3 Configuring the Oracle Internet Directory Connector for OID
While creating an application, you must configure connection-related parameters that the connector uses to connect Oracle Identity Governance with your target system and perform connector operations. In addition, you can view and edit attribute mappings between the process form fields in Oracle Identity Governance and target system attributes, predefined correlation rules, situations and responses, and reconciliation jobs.
Basic Configuration Parameters for OID
These are the connection-related parameters that Oracle Identity Governance requires to connect to an OID target system. These parameters are common for both target applications and authoritative applications.
Table 3-1 Parameters in the Basic Configuration Section for OID
| Parameter | Mandatory? | Description |
|---|---|---|
|
Base Contexts |
Yes |
Enter the base contexts for operations on the target system. Sample value: Note: In a multilevel base context, each base context must be specified within double quotes (") and separated by a comma (,). |
|
Principal |
Yes |
Enter the bind DN for performing operations on the target system. Sample value for ODSEE or OUD: Sample value for OID: Sample value for eDirectory: Note: For eDirectory, the bind DN should be the complete DN name. |
|
Password |
Yes |
Enter the password to connect to the target system. Note: This parameter is available only when you are creating a Target application. |
|
credentials |
Yes |
Enter the credentials to connect to the target system. Note: This parameter is available only when you are creating an Authoritative application. |
|
Host |
Yes |
Enter the host name or IP address of the target system. Sample values:
|
|
Port |
Yes |
Enter the port number to connect to the target system. Default value: |
|
Connector Server Name |
No |
If you are using this connector with a Connector Server, then enter the name of Connector Server IT resource. |
|
Failover |
No |
Enter the complete URL of LDAP backup server or servers that the connector must switch to if the primary LDAP server fails or becomes unavailable. The URL is a fully qualified host name or an IP address in the following format: ldap://172.20.55.191:389
If you specify more than one URL, each URL must be enclosed in double quotes (") and separated by a comma (,). For example: |
|
SSL |
No |
Specifies whether communication with the target system must be secured using SSL. Default value: Note: You can set the value to true, when SSL is enabled between Oracle Identity Manager and the Connector Server or between Oracle Identity Manager and the target system. Set the To configure SSL, see Configuring the Java Connector Server with SSL for Oracle Identity Governance in Oracle Fusion Middleware Developing and Customizing Applications for Oracle Identity Governance. |
Advanced Settings Parameters for OID
Advanced configuration parameters vary depending on whether you are creating a target application or an authoritative application.
Advanced Settings Parameters for an OID Target Application
These are the configuration-related entries that the connector uses during reconciliation and provisioning operations against a target application.
Note:
Unless specified, do not modify entries in the below table.Table 3-2 Advanced Settings Parameters for an OID Target Application
| Parameter | Mandatory? | Description |
|---|---|---|
|
Standard Change Log |
No |
This parameter specifies how the connector accesses the changelog attribute. Default value: Note: Do not modify this value. |
|
readSchema |
No |
This parameter specifies whether the schema must be read from the server. Default value: |
|
Connector Package Version |
No |
This parameter holds the version of the connector. Default value: |
|
usePagedResultControl |
No |
This parameter specifies whether simple paged search is preferred over VLV index search when both are available. Default value: |
|
filterwithOrInsteadOfAnd |
No |
This parameter specifies whether the changelog filter is built using an OR or AND filter. Enter An OR filter is in the following the following format: An AND filter is of the following format: |
|
disabledValue |
No |
This parameter specifies the value to use for the attribute defined by the enabledAttribute parameter whenever an account is disabled. Default value: |
|
enabledWhenNoAttribute |
No |
This parameter defines if the status must be enabled or disabled when the property defined in enabledAttribute is not present in the parameter. Default value: |
|
changelogUidAttribute |
No |
This parameter holds the name of the attribute that contains the unique ID of the modified entry in the changelog. Default value: |
|
attributesToSynchronize |
No |
This parameter holds the list of attributes that the connector must return whenever a SyncOp is run. Default value: |
|
groupMemberAttribute |
No |
This parameter holds the LDAP attribute that stores the member for non-POSIX static groups. Default value: |
|
enabledValue |
No |
This parameter specifies the value that the connector must use for the attribute defined by the enabledAttribute parameter whenever an account is enabled. Default value: |
|
Connector Package Name |
Yes |
This parameter holds the name of the connector package. Default value: |
|
respectResourcePasswordPolicyChangeAfterReset |
No |
By default, this value is set to Default value: |
|
vlvSortAttribute |
No |
This parameter is used as the sort key for the VLV index. Default value: |
|
blockSize |
No |
This parameter holds the block size for simple paged results and VLV index searches. Default value: |
|
Connector Name |
Yes |
This parameter holds the name of the connector class. Default value: Do not modify this parameter. |
|
synchronizeWithModifyTimestamps |
No |
This parameter specifies whether the connector must use the modify timestamps attribute instead of the changelog attribute during a SyncOp operation. Default value: |
|
enabledAttribute |
No |
This parameter holds the name of the attribute that is required to enable or disable accounts. Default value: |
|
objectClassesToSynchronize |
No |
This parameter holds the object classes to synchronize. The change log is for all objects; this filters updates the listed object classes. You should not list the superclasses of an object class unless you intend to synchronize objects with any of the superclass values. Default value: |
|
accountObjectClasses |
No |
This parameter holds the list of object classes required for a USER object. Default value: |
|
accountUserNameAttribute |
No |
This parameter holds attributes that contain the name of a USER object. Default value: |
|
changelogBaseDn |
No |
This parameter holds the baseDN where the connector is to find the changelog attribute value. Default value: |
|
uidAttribute |
No |
This parameter holds the LDAP attribute to which the connector must map predefined UID attribute. Default value: |
|
removeLogEntryObjectClassFromFilter |
No |
This parameter specifies whether the changelog filter contains a condition on the changelog objectclass. Default value: |
|
accountSearchFilter |
No |
This parameter holds a search filter that any account needs to match in order to be returned. Default value: |
|
accountSynchronizationFilter |
No |
This parameter holds a filter for all the entries that the connector returns during the SyncOp operation that must match. Default value: |
|
changeNumberAttribute |
No |
This parameter holds the attribute name that connector must use for changelog. Default value: |
|
maintainPosixGroupMembership |
No |
This parameter specifies whether the connector modifies POSIX group membership of renamed or deleted user entries. Default value: |
|
passwordAttribute |
No |
This parameter holds the name of the attribute to which the predefined PASSWORD attribute is written to. Default value: |
|
maintainLdapGroupMembership |
No |
This parameter specifies whether the connector modifies group membership of renamed and deleted user entries. Default value: |
|
changeLogBlockSize |
No |
This parameter holds the block size for simple paged results and VLV index searches when reading changelog during a SyncOp operation. Default value: |
|
Any Incremental Recon Attribute Type |
No |
This parameter indicates that the connector accepts any format of token during reconciliation. Default value: |
|
ldapGroupFilterBehavior |
No |
This parameter specifies the behavior for an LDAP group filter. Default value: |
|
ldapGroupMembershipAttribute |
No |
This parameter specifies the value for the LDAP group membership attribute. Default value: |
|
dateFormat |
No |
This parameter specifies the format of date data on the target system. Default value: |
|
dateTypeAttrNames |
No |
This parameter specifies the list of target system attributes that the connector must format to match the date format that you specify in the dateFormat parameter. Default value: |
|
pwdMaxFailure |
No |
This parameter indicates the number of consecutive failed bind attempts after which a user account is locked. If the value of this parameter is 0 (zero), then the account is not locked due to failed bind attempts, and the value of the password lockout policy is ignored. Default value: |
|
Pool Max Idle |
No |
Maximum number of idle objects in a pool. Default value: |
|
Pool Max Size |
No |
Maximum number of connections that the pool can create. Default value: |
|
Pool Max Wait |
No |
Maximum time, in milliseconds, the pool must wait for a free object to make itself available to be consumed for an operation. Default value: |
|
Pool Min-Evict Idle |
No |
Minimum time, in milliseconds, the connector must wait before evicting an idle object. Default value: |
|
Pool Min Idle |
No |
Minimum number of idle objects in a pool. Default value: |
Advanced Settings Parameters for an OID Authoritative Application
These are the configuration-related entries that the connector uses during reconciliation runs against an authoritative application.
Table 3-3 Advanced Settings Parameters for OID Authoritative Application
| Parameter | Mandatory? | Description |
|---|---|---|
| changeNumberAttribute | No | This entry holds the attribute name used for changelog.
Default value: |
| enabledValue | No | This entry specifies the value to use for the attribute defined by the enabledAttribute parameter whenever an account is enabled.
Default value: |
| disabledValue | No | This entry specifies the value to use for the attribute defined by the enabledAttribute property whenever an account is disabled.
Default value: |
| Bundle Name | Yes | This entry holds the name of the connector bundle package.
Default value: |
| enabledWhenNoAttribute | No | This entry defines if the status must be enabled or disabled when the property defined in enabledAttribute is not present in the entry.
Default value: |
| Connector Name | No |
This entry holds the name of the connector class. Do not modify this entry. Default value: |
| objectClassesToSynchronize | No |
This entry holds the list of object classes that the connector must synchronize. Any synchronized entry in order to be returned must have at least one object class from this list. If this list of object classes is empty or the value is missing, then the connector does not perform filtering on the object classes. Default value: |
| Bundle Version | No | This entry holds the version of the connector bundle class.
Default value: |
| uidAttribute | No | This entry holds the LDAP attribute to which the predefined UID attribute must be mapped to.
Default value: |
| enabledAttribute | No | This entry holds the name of the attribute that is required to enable or disable accounts.
Default value: |
|
changeLogBlockSize |
No | This entry holds the block size for simple paged results and VLV index searches when reading changelog during a SyncOp operation.
Default value: |
| accountObjectClasses | No | This entry holds the list of object classes required for a USER object.
Default value: |
| usePagedResultControl | No | This entry specifies whether simple paged search is preferred over VLV index search when both are available.
Default value: |
| Any Incremental Recon Attribute Type | No | This parameter indicates that the connector accepts any format of token during reconciliation.
Default value: |
| pwdMaxFailure | No |
Indicates the number of consecutive failed bind attempts after which the connector locks a user account. If the value of this parameter is 0 (zero), then the account is not locked due to failed bind attempts, and the connector ignores the value of the password lockout policy. Default value: |
| Pool Max Idle | No |
Maximum number of idle objects in a pool. Default value: 10 |
| Pool Max Size | No | Maximum number of connections that the pool can create.
Default value: |
| Pool Max Wait | No | Maximum time, in milliseconds, the pool must wait for a free object to make itself available to be consumed for an operation.
Default value: |
| Pool Min-Evict Idle | No | Minimum time, in milliseconds, the connector must wait before evicting an idle object.
Default value: |
| Pool Min Idle | No | Minimum number of idle objects in a pool.
Default value: |
Attribute Mappings for OID
The attribute mappings on the Schema page vary depending on whether you are creating a target application or an authoritative application.
Attribute Mappings for an OID Target Application
The Schema page for a Target application displays the default schema (provided by the connector) that maps Oracle Identity Governance attributes to target system attributes. The connector uses these mappings during reconciliation and provisioning operations.
Default Attributes for an OID Target Application
Table 3-4 lists the user-specific attribute mappings between the process form fields in Oracle Identity Governance and OID Target application attributes. The table also lists whether a specific attribute is used during provisioning or reconciliation and whether it is a matching key field for fetching records during reconciliation.
If required, you can edit the default attribute mappings by adding new attributes or deleting existing attributes as described in Creating a Target Application in Oracle Fusion Middleware Performing Self Service Tasks with Oracle Identity Governance.
Table 3-4 Default Attributes for an OID Target Application
| Display Name | Target Attribute | Data Type | Mandatory Provisioning Property? | Provision Field? | Recon Field? | Key Field? | Case Insensitive? |
|---|---|---|---|---|---|---|---|
| User ID | uid | String | Yes | Yes | Yes | No | Not applicable |
| First Name | givenname | String | No | Yes | Yes | No | Not applicable |
| Middle Name | initials | String | No | Yes | Yes | No | Not applicable |
| Last Name | sn | String | Yes | Yes | Yes | No | Not applicable |
| Common Name | cn | String | Yes | Yes | Yes | No | Not applicable |
| Container DN | __parentDN__ | String | Yes | No | Yes | No | Not applicable |
| Department | departmentnumber | String | No | Yes | Yes | No | Not applicable |
| Location | l | String | No | Yes | Yes | No | Not applicable |
| Telephone | telephonenumber | String | No | Yes | Yes | No | Not applicable |
| Email ID | String | No | Yes | Yes | No | Not applicable | |
| Preferred Language | preferredLanguage | String | No | Yes | Yes | No | Not applicable |
| Time Zone | orclTimeZone | String | No | Yes | Yes | No | Not applicable |
| Title | title | String | No | Yes | Yes | No | Not applicable |
| orclGuid | __UID__ | String | No | Yes | Yes | Yes | No |
| Start Date | orclActiveStartDate | String | No | Yes | Yes | No | Not applicable |
| End Date | orclActiveEndDate | String | No | Yes | Yes | No | Not applicable |
| manager | manager | String | No | Yes | Yes | No | Not applicable |
| Status | __ENABLE__ | String | No | No | Yes | No | Not applicable |
| Name | __NAME__ | String | No | Yes | No | No | Not applicable |
| Login Disabled | __ENABLED__ | String | No | Yes | No | No | Not applicable |
| Password | __PASSWORD__ | String | No | Yes | No | No | Not applicable |
Figure 3-1 shows the default User account attribute mappings.
Figure 3-1 Default Attribute Mappings for an OID User Account
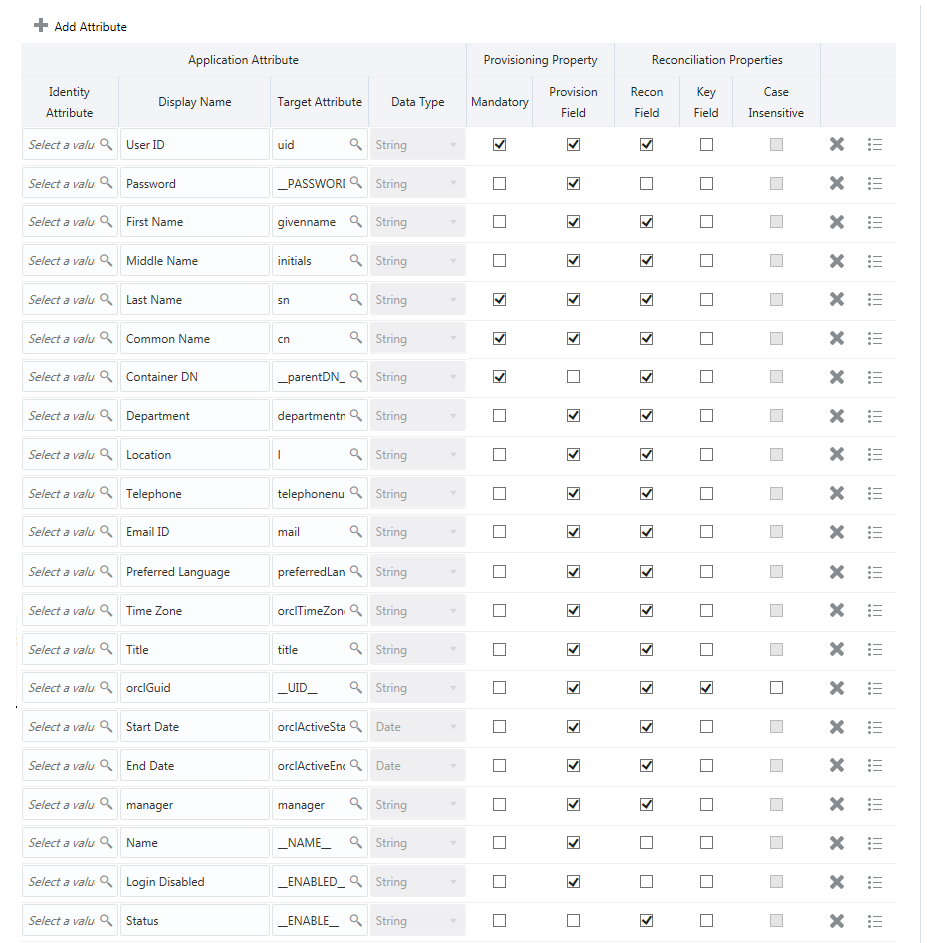
Description of "Figure 3-1 Default Attribute Mappings for an OID User Account"
Groups Entitlement
Table 3-5 lists the group forms attribute mappings between the process form fields in Oracle Identity Governance and OID Target application attributes. The table lists whether a given attribute is mandatory during provisioning. It also lists whether a given attribute is used during reconciliation and whether it is a matching key field for fetching records during reconciliation.
If required, you can edit the default attribute mappings by adding new attributes or deleting existing attributes as described in Creating a Target Application in Oracle Fusion Middleware Performing Self Service Tasks with Oracle Identity Governance.
Table 3-5 Default Attribute Mappings for Groups Forms
| Display Name | Target Attribute | Data Type | Mandatory Provisioning Property? | Recon Field? | Key Field? | Case Insensitive? |
|---|---|---|---|---|---|---|
|
Group Name |
ldapGroups |
String | No | Yes | Yes | No |
Figure 3-2 shows the default attribute groups mapping.
Figure 3-2 Default Attribute Mappings for Groups
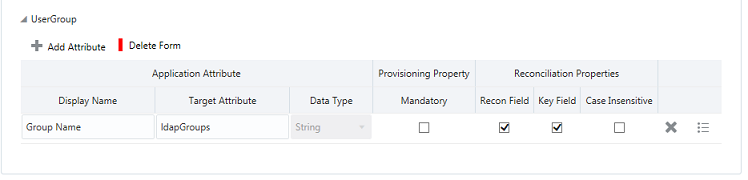
Description of "Figure 3-2 Default Attribute Mappings for Groups"
Attribute Mappings for an OID Authoritative Application
The Schema page for an authoritative application displays the default schema (provided by the connector) that maps Oracle Identity Governance attributes to authoritative system attributes. The connector uses these mappings during reconciliation runs against an authoritative application.
Table 3-6 lists the user-specific attribute mappings between the process form fields in Oracle Identity Governance and OID Authoritative application attributes. The table also lists the data type for a given attribute and specified whether it is a mandatory attribute for reconciliation.
If required, you can edit the default attribute mappings by adding new attributes or deleting existing attributes as described in Creating an Authoritative Application in Oracle Fusion Middleware Performing Self Service Tasks with Oracle Identity Governance.
You may use the default schema that has been set for you or update and change it before continuing to the next step.
The Organization Name, Xellerate Type, and Role identity attributes are mandatory fields on the OIG User form. They cannot be left blank during reconciliation. The target attribute mappings for these identity attributes are empty by default because there are no corresponding columns in the target system. Therefore, the connector provides default values (as listed in the “Default Value for Identity Display Name” column of Table 3-6) that it can use during reconciliation. For example, the default target attribute value for the Organization Name attribute is Xellerate Users. This implies that the connector reconciles all target system user accounts into the Xellerate Users organization in Oracle Identity Governance. Similarly, the default attribute value for Xellerate Type attribute is End-User, which implies that all reconciled user records are marked as end users.
Table 3-6 Default Attributes for an OID Authoritative Application
| Display Name | Target Attribute | Data Type | Mandatory Provisioning Property? | Recon Field? | Advanced Flag Settings | Default Value for Identity Display Name |
|---|---|---|---|---|---|---|
| String | No | Yes |
Yes |
NA |
||
| Role | NA | String | No | Yes | Yes |
Full-Time |
| First Name | givenname | String | No | Yes | Yes |
NA |
| Last Name | sn | String | No | Yes | Yes |
NA |
| Manager Login | manager | String | No | Yes | Yes |
NA |
| Middle Name | initials | String | No | Yes | Yes |
NA |
| OrclGuid | __UID__ | String | No | Yes | Yes |
NA |
| Organization Name | NA | String | No | Yes | Yes |
Xellerate Users |
| Status | __ENABLE__ | String | No | Yes | Yes |
NA |
| User Login | uid | String | No | Yes | Yes |
NA |
| Xellerate Type | NA | String | No | Yes | Yes |
End-User |
Figure 3-3 shows the default User account attribute mappings.
Figure 3-3 Default Attributes for an OID Authoritative Application
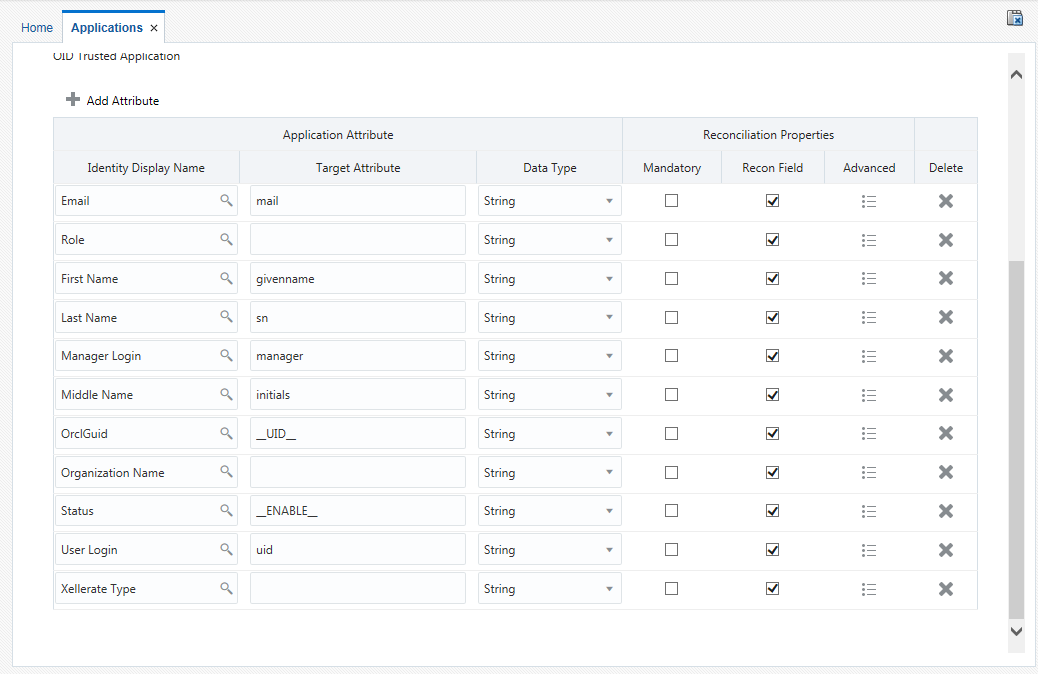
Description of "Figure 3-3 Default Attributes for an OID Authoritative Application"
Correlation Rules for OID
Learn about the predefined rules, responses and situations for Target and Authoritative applications. The connector uses these rules and responses for performing reconciliation.
Correlation Rules for an OID Target Application
When you create a Target application, the connector uses correlation rules to determine the identity to which Oracle Identity Governance must assign a resource.
Predefined Identity Correlation Rules
By default, the OID connector provides a simple correlation rule when you create a Target application. The connector uses this correlation rule to compare the entries in Oracle Identity Governance repository and the target system repository, determine the difference between the two repositories, and apply the latest changes to Oracle Identity Governance.
Table 3-7 lists the default simple correlation rule for OID. If required, you can edit the default correlation rule or add new rules. You can create complex correlation rules also. For more information about adding or editing simple or complex correlation rules, see Updating Identity Reconciliation Rule in Oracle Fusion Middleware Performing Self Service Tasks with Oracle Identity Governance.
Table 3-7 Predefined Identity Correlation Rule for OID
| Target Attribute | Element Operator | Identity Attribute | Case Sensitive? |
|---|---|---|---|
|
uid |
Equals |
User Login |
No |
|
__UID__ |
Equals |
OrclGuid |
No |
-
uid is a single-valued attribute on the target system that identifies the user account.
-
User Login is the field on the OIG User form.
-
__UID__ is a single-valued attribute on the target system that identifies the user account.
-
OrclGuid is the field on the OIG User form.
Rule operator: OR
Figure 3-4 shows the simple correlation rule for an OID Target application.
Figure 3-4 Simple Correlation Rule for an OID Target Application
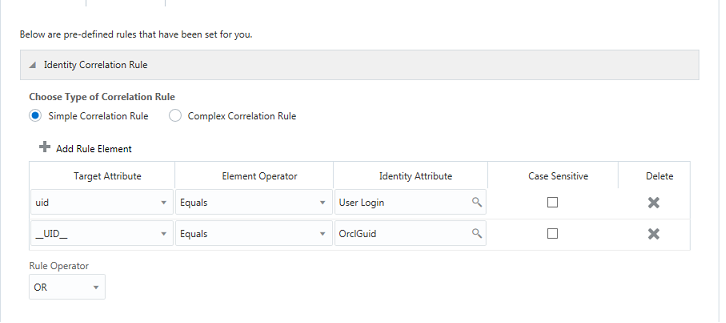
Description of "Figure 3-4 Simple Correlation Rule for an OID Target Application"
Predefined Situations and Responses
The OID connector provides a default set of situations and responses when you create a Target application. These situations and responses specify the action that Oracle Identity Governance must take based on the result of a reconciliation event.
Table 3-8 lists the default situations and responses for an OID Target application. If required, you can edit these default situations and responses or add new ones. For more information about adding or editing situations and responses, see Creating a Target Application in Oracle Fusion Middleware Performing Self Service Tasks with Oracle Identity Governance
Table 3-8 Predefined Situations and Responses for an OID Target Application
| Situation | Response |
|---|---|
|
One Entity Match Found |
Establish Link |
|
One Process Match Found |
Establish Link |
Figure 3-5 shows the situations and responses that the connector provides by default when you create a Target application for OID.
Figure 3-5 Predefined Situations and Responses for an OID Target Application
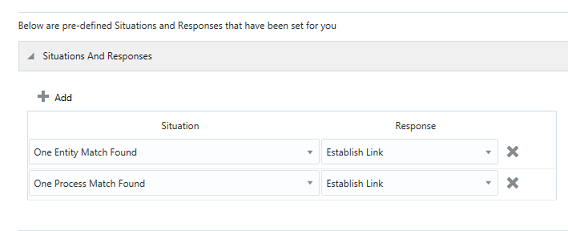
Description of "Figure 3-5 Predefined Situations and Responses for an OID Target Application"
Correlation Rules for an OID Authoritative Application
When you create an Authoritative application, the connector uses correlation rules to determine the identity that must be reconciled into Oracle Identity Governance.
Predefined Identity Correlation Rules
By default, the OID connector provides a simple correlation rule when you create an Authoritative application. The connector uses this correlation rule to compare the entries in Oracle Identity Governance repository and the target system repository, determine the difference between the two repositories, and apply the latest changes to Oracle Identity Governance.
Table 3-9 lists the default simple correlation rule for an OID connector. If required, you can edit the default correlation rule or add new rules. You can create complex correlation rules also. For more information about adding or editing simple or complex correlation rules, see Creating an Authoritative Application in Oracle Fusion Middleware Performing Self Service Tasks with Oracle Identity Governance.
Table 3-9 Predefined Identity Correlation Rule for an OID Authoritative Application
| Authoritative Attribute | Element Operator | Identity Attribute | Case Sensitive? |
|---|---|---|---|
| uid | Equals | User Login | No |
Correlation Rule element: uid Equals User Login
-
uid is the unique login name of a user.
-
User Login is the User ID field of the OIG User form.
Figure 3-6 shows the simple correlation rule for an OID Authoritative application.
Figure 3-6 Simple Correlation Rule for an OID Authoritative Application
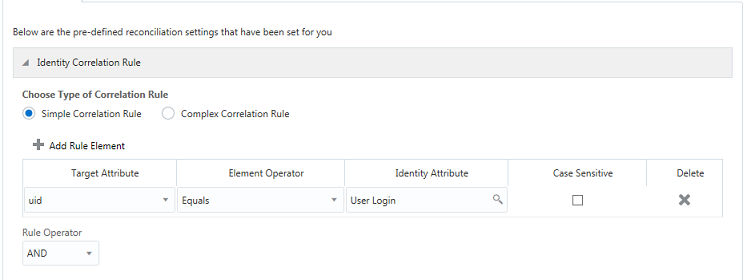
Description of "Figure 3-6 Simple Correlation Rule for an OID Authoritative Application"
Predefined Situations and Responses
The OID connector provides a default set of situations and responses when you create an Authoritative application. These situations and responses specify the action that Oracle Identity Governance must take based on the result of a reconciliation event.
Table 3-10 lists the default situations and responses for an OID Authoritative Application. If required, you can edit these default situations and responses or add new ones. For more information about adding or editing situations and responses, see Creating an Authoritative Application in Oracle Fusion Middleware Performing Self Service Tasks with Oracle Identity Governance.
Table 3-10 Predefined Situations and Responses for an OID Authoritative Application
| Situation | Response |
|---|---|
|
No Matches Found |
Create User |
|
One Entity Match Found |
Establish Link |
|
One Process Match Found |
Establish Link |
Figure 3-7 shows the situations and responses that the connector provides by default when you create an Authoritative application for OID.
Figure 3-7 Predefined Situations and Responses for an OID Authoritative Application
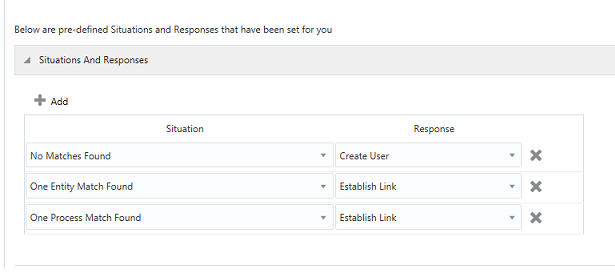
Description of "Figure 3-7 Predefined Situations and Responses for an OID Authoritative Application"
Reconciliation Jobs for OID
Learn about reconciliation jobs that are automatically created in Oracle Identity Governance after you create a target or an authoritative application for your target system.
Reconciliation Jobs for an OID Target Application
These are the reconciliation jobs that are automatically created in Oracle Identity Governance after you create an OID Target application.
Reconciliation Jobs for an OID Target Application
You can either use these predefined jobs or edit them to meet your requirements. Alternatively, you can create custom reconciliation jobs. For information about editing these predefined jobs or creating new ones, see Updating Reconciliation Jobs in Oracle Fusion Middleware Performing Self Service Tasks with Oracle Identity Governance.
The following reconciliation jobs are available for reconciling user data:
-
OID Connector User Search Reconciliation: Use this reconciliation job to reconcile user data from a Target application. Use this job if either of the following conditions is true:
-
You want to perform Full or Incremental Reconciliation.
-
Your target system supports the modifyTimestamp attribute.
-
-
OID Connector User Sync Reconciliation: Use this reconciliation job to reconcile user data from a Target application. Use this job if either of the following conditions is true:
-
You want to perform incremental reconciliation.
-
Your target system supports the changelog attribute.
-
-
OID Connector User Search Delete Reconciliation: Use this reconciliation job to reconcile user records that are deleted from a Target application.
Table 3-11 describes the parameters of the OID Connector User Search Reconciliation job.
Table 3-11 Parameters of the OID Connector User Search Reconciliation Job
| Parameter | Description |
|---|---|
|
Application name |
Name of the AOB application with which the reconciliation job is associated. This value is the same as the value that you provided for the Application Name field while creating your target application. Do not modify this value. |
|
Filter |
Enter the expression for filtering records that this job must reconcile. Sample value: equalTo('__UID__','EXAMPLEUSER') For information about the filters expressions that you can create and use, see ICF Filter Syntax in Oracle Fusion Middleware Developing and Customizing Applications for Oracle Identity Governance. |
|
Object Type |
This parameter holds the type of object you want to reconcile. Default value: Do not modify the value of this parameter. |
|
Incremental Recon Attribute |
Name of the target system attribute that holds the timestamp at which the user record was modified. Default value: |
|
Scheduled Task Name |
Name of the scheduled task used for reconciliation. Note: For the scheduled job included with this connector, you must not change the value of this parameter. However, if you create a new job or create a copy of the job, then enter the unique name for that scheduled job as the value of this parameter. |
|
Latest Token |
This parameter holds the value of the target system attribute that is specified as the value of the Incremental Recon Attribute parameter. The connector uses the Latest Token parameter for internal purposes. By default, this value is empty. Note: Do not enter a value for this attribute. The reconciliation engine automatically enters a value in this attribute. Sample value: |
Table 3-12 describes the parameters of the OID Connector User Sync Reconciliation job.
Table 3-12 Parameters of the OID Connector User Sync Reconciliation Job
| Parameter | Description |
|---|---|
|
Application name |
Name of the AOB Application with which the job is associated. This value is the same as the value that you provided for the Application Name field while creating your target application. Do not modify this value. |
|
Sync Token |
You can manually enter the first Sync Token. To retrieve this token, query cn=changelog on rootDSE on the target system. Then, every time this job is run, the connector updates the value of Sync Token parameter. Browse the changelog attribute of the target system to determine a value from the changelog that the connector must use to resume a reconciliation run. From the next reconciliation run onward, only data about records that are created or modified since the last reconciliation run ended are fetched into Oracle Identity Governance. Or, you can also leave this field blank, which causes the entire changelog to be read. As OID is a target system for which the value of the standardChangelog advanced settings parameter is set to true, this parameter stores values in the following format: Sample value: |
|
Object Type |
This parameter holds the type of object you want to reconcile. Default value: Do not modify the value of this parameter. |
|
Scheduled Task Name |
Name of the scheduled task used for reconciliation. Note: For the scheduled job included with this connector, you must not change the value of this parameter. However, if you create a new job or create a copy of the job, then enter the unique name for that scheduled job as the value of this parameter. |
Table 3-13 Parameters of the OID User Search Delete Reconciliation Job
| Attribute | Description |
|---|---|
|
Application name |
Name of the AOB Application with which the job is associated. This value is the same as the value that you provided for the Application Name field while creating your target application. Do not modify this value. |
|
Object Type |
This parameter holds the type of object you want to reconcile. Default value: Do not modify the value of this parameter. |
Reconciliation Jobs for Entitlements
-
OID Connector Group Lookup Reconciliation: Use this job to search for and reconcile all group data in the target system into lookup fields in Oracle Identity Governance.
-
OID Connector OU Lookup Reconciliation: Use this job to search for and reconcile all organization data in the target system into lookup fields in Oracle Identity Governance.
Table 3-14 Parameters of the Reconciliation Jobs for Entitlements
| Parameter | Description |
|---|---|
|
Application Name |
Name of the application you created for your target system. This value is the same as the value that you provided for the Application Name field while creating your target application. Do not modify this value. |
|
Lookup Name |
Enter the name of the lookup definition in Oracle Identity Governance that the connector must populate with values it fetches from the target system. Depending on the reconciliation job that you are using, the default values are as follows:
If you create a copy of any of these lookup definitions, then enter the name of that new lookup definition as the value of the Lookup Name parameter. |
|
Object Type |
This parameter holds the type of object you want to reconcile. Depending on the reconciliation job that you are using, the default values are as follows:
Note: Do not change the value of this parameter. |
|
Code Key Attribute |
Name of the connector or target system attribute that the connector uses to populate the Code Key column of the lookup definition (specified as the value of the Lookup Name parameter). Default value: Do not modify this value. |
|
Decode Attribute |
Name of the connector or target system attribute that the connector uses to populate the Decode column of the lookup definition (specified as the value of the Lookup Name parameter). Depending on the reconciliation job that you are using, the default values are as follows:
|
|
Filter |
Expression for filtering records that must be reconciled by the scheduled job. Sample value: |
Reconciliation Jobs for an OID Authoritative Application
These are the reconciliation jobs that are automatically created in Oracle Identity Governance after you create an OID authoritative application.
User Reconciliation Jobs for an OID Authoritative Application
You can either use these predefined jobs or edit them to meet your requirements. Alternatively, you can create custom reconciliation jobs. For information about editing these predefined jobs or creating new ones, see Updating Reconciliation Jobs in Oracle Fusion Middleware Performing Self Service Tasks with Oracle Identity Governance.
The following reconciliation jobs are available for reconciling user data:
-
OID Connector Trusted User Reconciliation: Use this reconciliation job to reconcile user data from an Authoritative application.
Note:
Before you run this job, ensure that the accounts in the target system have a unique User ID. Otherwise, you might observe unexpected results while running the job. -
OID Connector Trusted User Delete Reconciliation: Use this reconciliation job to reconcile user records that are deleted from an Authoritative Application.
Table 3-15 describes the parameters of the OID Trusted User Reconciliation job.
Table 3-15 Parameters of the OID Connector Trusted User Reconciliation Job
| Parameter | Description |
|---|---|
|
Application name |
Name of the AOB Application with which the job is associated. This value is the same as the value that you provided for the Application Name field while creating your authoritative application. Do not modify this value. |
|
Filter |
Enter the search filter for fetching user records from the authoritative application during a reconciliation run. Sample value: |
|
Object Type |
This parameter holds the type of object you want to reconcile. Default value: Do not modify the value of this parameter. |
|
Incremental Recon Attribute |
Name of the target system attribute that holds the timestamp at which the user record was modified. Default value: |
|
Scheduled Task Name |
Name of the scheduled task used for reconciliation. Note: For the scheduled job included with this connector, you must not change the value of this parameter. However, if you create a new job or create a copy of the job, then enter the unique name for that scheduled job as the value of this parameter. |
|
Latest Token |
This parameter holds the value of the target system attribute that is specified as the value of the Incremental Recon Attribute parameter. The connector uses the Latest Token parameter for internal purposes. By default, this value is empty. Note: Do not enter a value for this attribute. The reconciliation engine automatically enters a value for this attribute after execution. It is recommended that you do not change the value of this attribute. If you manually specify a value for this attribute, then only user accounts that have been modified after the time stamp specified as the value of this attribute are reconciled. If you want to perform a full reconciliation, then clear the value in this field. Sample value: |
Table 3-16 Parameters of the OID Connector Trusted User Delete Reconciliation Job
| Parameter | Description |
|---|---|
|
Application name |
Name of the AOB Application with which the job is associated. This value is the same as the value that you provided for the Application Name field while creating your authoritative application. Do not modify this value. |
|
Object Type |
This parameter holds the type of object you want to reconcile. Default value: Do not modify the value of this parameter. |