6 Auditing for Vulnerabilities By Using OVAL Definitions
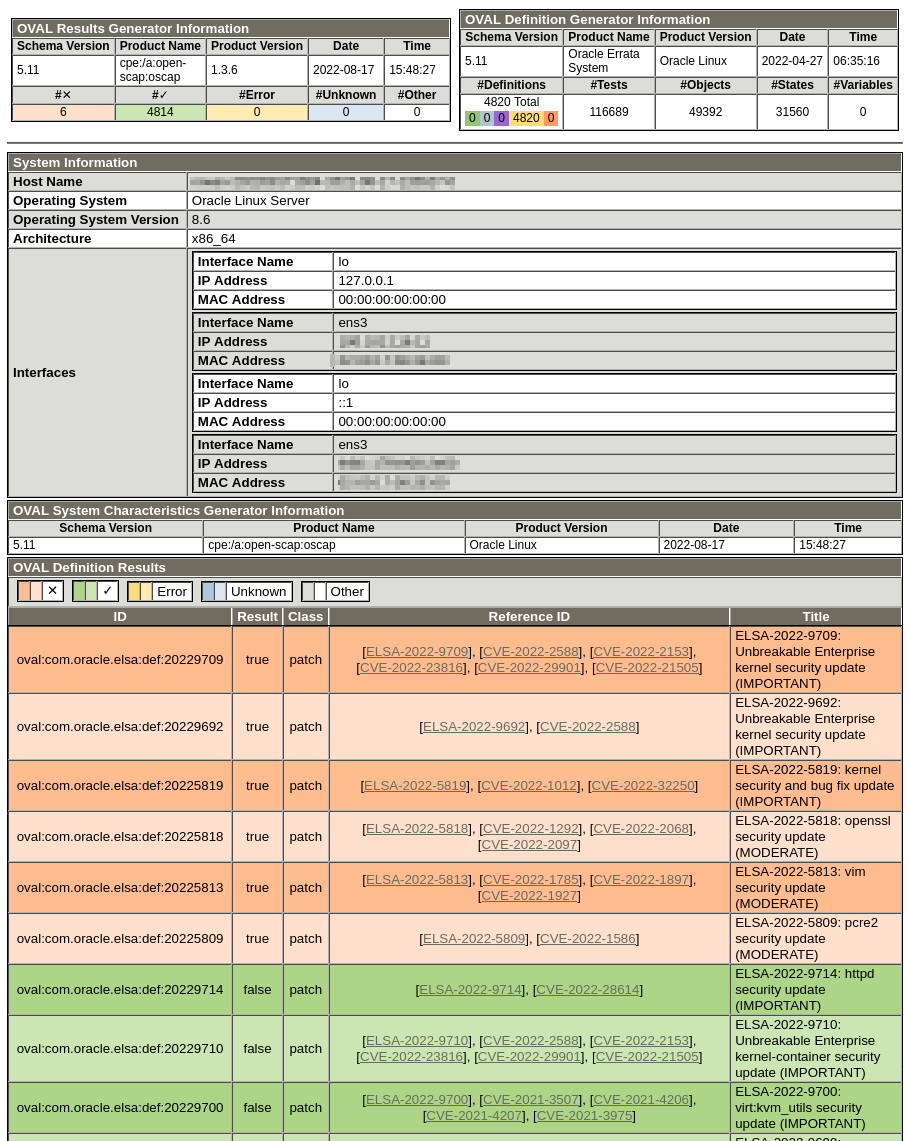
You can use OVAL definition files to audit a system for known vulnerabilities and configuration issues. By performing an OVAL auditing scan, you can see whether a system has had the appropriate security patches applied.
OVAL definition entries included in a SCAP data stream file can automatically download and apply remote OVAL definitions, such as the ones provided by Oracle at https://linux.oracle.com/security.
If you're working in a disconnected environment, you can manually download OVAL definition files to make available to systems within the environment. Scans can be performed with these local definition files using the --local-files option.
Downloading OVAL Files
Oracle provides OVAL definitions for all errata on ULN. Use these definitions to ensure that all applicable errata are installed on an Oracle Linux system.
Displaying Information About an OVAL File
You can display information about an OVAL file using the oscap info command.
The command syntax is as follows:
oscap info path/OVAL fileFor example:
oscap info com.oracle.elsa-2024.xmlThe output shows the OVAL version and when the file was generated and imported:
Document type: OVAL Definitions
OVAL version: 5.11
Generated: date and time
Imported: date and timeValidating OVAL Files
oscap validate command.
Use oscap validate and examine the exit code to validate an OVAL file against its schema. This confirms that the file is correctly formatted.
For example, to validate the com.oracle.elsa-2024.xml OVAL file, run the following command:
oscap oval validate com.oracle.elsa-2024.xml \
&& echo "ok" || echo "exit code = $? not ok"ok