3 Configuring the Connector
While creating a target or an authoritative application, you must configure connection-related parameters that the connector uses to connect to Oracle Identity Governance with your target system and perform connector operations. In addition, you can view and edit attribute mappings between the process form fields in Oracle Identity Governance and target system columns, predefined correlation rules, situations and responses, and reconciliation jobs.
Basic Configuration Parameters
These are the connection-related parameters that Oracle Identity Governance requires to connect to an Eloqua application.
Note:
Unless specified, do not modify entries in the below table.Table 3-1 Parameters in the Basic Configuration
| Parameter | Mandatory ? | Description |
|---|---|---|
|
authenticationType |
Yes |
Enter the type of authentication used by your target system. Sample value: |
| username | Yes | Enter the user name of the target system that you create
for performing connector operations.
Sample value:
|
| password | Yes | Enter the password of the target system user account that you create
for connector operations.
Sample value:
|
|
host |
Yes |
Enter the host name of the machine hosting your target system. This is a mandatory attribute while creating an application. Sample value: |
|
port |
No |
Enter the port number at which the target system is listening. Sample value: |
|
proxyHost |
No |
Enter the name of the proxy host used to connect to an external target. Sample value: |
|
proxyPassword |
No |
Enter the password of the proxy user ID of the target system user account that Oracle Identity Governance uses to connect to the target system. |
|
proxyPort |
No |
Enter the proxy port number. Sample value: |
|
proxyUser |
No |
Enter the proxy user name of the target system user account that Oracle Identity Governance uses to connect to the target system. |
|
sslEnabled |
No |
If the target system requires SSL connectivity, then set the value of this parameter to Default value: |
Advanced Settings Parameters
These are the configuration-related entries that the connector uses during reconciliation and provisioning operations.
Note:
-
Unless specified, do not modify entries in the below table.
-
All parameters in the below table are mandatory.
Table 3-2 Advanced Settings Parameters
| Parameter | Description |
|---|---|
|
relURIs |
This entry holds the relative URL of every object class supported by this connector and the connector operations that can be performed on these object classes. This is a mandatory attribute while creating an application. Default value:
|
|
nameAttributes |
This entry holds the name attribute for all the objects that are handled by this connector. For example, for
the Default value: "__ACCOUNT__.loginName","securityGroups.id","license.name" |
|
uidAttributes |
This entry holds the uid attribute for all the objects that are handled by this connector. Default
value: |
|
Bundle Name |
This entry holds the name of the connector bundle. Default value: |
|
Bundle Version |
This entry holds the version of the connector bundle. Default value: |
|
Connector Name |
This entry holds the name of the connector class. Default value: |
|
opTypes |
This entry specifies the HTTP operation type for each object class supported by the connector. Values are comma separated and are in the following format: OBJ_CLASS.OP=HTTP_OP In this format, Default value:
|
|
Any Incremental Recon Attribute Type |
By default, during incremental reconciliation, Oracle Identity Governance accepts timestamp information sent from the target system only in Long datatype format. Setting the value of this parameter to Default value: |
|
jsonResourcesTag |
This entry holds the json tag value that is used during reconciliation for parsing multiple entries in a single payload. Default value:
|
|
httpHeaderContentType |
This entry holds the content type expected by the target system in the header. Default value: |
|
httpHeaderAccept |
This entry holds the accept type expected from the target system in the header. Default value: |
|
specialAttributeTargetFormat |
This entry lists the format in which an attribute is present in the target system endpoint. Values are comma separated and are presented in the following format: OBJ_CLASS.ATTR_NAME= TARGET_FORMAT Default value |
|
specialAttributeHandling |
This entry lists the special attributes whose values should be sent to the target system one by one ("SINGLE"). Values are comma separated and are in the following format: OBJ_CLASS.ATTR_NAME.PROV_OP=SINGLE For example, the Default
value |
|
pageSize |
This entry holds how many resources appears on a page for a search operation. Default value:
|
|
customPayload |
This entry lists the payloads for all operations that are not in the standard format. Default value: Note: The |
|
passwordAttribute |
This entry holds the name of the target system attribute that is mapped to the __PASSWORD__ attribute of the connector in OIM. Default value: Password |
|
statusAttributes |
This entry lists the name of the target system attribute that holds the status of an
account. For example, for the Default value: |
|
statusEnableValue |
This entry holds the name attribute for all target values
indicating the status as |
|
statusDisableValue |
This entry holds the name attribute for all target values
indicating the status as |
Attribute Mappings
The Schema page for a target application displays the default schema (provided by the connector) that maps Oracle Identity Governance attributes to target system attributes. The connector uses these mappings during reconciliation and provisioning operations.
Default Attributes for Eloqua Target Application
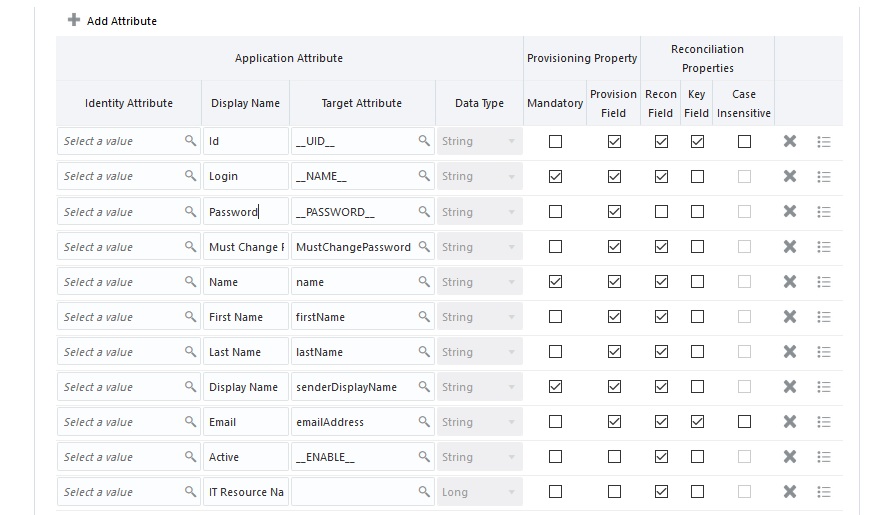
Table 3-3 lists the user-specific attribute mappings between the process form fields in Oracle Identity Governance and Eloqua target application attributes. The table also lists whether a specific attribute is used during provisioning or reconciliation and whether it is a matching key field for fetching records during reconciliation.
If required, you can edit the default attribute mappings by adding new attributes or deleting existing attributes as described in Creating a Target Application in Oracle Fusion Middleware Performing Self Service Tasks with Oracle Identity Governance.
Table 3-3 Default Attributes for Eloqua Target Application
| Display Name | Target Attribute | Data Type | Mandatory Provisioning Property? | Provision Field? | Recon Field? | Key Field? | Case Insensitive? | Advanced Flag Settings |
|---|---|---|---|---|---|---|---|---|
|
Id |
__UID__ |
String |
No |
Yes |
Yes |
Yes |
No |
Yes |
|
Login |
__NAME__ |
String |
Yes |
Yes |
Yes |
Yes |
Not applicable |
Yes |
|
Name |
name |
String |
Yes |
Yes |
Yes |
Yes |
Not applicable |
Yes |
|
First Name |
firstName |
String |
No |
Yes |
Yes |
No |
Not applicable |
Yes |
|
Last Name |
lastname |
String |
No |
Yes |
Yes |
No |
Not applicable |
Yes |
|
Display Name |
senderDisplayName |
String |
Yes |
Yes |
Yes |
No |
Not applicable |
Yes |
|
|
emailAddress |
String |
No |
Yes |
Yes |
Yes |
No |
Yes |
|
Password |
__PASSWORD__ |
String |
No |
Yes |
No |
No |
Yes |
Yes |
|
Active |
__ENABLE__ |
String |
No |
No |
Yes |
No |
Not applicable |
Yes |
|
IT Resource Name |
Not applicable |
Long |
No |
No |
Yes |
No |
Not applicable |
Yes |
Figure 3-1 shows the default User account attribute mappings.
Figure 3-1 Default Attribute Mappings for Eloqua User Account
Groups Entitlement
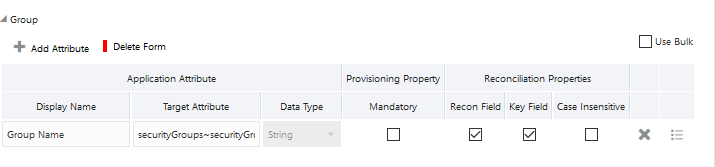
Table 3-4 lists the group forms attribute mappings between the process form fields in Oracle Identity Governance and Eloqua target application attributes. The table lists whether a given attribute is mandatory during provisioning. It also lists whether a given attribute is used during reconciliation and whether it is a matching key field for fetching records during reconciliation.
If required, you can edit the default attribute mappings by adding new attributes or deleting existing attributes as described in Creating a Target Application in Oracle Fusion Middleware Performing Self Service Tasks with Oracle Identity Governance.
Table 3-4 Default Attribute Mappings for Groups Forms
| Display Name | Target Attribute | Data Type | Mandatory Provisioning Property? | Recon Field? | Key Field? | Case Insensitive? |
|---|---|---|---|---|---|---|
|
Group Name |
securityGroups~securityGroups |
String | No | Yes | Yes | No |
Figure 3-2 shows the default attribute groups mapping.
Figure 3-2 Default Attribute Mappings for Groups
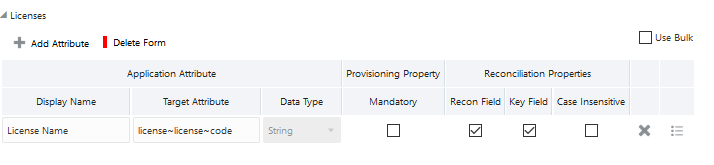
Licenses Entitlement
Table 3-5 lists the license attribute mappings between the process form fields in Oracle Identity Governance and Eloqua target application attributes. The table lists whether a given attribute is mandatory during provisioning. It also lists whether a given attribute is used during reconciliation and whether it is a matching key field for fetching records during reconciliation.
If required, you can edit the default attribute mappings by adding new attributes or deleting existing attributes as described in Creating a Target Application in Oracle Fusion Middleware Performing Self Service Tasks with Oracle Identity Governance.
Table 3-5 Default Attribute Mappings for Licenses
| Display Name | Target Attribute | Data Type | Mandatory Provisioning Property? | Recon Field? | Key Field? | Case Insensitive? |
|---|---|---|---|---|---|---|
|
License Name |
license~license~code |
String | No | Yes | Yes | No |
Figure 3-3 shows the default attribute licenses mapping.
Figure 3-3 Default Attribute Mappings for Licenses
Correlation Rules, Situations, and Responses for a Target Application
When you create a Target application, the connector uses correlation rules to determine the identity to which Oracle Identity Governance must assign a resource.
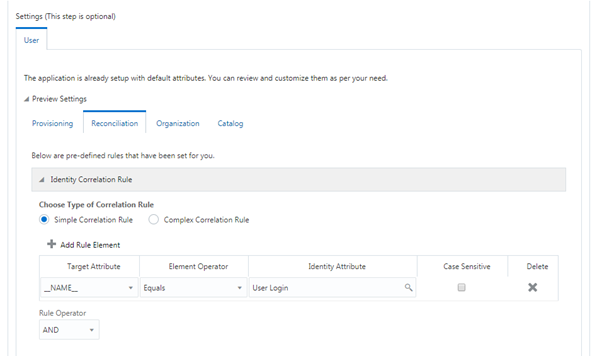
Predefined Identity Correlation Rules
By default, the Eloqua connector provides a simple correlation rule when you create a target application. The connector uses this correlation rule to compare the entries in Oracle Identity Governance repository and the target system repository, determine the difference between the two repositories, and apply the latest changes to Oracle Identity Governance.
Table 3-6 lists the default simple correlation rule for Eloqua connector. If required, you can edit the default correlation rule or add new rules. You can create simple correlation rules also. For more information about adding or editing simple or complex correlation rules, see Updating Identity Correlation Rule in Oracle Fusion Middleware Performing Self Service Tasks with Oracle Identity Governance.
Table 3-6 Predefined Identity Correlation Rule for a Eloqua Target Application
| Target Attribute | Element Operator | Identity Attribute | Case Sensitive? | Rule Operator |
|---|---|---|---|---|
|
__NAME__ |
Equals |
User Login |
No |
AND |
-
__NAME__ is a single-valued attribute on the target system that identifies the user account.
-
User Login is the field on the OIG User form.
-
Rule Operator is AND
Figure 3-4 shows the simple correlation rule for a Eloqua target application.
Figure 3-4 Simple Correlation Rule for a Eloqua Target Application
Predefined Situations and Responses
The Eloqua connector provides a default set of situations and responses when you create a target application. These situations and responses specify the action that Oracle Identity Governance must take based on the result of a reconciliation event.
Table 3-7 lists the default situations and responses for Eloqua target application. If required, you can edit these default situations and responses or add new ones. For more information about adding or editing situations and responses, see Creating a Target Application in Oracle Fusion Middleware Performing Self Service Tasks with Oracle Identity Governance.
Table 3-7 Predefined Situations and Responses for a Eloqua Target Application
| Situation | Response |
|---|---|
|
No Matches Found |
None |
|
One Entity Match Found |
Establish Link |
|
One Process Match Found |
Establish Link |
Reconciliation Jobs
These are the reconciliation jobs that are automatically created in Oracle Identity Governance after you create the application.
User Reconciliation Jobs
You can either use these predefined jobs or edit them to meet your requirements. Alternatively, you can create custom reconciliation jobs. For information about editing these predefined jobs or creating new ones, see Updating Reconciliation Jobs in Oracle Fusion Middleware Performing Self Service Tasks with Oracle Identity Governance.
Table 3-8 describes the parameters of the Eloqua Full User Reconciliation job.
Table 3-8 Parameters of the Eloqua Full User Reconciliation Job
| Parameter | Description |
|---|---|
|
Application name |
Name of the AOB application with which the reconciliation job is associated. This value is the same as the value that you provided for the Application Name field while creating your target application. Do not change the default value. |
|
Latest Token |
This parameter holds the value of the target system attribute that is specified as the value of the Incremental Recon Attribute parameter. The Latest Token parameter is used for internal purposes. By default, this value is empty. Note: Do not enter a value for this parameter. The reconciliation engine automatically enters a value in this parameter. Sample value: <String>2017-09-19T14:16:24Z</String> |
|
Object Type |
This parameter holds the name of the object type for the reconciliation run. Default value: User Do not change the default value. |
|
Filter Suffix |
Enter the search filter for fetching user records from the target system during a reconciliation run. Sample value when incremental recon is enabled: search=loginName='abcuser' Sample value when incremental recon is not enabled: search=loginName='abcuser' |
|
Scheduled Task Name |
Name of the scheduled task used for reconciliation. Do not modify the value of this parameter. |
|
Incremental Recon Attribute |
Enter the name of the attribute that holds the timestamp at which the token record was modified. Sample value: updatedAt |
Delete User Reconciliation Job
The Eloqua Target User Delete Reconciliation job is used to reconcile user data when for target application.
Table 3-9 Parameters of the Eloqua Target User Delete Reconciliation Job
| Parameter | Description |
|---|---|
|
Application Name |
Name of the application you created for your target system. This value is the same as the value that you provided for the Application Name field while creating your target application. Do not modify this value. |
|
Disable User |
Enter Default value: no |
|
Object Type |
Type of object you want to reconcile. Default value: User |
|
Scheduled Task Name |
Name of the scheduled task used for reconciliation. Default value: ELOQUAAOBAPP Eloqua Target User Delete Reconciliation |
Reconciliation Jobs for Entitlements
-
Eloqua Group Lookup Reconciliation
-
Eloqua Licenses Lookup Reconciliation
Table 3-10 Parameters of the Reconciliation Jobs for Entitlements
| Parameter | Description |
|---|---|
|
Application Name |
Current AOB application name with which the reconciliation job is associated. Default value: Eloqua Do not modify this value. |
|
Code Key Attribute |
Name of the connector attribute that is used to populate the Code Key column of the lookup definition (specified as the value of the Lookup Name attribute). Default value: Do not modify this value. |
|
Decode Attribute |
Name of the connector attribute that is used to populate the Decode column of the lookup definition (specified as the value of the Lookup Name attribute). Default value: |
|
Lookup Name |
Enter the name of the lookup definition in Oracle Identity Governance that must be populated with values fetched from the target system. Depending on the Reconciliation job that you are using, the default values are as follows:
If you create a copy of any of these lookup definitions, then enter the name of that new lookup definition as the value of the Lookup Name attribute. |
|
Object Type |
Enter the type of object you want to reconcile. Depending on the reconciliation job that you are using, the default values are as follows:
Note: Do not change the value of this parameter. |