Learn About Security in Oracle Cloud Infrastructure
Your applications need reliable, high-performance, and cost-effective cloud solutions that meet all your security, data protection, and compliance requirements. Oracle Cloud is built on a foundation of state-of-the-art security technologies and operational processes that allow you to exercise complete control with unmatched security.
Use this document to learn about the security design principles of Oracle Cloud Infrastructure and understand the shared security model. Review the wide range of security controls that you can use to build the most secure cloud topology for your mission-critical enterprise applications and modern cloud-native workloads.
The checklists included in this document align with the best practices for security and compliance, as described in Best practices framework for Oracle Cloud Infrastructure.
Security Pillars
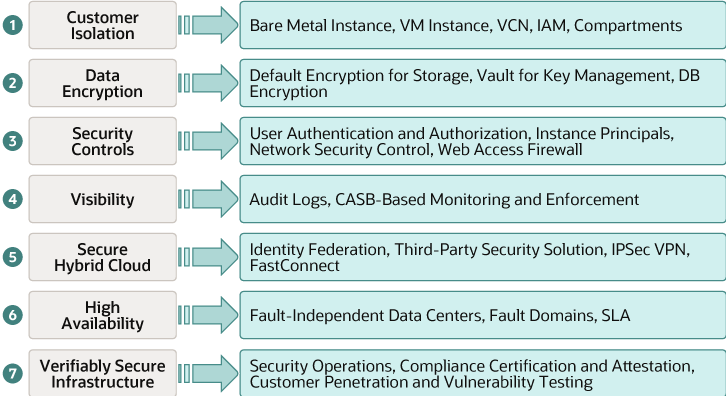
Security in Oracle Cloud Infrastructure is based on seven core pillars. Each pillar includes multiple solutions designed to maximize the security and compliance of the platform.
- Customer isolation: Isolate your application, data, and resources in the cloud from other tenants and Oracle.
- Data encryption: Protect your data by using security controls, and fulfill your security and compliance requirements.
- Security controls: Reduce the risks associated with malicious and accidental user actions by managing access to your services and segregating operational responsibilities.
- Visibility: Minimize security and operational risk by auditing and monitoring actions on your resources through comprehensive logs and security monitoring solutions.
- Secure hybrid cloud: Use your existing security assets—such as user accounts, policies, and third-party security solutions—when accessing cloud resources and securing data and application assets.
- High availability: Ensure consistent up time for your workloads, by taking advantage of fault-tolerant data centers that are resilient against network attacks.
- Verifiably secure infrastructure: Run business-critical workloads on a verifiably secure infrastructure that implements rigorous processes and security controls in all the phases of development and operation.
Oracle Cloud Infrastructure services are compliant with a wide range of standards and requirements, including FedRAMP, FIPS 140-2, GDPR, HIPAA, PCI DSS, and SOC 1/2/3. For the complete list of compliance certifications and attestations, see Oracle Cloud Compliance.
The following figure shows the key Oracle Cloud Infrastructure services and features that constitute the seven core security pillars:
Design Principles
Apply the following design principles to deploy, operate, and use your applications securely in Oracle Cloud Infrastructure:
- Understand and implement the security services and features of Oracle Cloud Infrastructure. See Security Services and Features.
- Understand the shared security responsibility model. See the next section.
- Implement the principles of least privilege and separation of duties.
Limit privileges as much as possible. Users should be given only the access that's essential to perform their work. Review user privileges periodically to determine relevance to the current work requirements.
- Implement multilayer security mechanisms.
- Protect data at rest and in transit.
- Monitor and respond to security events.
Monitor system activity. Establish who should access which system components, and how often; and monitor those components.
- Stay up to date on security alerts, patches, and software updates.
Oracle regularly issues security-related patch updates and security alerts. Install all security patches as soon as possible. See Critical Patch Updates, Security Alerts and Bulletins.
- Implement security-related best practices. See Security Best Practices.
Shared Security Model
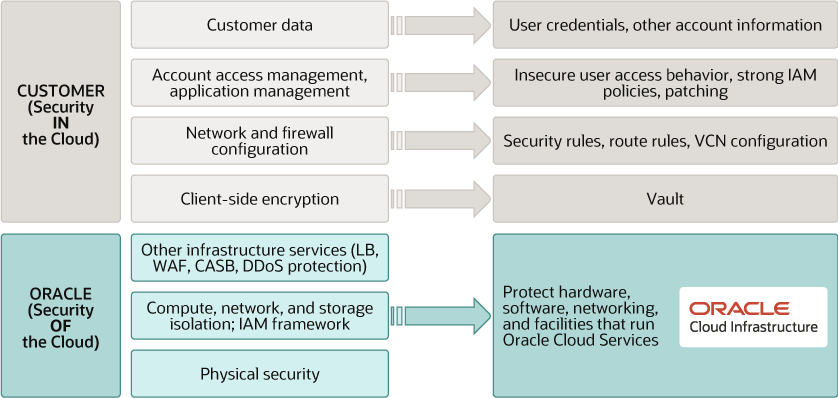
Oracle employs best-in-class, enterprise-grade security technology and operational processes to secure the cloud services. To deploy and operate your workloads securely in Oracle Cloud, you must be aware of your security and compliance responsibilities.
Oracle ensures security of cloud infrastructure and operations, such as cloud operator access controls and infrastructure security patching. You’re responsible for configuring your cloud resources securely. The following graphic illustrates the shared security responsibility model:
Oracle is solely responsible for all aspects of the physical security of the availability domains and fault domains in each region. Both Oracle and you are responsible for the infrastructure security of hardware, software, and the associated logical configurations and controls.
- The platform you create on top of Oracle Cloud.
- The applications that you deploy.
- The data that you store and use.
- The overall governance, risk, and security of your workloads.
- Identity and access management (IAM)
Protect your cloud access credentials, and set up individual user accounts. Manage and review access permissions for your own employee accounts and for all the activities in your tenancy.
Oracle provides the required IAM services, such as identity management, authentication, authorization, and auditing.
- Workload security
Oracle provides secure images that are hardened and include the latest patches. Oracle makes it simple for you to bring the same third-party security solutions that you use today.
After you provision compute instances, protect and secure the operating system and application layers from attacks and compromises. This includes patching the applications and operating systems, ensuring that the operating system configuration is secure, and protecting your applications against malware and network attacks. Use the OS management service to manage updates and patches for the operating system environment of your compute instances. See OS Management.
- Data classification and compliance
Classify and label data appropriately to fulfill your security and compliance requirements. Audit and monitor your deployments to ensure that they continue to meet your data-compliance obligations.
- Host infrastructure security
Securely configure and manage your compute resources (virtual machines, bare metal instances, and containers), storage resources (object storage, local storage, and block volumes), and database services.
Oracle shares the responsibility to ensure that the services are configured optimally and secured. This responsibility includes security of the hypervisor. It extends to configuring the permissions and network access controls necessary for hosts to communicate correctly and for storage devices to be attached and mounted securely.
- Network security
Securely configure network elements, such as virtual networking, load balancing, DNS, and gateways.
Oracle ensures security of the networking infrastructure.
- Client and endpoint protection
Your users might use various hardware and software systems, such as mobile devices and browsers, to access your cloud resources. Ensure the security of all the clients and endpoints that you allow to access Oracle Cloud Infrastructure services.
- Physical security
Oracle protects the global physical infrastructure (hardware, software, networking, and facilities) that are used to run the Oracle Cloud Infrastructure services.