15 Creating Infrastructure for Oracle Identity Governance
A complete Oracle Identity and Access Management uses a split domain deployment, where there is a single domain for Oracle Access Management and a different one for Oracle Identity Governance. You must create a separate infrastructures for Access and Governance.
- Synchronizing the System Clocks
Before you extend the domain to include Oracle Identity Governance, verify that the system clocks on each host computer are synchronized. You can do this by running thedatecommand simultaneously on all the hosts in each cluster. - About the Initial Infrastructure Domain
Before you create the initial Infrastructure domain, be sure to review the following key concepts. - Variables Used When Creating the Infrastructure Domain
As you perform the tasks in this chapter, you reference the directory variables that are listed in this section. - Support for Dynamic Clusters in Infrastructure Domains
Infrastructure domains support two different topologies: static clusters-based topology and dynamic clusters-based topology. When choosing the dynamic cluster topology, there are some differences with respect to the conventional static clusters configuration. - Installing the Oracle Fusion Middleware Infrastructure on OIMHOST1
Use the following sections to install the Oracle Fusion Middleware Infrastructure software in preparation for configuring a new domain for an enterprise deployment. - Installing Oracle Identity Governance for an Enterprise Deployment
The procedure for installing Oracle Identity Governance and the dependant softwares for an enterprise deployment is explained in this section. - Creating the Database Schemas for Oracle Identity Governance
Oracle Fusion Middleware components require the existence of schemas in a database before you configure a Fusion Middleware Infrastructure domain. Install the schemas listed in this topic in a certified database for use with this release of Oracle Fusion Middleware. - Configuring the Oracle Identity Governance Domain
The following topics provide instructions for creating an Oracle Identity Governance domain using the Fusion Middleware Configuration wizard. - Creating Oracle Identity Manager Authenticator
Before you start the domain, you have to run a script which creates the Oracle Identity Manager (OIM) Authenticator in the domain. - Configuring the Domain Directories and Starting the Servers
After the domain is created and the Node Manager is configured, you can then configure the additional domain directories and start the Administration Server and any Managed Servers on the AdminHost. - Configuring Listen Addresses When Using Dynamic Clusters
- Propagating the Domain and Starting the Servers on OIMHOST2
After you start and validate the Administration Server and WLS_WSM1 Managed Server on OIMHOST1, you can then perform the following tasks on OIMHOST2. - Modifying the Upload and Stage Directories to an Absolute Path
- About the Supported Authentication Providers
- Creating a New LDAP Authenticator and Provisioning Enterprise Deployment Users and Group
When you configure an Oracle Fusion Middleware domain, the domain is configured by default to use the WebLogic Server authentication provider (DefaultAuthenticator). However, for an enterprise deployment, Oracle recommends that you use a dedicated, centralized LDAP-compliant authentication provider. - Configuring the WebLogic Proxy Plug-In
- Enabling Exalogic Optimizations
- Backing Up the Configuration
It is an Oracle best practices recommendation to create a backup after you successfully extended a domain or at another logical point. Create a backup after you verify that the installation so far is successful. This is a quick backup for the express purpose of immediate restoration in case of problems in later steps. - Verification of Manual Failover of the Administration Server
Parent topic: Configuring the Enterprise Deployment
Synchronizing the System Clocks
Before you extend the domain to include Oracle Identity Governance, verify that the system clocks on each host computer are synchronized. You can do this by running the date command simultaneously on all the hosts in each cluster.
Alternatively, there are third-party and open-source utilities you can use for this purpose.
Parent topic: Creating Infrastructure for Oracle Identity Governance
About the Initial Infrastructure Domain
Before you create the initial Infrastructure domain, be sure to review the following key concepts.
Parent topic: Creating Infrastructure for Oracle Identity Governance
About the Infrastructure Distribution
You create the initial Infrastructure domain for an enterprise deployment by using the Oracle Fusion Middleware Infrastructure distribution. This distribution contains both the Oracle WebLogic Server software and the Oracle JRF software.
The Oracle JRF software consists of Oracle Web Services Manager, Oracle Application Development Framework (Oracle ADF), Oracle Enterprise Manager Fusion Middleware Control, the Repository Creation Utility (RCU), and other libraries and technologies that are required to support the Oracle Fusion Middleware products.
Note:
The Access infrastructure does not use the Web Services Manager.
Later in this guide, you can then extend the domain to support the Oracle Fusion Middleware products that are required for your enterprise deployment.
See Understanding Oracle Fusion Middleware Infrastructure in Understanding Oracle Fusion Middleware.
Parent topic: About the Initial Infrastructure Domain
Characteristics of the Domain
The following table lists some of the key characteristics of the domain that you are about to create. Reviewing these characteristics helps you to understand the purpose and context of the procedures that are used to configure the domain.
Many of these characteristics are described in more detail in Understanding a Typical Enterprise Deployment.
| Characteristic of the Domain | More Information |
|---|---|
|
Uses a separate virtual IP (VIP) address for the Administration Server. |
Configuration of the Administration Server and Managed Servers Domain Directories |
|
Uses separate domain directories for the Administration Server and the Managed Servers in the domain. |
Configuration of the Administration Server and Managed Servers Domain Directories |
|
Includes a dedicated cluster for Oracle Web Services Manager. |
|
|
Uses a per domain Node Manager configuration. |
About the Node Manager Configuration in a Typical Enterprise Deployment |
|
Requires a separately installed LDAP-based authentication provider. |
Understanding OPSS and Requests to the Authentication and Authorization Stores |
Parent topic: About the Initial Infrastructure Domain
Variables Used When Creating the Infrastructure Domain
As you perform the tasks in this chapter, you reference the directory variables that are listed in this section.
These directory variables are defined in File System and Directory Variables Used in This Guide.
-
ORACLE_HOME
-
ASERVER_HOME
-
MSERVER_HOME
-
APPLICATION_HOME
-
JAVA_HOME
Note:
To simplify, the above variables are used. Depending on the domain you are creating, you must add the prefix to the above variables with the infrastructure you are creating for. For example:
-
For access deployments, use IAD. For example: IAD_ASERVER_HOME
-
For governance, use IGD. For example: IGD_ASERVER_HOME
In addition, you reference the following virtual IP (VIP) addresses and host names that are defined in Physical and Virtual IP Addresses Required by the Enterprise Topology:
-
ADMINVHN
-
OIMHOST1
-
OIMHOST2
-
DBHOST1
-
DBHOST2
-
SCAN Address for the Oracle RAC Database (
DB-SCAN.example.com)
Note:
Depending on the domain you are creating, you must add the prefix to ADMINVHN. For example, IAD_ADMINVHN.
Note:
The instructions in this section use the installation on OIMHOST1 and OIMHOST2 as an example. If you are creating the infrastructure domain for Access, then substitute OAMHOST1 and OAMHOST2 wherever appropriate.
Parent topic: Creating Infrastructure for Oracle Identity Governance
Support for Dynamic Clusters in Infrastructure Domains
Infrastructure domains support two different topologies: static clusters-based topology and dynamic clusters-based topology. When choosing the dynamic cluster topology, there are some differences with respect to the conventional static clusters configuration.
Static clusters, also called configured clusters, are conventional clusters where you manually configure and add each server instance. A dynamic cluster includes a new "server-template" object that is used to define a centralized configuration for all generated (dynamic) server instances. When you create a dynamic cluster, the dynamic servers are preconfigured and automatically generated for you. This feature enables you to scale up the number of server instances in the dynamic cluster when you need additional server capacity. You can simply start the dynamic servers without having to first manually configure and add them to the cluster.
-
The Configuration Wizard process may differ for each case. For example, you should define server templates for dynamic clusters instead of servers.
-
For dynamic clusters, you should perform the server-specific configurations such as setting the listen address, configuring the upload and staging directories, or configuring the keystores in the server template instead of in the server.
-
Service migration is configured in a different way for dynamic clusters. Dynamic clusters do not use migratable targets, instead the JMS resources are targeted to the cluster. Specific procedure for configuring service migration for dynamic clusters is included in this guide.
Mixed clusters (clusters that contains both dynamic and configured server instances) are not supported in the Oracle Identity and Access Management enterprise deployment.
Parent topic: Creating Infrastructure for Oracle Identity Governance
Installing the Oracle Fusion Middleware Infrastructure on OIMHOST1
Use the following sections to install the Oracle Fusion Middleware Infrastructure software in preparation for configuring a new domain for an enterprise deployment.
- Installing a Supported JDK
- Starting the Infrastructure Installer
- Navigating the Infrastructure Installation Screens
- Installing Oracle Fusion Middleware Infrastructure on the Other Host Computers
- Checking the Directory Structure
After you install the Oracle Fusion Middleware Infrastructure and create the Oracle home, you should see the directory and sub-directories listed in this topic. The contents of your installation vary based on the options that you selected during the installation.
Parent topic: Creating Infrastructure for Oracle Identity Governance
Installing a Supported JDK
Oracle Fusion Middleware requires that a certified Java Development Kit (JDK) is installed on your system.
- Locating and Downloading the JDK Software
- Installing the JDK Software
Oracle Fusion Middleware requires you to install a certified Java Development Kit (JDK) on your system.
Locating and Downloading the JDK Software
To find a certified JDK, see the certification document for your release on the Oracle Fusion Middleware Supported System Configurations page.
After you identify the Oracle JDK for the current Oracle Fusion Middleware release, you can download an Oracle JDK from the following location on Oracle Technology Network:
http://www.oracle.com/technetwork/java/index.html
Be sure to navigate to the download for the Java SE JDK.
Parent topic: Installing a Supported JDK
Installing the JDK Software
Oracle Fusion Middleware requires you to install a certified Java Development Kit (JDK) on your system.
You must install the JDK in the following locations:
-
On the shared storage device, install the JDK in the
/u01/oracle/products/jdkdirectory. The JDK will be accessible from each of the application tier host computers. -
On the local storage device for each of the Web tier host computers. The Web tier host computers, which reside in the DMZ, do not necessarily have access to the shared storage on the application tier.
-
On the local storage device for each of the directory tier host computers, in case of the directory hosts not utilizing the shared storage.
For more information about the recommended location for the JDK software, see Understanding the Recommended Directory Structure for an Enterprise Deployment.
Parent topic: Installing a Supported JDK
Starting the Infrastructure Installer
To start the installation program, perform the following steps.
When the installation program appears, you are ready to begin the installation. See Navigating the Installation Screens for a description of each installation program screen.
Navigating the Infrastructure Installation Screens
The installation program displays a series of screens, in the order listed in the following table.
If you need additional help with any of the installation screens, click the screen name or click the Help button on the screen.
Table 15-1 Navigating the Infrastructure Installation Screens
| Screen | Description |
|---|---|
|
On UNIX operating systems, this screen appears if you are installing any Oracle product on this host for the first time. Specify the location where you want to create your central inventory. Ensure that the operating system group name selected on this screen has write permissions to the central inventory location. See Understanding the Oracle Central Inventory in Installing Software with the Oracle Universal Installer. Note: Oracle recommends that you configure the central inventory directory on the products shared volume. Example: You may also need to execute the |
|
|
This screen introduces you to the product installer. |
|
|
Use this screen to search My Oracle Support automatically for available patches or automatically search a local directory for patches that you have already downloaded for your organization. |
|
|
Use this screen to specify the location of your Oracle home directory. For the purposes of an enterprise deployment, enter the value of the IGD_ORACLE_HOME variable listed in Table 9-2. |
|
|
Use this screen to select the type of installation and as a consequence, the products and feature sets that you want to install. For this topology, select Fusion Middleware Infrastructure. Note: The topology in this document does not include server examples. Oracle strongly recommends that you do not install the examples into a production environment. |
|
|
This screen verifies that your system meets the minimum requirements. If there are any warning or error messages, refer to the Oracle Fusion Middleware System Requirements and Specifications document on the Oracle Technology Network (OTN). |
|
|
If you already have an Oracle Support account, use this screen to indicate how you would like to receive security updates. If you do not have one and are sure that you want to skip this step, clear the check box and verify your selection in the follow-up dialog box. |
|
|
Use this screen to verify the installation options that you have selected. If you want to save these options to a response file, click Save Response File and provide the location and name of the response file. Response files can be used later in a silent installation situation. For more information about silent or command-line installation, see Using the Oracle Universal Installer in Silent Mode in Installing Software with the Oracle Universal Installer. |
|
|
This screen allows you to see the progress of the installation. |
|
|
This screen appears when the installation is complete. Review the information on this screen, then click Finish to dismiss the installer. |
Installing Oracle Fusion Middleware Infrastructure on the Other Host Computers
If you have configured a separate shared storage volume or partition for secondary hosts, then you must install the Infrastructure on one of those hosts.
See Shared Storage Recommendations When Installing and Configuring an Enterprise Deployment.
To install the software on the other host computers in the topology, log in to each host, and use the instructions in Starting the Infrastructure Installer and Navigating the Infrastructure Installation Screens to create the Oracle home on the appropriate storage device.
Checking the Directory Structure
After you install the Oracle Fusion Middleware Infrastructure and create the Oracle home, you should see the directory and sub-directories listed in this topic. The contents of your installation vary based on the options that you selected during the installation.
To check the directory structure:
Installing Oracle Identity Governance for an Enterprise Deployment
The procedure for installing Oracle Identity Governance and the dependant softwares for an enterprise deployment is explained in this section.
- Starting the SOA Suite Installer on OIMHOST1
- Navigating the Oracle SOA Suite Installation Screens
- Starting the Oracle Identity and Access Management Installer
- Navigating the Oracle Identity and Access Management Installation Screens
- Verifying the Installation
- Downloading the Oracle Connector Bundle
Download the Oracle Connector bundle using the instructions in this section. - Installing the Oracle Identity Governance Connector
After you download the Oracle Connector for LDAP, install it into the ORACLE_HOME directory.
Parent topic: Creating Infrastructure for Oracle Identity Governance
Starting the SOA Suite Installer on OIMHOST1
To start the installation program:
When the installation program appears, you are ready to begin the installation.
Navigating the Oracle SOA Suite Installation Screens
The installation program displays a series of screens, in the order listed in the following table.
If you need additional help with any of the installation screens, click the screen name.
| Screen | Description |
|---|---|
|
This screen introduces you to the product installer. |
|
|
Use this screen to automatically search My Oracle Support for available patches or automatically search a local directory for patches that you’ve already downloaded for your organization. |
|
|
For Oracle Identity Governance enter IGD_ORACLE_HOME. For more information about Oracle Fusion Middleware directory structure, see Selecting Directories for Installation and Configuration in Planning an Installation of Oracle Fusion Middleware. |
|
|
Use this screen to select the type of installation and consequently, the products and feature sets you want to install.
|
|
|
This screen verifies that your system meets the minimum necessary requirements. If there are any warning or error messages, you can refer to one of the documents in the Roadmap for Verifying Your System Environment section in Installing and Configuring the Oracle Fusion Middleware Infrastructure. |
|
|
Use this screen to verify the installation options you selected. Click Install to begin the installation. |
|
|
This screen allows you to see the progress of the installation. Click Next when the progress bar reaches 100% complete. |
|
|
Review the information on this screen, then click Finish to dismiss the installer. |
Starting the Oracle Identity and Access Management Installer
To start the installation program:
When the installation program appears, you are ready to begin the installation.
Navigating the Oracle Identity and Access Management Installation Screens
The installation program displays a series of screens, in the order listed in the following table.
If you need additional help with any of the installation screens, click the screen name.
| Screen | Description |
|---|---|
|
This screen introduces you to the product installer. |
|
|
Use this screen to automatically search My Oracle Support for available patches or automatically search a local directory for patches that you’ve already downloaded for your organization. |
|
|
Use this screen to specify the location of your Oracle home directory. For Oracle Identity Governance, this must be set to For more information about Oracle Fusion Middleware directory structure, see Selecting Directories for Installation and Configuration in Planning an Installation of Oracle Fusion Middleware. |
|
|
Use this screen to choose the type of installation you wish to deploy. You have two options:
|
|
|
This screen verifies that your system meets the minimum necessary requirements. If there are any warning or error messages, you can refer to one of the documents in the Roadmap for Verifying Your System Environment section in Installing and Configuring the Oracle Fusion Middleware Infrastructure. |
|
|
Use this screen to verify the installation options you selected. Click Install to begin the installation. |
|
|
This screen allows you to see the progress of the installation. Click Next when the progress bar reaches 100% complete. |
|
|
Review the information on this screen, then click Finish to dismiss the installer. |
Verifying the Installation
After you complete the installation, you can verify it by successfully completing the following tasks.
Reviewing the Installation Log Files
Review the contents of the installation log files to make sure that no problems were encountered. For a description of the log files and where to find them, see Understanding Installation Log Files in Installing Software with the Oracle Universal Installer.
Parent topic: Verifying the Installation
Checking the Directory Structure
The contents of your installation vary based on the options that you select during the installation.
The addition of Oracle Identity Governance adds the following directory and sub-directories. Use the ls --format=single-column command to verify the directory structure.
IGD_ORACLE_HOME/
OPatch
cfgtoollogs
coherence
em
idm
inventory
jdeveloper
mft
oep
oraInst.loc
oracle_common
osb
oui
soa
wlserveridm/ clone common connectors designconsole idmdiag idmtools jlib libovd mbeans modules oam oic opam-connectors plugins remote_manager schema server upgrade
For more information about the directory structure you should see after installation, see What are the Key Oracle Fusion Middleware Directories? in Understanding Oracle Fusion Middleware.
Parent topic: Verifying the Installation
Viewing the Contents of Your Oracle Home
You can also view the contents of your Oracle home by using the viewInventory script. See Viewing the contents of an Oracle home in Installing Software with the Oracle Universal Installer.
Parent topic: Verifying the Installation
Downloading the Oracle Connector Bundle
Download the Oracle Connector bundle using the instructions in this section.
Download the Oracle Connector bundle from the following location:
http://www.oracle.com/technetwork/middleware/id-mgmt/downloads/connectors-101674.html
Copy the connector bundle for Oracle Internet Directory (it covers OUD as well) to the following directory:
IGD_ORACLE_HOME/idm/server/ConnectorDefaultDirectoryCreating the Database Schemas for Oracle Identity Governance
Oracle Fusion Middleware components require the existence of schemas in a database before you configure a Fusion Middleware Infrastructure domain. Install the schemas listed in this topic in a certified database for use with this release of Oracle Fusion Middleware.
-
Oracle Identity Manager
This automatically selects Oracle SOA Suite schemas along with the following ones:
-
Metadata Services (MDS)
-
Audit Services (IAU)
-
Audit Services Append (IAU_APPEND)
-
Audit Services Viewer (IAU_VIEWER)
-
Oracle Platform Security Services (OPSS)
-
User Messaging Service (UMS)
-
WebLogic Services (WLS)
-
Common Infrastructure Services (STB)
-
Use the Repository Creation Utility (RCU) to create the schemas. This utility is installed in the Oracle home for each Oracle Fusion Middleware product. For more information about RCU and how the schemas are created and stored in the database, see Preparing for Schema Creation in Creating Schemas with the Repository Creation Utility.
Complete the following steps to install the required schemas:
- Installing and Configuring a Certified Database
- Starting the Repository Creation Utility (RCU)
- Navigating the RCU Screens to Create the Schemas
- Verifying Schema Access
- Configuring OIM Schemas for Transactional Recovery
Parent topic: Creating Infrastructure for Oracle Identity Governance
Installing and Configuring a Certified Database
Make sure that you have installed and configured a certified database, and that the database is up and running.
See the Preparing the Database for an Enterprise Deployment.
Navigating the RCU Screens to Create the Schemas
Schema creation involves the following tasks:
- Task 1 Introducing RCU
-
Review the Welcome screen and verify the version number for RCU. Click Next to begin.
- Task 2 Selecting a Method of Schema Creation
-
If you have the necessary permission and privileges to perform DBA activities on your database, select System Load and Product Load. This procedure assumes that you have the necessary privileges.
If you do not have the necessary permission or privileges to perform DBA activities in the database, you must select Prepare Scripts for System Load on this screen. This option will generate a SQL script, which can be provided to your database administrator to create the required schema. See Understanding System Load and Product Load in Creating Schemas with the Repository Creation Utility.
- Task 3 Providing Database Connection Details
-
Provide the database connection details for RCU to connect to your database.
-
In the Host Name field, enter the SCAN address of the Oracle RAC Database.
-
Enter the Port number of the RAC database scan listener, for example 1521.
-
Enter the RAC Service Name of the database.
-
Enter the User Name of a user that has permissions to create schemas and schema objects, for example SYS.
-
Enter the Password of the user name that you provided in step 4.
-
If you have selected the SYS user, ensure that you set the role to SYSDBA.
-
Click Next to proceed, then click OK on the dialog window confirming that connection to the database was successful.
Tip:
For more information about the options on this screen, see Database Connection Details in Creating Schemas with the Repository Creation Utility.
-
- Task 4 Specifying a Custom Prefix and Selecting Schemas
-
-
Specify the custom prefix you want to use to identify the Oracle Fusion Middleware schemas.
The custom prefix is used to logically group these schemas together for use in this domain; you must create a unique set of schemas for each domain as schema sharing across domains is not supported.
Tip:
Make a note of the custom prefix you choose to enter here; you will need this later, during the domain creation process.
For more information about custom prefixes, see Understanding Custom Prefixes in Creating Schemas with the Repository Creation Utility.
For more information about how to organize your schemas in a multi-domain environment, see Planning Your Schema Creation in Creating Schemas with the Repository Creation Utility.
-
Expand the group IDM Schemas, and then select the Oracle Identity Manager schema. All the relative schemas will be selected:
-
Common infrastructure Services
-
Oracle Platform Security Services
-
User Messaging Service
-
Audit Services
-
Audit Services Append
-
Audit Services Viewer
-
Metadata Services
-
SOA Infrastructure
-
Weblogic Services
-
There are two mandatory schemas that are selected by default. You cannot deselect them: Common Infrastructure Services (the STB schema) and WebLogic Services (the WLS schema). The Common Infrastructure Services schema enables you to retrieve information from RCU during domain configuration. See Understanding the Service Table Schema in Creating Schemas with the Repository Creation Utility.
Tip:
For more information about how to organize your schemas in a multi-domain environment, see Planning Your Schema Creation in Creating Schemas with the Repository Creation Utility.
Click Next to proceed, then click OK on the dialog window confirming that prerequisite checking for schema creation was successful.
-
- Task 5 Specifying Schema Passwords
-
Specify how you want to set the schema passwords on your database, then specify and confirm your passwords. Ensure that the complexity of the passwords meet the database security requirements before you continue. RCU will proceed at this point even if you do not meet the password polices. Hence, perform this check outside RCU itself.
Tip:
You must make a note of the passwords you set on this screen; you will need them later on during the domain creation process.
- Task 6 Verifying the Tablespaces for the Required Schemas
-
You can accept the default settings on the remaining screens, or you can customize how RCU creates and uses the required tablespaces for the Oracle Fusion Middleware schemas.
Note:
You can configure a Fusion Middleware component to use JDBC stores for JMS servers and Transaction Logs, by using the Configuration Wizard. These JDBC stores are placed in the Weblogic Services component tablespace. If your environment expects to have a high level of transactions and/or JMS activity, you can increase the default size of the <PREFIX>_WLS tablespace to better suit the environment load.
Click Next to continue, and then click OK on the dialog window to confirm the tablespace creation.
For more information about RCU and its features and concepts, see About the Repository Creation Utility in Creating Schemas with the Repository Creation Utility.
- Task 7 Creating Schemas
-
Review the summary of the schemas to be loaded and click Create to complete schema creation.
Note:
If failures occurred, review the listed log files to identify the root cause, resolve the defects, and then use RCU to drop and re-create the schemas before you continue.
- Task 8 Reviewing Completion Summary and Completing RCU Execution
-
When you reach the Completion Summary screen, verify that all schema creations have been completed successfully, and then click Close to dismiss RCU.
Verifying Schema Access
Verify schema access by connecting to the database as the new schema users created by the RCU. Use SQL*Plus or another utility to connect, and provide the appropriate schema names and passwords entered in the RCU.
For example:
./sqlplus
SQL*Plus: Release 12.1.0.2.0 Production on Wed Aug 31 05:41:31 2016
Copyright (c) 1982, 2014, Oracle. All rights reserved.
Enter user-name: OIM
Enter password: OIM_schema_password
Connected to:
Oracle Database 12c Enterprise Edition Release 12.1.0.2.0 - 64bit Production
With the Partitioning, Real Application Clusters, Automatic Storage Management, OLAP, Advanced Analytics and Real Application Testing options
SQL>Configuring OIM Schemas for Transactional Recovery
After you have installed the Oracle Identity Governance schemas successfully, use the procedure in this section to configure the schemas for transactional recovery.
This procedure sets the appropriate database privileges so that the Oracle WebLogic Server transaction manager can query the schemas for transaction state information and issue the appropriate commands, such as commit and rollback, during recovery of in-flight transactions after a WebLogic Server is unexpectedly unavailable.
These privileges should be granted to the owner of the OIM schema, which you defined when you created the schemas with the Repository Creation Utility.
To configure the OIM schemas for transactional recovery privileges:
Configuring the Oracle Identity Governance Domain
The following topics provide instructions for creating an Oracle Identity Governance domain using the Fusion Middleware Configuration wizard.
For more information on the other methods that are available for creating a domain, see Additional Tools for Creating, Extending, and Managing WebLogic Domains in Creating WebLogic Domains Using the Configuration Wizard.
- Starting the Configuration Wizard
- Navigating the Configuration Wizard Screens to Configure the Oracle Identity GovernanceDomain
Parent topic: Creating Infrastructure for Oracle Identity Governance
Starting the Configuration Wizard
To begin domain configuration, run the following command in the Oracle Fusion Middleware Oracle home.
IAD_ORACLE_HOME/oracle_common/common/bin/config.shParent topic: Configuring the Oracle Identity Governance Domain
Navigating the Configuration Wizard Screens to Configure the Oracle Identity GovernanceDomain
Follow the instructions in the following sections to create and configure the domain for the topology, with static or dynamic clusters.
Parent topic: Configuring the Oracle Identity Governance Domain
Creating the Domain with Static Clusters
Follow the instructions in this section to create and configure the domain for the topology.
Domain creation and configuration includes the following tasks.- Task 1 Selecting the Domain Type and Domain Home Location
-
On the Configuration Type screen, select Create a new domain.
In the Domain Location field, specify the value of the IGD_ASERVER_HOME variable, as defined in File System and Directory Variables Used in This Guide.
Tip:
More information about the other options on this screen of the Configuration Wizard, see Configuration Type in Creating WebLogic Domains Using the Configuration Wizard.
Click Next.
- Task 2 Selecting the Configuration Templates
-
Select Oracle Identity Manager - 12.2.1.3.0 [idm], the following template will be automatically selected:
-
Oracle SOA Suite -12.2.1.3.0[soa]
-
Oracle Enterprise Manager - 12.2.1.3.0[em]
-
Oracle WSM Policy Manager - 12.2.1.3.0[oracle_common]
-
Oracle JRF - 12.2.1.3.0[oracle_common]
-
WebLogic Coherence Cluster Extension - 12.2.1.3.0[wlserver]
Tip:
More information about the options on this screen can be found in Templates in Creating WebLogic Domains Using the Configuration Wizard.
Click Next.
-
- Task 3 Configuring High Availability Options
-
This screen appears for the first time when you create a cluster that uses Automatic Service Migration or JDBC stores or both. After you select HA Options for a cluster, all subsequent clusters that are added to the domain by using the Configuration Wizard, automatically apply HA options (that is, the Configuration Wizard creates the JDBC stores and configures ASM for them).
Note:
Oracle recommends that you use JDBC stores, which leverage the consistency, data protection, and high availability features of an oracle database and makes resources available for all the servers in the cluster. So, the Configuration Wizard steps assume that the JDBC persistent stores are used along with Automatic Service Migration.
If, for any reason, you want to use Files Stores, you can retain the default values for TLOGs and JMS persistent store options in this screen and configure them in a shared location later. See Configuring TLOGs File Persistent Store in a Shared Folder. Shared location is required to resume JMS and HA in a failover scenario.
You can also configure TLOGs and JMS persistent stores manually in a post step. For information about the differences between JDBC and Files Stores, and for specific instructions to configure them manually, see JDBC Persistent Stores vs. File Persistent Stores.
On the High Availability Options screen:
-
Select Enable Automatic Service Migration with Database Leasing.
-
Set JTA Transaction Log Persistence to JDBC TLog Store.
-
Set JMS Server Persistence to JMS JDBC Store.
-
Click Next.
-
- Task 4 Selecting the Application Home Location
-
On the Application Location screen, specify the value of the APPLICATION_HOME variable, as defined in File System and Directory Variables Used in This Guide.
Tip:
More information about the options on this screen can be found in Application Location in Creating WebLogic Domains Using the Configuration Wizard.
Click Next.
- Task 5 Configuring the Administrator Account
-
On the Administrator Account screen, specify the user name and password for the default WebLogic Administrator account for the domain.
Make a note of the user name and password specified on this screen; you will need these credentials later to boot and connect to the domain's Administration Server.
Click Next.
- Task 6 Specifying the Domain Mode and JDK
-
On the Domain Mode and JDK screen:
-
Select Production in the Domain Mode field.
-
Select the Oracle Hotspot JDK in the JDK field.
Selecting Production Mode on this screen gives your environment a higher degree of security, requiring a user name and password to deploy applications and to start the Administration Server.
Tip:
More information about the options on this screen, including the differences between development mode and production mode, can be found in Domain Mode and JDK in Creating WebLogic Domains Using the Configuration Wizard.
In production mode, a boot identity file can be created to bypass the need to provide a user name and password when starting the Administration Server. See Creating the boot.properties File.
Click Next.
-
- Task 7 Specifying the Database Configuration Type
-
On the Database Configuration Type screen:
-
Select RCU Data to activate the fields on this screen.
The RCU Data option instructs the Configuration Wizard to connect to the database and Service Table (STB) schema to automatically retrieve schema information for the schemas needed to configure the domain.
-
Verify that Vendor is Oracle and Driver is *Oracle's Driver (Thin) for Service Connections; Versions: Any.
-
Verify that Connection Parameters is selected.
Note:
If you choose to select Manual Configuration on this screen, you will have to manually fill in the parameters for your schema on the JDBC Component Schema screen.
After you select RCU Data, fill in the fields as shown in the following table:
Field Description Host Name
Enter the Single Client Access Name (SCAN) Address for the Oracle RAC database, which you entered in the Enterprise Deployment Workbook.
For information about the Enterprise Deployment Workbook, see Using the Enterprise Deployment Workbook.
DBMS/Service
Enter the service name for the Oracle RAC database appropriate for this domain where you will install the product schemas. For example:
iamedg.example.comSpecify the service name based on the value configured earlier in the Preparing the Database for an Enterprise Deployment section.
Port
Enter the port number on which the database listens. For example,
1521.Schema Owner
Schema Password
Enter the user name and password for connecting to the database's Service Table schema.
This is the schema user name and password that was specified for the Service Table component on the "Schema Passwords" screen in RCU (see Creating the Database Schemas).
The default user name is
prefix_STB, whereprefixis the custom prefix that you defined in RCU.Click Get RCU Configuration when you are finished specifying the database connection information. The following output in the Connection Result Log indicates that the operating succeeded:
Connecting to the database server...OK Retrieving schema data from database server...OK Binding local schema components with retrieved data...OK Successfully Done.
Click Next if the connection to the database is successful.
Tip:
More information about the RCU Data option can be found in Understanding the Service Table Schema in Creating Schemas with the Repository Creation Utility.
More information about the other options on this screen can be found in Datasource Defaults in Creating WebLogic Domains Using the Configuration Wizard.
-
- Task 8 Specifying JDBC Component Schema Information
-
Verify that the values on the JDBC Component Schema screen are correct for all schemas.
The schema table should be populated, because you selected Get RCU Data on the previous screen. As a result, the Configuration Wizard locates the database connection values for all the schemas required for this domain.
At this point, the values are configured to connect to a single-instance database. However, for an enterprise deployment, you should use a highly available Real Application Clusters (RAC) database, as described in Preparing the Database for an Enterprise Deployment.
In addition, Oracle recommends that you use an Active GridLink datasource for each of the component schemas. For more information about the advantages of using GridLink data sources to connect to a RAC database, see Database Considerations in the High Availability Guide.
To convert the data sources to GridLink:
-
Select all the schemas by selecting the checkbox at in the first header row of the schema table.
-
Click Convert to GridLink and click Next.
-
- Task 9 Providing the GridLink Oracle RAC Database Connection Details
-
On the GridLink Oracle RAC Component Schema screen, provide the information required to connect to the RAC database and component schemas, as shown in following table.
Element Description and Recommended Value SCAN, Host Name, and Port
Select the SCAN check box.
In the Host Name field, enter the Single Client Access Name (SCAN) Address for the Oracle RAC database.
In the Port field, enter the SCAN listening port for the database (for example,
1521)ONS Host and Port
In the ONS Host field, enter the SCAN address for the Oracle RAC database.
In the Port field, enter the ONS Remote port (typically,
6200).Enable Fan
Verify that the Enable Fan check box is selected, so the database can receive and process FAN events.
For more information about specifying the information on this screen, as well as information about how to identify the correct SCAN address, see Configuring Active GridLink Data Sources with Oracle RAC in the High Availability Guide.
You can also click Help to display a brief description of each field on the screen.
Click Next.
- Task 10 Testing the JDBC Connections
-
Use the JDBC Component Schema Test screen to test the data source connections you have just configured.
A green check mark in the Status column indicates a successful test. If you encounter any issues, see the error message in the Connection Result Log section of the screen, fix the problem, then try to test the connection again.
Tip:
More information about the other options on this screen can be found in Test Component Schema in Creating WebLogic Domains Using the Configuration Wizard
Click Next.
- Task 11 Entering Credentials
-
Enter the credentials you wish to use for the Oracle Identity Governance components. You have the choice of choosing both a username and a password for the various objects.
-
keystore: Set the username to keystore and the password to the password you wish to use for all automatically created keystores.
-
OIMSchemaPassword: Set the username to the OIM schema which you created in the earlier sections. For example,
IGD_OIM(username) and its associated password. -
Sysadmin: This is the administrative user you will use for OIM. This is typically
xelsysadm, but can be anything. Set the password to a value you wish to use for this account. -
WebLogicAdminKey: This is the domain admin username and password. For example,
weblogic.
Click Next.
-
- Task 12 Keystore
-
Use this screen to specify details about the keystore to be used in the domain.
For a typical enterprise deployment, you can leave the default values.
See Keystore in Creating WebLogic Domains Using the Configuration Wizard.
Click Next.
- Task 13 Selecting Advanced Configuration
-
Note:
This is not required for Access infrastructure.
To complete domain configuration for the topology, select the following options on the Advanced Configuration screen:
-
Administration Server
This is required to properly configure the listen address of the Administration Server.
-
Node Manager
This is required to configure Node Manager.
-
Topology
This is required to add, delete, or modify the Settings for Server Templates, Managed Servers, Clusters, Virtual Targets, and Coherence.
-
Domain Frontend Host Capture:
This allows you to specify the public entry point for OIM.
Note:
When using the Advanced Configuration screen in the Configuration Wizard, if any of the above options are not available on the screen, then return to the Templates screen, and be sure you selected the required templates for this topology.
Click Next.
-
- Task 14 Configuring the Administration Server Listen Address
-
On the Administration Server screen:
-
In the Server Name field, retain the default value - AdminServer.
-
In the Listen Address field, enter the virtual host name that corresponds to the VIP of the ADMINVHN that you procured in Procuring Resources for an Enterprise Deployment and enabled in Preparing the Host Computers for an Enterprise Deployment.
For more information on the reasons for using the ADMINVHN virtual host, see Reserving the Required IP Addresses for an Enterprise Deployment.
-
In the Listen Port field, enter the port number to access the administration server. This guide recommends you to use the default port
7101for Governance.Leave the other fields at their default values. In particular, be sure that no server groups are assigned to the Administration Server.
Click Next.
-
- Task 15 Configuring Node Manager
-
Select Per Domain Default Location as the Node Manager type, then specify the following Node Manager credentials you will use to connect to the Node Manager:
-
Username: This is the user name used to connect to the Node Manager. For example,
admin. -
Password and Confirm Password: Enter the password you wish to associate with the Node Manager username.
Tip:
For more information about the options on this screen, see Node Manager in Creating WebLogic Domains Using the Configuration Wizard.
For more information about per domain and per host Node Manager implementations, see About the Node Manager Configuration in a Typical Enterprise Deployment.
For information about Node Manager configurations, see Configuring Node Manager on Multiple Machines in Administering Node Manager for Oracle WebLogic Server.
Click Next.
-
- Task 16 Configuring Managed Servers
-
Use the Managed Servers screen to create two new Managed Servers:
-
Click the Add button to create a new Managed Server.
-
Specify
WLS_WSM1in the Server name column. -
In the Listen Address column, enter OIMHOST1.
Be sure to enter the host name that corresponds to OIMHOST1; do not use the IP address.
-
In the Listen Port column, enter
WSM_PORT – 7010. -
In the Server Groups drop-down list, select JRF-MAN-SVR and WSMPM-MAN-SVR.
These server groups ensure that the Oracle JRF and Oracle Web Services Manager (OWSM) services are targeted to the Managed Servers that you are creating.
Server groups target Fusion Middleware applications and services to one or more servers by mapping defined groups of application services to each defined server group. Any application services that are mapped to a given server group are automatically targeted to all servers that are assigned to that group. See Application Service Groups, Server Groups, and Application Service Mappings in Domain Template Reference.
Note:
Nonce caching for Oracle Web Services is initialized automatically by the WSM-CACHE-SVR server group and is suitable for most custom applications. This initialization is automatically performed in SOA, OSB, and other FMW servers that run JRF and create a coherence cluster. Nonce is a unique number that can be used only once in a SOAP request and is used to prevent replay attacks. Nonce caching naturally scales with the number of added Managed Servers that run Web service applications.
For information about advanced caching configurations, see Caching the Nonce with Oracle Coherence in Securing Web Services and Managing Policies with Oracle Web Services Manager, which provides additional guidance for the use of nonce caching and the WSM-CACHE-SVR server-group in custom WLS servers.
-
Repeat this process to create a second Managed Server named
WLS_WSM2.For the Listen Address, enter OIMHOST2. For the Listen Port, enter 7010. Apply the same server groups that you applied to the first managed server to the WLS_WSM2.
The Managed Server names suggested in this procedure (WLS_WSM1 and WLS_WSM2) are referenced throughout this document; if you choose different names then be sure to replace them as needed.
On the Managed Servers screen, a new Managed Server for Oracle SOA Suite and Oracle Identity Manger appears in the list of servers. This server was created automatically by the Oracle SOA Suite configuration template you selected in Table 9-3.
Perform the following tasks to modify the default Oracle SOA Suite and Oracle Identity Manager Managed Server and create a second Managed Server:
-
Rename the default Managed Server to
oim_server1toWLS_OIM1.Rename the default Managed Server
soa_server1toWLS_SOA1. -
Click Add to create a new Oracle Identity Governance Managed Server, and name it
WLS_OIM2.Tip:
The server names recommended here will be used throughout this document; if you choose different names, be sure to replace them as needed.
-
Click Add to create a new Oracle SOA Suite Managed Server, and name it
WLS_SOA2. -
Use the information in Oracle Identity Governance Managed Server Details to fill in the rest of the columns for each Oracle Identity Governance Managed Server.
For more information about the options on the Managed Server screen, see Managed Servers in Creating WebLogic Domains Using the Configuration Wizard.
Server Name Listen Address Listen Port Enable SSL SSL Listen Port Server Groups WLS_OIM1
OIMHOST1
14000
No
Disabled
OIM-MGD-SVRS
WLS_OIM2
OIMHOST2
14000
No
Disabled
OIM-MGD-SVRS
WLS_SOA1
OIMHOST1
8001
No
Disabled
SOA-MGD-SVRS-ONLY
WLS_SOA2
OIMHOST2
8001
No
Disabled
SOA-MGD-SVRS-ONLY
Click Next.
-
- Task 17 Configuring a Cluster
-
In this task, you create a cluster for each set of Managed Servers. You can then target the Oracle Identity Governance and Oracle SOA Suite components to the relevant cluster.
Create the following clusters:
-
OIM_Cluster
-
SOA_Cluster
-
WSM-PM_Cluster
Use the Clusters screen to create a new cluster:
-
Click the Add button.
-
Specify the cluster name in the Cluster Name field.
-
From the Dynamic Server Groups drop-down list, select
Unspecified. -
Repeat the steps to create all of the clusters.
Note:
By default, server instances in a cluster communicate with one another using unicast. If you want to change your cluster communications to use multicast, refer to Considerations for Choosing Unicast or Multicast in Administering Clusters for Oracle WebLogic Server.
Click Next.
For more information about the options on this screen, see Clusters in Creating WebLogic Domains Using the Configuration Wizard.
-
- Task 18 Assigning Server Templates
-
Click Next .
- Task 19 Configuring Dynamic Servers
-
Verify that all dynamic server options are disabled for clusters that are to remain as static clusters.
-
Confirm that the Dynamic Cluster, Calculated Listen Port, and Calculated Machine Names checkboxes on this screen are unchecked.
-
Confirm the Server Template selection is Unspecified.
-
Click Next.
Note:
This screen will not be displayed if you are creating the Access Infrastructure. -
- Task 20 Assigning Managed Servers to the Cluster
-
Use the Assign Servers to Clusters screen to assign your managed servers to the clusters you have just created. At the end of this you will have the following assignments:
Cluster Managed Servers OIM_Cluster
WLS_OIM1
WLS_OIM2
SOA_Cluster
WLS_SOA1
WLS_SOA2
WSM-PM_Cluster
WLS_WSM1
WLS_WSM2
-
In the Clusters pane, select the cluster to which you want to assign the servers.
-
In the Servers pane, assign the Managed Servers to the cluster as in the table above, using one of the following methods:
-
Click on the Managed Server to select it, and then click on the right arrow to move it beneath the selected cluster in the Clusters pane.
-
Double-click on the Managed Server to move it beneath the selected cluster in the clusters pane.
-
-
Repeat to assign each of the Managed Server to the respective cluster.
-
Click Next.
For more information about the options on this screen, see Assign Servers to Clusters in Creating WebLogic Domains Using the Configuration Wizard.
-
- Task 21 Configuring Coherence Clusters
-
Use the Coherence Clusters screen to configure the Coherence cluster that is automatically added to the domain.
In the Cluster Listen Port, enter
9991.Note:
For Coherence licensing information, Oracle Coherence Products in Oracle Fusion Middleware Licensing Information User Manual.
Click Next.
- Task 22 Creating Machines
-
Use the Machines screen to create new machines in the domain. A machine is required in order for the Node Manager to be able to start and stop the servers.
You must create a machine even if your topology contains just the Administration Server.
-
Select the Unix Machine tab.
-
Click the Add button to create new UNIX machines.
Use the values in Values to Use When Creating Unix Machines to define the Name and Node Manager Listen Address of each machine.
-
Verify the port in the Node Manager Listen Port field.
The port number
5556, shown in this example, may be referenced by other examples in the documentation. Replace this port number with your own port number as needed.
Table 15-2 Values to Use When Creating Unix Machines
Name Node Manager Listen Address Node Manager Listen Port ADMINHOST
Enter the value of the ADMINVHN variable.
5556
OIMHOST1
The value of the OIMHOST1 host name variable or OIMHOST1 alias. For example,
OIMHOST1.example.com.5556
OIMHOST2
The value of the OIMHOST2 host name variable or OIMHOST2 alias. For example,
OIMHOST2.example.com.5556
Note:
If you are installing OIM on the same host as Oracle Access Management (OAM), ensure that the Node Manager ports are unique to each deployment.Tip:
More information about the options on this screen can be found in Machines in Creating WebLogic Domains Using the Configuration Wizard.
Click Next.
-
- Task 23 Assigning Servers to Machines
-
Use the Assign Servers to Machines screen to assign the Oracle Identity Governance Managed Servers to the corresponding machines in the domain.
Assign the machines as shown in the following table:
Servers Machines AdminHost AdminServer WLS_OIM1
WLS_SOA1
WLS_WSM1
OIMHOST1
WLS_OIM2
WLS_SOA2
WLS_WSM2
OIMHOST2
-
In the Machines pane, select the machine to which you want to assign the servers.
-
In the Servers pane, assign the Managed Servers to the machine as in the table above, using one of the following methods:
-
Click on the Managed Server to select it, and then click on the right arrow to move it beneath the selected machines in the machines pane.
-
Double-click on the Managed Server to move it beneath the selected machine in the machines pane.
-
-
Repeat to assign each of the Managed Server to the respective machine.
-
Click Next.
For more information about the options on this screen, see Assign Servers to Machines in Creating WebLogic Domains Using the Configuration Wizard.
-
- Task 24 Creating Virtual Targets
-
Click Next.
- Task 25 Creating Partitions
-
Click Next.
- Task 26 Configuring Domain Front End Host
-
In the Domain Front End host screen you specify the main entry point for OIM. This will equate to the name on the load balancer. For example, set Plain to
http://prov.example.com.Note:
Even though you are specifying this value it will never be used.SSL: https://prov.example.com
Default: SSL
Click Next.
- Task 27 Reviewing Your Configuration Specifications and Configuring the Domain
-
The Configuration Summary screen contains the detailed configuration information for the domain you are about to create. Review the details of each item on the screen and verify that the information is correct.
You can go back to any previous screen if you need to make any changes, either by using the Back button or by selecting the screen in the navigation pane.
Domain creation will not begin until you click Create.
Tip:
More information about the options on this screen can be found in Configuration Summary in Creating WebLogic Domains Using the Configuration Wizard.
Click Next.
- Task 28 Writing Down Your Domain Home and Administration Server URL
-
The Configuration Success screen will show the following items about the domain you just configured:
-
Domain Location
-
Administration Server URL
You must make a note of both items as you will need them later; the domain location is needed to access the scripts used to start the Administration Server.
Click Finish to dismiss the Configuration Wizard.
-
After you have completed creating the domain with static clusters, go to Creating Oracle Identity Manager Authenticator..
Creating the Domain with Dynamic Clusters
Follow the instructions in this section to create and configure the domain for the topology.
- Task 1 Selecting the Domain Type and Domain Home Location
-
On the Configuration Type screen, select Create a new domain.
In the Domain Location field, specify the value of the ASERVER_HOME variable, as defined in File System and Directory Variables Used in This Guide.
Tip:
More information about the other options on this screen of the Configuration Wizard, see Configuration Type in Creating WebLogic Domains Using the Configuration Wizard.
Click Next.
- Task 2 Selecting the Configuration Templates
-
On the Templates screen, make sure that Create Domain Using Product Templates is selected, then select the following templates:
-
Oracle Identity Manager - 12.2.1.3.0 [oim]
Oracle SOA Suite will also be selected.
-
Oracle Enterprise Manager -12.2.1.3.0 [em]
Selecting this template automatically selects the following dependencies:
-
Oracle JRF -12.2.1.3.0 [oracle_common]
-
WebLogic Coherence Cluster Extension -12.2.1.3.0 [wlserver]
-
-
Oracle WSM Policy Manager -12.2.1.3.0[oracle_common]
Tip:
More information about the options on this screen can be found in Templates in Creating WebLogic Domains Using the Configuration Wizard.
Click Next.
-
- Task 3 Configuring High Availability Options
-
This screen appears for the first time when you create a cluster that uses Automatic Service Migration or JDBC stores or both. After you select HA Options for a cluster, all subsequent clusters that are added to the domain by using the Configuration Wizard, automatically apply these HA options.
On the High Availability Options screen, complete the following steps:
-
Verify that Enable Automatic Service Migration is not selected.
-
Verify that Default Persistent Store is selected as the JTA Transaction Log Persistence option.
-
Select JDBC Store as the JMS Service Persistence option.
You can configure only JMS Server persistence for Dynamic Clusters by using the Configuration Wizard. You cannot configure Service Migration and JTA Transaction Logs Persistence for Dynamic Clusters by using the Configuration Wizard, you have to configure them manually. Instructions are covered in later chapters of this guide.
Click Next.
-
- Task 4 Selecting the Application Home Location
-
On the Application Location screen, specify the value of the APPLICATION_HOME variable, as defined in File System and Directory Variables Used in This Guide.
Tip:
More information about the options on this screen can be found in Application Location in Creating WebLogic Domains Using the Configuration Wizard.
Click Next.
- Task 5 Configuring the Administrator Account
-
On the Administrator Account screen, specify the user name and password for the default WebLogic Administrator account for the domain.
Make a note of the user name and password specified on this screen; you need to use these credentials later to boot and connect to the Administration Server domain.
Click Next.
- Task 6 Specifying the Domain Mode and JDK
-
On the Domain Mode and JDK screen:
-
Select only Production in the Domain Mode field.
-
Select the Oracle Hotspot JDK in the JDK field.
Selecting Production Mode on this screen gives your environment a higher degree of security, requiring a user name and password to deploy applications and to start the Administration Server.
Tip:
More information about the options on this screen, including the differences between development mode and production mode, can be found in Domain Mode and JDK in Creating WebLogic Domains Using the Configuration Wizard.
In production mode, a boot identity file can be created to bypass the need to provide a user name and password when starting the Administration Server. See Creating the boot.properties File.
Click Next.
-
- Task 7 Specifying the Database Configuration Type
-
On the Database Configuration Type screen:
-
Select RCU Data to activate the fields on this screen.
The RCU Data option instructs the Configuration Wizard to connect to the database and Service Table (STB) schema. This connection automatically retrieves schema information for the schemas to configure the domain.
-
Verify that Vendor is Oracle and Driver is *Oracle's Driver (Thin) for Service Connections; Versions: Any.
-
Verify that Connection Parameters is selected.
Note:
If you choose to select Manual Configuration on this screen, you have to manually fill in the parameters for the schema on the JDBC Component Schema screen.
After you select RCU Data, fill in the fields as shown in the following table:
Field Description Host Name
Enter the Single Client Access Name (SCAN) Address for the Oracle RAC database, which you entered in the Enterprise Deployment Workbook.
DBMS/Service
Enter the service name for the Oracle RAC database where you will install the product schemas. For example:
orcl.example.com
Be sure to specify the common service name that is used to identify all the instances in the Oracle RAC database; do not use the host-specific service name.
Port
Enter the port number on which the database listens. For example,
1521.Schema Owner
Schema Password
Enter the user name and password for connecting to the database's Service Table schema.
The schema user name and password that was specified for the Service Table component on the "Schema Passwords" screen in RCU (see Creating the Database Schemas) is used here.
The default user name is
prefix_STB, whereprefixis the custom prefix that you defined in RCU.Click Get RCU Configuration when you are finished specifying the database connection information. The following output in the Connection Result Log indicates that the operating succeeded:
Connecting to the database server...OK Retrieving schema data from database server...OK Binding local schema components with retrieved data...OK Successfully Done.
Click Next if the connection to the database is successful.
Tip:
More information about the RCU Data option can be found in Understanding the Service Table Schema in Creating Schemas with the Repository Creation Utility.
More information about the other options on this screen can be found in Datasource Defaults in Creating WebLogic Domains Using the Configuration Wizard
-
- Task 8 Specifying JDBC Component Schema Information
-
Verify that the values on the JDBC Component Schema screen are correct for all schemas.
The schema table is populated because you selected Get RCU Data on the previous screen. As a result, the Configuration Wizard locates the database connection values for all the schemas required for this domain.
At this point, the values are configured to connect to a single-instance database. However, for an enterprise deployment, you must use a highly available Real Application Clusters (RAC) database, as described in Preparing the Database for an Enterprise Deployment.
In addition, Oracle recommends that you use an Active GridLink datasource for each of the component schemas. For more information about the advantages of using GridLink data sources to connect to a RAC database, see Database Considerations in theHigh Availability Guide.
To convert the data sources to GridLink:
-
Select all the schemas by selecting the checkbox at in the first header row of the schema table.
-
Click Convert to GridLink and click Next.
-
- Task 9 Providing the GridLink Oracle RAC Database Connection Details
-
On the GridLink Oracle RAC Component Schema screen, provide the information required to connect to the RAC database and component schemas, as shown in following table.
Element Description and Recommended Value SCAN, Host Name, and Port
Select the SCAN check box.
In the Host Name field, enter the Single Client Access Name (SCAN) Address for the Oracle RAC database.
In the Port field, enter the SCAN listening port for the database (for example,
1521)ONS Host and Port
In the ONS Host field, enter the SCAN address for the Oracle RAC database.
In the Port field, enter the ONS Remote port (typically,
6200).Enable Fan
Verify that the Enable Fan check box is selected, so the database can receive and process FAN events.
For more information about specifying the information on this screen, as well as information about how to identify the correct SCAN address, see Configuring Active GridLink Data Sources with Oracle RAC in the High Availability Guide.
You can also click Help to display a brief description of each field on the screen.
Click Next.
- Task 10 Testing the JDBC Connections
-
Use the JDBC Component Schema Test screen to test the data source connections you have configured.
A green check mark in the Status column indicates a successful test. If you encounter any issues, see the error message in the Connection Result Log section of the screen, fix the problem, then try to test the connection again.
Tip:
More information about the other options on this screen can be found in Test Component Schema in Creating WebLogic Domains Using the Configuration Wizard
Click Next.
- Task 11 Entering Credentials
-
Enter the credentials you wish to use for the Oracle Identity Governance components. You have the choice of choosing both a username and a password for the various objects.
-
keystore: Set the username to keystore and the password to the password you wish to use for all automatically created keystores.
-
OIMSchemaPassword: Set the username to the OIM schema which you created in the earlier sections. For example,
IGD_OIM(username) and its associated password. -
Sysadmin: This is the administrative user you will use for OIM. This is typically
xelsysadm, but can be anything. Set the password to a value you wish to use for this account. -
WebLogicAdminKey: This is the domain admin username and password. For example,
weblogic.
Click Next.
-
- Task 12 Keystore
-
Use this screen to specify details about the keystore to be used in the domain.
For a typical enterprise deployment, you can leave the default values.
See Keystore in Creating WebLogic Domains Using the Configuration Wizard.
Click Next.
- Task 13 Selecting Advanced Configuration
-
To complete domain configuration for the topology, select the following options on the Advanced Configuration screen:
-
Administration Server
This is required to configure the listen address of the Administration Server.
-
Node Manager
This is required to configure Node Manager.
-
Topology
This is required to add, delete, or modify the Settings for Server Templates, Managed Servers, Clusters, Virtual Targets, and Coherence.
Note:
When using the Advanced Configuration screen in the Configuration Wizard:
-
If any of the options are not available on the screen, then return to the Templates screen, and ensure that you have selected the required templates for this topology.
-
Do not select the Domain Frontend Host Capture advanced configuration option. Later, you have to configure the frontend host property for specific clusters, rather than for the domain.
Click Next.
-
- Task 14 Configuring the Administration Server Listen Address
-
On the Administration Server screen:
-
In the Server Name field, retain the default value:
AdminServer. -
In the Listen Address field, enter the virtual host name that corresponds to the VIP of the ADMINVHN that you procured in Procuring Resources for an Enterprise Deployment and enabled in Preparing the Host Computers for an Enterprise Deployment.
For more information on the reasons for using the ADMINVHN virtual host, see Reserving the Required IP Addresses for an Enterprise Deployment.
-
In the Listen Port field, enter the port number to access the administration server. This guide recommends you to use the default port 7001 for Access and 7101 for Governance.
Leave the other fields at their default values. In particular, be sure that no server groups are assigned to the Administration Server.
Click Next.
-
- Task 15 Configuring Node Manager
-
Select Per Domain Default Location as the Node Manager type, then specify the following Node Manager credentials you will use to connect to the Node Manager:
-
Username: This is the user name used to connect to the Node Manager. For example,
admin. -
Password and Confirm Password: Enter the password you wish to associate with the Node Manager username.
Tip:
For more information about the options on this screen, see Node Manager in Creating WebLogic Domains Using the Configuration Wizard.
For more information about per domain and per host Node Manager implementations, see About the Node Manager Configuration in a Typical Enterprise Deployment.
For additional information, see Configuring Node Manager on Multiple Machines in Administering Node Manager for Oracle WebLogic Server.
Click Next.
-
- Task 16 Configuring Managed Servers
-
On the Managed Servers screen, a new Managed Server for Oracle Identity Governance appears in the list of servers. These servers were created automatically by the Oracle Identity Governance configuration template you selected in File System and Directory Variables Used in This Guide.
Static Managed Server definitions are not needed for dynamic cluster configurations. To remove the default Managed Servers, complete the following steps:
-
Click on the Managed Server.
-
Click Delete.
-
Repeat for each of the Managed Servers.
-
Click Next.
-
- Task 17 Configuring a Cluster
-
In this task, you create a cluster of Managed Servers to which you can target the Oracle Identity Governance software.
Use the Clusters screen to create a new cluster:
-
Click the Add button.
-
Specify
OIM_Clusterin the Cluster Name field. -
From the Dynamic Server Groups drop-down list, select
OIM-DYN-CLUSTER. -
Create a second cluster called
SOA_Clusterand assign the Dynamic Server groupSOA-DYN-CLUSTER. -
Create a third cluster called WSM-PM_Cluster and assign the Dynamic Server group WSMPM-DYN-CLUSTER.
Note:
By default, server instances in a cluster communicate with one another using unicast. If you want to change your cluster communications to use multicast, refer to Considerations for Choosing Unicast or Multicast in Administering Clusters for Oracle WebLogic Server.
Tip:
More information about the options on this screen can be found in Clusters in Creating WebLogic Domains Using the Configuration Wizard.
Tips:
For more information about the options on this screen, see Clusters in Creating WebLogic Domains Using the Configuration Wizard.
Click Next.
-
- Task 18 Assigning Server Templates
-
Use the Server Templates screen to configure the template:
-
Verify that
wsmpm-server-templateis selected in the Name field. -
Specify
7009in the Listen Port field. -
Leave the Enable SSL option unchecked.
-
Verify
OIM-server-templateis listed in the Name field. -
Specify
13999in the Listen Port field. -
Leave the Enable SSL option unchecked.
-
Specify
8000for the Listen Port for template soa-server-template. -
Click Next .
-
- Task 19 Configuring Dynamic Servers
-
Use the Dynamic Clusters screen to configure the following clusters:
Cluster Name Server Name Prefix Server Template Dynamic Cluster Size Machine Name Match Expression Calculated Machine Names oim_cluster WLS_OIM oim-server-template 2 OIMHOST* Selected soa_cluster WLS_SOA soa-server-template 2 OIMHOST* Selected WSM-PM_Cluster WLS_WSM wsmpm-server-template 2 OIMHOST* Selected Complete the following steps on this screen:
-
Verify
OIM_Clusteris listed in the Cluster Name field. -
Specify
WLS_OIMin the Server Name Prefix field. -
From the Server Template drop-down list, select
OIM-server-template. -
Specify
2in the Dynamic Server Count field. -
Specify
OIMHOST*in the Machine Name Match Expression field. -
Select Calculated Machine Names, Calculated Listen Ports, and Dynamic Cluster fields.
Note:
Dynamic clusters with the Calculated Listen Port option selected will have incremental port numbers for each dynamic managed server that is created automatically: dynamic server 1 will use Listen Port+1, dynamic server 2 will use Listen Port+2.
Since the Listen Port configured is
13999and calculated ports is checked, OIM dynamic servers will use the following:-
WLS_OIM1:14000
-
WLS_OIM2:14001
Since the SOA Listen Port configured is
8000and calculated ports is checked, SOA dynamic servers will use the following:-
WLS_SOA1:8001
-
WLS_SOA2:8002
Since the Listen Port that is configured is 7009 and calculated ports is checked, WSMPM dynamic servers use the following ports:
-
WLS_WSM1: 7010
-
WLS_WSM2: 7011
-
-
Repeat the steps 1 through 6 for each of the clusters to be created.
-
Click Next.
Note:
The Configuration Wizard does not allow you to specify a specific listen address for dynamic servers. For information about setting a specific listen address for WebLogic servers that are members of a dynamic cluster, see Configuring Listen Addresses in Dynamic Cluster Server Templates.
-
- Task 20 Configuring Coherence Clusters
-
Use the Coherence Clusters screen to configure the Coherence cluster that is automatically added to the domain.
In the Cluster Listen Port, enter
9991.Note:
For Coherence licensing information, Oracle Coherence Products in Oracle Fusion Middleware Licensing Information User Manual.
Click Next.
- Task 21 Creating Machines
-
Use the Machines screen to create new machines in the domain. A machine is required in order for the Node Manager to be able to start and stop the servers.
-
Select the Unix Machine tab.
-
Click the Add button to create the new UNIX machines.
Use the values in Table 15-3 to define the Name and Node Manager Listen Address of each machine.
-
Verify the port in the Node Manager Listen Port field.
The port number
5556, shown in this example, may be referenced by other examples in the documentation. Replace this port number with your own port number as needed.
Table 15-3 Values to Use When Creating Unix Machines
Name Node Manager Listen Address Node Manager Listen Port ADMINHOST
Enter the value of the ADMINVHN variable.
5556
OIMHOST1
The value of the OIMHOST1 host name variable or OIMHOST1 alias. For example,
OIMHOST1.example.com.5556
OIMHOST2
The value of the OIMHOST2 host name variable or OIMHOST2 alias. For example,
OIMHOST2.example.com.5556
Note:
The name of the machine should reflect the value that you have specified in the Machine Match Expression field with the addition of a sequential number. That is, if you have specified
OIMHOST*in the Machine Match Expression field, then the names of your machines should be OIMHOST1, OIMHOST2, and so on.Tip:
More information about the options on this screen can be found in Machines in Creating WebLogic Domains Using the Configuration Wizard.
Click Next.
-
- Task 22 Assigning Servers to Machines
-
Use the Assign Servers to Machines screen to assign any statically defined managed servers to the appropriate machines. Servers that are part of a dynamic cluster are assigned to the calculated machine names automatically.
Assign AdminServer to the ADMINHOST machine.
Click Next.
- Task 23 Creating Virtual Targets
-
Click Next.
- Task 24 Creating Partitions
-
Click Next.
- Task 25 Reviewing Your Configuration Specifications and Configuring the Domain
-
The Configuration Summary screen contains the detailed configuration information for the domain you are about to create. Review the details of each item on the screen and verify that the information is correct.
You can go back to any previous screen if you need to make any changes, either by using the Back button or by selecting the screen in the navigation pane.
Click Update to execute the domain extension.
Tip:
More information about the options on this screen can be found in Configuration Summary in Creating WebLogic Domains Using the Configuration Wizard.
Click Next.
- Task 26 Reviewing Your Configuration Specifications and Configuring the Domain
-
The Configuration Summary screen contains the detailed configuration information for the domain you are about to create. Review the details of each item on the screen and verify that the information is correct.
You can go back to any previous screen if you need to make any changes, either by using the Back button or by selecting the screen in the navigation pane.
Domain creation begins when you click Create.
Tip:
More information about the options on this screen can be found in Configuration Summary in Creating WebLogic Domains Using the Configuration Wizard.
Click Next.
- Task 27 Writing Down Your Domain Home and Administration Server URL
-
The Configuration Success screen shows the following items about the domain you have configured:
-
Domain Location
-
Administration Server URL
You must make a note of both items because you need them later; the domain location is required to access the scripts that are used to start the Administration Server.
Click Finish to dismiss the Configuration Wizard.
-
Creating Oracle Identity Manager Authenticator
Before you start the domain, you have to run a script which creates the Oracle Identity Manager (OIM) Authenticator in the domain.
Parent topic: Creating Infrastructure for Oracle Identity Governance
Configuring the Domain Directories and Starting the Servers
After the domain is created and the Node Manager is configured, you can then configure the additional domain directories and start the Administration Server and any Managed Servers on the AdminHost.
- Starting the Node Manager in the Administration Server Domain Home
Use these steps to start the per-domain Node Manager for the IAD_ASERVER_HOME domain directory. - Creating the boot.properties File
You must create aboot.propertiesif you want to start the Administrator Server without being prompted for the Administrator Server credentials. This step is required in an enterprise deployment. When you start the Administration Server, the credentials that you enter in this file are encrypted. - Disabling the Derby Database
- Enabling the Managed Servers to use IPv4 Networking
If the Managed Server is configured to use IPv6 networking, then you may encounter issues when you start the Managed Server. Therefore, you must enable the Managed Servers to use IPv4 networking. - Setting the Memory Parameters in IAMGovernanceDomain
- Starting the Administration Server Using the Node Manager
After you have configured the domain and configured the Node Manager, you can start the Administration Server by using the Node Manager. In an enterprise deployment, the Node Manager is used to start and stop the Administration Server and all the Managed Servers in the domain. - Validating the Administration Server
Before you proceed with the configuration steps, validate that the Administration Server has started successfully by making sure that you have access to the Oracle WebLogic Server Administration Console and Oracle Enterprise Manager Fusion Middleware Control; both of these are installed and configured on the Administration Servers. - Creating a Separate Domain Directory for Managed Servers
When you initially create the domain for enterprise deployment, the domain directory resides on a shared disk. This default domain directory is used to run the Administration Server. You can now create a copy of the domain on the local storage for each of your managed server hosts. The domain directory on the local (or private) storage is used to run the Managed Servers. - Starting the Node Manager in the Managed Server Domain Directory on OIMHOST1
- Configuring Listen Addresses When Using Dynamic Clusters
- Starting and Validating the WLS_WSM1 Managed Server on OIMHOST1
After you have configured Node Manager and created the Managed Server domain directory, you can use Oracle Enterprise Manager Fusion Middleware Control to start the WLS_WSM1 Managed Server on OIMHOST1.
Parent topic: Creating Infrastructure for Oracle Identity Governance
Starting the Node Manager in the Administration Server Domain Home
Use these steps to start the per-domain Node Manager for the IAD_ASERVER_HOME domain directory.
Creating the boot.properties File
You must create a boot.properties if you want to start the Administrator Server without being prompted for the Administrator Server credentials. This step is required in an enterprise deployment. When you start the Administration Server, the credentials that you enter in this file are encrypted.
To create a boot.properties file for the Administration Server:
Disabling the Derby Database
Enabling the Managed Servers to use IPv4 Networking
If the Managed Server is configured to use IPv6 networking, then you may encounter issues when you start the Managed Server. Therefore, you must enable the Managed Servers to use IPv4 networking.
Setting the Memory Parameters in IAMGovernanceDomain
The initial startup parameter in the IAMGovernanceDomain, which defines the memory usage, is insufficient for production systems. If you are using the deployment for production purposes it is recommended that you increase the value of this parameter.
The example below sets the minimum heap size to 4GB and the maximium heap size to 8GB. To change the memory allocation setting, do the following:
Starting the Administration Server Using the Node Manager
After you have configured the domain and configured the Node Manager, you can start the Administration Server by using the Node Manager. In an enterprise deployment, the Node Manager is used to start and stop the Administration Server and all the Managed Servers in the domain.
To start the Administration Server by using the Node Manager:
Validating the Administration Server
Before you proceed with the configuration steps, validate that the Administration Server has started successfully by making sure that you have access to the Oracle WebLogic Server Administration Console and Oracle Enterprise Manager Fusion Middleware Control; both of these are installed and configured on the Administration Servers.
To navigate to Fusion Middleware Control, enter the following URL, and log in with the Oracle WebLogic Server administrator credentials:
http://IGDADMINVHN.example.com:7101/consoleTo navigate to the Oracle WebLogic Server Administration Console, enter the following URL, and log in with the same administration credentials:
http://IGDADMINVHN.example.com:7101/emCreating a Separate Domain Directory for Managed Servers
When you initially create the domain for enterprise deployment, the domain directory resides on a shared disk. This default domain directory is used to run the Administration Server. You can now create a copy of the domain on the local storage for each of your managed server hosts. The domain directory on the local (or private) storage is used to run the Managed Servers.
Note:
If you are creating a domain for Oracle Access Management, it is not necessary to perform this step at this time. This is because, at the time of infrastructure creation, there are no managed servers in existence yet.
Placing the IGD_MSERVER_HOME on local storage is recommended to eliminate the potential contention and overhead caused by servers writing logs to shared storage. It is also faster to load classes and jars need from the domain directory, so any temporary or cache data that the Managed Servers use from the domain directory is processed quicker.
As described in Preparing the File System for an Enterprise Deployment, the path to the Administration Server domain home is represented by the IGD_ASERVER_HOME variable, and the path to the Managed Server domain home is represented by the IGD_MSERVER_HOME variable.
To create the Managed Server domain directory:
Starting the Node Manager in the Managed Server Domain Directory on OIMHOST1
After you create the Managed Server domain directory, there are two domain home directories and two corresponding Node Manager instances on OIMHOST1. You use one Node Manager to control the Administration Server, running from Administration Server domain home, and you use the other Node Manager to control the Managed Servers, running from the Managed Server domain home.
You must start the two Node Managers independently.
Note:
The Node Manager for the Managed Server's MSERVER_HOME will be reset every time the domain configuration is unpacked. TheListenAddress will be changed to the ADMINVHN instead of the correct hostname. This needs to be changed to the correct value before starting the Node Manager service after an unpack is performed.
Follow these steps to update and start the Node Manager from the Managed Server home:
For information about additional Node Manager configuration options, see Administering Node Manager for Oracle WebLogic Server.
Configuring Listen Addresses When Using Dynamic Clusters
The default configuration for dynamic managed servers in dynamic clusters is to listen on all available network interfaces. In most cases, the default configuration may be undesirable. To limit the listen address to a specific address when you use dynamic clusters, see Configuring Listen Addresses in Dynamic Cluster Server Templates. Reverify the test URLs that are provided in the previous sections after you change the listen address and restart the clustered managed servers.
Starting and Validating the WLS_WSM1 Managed Server on OIMHOST1
After you have configured Node Manager and created the Managed Server domain directory, you can use Oracle Enterprise Manager Fusion Middleware Control to start the WLS_WSM1 Managed Server on OIMHOST1.
Note:
If you are creating a domain for Oracle Access Management, do not perform this step, as Oracle Access Management does not have a WLS_WSM Managed Server.
Configuring Listen Addresses When Using Dynamic Clusters
The default configuration for dynamic managed servers in dynamic clusters is to listen on all available network interfaces. In most cases, the default configuration may be undesirable. To limit the listen address to a specific address when you use dynamic clusters, see Configuring Listen Addresses in Dynamic Cluster Server Templates. Reverify the test URLs that are provided in the previous sections after you change the listen address and restart the clustered managed servers.
Parent topic: Creating Infrastructure for Oracle Identity Governance
Propagating the Domain and Starting the Servers on OIMHOST2
After you start and validate the Administration Server and WLS_WSM1 Managed Server on OIMHOST1, you can then perform the following tasks on OIMHOST2.
- Unpacking the Domain Configuration on OIMHOST2
- Starting the Node Manager in the Managed Server Domain Directory OIMHOST2
Parent topic: Creating Infrastructure for Oracle Identity Governance
Unpacking the Domain Configuration on OIMHOST2
Now that you have the Administration Server and the first WLS_WSM1 Managed Server running on OIMHOST1, you can configure the domain on OIMHOST2.
Starting the Node Manager in the Managed Server Domain Directory OIMHOST2
Follow these steps to update and start the Node Manager from the Managed Server home:
For information about additional Node Manager configuration options, see Administering Node Manager for Oracle WebLogic Server.
Modifying the Upload and Stage Directories to an Absolute Path
After you configure the domain and unpack it to the Managed Server domain directories on all the hosts, verify and update the upload and stage directories for Managed Servers in the new clusters. See Modifying the Upload and Stage Directories to an Absolute Path in an Enterprise Deployment.
Parent topic: Creating Infrastructure for Oracle Identity Governance
About the Supported Authentication Providers
Oracle Fusion Middleware supports a variety of LDAP authentication providers. See Identity Store Types and WebLogic Authenticators in Securing Applications with Oracle Platform Security Services.
The instructions in this guide assume that you are using Oracle Unified Directory.
Note:
By default, the instructions here describe how to configure the identity service instance to support querying against a single LDAP identity store with an unencrypted connection.
If the connection to your identity provider has to be secured through SSL, then additional keystone configuration is required for role management in the Enterprise Manager Fusion Middleware Control to function correctly. For additional configuration information, see Doc ID 1670789.1 at support.oracle.com.
Also, you can configure the service to support a virtualized identity store, which queries multiple LDAP identity stores, by using LibOVD.
For more information about configuring a Multi-LDAP lookup, refer to Configuring the Identity Store Service in Securing Applications with Oracle Platform Security Services.
Parent topic: Creating Infrastructure for Oracle Identity Governance
Creating a New LDAP Authenticator and Provisioning Enterprise Deployment Users and Group
When you configure an Oracle Fusion Middleware domain, the domain is configured by default to use the WebLogic Server authentication provider (DefaultAuthenticator). However, for an enterprise deployment, Oracle recommends that you use a dedicated, centralized LDAP-compliant authentication provider.
The following topics describe how to use the Oracle WebLogic Server Administration Console to create a new authentication provider for the enterprise deployment domain. This procedure assumes that you have already installed and configured a supported LDAP directory, such as Oracle Unified Directory or .
- About the Enterprise Deployment Users and Groups
- Creating the New Authentication Provider
- Adding the Administration Role to the New Administration Group
- Updating the boot.properties File and Restarting the System
Parent topic: Creating Infrastructure for Oracle Identity Governance
About the Enterprise Deployment Users and Groups
The following topics provide important information on the purpose and characteristics of the enterprise deployment administration users and groups.
About Using Unique Administration Users for Each Domain
When you use a central LDAP user store, you can provision users and groups for use with multiple Oracle WebLogic Server domains. As a result, there is a possibility that one WebLogic administration user can have access to all the domains within an enterprise.
It is a best practice to create and assign a unique distinguished name (DN) within the directory tree for the users and groups that you provision for the administration of your Oracle Fusion Middleware domains.
For example, create two users called oamLDAP and oimLDAP which is used to connect the WebLogic domain to LDAP. This allows the domain to see the users and groups which exist in the directory. You can create a different user for each domain or use a single user for multiple domains. Under no circumstances should the default LDAP administration user be used for this purpose. You must create these users in the systemids container. This container is used for system users that are not normally visible to users. Placing the user into the systemids container ensures that customers who have Oracle Identity Governance do not reconcile this user.
Using a different user for Oracle Access Management (OAM) and Oracle Identity Manager (OIM) LDAP connections ensures that the user that OAM uses to connect to LDAP has a restricted privilege set.
Create a user called weblogic_iam and an administration group called WLSAdministrators. Users in the WLSAdministrators group will be allowed to access the following:
-
Oracle Fusion Middleware Control
-
Oracle WebLogic Administration Console
Create a user called oamadmin and an administration group called OAMAdministrators. Users in the OAMAdministrators group are allowed to access the following:
-
Oracle Access Policy Manager
-
Oracle Access Manager Console
Parent topic: About the Enterprise Deployment Users and Groups
About the Domain Connector User
Oracle recommends that you create a separate domain connector user (for example, oimLDAP) in your LDAP directory. This user allows the domain to connect to the LDAP directory for the purposes of user authentication. It is recommended that this user be a non-administrative user.
In a typical Oracle Identity and Access Management deployment, you create this user in the systemids container. This container is used for system users that are not normally visible to users. Placing the user into the systemids container ensures that customers who have Oracle Identity Governance do not reconcile this user.
Parent topic: About the Enterprise Deployment Users and Groups
About Adding Users to the Central LDAP Directory
After you configure a central LDAP directory to be the authenticator for the enterprise domain, then you should add all new users to the new authenticator and not to the default WebLogic Server authenticator.
Users are added to the directory using the idmConfigTool. See Preparing an Existing LDAP Directory.
When you are using multiple authenticators (a requirement for an enterprise deployment), login and authentication will work, but role retrieval will not. The role is retrieved from the first authenticator only. If you want to retrieve roles using any other authenticator, then you must enable virtualization for the domain.
Parent topic: About the Enterprise Deployment Users and Groups
About Product-Specific Roles and Groups for Oracle Identity and Access Management
Each Oracle Fusion Middleware product implements its own predefined roles and groups for administration and monitoring.
-
Accessing Weblogic or Fusion Middleware consoles
-
Accessing Oracle Access Manager Components
-
Accessing Oracle Identity Manager components
-
• Weblogic Administrators: Example group name —
WLSAdministrators -
• Access/OIM Administrators: Example group name —
IAMAdministrators
For instructions on adding additional roles to the WLSAdministrators group, see Common Configuration and Management Tasks for an Enterprise Deployment.
Parent topic: About the Enterprise Deployment Users and Groups
Example Users and Groups Used in This Guide
These users will be created as a part of Preparing an Existing LDAP Directory.
-
Admin User DN:
cn=weblogic_iam,cn=users,dc=example,dc=com -
Admin Group DN:
cn=WLSAdministrators,cn=groups,dc=example,dc=com -
Product-specific LDAP Connector User:
cn=This is the user that you use to connect WebLogic Managed Servers to the LDAP authentication provider. This user must have permissions to read and write to the Directory Trees:oimLDAP,cn=systemids,dc=example,dc=comcn=users,dc=example,dc=com cn=groups,dc=example,dc=com
cn=reserve,dc=example,dc=com
Note:
This user needs to be granted membership in the following groups to provide read and write access:
cn=orclFAUserReadPrivilegeGroup,cn=groups,dc=example,dc=com
cn=orclFAUserWritePrivilegeGroup,cn=groups,dc=example,dc=com
cn=orclFAGroupReadPrivilegeGroup,cn=groups,dc=example,dc=com
cn=orclFAGroupWritePrivilegeGroup,cn=groups,dc=example,dc=comParent topic: About the Enterprise Deployment Users and Groups
Creating the New Authentication Provider
To configure a new LDAP-based authentication provider:
-
Log in to the WebLogic Server Administration Console using the URL.
http://IGDADMINVHN.example.com:7101/console -
Click Security Realms in the left navigational bar.
-
Click the myrealm default realm entry.
-
Click the Providers tab.
Note that there is a
DefaultAuthenticatorprovider configured for the realm. This is the default WebLogic Server authentication provider. -
Click Lock & Edit in the Change Center.
-
Click the New button below the Authentication Providers table.
-
Enter a name for the provider.
Use one of the following names, based on the LDAP directory service you are planning to use as your credential store:
OUDAuthenticatorfor Oracle Unified Directory -
Select the authenticator type from the Type drop-down list.
Select one of the following types, based on the LDAP directory service you are planning to use as your credential store:
-
OracleUnifiedDirectoryAuthenticatorfor Oracle Unified Directory
-
-
Click OK to return to the Providers screen.
-
On the Providers screen, click the newly created authenticator in the table.
-
Select SUFFICIENT from the Control Flag drop-down menu.
Setting the control flag to SUFFICIENT indicates that if the authenticator can successfully authenticate a user, then the authenticator should accept that authentication and should not continue to invoke any additional authenticators.
If the authentication fails, it will fall through to the next authenticator in the chain. Make sure all subsequent authenticators also have their control flags set to SUFFICIENT; in particular, check the
DefaultAuthenticatorand make sure that its control flag is set to SUFFICIENT. -
Click Save to persist the change of the control flag setting.
-
Click the Provider Specific tab and enter the details specific to your LDAP server, as shown in the following table.
Note that only the required fields are discussed in this procedure. For information about all the fields on this page, consider the following resources:
-
To display a description of each field, click Help on the Provider Specific tab.
-
For more information on setting the User Base DN, User From Name Filter, and User Attribute fields, see Configuring Users and Groups in the Oracle Internet Directory and Oracle Virtual Directory Authentication Providers in Administering Security for Oracle WebLogic Server.
Parameter Sample Value Value Description Host
For example:
idstore.example.comThe LDAP server's server ID.
Port
For example:
1389The LDAP server's port number.
Principal
For example:
cn=oimLDAP, cn=systemids,dc=example,dc=comThe LDAP user DN used to connect to the LDAP server.
Credential
Enter LDAP password.
The password used to connect to the LDAP server.
SSL Enabled
Unchecked (clear)
Specifies whether SSL protocol is used when connecting to the LDAP server.
User Base DN
For example:
cn=users,dc=example,dc=comSpecify the DN under which your users start.
All Users Filter
(&(uid=*)(objectclass=person))Instead of a default search criteria for All Users Filter, search all users based on the
uidvalue.If the User Name Attribute for the user object class in the LDAP directory structure is a type other than
uid, then change that type in the User From Name Filter field.For example, if the User Name Attribute type is
cn, then this field should be set to:(&(cn=*)(objectclass=person)))
User From Name Filter
For example:
(&(uid=%u)(objectclass=person))
If the User Name Attribute for the user object class in the LDAP directory structure is a type other than
uid, then change that type in the settings for the User From Name Filter.For example, if the User Name Attribute type is
cn, then this field should be set to:(&(cn=%u)(objectclass=person))).User Name Attribute
For example:
uidThe attribute of an LDAP user object that specifies the name of the user.
Use Retrieved User Name as Principal
Checked
Must be turned on.
Group Base DN
For example:
cn=groups,dc=example,dc=comSpecify the DN that points to your Groups node.
GUID Attribute
entryuuidThis value is prepopulated with
entryuuidwhenOracleUnifiedDirectoryAuthenticatoris used for OUD. Check this value if you are using Oracle Unified Directory as your authentication provider. -
-
Click Save to save the changes.
-
Return to the Providers page by clicking Security Realms in the right navigation pane, clicking the default realm name (myrealm), and then Providers.
-
Click Reorder, and then use the resulting page to make the Provider you just created first in the list of authentication providers.
List of Authentication Providers
-
OUDAuthenticator
-
DefaultAuthenticator
-
OIMAuthenticationProvider
-
Trust Service Identity Asserter
-
DefaultIdentityAsserter
Figure 15-1 List of Available Authentication Providers
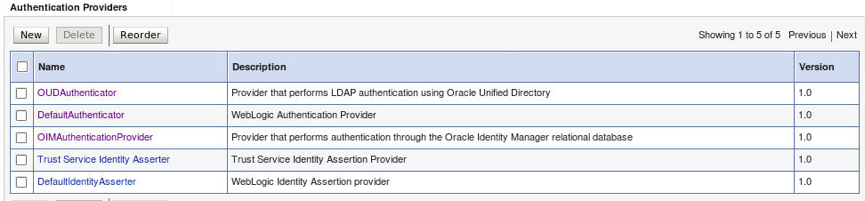
-
-
Click OK.
-
On the Providers Page, click DefaultAuthenticator.
-
From the Control Flag drop-down, select SUFFICIENT.
-
Click Save to update the DefaultAuthenticator settings.
-
In the Change Center, click Activate Changes.
-
Restart the Administration Server and all managed servers.
To stop the Managed Servers, log in to Fusion Middleware Control, select the Managed Servers in the Target Navigator and click Shut Down in the toolbar.
To stop and start the Administration Server using the Node Manager:
-
Start WLST:
cd ORACLE_COMMON_HOME/common/bin ./wlst.sh -
Connect to Node Manager using the Node Manager credentials you defined in when you created the domain in the Configuration Wizard:
wls:/offline>nmConnect('nodemanager_username','nodemanager_password', 'ADMINVHN','5556','domain_name', 'ASERVER_HOME') -
Stop the Administration Server:
nmKill('AdminServer') -
Start the Administration Server:
nmStart('AdminServer') -
Exit WLST:
exit()
To start the Managed Servers, log in to Fusion Middleware Control, select the Managed Servers, and click Start Up in the toolbar.
-
-
After the restart, review the contents of the following log file:
ASERVER_HOME/servers/AdminServer/logs/AdminServer.logVerify that no LDAP connection errors occurred. For example, look for errors such as the following:
The LDAP authentication provider named "OUDAuthenticator" failed to make connection to ldap server at ...
If you see such errors in the log file, then check the authorization provider connection details to verify they are correct and try saving and restarting the Administration Server again.
-
After you restart and verify that no LDAP connection errors are in the log file, try browsing the users and groups that exist in the LDAP provider:
In the Administration Console, navigate to the Security Realms > myrealm > Users and Groups page. You should be able to see all users and groups that exist in the LDAP provider structure.
Adding the Administration Role to the New Administration Group
After you have added the users and groups to LDAP, The WLSAdministrators group must be assigned to the Administration role within the Weblogic domain security realm.This enables all users that belong to the group to be administrators for the domain.
To assign the Administration role to the new enterprise deployment administration group:
Updating the boot.properties File and Restarting the System
Note:
This task is not required for Access Infrastructure.After you create the new administration user and group, you must update the Administration Server boot.properties file with the administration user credentials that you created in the LDAP directory:
Configuring the WebLogic Proxy Plug-In
Before you can validate that requests are routed correctly through the Oracle HTTP Server instances, you must set the WebLogic Plug-In Enabled parameter. It is recommended to set the WebLogic Plug-In Enabled parameter at the domain level. Any clusters or servers not using the plugin via the web-tier can have their WebLogic Plug-In Enabled parameter value set to no on an exception basis as needed.
- Log in to the Oracle WebLogic Server Administration Console.
- In the Domain Structure pane, click on the top-level domain node.
- Click Lock & Edit in the Change Center.
- Click on the Domain Name.
- Click on the Web Applications tab.
- Locate and select the WebLogic PlugIn Enabled option.
- Click Save.
- Click Activate Changes in the Change Center.
- Restart the Administration Server.
Parent topic: Creating Infrastructure for Oracle Identity Governance
Enabling Exalogic Optimizations
This section describes the tasks specific to Exalogic optimization. This sections contains the following topics:
Parent topic: Creating Infrastructure for Oracle Identity Governance
Enabling WebLogic Domain Exalogic Optimization
This section describes the tasks specific to Exalogic optimization. Perform these steps to enable WebLogic domain Exalogic optimizations:
- Log in to the Oracle WebLogic Server Administration Console.
- Select the domain name - IAMGovernanceDomain in the left navigation pane.
- Click Lock and Edit.
- On the settings page, click the General tab.
- Select Enable Exalogic Optimizations.
- Click Save and Activate Changes.
- Restart the WebLogic Administration Server.
Parent topic: Enabling Exalogic Optimizations
Backing Up the Configuration
It is an Oracle best practices recommendation to create a backup after you successfully extended a domain or at another logical point. Create a backup after you verify that the installation so far is successful. This is a quick backup for the express purpose of immediate restoration in case of problems in later steps.
The backup destination is the local disk. You can discard this backup when the enterprise deployment setup is complete. After the enterprise deployment setup is complete, you can initiate the regular deployment-specific Backup and Recovery process.
For information about backing up your configuration, see Performing Backups and Recoveries for an Enterprise Deployment.
Parent topic: Creating Infrastructure for Oracle Identity Governance
Verification of Manual Failover of the Administration Server
After you configure the domain, test failover by following the steps that are described in Verifying Manual Failover of the Administration Server.
Parent topic: Creating Infrastructure for Oracle Identity Governance