41 Users, Sites, and Roles in LDAP‐Integrated Sites Systems
Topics:
LDAP-Integrated WebCenter Sites Systems
WebCenter Sites can be integrated with LDAP servers that use the LDAP-2 protocol or any other protocol (although, in the latter case, write operations from the administrator's interface to the LDAP server are not supported).
This overview summarizes
-
the types of LDAP schema that WebCenter Sites supports,
-
operations that can be performed from the WebCenter Sites interface when each type of schema is deployed, and
-
the outcome of the operations, given the permissions of the WebCenter Sites administrator to the LDAP server and the nature of the LDAP server.
Topics:
LDAP Schema
The following LDAP-schema scenarios are covered in this chapter: flat- and hierarchical-schema LDAP. Each schema supports selected operations and installations:
-
Both flat- and hierarchical-schema LDAP support operations on ACLs and users (user accounts, user profiles, and user attributes) in WebCenter Sites.
-
Flat-schema LDAP supports operations on sites and roles in WebCenter Sites and levels the sites and roles so that no hierarchy exists among them.
-
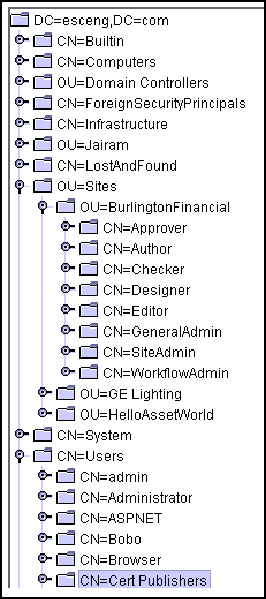
Hierarchical-schema LDAP supports operations on sites and roles in WebCenter Sites. This schema requires LDAP users to define a site organizational unit in the LDAP server in which roles must be subordinated to their relevant sites (for an example, see the following figure).
The following table summarizes LDAP schema and the possible operations. Using the correct schema, the WebCenter Sites administrator can perform operations in the WebCenter Sites interface and have them propagate to the WebCenter Sites database, or the LDAP server, or both, depending also on the conditions that are outlined in LDAP Connectivity for Site and Role Management.
Table 41-1 LDAP Integration Scenarios
| Create/Modify/Delete Operations on... | Flat-Schema LDAP | Hierarchical-Schema LDAP |
|---|---|---|
|
ACLs, Users, User Profiles, User Attributes |
||
|
Sites and Roles |
LDAP Connectivity for Site and Role Management
For operations on roles and sites to work as described in this chapter, LDAP connectivity must be enabled. Use the Property Management Tool in the Admin interface to set the values of two properties in the wcs_properties.json file:
xcelerate.usermanagerclass xcelerate.rolemanagerclass
These properties allow you to manage sites and roles directly in the LDAP server (as shown in this appendix) or exclusively in the database.
-
If the property values specify LDAP, then LDAP connectivity is established. Sites and roles can be managed in the LDAP server (and in the database).
-
For hierarchical-schema LDAP, only the
xcelerate.usermanagerclassproperty must specify LDAP. Thexcelerate.rolemanagerclassproperty uses the default value. For example:xcelerate.usermanagerclass=
com.openmarket.xcelerate.user.LDAPSchemaUserManagerxcelerate.rolemanagerclass=com.openmarket.xcelerate.roles.RoleManager
-
For flat-schema LDAP, both properties must specify LDAP. For example:
xcelerate.usermanagerclass=
com.openmarket.xcelerate.user.FlatLDAPSchemaUserManagerxcelerate.rolemanagerclass=com.openmarket.xcelerate.roles.FlatLDAPSchemaRoleManager
-
-
If the property values do not specify LDAP (for example,
xcelerate.usermanagerclass=com.openmarket.xcelerate.user.usermanager) then sites and roles can be managed only in the database.
LDAP Users and Their Permissions to LDAP Servers
In an LDAP-integrated system, the administrator of the system may or may not be an administrative user of the LDAP server, depending on the value of the jndi.connectAsUser property in the wcs_properties.json file, categorized under User. The value determines how the administrator is connected to the LDAP server, and therefore defines the LDAP user:
-
If jndi.connectAsUser is set to
true, then defines the LDAP user to be the same one that is logged in to and connects that user to the LDAP server. -
If jndi.connectAsUser is set to
false, then defines the LDAP user to be the one that is specified in thejndi.loginproperty (in thewcs_properties.jsonfile, categorized under User) and connects that user to the LDAP server.
For the connection to take place, the user and his permissions must also be defined in the LDAP server. If the user has read-only permissions to the LDAP server, he is not an administrative LDAP user. If the user has read and write permissions to the LDAP server, he is an administrative LDAP user (or simply, an LDAP administrator).
Note:
All LDAP properties are prefixed by jndi. For more information about LDAP-related properties, see User Properties in the Property Files Reference for Oracle WebCenter Sites.
LDAP-Integrated Operations
For the administrator to successfully perform an operation (such as creating an ACL in both the database and the LDAP server), it is critical for to be properly integrated with the LDAP server. Barring integration issues, the outcome of an operation depends on the following factors:
-
The LDAP user, as defined by the jndi.connectAsUser property (see the previous section).
-
The LDAP user's permissions, as defined in the LDAP server.
If the administrator is connected to the LDAP server as a user without administrative rights, his operations (such as deleting an ACL from the database) cannot be written to the LDAP server. The system responds by either writing the operations to the database, or not at all. The operations must then be repeated in the administrator's interface and performed manually in the LDAP server by an LDAP administrator.
-
The nature of the operation.
Certain operations that are performed in the administrator's interface (such as editing an ACL) are not written to the LDAP server, even when the administrator is connected with write permissions.
-
Whether the LDAP server supports the LDAP-2 protocol.
If the LDAP server does not support the LDAP-2 protocol, then write operations from the administrator's interface to the LDAP server are not supported, and the result of an operation cannot always be predicted.
Table 41-2, Table 41-3 and Table 41-4 summarize the results of operations that can be performed by a administrator who is connected to the LDAP server as a user with read-only and read/write permissions.
User Management Operations
Table 41-2 applies to flat- and hierarchical-schema LDAP web environments and summarizes system response to user management operations. The operations are performed by a WebCenter Sites administrator using the interfaces of three WebCenter Sites systems, each integrated with an LDAP option:
-
LDAP-2 server with read-only permissions for the LDAP user (defined in LDAP Connectivity for Site and Role Management).
-
LDAP-2 server with write permissions for the LDAP user.
-
LDAP server other than LDAP-2, in which case write operations are not supported.
The results of each user management operation are described on the pages that are noted in the left-hand column of Table 41-2.
Note:
The term "user management" in this appendix includes the management of ACLs, user accounts, user profiles, and user attributes.
Table 41-2 System Response to User Management Operations in WebCenter Sites
| Operation in WebCenter Sites | Result | System Response with LDAP-2: User has Read-Only Permissions (see note 1) | System Response with LDAP-2: User has Write Permissions (see note 2) | System Response with Other LDAP Server: Write not Supported (see note 3) |
|---|---|---|---|---|
|
ACL is created in: |
Returns error (see note 4) |
LDAP + WebCenter Sites database |
Unpredictable |
|
|
ACL is modified in: |
WebCenter Sites database |
WebCenter Sites database |
WebCenter Sites database |
|
|
ACL is deleted in: |
Returns error |
LDAP + WebCenter Sites database |
Unpredictable |
|
|
ACL is assigned in: |
WebCenter Sites database |
WebCenter Sites database |
WebCenter Sites database |
|
|
LDAP Server Response for Assigning ACLs to WebCenter Sites Pages (Site Catalog Page Entries) |
ACL is assigned in: |
WebCenter Sites database |
WebCenter Sites database |
WebCenter Sites database |
|
LDAP Server Response for Creating a User (Granting ACLs for Access Privileges) |
User is created in: |
Returns error |
LDAP |
Unpredictable |
|
User is modified in: |
Returns error |
LDAP |
Unpredictable |
|
|
User is deleted from: |
Returns error |
LDAP |
Unpredictable |
|
|
User profile is created/edited in: |
Returns error |
LDAP |
Unpredictable |
|
|
User profile is deleted from: |
Returns error |
LDAP |
Unpredictable |
|
|
User profile is created in: |
Returns error |
LDAP |
Unpredictable |
|
|
User profile is deleted from: |
Returns error |
LDAP |
Unpredictable |
Note:
-
ACLs and users cannot be stored in the LDAP server (the WebCenter Sites administrator is connected to the LDAP server as a user without write permissions.
-
ACLs and users can be stored in the LDAP server (the WebCenter Sites administrator is connected to the LDAP server as a user with write permissions.
-
The LDAP server does not support the LDAP-2 protocol (such as Netscape Server). For non-compliant LDAP servers, write operations from the administrator's interface to the LDAP server are not supported.
-
"Returns error" means that the operation is not performed (the system returns an error).
The following topics provide reference information about user management options:
LDAP Server Response for Creating an ACL
User Management Operation:
The administrator attempts to create an ACL by using the User Access Management node on the Admin tab.
System Response:
-
LDAP-2 Server with Read-Only Permissions—The system returns an error message; it cannot create the ACL. The LDAP administrator must first create the ACL manually in the LDAP server and then in the database.
-
LDAP-2 Server with Write Permissions—The system creates the ACL in both the LDAP server and the database.
-
Not LDAP-2: Write not Supported—Response is unpredictable. The LDAP administrator must first create the ACL in the LDAP server and then in .
LDAP Server Response for Editing an ACL
User Management Operation:
The WebCenter Sites administrator attempts to modify an ACL by using the User Access Management node on the Admin tab.
Note:
The WebCenter Sites administrator can modify either the description of the ACL, or the permission associated with the ACL, but not the ACL's name.
System Response:
-
LDAP-2 Server with Read-Only Permissions—The system modifies the ACL in the WebCenter Sites database. The modification is stored only in the database, even with LDAP integration.
-
LDAP-2 Server with Write Permissions—Responds as above (scenario 1).
-
Not LDAP-2: Write not Supported—Responds as above (scenario 1).
LDAP Server Response for Deleting an ACL
User Management Operation:
The WebCenter Sites administrator attempts to delete an ACL by using the User Access Management node on the Admin tab.
System Response:
-
LDAP-2 Server with Read-Only Permissions—The system returns an error message; it cannot delete the ACL. The LDAP administrator must first delete the ACL from the LDAP server and then from the WebCenter Sites database.
-
LDAP-2 Server with Write Permissions—The system deletes the ACL from the LDAP server and from the WebCenter Sites database.
-
Not LDAP-2: Write not Supported—Behavior is unpredictable. The LDAP administrator must first delete the ACL from the LDAP server before attempting to delete the ACL from WebCenter Sites.
LDAP Server Response for Assigning ACLs to Tables
User Management Operation:
The WebCenter Sites administrator attempts to assign an ACL to system tables.
System Response:
-
LDAP-2 Server with Read-Only Permissions—The system assigns the ACLs to the database tables. If the ACLs cannot be assigned, the system returns an error message.
-
LDAP-2 Server with Write Permissions—Responds as above (scenario 1).
-
Not LDAP-2: Write not Supported—Responds as above (scenario 1).
LDAP Server Response for Assigning ACLs to WebCenter Sites Pages (Site Catalog Page Entries)
User Management Operation:
The WebCenter Sites administrator attempts to assign an ACL to WebCenter Sites Pages.
System Response:
-
LDAP-2 Server with Read-Only Permissions—The system adds the selected ACLs for the specified WebCenter Sites Page. If the ACLs cannot be assigned, the system returns an error message.
-
LDAP-2 Server with Write Permissions—Responds as above (scenario 1).
-
Not LDAP-2: Write not Supported—Responds as above (scenario 1).
LDAP Server Response for Creating a User (Granting ACLs for Access Privileges)
User Management Operation:
You can attempt to create a user by using the User Access Management node under the Admin node of the General Admin tree.
Note:
WebCenter Sites shows only the ACLs that are stored in its database.
System Response:
-
LDAP-2 Server with Read-Only Permissions—The system returns an error message; it cannot add the user and the user's assigned ACLs. The LDAP administrator must use the LDAP server to manually add the user to the LDAP server and assign ACLs to the user.
-
LDAP-2 Server with Write Permissions—The system creates the user in the LDAP server and assigns ACLs to the user.
-
Not LDAP-2: Write not Supported—Behavior is unpredictable. The LDAP administrator must use the LDAP server to manually add the user to the LDAP server and assign ACLs to the user.
LDAP Server Response for Editing a User
User Management Operation:
You can attempt to modify the ACLs that are assigned to a user or to change the user's password by using the User Access Management node under the Admin node of the General Admin tree.
Note:
The Modify user operation allows you to change only the user password and the ACLs that are associated with the user.
The Modify user attributes operation allows you to change all attributes that are stored in the database or in the LDAP server.
System Response:
-
LDAP-2 Server with Read-Only Permissions—The system returns an error message; it cannot modify the user's password or ACLs. The LDAP administrator must manually modify the user in the LDAP server.
-
LDAP-2 Server with Write Permissions—The system modifies the user's password and/or assigned ACLs in the LDAP server.
-
Not LDAP-2: Write not Supported—Behavior is unpredictable. The LDAP administrator must manually modify the user in the LDAP server.
LDAP Server Response for Deleting a User
User Management Operation:
You can attempt to delete a user by using the User Access Management node under the Admin node of the General Admin tree.
Before deleting a user, the administrator must delete the user profile. If a user profile exists, an error message is triggered. The behavior described below is expected when no user profile exists for the user being deleted.
System Response:
-
LDAP-2 Server with Read-Only Permissions—The system returns an error message; it cannot delete the user. The LDAP administrator must manually delete the user from LDAP server.
-
LDAP-2 Server with Write Permissions—The system deletes the user from the LDAP server.
-
Not LDAP-2: Write not Supported—Behavior is unpredictable. The LDAP administrator must manually delete the user from the LDAP server.
LDAP Server Response for Creating/Editing a User Profile
User Management Operation:
The WebCenter Sites administrator attempts to create or modify a user profile by using the User Profiles node under Admin node of the General Admin tree.
System Response:
-
LDAP-2 Server with Read-Only Permissions—The system returns an error message; it cannot update the user's profile or Locale Preference. The LDAP administrator must manually update the user profile in the LDAP server.
-
LDAP-2 Server with Write Permissions—The system updates the user's profile or locale preference in the LDAP server.
-
Not LDAP-2: Write not Supported—Behavior is unpredictable. The LDAP administrator must manually update the user profile in the LDAP server.
LDAP Server Response for Deleting a User Profile
User Management Operation:
You can attempt to delete a user profile by using the User Profiles node under the Admin node of the General Admin tree.
System Response:
-
LDAP-2 Server with Read-Only Permissions—The system returns an error message; it cannot delete the user's profile. The LDAP administrator must manually delete the user profile in the LDAP server.
-
LDAP-2 Server with Write Permissions—The system deletes the user's profile from the LDAP server.
-
Not LDAP-2: Write not Supported—Behavior is unpredictable. The LDAP administrator must manually delete the user profile from the LDAP server.
LDAP Server Response for Creating User Attributes
User Management Operation:
The WebCenter Sites administrator attempts to create attributes for the user from the User Access Management node under the Admin node of the General Admin tree.
Note:
User attributes are stored in only one place—either in the database or in LDAP.
System Response:
-
LDAP-2 Server with Read-Only Permissions—The system returns an error message; it cannot add the new attributes to the LDAP server. The LDAP administrator must manually add user attributes to the LDAP server.
-
LDAP-2 Server with Write Permissions—The system adds the user's new attributes to the LDAP server.
-
Not LDAP-2: Write not Supported—Behavior is unpredictable. The LDAP administrator must manually add user attributes to the LDAP server.
LDAP Server Response for Editing/Deleting User Attributes
User Management Operation:
You can attempt to delete a user attributes by using the User Access Management node under the Admin node of the General Admin tree.
System Response:
-
LDAP-2 Server with Read-Only Permissions—The system returns an error message; it cannot modify or delete the user's attributes from the LDAP server. The LDAP administrator must manually modify user attributes in the LDAP server and delete user attributes from the LDAP server.
-
LDAP-2 Server with Write Permissions—The system modifies the user attributes in the LDAP server and deletes them from the LDAP server.
-
Not LDAP-2: Write not Supported—Behavior is unpredictable. The LDAP administrator must manually modify user attributes in the LDAP server, and manually delete user attributes from the LDAP server.
Site and Role Management Operations
The following topics provide information about site and role management operations with flat- and hierarchical-schema LDAP servers.
Operations with Flat-Schema LDAP Servers
The following table summarizes system response to site and role management operations. The operations are performed by a WebCenter Sites administrator using the interfaces of three WebCenter Sites systems, each integrated with an LDAP option:
-
An LDAP-2 server with read-only permissions for the LDAP user (defined in LDAP Connectivity for Site and Role Management).
-
An LDAP-2 server with write permissions for the LDAP user.
-
An LDAP server other than LDAP-2, in which case write operations are not supported.
The results of each operation are described in the sections that are noted in the left-hand column of the following table .
Table 41-3 System Response to Site and Role Management Operations with Flat-Schema LDAP
| Operation in WebCenter Sites | Results | System Response with Flat-Schema LDAP-2: User has Read Only Permissions (see note 1) | System Response with Flat-Schema LDAP-2: User has Write Permissions (see note 2) | System Response with Flat-Schema LDAP Server (Other Than LDAP-2): Write Not Supported (see note 3) |
|---|---|---|---|---|
|
Site is created in: |
WebCenter Sites database |
WebCenter Sites database |
WebCenter Sites database |
|
|
Site is edited in: |
WebCenter Sites database |
WebCenter Sites database |
WebCenter Sites database |
|
|
Site is deleted from: |
WebCenter Sites database |
WebCenter Sites database |
WebCenter Sites database |
|
|
Role is created in: |
Returns error (see note 4) |
LDAP + WebCenter Sites database (see note 5) |
Unpredictable |
|
|
Role is edited in: |
WebCenter Sites database |
WebCenter Sites database |
WebCenter Sites database |
|
|
Role is deleted from: |
Returns error |
LDAP + WebCenter Sites database |
Unpredictable |
|
|
Access is granted in: |
Returns error |
LDAP |
Unpredictable |
|
|
Access is removed from: |
Returns error |
LDAP |
Unpredictable |
Note:
-
Sites and roles cannot be stored in the LDAP server (the WebCenter Sites administrator is connected to the LDAP server as a user without write permissions).
-
Sites and roles can be stored in the LDAP server (the WebCenter Sites administrator is connected to the LDAP server as a user with write permissions).
-
The LDAP server does not support the LDAP-2 protocol (such as Netscape Server). For non-compliant LDAP server, write operations from the administrator's interface to the LDAP server are not supported.
-
"Returns error" means that the operation is not performed (the system returns an error).
-
For a role to be created in both the LDAP server and the WebCenter Sites database, at least one site must exist in the LDAP server. If no site exists, the role is created only in the WebCenter Sites database.
Operations with Hierarchical-Schema LDAP Servers
The following table summarizes system response to site and role management operations. The operations are performed by a WebCenter Sites administrator using the interfaces of three WebCenter Sites systems, each integrated with an LDAP option:
-
An LDAP-2 server with read-only permissions for the LDAP user (defined )
-
An LDAP-2 server with write permissions for the LDAP user
-
An LDAP server other than LDAP-2, in which case write operations are not supported
The results of each operation are described in the sections that are noted in the left-hand column of the following table .
Table 41-4 System Response to Site and Role Management Operations with Hierarchical-Schema LDAP (WebCenter Sites Web Applications)
| Operation in WebCenter Sites | Results | System Response with Hierarchical-Schema LDAP-2: User has Read-Only Permissions (see note 1) | System Response with Hierarchical-Schema LDAP-2: User has Write Permissions (see note 2) | System Response with Hierarchical-Schema LDAP Server (Other Than LDAP-2): Write Not Supported (see note 3) |
|---|---|---|---|---|
|
Site is created in: |
WebCenter Sites database |
WebCenter Sites database |
WebCenter Sites database |
|
|
Site is edited in: |
WebCenter Sites database |
WebCenter Sites database |
WebCenter Sites database |
|
|
Site is deleted in: |
WebCenter Sites database |
WebCenter Sites database |
WebCenter Sites database |
|
|
Role is created in: |
WebCenter Sites database |
WebCenter Sites database |
WebCenter Sites database |
|
|
Role is edited in: |
WebCenter Sites database |
WebCenter Sites database |
WebCenter Sites database |
|
|
Role is deleted in: |
WebCenter Sites database |
WebCenter Sites database |
WebCenter Sites database |
|
|
Access is granted in: |
Returns error (see note 4) |
LDAP |
Unpredictable |
|
|
Access is removed from: |
neither the WebCenter Sites database nor the LDAP server |
neither the WebCenter Sites database nor the LDAP server |
neither the WebCenter Sites database nor the LDAP server |
Note:
-
Sites and roles cannot be stored in the LDAP server (the WebCenter Sites administrator is connected to the LDAP server as a user without write permissions).
-
Sites and roles can be stored in the LDAP server (the WebCenter Sites administrator is connected to the LDAP server as a user with write permissions).
-
The LDAP server does not support the LDAP-2 protocol (such as Netscape Server). For non-compliant LDAP servers, write operations from the administrator's interface to the LDAP server are not supported.
-
"Returns error" means that the operation is not performed (the system returns an error).
LDAP Server Response for Creating a Site
Site Management Operation:
You can attempt to create a site by using the Sites node under the Admin node of the General Admin tree.
Note:
If you are manually creating a site in an LDAP-integrated system, you must ensure that the database and the LDAP server are synchronized. Otherwise, sites are not properly listed in the WebCenter Sites interfaces.
System Response - Hierarchical Schema:
-
LDAP-2 Server with Read-Only Permissions—The system creates the site in the WebCenter Sites database. The LDAP administrator must create the site entry in the LDAP server.
-
LDAP-2 Server with Write Permissions—Responds as above (scenario 1).
-
Not LDAP-2: Write not Supported—Responds as above (scenario 1).
System Response - Flat Schema:
-
LDAP server with Read-Only Permissions—The system creates the site in the WebCenter Sites database. The administrator must create an entry for all available roles by prefixing each site name to the role name in the LDAP server.
-
LDAP-2 Server with Write Permissions—Responds as above (scenario 1).
-
Not LDAP-2: Write not Supported—Responds as above (scenario 1).
LDAP Server Response for Editing a Site
Site Management Operation:
You can attempt to edit the description of a site by using the Site Edit option on the Admin node.
System Response - Hierarchical Schema:
-
LDAP-2 Server with Read-Only Permissions—The system modifies the site description in the WebCenter Sites database. (The site description is stored only in the WebCenter Sites database, even with LDAP integration.)
-
LDAP-2 Server with Write Permissions—Responds as above (scenario 1).
-
Not LDAP-2: Write not Supported—Responds as above (scenario 1).
System Response - Flat Schema:
-
LDAP-2 Server with Read-Only Permissions—The system modifies the site description in the WebCenter Sites database. (The site description is stored only in the WebCenter Sites database, even with LDAP integration.)
-
LDAP-2 Server with Write Permissions—Responds as above (scenario 1).
-
Not LDAP-2: Write not Supported—Responds as above (scenario 1).
LDAP Server Response for Deleting a Site
Site Management Operation:
-
In the General Admin tree, expand the Admin node, expand the Sites node, and then double-click the site you want to edit.
-
In the Site form, click Edit at the top of the form.
Note:
If you are manually deleting a site with LDAP integration, you must ensure that the database and the LDAP server are synchronized. Otherwise, sites are not properly listed in the WebCenter Sites interfaces.
System Response - Hierarchical Schema:
-
LDAP-2 Server with Read-Only Permissions—The system deletes the site from the WebCenter Sites database. The LDAP administrator must manually delete the site entry from the LDAP server.
-
LDAP-2 Server with Write Permissions—Responds as above (scenario 1).
-
Not LDAP-2: Write not Supported—Responds as above (scenario 1).
System Response - Flat Schema:
-
LDAP-2 Server with Read-Only Permissions—The system deletes the site from the WebCenter Sites database. The LDAP administrator must manually delete the site entry from the LDAP server.
-
LDAP-2 Server with Write permissions—Responds as above (scenario 1).
-
Not LDAP-2: Write not Supported—Responds as above (scenario 1).
LDAP Server Response for Granting Users Access to Sites
Site Management Operation:
The WebCenter Sites administrator attempts to grant users access to a site by using the Users node of the site, under the Sites node of the Admin node, in the General Admin tree.
Note:
WebCenter Sites shows only the roles that are stored in its database.
System Response - Hierarchical Schema:
-
LDAP-2 Server with Read-Only Permissions—The system returns an error message because, in the LDAP server, it cannot assign any roles to the specified users of the selected site. The LDAP administrator must manually assign the roles.
-
LDAP-2 Server with Write Permissions—The system assigns roles, within the LDAP server, to the specified users of the selected site.
-
Not LDAP-2: Write not Supported—Behavior is unpredictable.
System Response - Flat Schema:
-
LDAP-2 Server with Read-Only Permissions—The system returns an error message because, in the LDAP server, it cannot assign any roles to the specified users of the selected site. The LDAP administrator must manually assign the roles.
-
LDAP-2 Server with Write Permissions—The system assigns roles, within the LDAP server, to the specified users of the selected site.
-
Not LDAP-2: Write not Supported—Behavior is unpredictable.
LDAP Server Response for Removing Users' Access to Sites
Site Management Operation:
The WebCenter Sites administrator attempts to remove user access to sites by using the Users node of the site, under the Sites node of the Admin node, in the General Admin tree.
Note:
WebCenter Sites shows only the sites that are stored in its interface.
System Response - Hierarchical Schema:
-
LDAP-2 Server with Read-Only Permissions—The LDAP administrator must manually remove the user's permissions to the sites, directly in the LDAP server.
-
LDAP-2 Server with Write Permissions—Responds as above (scenario 1).
-
Not LDAP-2: Write not Supported—Behavior is unpredictable.
System Response - Flat Schema:
-
LDAP-2 Server with Read-Only Permissions—The system returns an error message. The LDAP administrator must manually remove the user's permissions to the sites, directly in the LDAP server.
-
LDAP-2 Server with Write Permissions—The system removes the user's permissions to the sites, directly in the LDAP server.
-
Not LDAP-2: Write not Supported—Behavior is unpredictable.
LDAP Server Response for Creating a Role
Role Management Operation:
-
In the General Admin tree, expand the Admin node, expand the User Access Management node, expand the Roles node, and then double-click Add New.
-
In the Add New Role form, enter the Name and Description of the Role, and then click Add New Role.
System Response - Hierarchical Schema:
-
LDAP-2 Server with Read-Only Permissions—The system creates the role in the WebCenter Sites database. The LDAP administrator must manually create the role in the LDAP server.
-
LDAP-2 Server with Write Permissions—Responds as above (scenario 1).
-
Not LDAP-2: Write not Supported—Responds as above (scenario 1).
System Response - Flat Schema:
-
LDAP-2 Server with Read-Only Permissions—The system returns an error message; it cannot create the role in the LDAP server or in the WebCenter Sites database. The LDAP administrator must create the role in the LDAP server. The same role must be re-created in the WebCenter Sites database.
-
LDAP-2 Server with Write Permissions—The system creates the role in the WebCenter Sites database. The system also creates the role for all available sites in the LDAP server by pre-fixing the name of each existing site to the name of the role (SiteA-Role, SiteB-Role, and so on).
Note:
For a role to be created in both the LDAP server and the WebCenter Sites database, at least one site must exist in the LDAP server. If no sites exist, the role is created only in the WebCenter Sites database.
-
Not LDAP-2: Write not Supported—Behavior is unpredictable. An error message can be returned.
LDAP Server Response for Editing a Role
Role Management Operation:
-
In the General Admin tree, expand the Admin node, expand the User Access Management node, expand the Roles node, and then double-click the role you want to modify.
-
In the Role form, click Edit.
System Response - Hierarchical Schema:
-
LDAP-2 Server with Read-Only Permissions—The system modifies the description of the role in the WebCenter Sites database. (The role description is stored only in the WebCenter Sites database, even with LDAP integration.)
-
LDAP-2 Server with Write Permissions—Responds as above (scenario 1).
-
Not LDAP-2: Write not Supported—Responds as above (scenario 1).
System Response - Flat Schema:
-
LDAP-2 Server with Read-Only Permissions—The system modifies the description of the role in the WebCenter Sites database. (The role description is stored only in the WebCenter Sites database, even with LDAP integration.)
-
LDAP-2 Server with Read-Only Permissions—Responds as above (scenario 1).
-
Not LDAP-2: Write not Supported—Responds as above (scenario 1).
LDAP Server Response for Deleting a Role
Role Management Operation:
-
In the General Admin tree, expand the Admin node, expand the User Access Management node, expand the Roles node, and then double-click the role you want to modify.
-
In the Role form, click Delete, and then in the Delete Role form, click Delete Role.
System Response - Hierarchical Schema:
-
LDAP-2 Server with Read-Only Permissions—The system deletes the role from the WebCenter Sites database. The LDAP administrator must manually delete this role from the LDAP server.
-
LDAP-2 Server with Write Permissions—Responds as above (scenario 1).
-
Not LDAP-2: Write not Supported—Responds as above (scenario 1).
System Response - Flat Schema:
-
LDAP server with Read-Only Permissions—The system returns an error message; it cannot delete the role from either the LDAP server or the WebCenter Sites database. The LDAP administrator must create the sites and roles in the LDAP server. The same sites and roles must be re-created in the WebCenter Sites database.
-
LDAP-2 Server with Read-Only Permissions—The system deletes the role from both the WebCenter Sites database and the LDAP server.
-
Not LDAP-2: Write not Supported—Behavior is unpredictable. The system can return an error message.