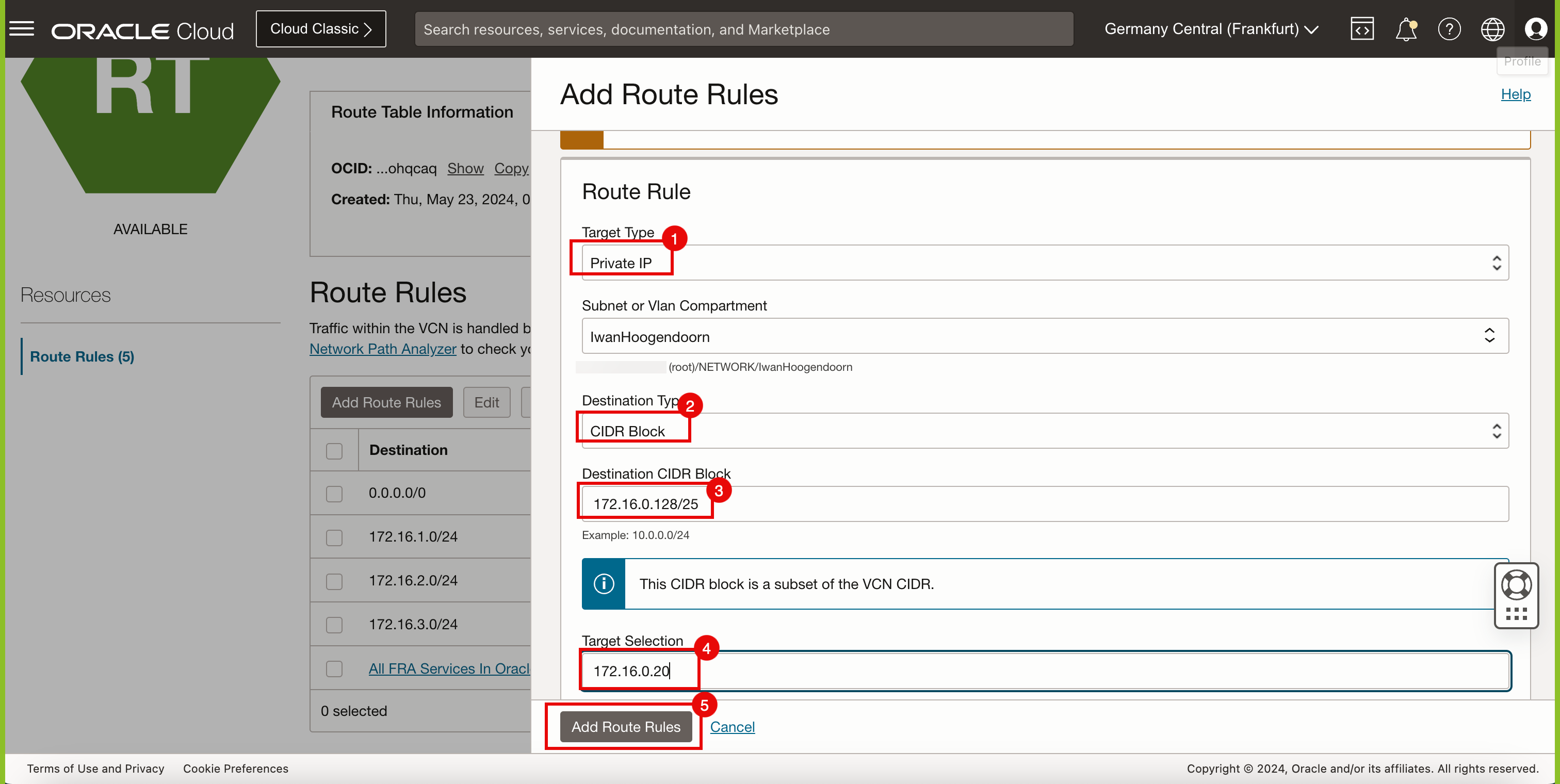
Click Add Route Rules.
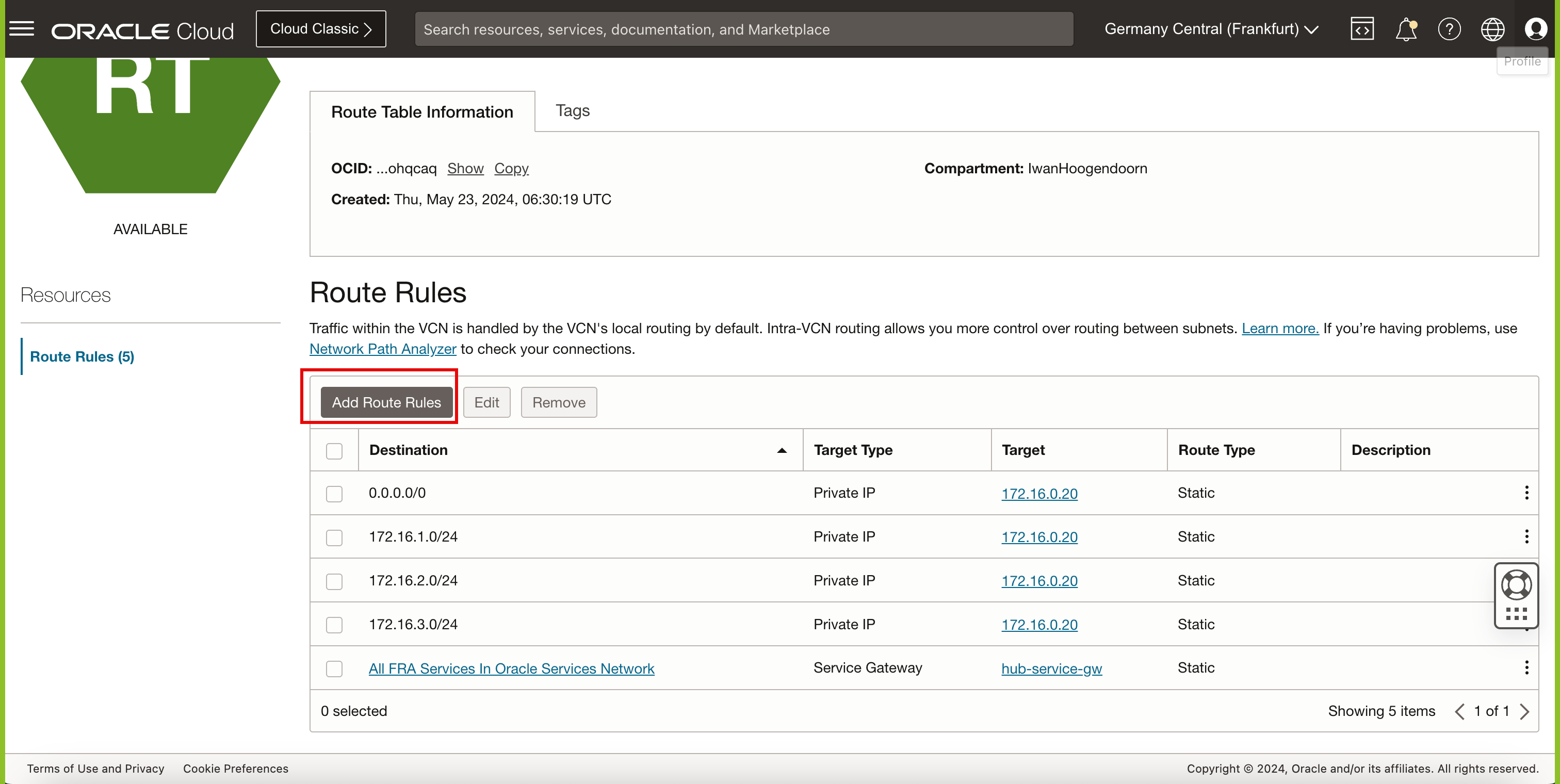
- Target Type: Select Private IP.
- Destination Type: Enter CIDR Block.
- Destination CIDR Block: Enter
0.0.0.0/0. - Target Selection: Enter
172.16.0.20, this is the IP address of our pfSense firewall. - Click Add Route Rules.
-
Note that the
172.16.0.128/25route is now added to the VCN_HUB_RT_DRG_TRANSIT route table.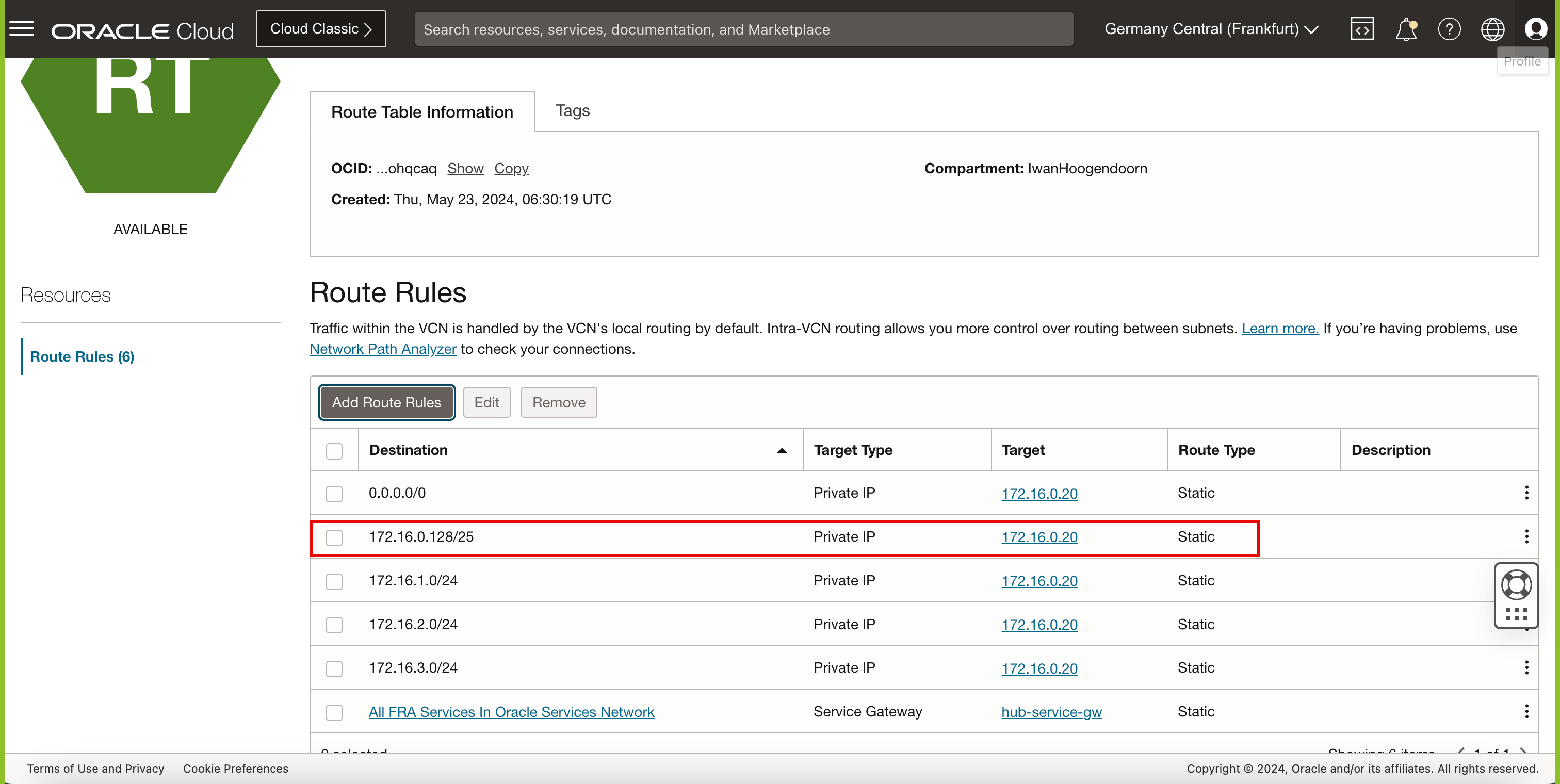
The following image illustrates the current Hub and Spoke network architecture with all the security lists and routing tables with route rules.
Task 3: Install a Web Server on the Backend Servers
Install a NGINX web server on all the instances in the spoke VCNs. For more information about how to install a NGINX web server on an Oracle Linux instance, see Task 6: Install a Web server on Instance.
Task 4: Create or Modify a Webpage on the Backend Servers
By default, each web server will be configured with a default webpage. To track where our OCI Load Balancer redirects the traffic to it is good practice to change something on the webpage so you know what server is hit.
We can do this by changing the content of the default NGINX index.html file.
sudo nano /usr/share/nginx/html/index.html
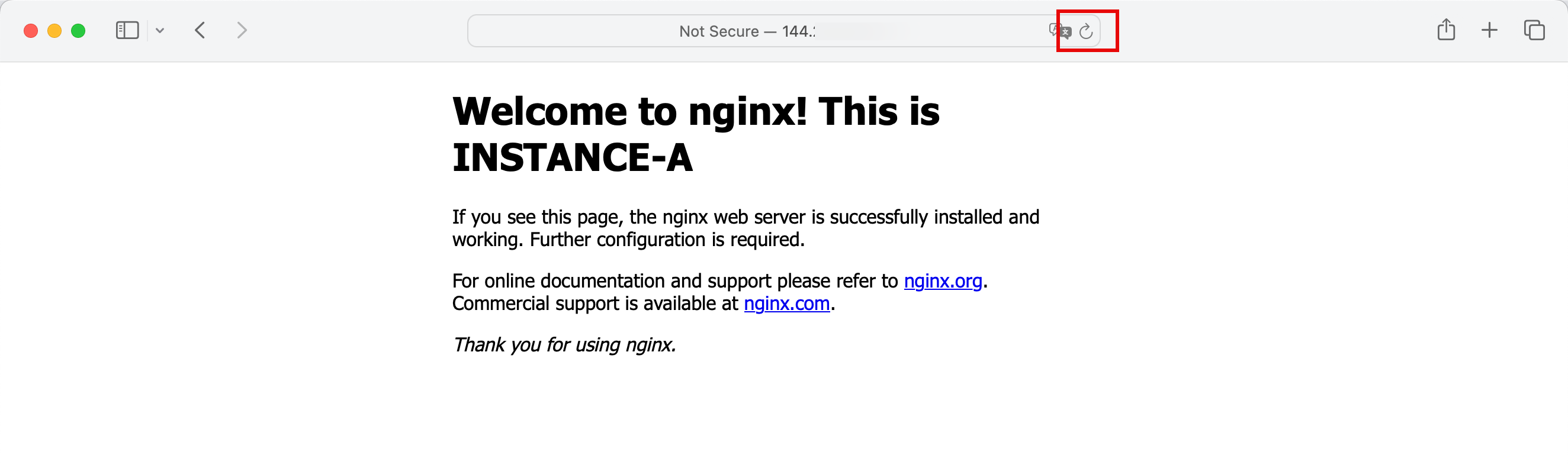
For Instance-A, change the header:
<h1>Welcome to nginx! This is INSTANCE-A</h1>
For Instance-B, change the header:
<h1>Welcome to nginx! This is INSTANCE-B</h1>
For Instance-C, change the header:
<h1>Welcome to nginx! This is INSTANCE-C</h1>
Make sure you save the index.html files after changing them.
Task 5: Install an OCI Load Balancer
Before we create the OCI Load Balancer, we first need to allow port 80 ingress on the Hub VCN security list. All the traffic including the traffic that is going from the load balancer in the public subnet of the Hub VCN is routed to the HUB firewall. The instances that the load balancer is going to use endpoints are listening on port TCP/80. For this reason, we also need to allow port TCP/80 ingress on the Hub VCN so that the private subnet in the Hub VCN where the traffic is routed also allows the communication towards the spoke VCNs.
-
Add ingress rule.
- Click the hamburger menu (≡) from the upper left corner.
- Click Networking.
- Click Virtual cloud networks.
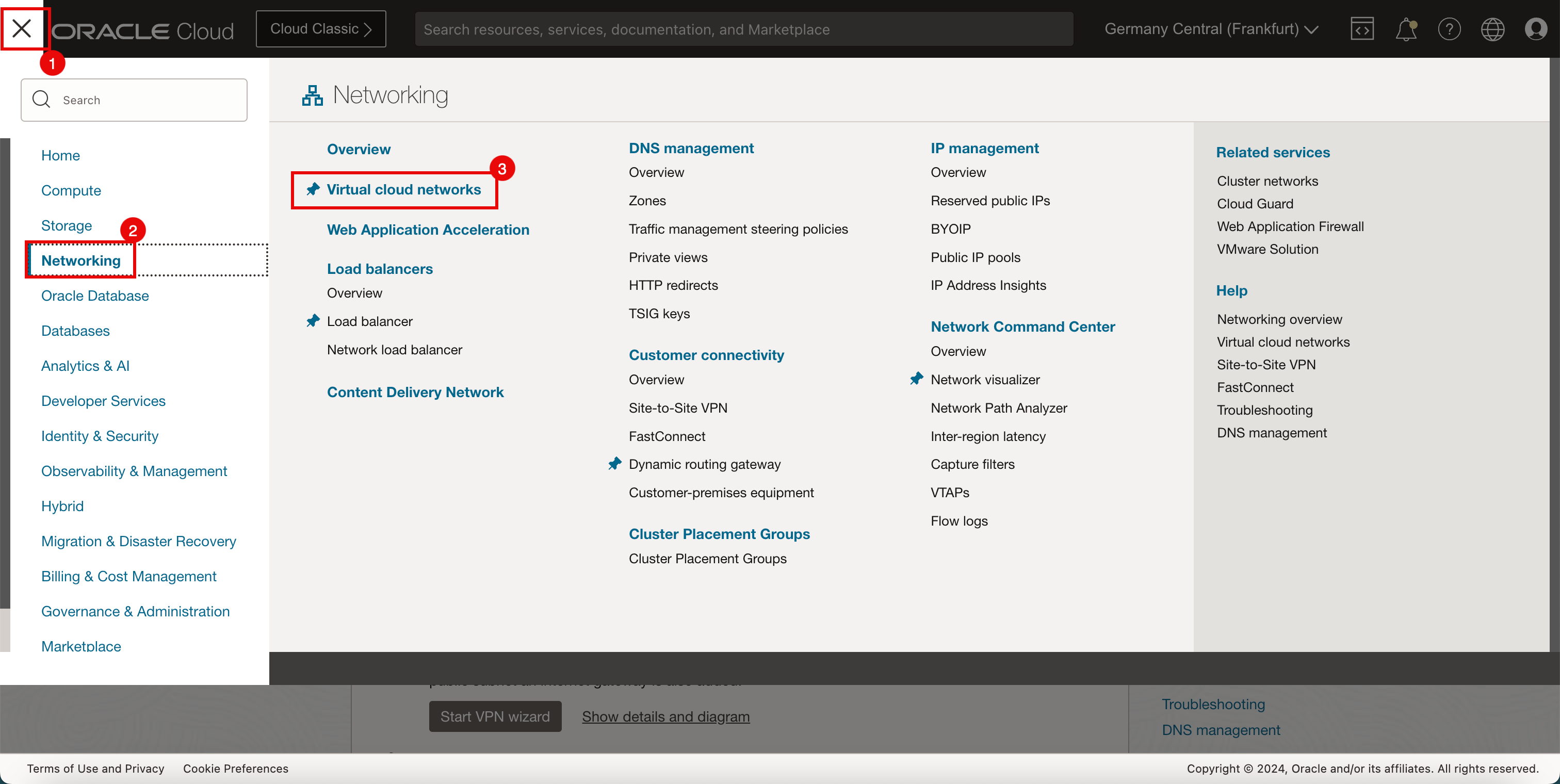
- Make sure you are in the Virtual cloud network section.
- Click the HUB-VCN VCN.
-
Click Security Lists.
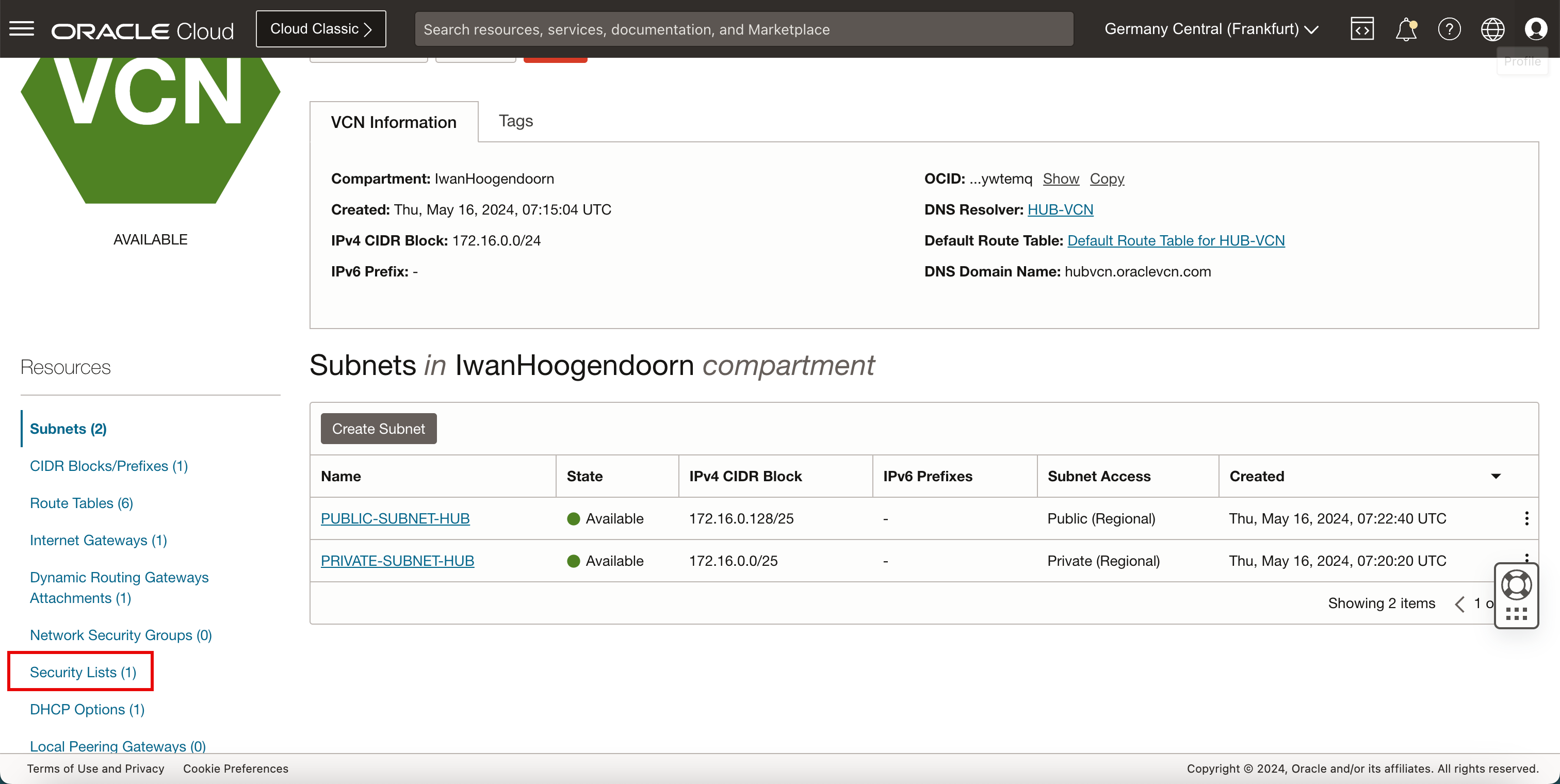
-
Click Default Security List for HUB-VCN.
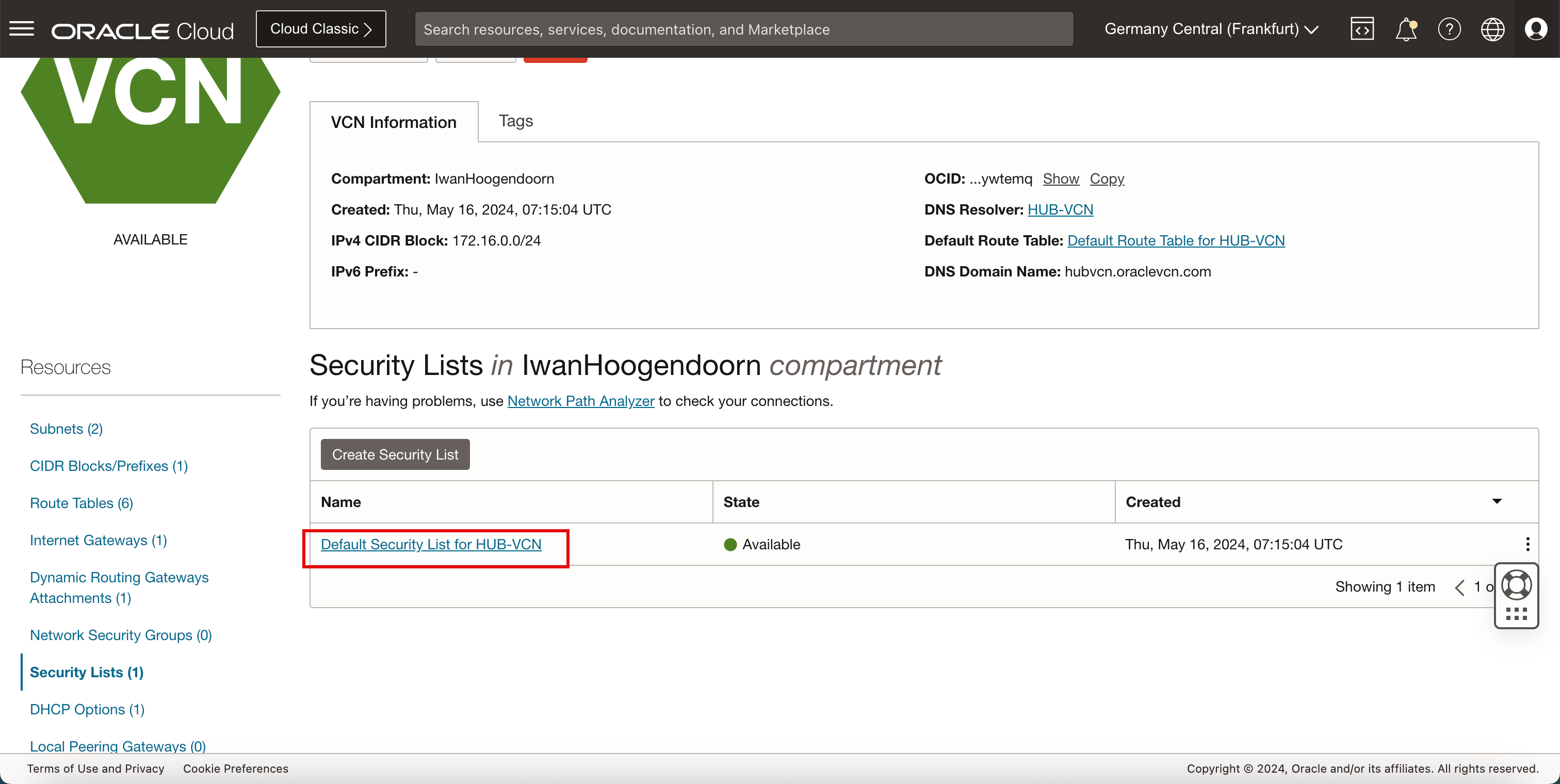
- Make sure you are in the Ingress Rules section.
- Click Add Ingress Rules.
- Add in a security rule that TCP/80 is allowed from the Source (
172.16.0.128/25) to ALL destinations.
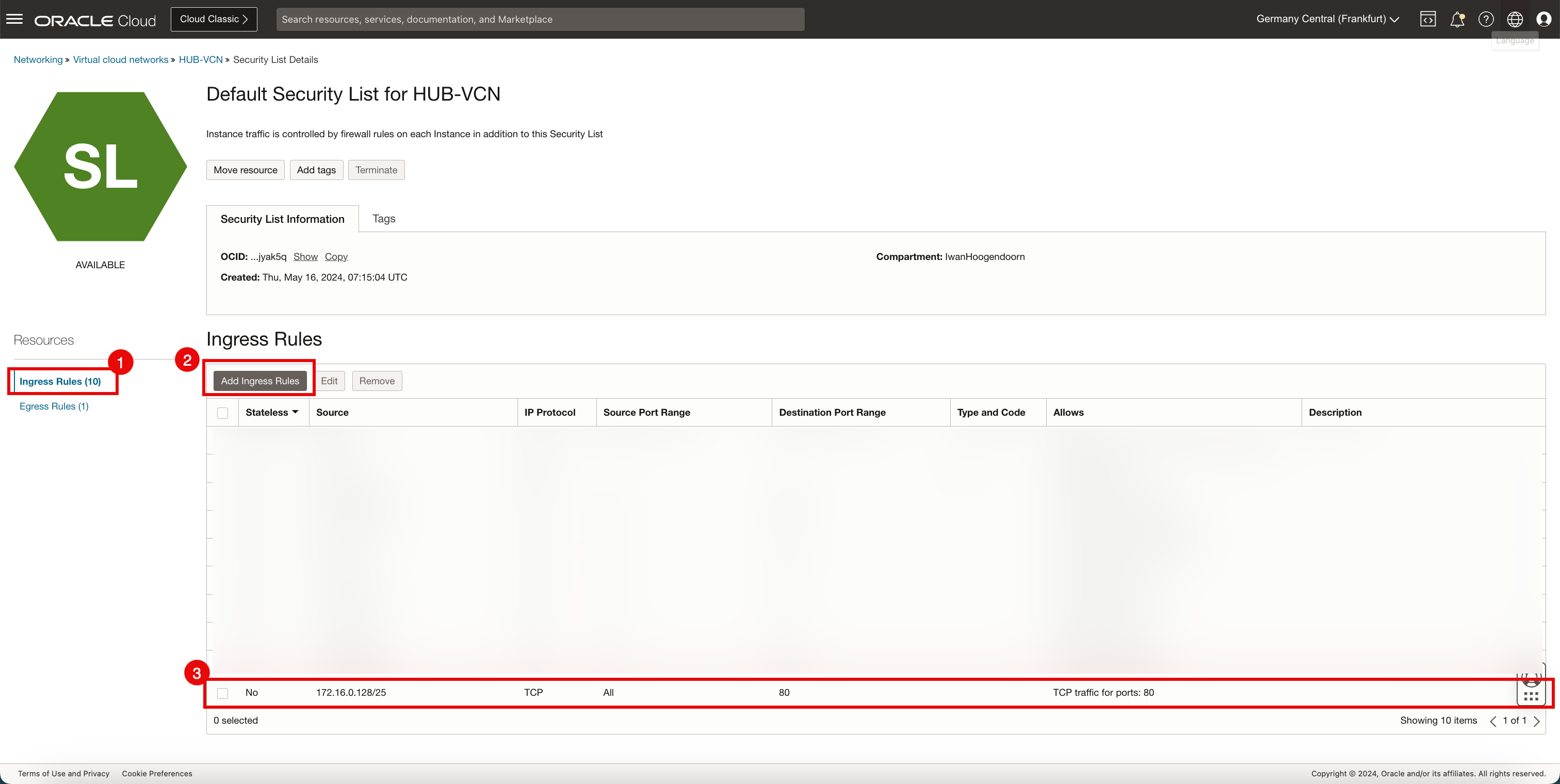
Note:
-
We are using the default security list that is applied to the HUB-VCN and therefore applied to all separate subnets inside this HUB-VCN.
-
This also means that traffic going from the public subnet towards the private subnet inside the HUB-VCN is also subject to this default security list as the same default security list is applied to both subnets.
-
For this reason we are allowing port TCP/80 ingress because if we do not do this the load balancer is not able to communicate with the backend servers as all the traffic is sent from the public subnet to the private subnet because we are using a Hub-and-Spoke architecture with a firewall inside the private subnet of the HUB-VCN.
-
The following image illustrates what you have created so far with the security rule added.
-
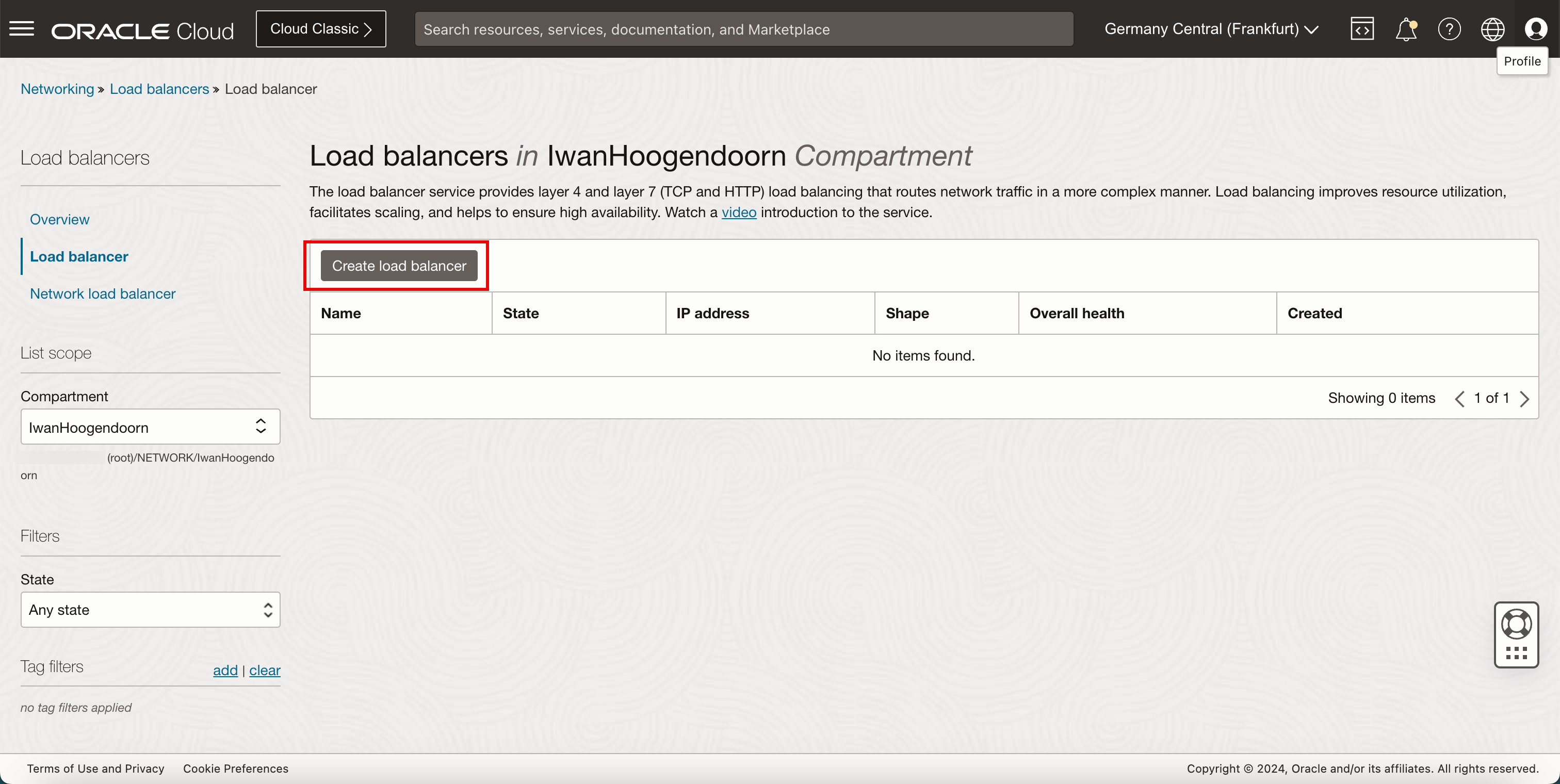
Create the load balancer.
- Click the hamburger menu (≡) from the upper left corner.
- Click Networking.
- Click Load Balancer.
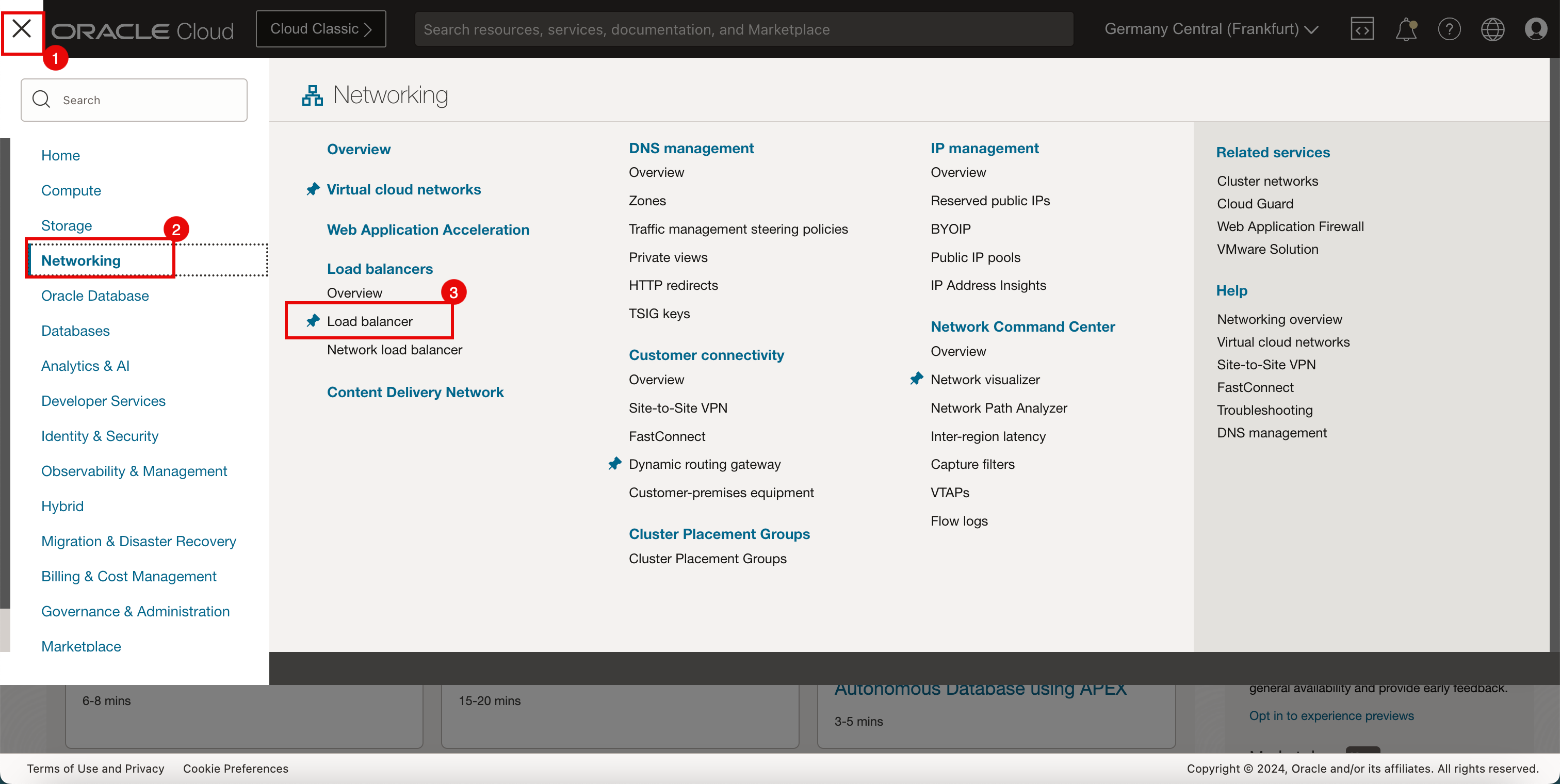
-
Click Create load balancer.
- Enter a Load balancer name.
- Select Public for the Visibility type.
- Select Ephemeral IP address.
- Scroll down.
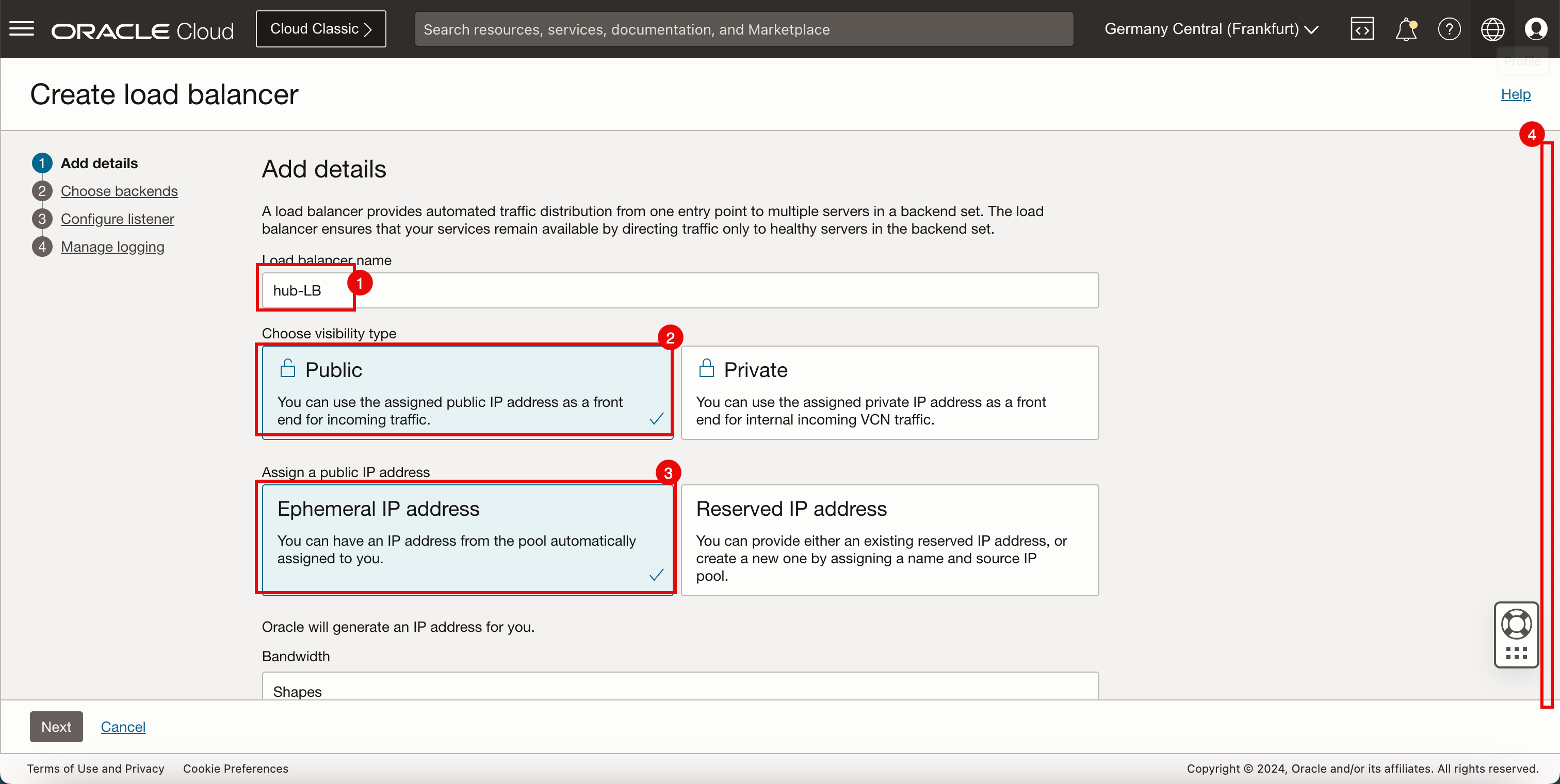
-
Keep everything default and scroll down.
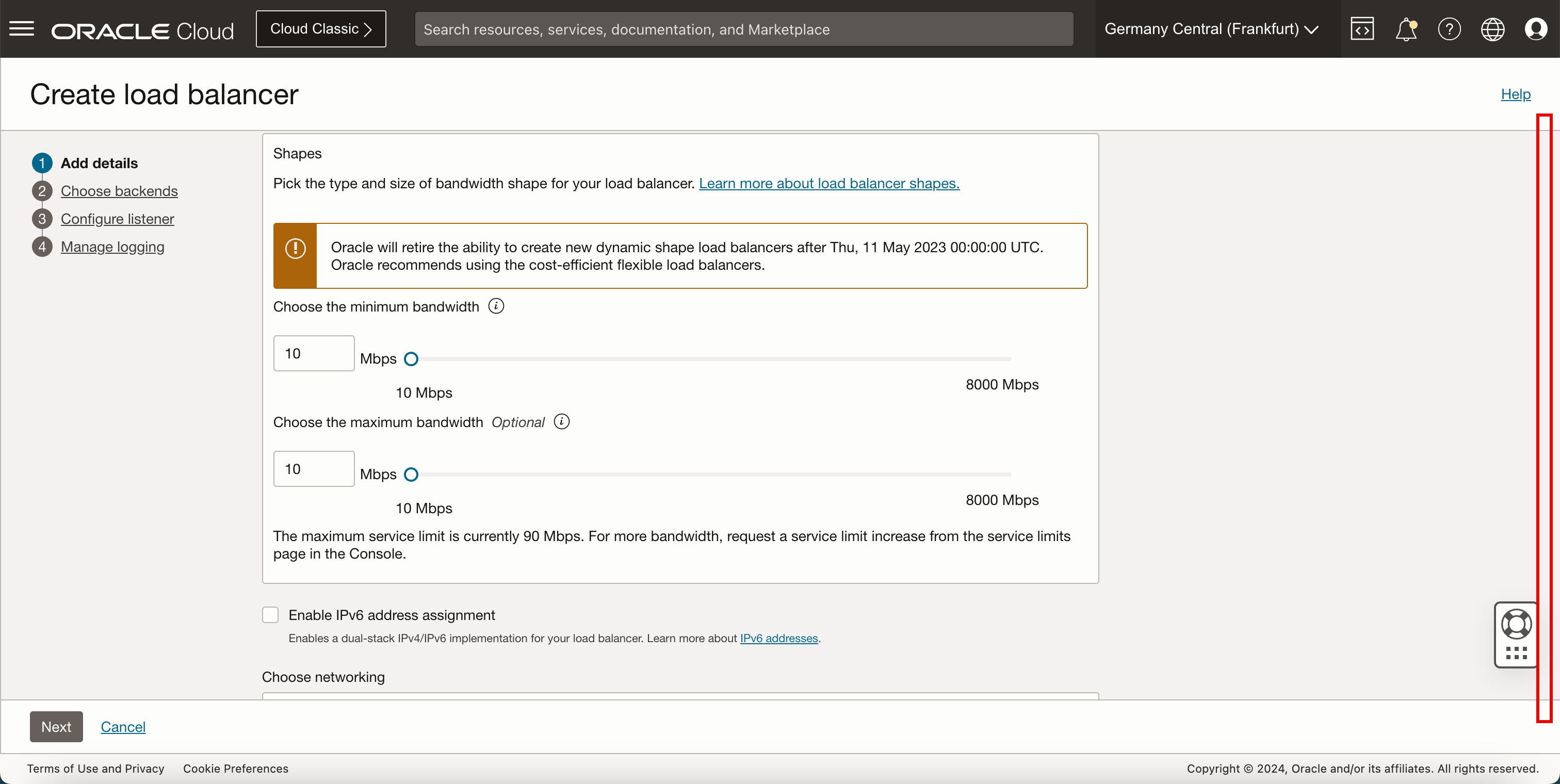
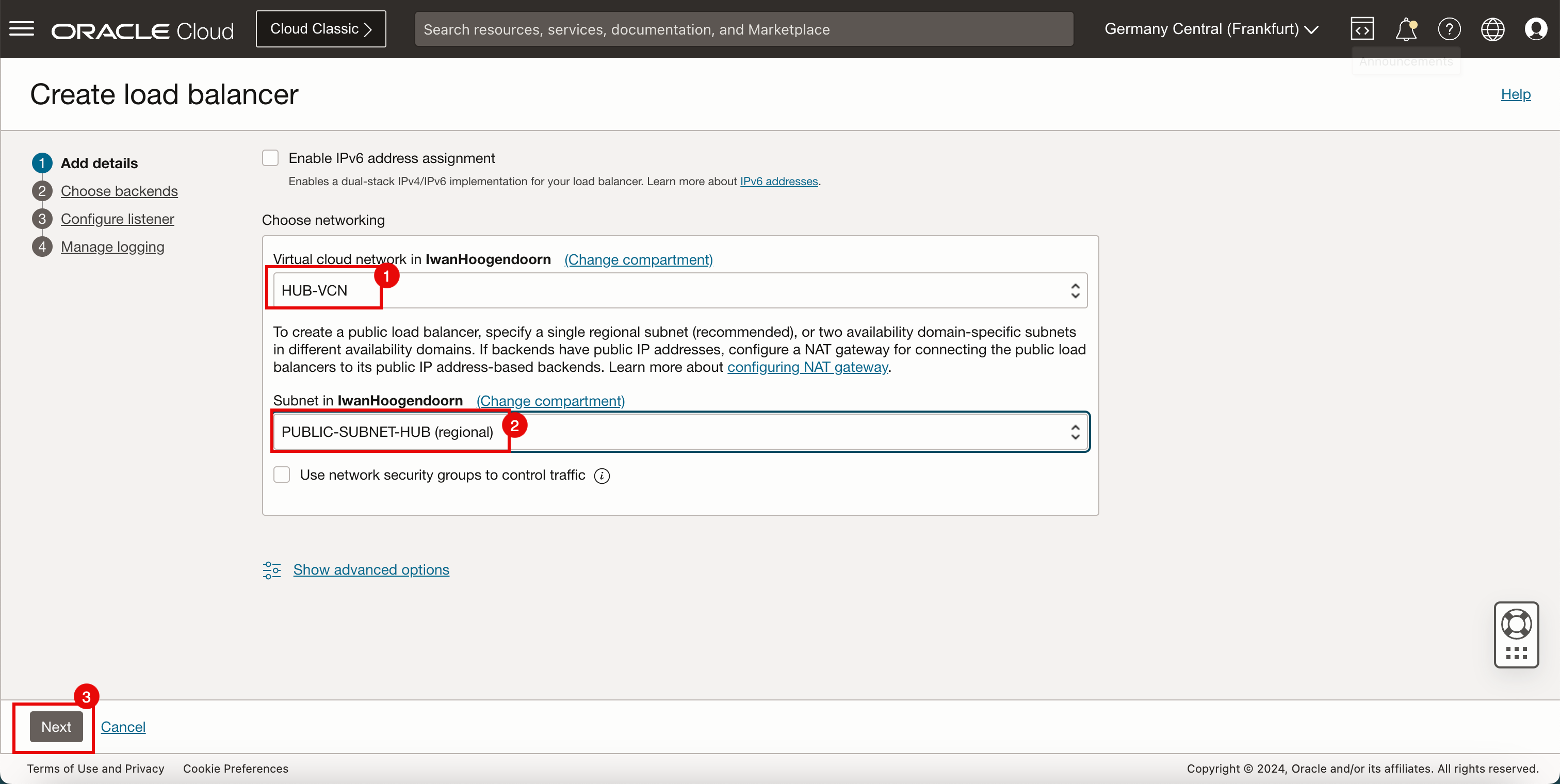
- Select the VCN where you want to attach the load balancer.
- Select the Subnet where you want to attach the load balancer.
- Click Next.
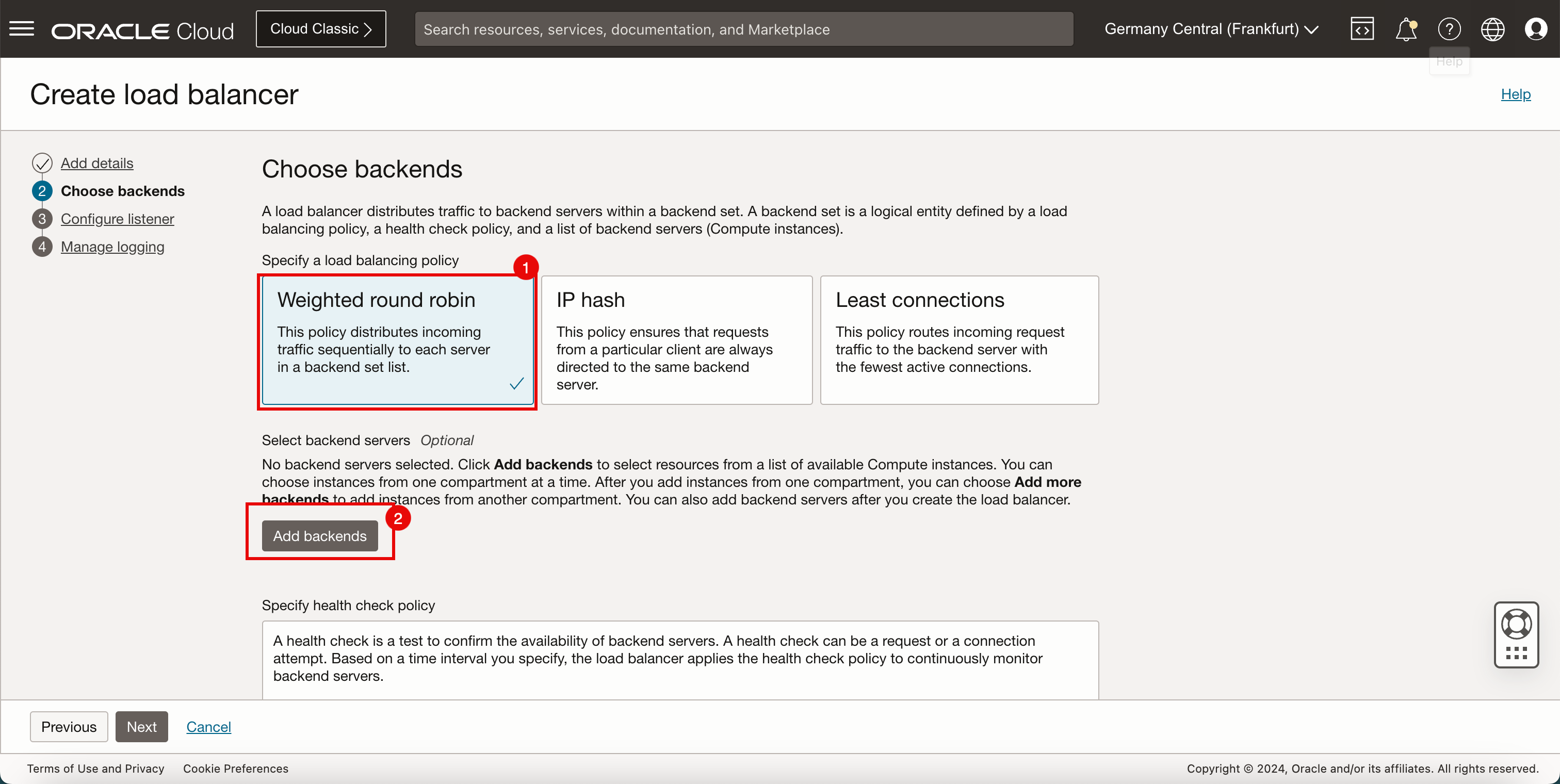
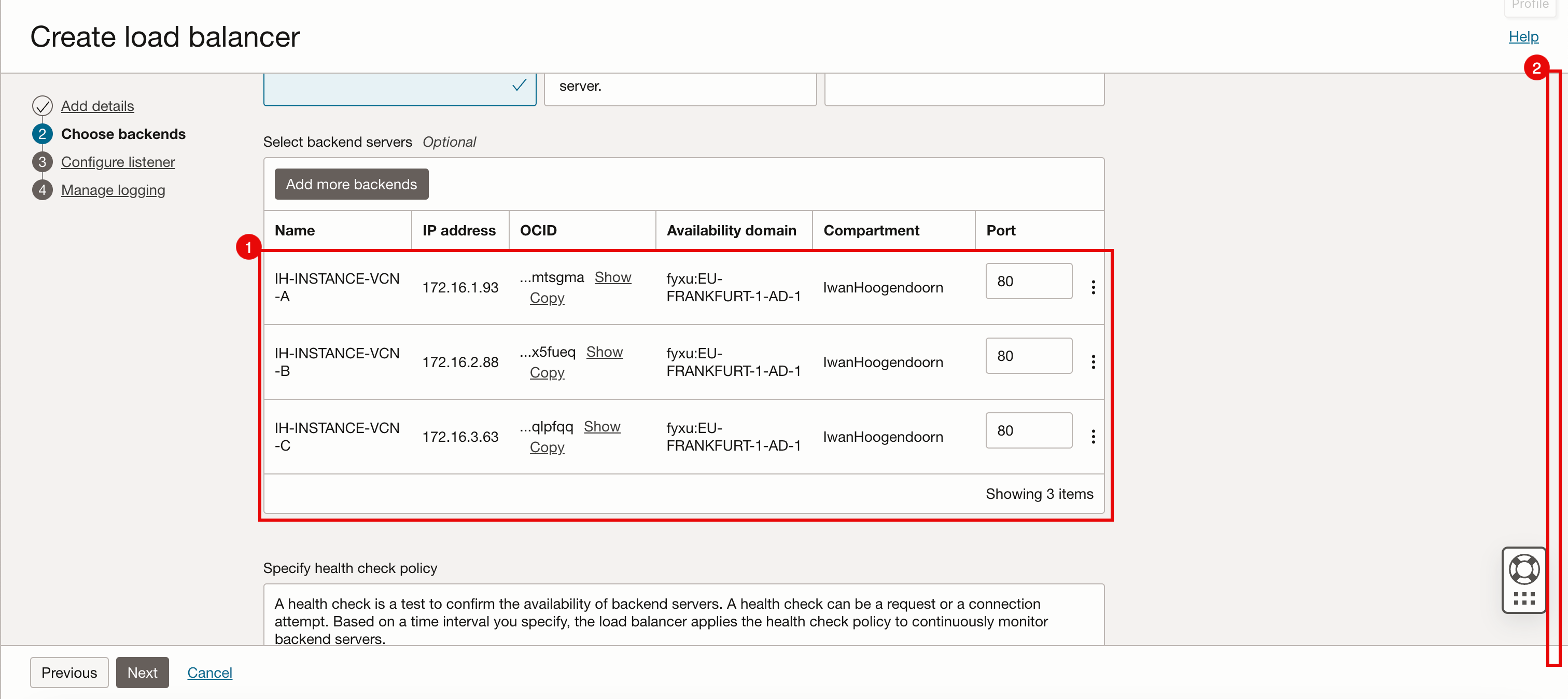
- Select Weighted round Robin as the load balancing policy.
- Click Add backends.
- Select all the backends of the instances in the spoke VCNs.
- Click Add Selected backends.
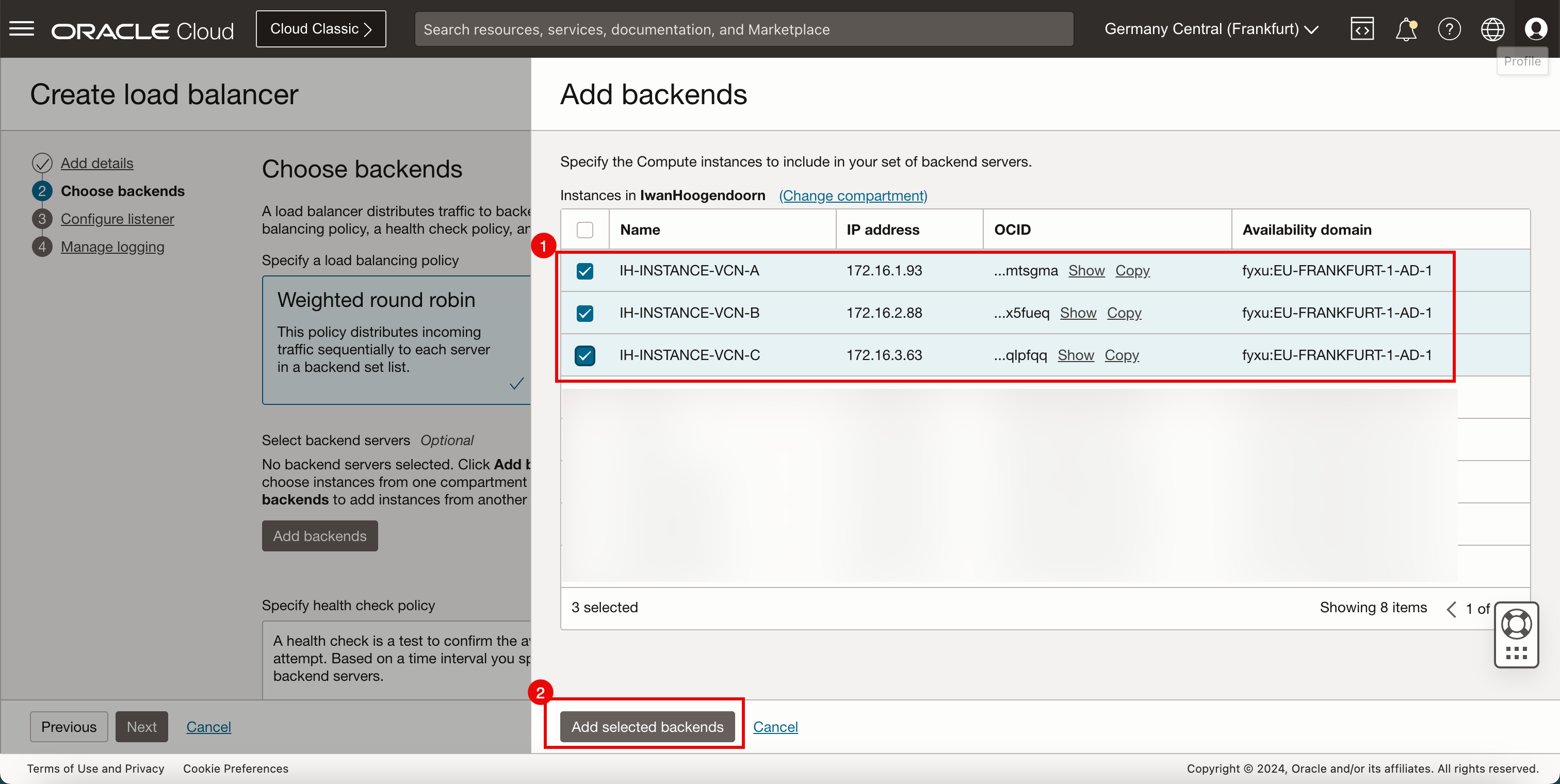
- Review the backends, and change the port if necessary, in this tutorial, all backend instances listen to port 80.
- Scroll down.
-
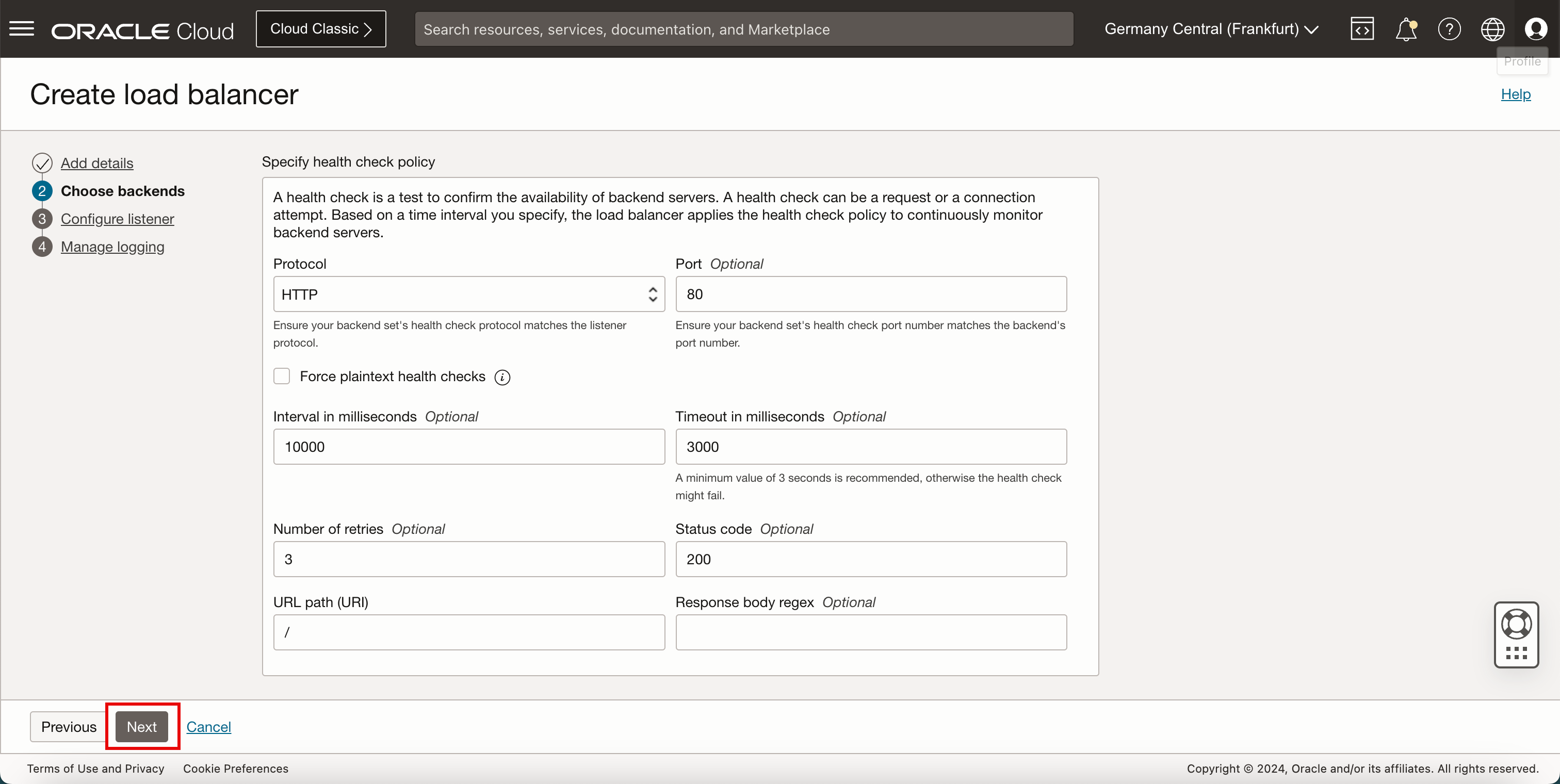
Keep the health check policy default, and click Next.
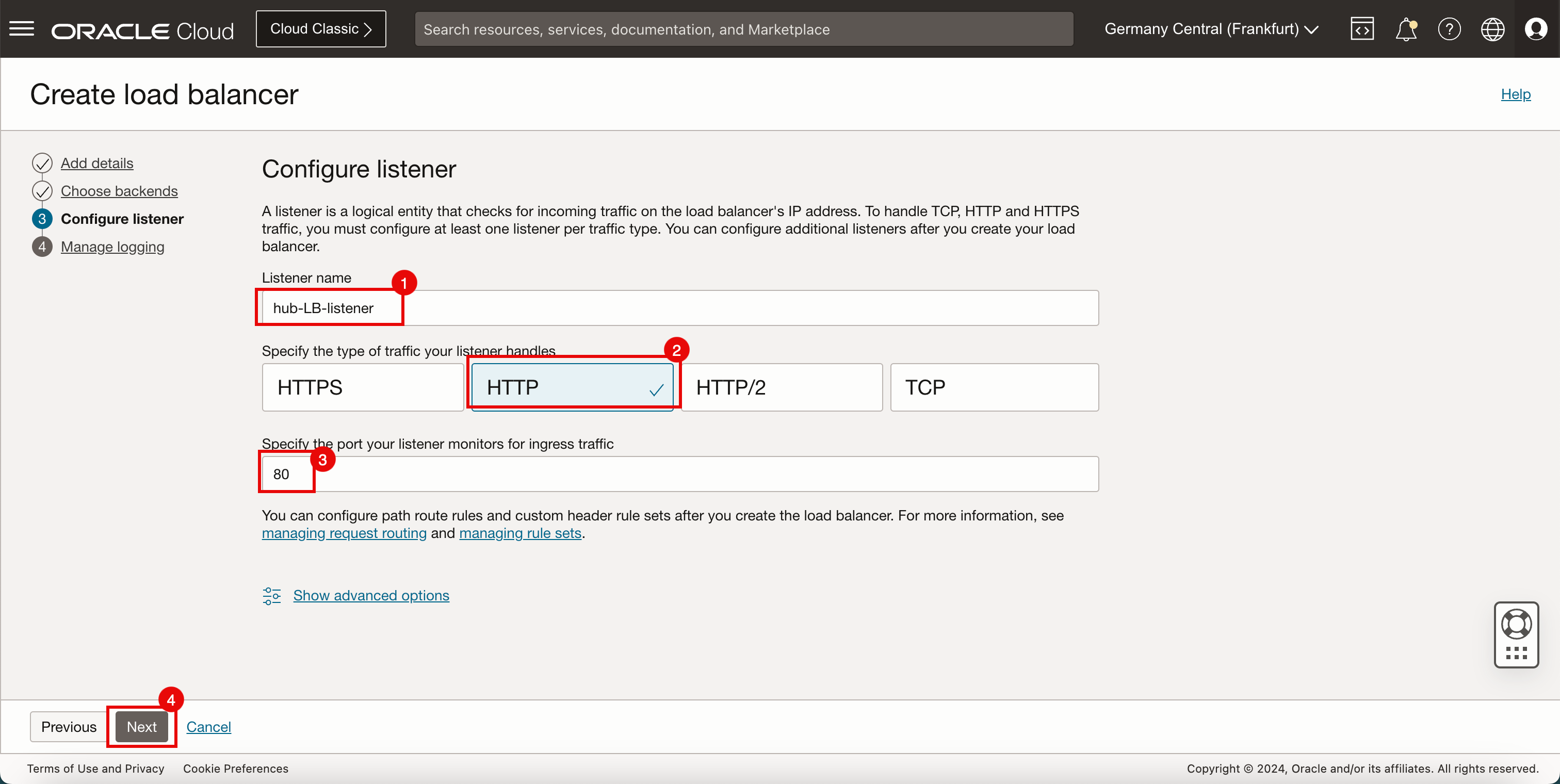
- Enter a Listener name.
- Select HTTP as type of traffic your listener handles.
- Enter a Listener port to be 80.
- Click Next.
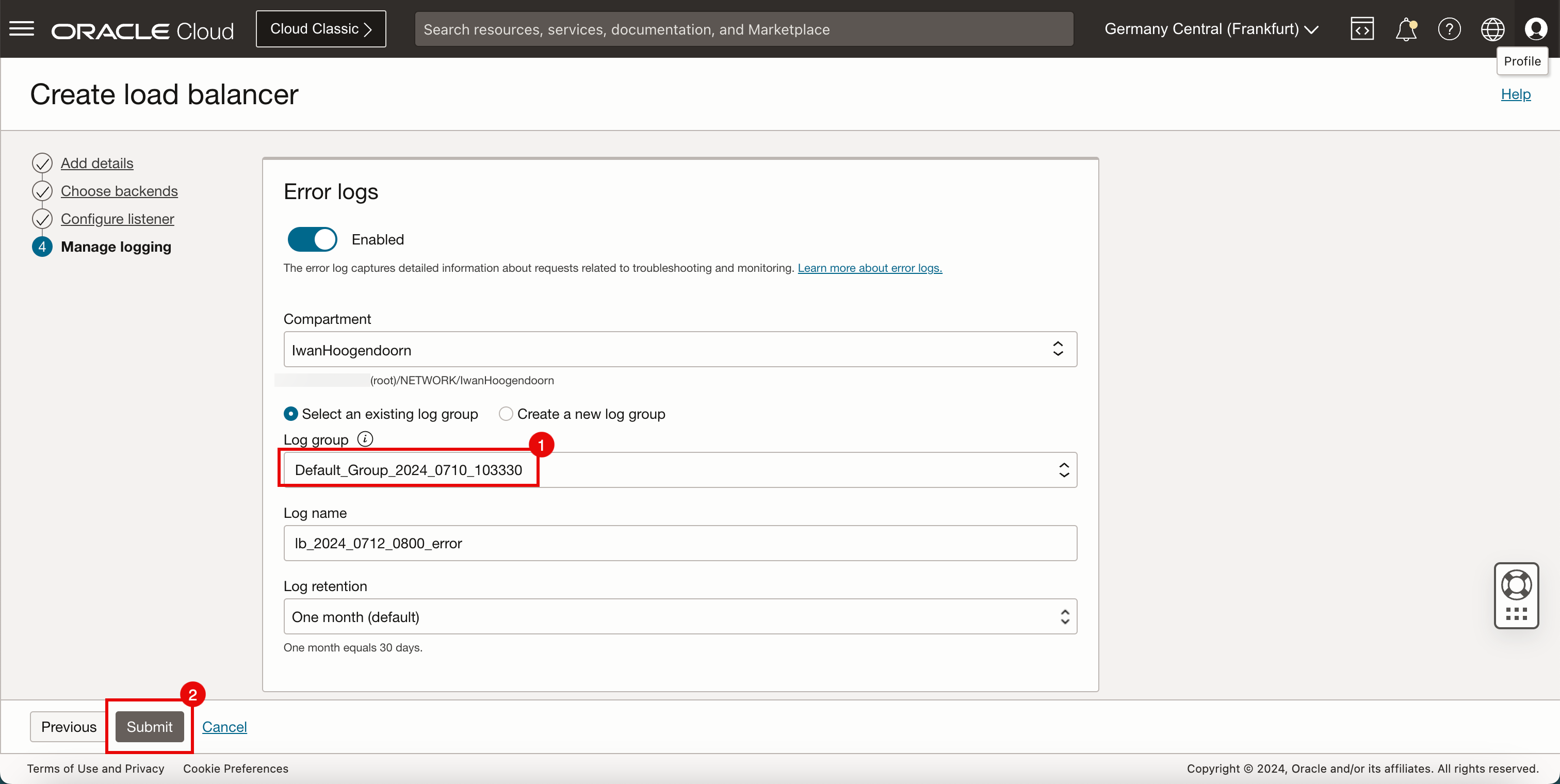
- Select a Log group.
- Click Submit.
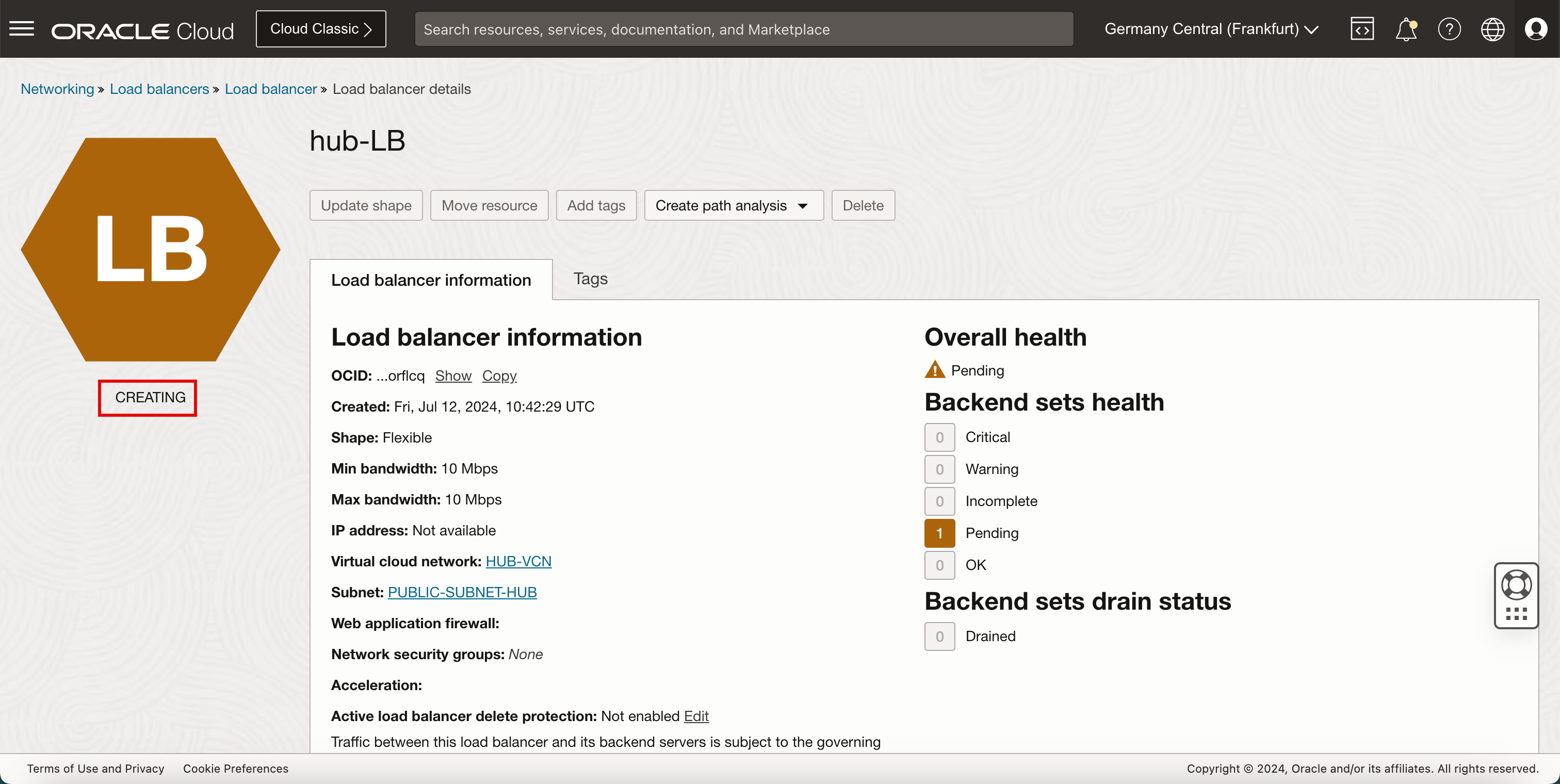
-
Note that the load balancer status is CREATING.
- Note that the load balancer status changed from CREATING to ACTIVE.
- Note that the Overall health is pending.
- Note that the Backend sets health is pending.
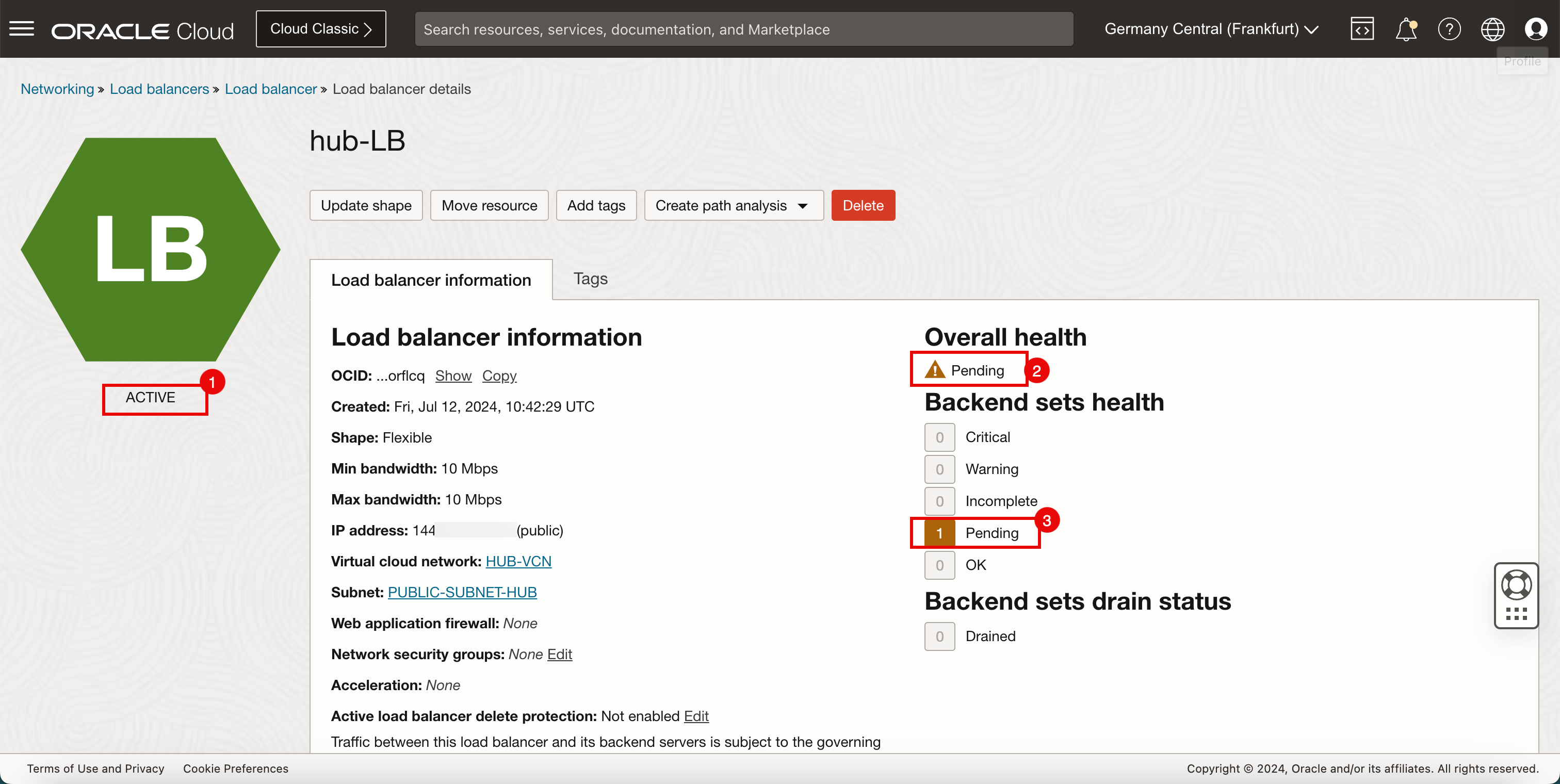
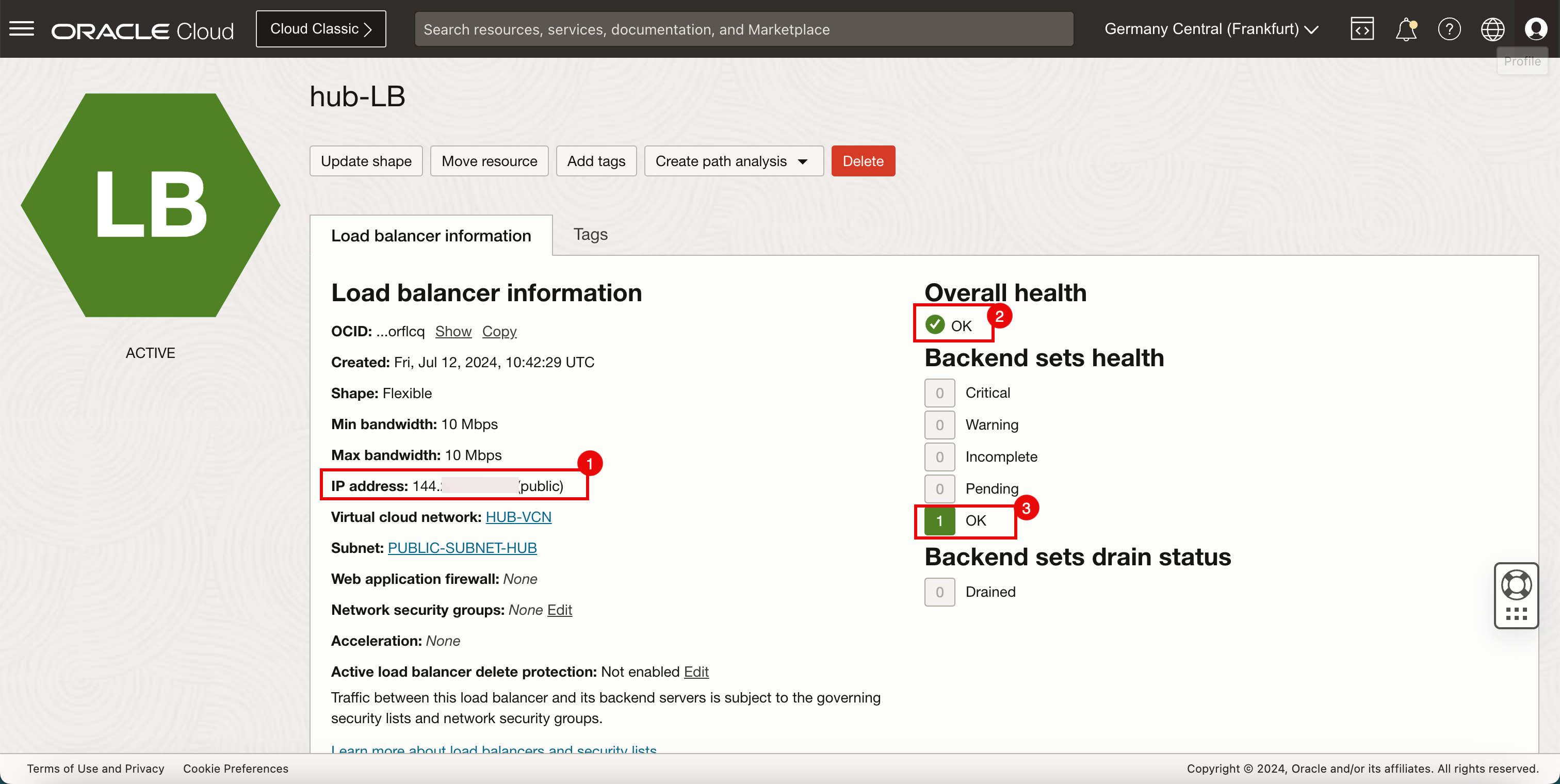
- Make a note of the Public IP address of the load balancer.
- After a few minutes the Overall health is OK.
- After a few minutes the Backend sets health is OK.
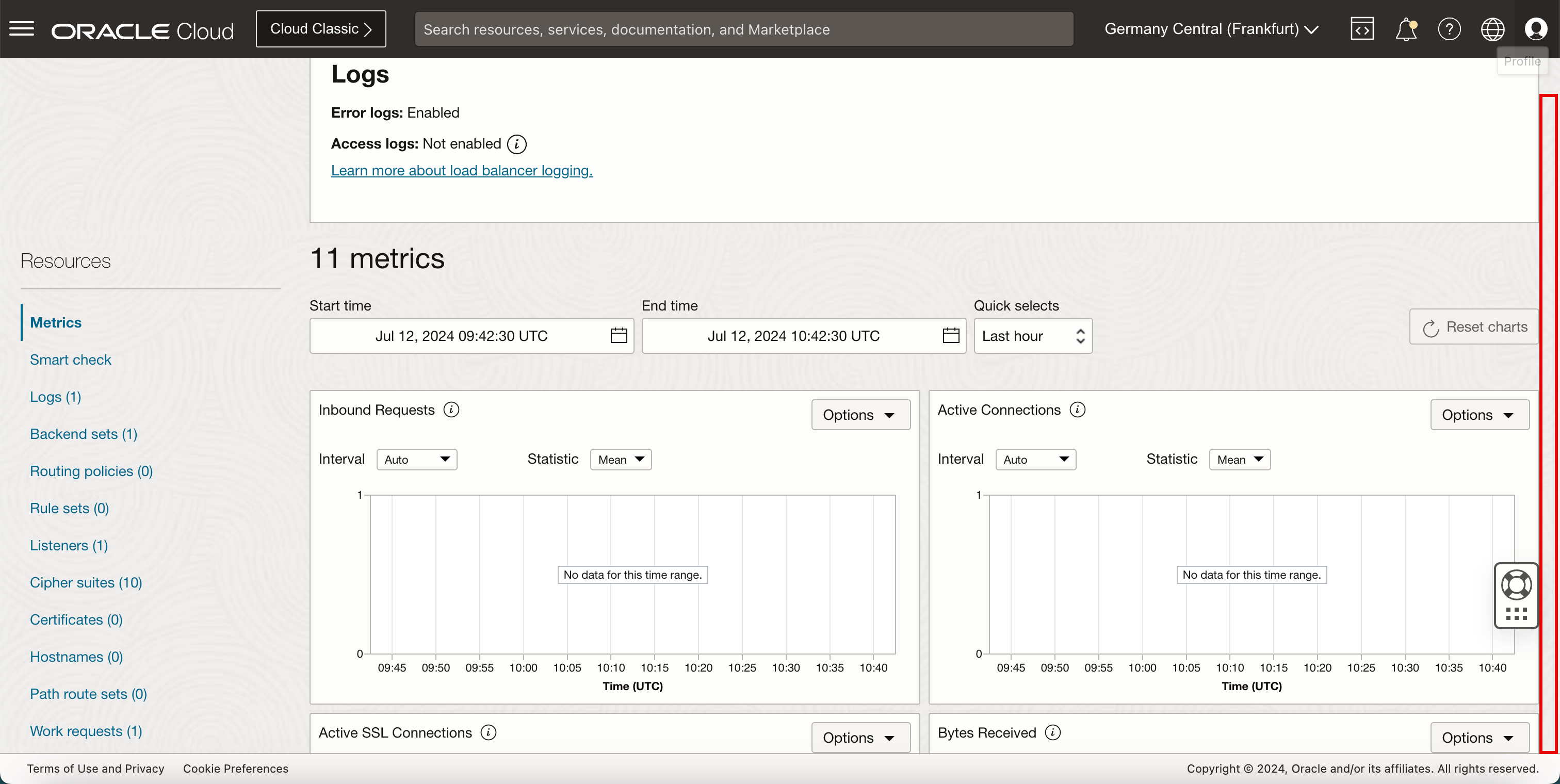
-
Scroll down to take a closer look at the backend set.
- Click Backend Sets.
- Click the available backend set.
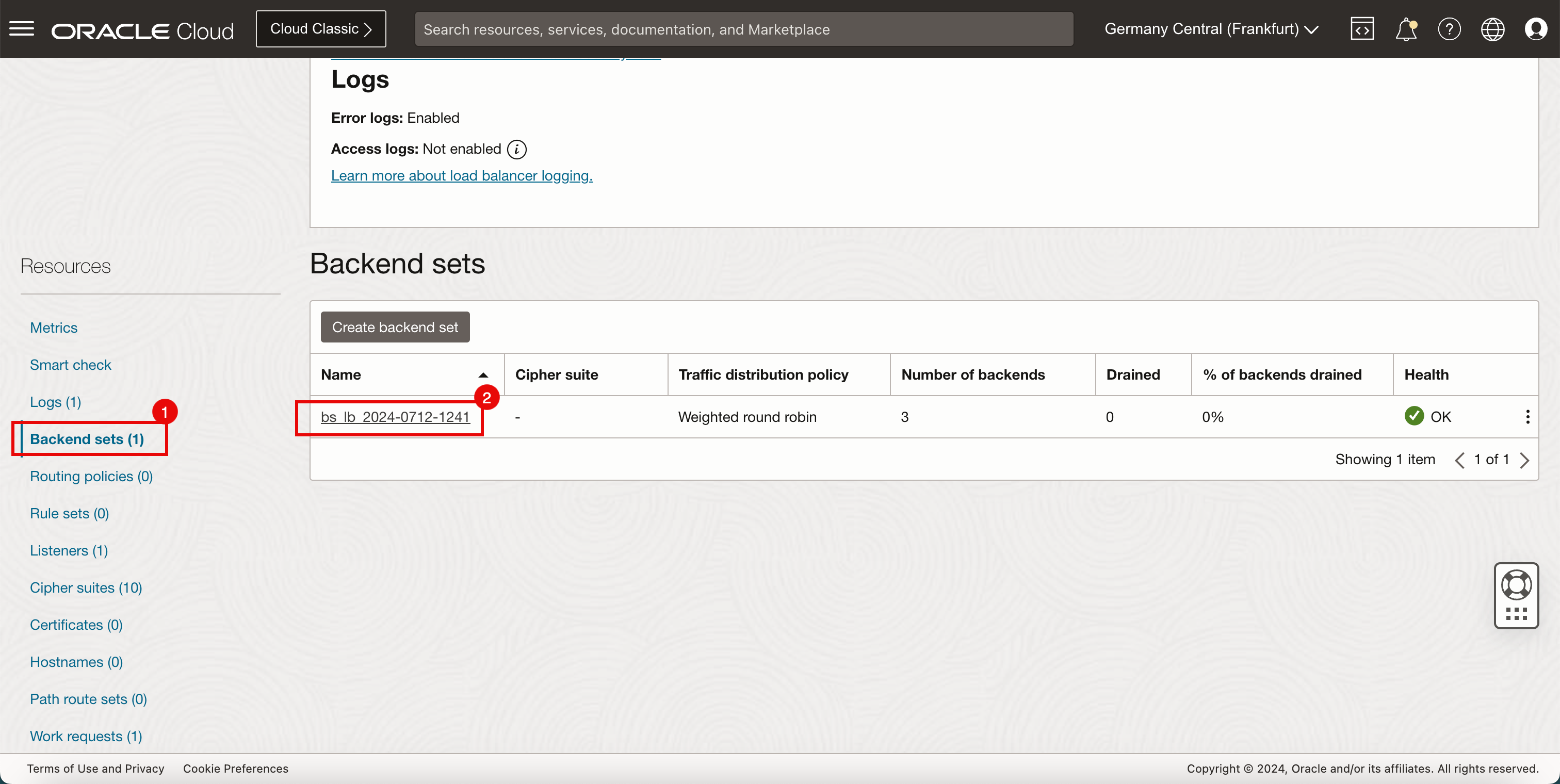
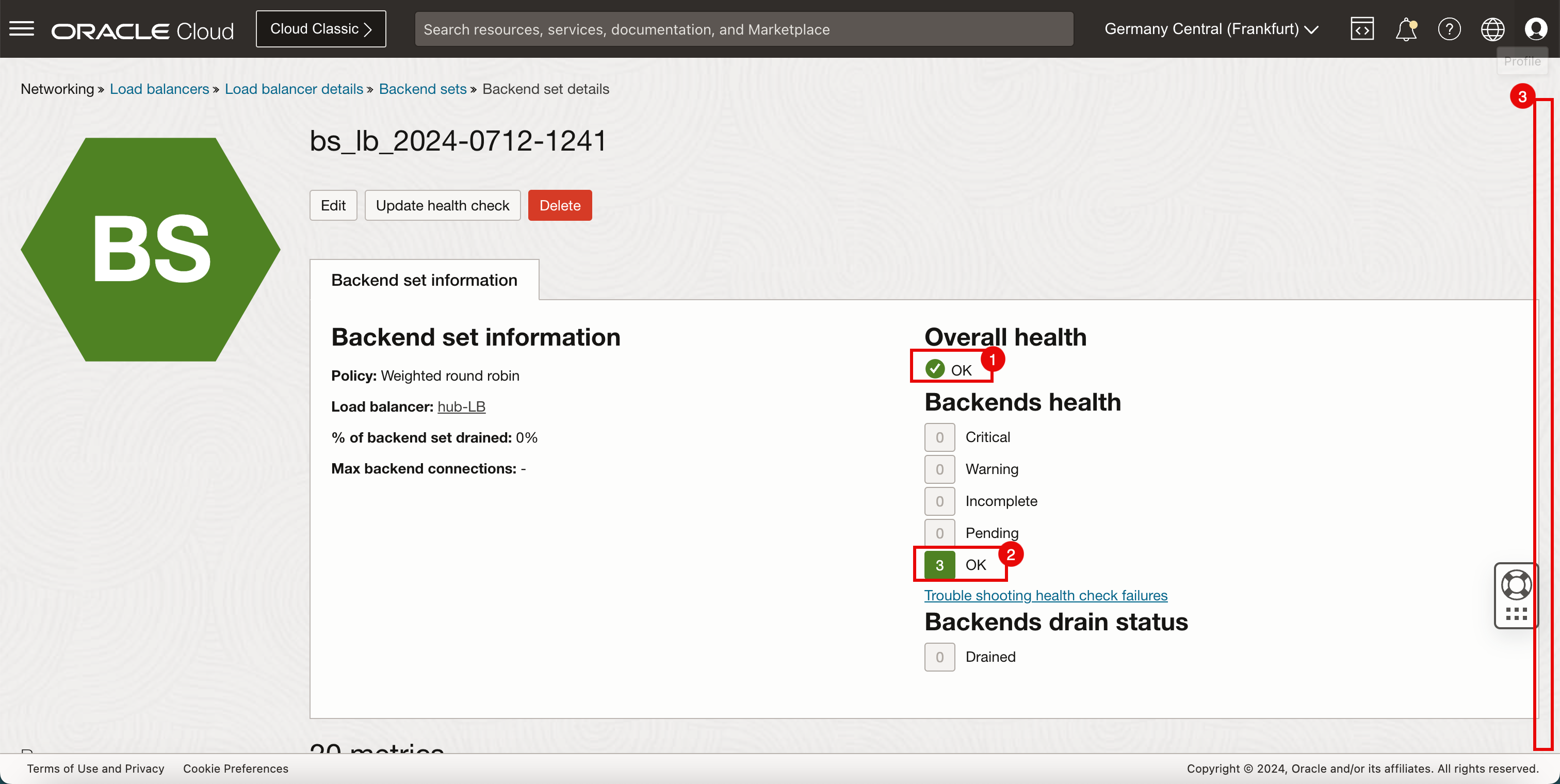
- Note that the Overall health is OK.
- Note that the Backend sets health is OK.
- Scroll down.
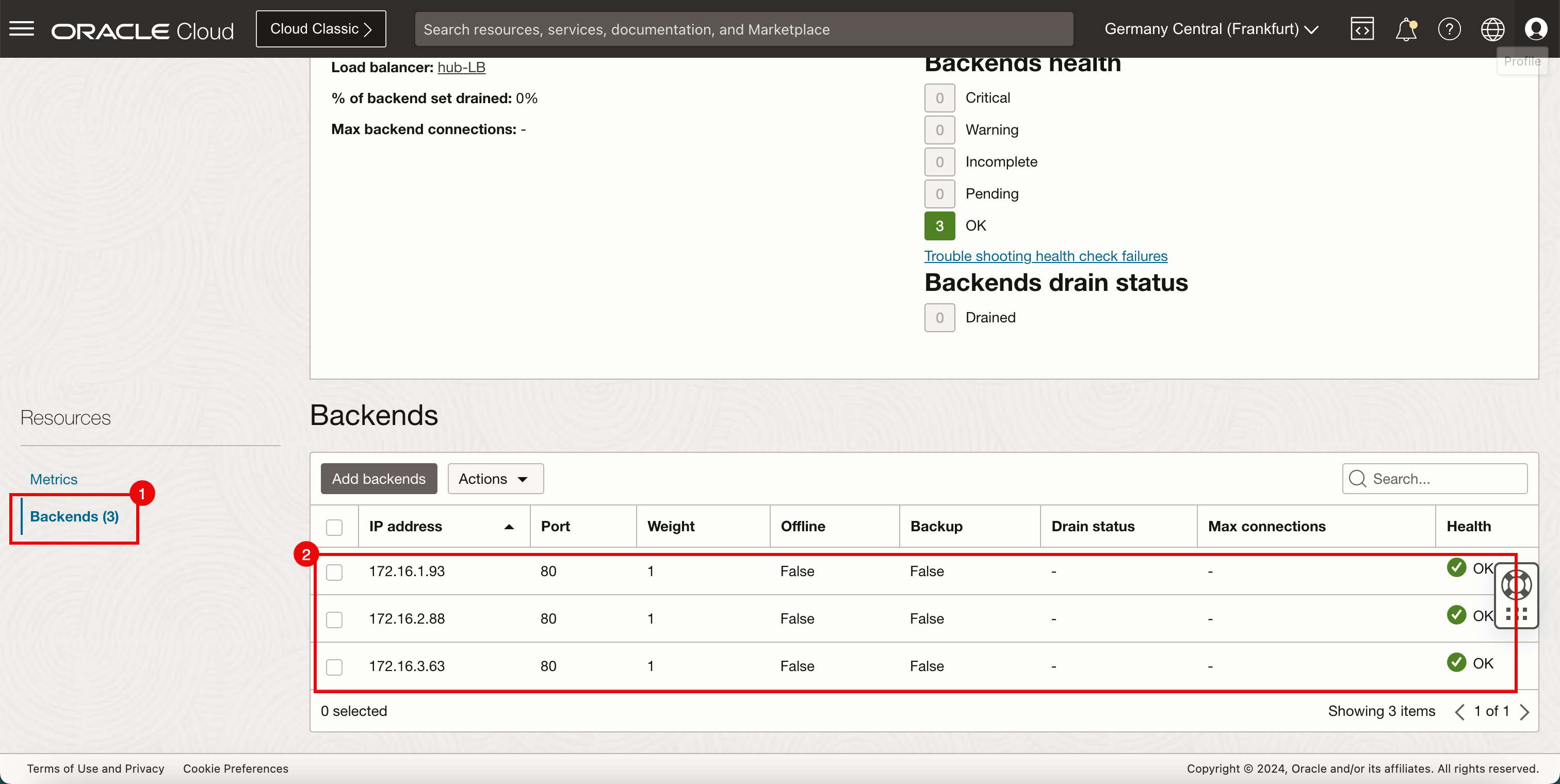
- Click Backends.
- Note the backends in the Backends section.
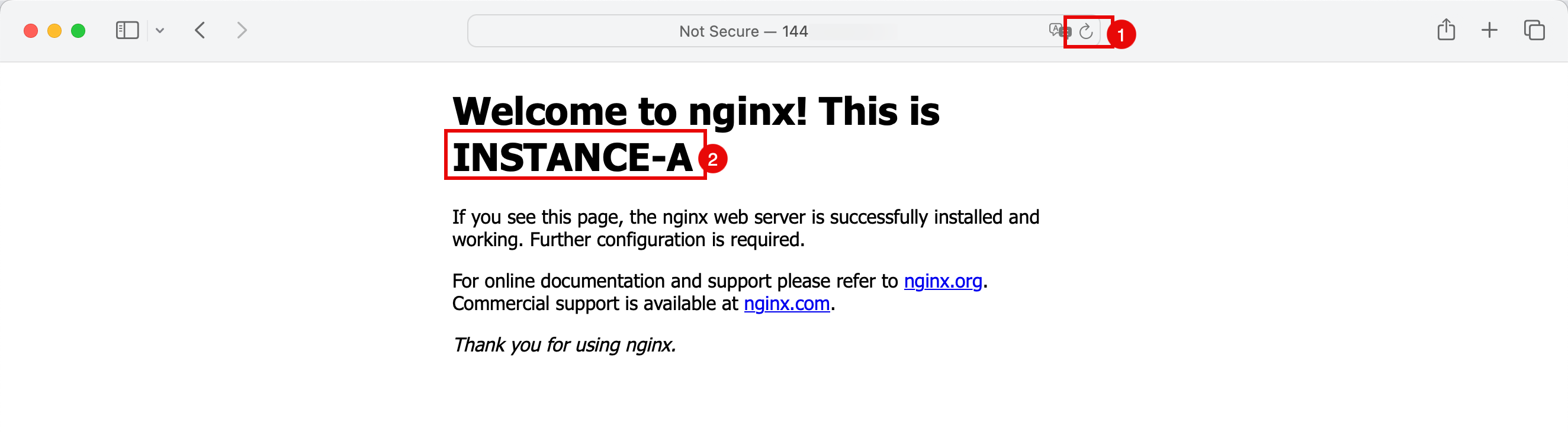
- Open a new browser.
- Enter the public IP address of the load balancer.
- Note that the load balancer redirects the traffic to the instance in the spoke VCN B.
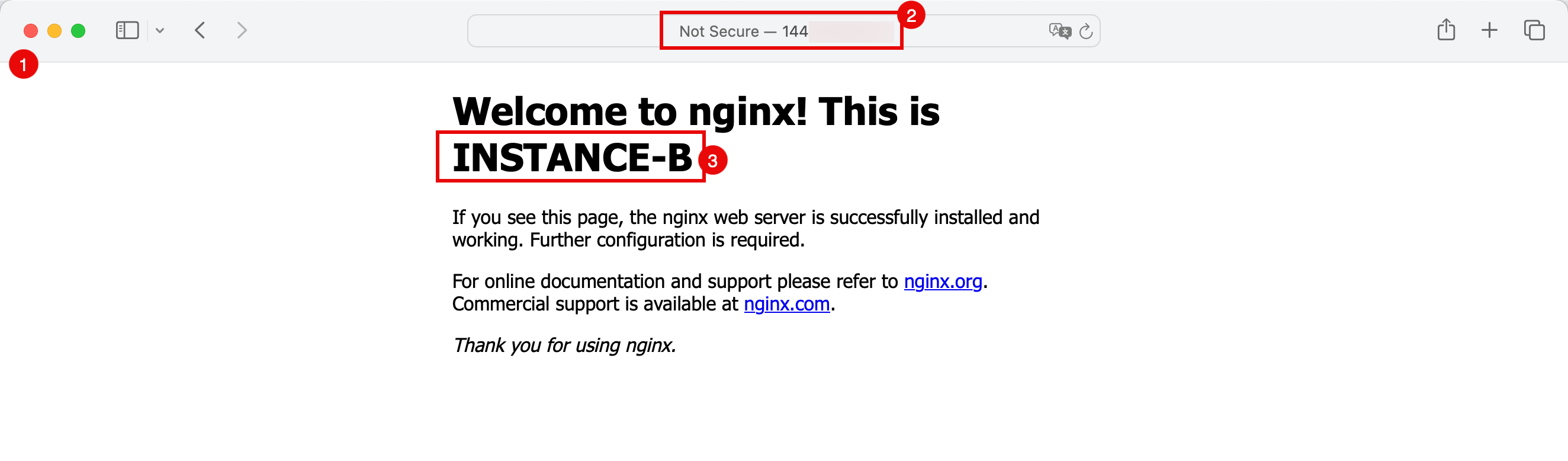
- Refresh the page.
- Notice that the load balancer now redirects the traffic to the instance in the spoke VCN C.
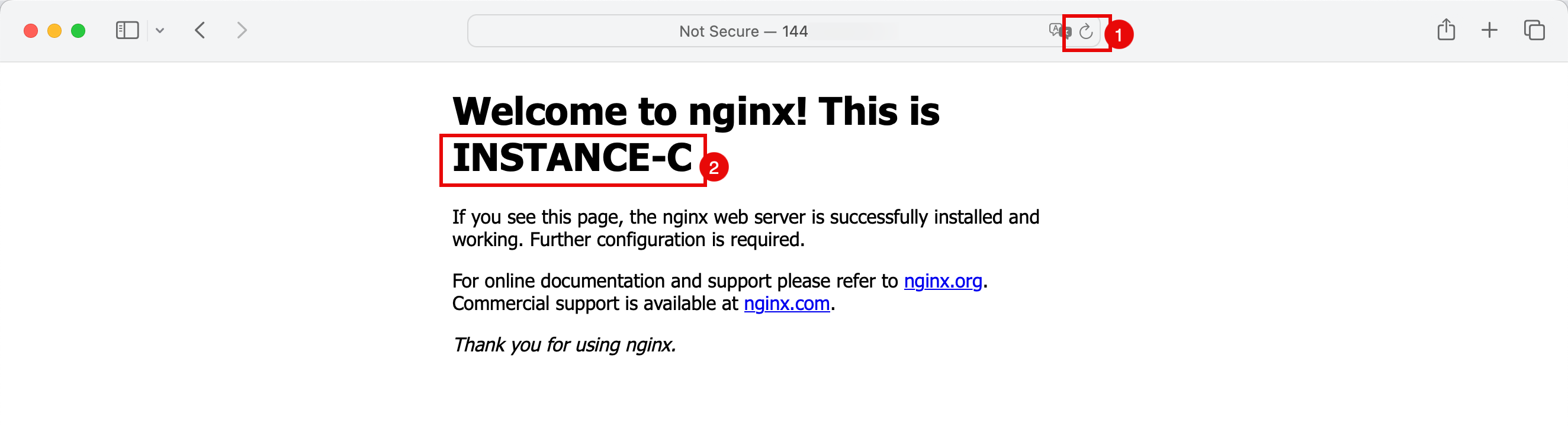
- Refresh the page.
- Note that the load balancer now redirects the traffic to the instance in the spoke VCN B again.
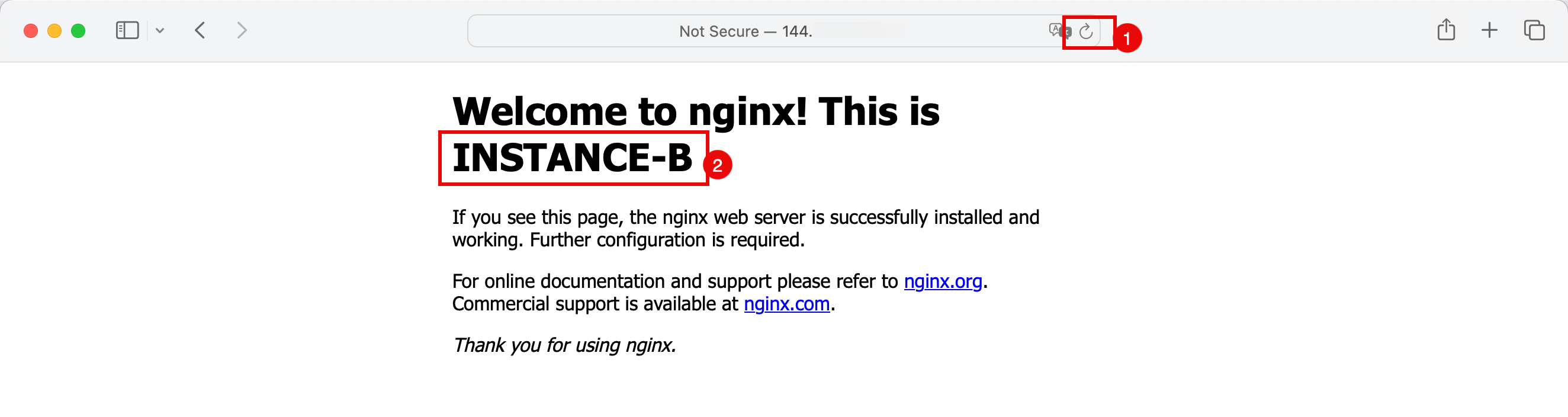
- Refresh the page.
- Note that the load balancer now redirects the traffic to the instance in the spoke VCN A.
-
The following image illustrates what you have created so far and how the traffic is flowing.
-
Make sure that the hub firewall is allowing port TCP/80 from the load balancer to the backend servers. In this tutorial, we allowed all traffic in the hub firewall for testing purposes.
Task 6: Install and Configure an OCI Web Application Firewall
-
Configure the OCI Web Application Firewall.
- Click the hamburger menu (≡) from the upper left corner.
- Click Identity & Security.
- Click Web Application Firewall.
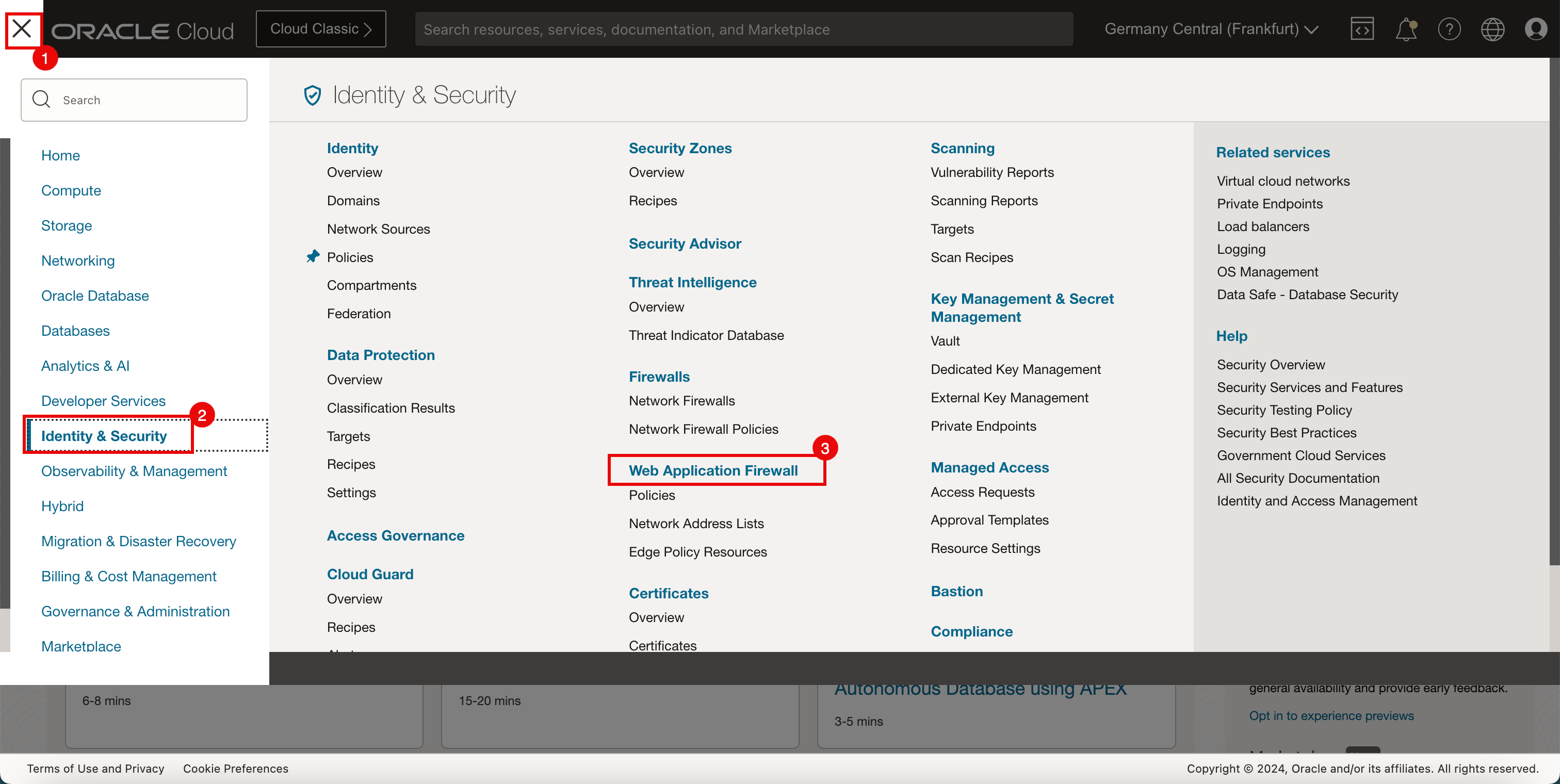
-
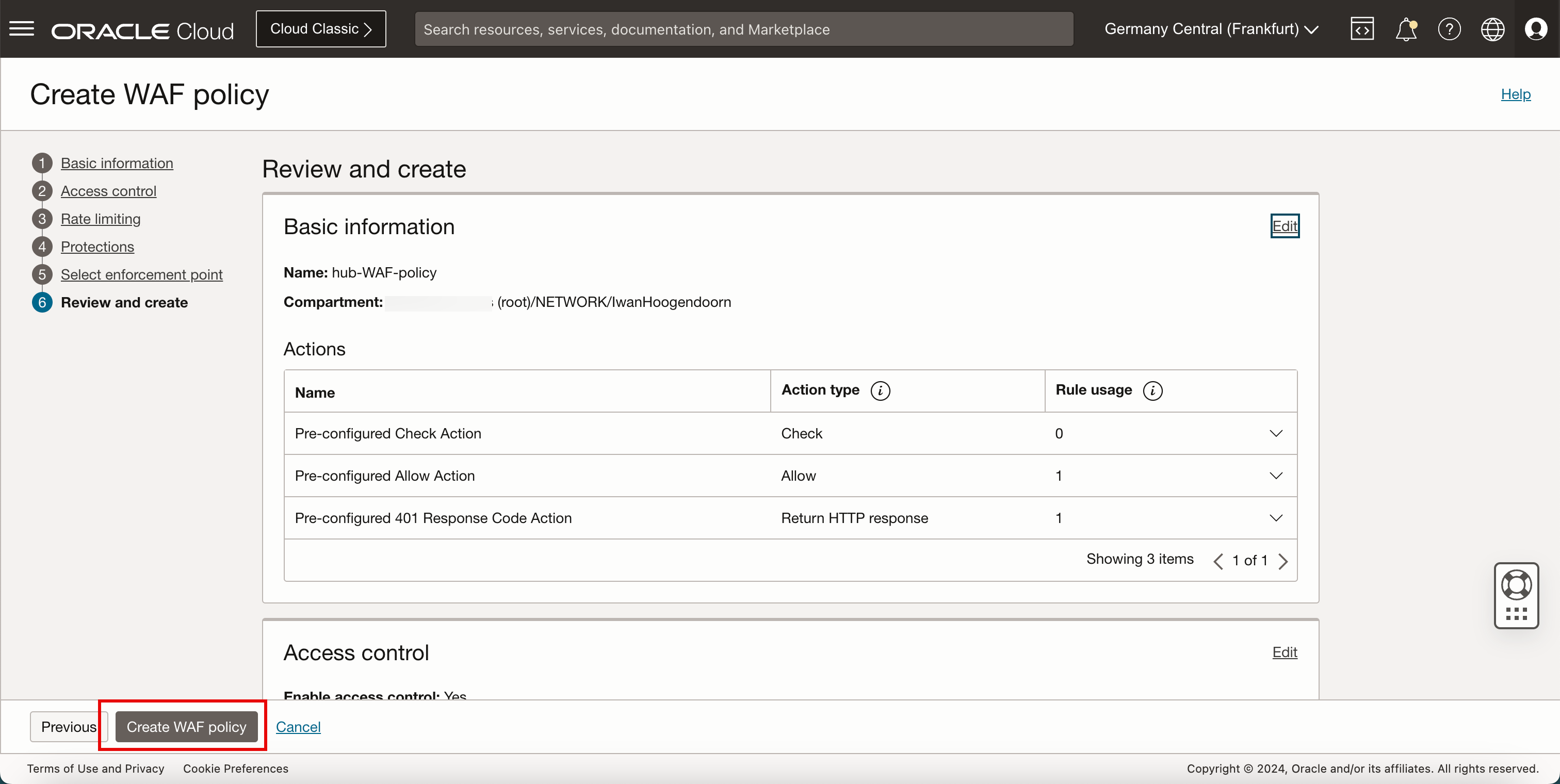
Click Create WAF Policy.
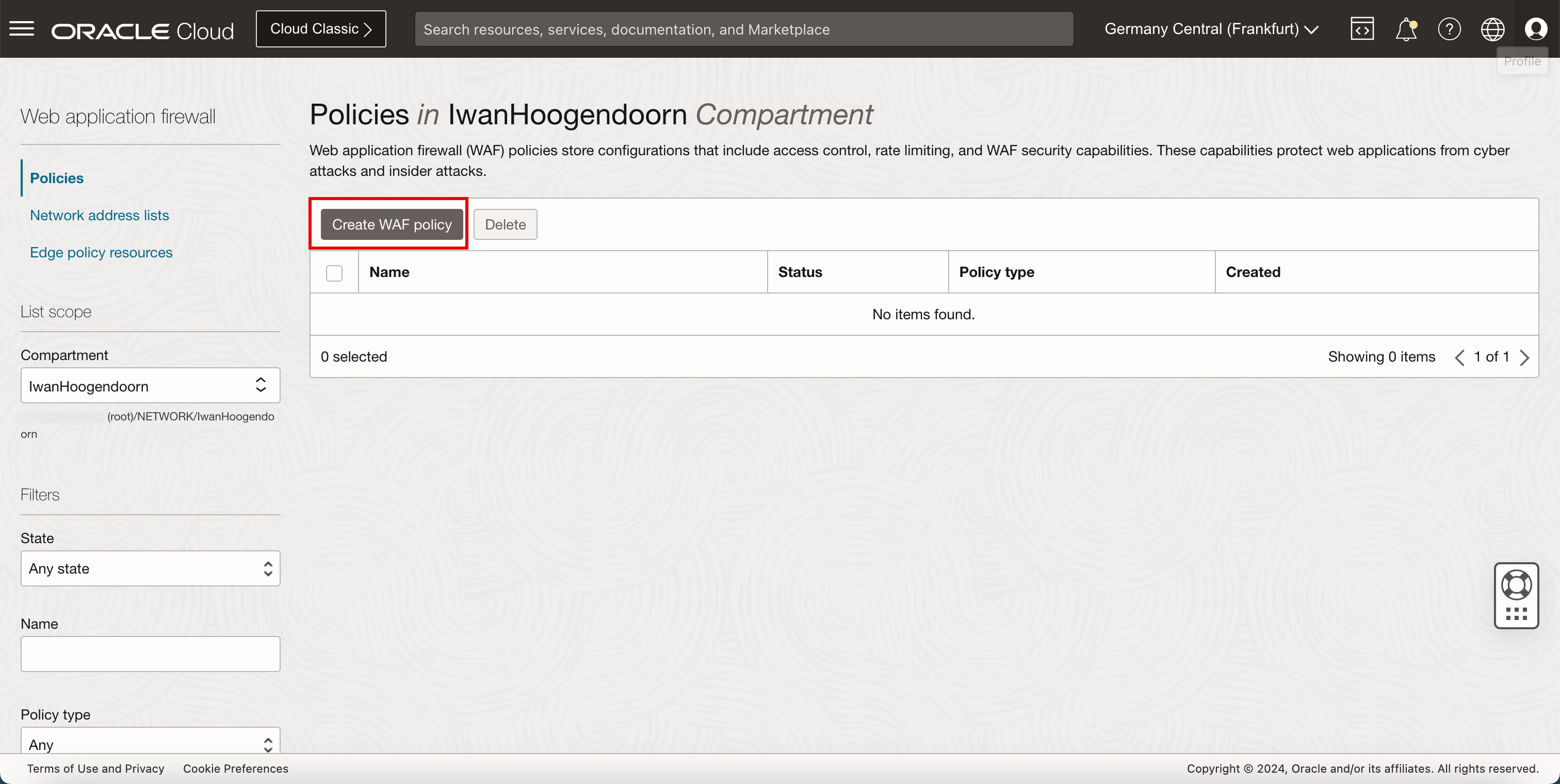
- Enter a Name for the WAF policy.
- Click Next.
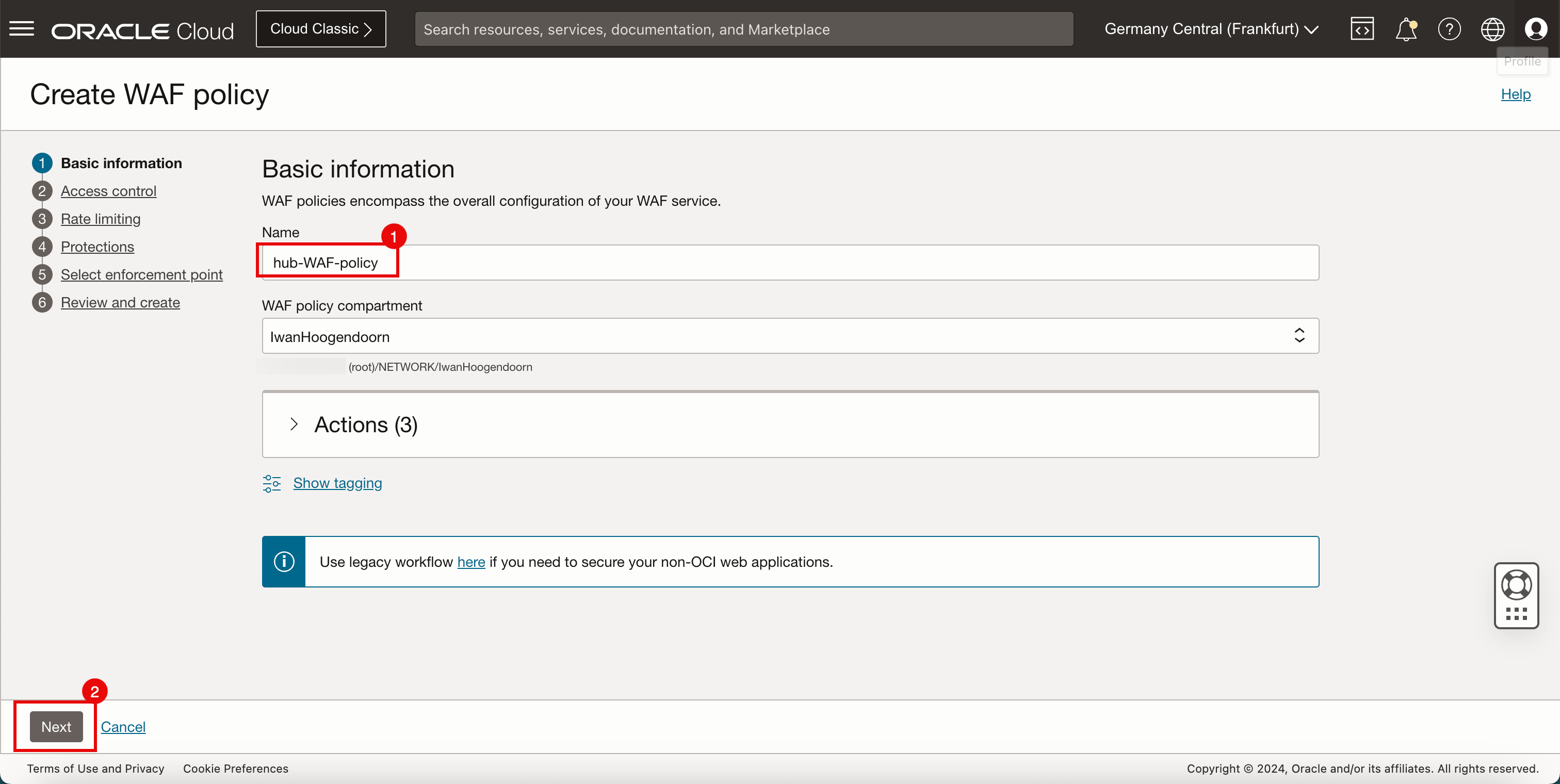
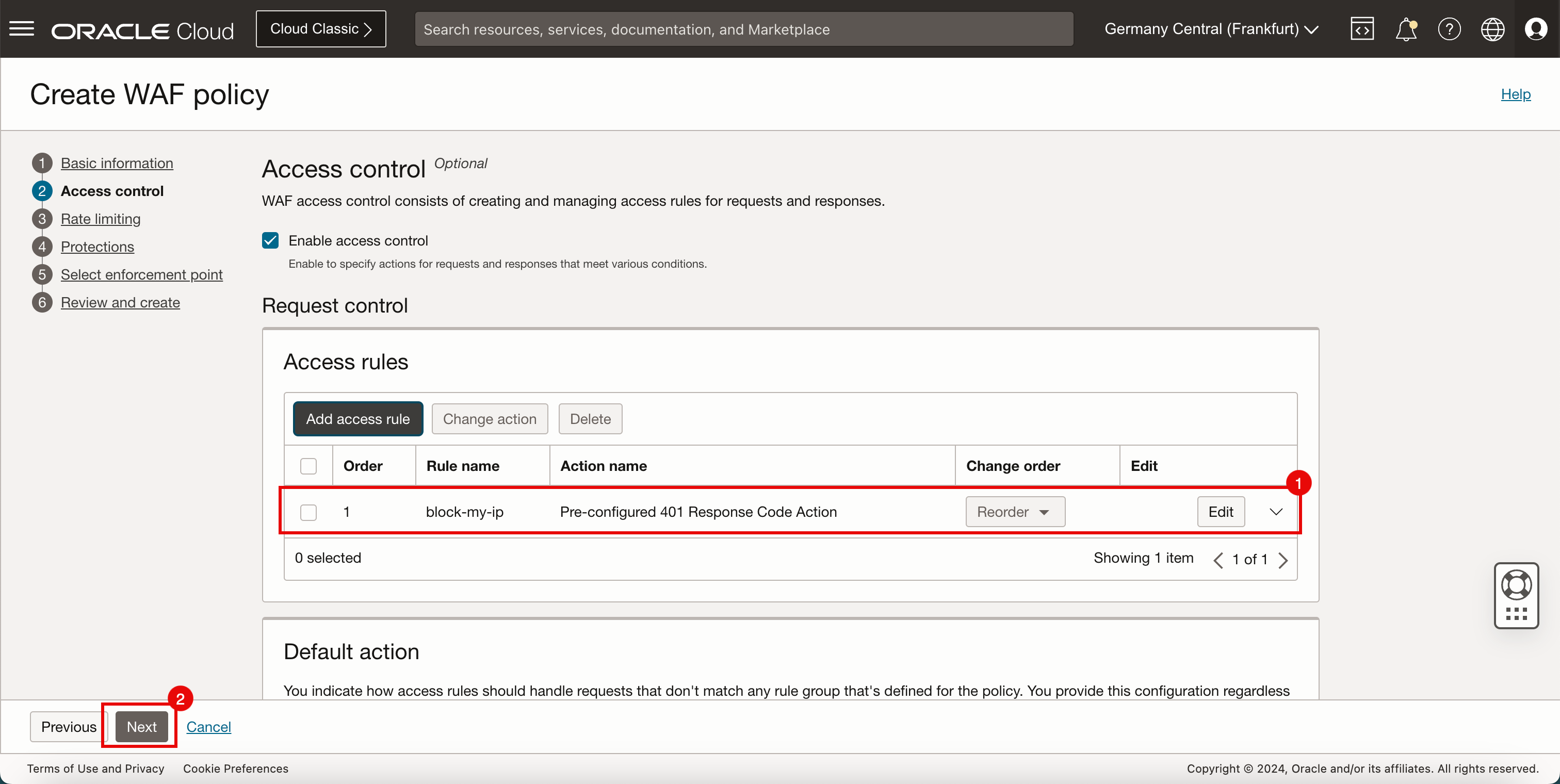
- Make sure that Enable access control is enabled.
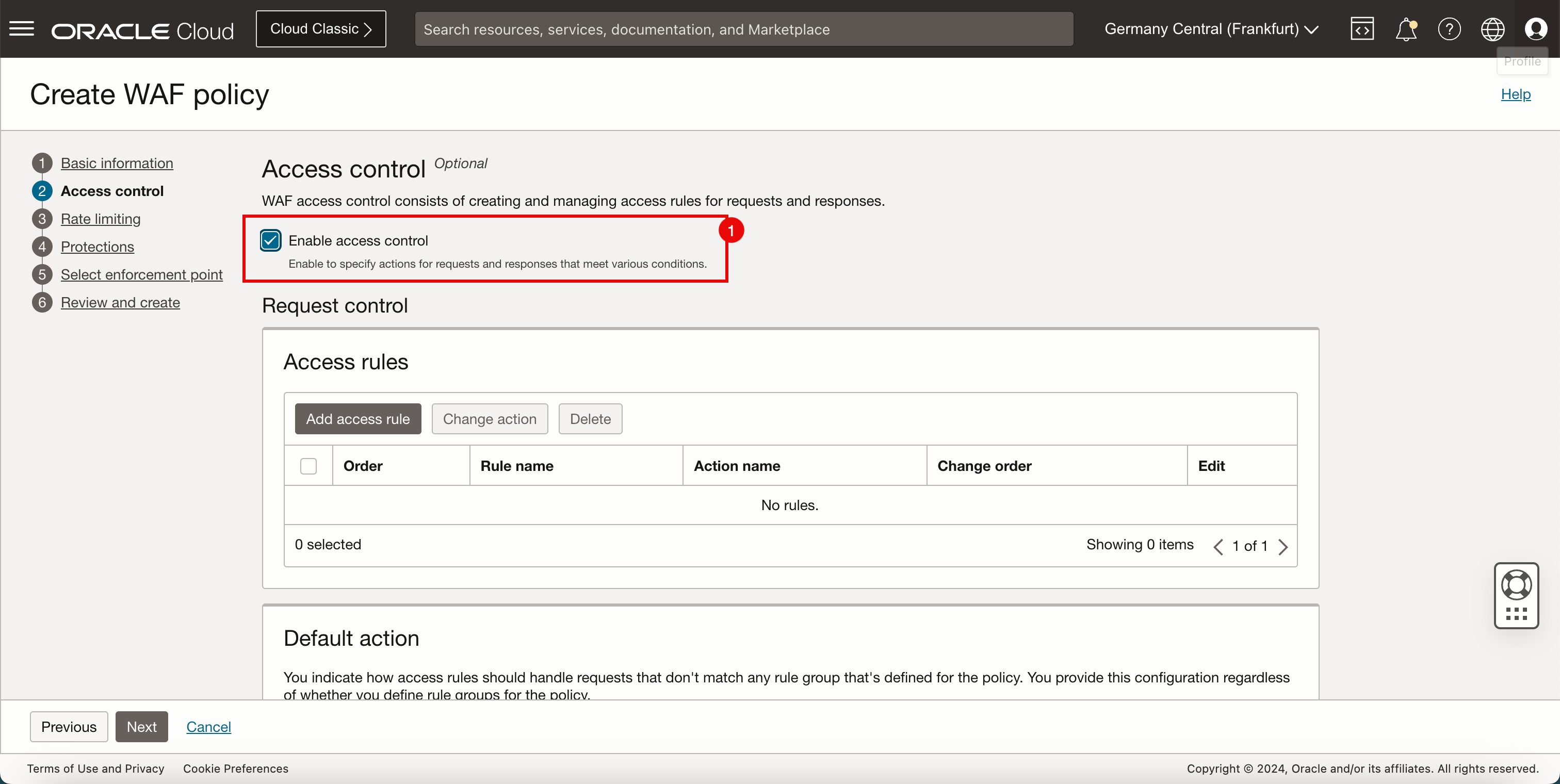
-
Use a website that is capable of retrieving your ISP IP address. This is required to configure your access control in the OCI Web Application Firewall. In this tutorial, we are using
www.ipchicken.comto retrieve ISP IP address.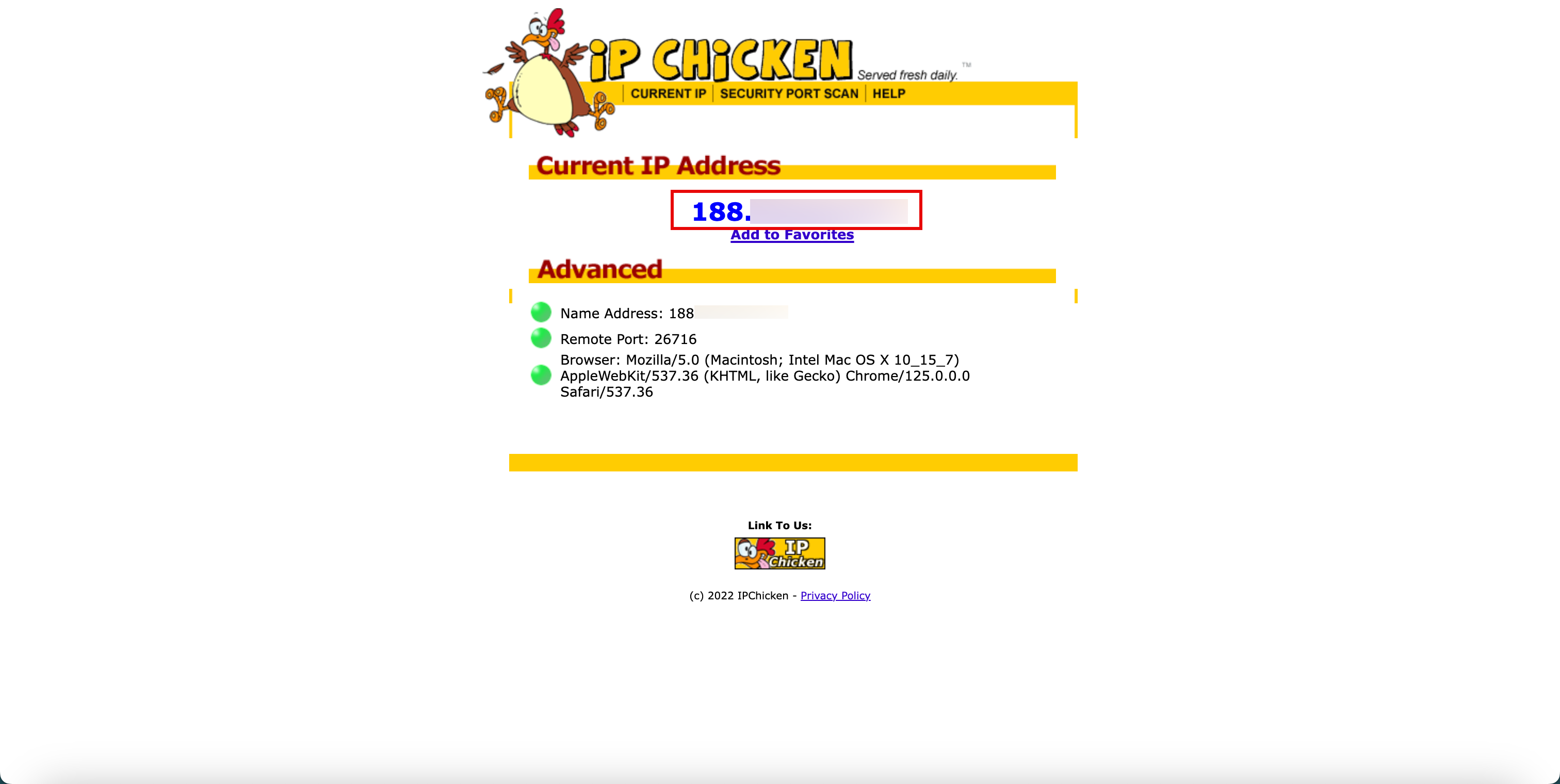
-
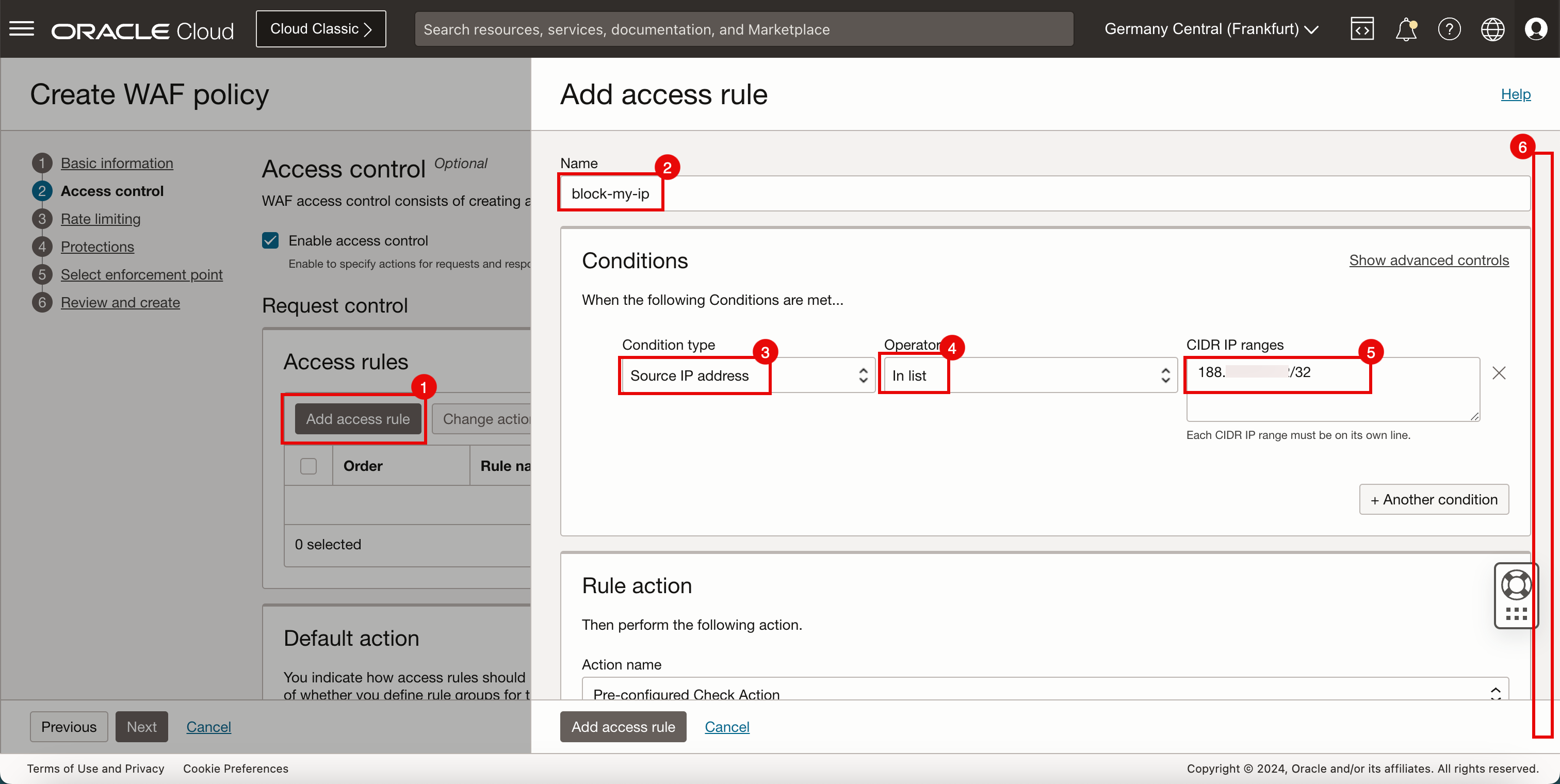
In the Add access rule section, enter the following information.
- Click Add access rule.
- Enter a Name for the access rule.
- Condition Type: Select Source IP address.
- Operator: Select In list.
- CIDR IP ranges: Enter the IP address of your own ISP.
- Scroll down.
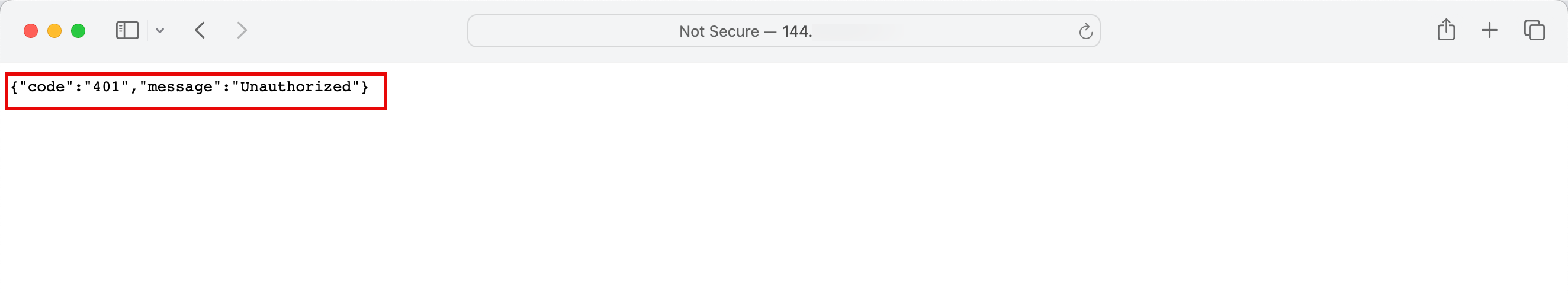
- In Rule action, enter the action name and select Pre-configured 401 Response Code Action.
- Click Add access rule.
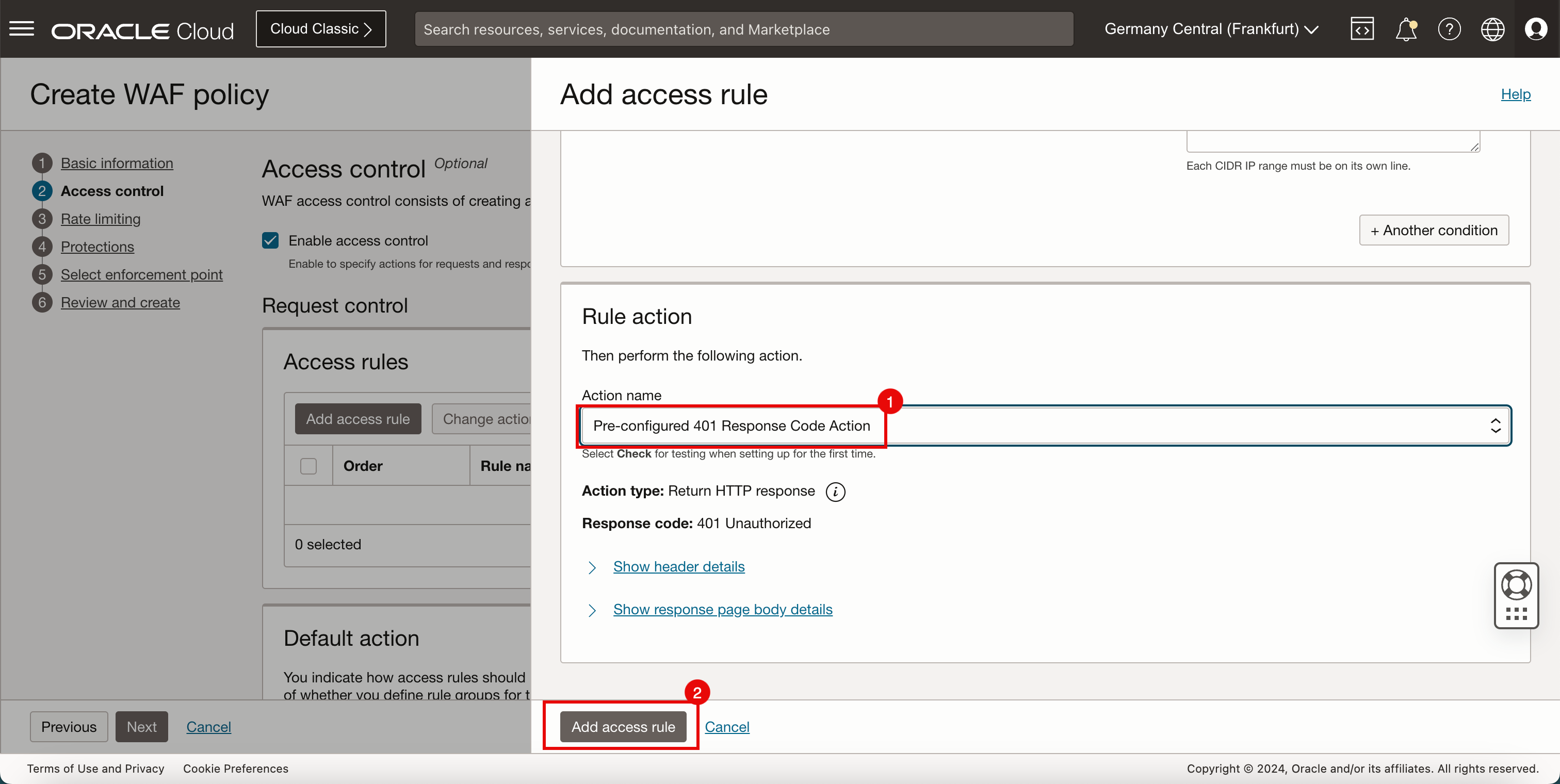
- Note that the access rule has been added.
- Click Next.
-
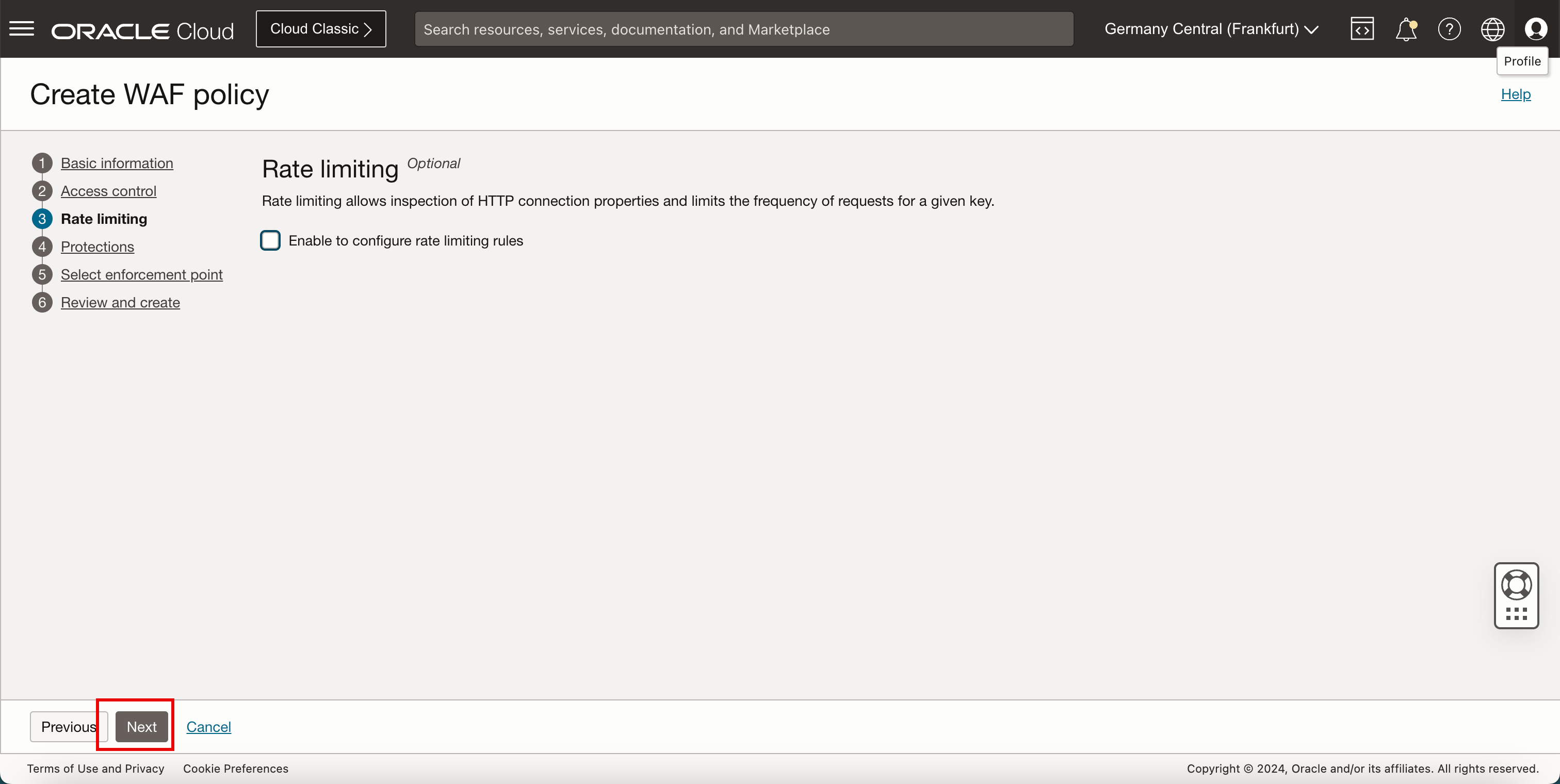
Click Next.
-
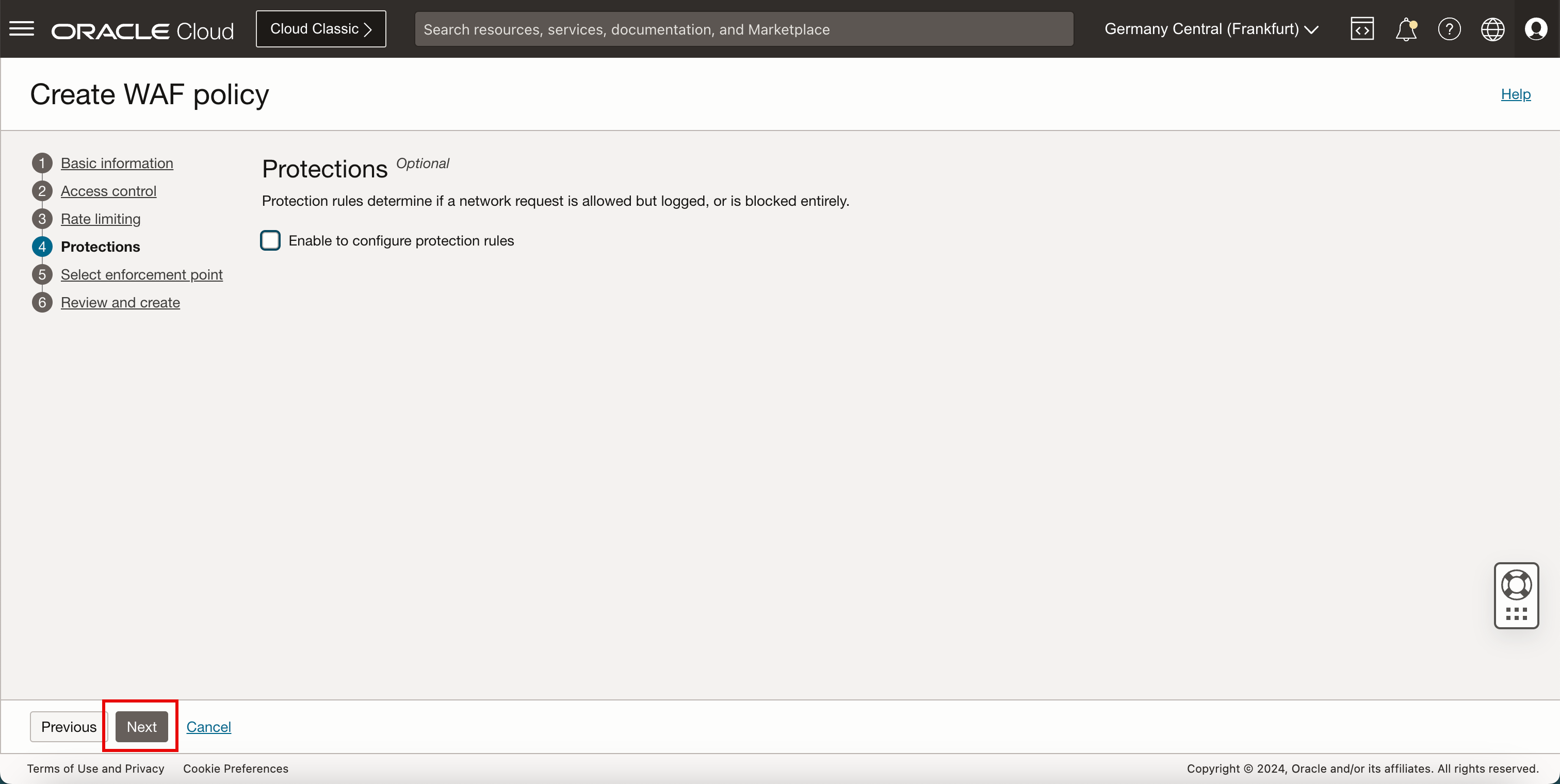
Click Next.
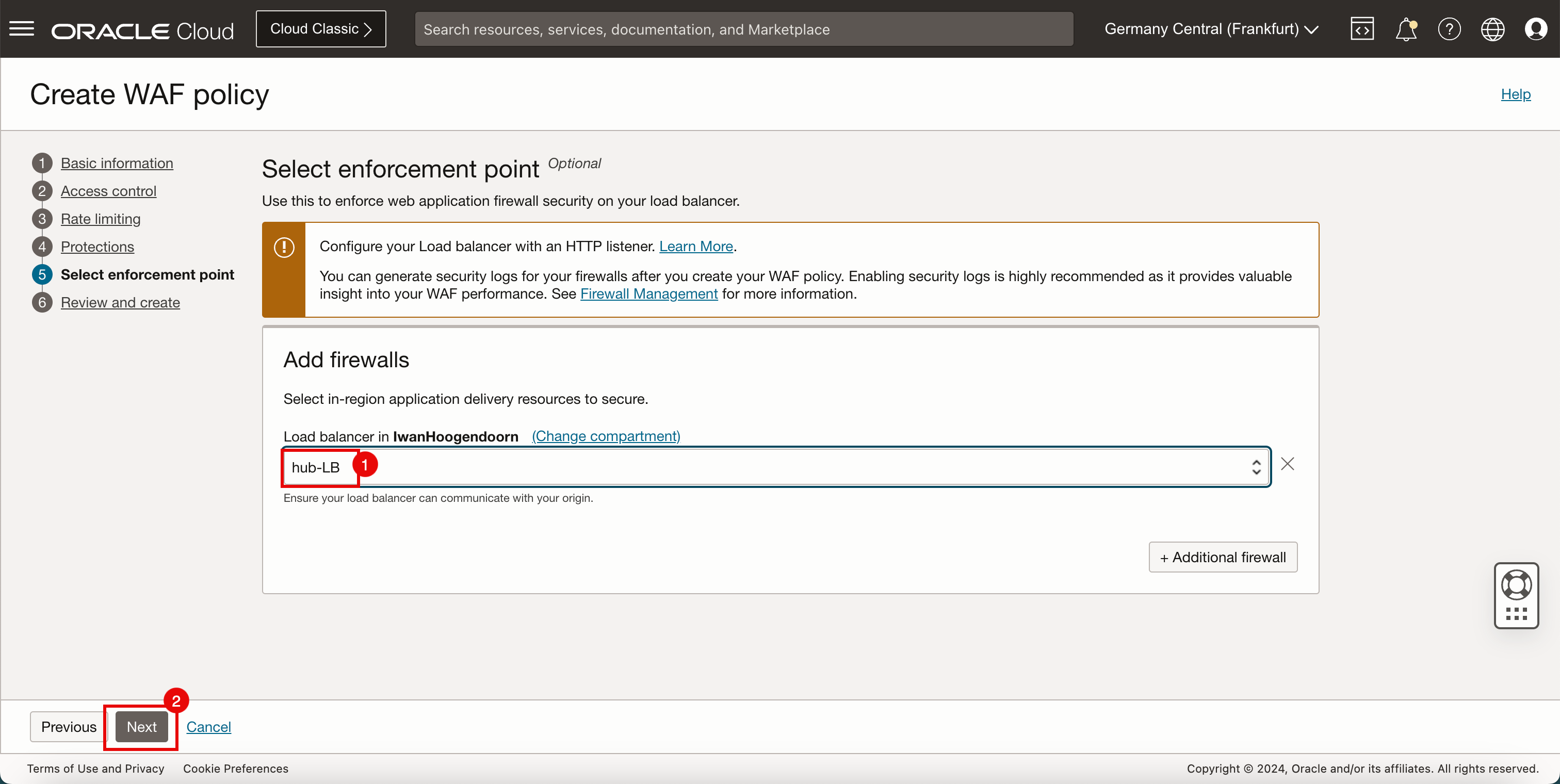
- Select the Load balancer that you want to configure the WAF policy on. Use the load balancer created in Task 5.
- Click Next.
-
Click Create WAF policy.
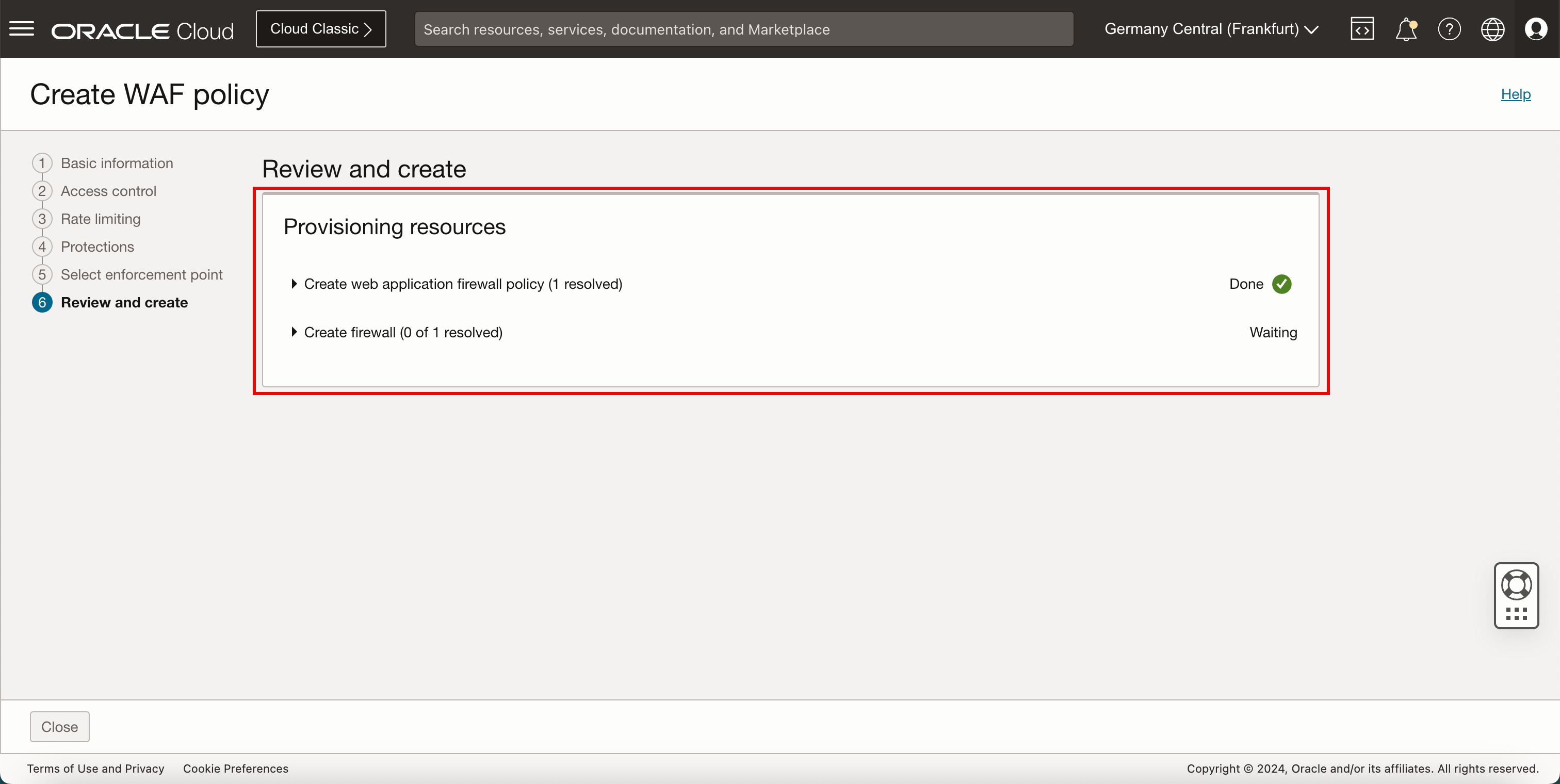
-
Note that the WAF policy is created.
- Note that the status of the WAF policy is ACTIVE.
- Click Policies to return to the WAF policies page.
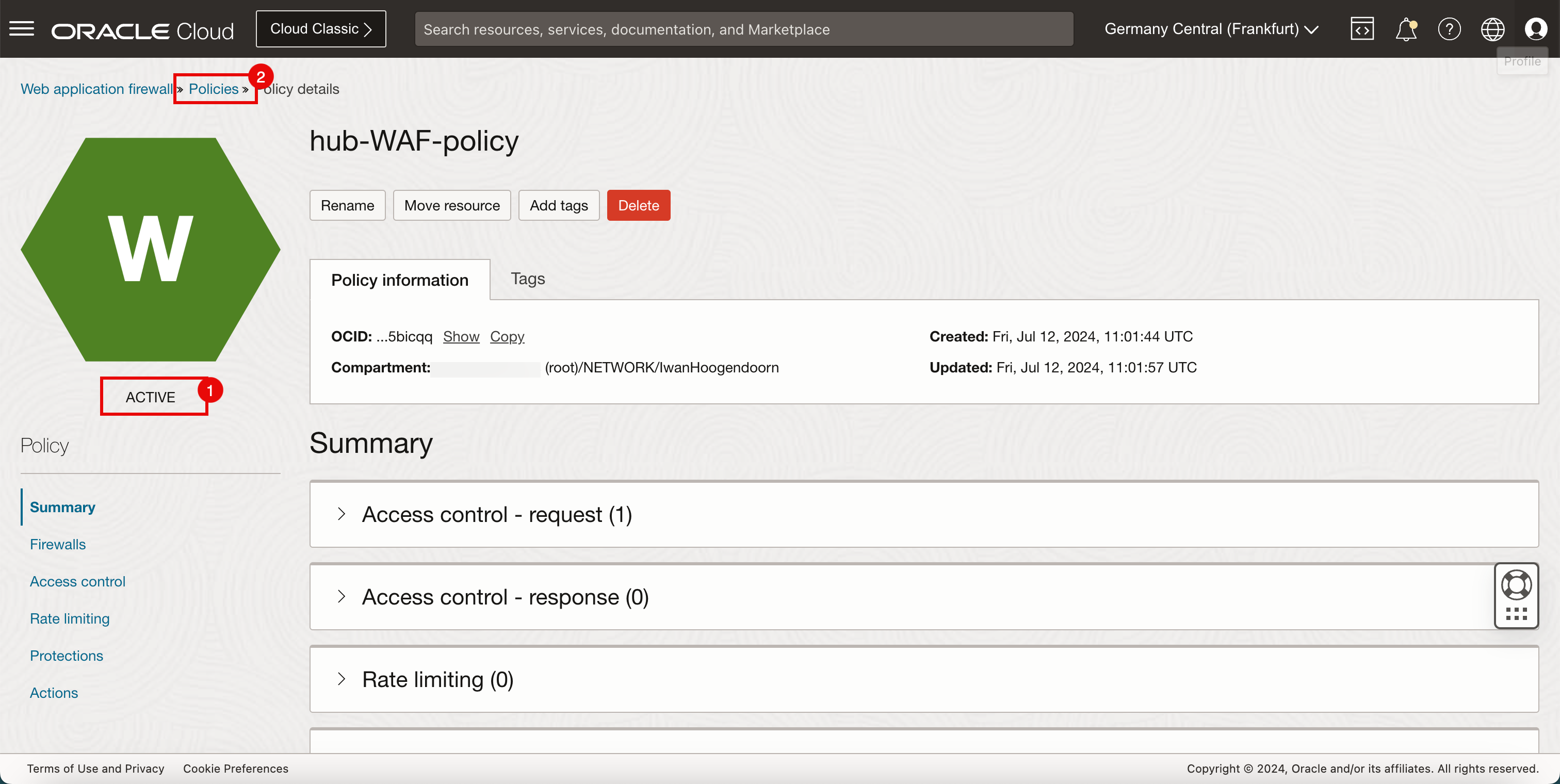
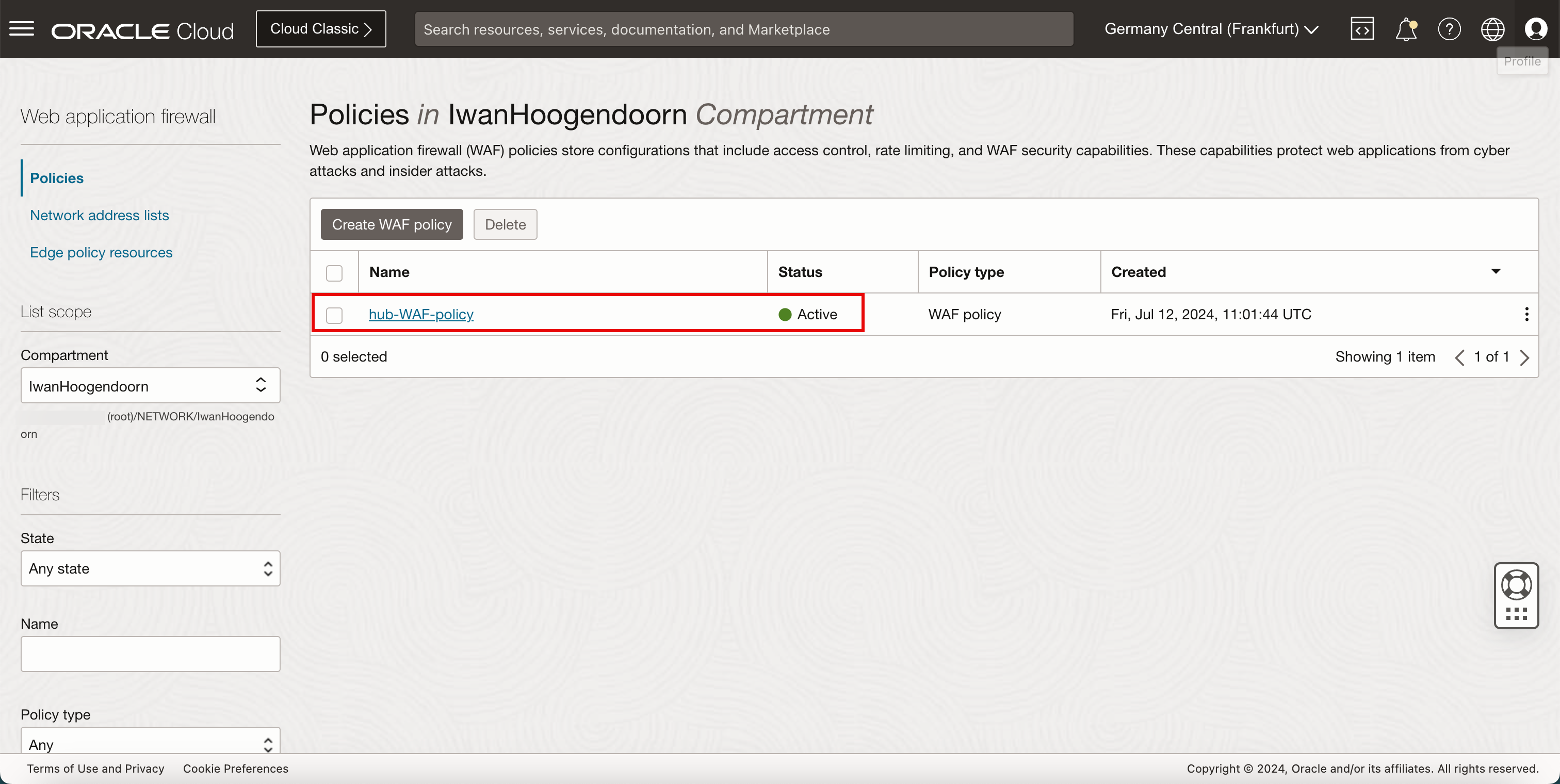
-
Note the WAF policy that we just configured.
Task 7: Test the OCI WAF, OCI Load Balancer Connectivity and WAF Security
-
Open the browser used in Task 5 and refresh the page.
Note: If you closed it, enter the public IP address of the load balancer.
-
Note that the web servers can no longer be accessed because we have blocked them with the WAF policy.
Acknowledgments
- Author - Iwan Hoogendoorn (OCI Network Specialist)
More Learning Resources
Explore other labs on docs.oracle.com/learn or access more free learning content on the Oracle Learning YouTube channel. Additionally, visit education.oracle.com/learning-explorer to become an Oracle Learning Explorer.
For product documentation, visit Oracle Help Center.
Add OCI Load Balancer and OCI WAF to a Hub with Hub and Spoke VCN Routing Architecture
G12085-01
July 2024