Set Up a Private Interconnection Between Microsoft Azure and Oracle Cloud Regions
Oracle and Microsoft have partnered to provide cloud interoperability that enables you to build and deploy cross-cloud applications using a direct network connection between the cloud providers.
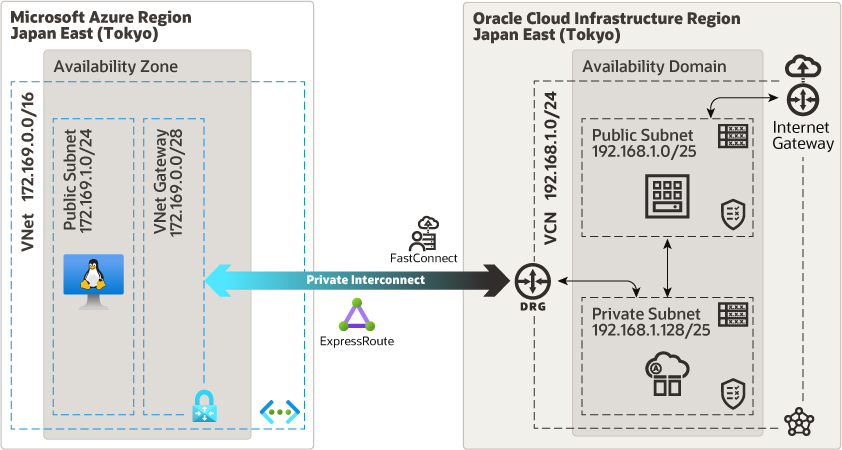
Architecture
This architecture shows how you can enable private, low-latency connectivity between your cloud resources in a Microsoft Azure region and resources in an Oracle Cloud Infrastructure region, such as an autonomous database with a private endpoint.
In this architecture, a virtual network (VNet) in a Microsoft Azure region is connected with a virtual cloud network (VCN) in an Oracle Cloud Infrastructure region using a private interconnection composed of Azure ExpressRoute and Oracle Cloud Infrastructure FastConnect.
The architecture has the following components:
- Region
A region is a localized geographic area composed of one or more availability domains. Regions are independent of other regions, and vast distances can separate them (across countries or continents).
You can set a private interconnection between Azure and Oracle Cloud in regions where this interconnection is available.
- Oracle Cloud
Infrastructure Components
- Availability domains
Availability domains are standalone, independent data centers within a region. The physical resources in each availability domain are isolated from the resources in the other availability domains, which provides fault tolerance. Availability domains don’t share infrastructure such as power or cooling, or the internal availability domain network. So, a failure at one availability domain is unlikely to affect the other availability domains in the region.
- Virtual cloud network (VCN) and subnet
A VCN is a customizable, software-defined network that you set up in an Oracle Cloud Infrastructure region. Like traditional data center networks, VCNs give you complete control over your network environment. A VCN can have multiple non-overlapping CIDR blocks that you can change after you create the VCN. You can segment a VCN into subnets, which can be scoped to a region or to an availability domain. Each subnet consists of a contiguous range of addresses that don't overlap with the other subnets in the VCN. You can change the size of a subnet after creation. A subnet can be public or private.
- Security list
For each subnet, you can create security rules that specify the source, destination, and type of traffic that must be allowed in and out of the subnet.
- Route table
Virtual route tables contain rules to route traffic from subnets to destinations outside a VCN, typically through gateways.
- Dynamic routing gateway (DRG)
The DRG is a virtual router that provides a path for private network traffic between a VCN and a network outside the region, such as a VCN in another Oracle Cloud Infrastructure region, an on-premises network, or a network in another cloud provider.
A DRG is required to set up a private interconnection using FastConnect between a VCN in an Oracle Cloud Infrastructure region and a VNet in an Azure region.
- FastConnect
Oracle Cloud Infrastructure FastConnect provides a dedicated, private connection between your Azure region and Oracle Cloud. FastConnect provides higher-bandwidth options and a more reliable and consistent networking experience than typical internet connections.
- Availability domains
- Microsoft Azure Components
- Virtual network (VNet) and subnet
A VNet is a virtual network that you define in Azure. A VNet can have multiple non-overlapping CIDR blocks subnets that you can add after your create the VNet. You can segment a VNet into subnets, which can be scoped to a region or to an availability zones. Each subnet consists of a contiguous range of addresses that don't overlap with the other subnets in the VNet. Use VNet to isolate your Azure resources logically at the network level.
- ExpressRoute
Azure ExpressRoute lets you set up a private connection between a VNet and another network, such as your on-premises network or a network in another cloud provider. ExpressRoute is a more reliable and faster alternative to typical internet connections, because the traffic over ExpressRoute doesn't traverse the public internet.
- Virtual network gateway
A virtual network gateway allows traffic between an Azure VNet and a network outside Azure, either over the public internet or using ExpressRoute, depending on the gateway type that you specify.
- Route table
Route tables direct traffic between Azure subnets, VNets, and networks outside Azure.
- Network security group
A network security group contains rules to control network traffic between the Azure resources within a VNet. Each rule specifies the source or destination, port, protocol, and direction of network traffic that's allowed or denied.
- Virtual network (VNet) and subnet
Recommendations
Use the following recommendations as a starting point to set up a private interconnection between Microsoft Azure and Oracle Cloud. Your requirements might differ from the architecture described here.
- VCN
Note:
These recommendations apply to the Azure VNet as well.When you create a VCN, determine the number of CIDR blocks required and the size of each block based on the number of resources that you plan to attach to subnets in the VCN. Use CIDR blocks that are within the standard private IP address space.
Select CIDR blocks that don't overlap with any other network (in Oracle Cloud Infrastructure, your on-premises data center, or another cloud provider) to which you intend to set up private connections.
After you create a VCN, you can change, add, and remove its CIDR blocks.
- Azure virtual network gateway: SKUs
While creating a virtual network gateway in Azure, you select a gateway SKU. The SKU you select determines the CPUs and network bandwidth allocated to the gateway.
- Azure virtual network gateway: FastPath
You can use Azure ExpressRoute FastPath to improve the data-path performance between your VNet and other connected networks. FastPath routes traffic directly to resources in the VNet, bypassing the virtual network gateway.
Azure FastPath is available only with the UltraPerformance SKU or ErGw3AZ. For reduced latency between Azure and Oracle Cloud Infrastructure, consider using FastPath.
- Security
The traffic within Azure and Oracle Cloud networks is fully encrypted, and the traffic flow between Azure and Oracle Cloud flows directly through the private physical connection. You can further restrict the flow of traffic on the private interconnection by using network security groups (NSGs) and security lists.
Considerations
When implementing a private interconnection between Azure and Oracle Cloud Infrastructure, consider the following factors:
- Cost
- Oracle Cloud
Infrastructure FastConnect
The cost of FastConnect is the same across all the Oracle Cloud Infrastructure regions. There are no separate ingress or egress data charges.
- Azure ExpressRoute
The Azure ExpressRoute cost varies from one region to another. Azure has more than one SKU available for an express route; Oracle recommends using the Local setting, because it has no separate ingress or egress charges, and it starts at the minimum bandwidth of 1 Gbps. The Standard and Premium configurations offer lower bandwidth, but incur separate egress charges in a metered setup.
- Oracle Cloud
Infrastructure FastConnect
- Border gateway protocol (BGP)
The connection between the Azure VNet and the Oracle Cloud VCN uses BGP dynamic routing. When you set up the Oracle virtual circuit, you provide the BGP IP addresses that are used for the two redundant BGP sessions between Oracle and Azure. For each pair, specify a nonoverlapping, separate /30-block of addresses.
FastConnect always uses BGP for route advertisements.
- High availability
Every interconnect circuit (ExpressRoute and FastConnect) comes with a redundant circuit on the same POP but different physical router, providing high availability.
- Disaster recovery (DR)
To enable customers to deploy an effective DR architecture, we offer more than one interconnect region in each geography, such as US East and US West in North America.
- Support for transit routing
You can extend the Oracle Cloud Infrastructure–Microsoft Azure interconnect to a transit routing setup, either within Oracle Cloud or in Azure.
Deploy
The code for setting up an interconnect circuit as a new or an existing environment available on Github. You can also download the code from GitHub, and customize it to suit your specific business requirements.
- Go to the Github repository.
- Clone or download the repository to your local computer.
- Follow the instructions in the
READMEdocument.
Explore More
Learn more about setting up private interconnections between Microsoft Azure and Oracle Cloud.
- Set Up Oracle Cloud Infrastructure Access to Microsoft Azure
- Example of how to set up interconnect by using Terraform
- Oracle Cloud Infrastructure FastConnect Pricing
- Microsoft Azure ExpressRoute Virtual Network Gateway SKUs
- Microsoft Azure ExpressRoute Overview
- Microsoft Azure ExpressRoute Pricing
- Learn about interconnecting Oracle Cloud with Microsoft Azure
- Set up a hub-and-spoke network topology