Note:
- This tutorial requires access to Oracle Cloud. To sign up for a free account, see Get started with Oracle Cloud Infrastructure Free Tier.
- It uses example values for Oracle Cloud Infrastructure credentials, tenancy, and compartments. When completing your lab, substitute these values with ones specific to your cloud environment.
Use Oracle Cloud Infrastructure to Publish a Webserver Accessible from the Internet with IPv6
Introduction
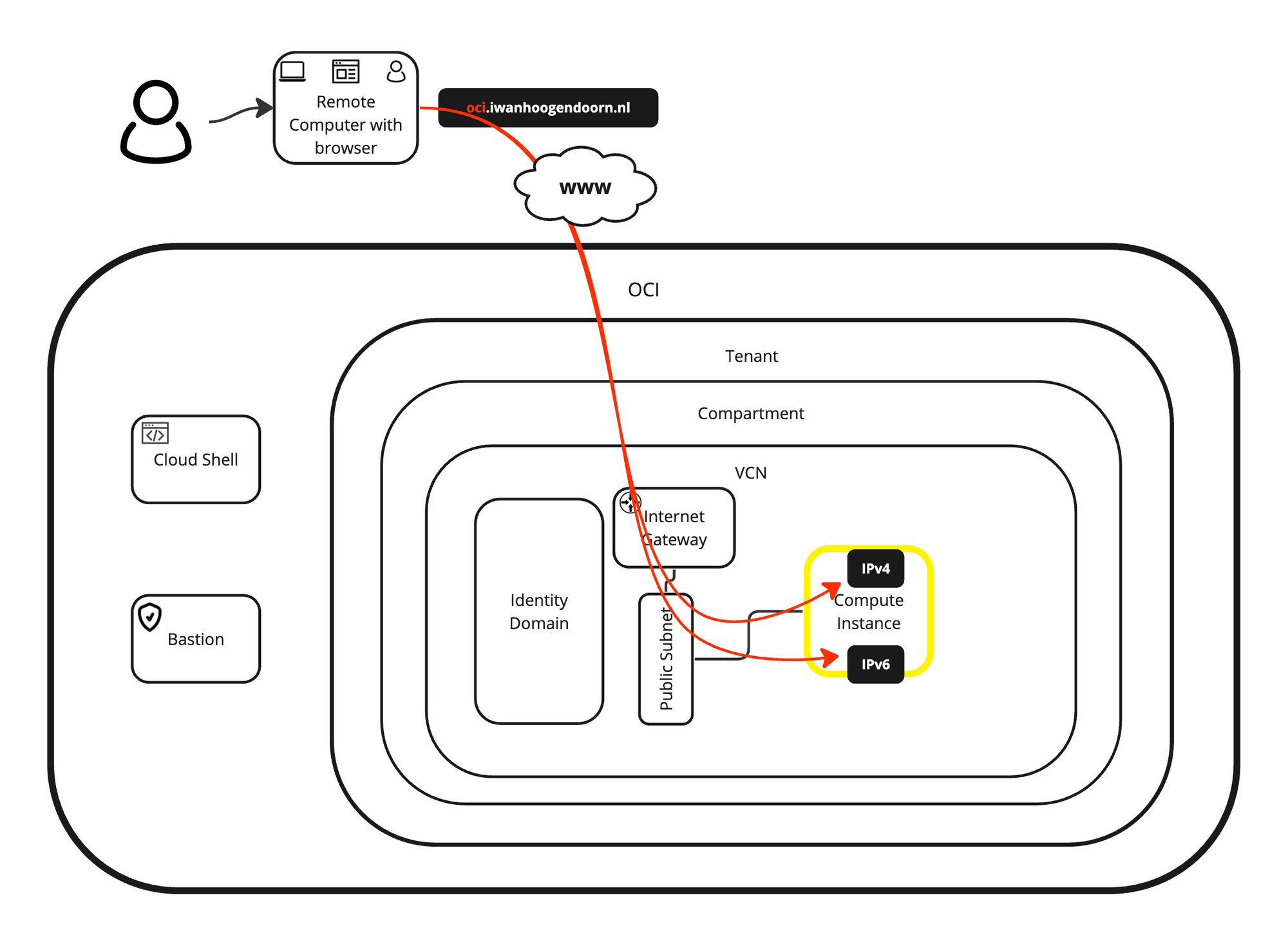
In this tutorial, we are going to explain how we can create a webserver (OCI instance) within Oracle Cloud Infrastructure (OCI) and we will make this webserver accessible from the internet. We are not only going to make this webserver accessible from a public IPv4 address, but will also make it accessible from the public IPv6 address with the DNS records (FQDN) fully configured.
Note: The domains that we have used in this tutorial were created and configured for testing purposes only.
Objectives
-
Create a website using an OCI instance that is reachable through IPv6. We have also explained how to create and configure all the other prerequisites to make the website available eventually. As a bonus, we have also explained how the NGINX webserver is installed and how PHP is integrated. At last, we will provide a custom PHP website or script that can be used to verify IPv4 or IPv6 connectivity to your web server and if you are connecting with HTTP or HTTPS.
- Task 1: Create a new VCN with IPv6 enabled.
- Task 2: Create a new subnet with IPv6 enabled.
- Task 3: Create a new instance with IPv6 enabled.
- Task 4: Create a new internet gateway and configure routing.
- Task 5: Open HTTP and HTTPS on the default security list.
- Task 6: Install a webserver on this instance.
- Task 7: Configure DNS records.
- Task 8: Create a custom website with NGINX and PHP.
- Task 9: Test the webserver from the internet.
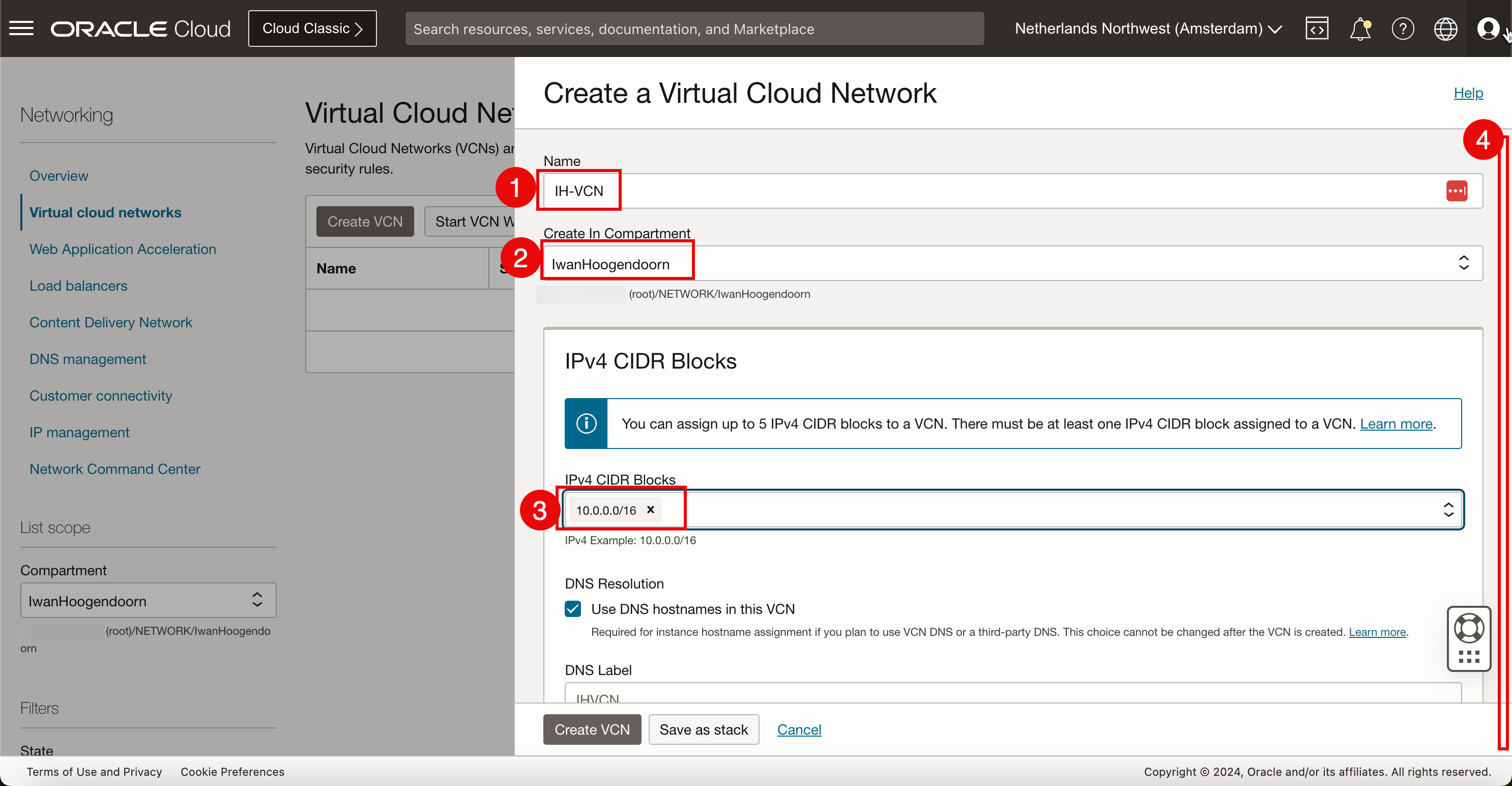
Task 1: Create a New VCN with IPv6 Enabled
-
Open the hamburger menu and click Virtual Cloud Networking.
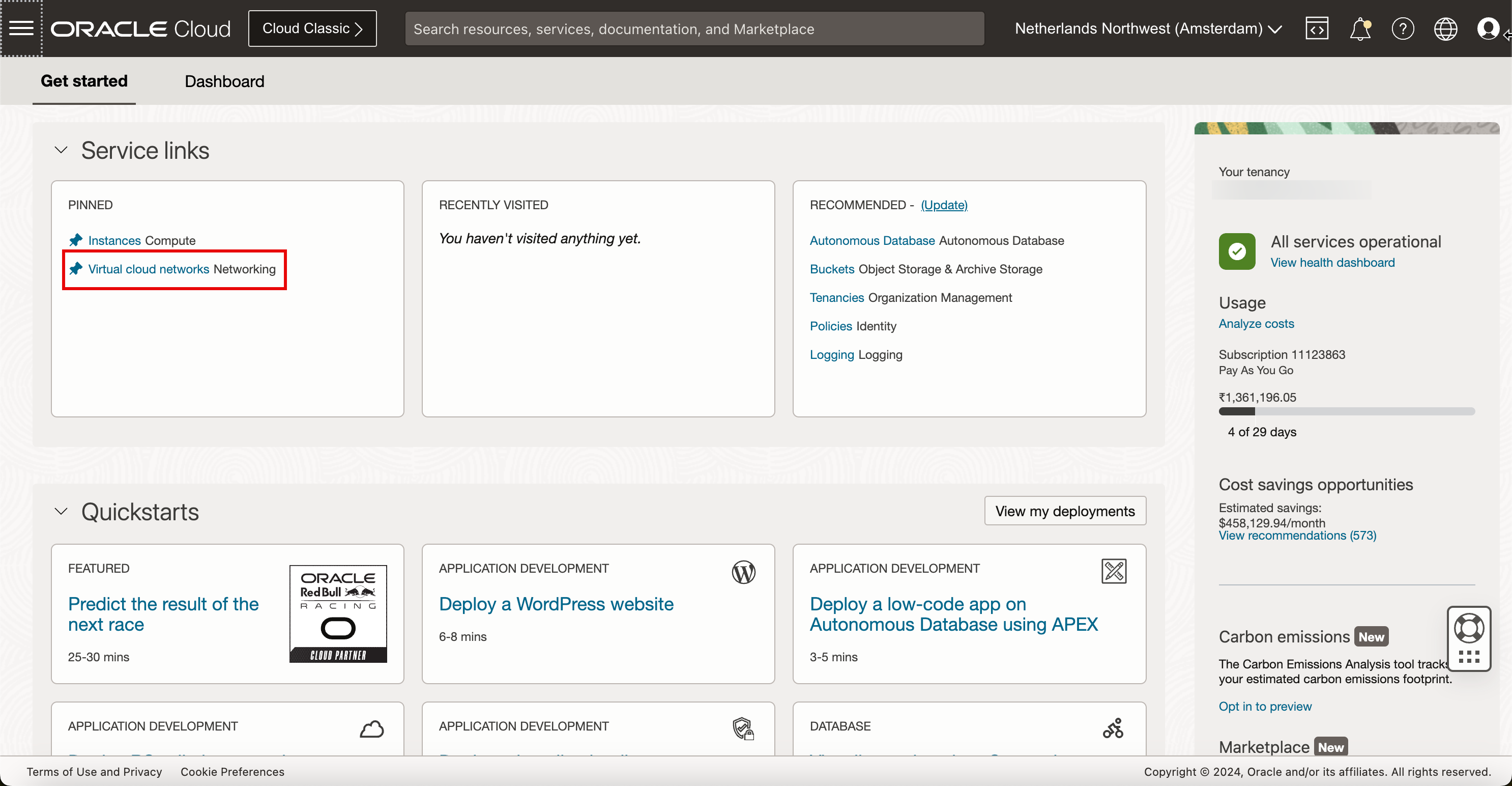
- Make sure you select Virtual Cloud Networks in the menu.
- Select the compartment that you want to work in. If you have not set up the compartment, use the root compartment.
- Click Create VCN.
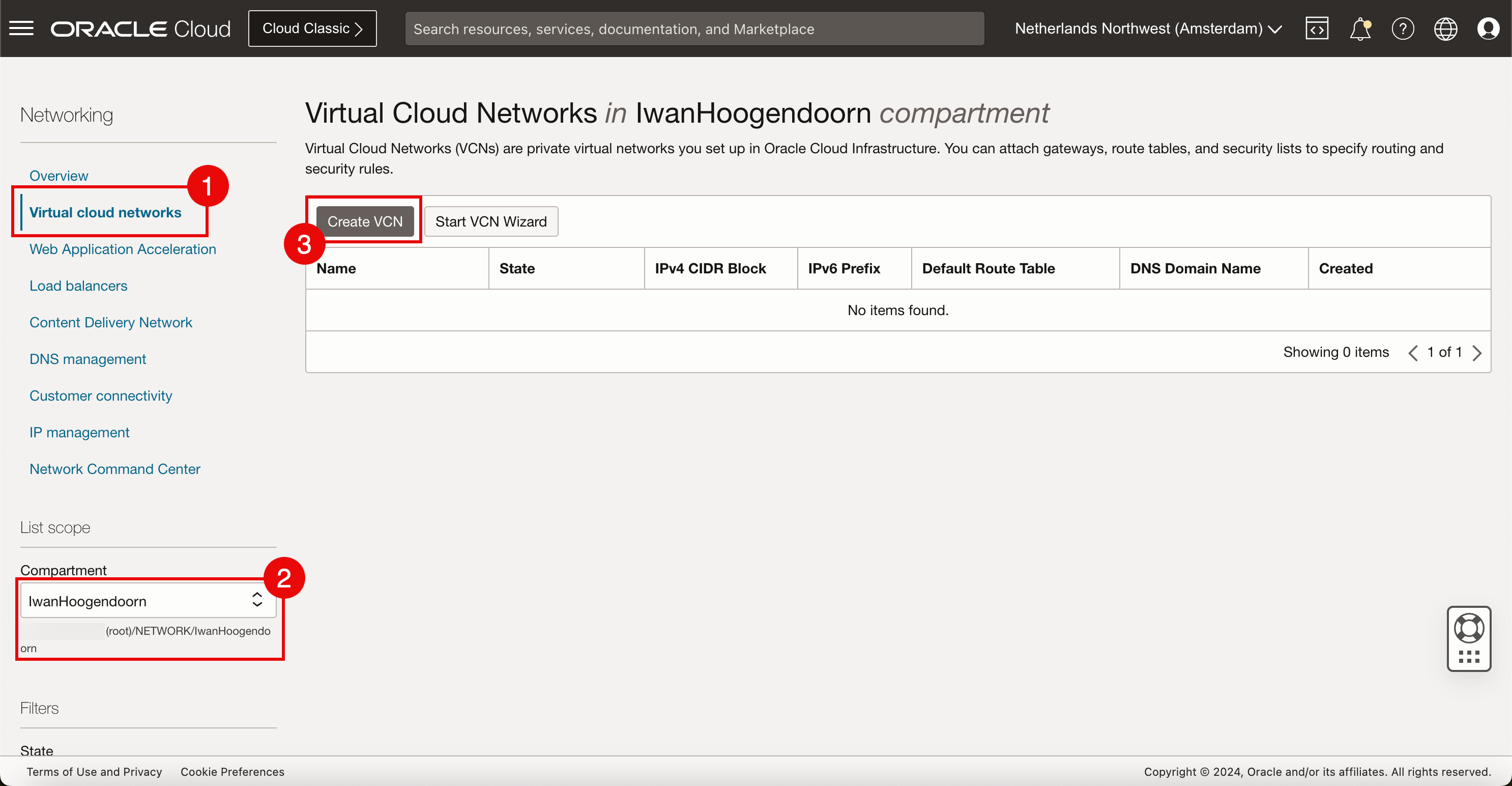
-
In Create a Virtual Cloud Networks, enter the following information.
- Enter a VCN Name.
- Select the compartment again, if it is not already pre-populated.
- Select the IPv4 CIDR that you want to use inside this VCN. For this tutorial, we have used a /16 CIDR because IPv4 Subnets (typically, /24’s) will be carved out of this CIDR clock.
- Scroll down.
- For IPv6, we will assign an Oracle allocated prefix. Select Assign an Oracle allocated /56 prefix.
- Click Create VCN.
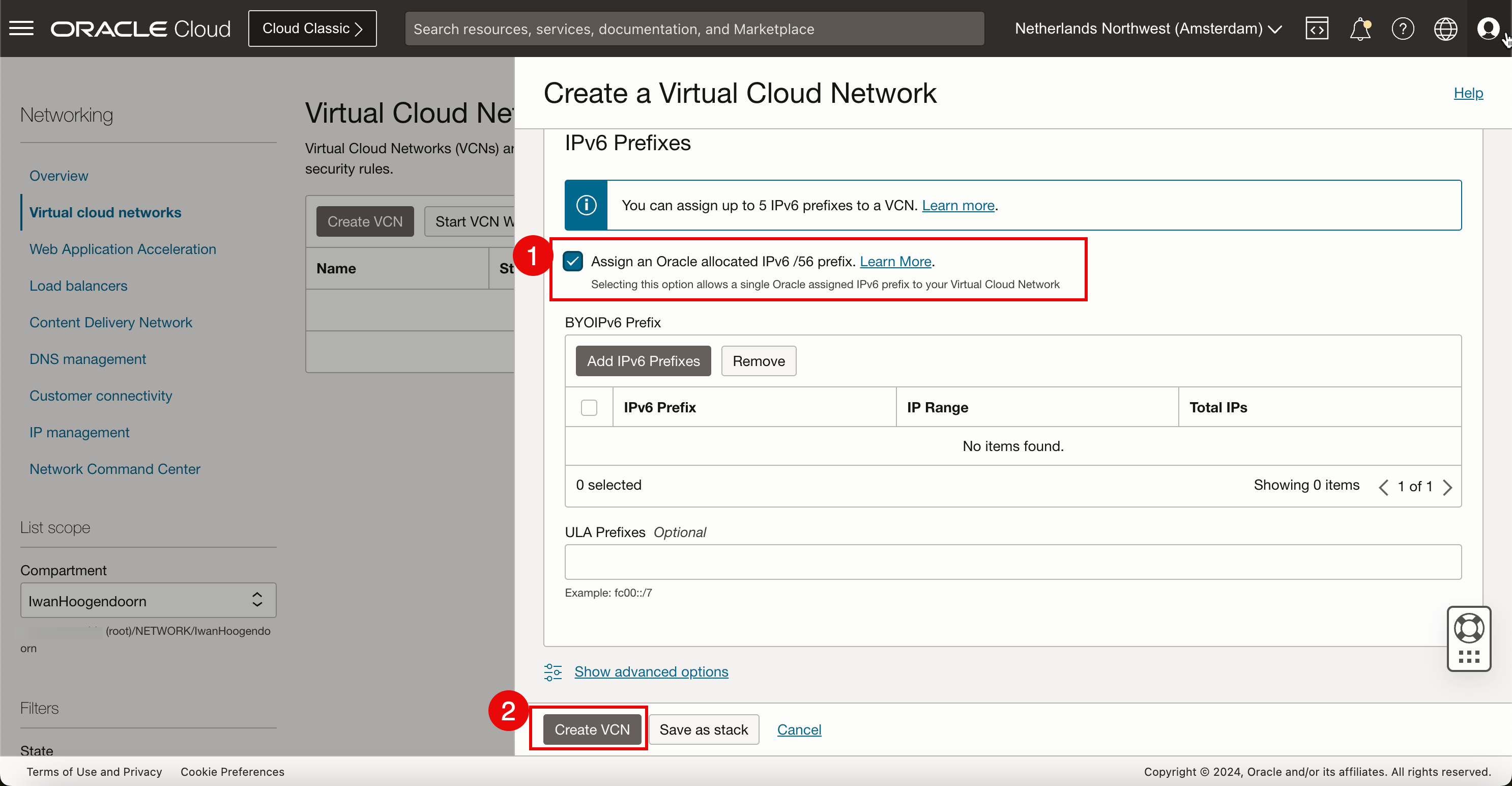
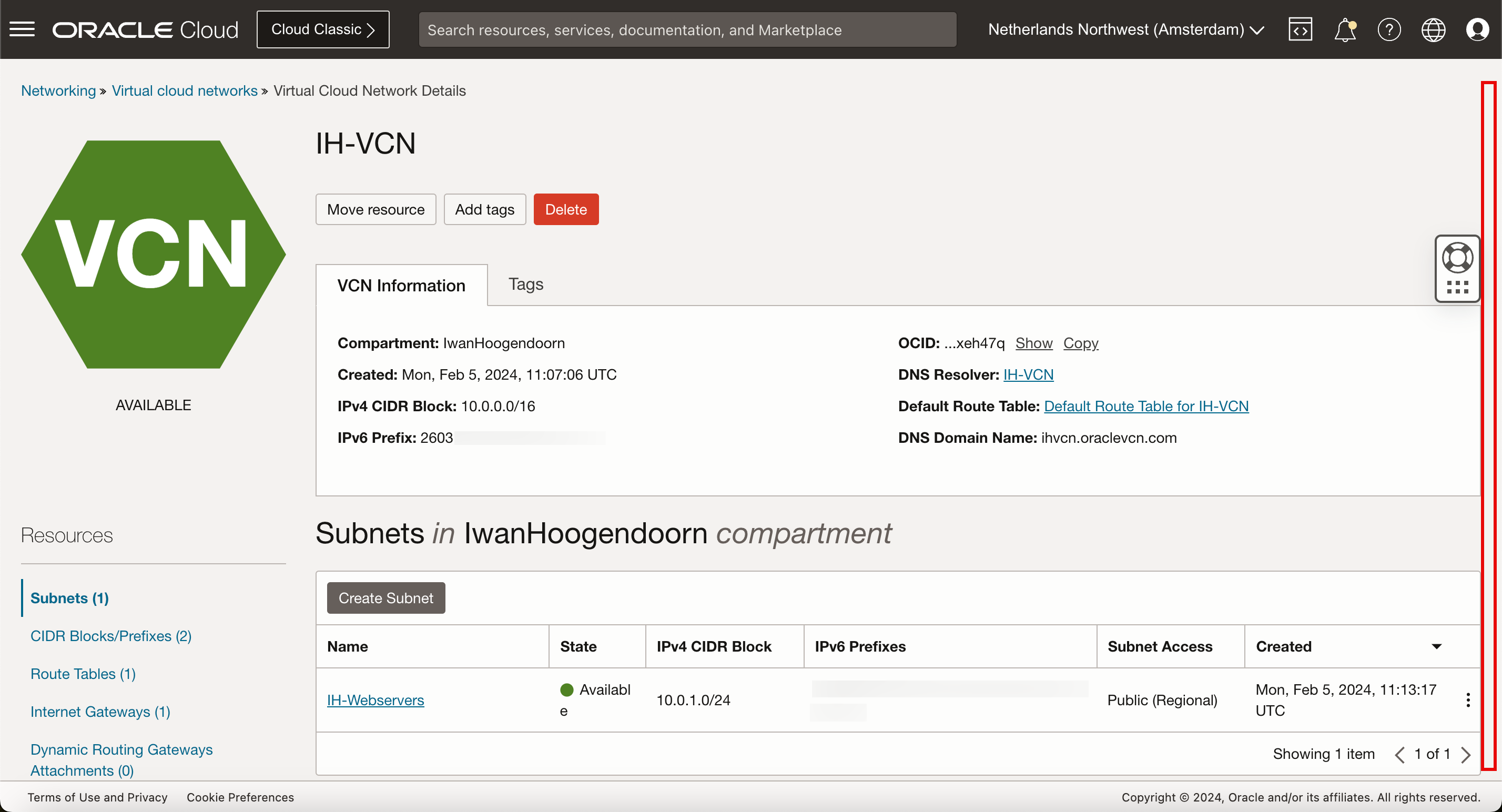
We have now created a new VCN with new IPv4 and IPv6 network spaces that we can use to carve IPv4 and IPv6 subnets.
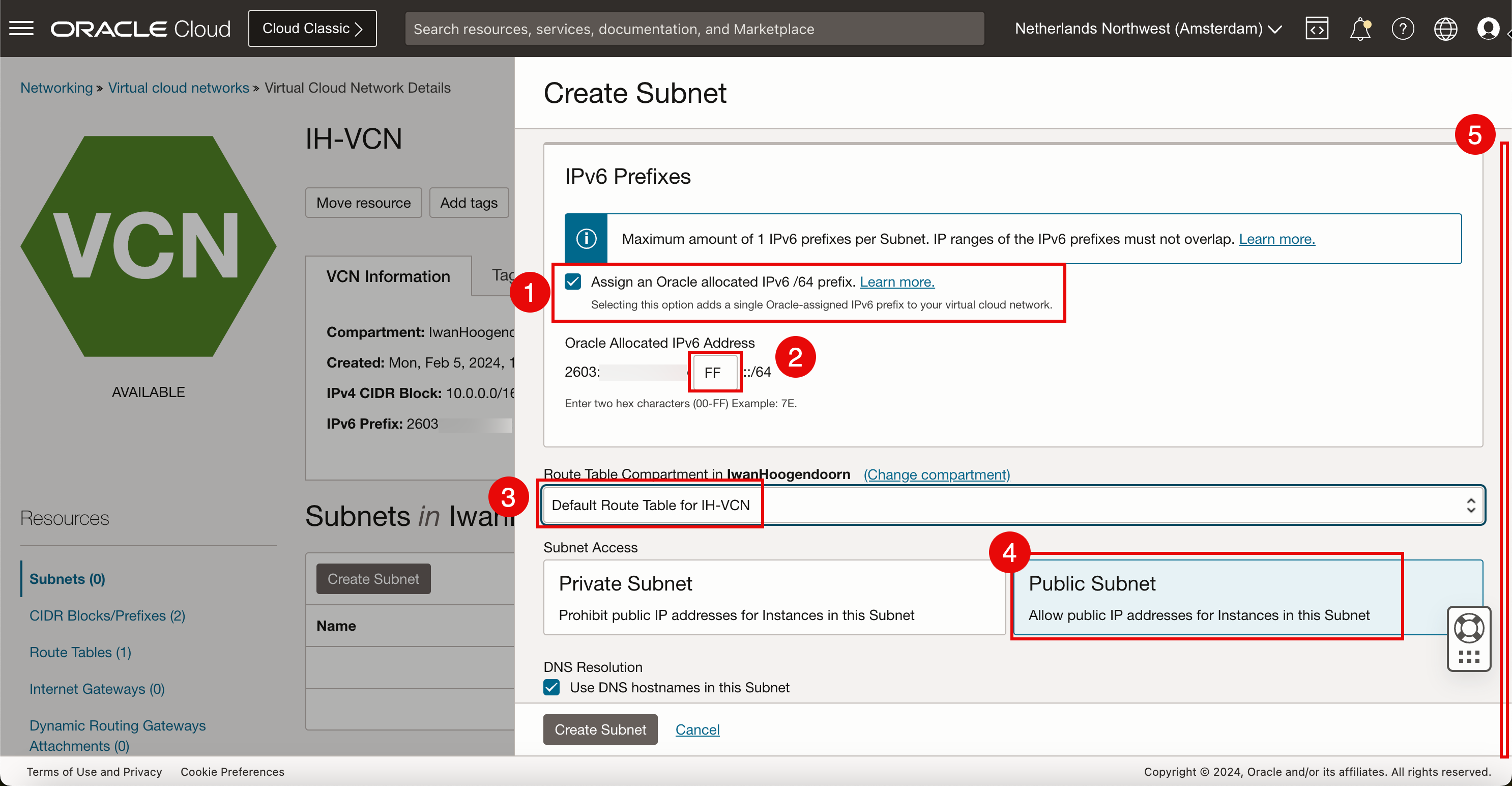
Task 2: Create a New Subnet with IPv6 Enabled
-
Click Create Subnet.
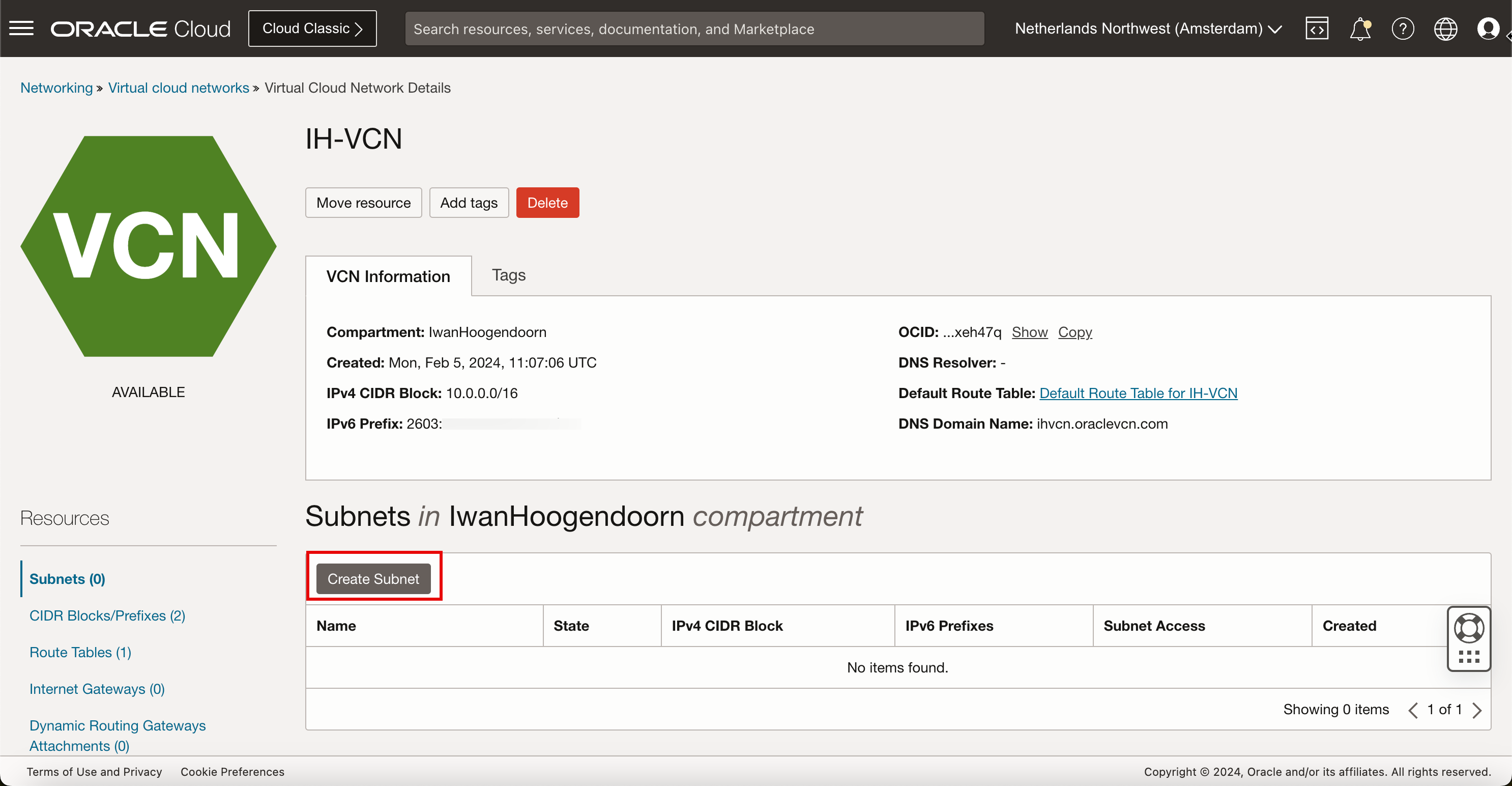
-
In Subnet, enter the following information.
- Enter the Name of the subnet.
- Select the compartment that this subnet needs to be in, if it is not already pre-populated.
- For the Subnet Type, we will select Regional for now.
- Enter the IPv4 subnet that we will carve out of the CIDR block we have assigned in the VCN. Make sure the new /24 CIDR block falls within the /16 that was determined in the VCN.
- Scroll down.
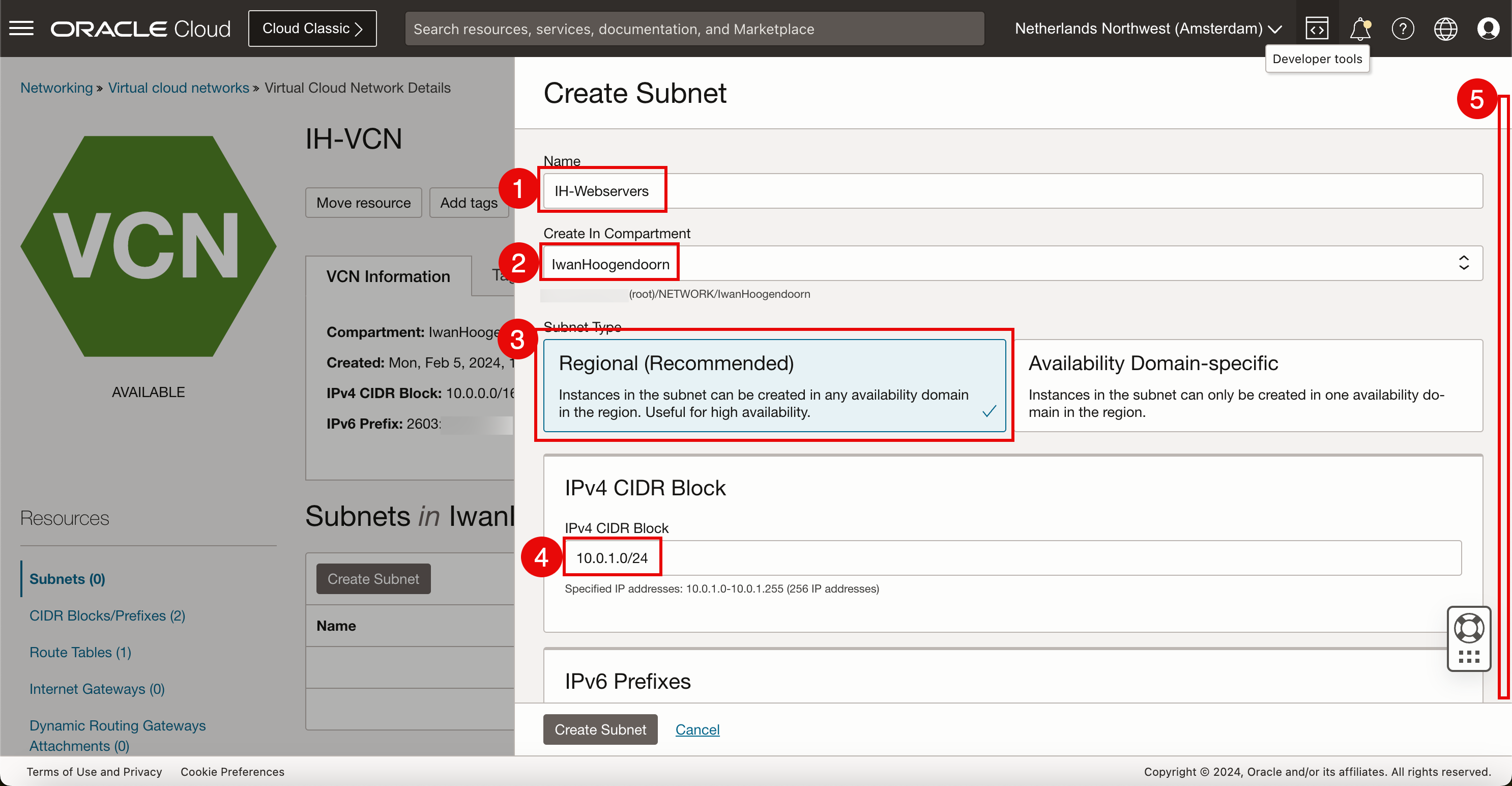
- For IPv6, we will assign an Oracle allocated prefix. Select Assign an Oracle allocated /64 prefix.
- Select a new HEX decimal to complete the Oracle allocated prefix.
- Select the default route table for the VCN.
- Make the subnet public, so that we get public IP addresses as we need this to make webserver accessible from the internet.
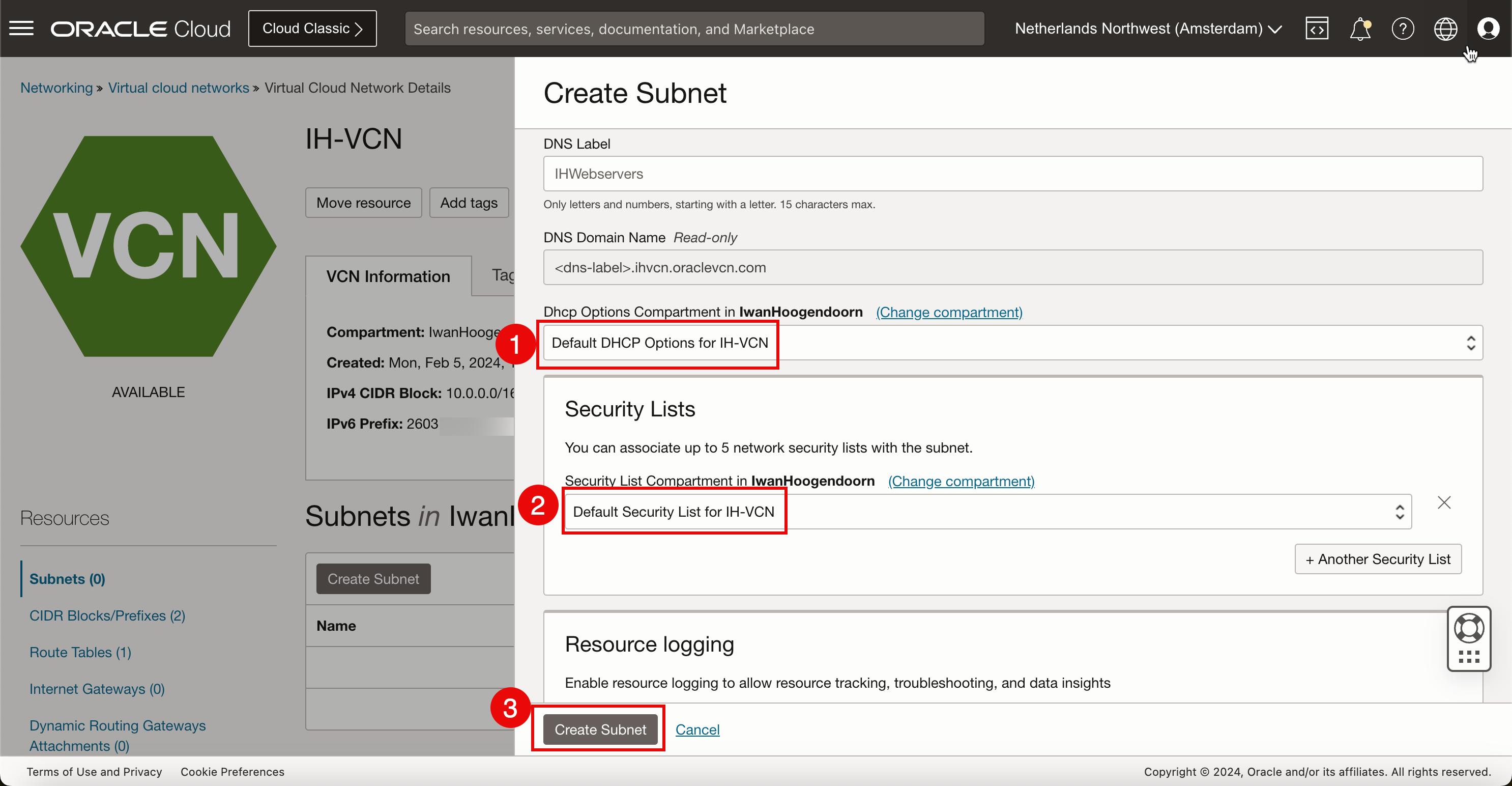
- Scroll down.
- Select the default DHCP for the VCN.
- Select the default security list for the VCN.
- Click Create Subnet.
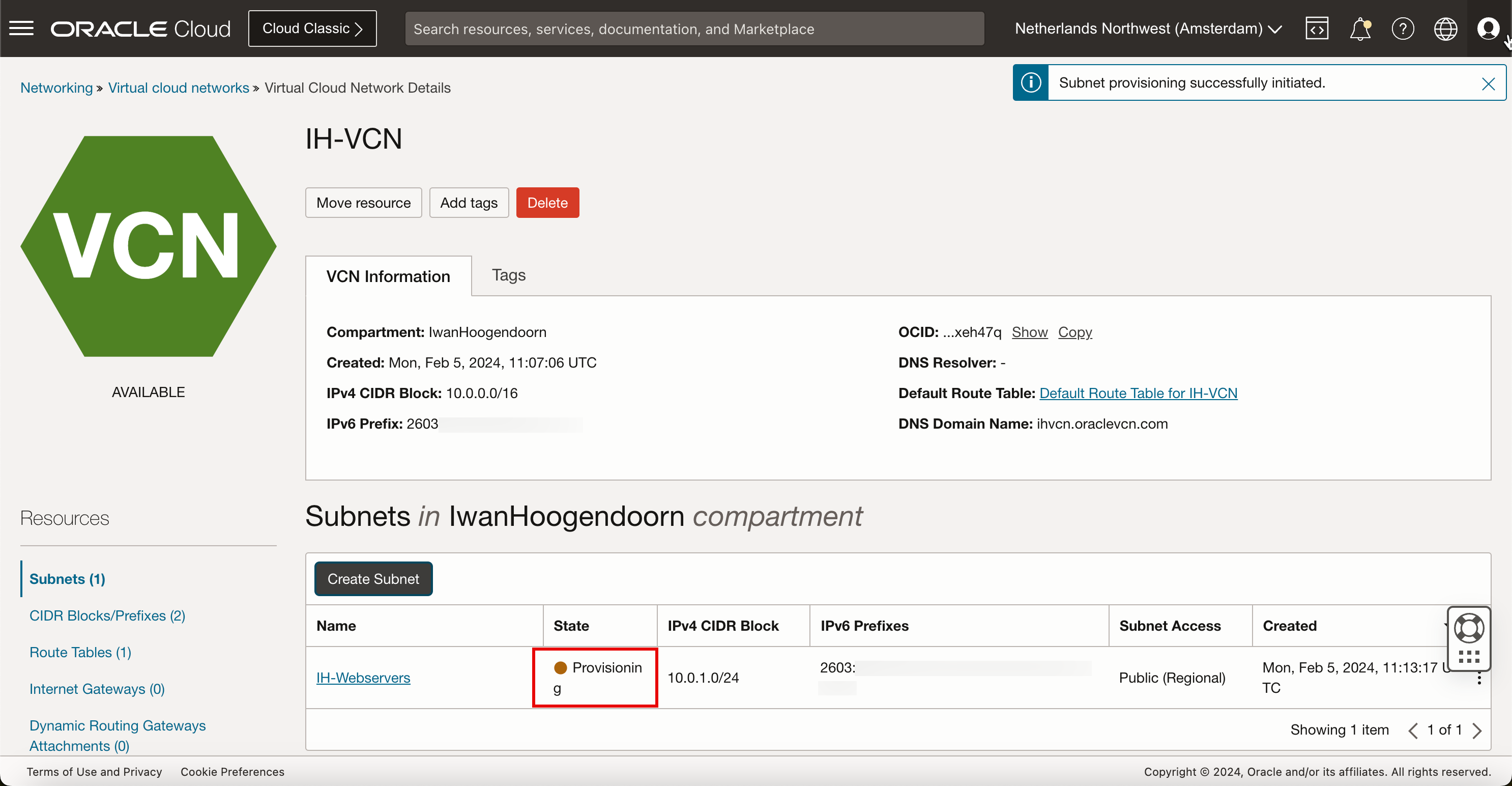
-
Notice that the state of the newly created subnet is Provisioning.
After a few minutes, the state of the new subnet will be Available.
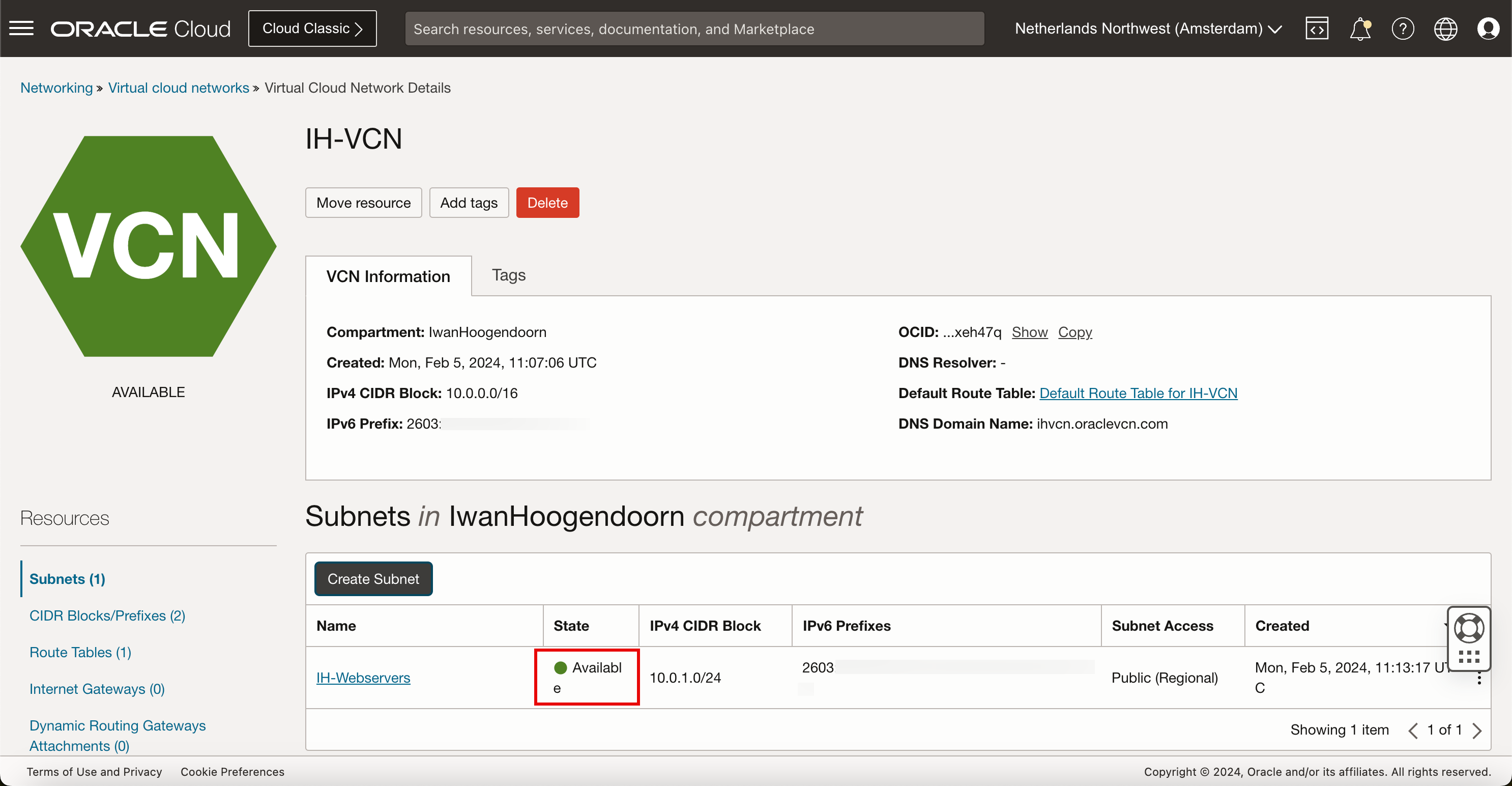
Now the subnet is ready to use for IPv4 and IPv6 addresses.
Task 3: Create a New Instance with IPv6 Enabled
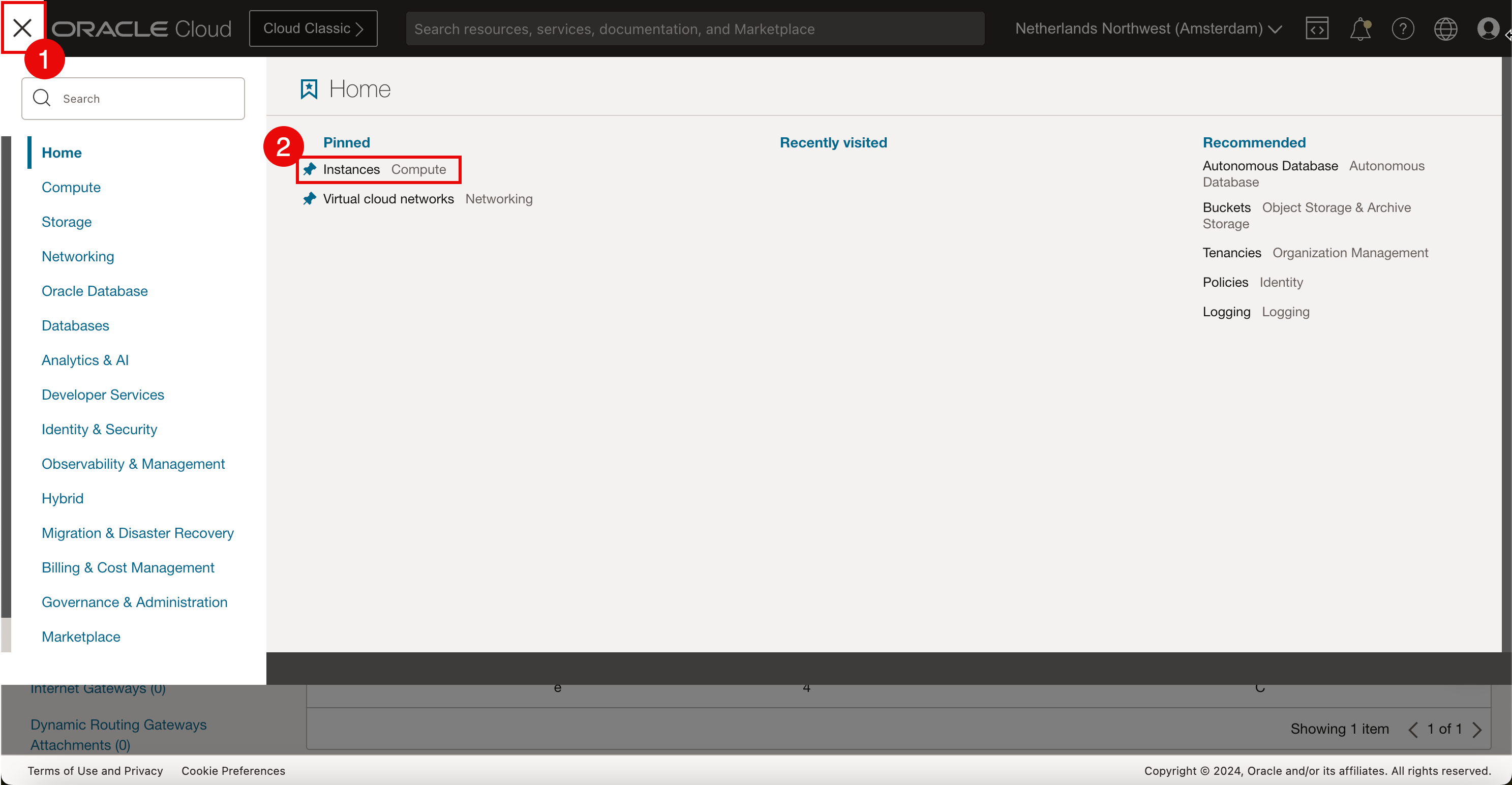
-
Open the OCI Console.
- Click the hamburger menu in the top left corner.
- Click Instances from the pinned section.
-
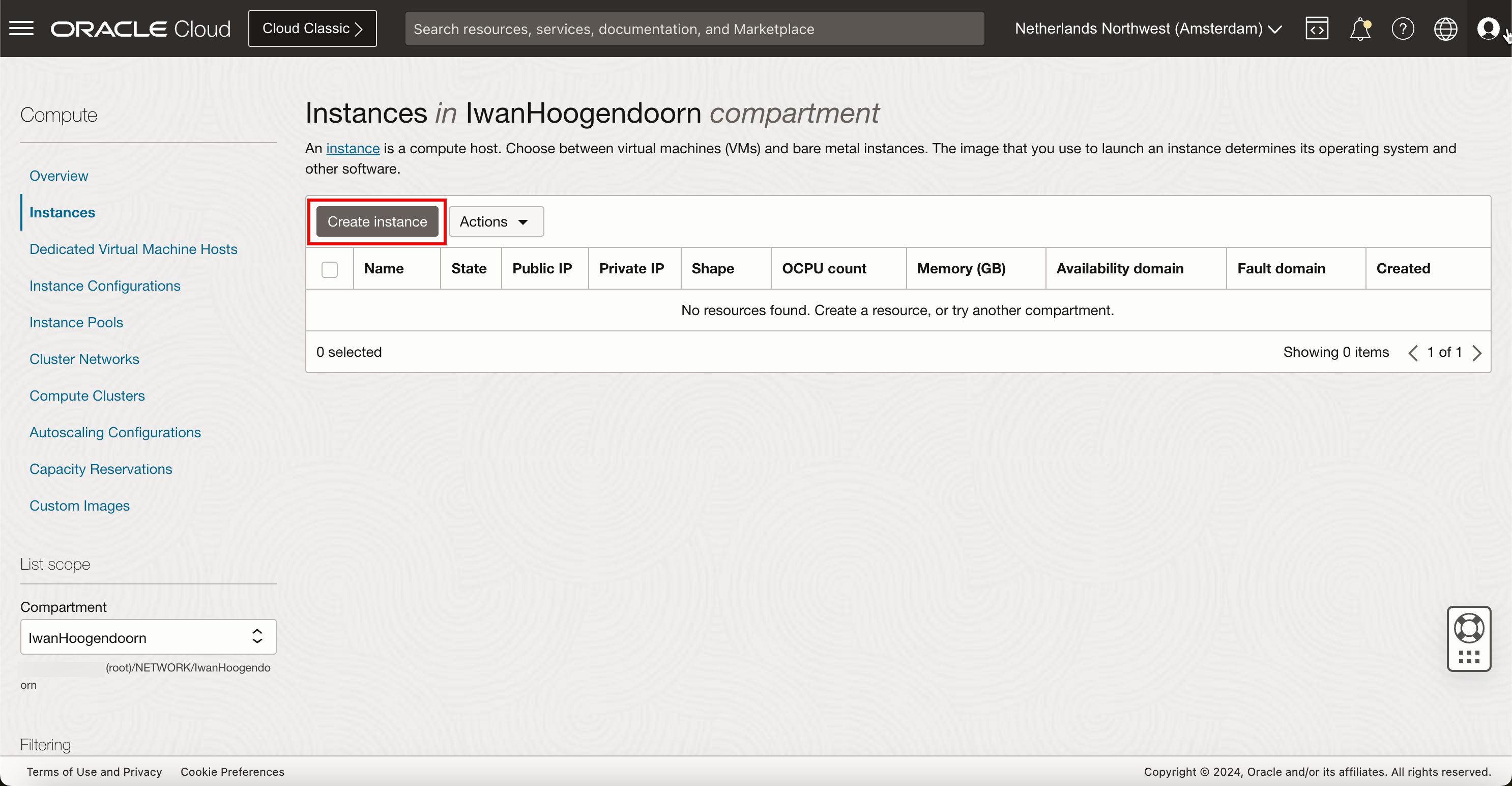
Click Create Instance.
-
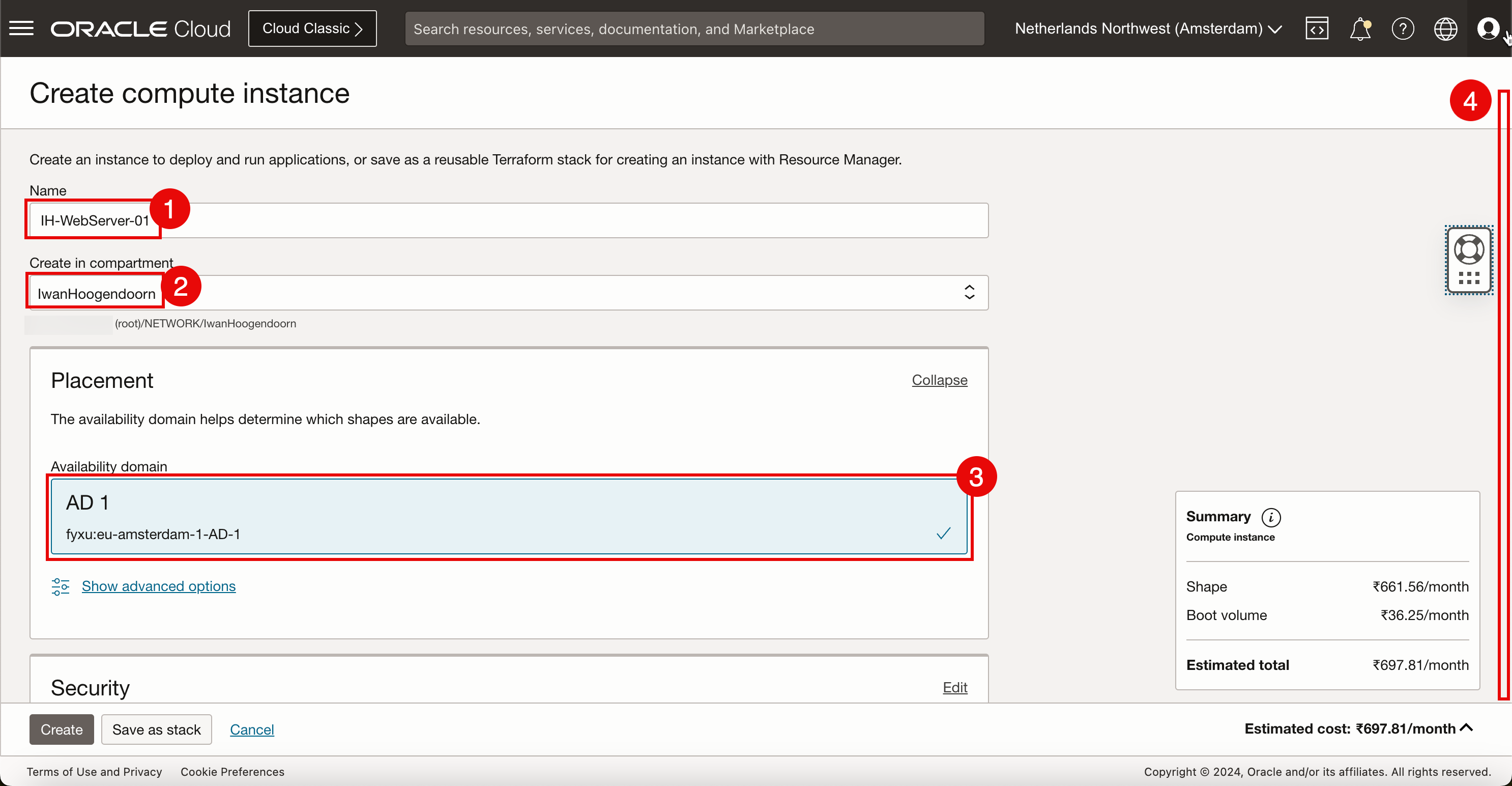
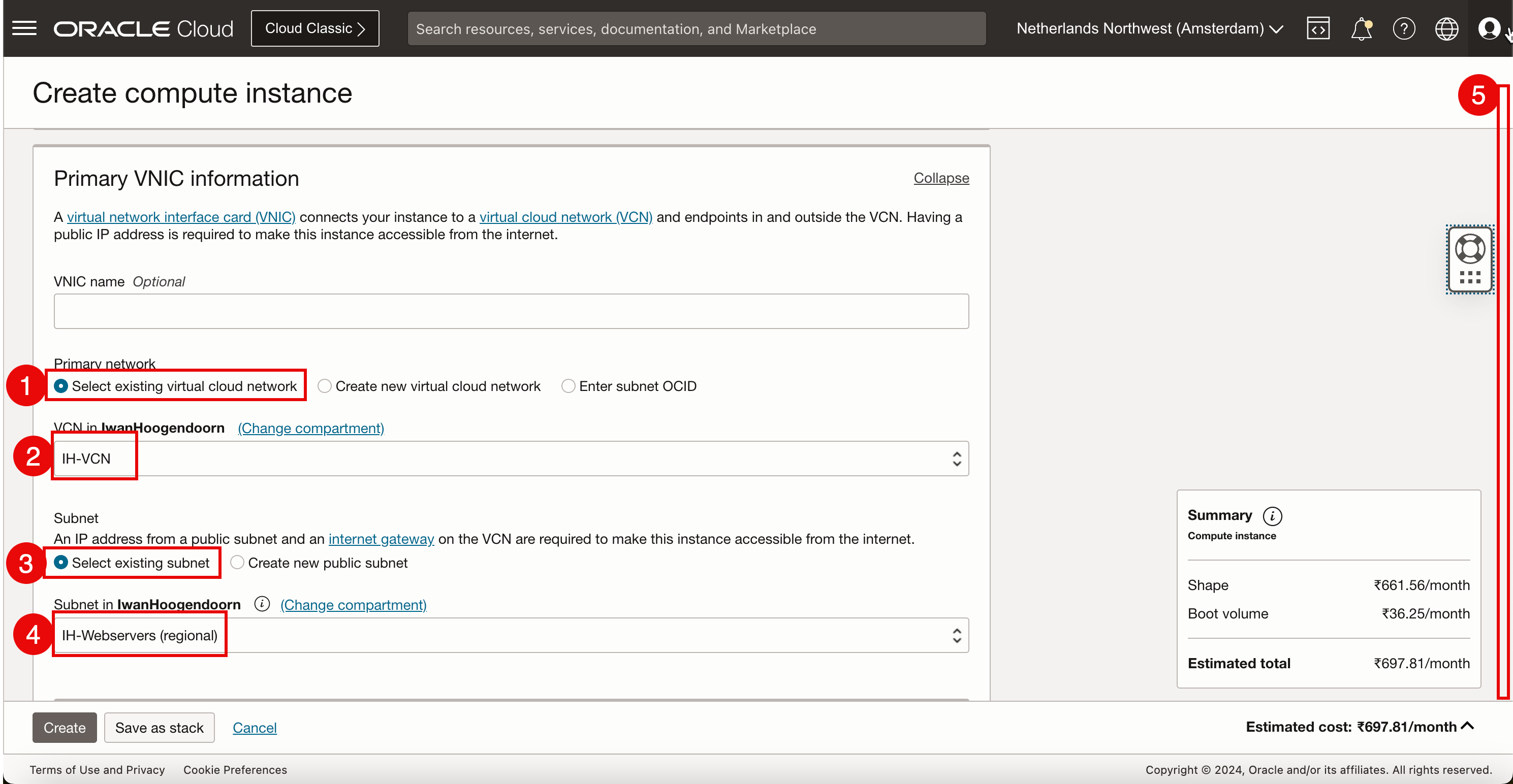
In Create compute instance, enter the following information.
- Enter the Name of the instance.
- Select the compartment where the instance needs to be in.
- Select in which Availability Domain you want to place this instance. For this tutorial, as the Northwest region of The Netherlands, we only have one availability domain.
- Scroll down.
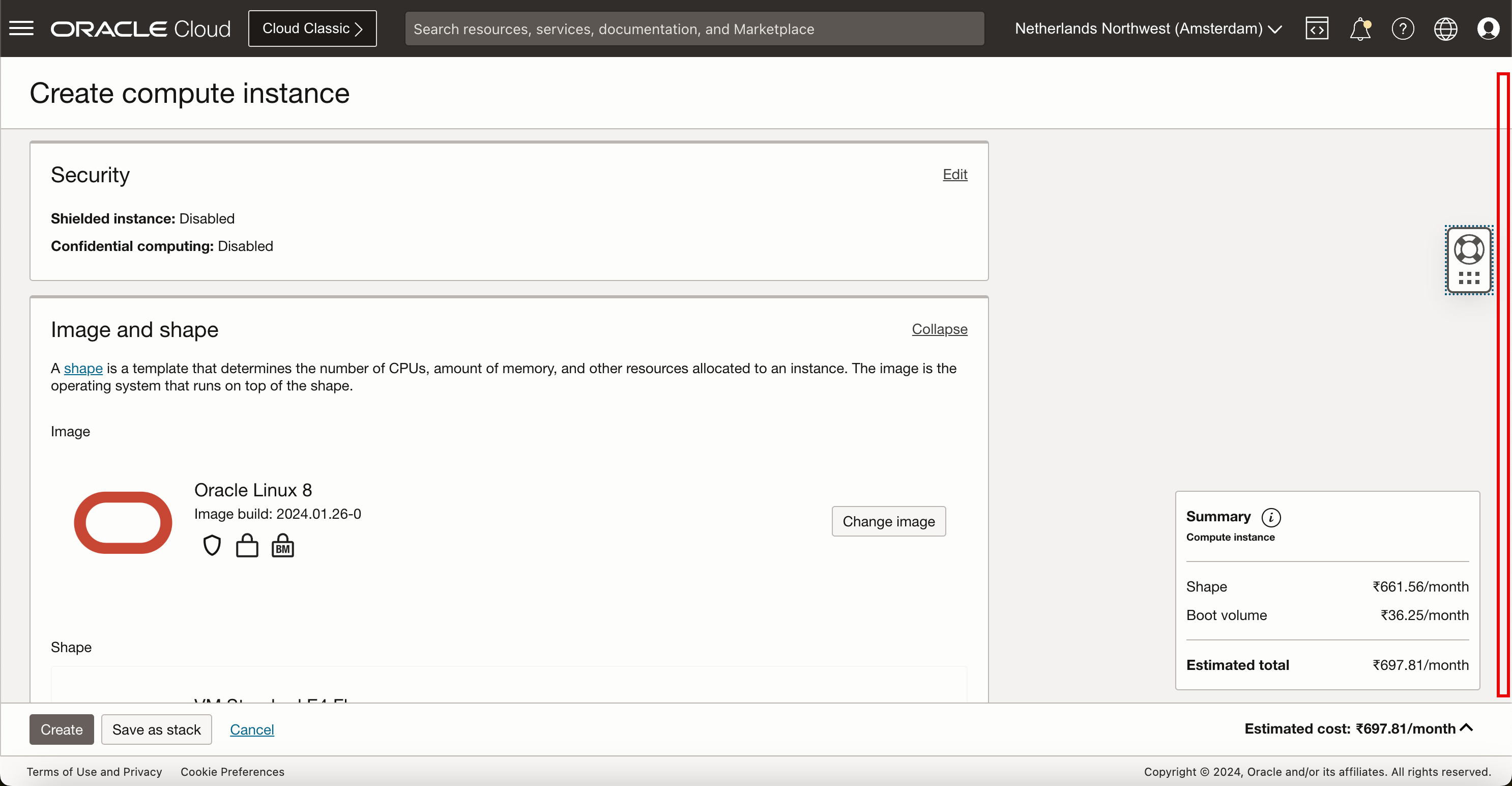
Keep everything default and scroll down.
- In Primary network, select Select existing virtual cloud network.
- Selected the VCN created in Task 1.
- For the subnet, select Select existing subnet.
- Select the subnet created in Task 2.
- Scroll down.
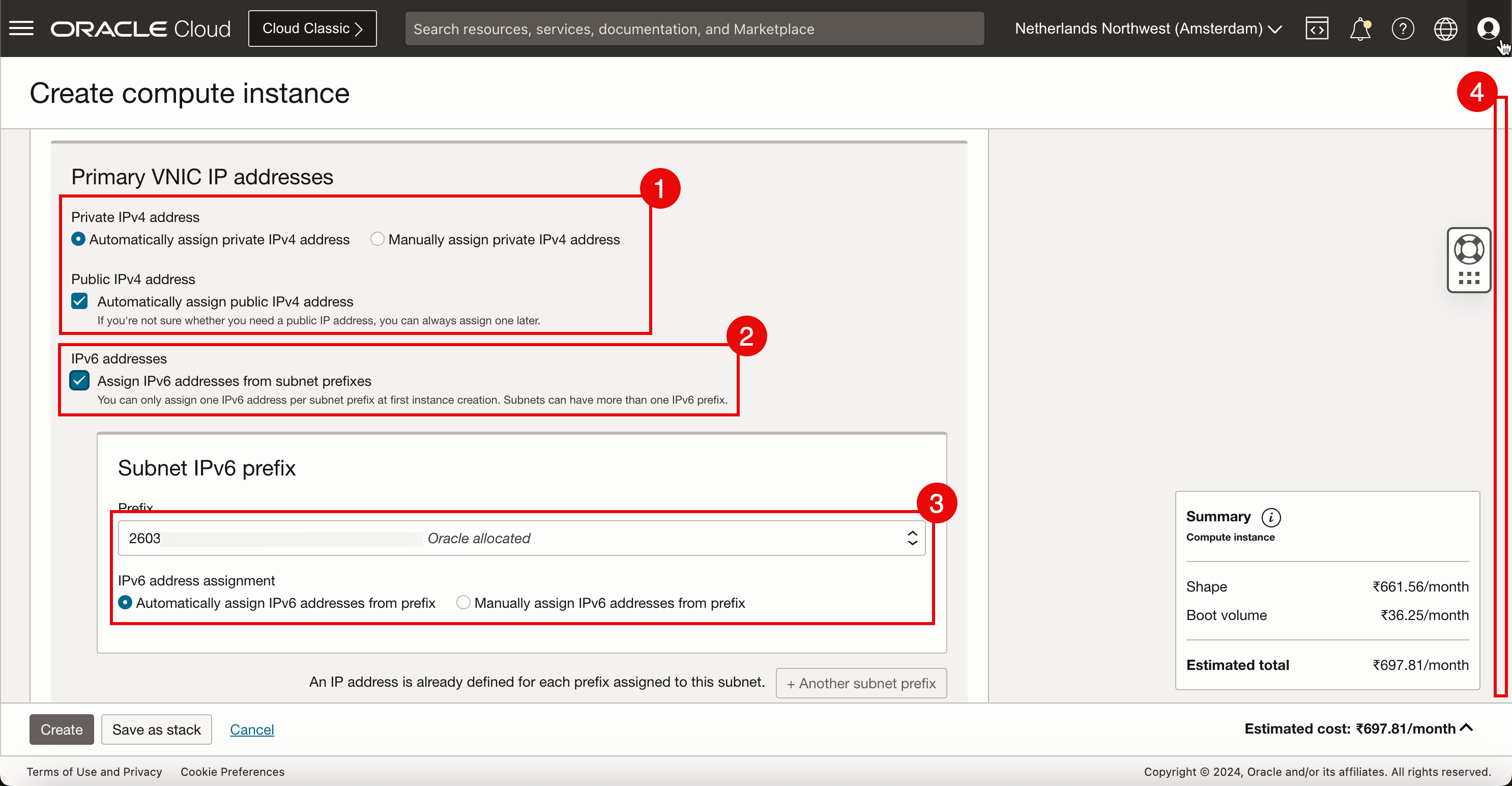
- Private IPv4 address: Select Automatically assign private IPv4 address.
- IPv6 address: Select Assign IPv6 addresses from subnet prefix that was configured during subnet creation in Task 2.
- IPv6 address assignment: Select Automatically assign private IPv6 address from prefix.
- Scroll down.
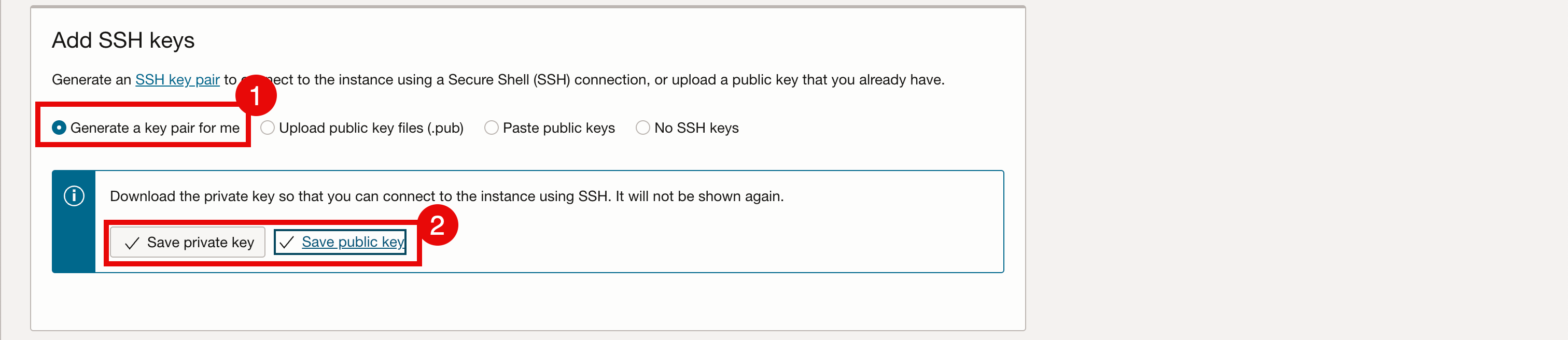
- In order to access and manage this Linux instance we need to work with SSH Keys. For this tutorial, we will let OCI generate a new SSH key pair.
- Download the private and public keys on the local computer so we can use these to access and manage this Linux instance after creation.
-
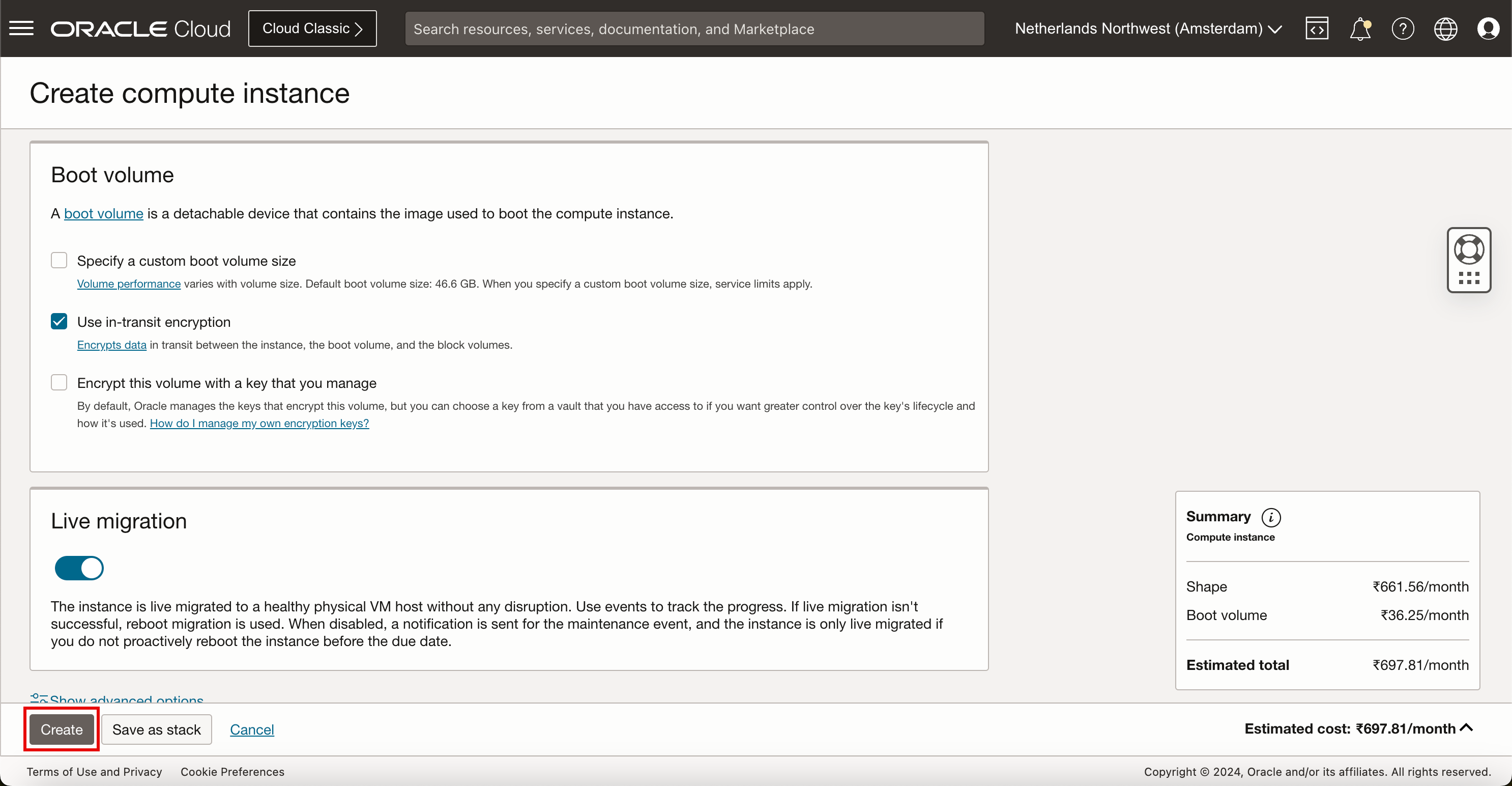
Click Create to create the instance.
- During creation, the state of the instance will be PROVISIONING.
- Notice that there are no IP address details available yet.
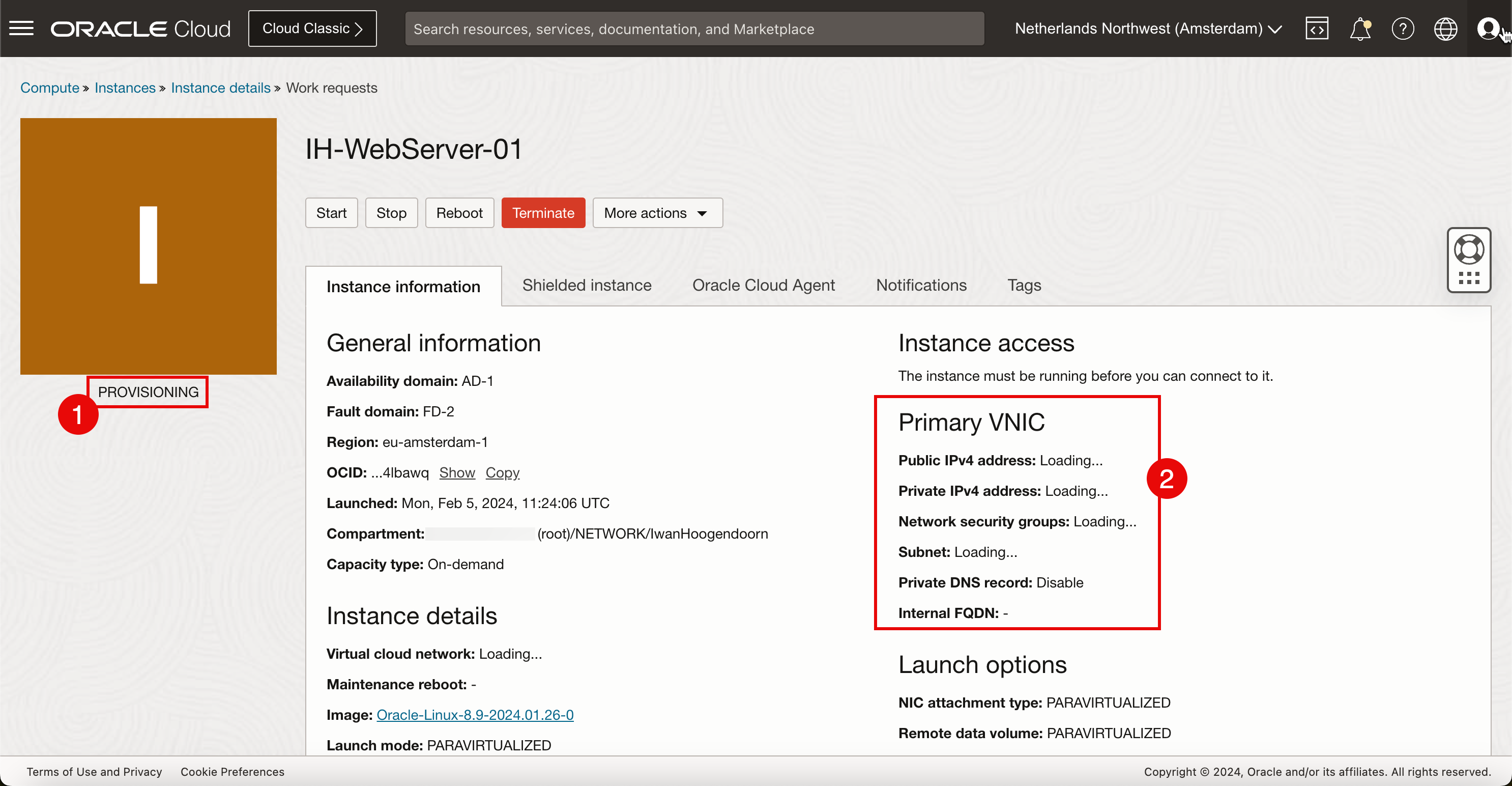
- When the instance is fully created and ready, the state will be set to RUNNING.
- Notice that the IP address details are available now.
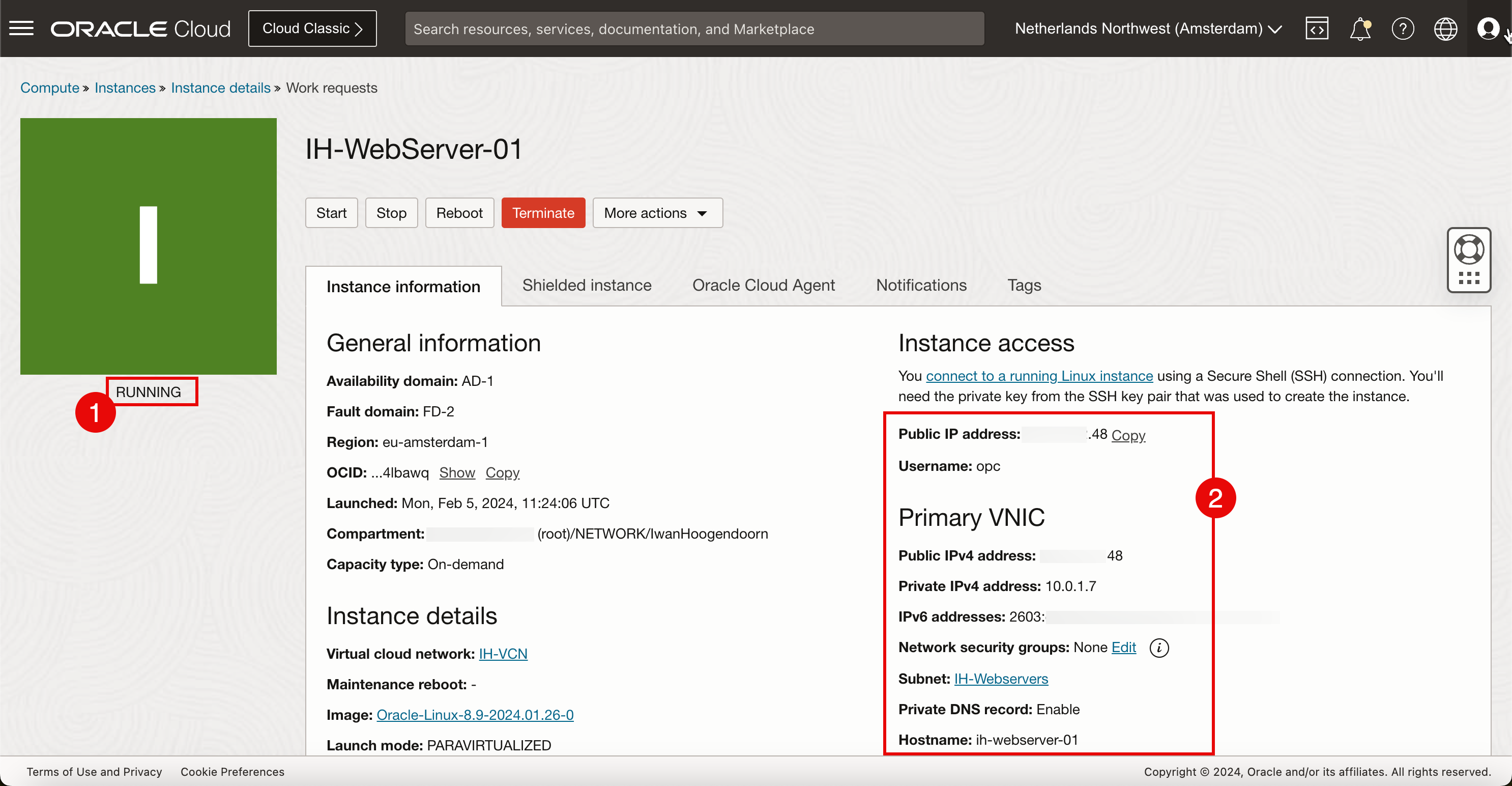
The next logical task will be to access the instance using SSH so we can start installing and configuring the webserver. When we try to connect to the webserver using public IPv4 address and the private key, we are not able to connect because the VCN created in Task 1 has no internet gateway and now we need to create that internet gateway first in the VCN and also configure routing.
Task 4: Create a New Internet Gateway and Configure Routing
To enable access to a new instance (webserver) from the internet, initially using SSH and eventually transitioning to HTTP, we must establish an internet gateway.
-
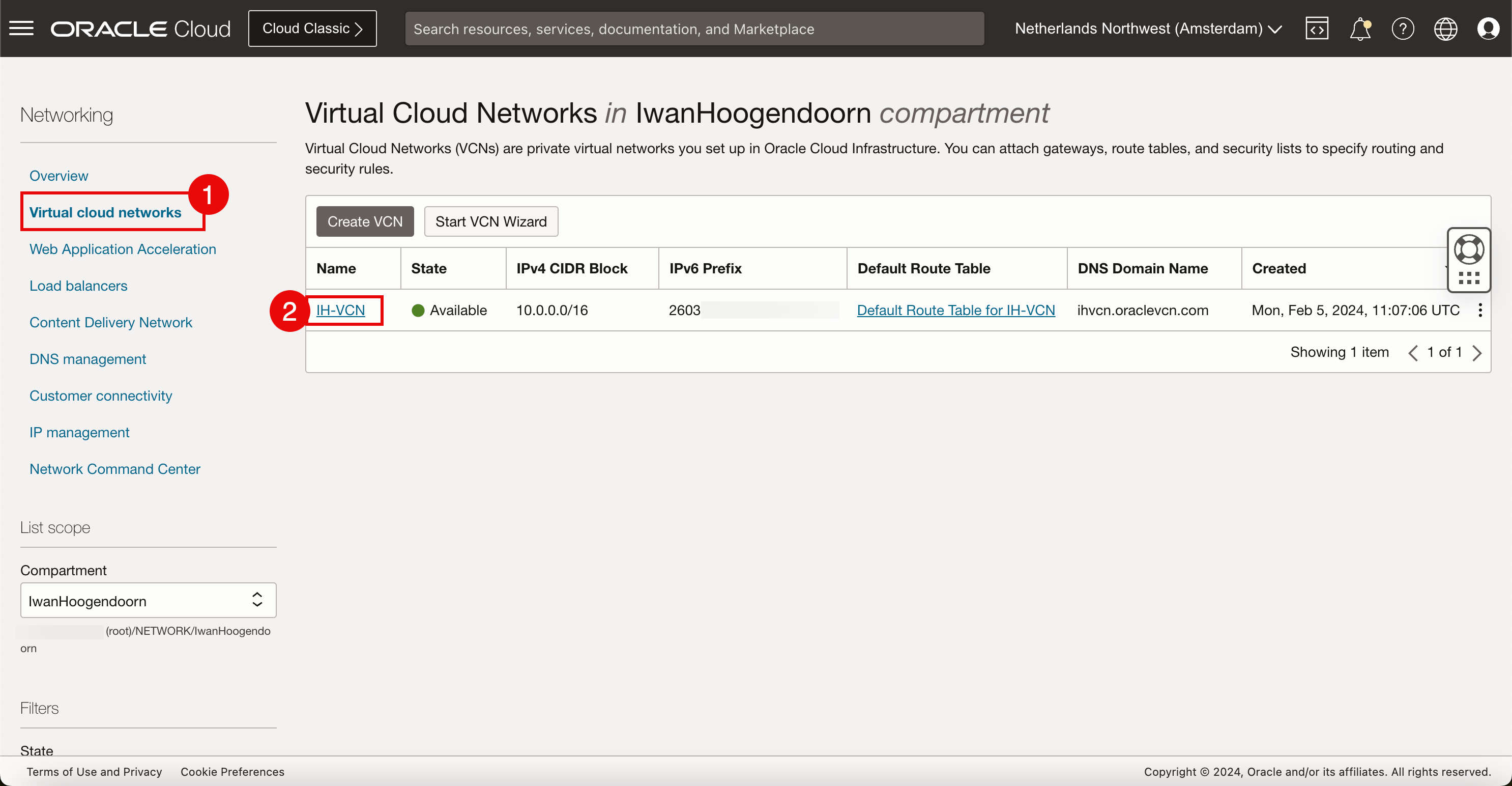
Open the OCI Console.
- Go to Virtual Cloud Networks.
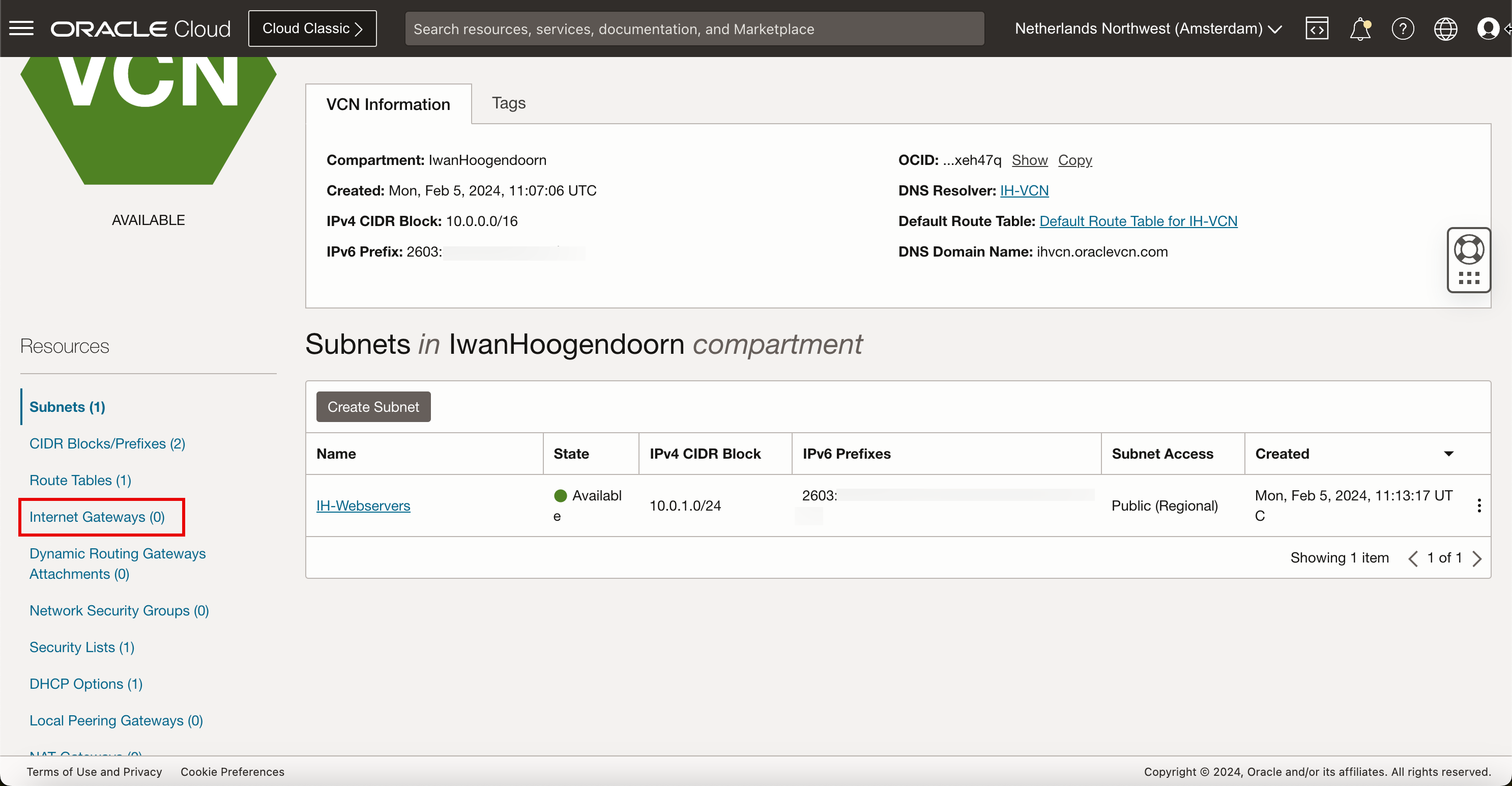
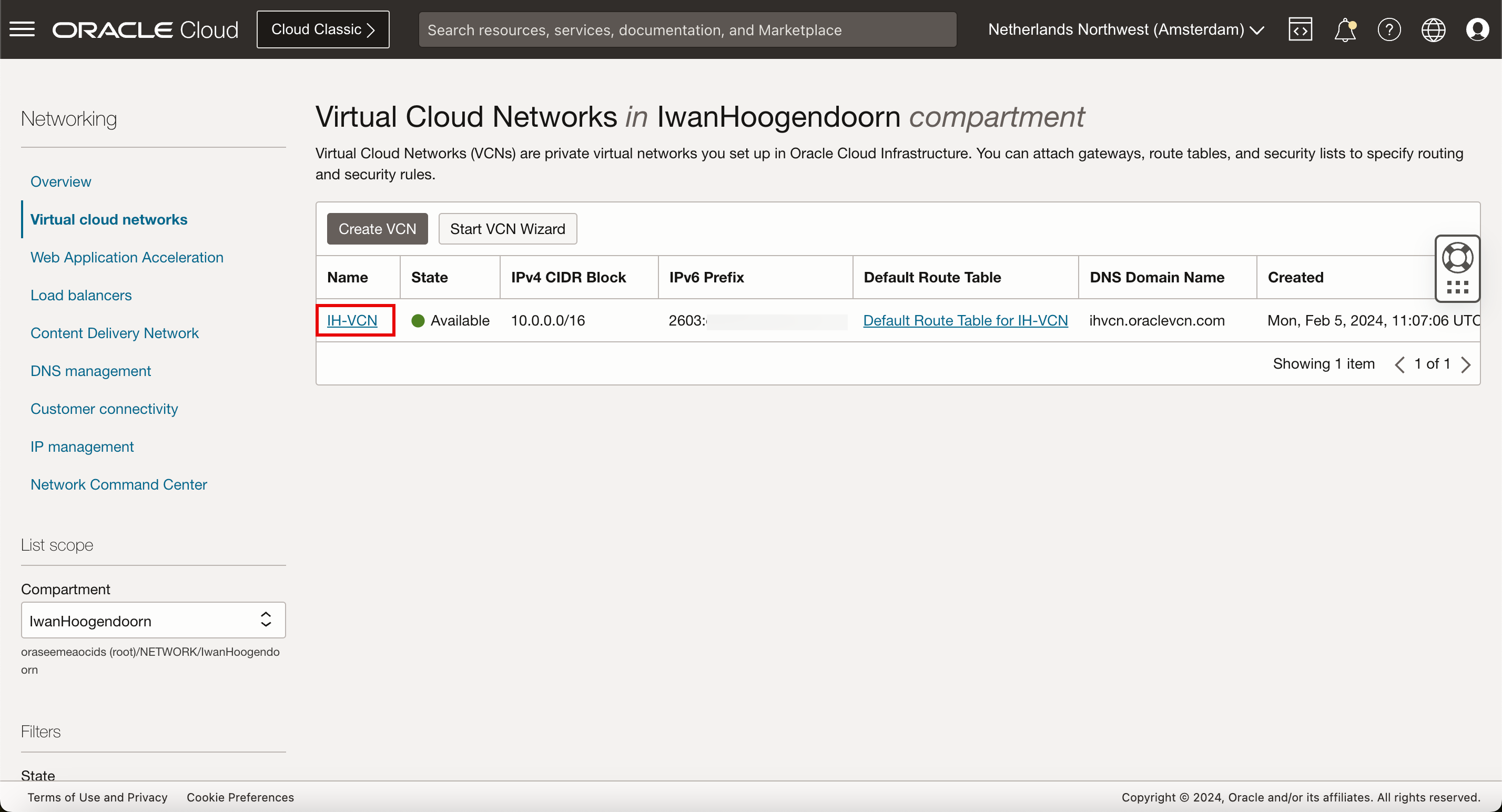
- Select the VCN created in Task 1.
-
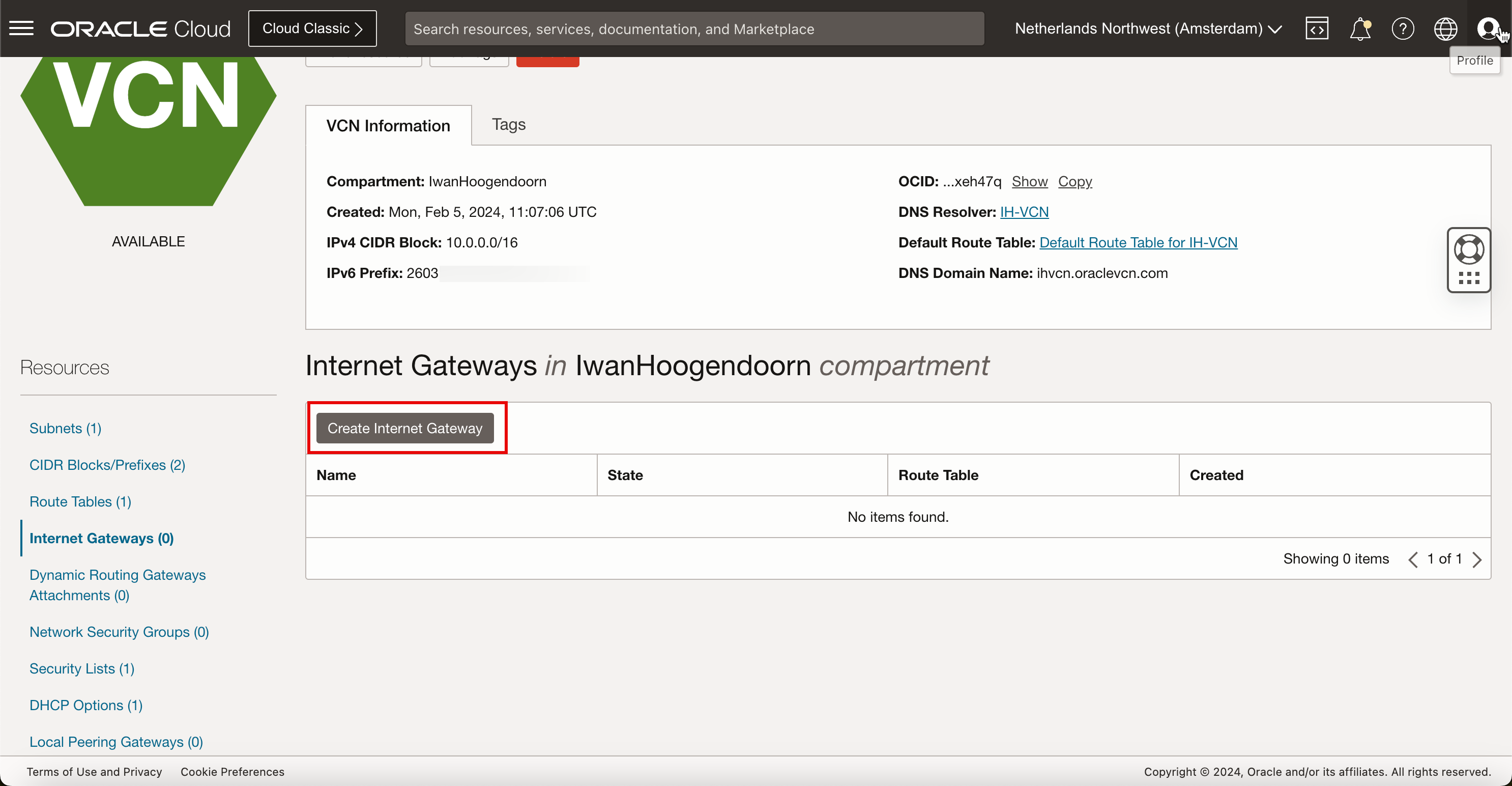
In the VCN details page, click Internet Gateways.
-
Click Create Internet Gateway.
-
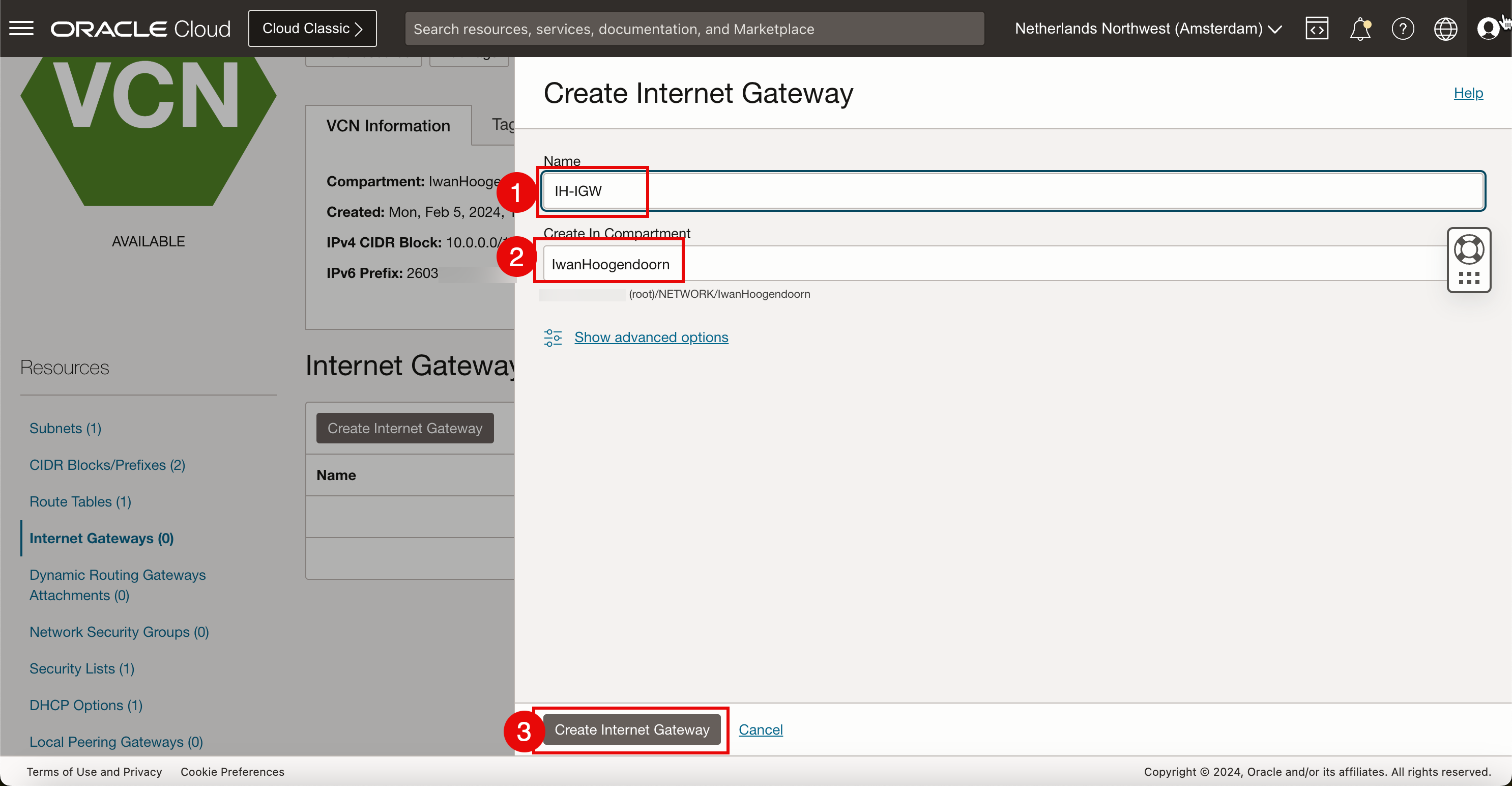
In Create Internet Gateway, enter the following information.
- Enter the name.
- Select the compartment.
- Click Create Internet Gateway.
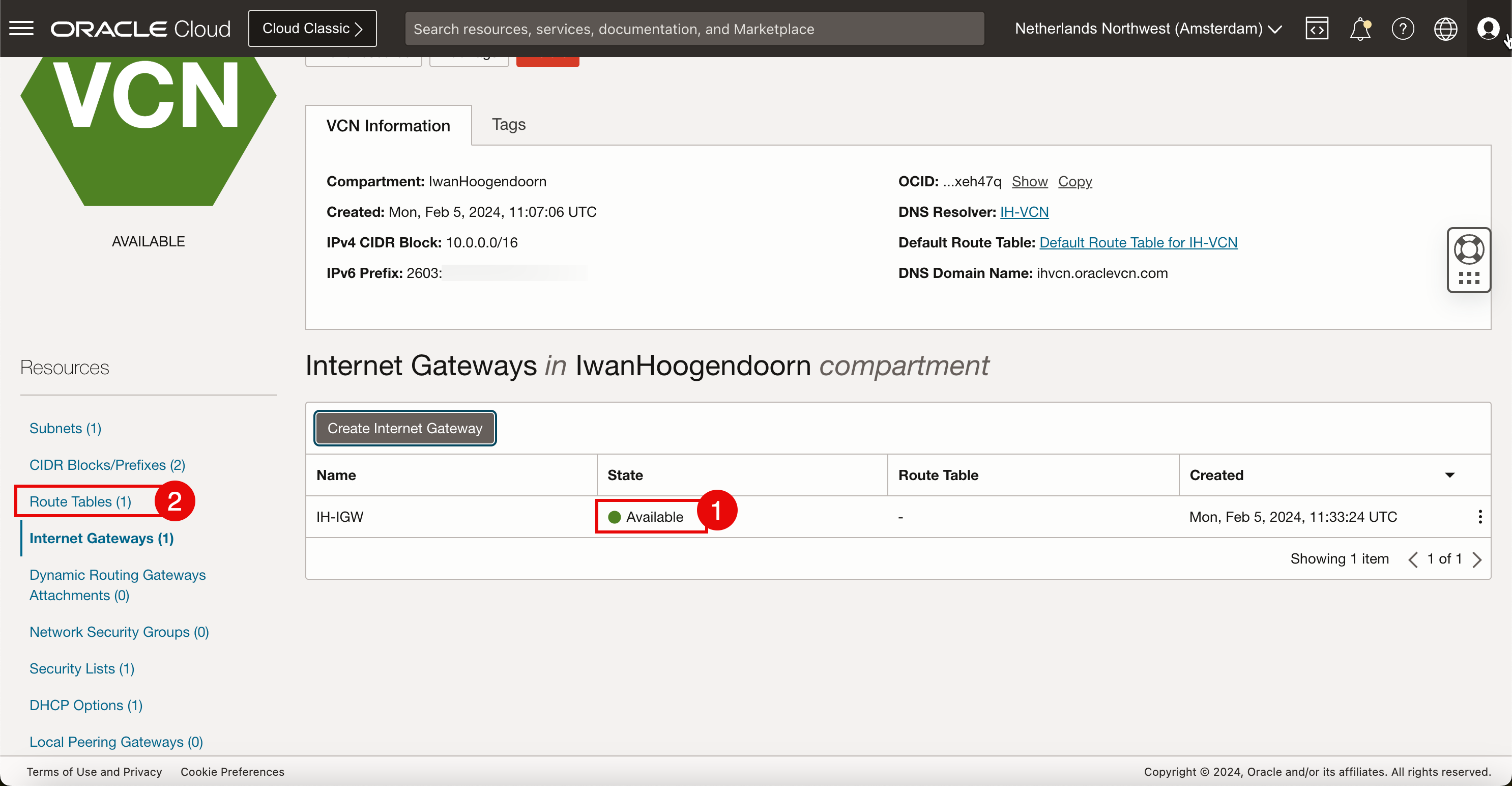
-
Add a route rule.
- Notice that the internet gateway is Available.
- Click Route Tables.
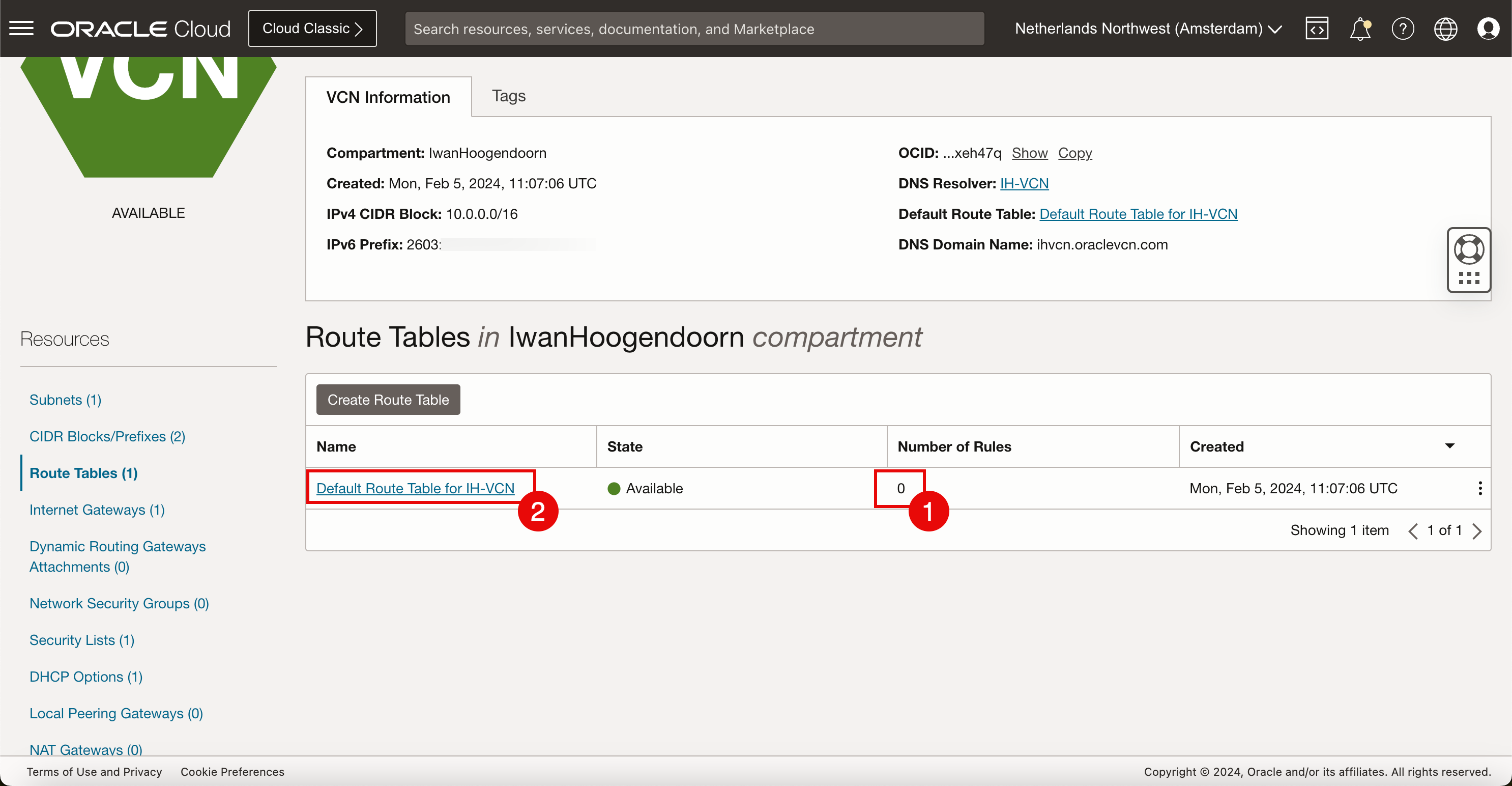
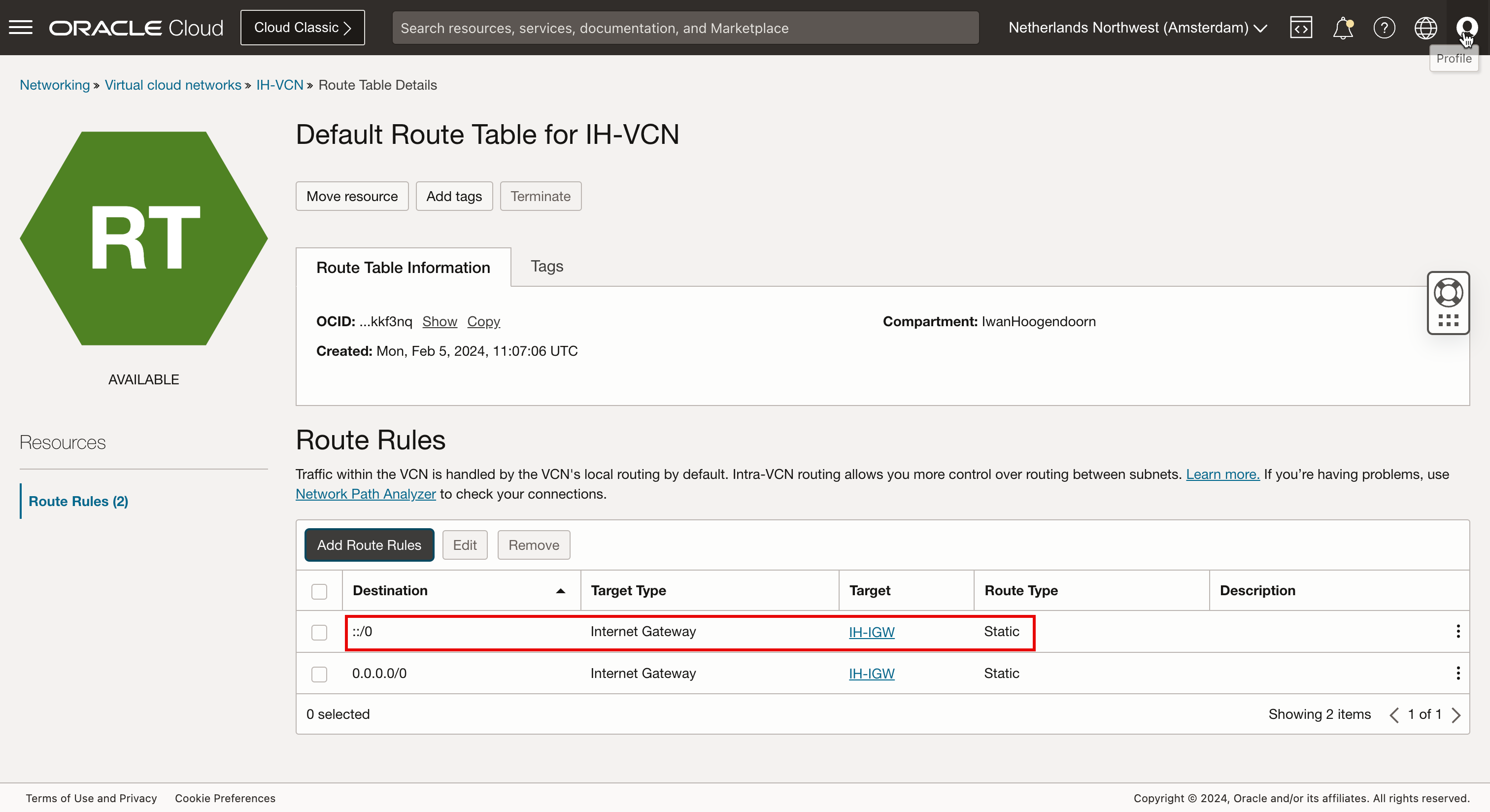
- Notice that the Default Route Table has a
0in the number of rules. - Click Default Route Table.
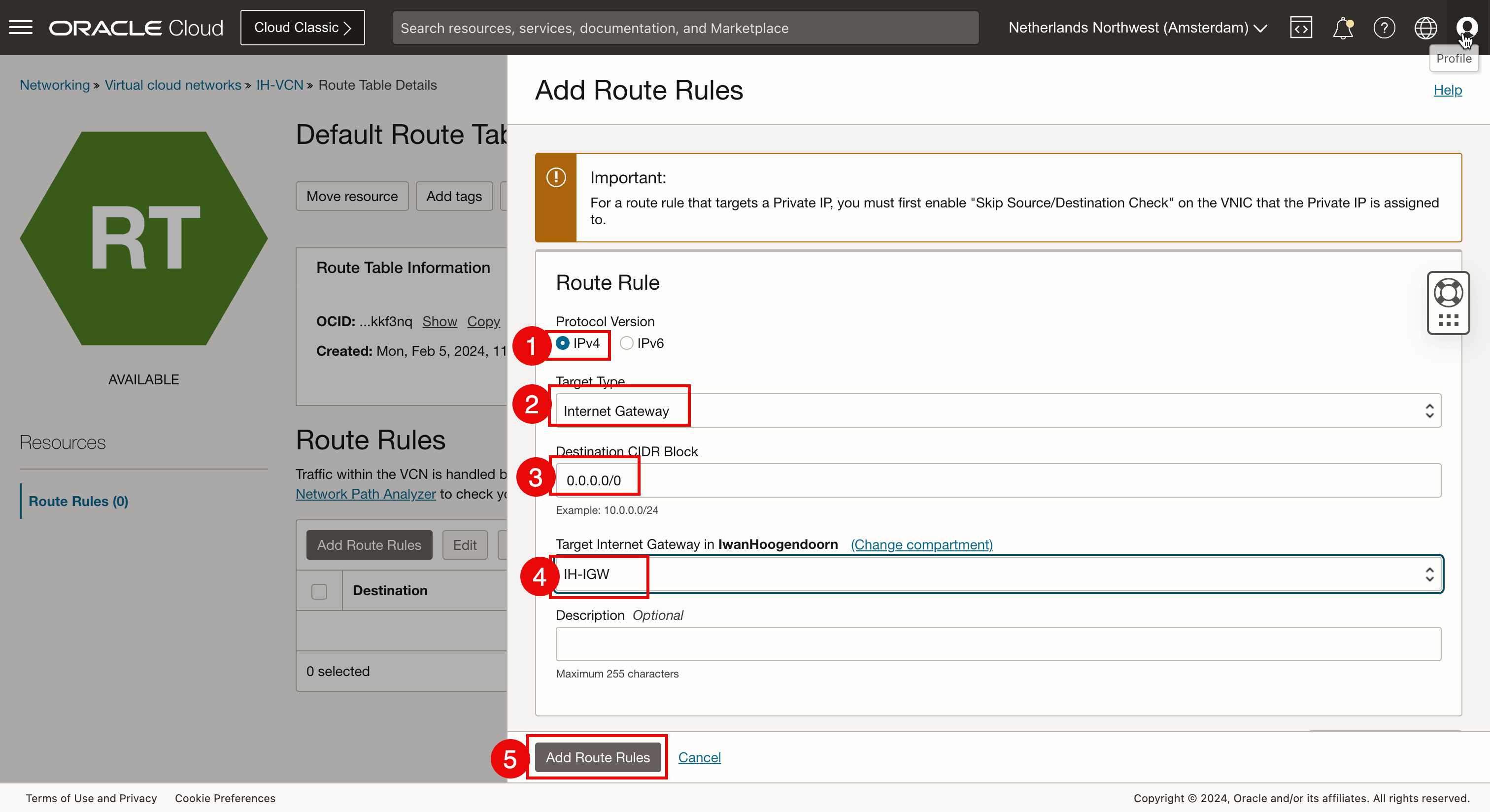
- Protocol Version: Select IPv4.
- Target Type: Select Internet Gateway.
- Destination CIDR Block: For this tutorial, select
0.0.0.0/0as we want all default IPv4 network traffic to go to the internet gateway. - Select the Target Internet Gateway created above in this task.
- Click Add Route Rules.
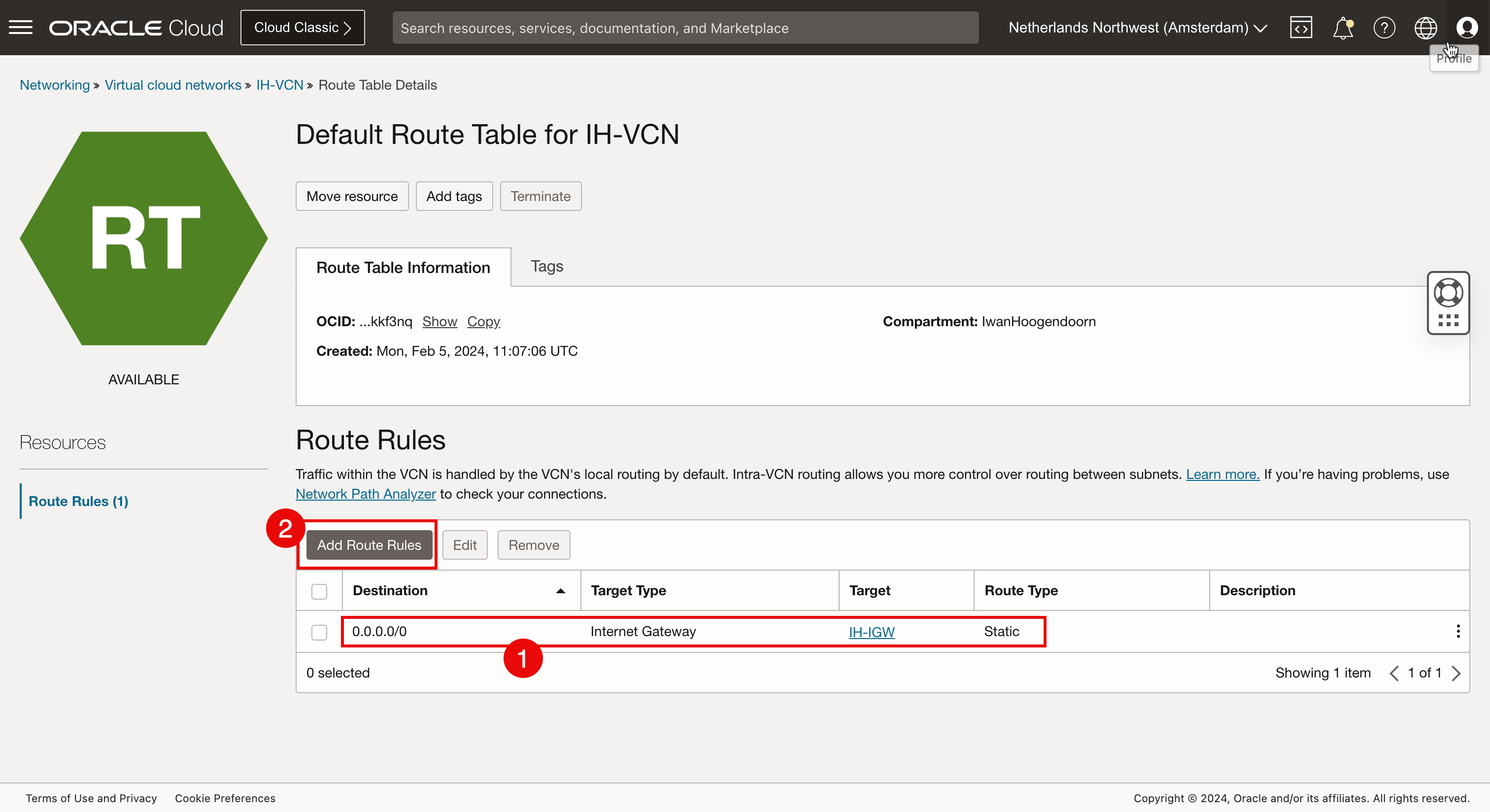
- Notice that the new IPv4 default route rule has been created.
- To route IPv6 internet traffic, we also need to create a new IPv6 default internet rule. Click Add Route Rules again.
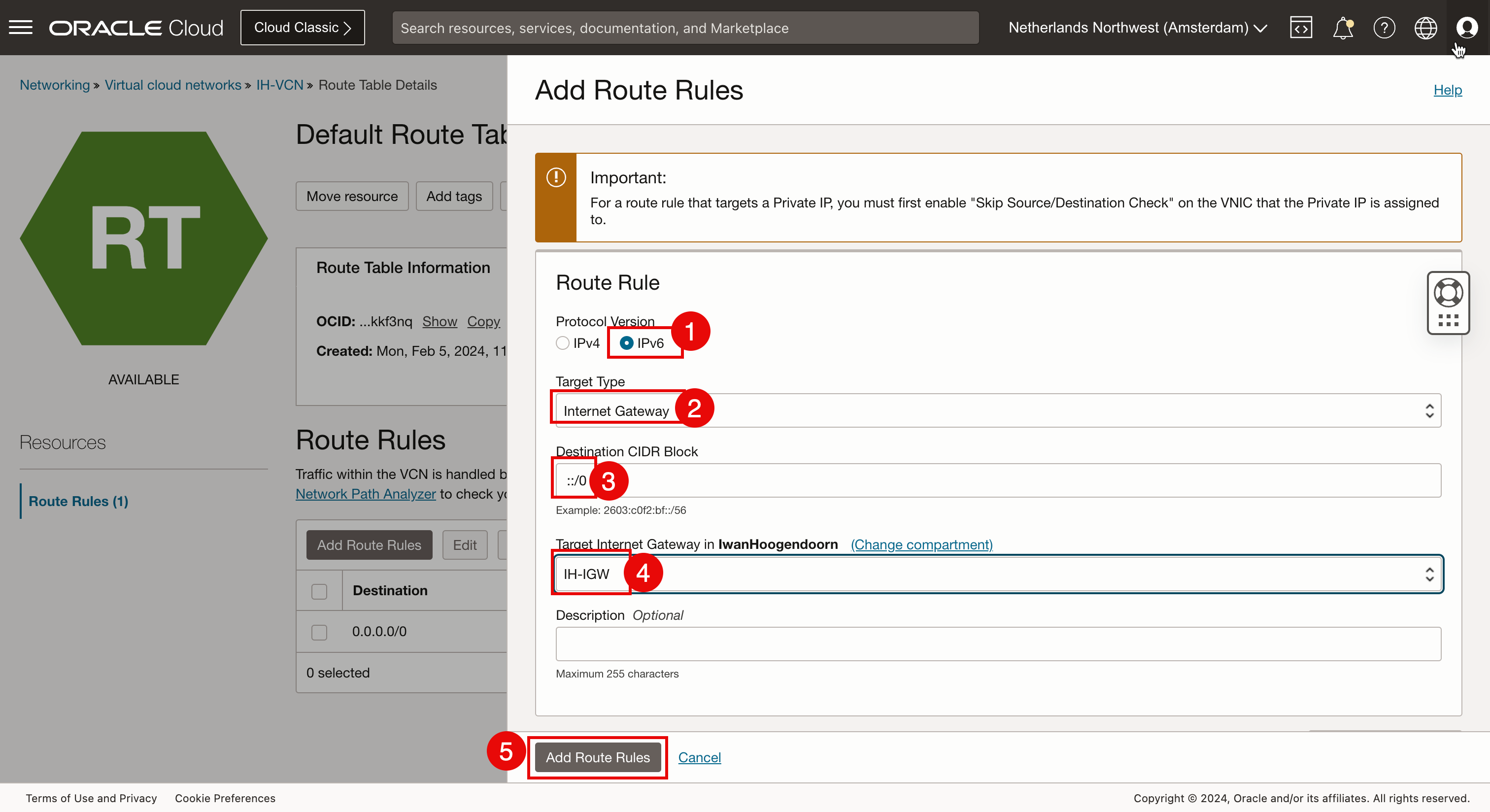
- Protocol Version: Select IPv6.
- Target Type: Select Internet Gateway.
- Destination CIDR Block: For this tutorial, select
:/0as we want all default IPv6 network traffic to go to the internet gateway. - Select the Target Internet Gateway created above in this task.
- Click Add Route Rules.
-
Notice that the new IPv6 default route rule has been created.
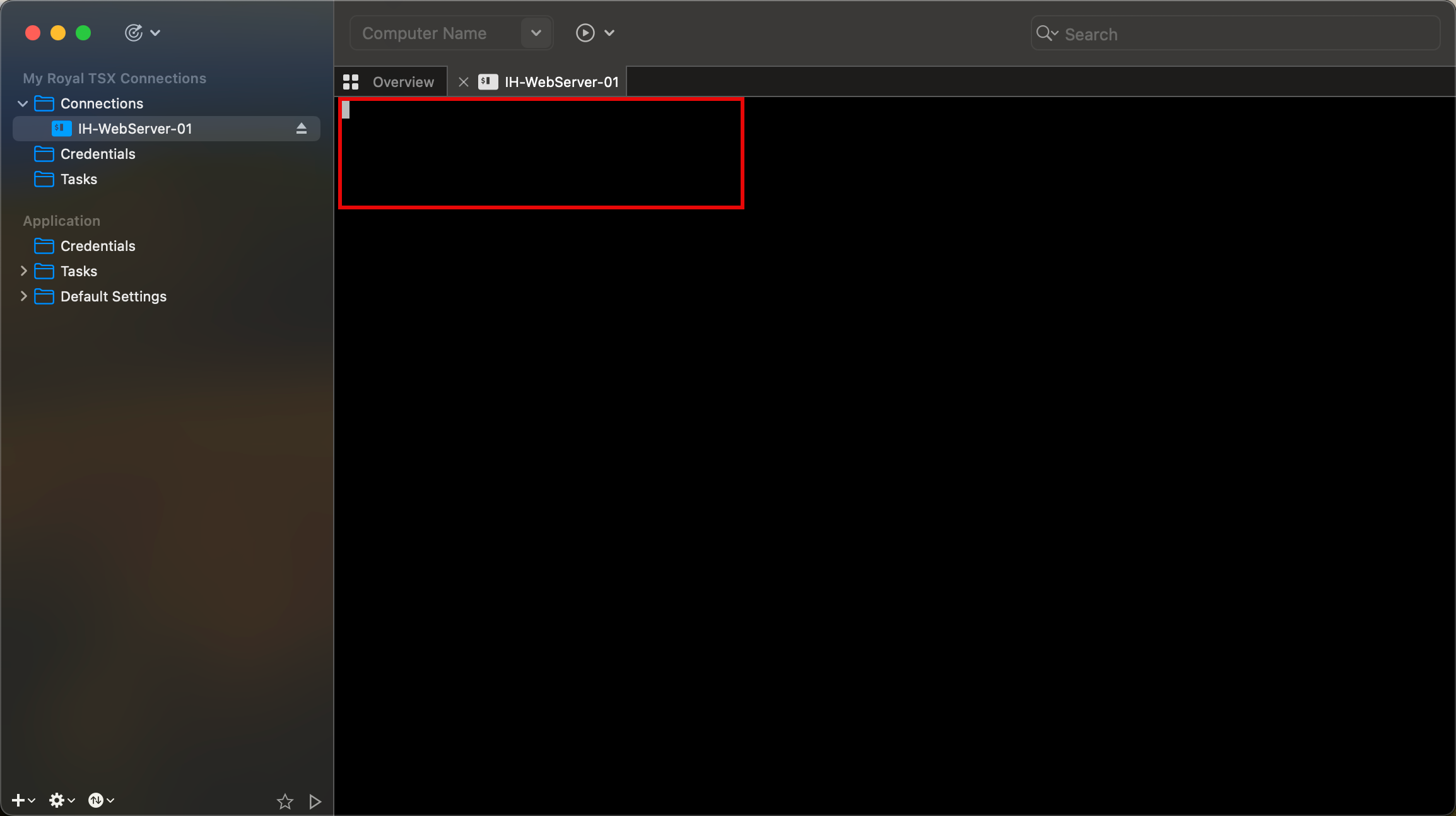
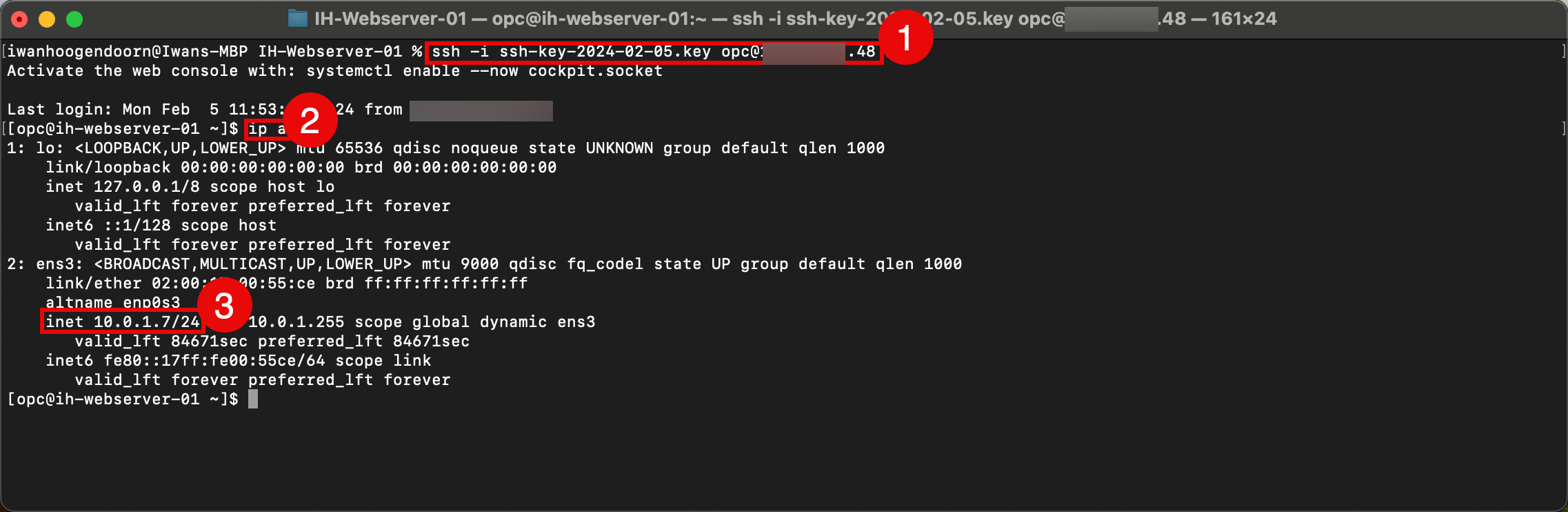
- We connect to the newly created instance through SSH using the private key.
- After the connection has been established successfully, run
ip acommand to verify IP addresses. - Notice that the private IPv4 address is the same as provided for the instance details.
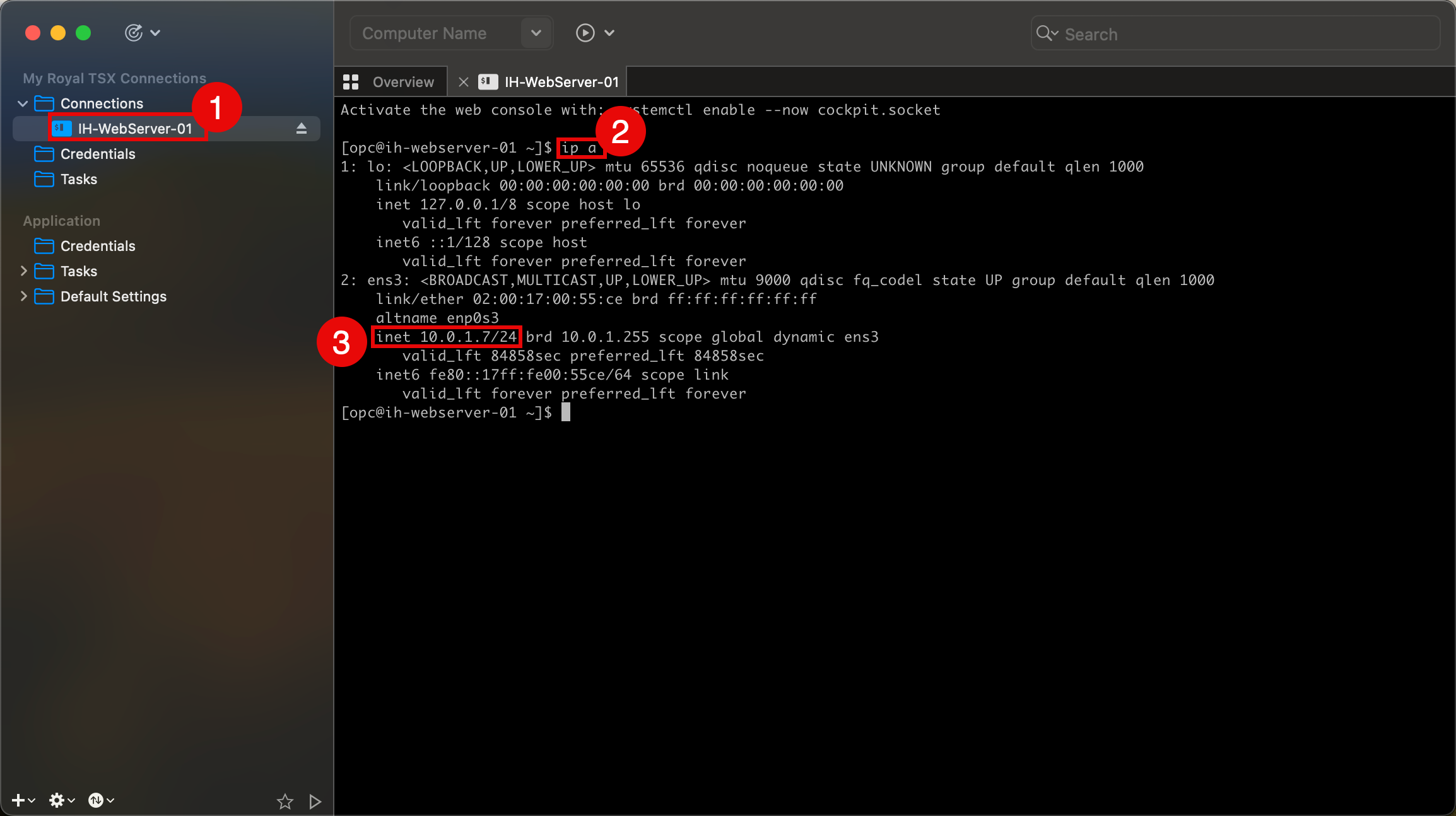
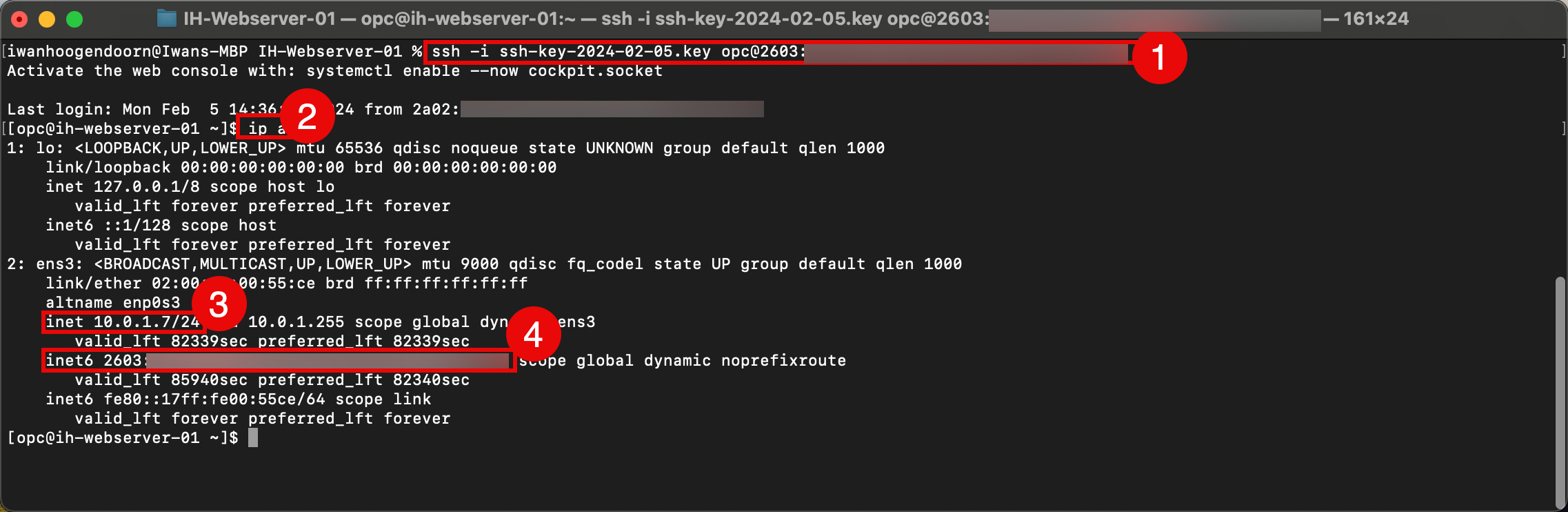
- We also test the connection using the macOS CLI terminal, run the
ssh -i ssh-key-2024-02-05.key opc@xxx.xxx.xxx.48command. - After the connection has been established successfully, run the
ip acommand to verify IP addresses. - Notice that the private IPv4 address is the same as provided for the instance details in the OCI Console.
Note that the instance does not have the IPv6 address that was provided for the instance details in the OCI Console.
-
This problem can be fixed by doing a reboot of the instance.
- Navigate to the instance.
- Click Reboot.
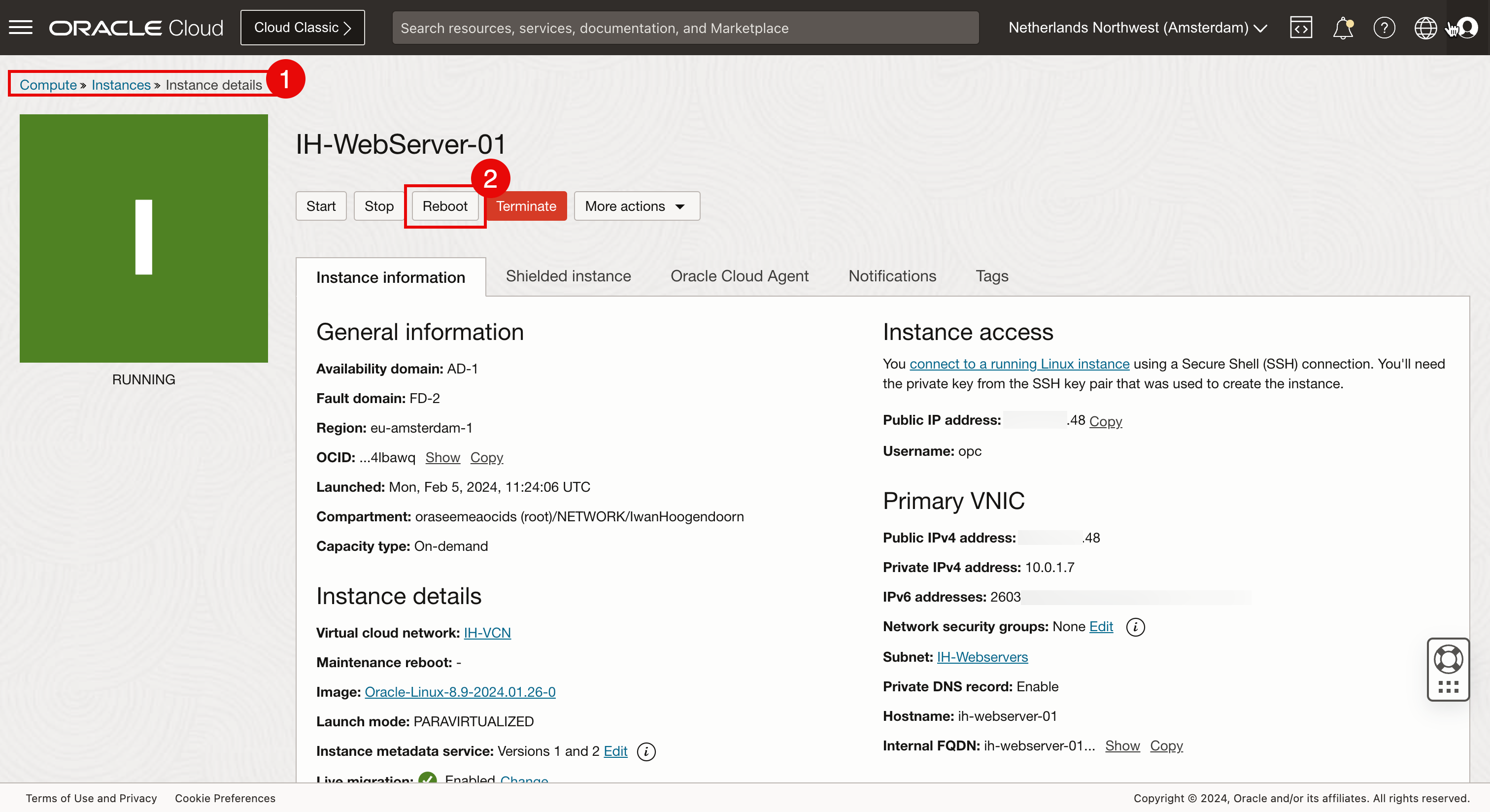
- Connect to the instance again through SSH using the private key.
- After the connection has been established successfully, run the
ip acommand to verify IP addresses. - Notice that the private IPv4 address is the same as provided in the instance details.
- Notice that the private IPv6 address is the same as provided in the instance details.
- To test connectivity towards the internet we also do a ping to the IPv6 IP address of one of Google’s DNS servers.
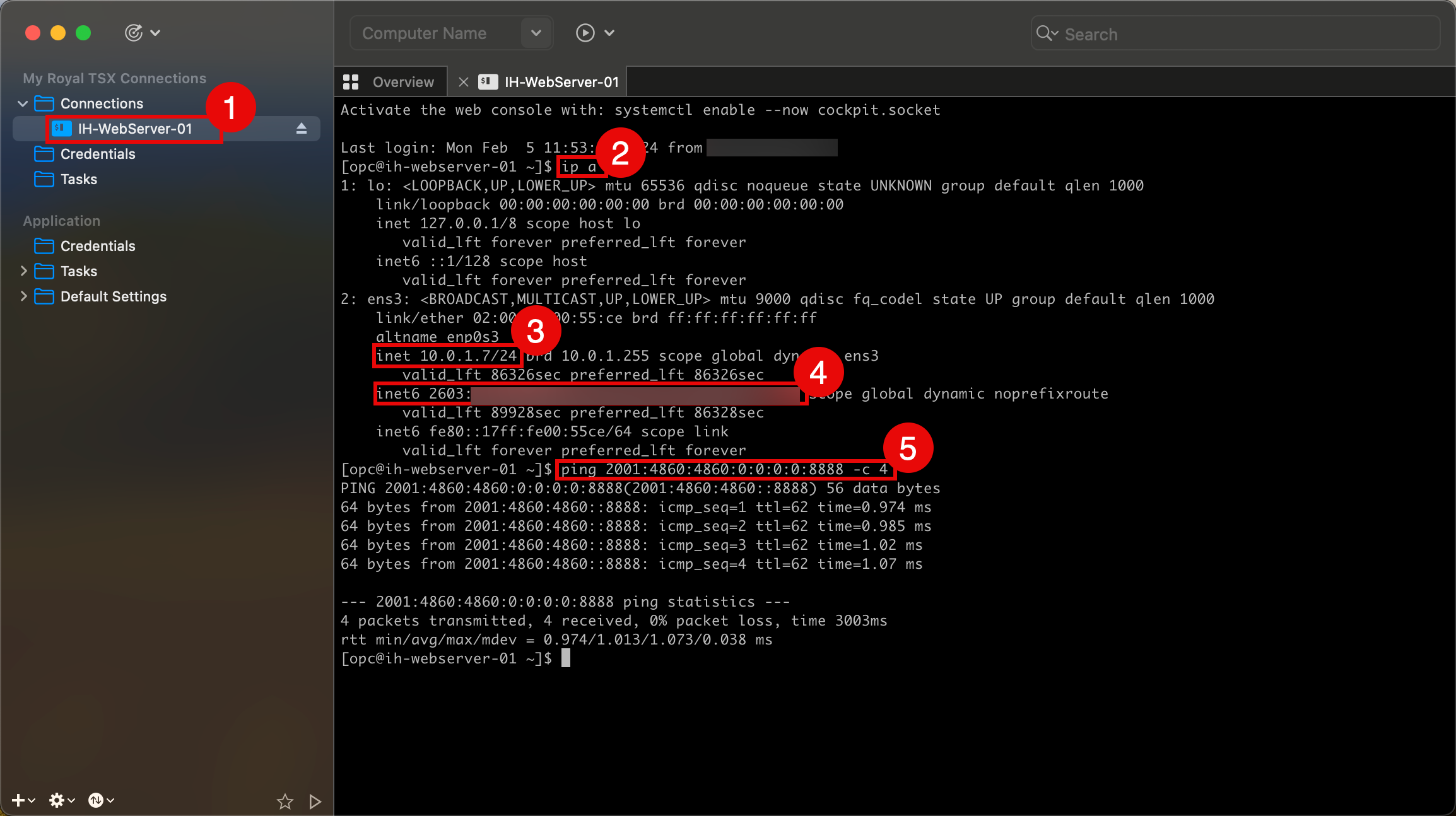
- Do a quick test to see if we can connect to an instance using an IPv6 address. Run the
ssh -i ssh-key-2024-02-05.key opc@2603:xxxx:xxxx:xxxx:xxxx:xxxx:xxxx:xxxxcommand to test. - After the connection has been established successfully, run the
ip acommand to verify IP addresses. - Notice that the private IPv4 address is the same as provided in the instance details.
- Notice that the private IPv6 address is the same as provided in the instance details.
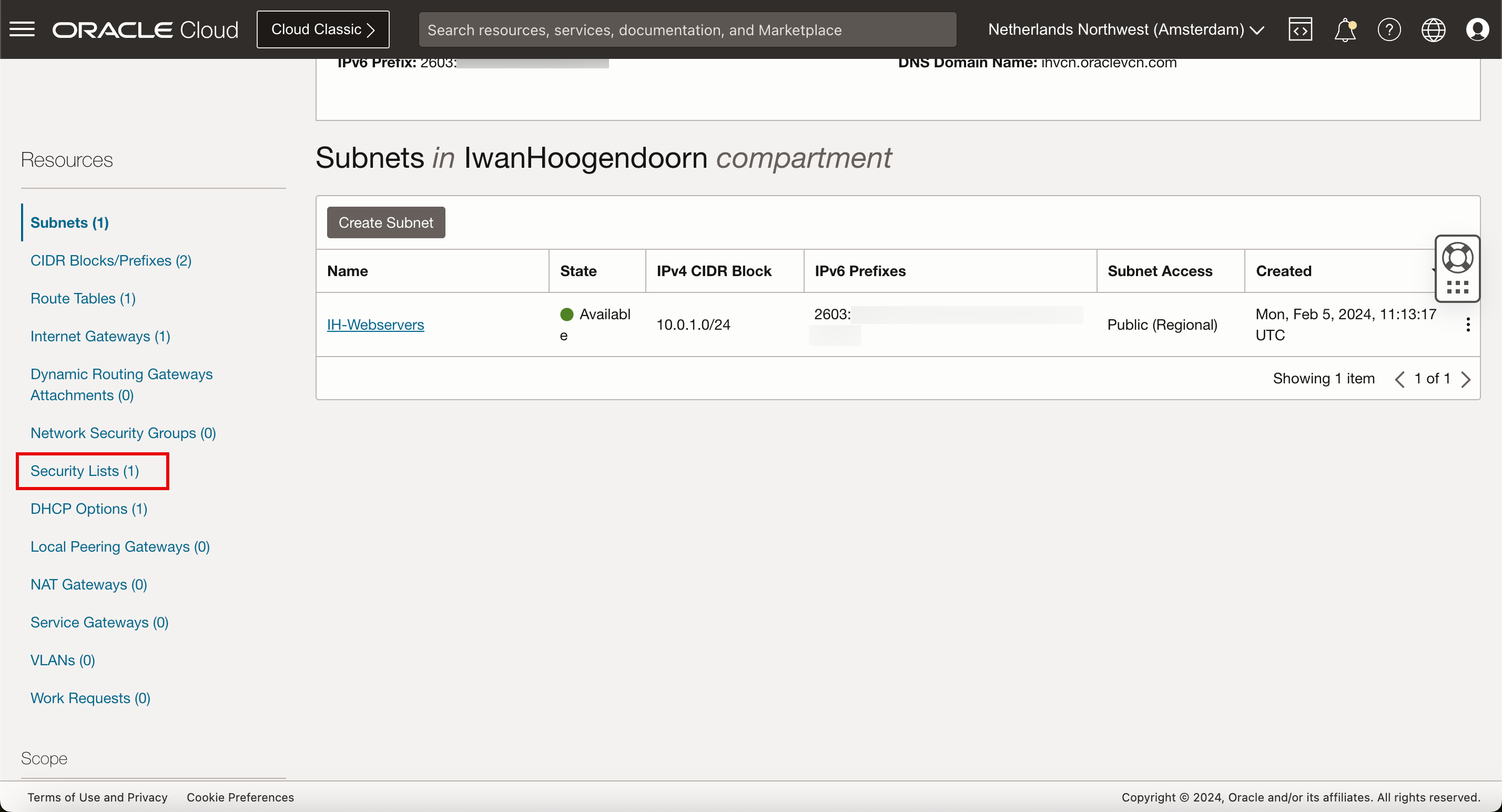
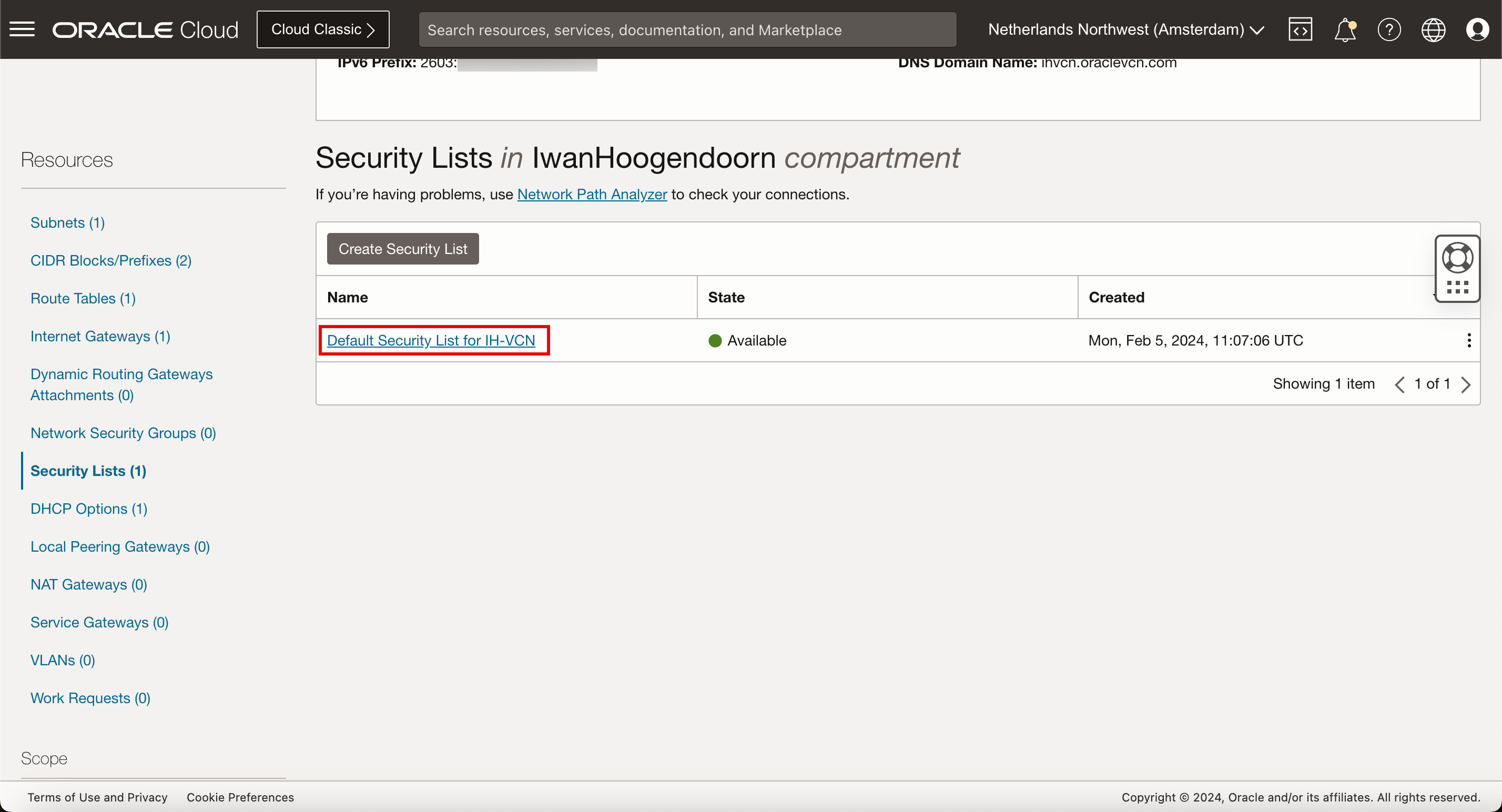
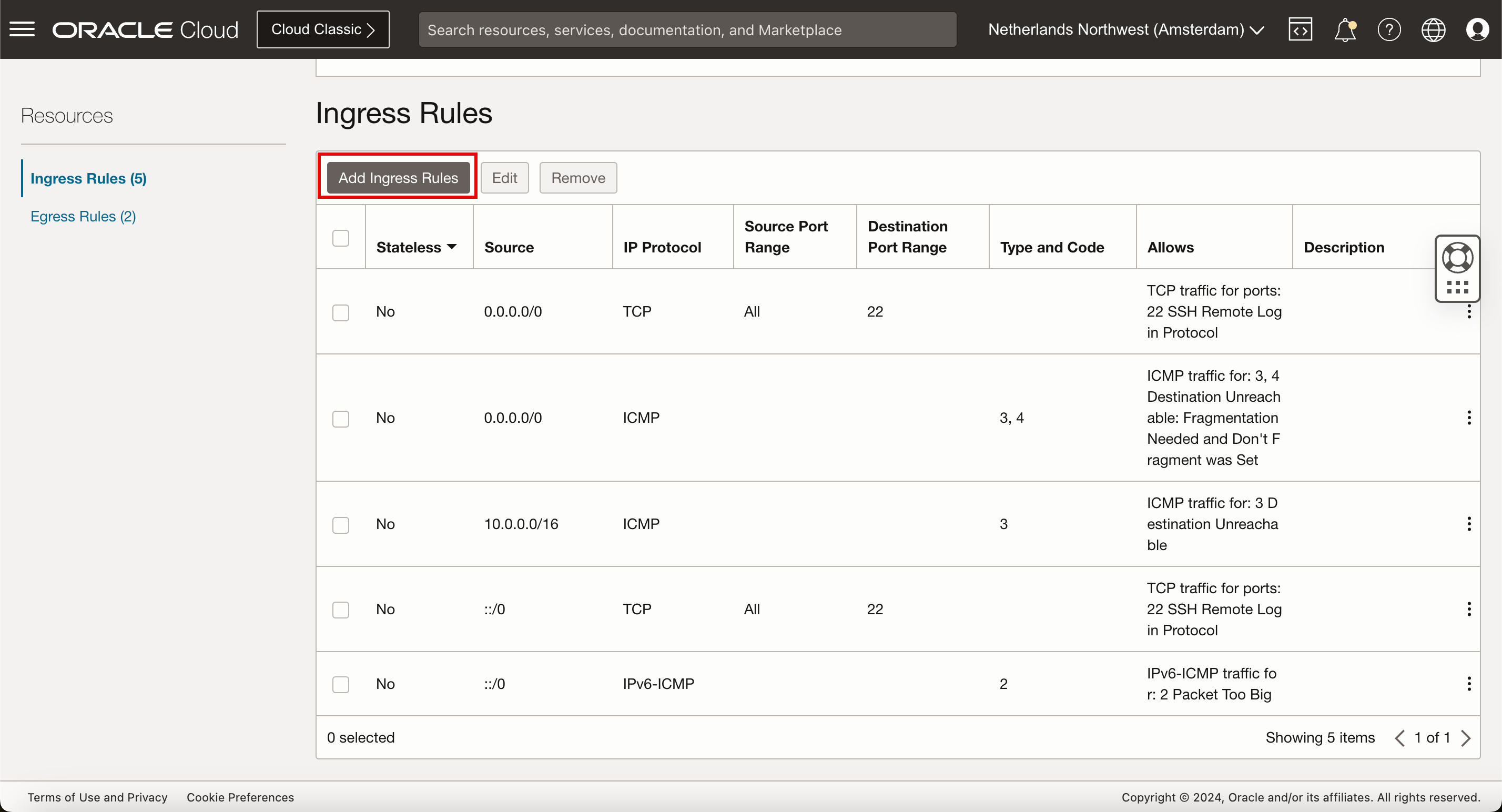
Task 5: Open HTTP and HTTPS on the Default Security List
When a new VCN is created a default security list is applied to the subnets inside that VCN. By default, ICMP and SSH are permitted inbound (ingress). We need to add HTTP and HTTPS to that list to allow incoming traffic for the webserver.
-
Click the hamburger menu, and select Virtual Cloud Networks.
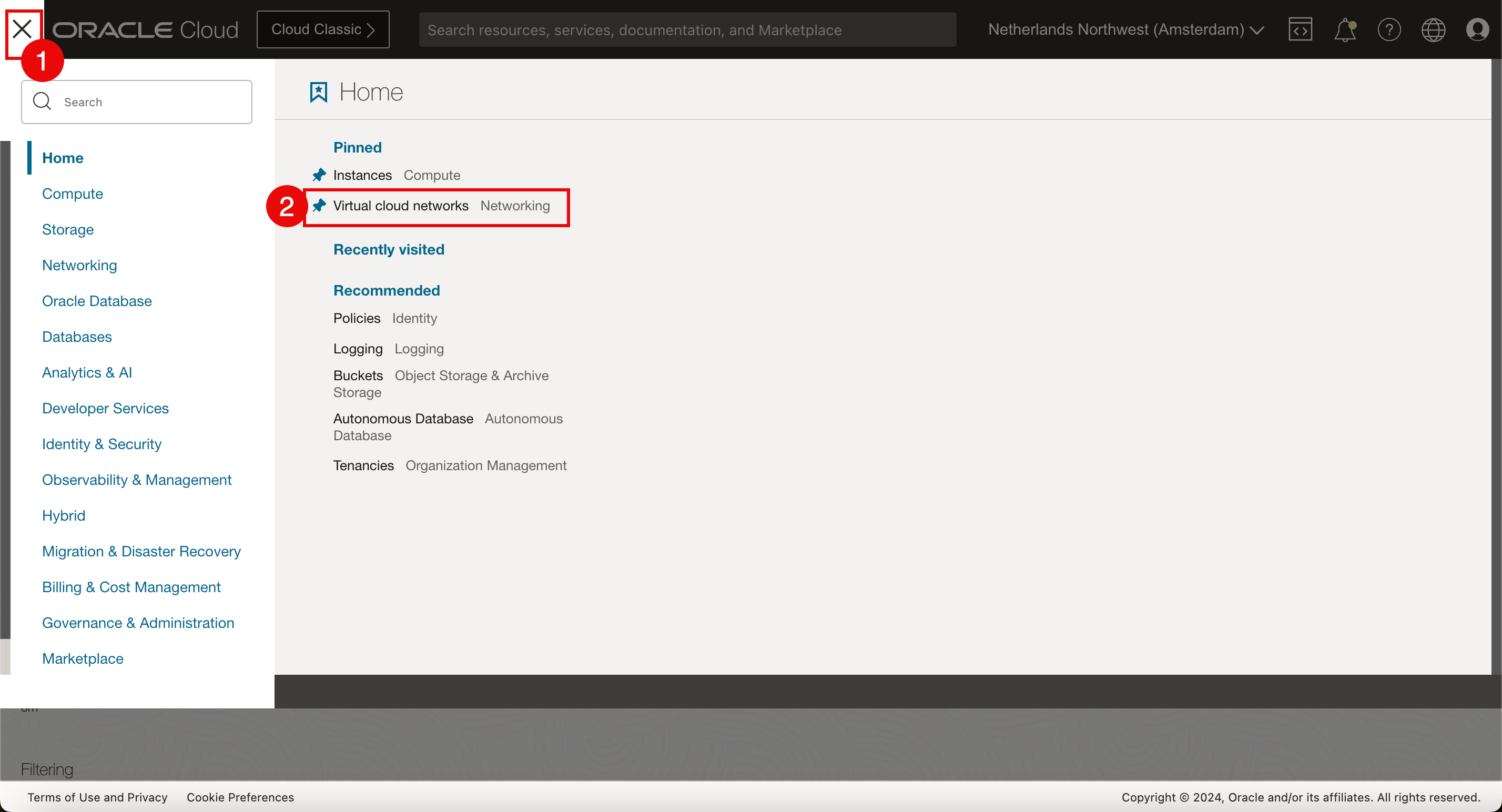
-
Click the VCN created in Task 1.
-
Scroll down.
-
Click Security Lists.
-
Click Default Security List.
-
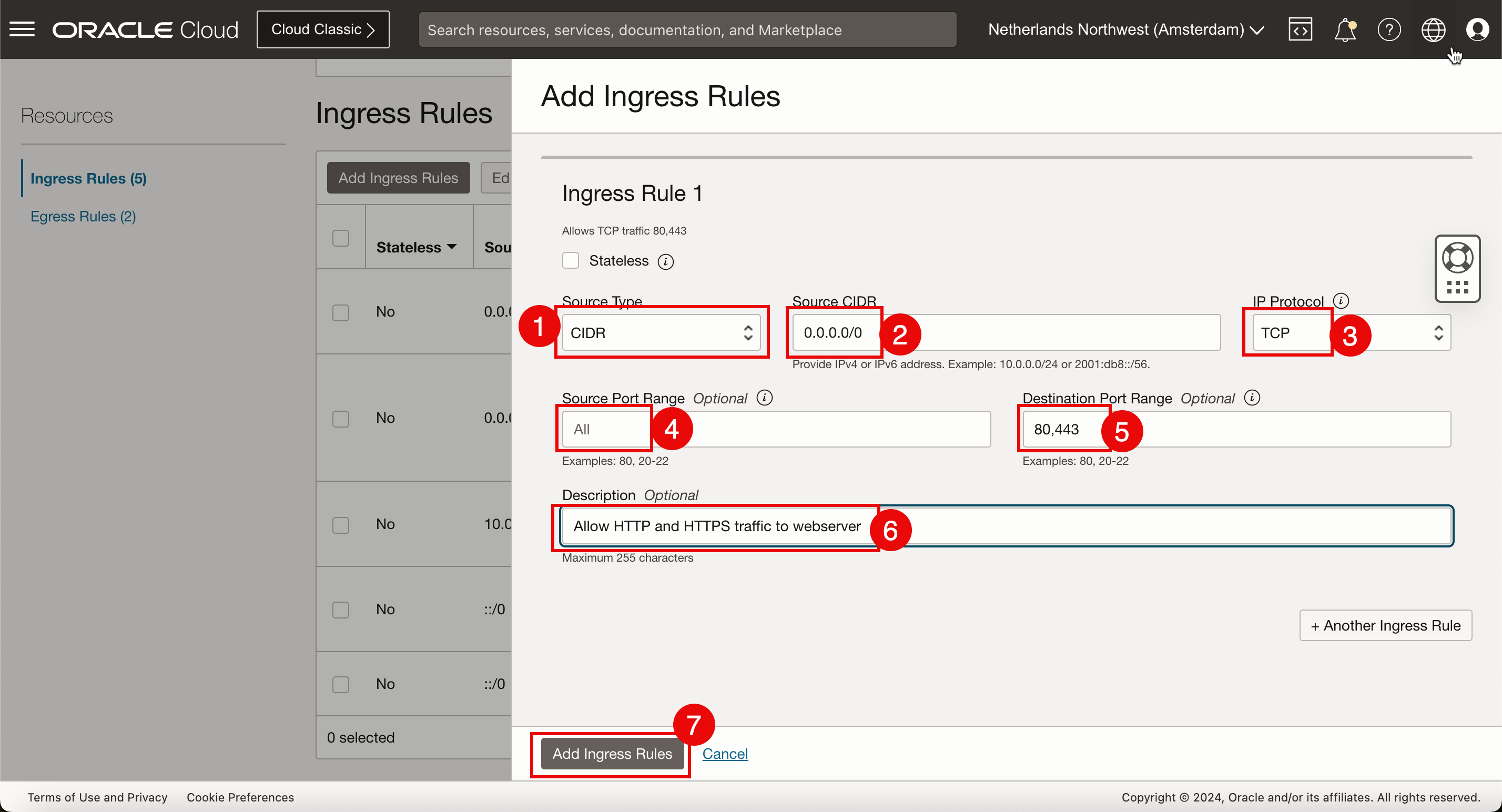
Click Add Ingress Rules.
-
Add new security rules for IPv4 network traffic.
- Source Type: Select CIDR.
- Source CIDR: Enter
0.0.0.0/0. - IP Protocol: Select TCP.
- Source Port Range: Keep default (All).
- Destination Port Range: Select
80,443(HTTP and HTTPS). - Enter the Description.
- Click Add Ingress Rules.
-
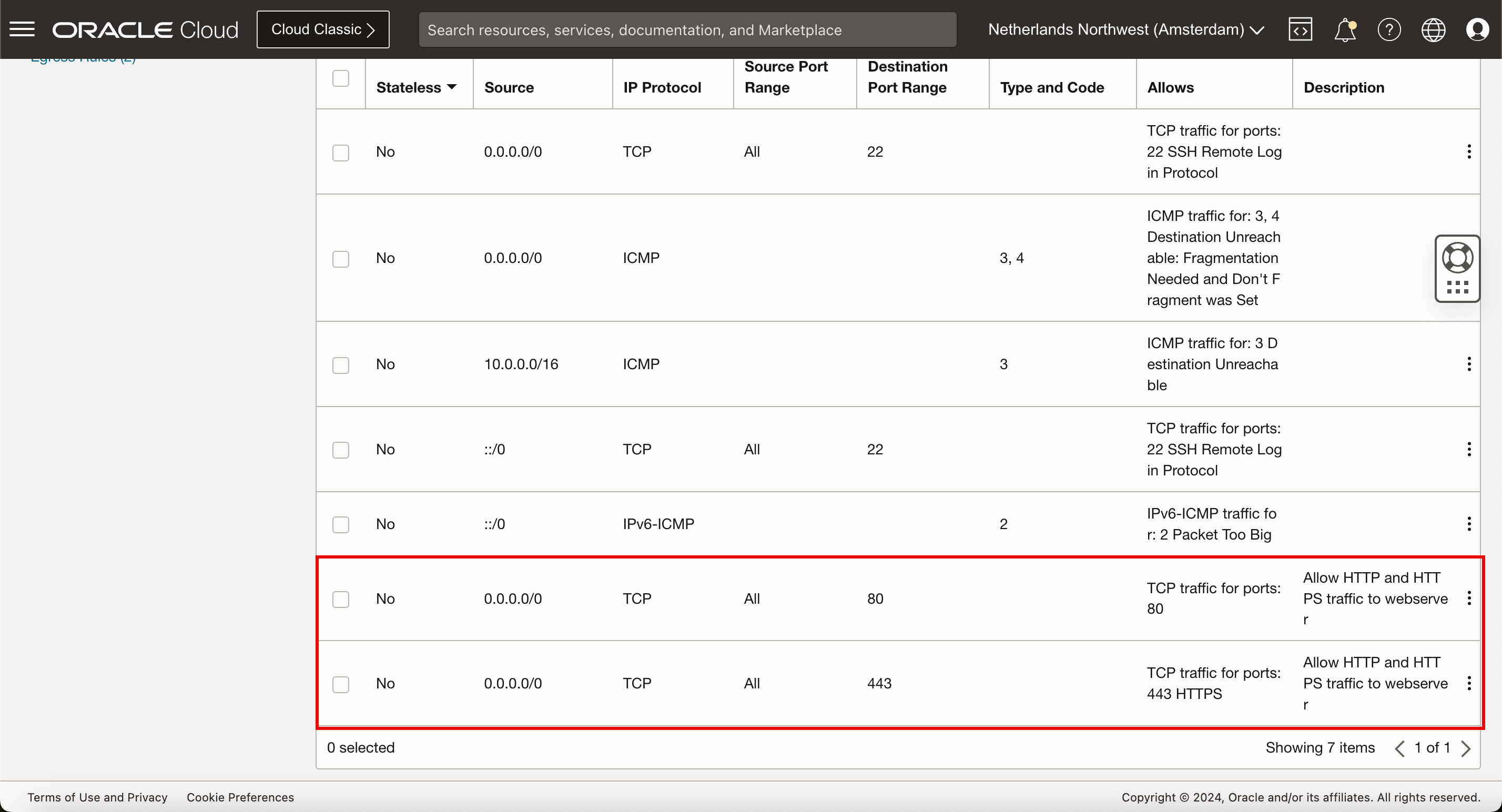
Review the IPv4 Security Rules to allow HTTP and HTTPS traffic inbound.
-
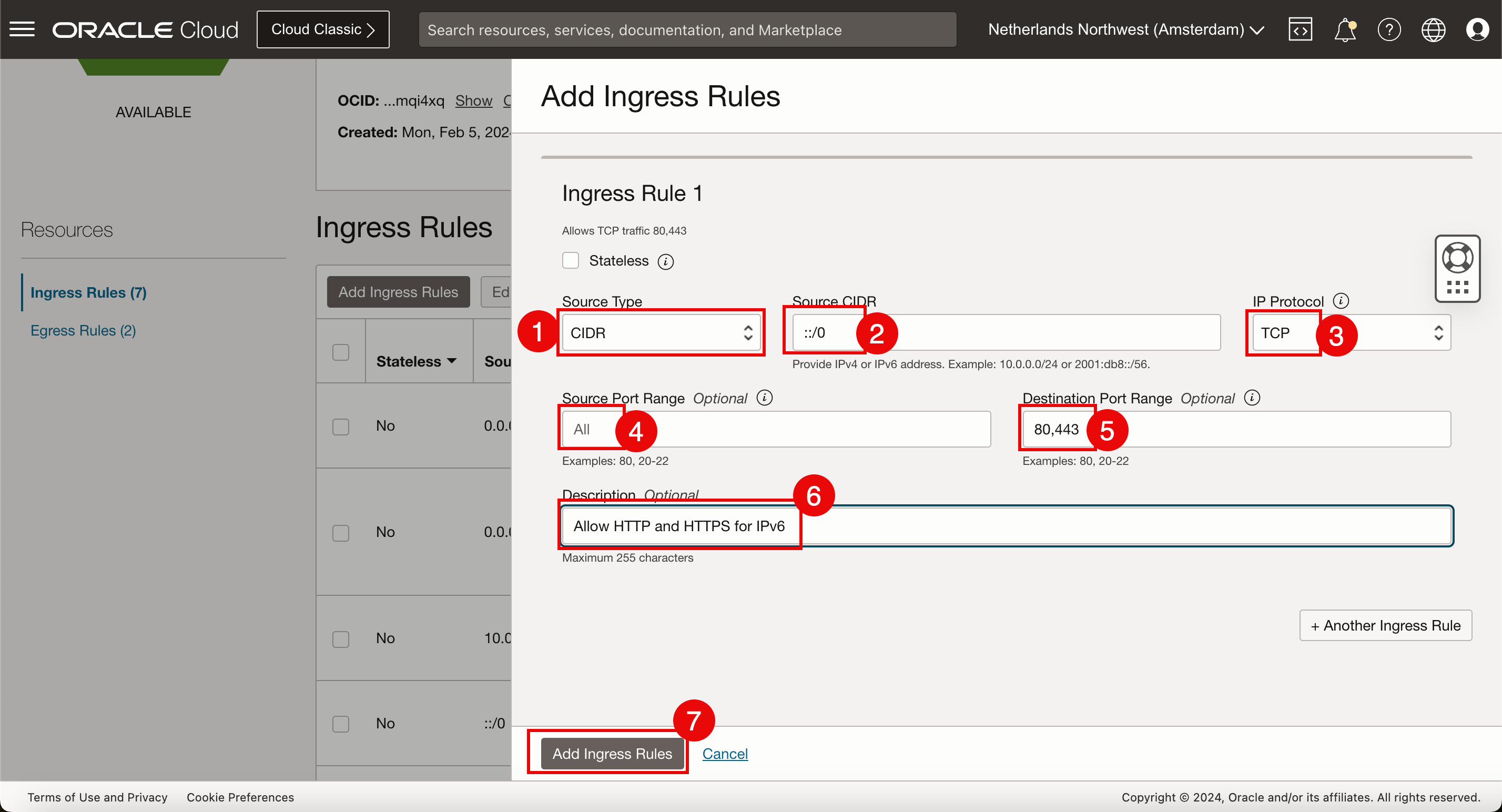
To add new security rules for IPv6 network traffic, create new ingress rules. Click Add Ingress Rules again.
- Source Type: Select CIDR.
- Source CIDR: Enter
::/0. - IP Protocol: Select TCP.
- Source Port Range: Keep default (All).
- Destination Port Range: Select
80,443(HTTP and HTTPS). - Enter the Description.
- Click Add Ingress Rules.
-
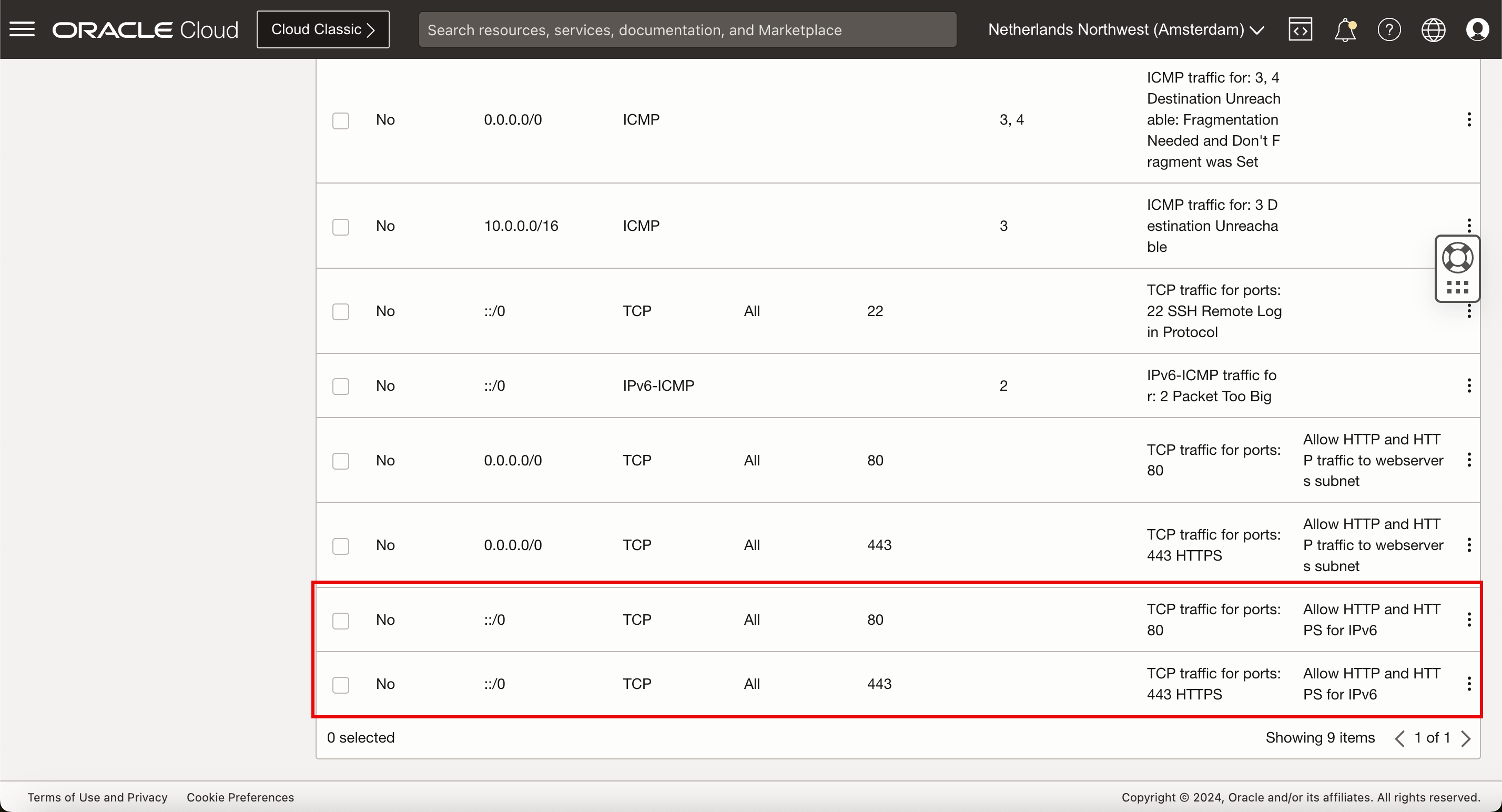
Review the IPv6 Security Rules to allow HTTP and HTTPS traffic inbound.
The security rules are in place and IPv4 and IPv6 traffic is allowed on the VCN subnets, we will install the webserver application on the instance.
Task 6: Install a Webserver on Instance
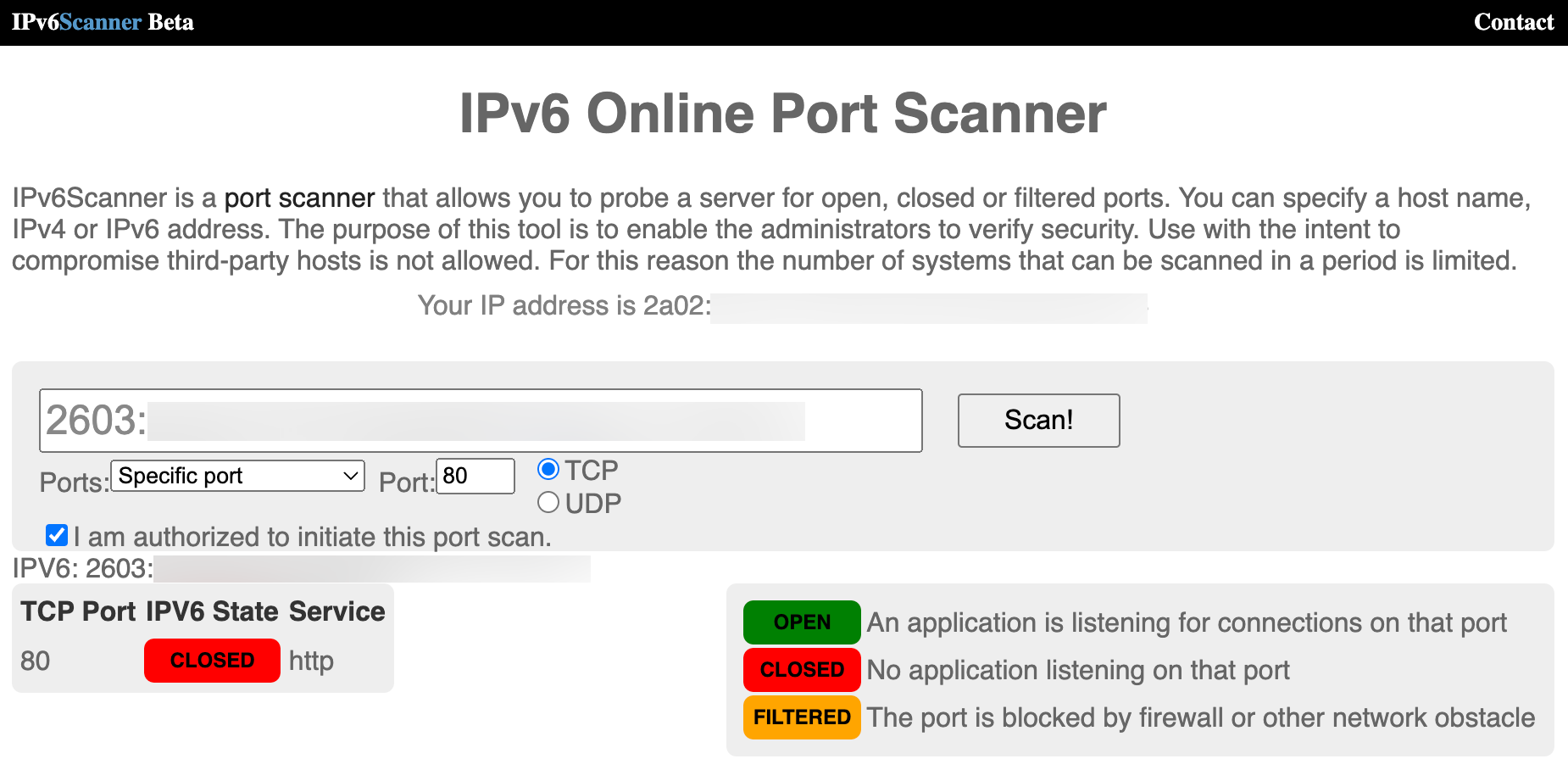
Before we install the webserver application, quickly validate if the firewall ports are configured correctly. use the following website IPV6 Online Port Scanner. This website has an IPv6 port scanner, but you can also enter IPv4 addresses.
-
Enter the IPv4 address with the details to perform the scan on TCP port
80. Notice that this state is CLOSED as the webserver application is not installed yet and the state is not FILTERED as we have added the rules to the default security list.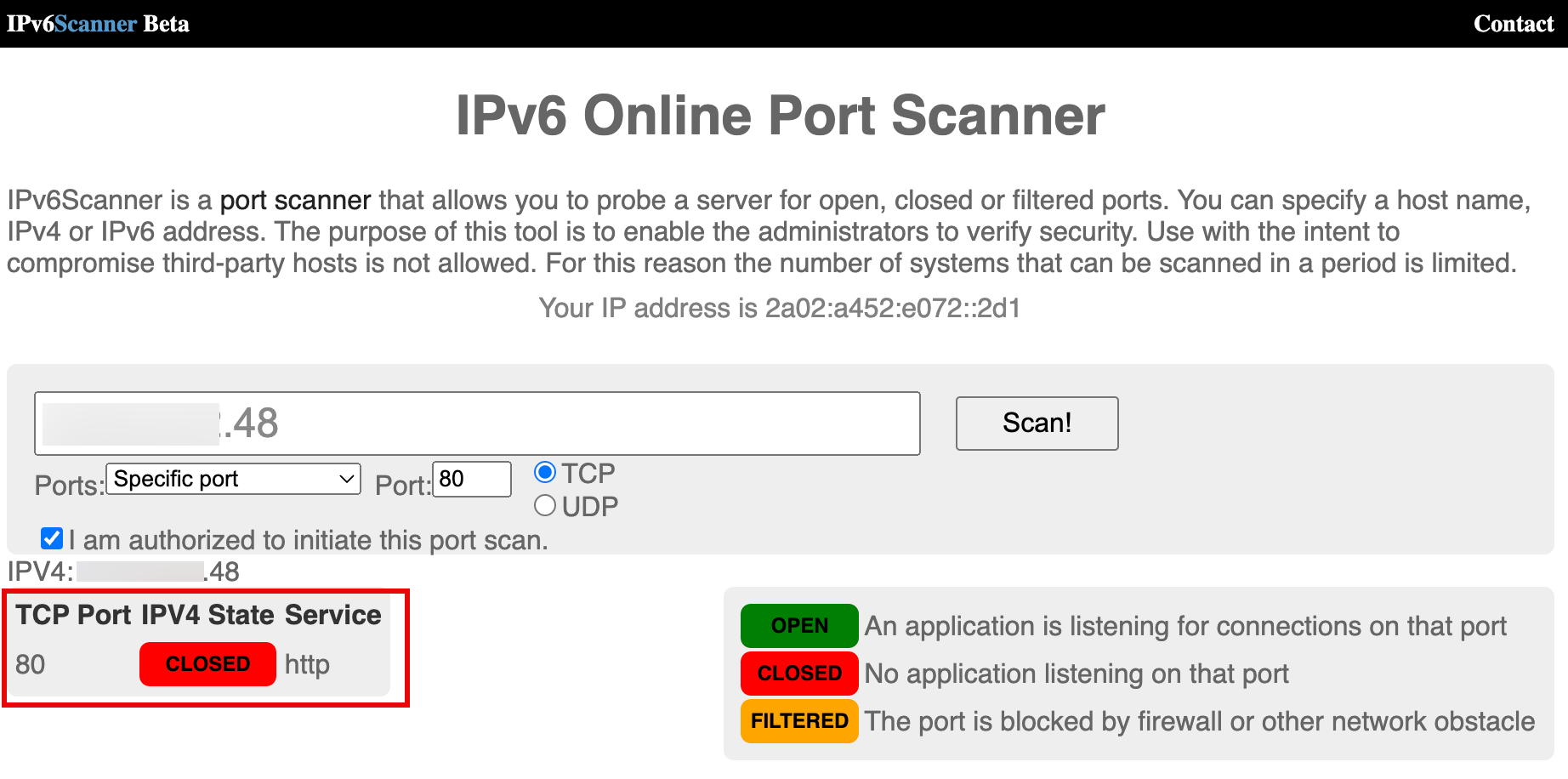
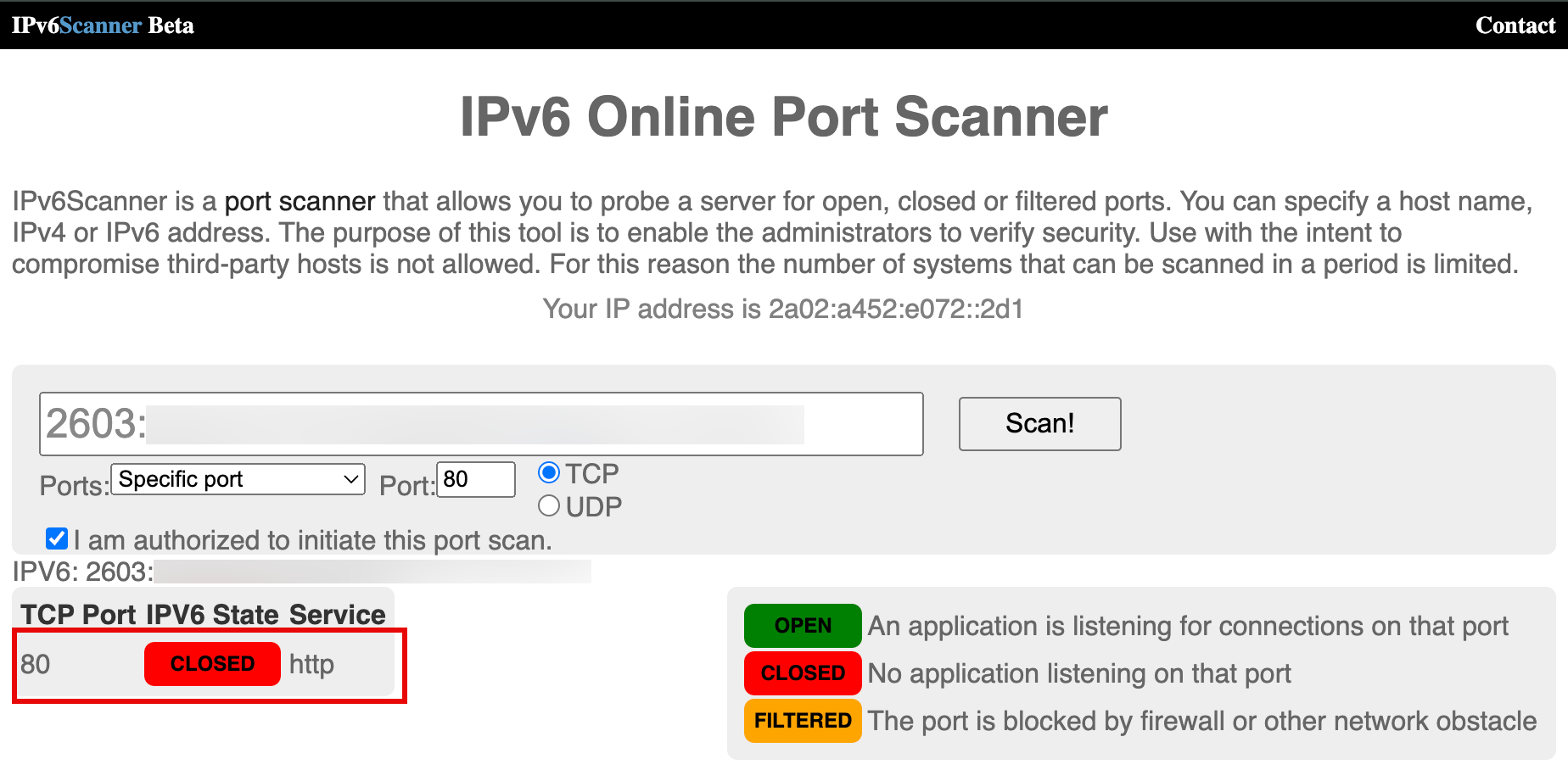
-
For the IPv6 address, Enter the following details. The output is the same as IPv4 for the same reasons.
-
On the webserver instance terminal console or SSH. Enter the following commands to update the DNF software package manager and to install DNF utils.
[opc@ih-webserver-01 ~]$ sudo dnf update -y [opc@ih-webserver-01 ~]$ sudo dnf install dnf-utils -y -
Update the
nginx.repofile to specify the details to download and install the NGINX webserver application.[opc@ih-webserver-01 ~]$ sudo nano /etc/yum.repos.d/nginx.repoCopy and paste the following content in the
nginx.repofile.[nginx-stable] name=nginx stable repo baseurl=http://nginx.org/packages/centos/$releasever/$basearch/ gpgcheck=1 enabled=1 gpgkey=https://nginx.org/keys/nginx_signing.key module_hotfixes=true [nginx-mainline] name=nginx mainline repo baseurl=http://nginx.org/packages/mainline/centos/$releasever/$basearch/ gpgcheck=1 enabled=0 gpgkey=https://nginx.org/keys/nginx_signing.key module_hotfixes=trueVerify the content of the
nginx.repofile.[opc@ih-webserver-01 ~]$ sudo more /etc/yum.repos.d/nginx.repo [nginx-stable] name=nginx stable repo baseurl=http://nginx.org/packages/centos/$releasever/$basearch/ gpgcheck=1 enabled=1 gpgkey=https://nginx.org/keys/nginx_signing.key module_hotfixes=true [nginx-mainline] name=nginx mainline repo baseurl=http://nginx.org/packages/mainline/centos/$releasever/$basearch/ gpgcheck=1 enabled=0 gpgkey=https://nginx.org/keys/nginx_signing.key module_hotfixes=true [opc@ih-webserver-01 ~]$ -
By default, the repository for stable Nginx packages is used. To use mainline Nginx packages, run the following command.
[opc@ih-webserver-01 ~]$ sudo yum-config-manager --enable nginx-mainline -
Use the following command to install the NGINX webserver application.
[opc@ih-webserver-01 ~]$ sudo dnf install nginx -
To start the NGINX webserver application, run the following command.
[opc@ih-webserver-01 ~]$ sudo systemctl start nginx -
When the installation is complete, enable NGINX to start automatically upon system boot and start the webserver.
[opc@ih-webserver-01 ~]$ sudo systemctl enable nginx Created symlink /etc/systemd/system/multi-user.target.wants/nginx.service → /usr/lib/systemd/system/nginx.service. -
Use the following command to verify the running status of the NGINX webserver application.
[opc@ih-webserver-01 ~]$ systemctl status nginx ● nginx.service - nginx - high performance web server Loaded: loaded (/usr/lib/systemd/system/nginx.service; enabled; vendor preset: disabled) Active: active (running) since Tue 2024-02-06 08:58:43 GMT; 2min 47s ago Docs: http://nginx.org/en/docs/ Main PID: 43323 (nginx) Tasks: 3 (limit: 99901) Memory: 2.8M CGroup: /system.slice/nginx.service ├─43323 nginx: master process /usr/sbin/nginx -c /etc/nginx/nginx.conf ├─43324 nginx: worker process └─43325 nginx: worker process Feb 06 08:58:43 ih-webserver-01 systemd[1]: Starting nginx - high performance web server... Feb 06 08:58:43 ih-webserver-01 systemd[1]: Started nginx - high performance web server. [opc@ih-webserver-01 ~]$ -
Use the following command to verify the version of the NGINX webserver application.
[opc@ih-webserver-01 ~]$ nginx -v nginx version: nginx/1.25.3 [opc@ih-webserver-01 ~]$ -
firewalldis a zone-based personal firewall that is installed on the Oracle Linux deployment on OCI. We already have a firewall configured through the default security list on the VCN subnets. We will disable the internalfirewalldservice. Run the following command.[opc@ih-webserver-01 nginx]$ sudo systemctl stop firewalld [opc@ih-webserver-01 nginx]$ sudo systemctl disable firewalld Removed /etc/systemd/system/multi-user.target.wants/firewalld.service. Removed /etc/systemd/system/dbus-org.fedoraproject.FirewallD1.service. [opc@ih-webserver-01 nginx]$ sudo setenforce 0 [opc@ih-webserver-01 nginx]$ -
To verify if the webserver service is running, check if the listener is running. Run the following command. Notice that the three NGINX services are running all listening on IPv4 and port
80. What stands out here is that we are missing the IPv6 listener.[opc@ih-webserver-01 ~]$ sudo lsof -i -P -n | grep LISTEN systemd 1 root 71u IPv4 19039 0t0 TCP *:111 (LISTEN) systemd 1 root 82u IPv6 19041 0t0 TCP *:111 (LISTEN) rpcbind 1421 rpc 4u IPv4 19039 0t0 TCP *:111 (LISTEN) rpcbind 1421 rpc 6u IPv6 19041 0t0 TCP *:111 (LISTEN) osms-agen 2429 root 7u IPv6 41713 0t0 TCP 127.0.0.1:32768 (LISTEN) osms-agen 2429 root 10u IPv4 41722 0t0 TCP 127.0.0.1:9003 (LISTEN) pmcd 2469 pcp 0u IPv4 35603 0t0 TCP 127.0.0.1:44321 (LISTEN) pmcd 2469 pcp 3u IPv6 35604 0t0 TCP [::1]:44321 (LISTEN) pmlogger 3188 pcp 7u IPv4 42005 0t0 TCP 127.0.0.1:4330 (LISTEN) pmlogger 3188 pcp 8u IPv6 42006 0t0 TCP [::1]:4330 (LISTEN) sshd 6745 root 3u IPv4 54797 0t0 TCP *:22 (LISTEN) sshd 6745 root 4u IPv6 54799 0t0 TCP *:22 (LISTEN) nginx 43323 root 6u IPv4 98324 0t0 TCP *:80 (LISTEN) nginx 43324 nginx 6u IPv4 98324 0t0 TCP *:80 (LISTEN) nginx 43325 nginx 6u IPv4 98324 0t0 TCP *:80 (LISTEN) -
Another quick check, we do a curl to the local webserver to see if we can see the default NGINX webserver is reachable using IPv4.
[opc@ih-webserver-01 ~]$ curl http://localhost <!DOCTYPE html> <html> <head> <title>Welcome to nginx!</title> <style> html { color-scheme: light dark; } body { width: 35em; margin: 0 auto; font-family: Tahoma, Verdana, Arial, sans-serif; } </style> </head> <body> <h1>Welcome to nginx!</h1> <p>If you see this page, the nginx web server is successfully installed and working. Further configuration is required.</p> <p>For online documentation and support please refer to <a href="http://nginx.org/">nginx.org</a>.<br/> Commercial support is available at <a href="http://nginx.com/">nginx.com</a>.</p> <p><em>Thank you for using nginx.</em></p> </body> </html> [opc@ih-webserver-01 ~]$ -
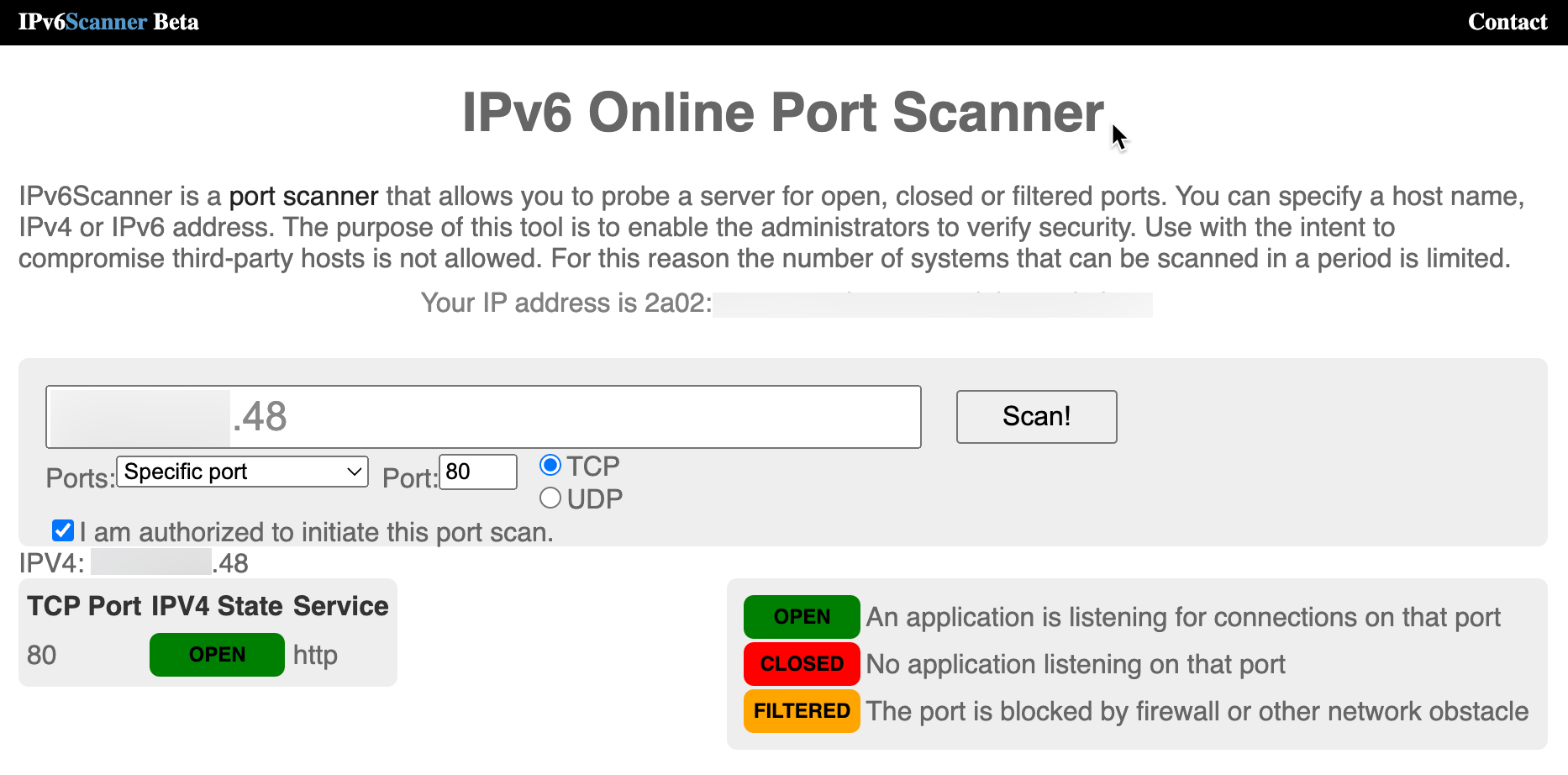
We will do the same test from the internet using the same IPv6 Online Port Scanner website and now the port is OPEN for IPv4.
-
The final test will be to test the website or webserver is reachable using a remote browser using IPv4. The URL used is
http://144.xxx.xxx.xxx.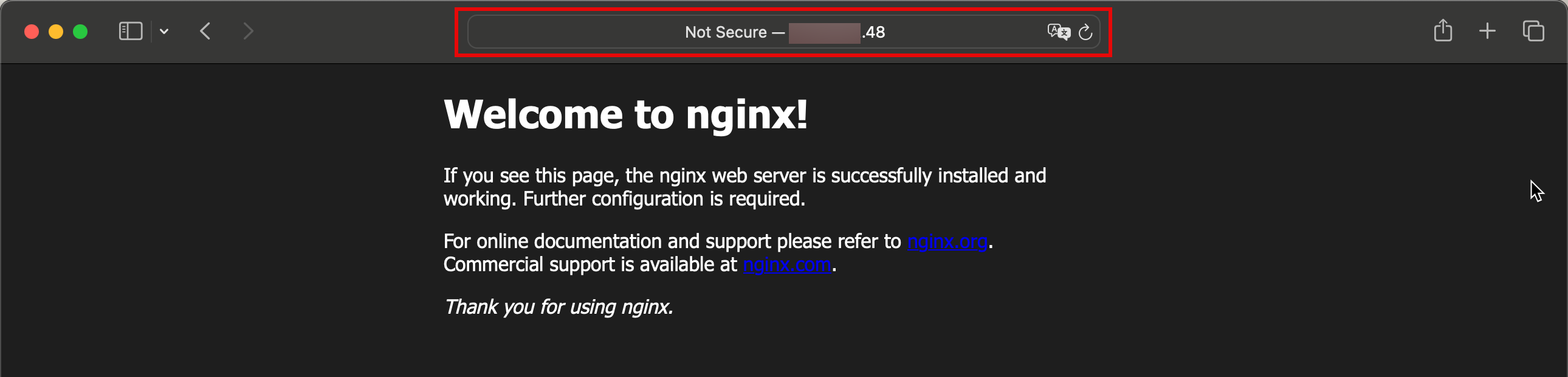
-
Even though we have installed the NGINX webserver application, we still get the following result for the IPv6 address.
To fix this, we need to make sure that the webserver is configured to listen to IPv6 addresses as well. To do this, edit the
default.confnginx file.[opc@ih-webserver-01 conf.d]$ sudo nano /etc/nginx/conf.d/default.confThe server section of the configuration file looks like this.
server { listen 80; server_name localhost; #access_log /var/log/nginx/host.access.log main; location / { root /usr/share/nginx/html; index index.html index.htm; }Add the following line to the server section.
**listen [::]:80;**The server section will look like this.
server { listen 80; **listen [::]:80;** server_name localhost; #access_log /var/log/nginx/host.access.log main; location / { root /usr/share/nginx/html; index index.html index.htm; }After the update, the
default.conffile will look like.[opc@ih-webserver-01 conf.d]$ sudo more /etc/nginx/conf.d/default.conf server { listen 80; **listen [::]:80;** server_name localhost; #access_log /var/log/nginx/host.access.log main; location / { root /usr/share/nginx/html; index index.html index.htm; } #error_page 404 /404.html; # redirect server error pages to the static page /50x.html # error_page 500 502 503 504 /50x.html; location = /50x.html { root /usr/share/nginx/html; } # proxy the PHP scripts to Apache listening on 127.0.0.1:80 # #location ~ \.php$ { # proxy_pass http://127.0.0.1; #} # pass the PHP scripts to FastCGI server listening on 127.0.0.1:9000 # #location ~ \.php$ { # root html; # fastcgi_pass 127.0.0.1:9000; # fastcgi_index index.php; # fastcgi_param SCRIPT_FILENAME /scripts$fastcgi_script_name; # include fastcgi_params; #} # deny access to .htaccess files, if Apache's document root # concurs with nginx's one # #location ~ /\.ht { # deny all; #} } [opc@ih-webserver-01 conf.d]$ -
Use the following command to restart the NGINX webserver.
[opc@ih-webserver-01 ~]$ sudo systemctl restart nginx -
Use the following command to verify the listeners again. Notice that NGINX is also listed on IPv6 next to IPv4 now.
[opc@ih-webserver-01 conf.d]$ sudo lsof -i -P -n | grep LISTEN systemd 1 root 46u IPv4 19039 0t0 TCP *:111 (LISTEN) systemd 1 root 48u IPv6 19041 0t0 TCP *:111 (LISTEN) rpcbind 1421 rpc 4u IPv4 19039 0t0 TCP *:111 (LISTEN) rpcbind 1421 rpc 6u IPv6 19041 0t0 TCP *:111 (LISTEN) osms-agen 2429 root 7u IPv6 41713 0t0 TCP 127.0.0.1:32768 (LISTEN) osms-agen 2429 root 10u IPv4 41722 0t0 TCP 127.0.0.1:9003 (LISTEN) pmcd 2469 pcp 0u IPv4 35603 0t0 TCP 127.0.0.1:44321 (LISTEN) pmcd 2469 pcp 3u IPv6 35604 0t0 TCP [::1]:44321 (LISTEN) pmlogger 3188 pcp 7u IPv4 42005 0t0 TCP 127.0.0.1:4330 (LISTEN) pmlogger 3188 pcp 8u IPv6 42006 0t0 TCP [::1]:4330 (LISTEN) sshd 6745 root 3u IPv4 54797 0t0 TCP *:22 (LISTEN) sshd 6745 root 4u IPv6 54799 0t0 TCP *:22 (LISTEN) nginx 54944 root 6u IPv4 219674 0t0 TCP *:80 (LISTEN) nginx 54944 root 7u IPv6 219675 0t0 TCP *:80 (LISTEN) nginx 54945 nginx 6u IPv4 219674 0t0 TCP *:80 (LISTEN) nginx 54945 nginx 7u IPv6 219675 0t0 TCP *:80 (LISTEN) nginx 54946 nginx 6u IPv4 219674 0t0 TCP *:80 (LISTEN) nginx 54946 nginx 7u IPv6 219675 0t0 TCP *:80 (LISTEN) [opc@ih-webserver-01 conf.d]$We will do the same test from the internet using the same IPv6 Online Port Scanner website and now the port is OPEN for IPv6.
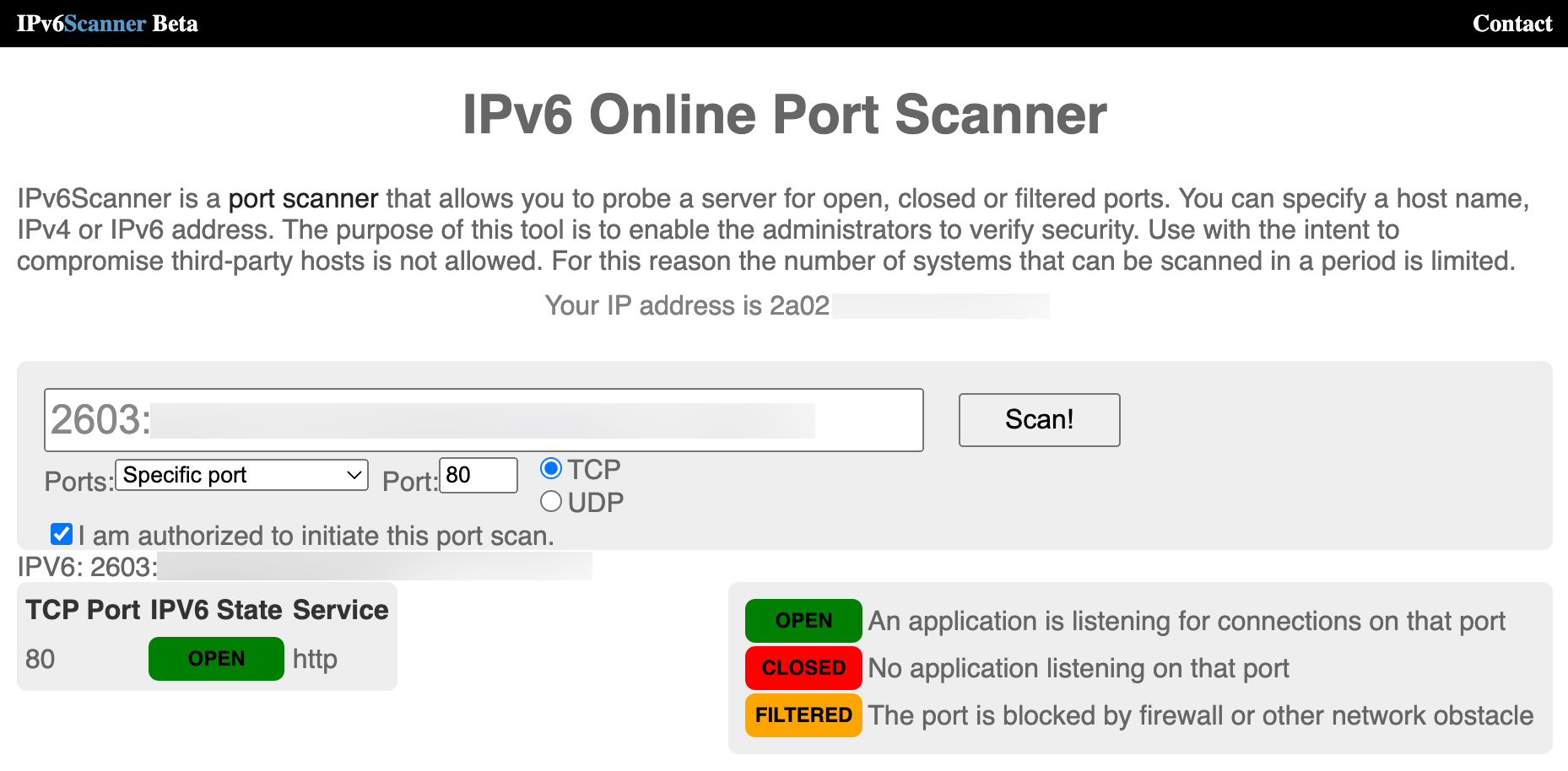
Another quick check, we do a curl to the local webserver to see if we can see the default NGINX webserver is reachable using IPv6.
[opc@ih-webserver-01 conf.d]$ curl -6 "http://[::1]:80" <!DOCTYPE html> <html> <head> <title>Welcome to nginx!</title> <style> html { color-scheme: light dark; } body { width: 35em; margin: 0 auto; font-family: Tahoma, Verdana, Arial, sans-serif; } </style> </head> <body> <h1>Welcome to nginx!</h1> <p>If you see this page, the nginx web server is successfully installed and working. Further configuration is required.</p> <p>For online documentation and support please refer to <a href="http://nginx.org/">nginx.org</a>.<br/> Commercial support is available at <a href="http://nginx.com/">nginx.com</a>.</p> <p><em>Thank you for using nginx.</em></p> </body> </html> [opc@ih-webserver-01 conf.d]$ -
The final test is to test if the website or webserver is reachable using a remote browser using IPv6. The URL used is
http://[2603:xxxx:xxxx:xxxx:xxxx:xxxx:xxxx:xxxx]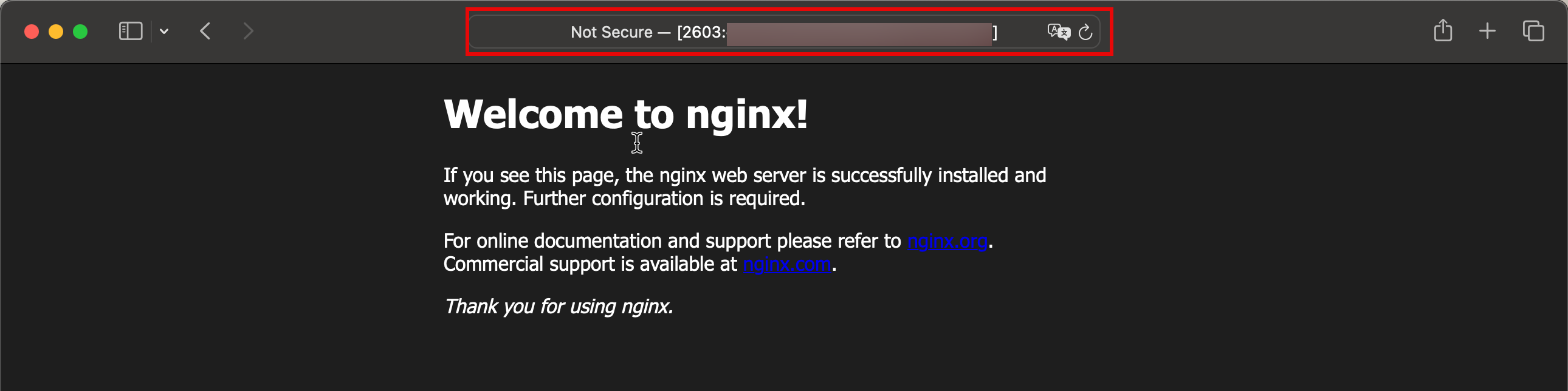
Note: When we use an IPv6 address in the browser, we need to place it between square brackets.
Task 7: Configure DNS records
Note: The domains that we have used in this tutorial were created and configured for testing purposes only.
Now, the website or webserver is reachable from the internet. We are going one step further by configuring an FQDN that can be remembered more easily than an IPv4 address or an IPv6 address. For this tutorial, we use the following subdomain as an example: oci.iwanhoogendoorn.nl for the new webserver.
-
We will log in to the registrar’s domain administration panel for the domain
iwanhoogendoorn.nl.- Notice that we have selected the correct domain to configure.
- Select DNS Management.

-
All the DNS records for the domain iwanhoogendoorn.nl are listed as shown in the following image.
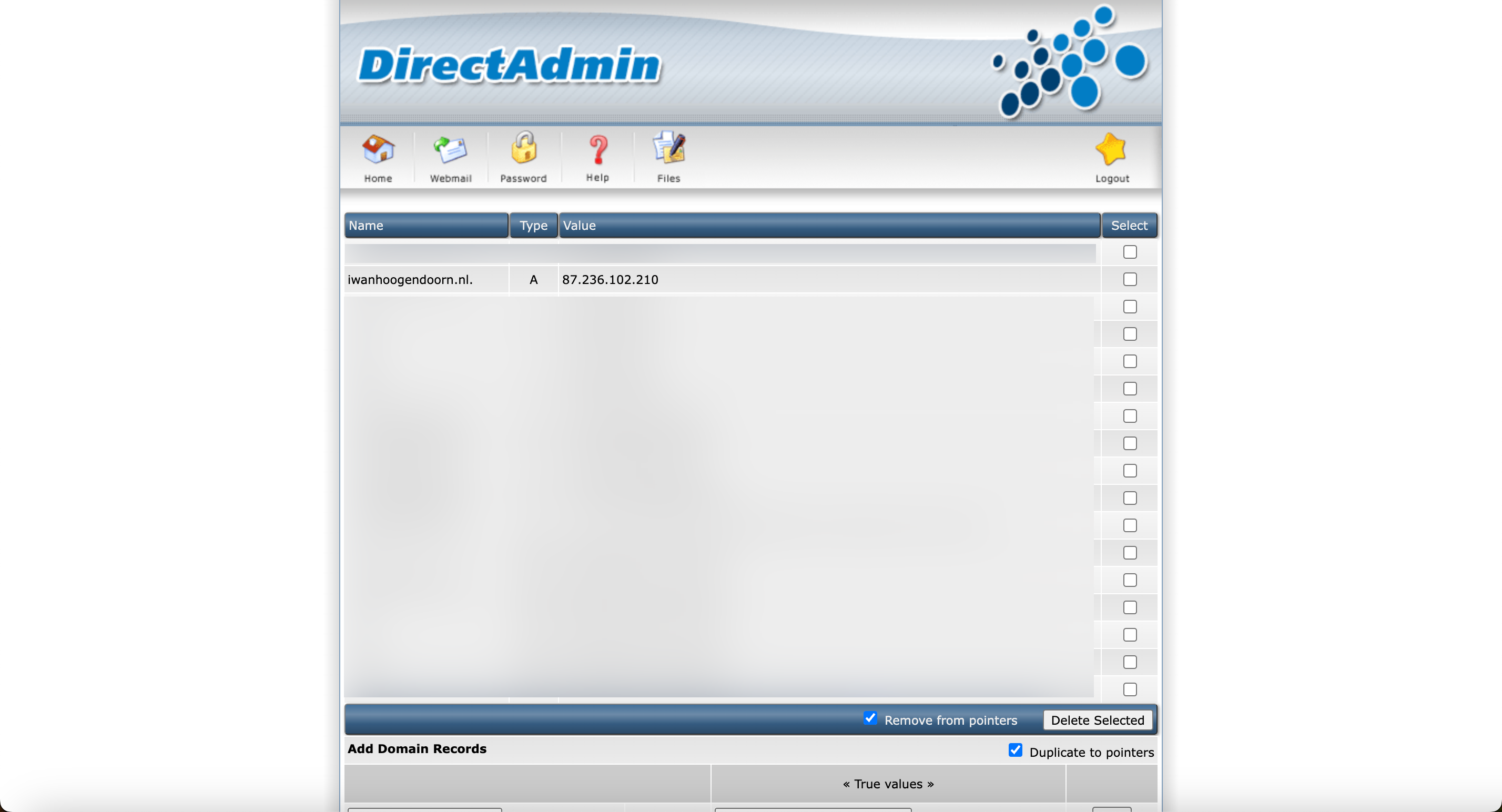
- Add the
ocisubdomain to the domain for IPv4 and select the public IPv4 address of the instance. - Click Add.
- Now let’s add the
ocisubdomain to the domain for IPv6 and select the IPv6 address of the instance. - Click Add.
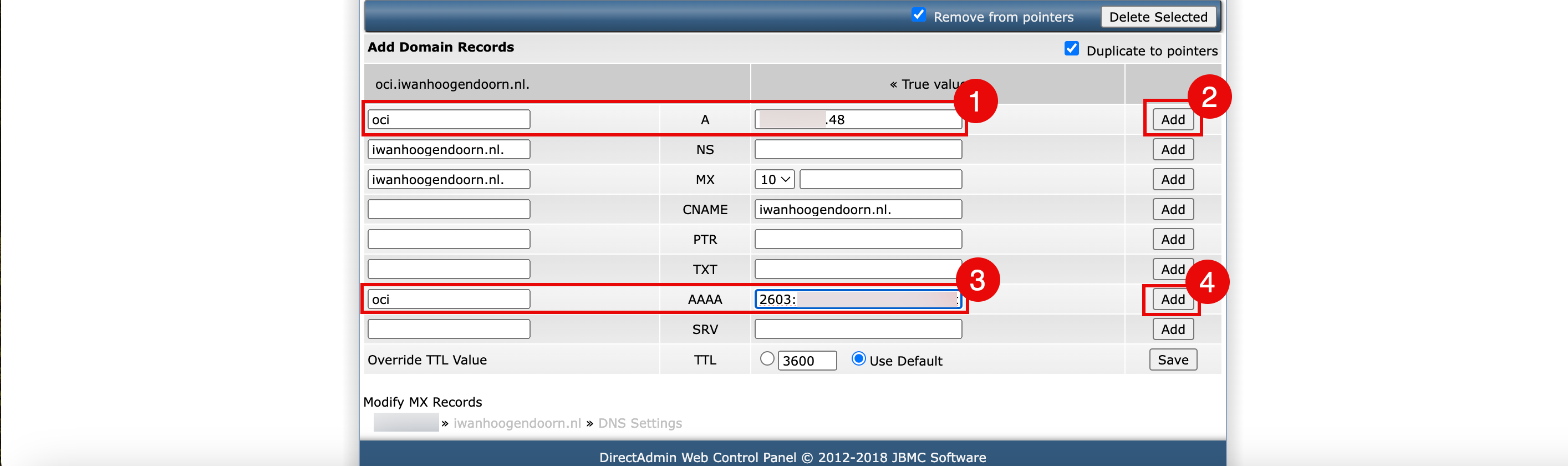
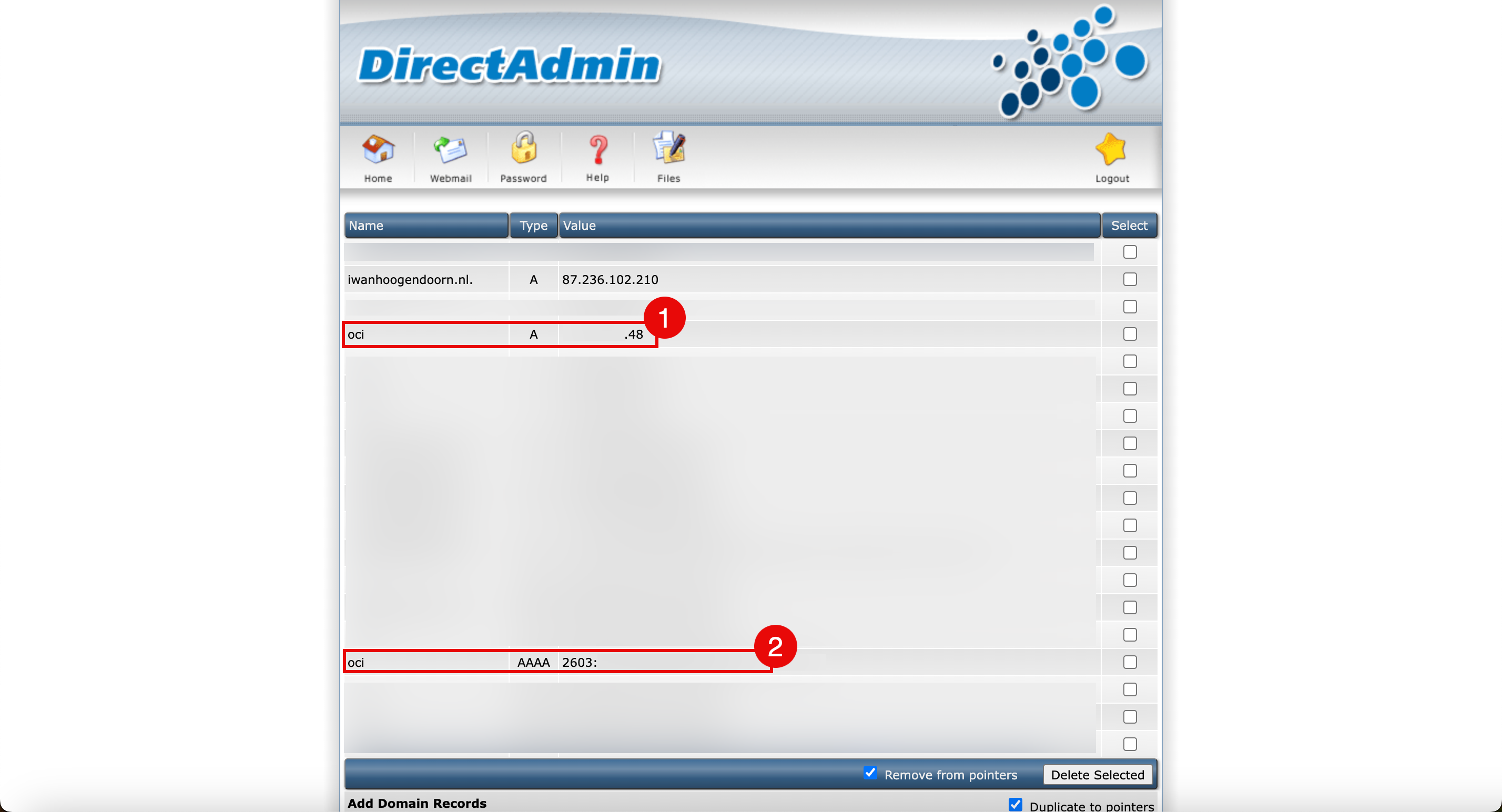
- In the DNS overview page, review the oci.iwanhoogendoorn.nl DNS record for IPv4.
- In the DNS overview page, review the oci.iwanhoogendoorn.nl DNS record for IPv6.
- Add the
-
Use
nslookupcommand to test the oci.iwanhoogendoorn.nl is resolved to the correct IPv4 address.iwanhoogendoorn@Iwans-MacBook-Pro ~ % nslookup oci.iwanhoogendoorn.nl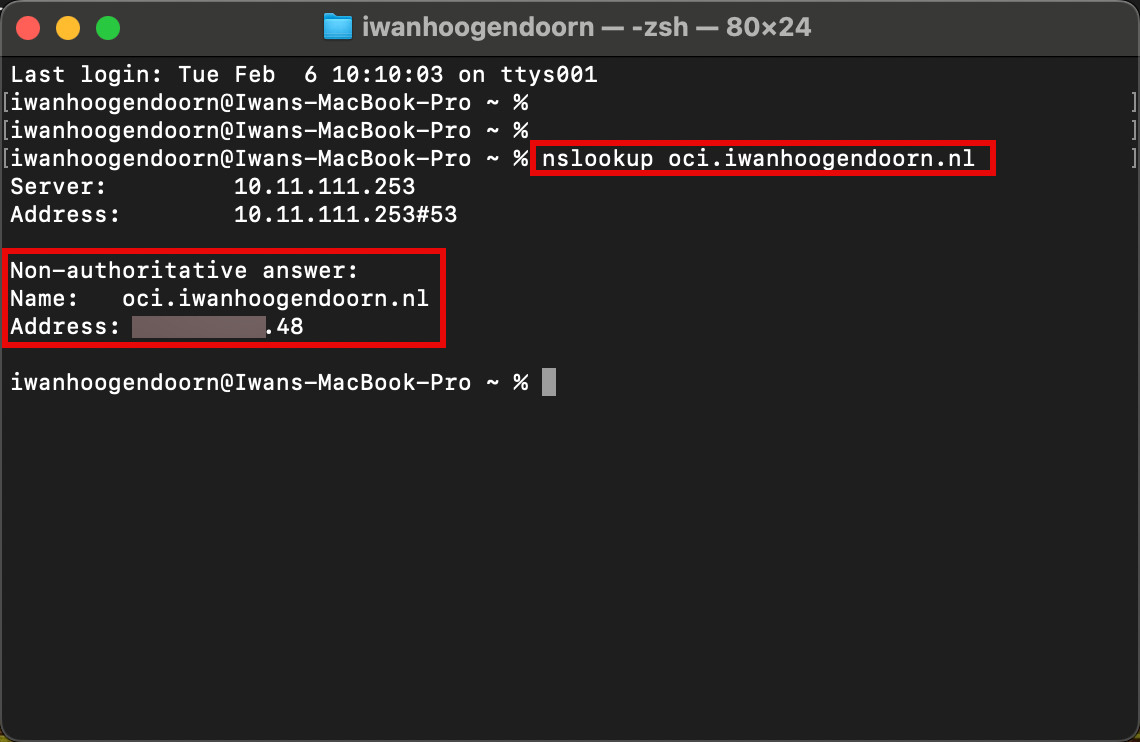
-
Use
nslookupcommand to test the oci.iwanhoogendoorn.nl is resolved to the correct IPv6 address.iwanhoogendoorn@Iwans-MacBook-Pro ~ % nslookup -q=AAAA oci.iwanhoogendoorn.nl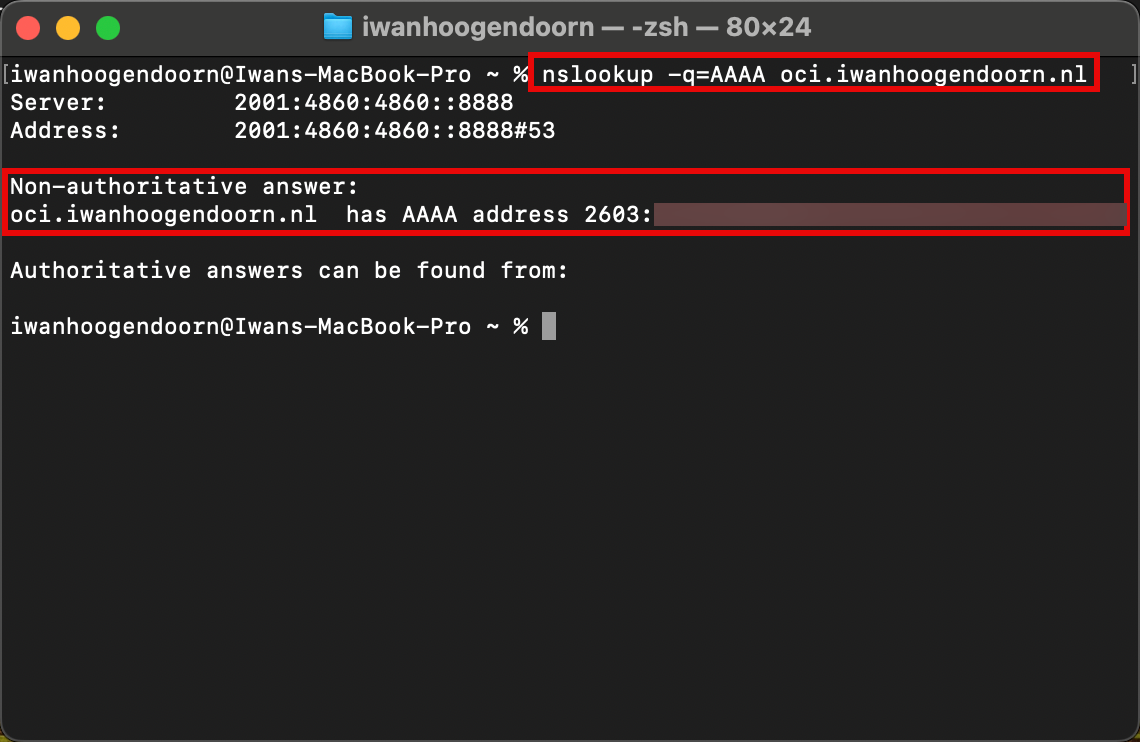
Task 8: Create a Custom Website with NGINX and PHP
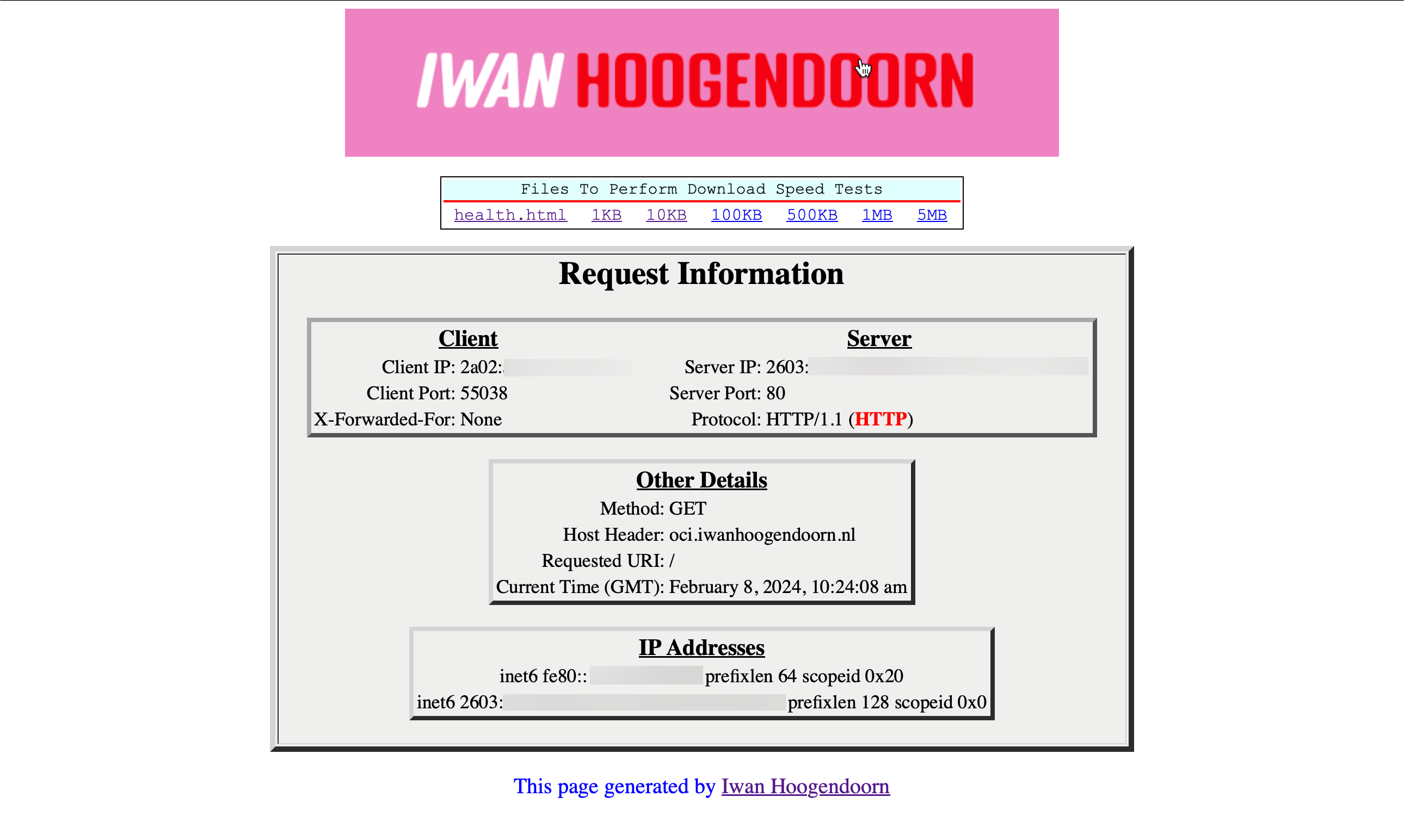
We will create a custom PHP website or script that provides a bit more information about the network and IP addresses with NGINX.
-
Install PHP FastCGI Process Manager (PHP-FPM). PHP-FPM is an alternative FastCGI daemon for PHP that allows a website to handle high loads.
sudo dnf install php-fpm -
Check the installed PHP version.
[opc@ih-webserver-01 /]$ php -v PHP 7.2.24 (cli) (built: Oct 22 2019 08:28:36) ( NTS ) Copyright (c) 1997-2018 The PHP Group Zend Engine v3.2.0, Copyright (c) 1998-2018 Zend Technologies [opc@ih-webserver-01 /]$ -
To get NGINX to work with PHP and the other way around some configuration needs to be done. One configuration file on the PHP side and the NGNIX side.
Depending on your Linux distribution, NGINX and PHP-FPM versions, the configuration file names and path names may be different and this makes the integration part of NGINX and PHP much harder.
Important files and directories for PHP-FPM and NGINX.
Description Oracle Linux 8 Other installations/distributions NGINX web root path /usr/share/nginx/html /usr/share/nginx/www PHP FPM configuration file /etc/php-fpm.d/www.conf php-fpm.conf NGINX configuration file /etc/nginx/conf.d/default.conf nginx.conf PHP FPM socket file /run/php-fpm/www.sock php-fpm.sock, phpx.x-fpm.sock (x.x = version) FastCGI settings file /etc/nginx/fastcgi_params fastcgi.conf PHP configuration file /etc/php.ini
To integrate NGINX with PHP, follow the steps:
-
Edit the PHP-FPM configuration file to integrate NGINX.
Edit
/etc/php-fpm.d/www.conffile.sudo nano /etc/php-fpm.d/www.conf-
Contents of the
/etc/php-fpm.d/www.conffile before changes.; Unix user/group of processes ; Note: The user is mandatory. If the group is not set, the default user's group ; will be used. ; RPM: apache user chosen to provide access to the same directories as httpd **user =** apache ; RPM: Keep a group allowed to write in log dir. **group =** apache -
Contents of the
/etc/php-fpm.d/www.conffile after changes.; Unix user/group of processes ; Note: The user is mandatory. If the group is not set, the default user's group ; will be used. ; RPM: apache user chosen to provide access to the same directories as httpd **user = nginx** ; RPM: Keep a group allowed to write in log dir. **group = nginx**
-
-
Edit the NGINX configuration file to integrate PHP-FPM.
-
Edit the
/etc/nginx/conf.d/default.conffile.[opc@ih-webserver-01 html]$ sudo nano /etc/nginx/conf.d/default.conf -
Add the following configuration.
location / { **# where is the NGINX root www folder?** root /usr/share/nginx/html; # what are the default index files to look for in the directory? index **index.php** index.html index.htm; } # tell NGINX what to do when it sees PHP-FPM giving a 404 HTTP status in the response **location = /404.php { # where is the NGINX root www folder? root /usr/share/nginx/html; # not return error responses with relevant status codes fastcgi_intercept_errors off; # where is PHP-FPM listening? the socket fastcgi_pass unix:/var/run/php-fpm/www.sock; # everytime we're in this location, tell PHP-FPM the complete script filename to be executed fastcgi_param SCRIPT_FILENAME $document_root$fastcgi_script_name; # and don't forget to tell PHP-FPM stuff like SERVER_NAME: include fastcgi_params; }** # tell NGINX what to do when it sees PHP-FPM a .php file **location ~ \.php$ { # where is the NGINX root www folder? root /usr/share/nginx/html; # define custom error pages error_page 404 /404.php; # return error responses with relevant status codes fastcgi_intercept_errors on; # where is PHP-FPM listening? the socket fastcgi_pass unix:/var/run/php-fpm/www.sock; # everytime we're in this location, tell PHP-FPM the complete script filename to be executed fastcgi_param SCRIPT_FILENAME $document_root$fastcgi_script_name; # and don't forget to tell PHP-FPM stuff like SERVER_NAME: include fastcgi_params; }**
-
-
Edit the
php.iniconfiguration file.-
Edit
/etc/php.inifile.[opc@ih-webserver-01 /]$ sudo nano /etc/php.ini -
Make sure the following line is present, changed or uncommented.
cgi.fix_pathinfo = 0;
-
-
Restart the PHP-FPM and NGINX services.
-
Restart the PHP-FPM service.
sudo systemctl start php-fpm -
Restart the NGINX service.
sudo systemctl restart nginx
-
-
Create a custom page for proper webpage to handle and test.
-
Create a custom
404.phppage. This is required to properly handle the redirection to a custom 404 page if the page does not exist, and trying to be accessed.[opc@ih-webserver-01 html]$ sudo nano 404.phpCode for the custom
404.phppage.<?php header("HTTP/1.0 404 Not Found"); ?> <html> <head> <title>404 Error - Page Not Found</title> </head> <body>404 Error - Page Not Found!</body> </html> -
Create a custom
info.phppage.[opc@ih-webserver-01 html]$ sudo nano info.phpCode for
info.phppage.<?php phpinfo(); -
Test the
info.phpwebsite which provides the proof that PHP is working with NGNIX.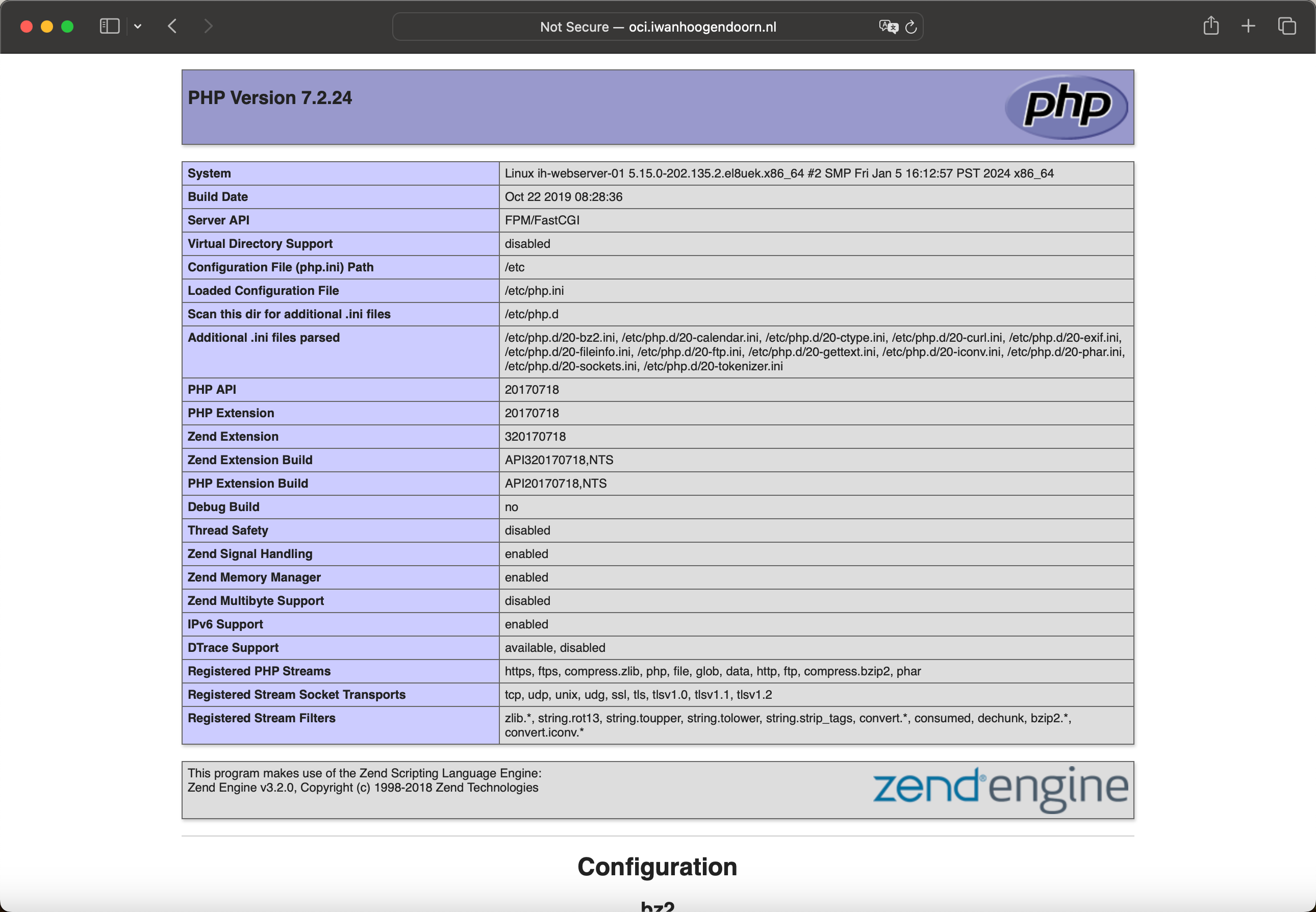
When the website is installed and configured correctly the following webpage is displayed. This page will provide information about your local and remote IPv4 or IPv6 addresses depending on which IP version you use to connect. This page will also tell about the protocol you are using, HTTP or HTTPS.
-
Task 9: Test the Webserver from the Internet
Note: The domains that we have used in this tutorial were created and configured for testing purposes only.
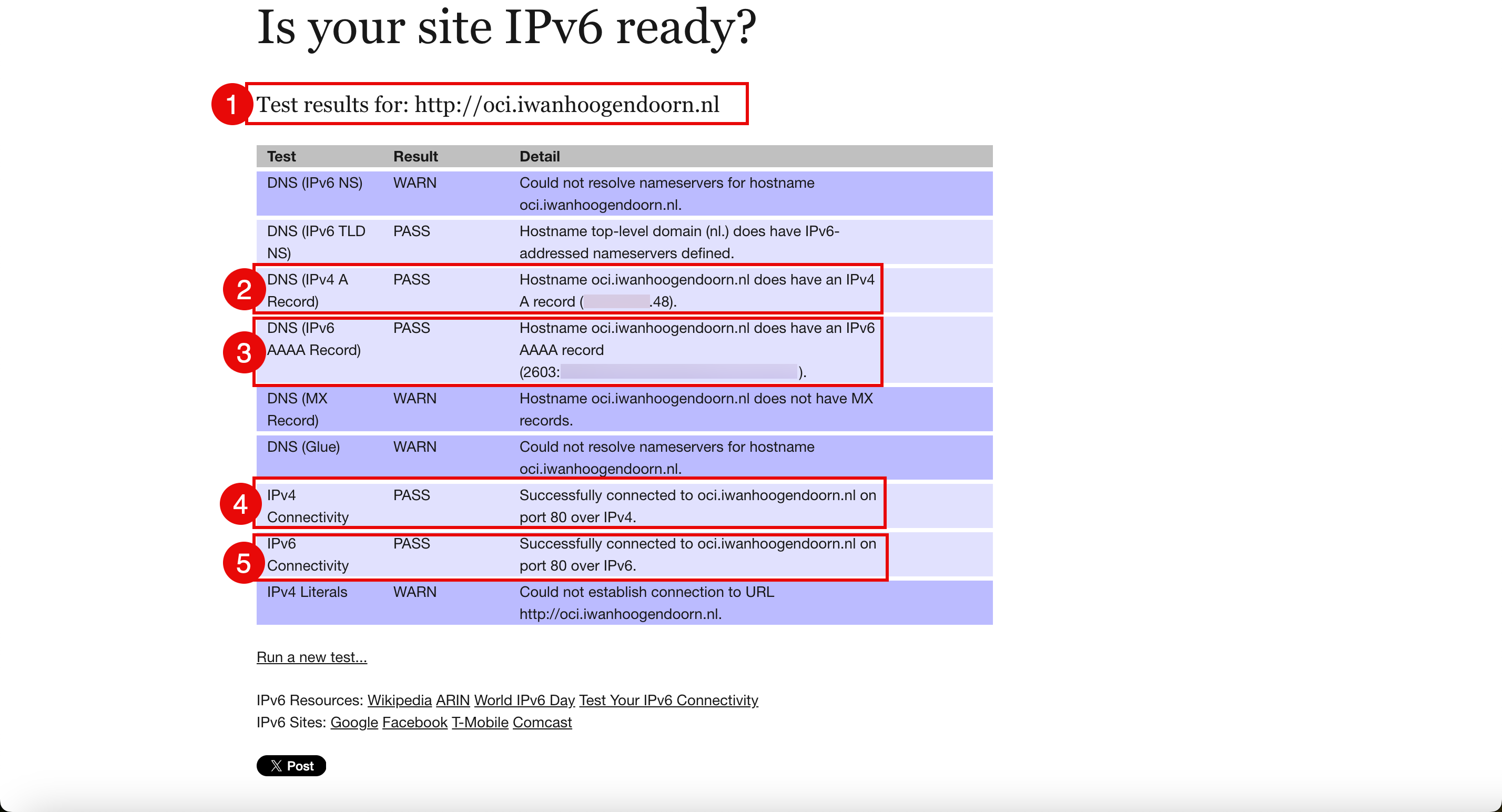
Even though we have already tested the reachability of the website or webserver using multiple methods. We like to use the following website to perform the final test that will test the reachability and the DNS record configuration in one go. Is your site IPv6 ready?
- Use the FQDN oci.iwanhoogendoorn.nl to test with.
- Verify the IPv4 DNS records are configured correctly.
- Verify the IPv6 DNS records are configured correctly.
- Verify the website is reachable on IPv4.
- Verify the website is reachable on IPv6.
Acknowledgments
- Author - Iwan Hoogendoorn (OCI Network Specialist)
More Learning Resources
Explore other labs on docs.oracle.com/learn or access more free learning content on the Oracle Learning YouTube channel. Additionally, visit education.oracle.com/learning-explorer to become an Oracle Learning Explorer.
For product documentation, visit Oracle Help Center.
Use Oracle Cloud Infrastructure to Publish a Webserver Accessible from the Internet with IPv6
F93495-01
February 2024
Copyright © 2024, Oracle and/or its affiliates.