Secure workloads with Cisco Threat Defense using a flexible network load balancer
The Secure Firewall Threat Defense Virtual brings Cisco's next-generation firewall functionalities to virtualized environments, enabling consistent security policies to follow workloads across your physical, virtual, and cloud environments, and between clouds.
Cisco Secure Firewall supports the Oracle Cloud Infrastructure (OCI) platform to implement its next-generation security features, such as application visibility and control, intrusion prevention system, advanced malware protection, URL filtering, and virtual private network. You can also enable security intelligence feed by provided Cisco Talos threat intelligence research team.
Architecture
This reference architecture illustrates how organizations can protect Oracle applications, like Oracle E-Business Suite and PeopleSoft, deployed in Oracle Cloud Infrastructure (OCI) using Cisco Threat Defense Firewall with a flexible network load balancer and dynamic routing gateways enhancements.
To protect these traffic flows, Oracle recommends segmenting the network using a dedicated virtual cloud network (VCN), where traffic is routed through a transit hub and is connected to multiple distinct networks (spokes). Ensure that you have deployed multiple Threat Defense instances between flexible network load balancers considered as a sandwich topology. All traffic, whether to and from the internet, to and from on-premises, or to the Oracle Services Network, is routed through Cisco Secure Firewall’s multilayered threat prevention technologies.
Deploy each tier of your application in its own virtual cloud network (VCN), which acts as a spoke. The hub VCN contains a Cisco Threat Defense firewall active-active cluster, Oracle internet gateway, dynamic routing gateway (DRG), Oracle Service Gateway, and internal and external flexible network load balancers.
The hub VCN connects to the spoke VCNs through DRG. All spoke traffic uses route table rules to route traffic through the DRG to the hub using flexible network load balancer for inspection by the Cisco Threat Defense Firewall cluster.
In a Cisco Secure Firewall deployment, you use a secure firewall management center to manage Threat Defense. A management center provides complete and unified management over threat defense. Easily go from managing a firewall to controlling applications to investigating and remediating malware outbreaks.
The following diagram illustrates this reference architecture.
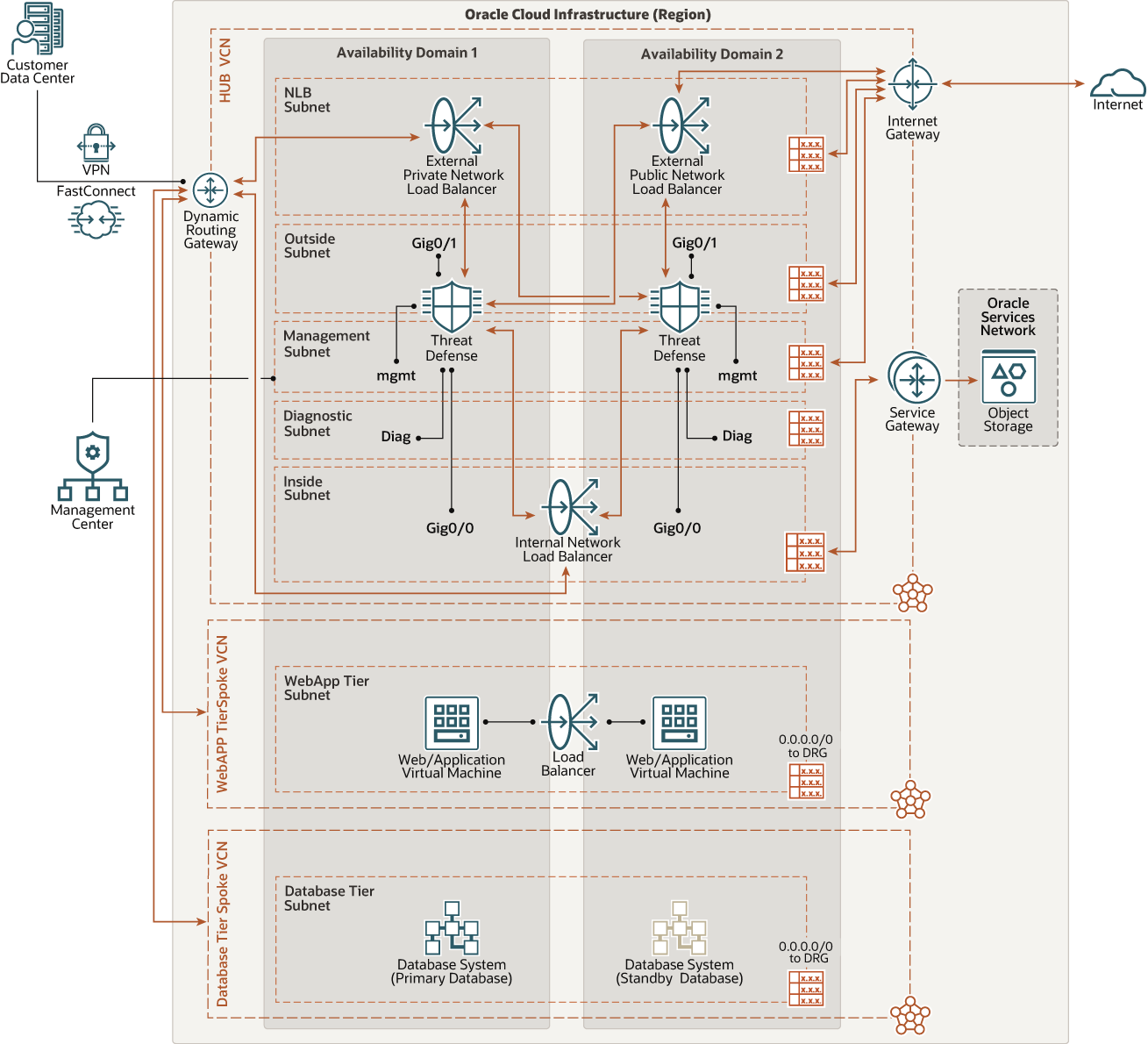
Description of the illustration cisco_nlb_nw_vm_oci.png
Each traffic flow ensures that network address translation (NAT) and security policies are open on Cisco Threat Defense Firewall.
North-south inbound traffic
The following diagram illustrates how north-south inbound traffic accesses the web application tier from the internet and from remote data centers.
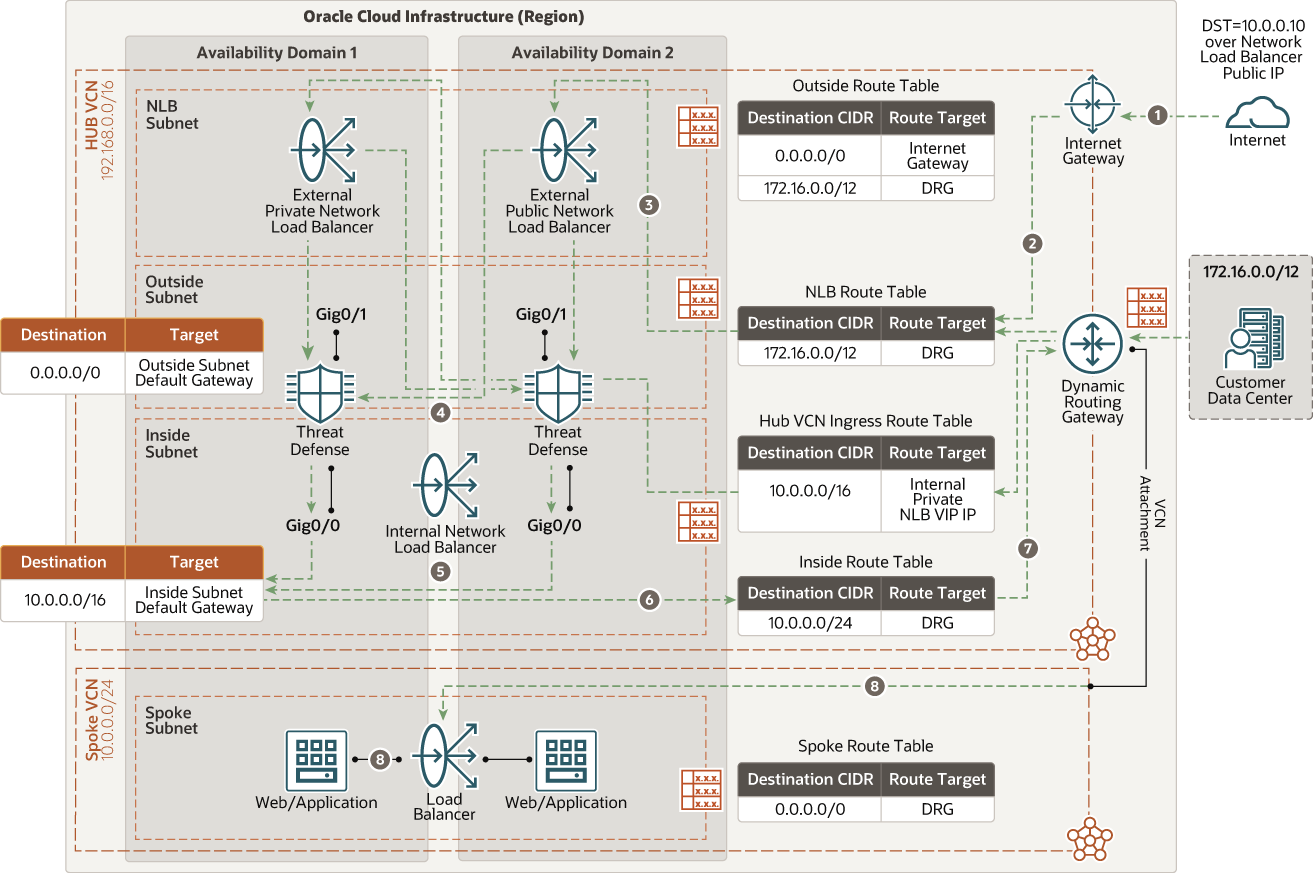
Description of the illustration cisco_nlb_north_south_inbound.png
North-south outbound traffic
The following diagram illustrates how outgoing connections from the web application and database tiers to the internet provide software updates and access to external web services.
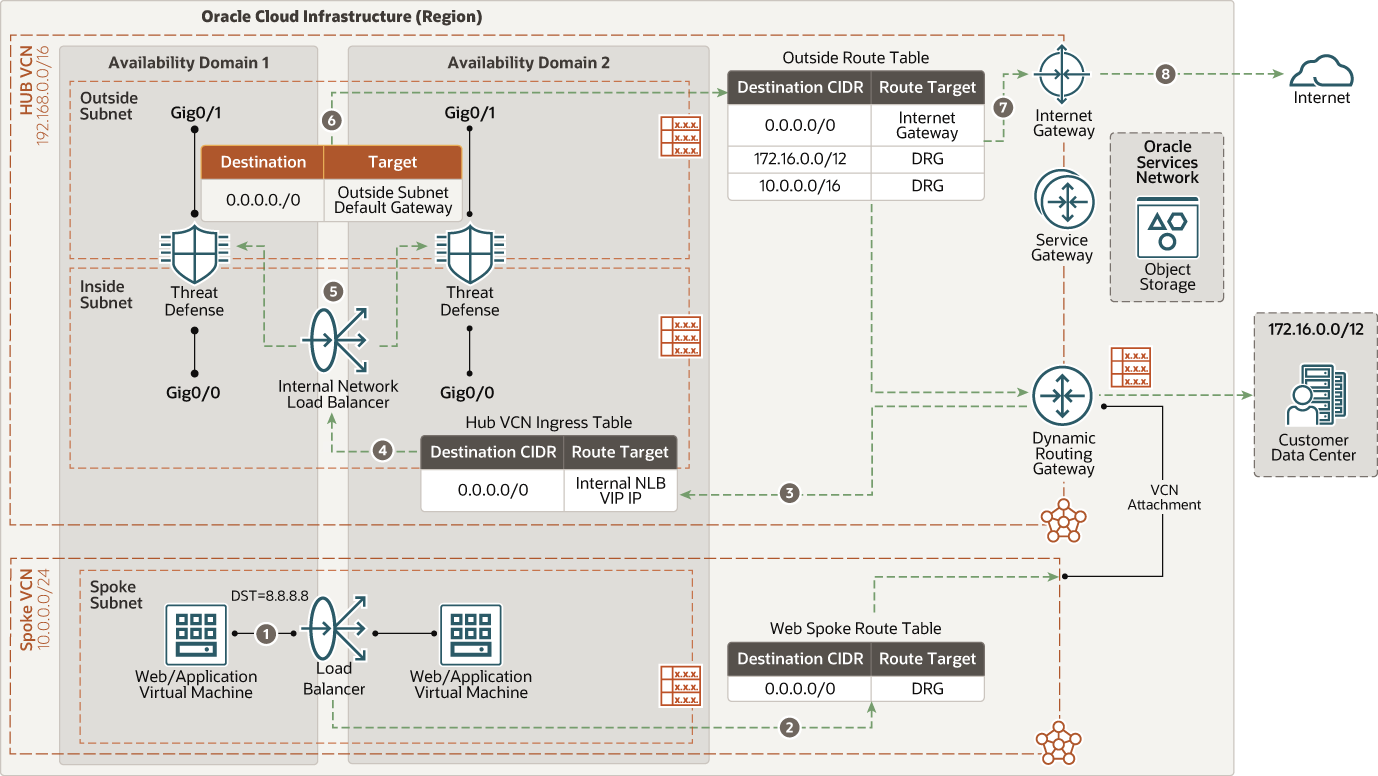
Description of the illustration cisco_nlb_north_south_outbound.png
East-west traffic (web to database)
The following diagram illustrates how traffic moves from the web application to the database tier.
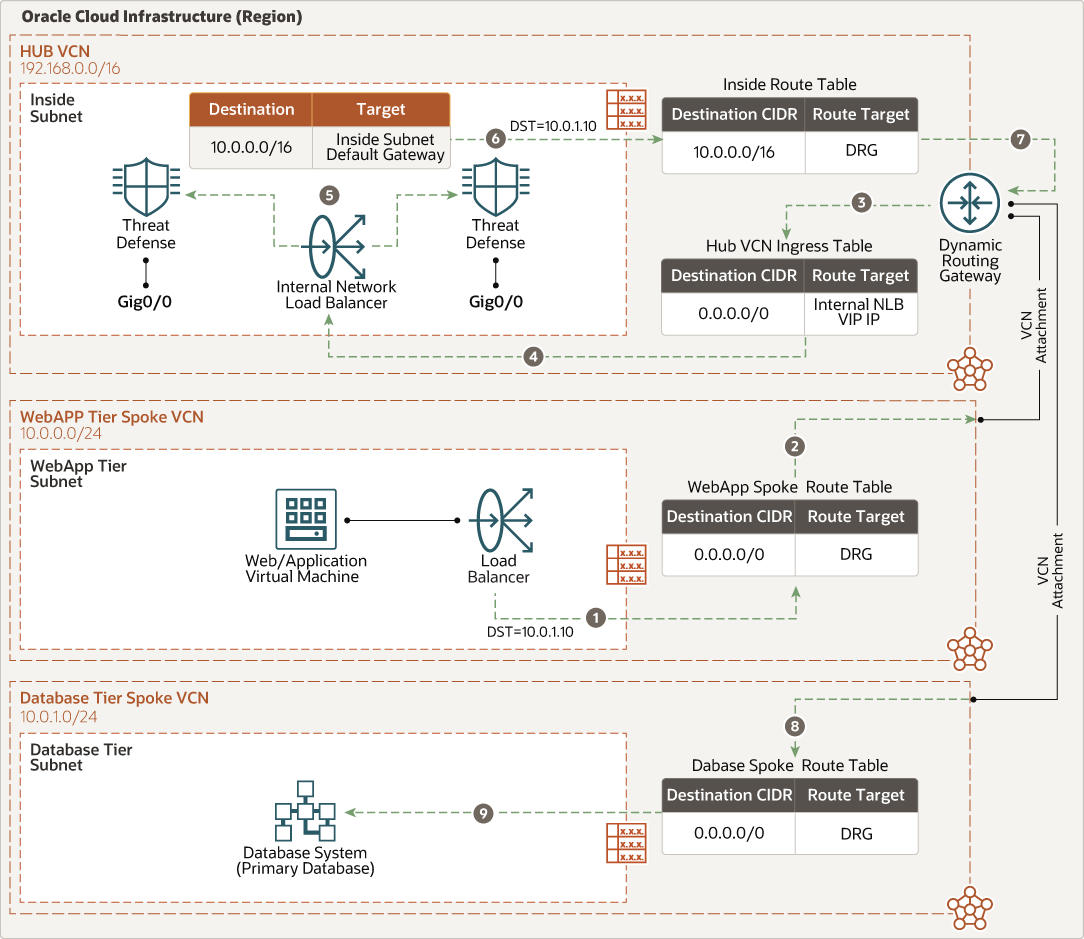
Description of the illustration cisco_nlb_east_west_web_db.png
East-west traffic (database to web)
The following diagram illustrates how traffic moves from the database tier to the web application.
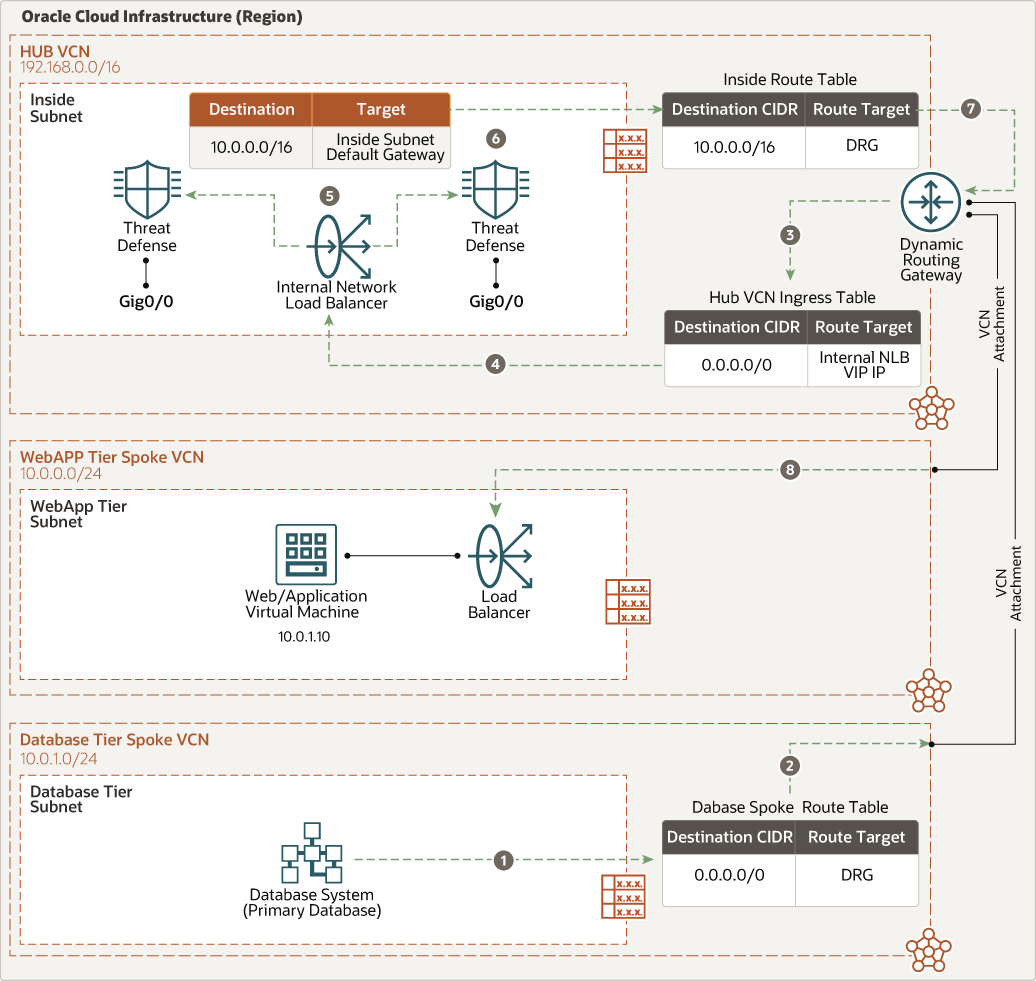
Description of the illustration cisco_nlb_east_west_db_web.png
East-west traffic (web application to Oracle Services Network)
The following diagram illustrates how traffic moves from the web application to the Oracle Services Network.
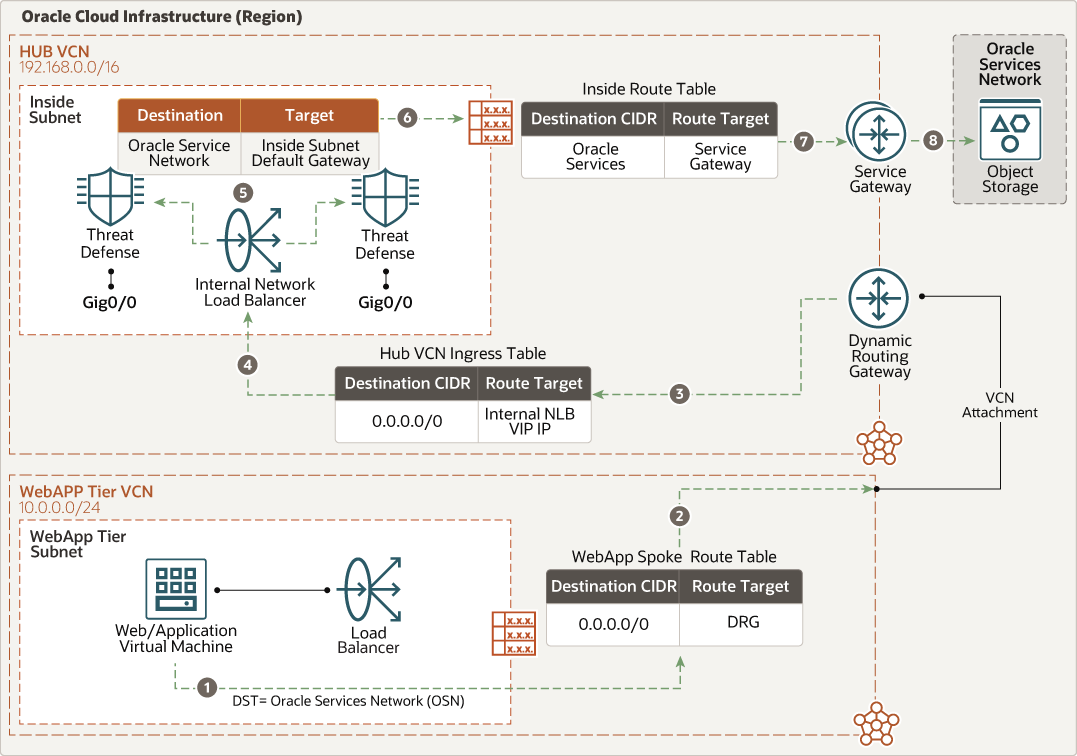
Description of the illustration cisco_nlb_east_west_webapp_osn.png
East-west traffic (Oracle Services Network to web application)
The following diagram illustrates how traffic moves from the Oracle Services Network to the web application.
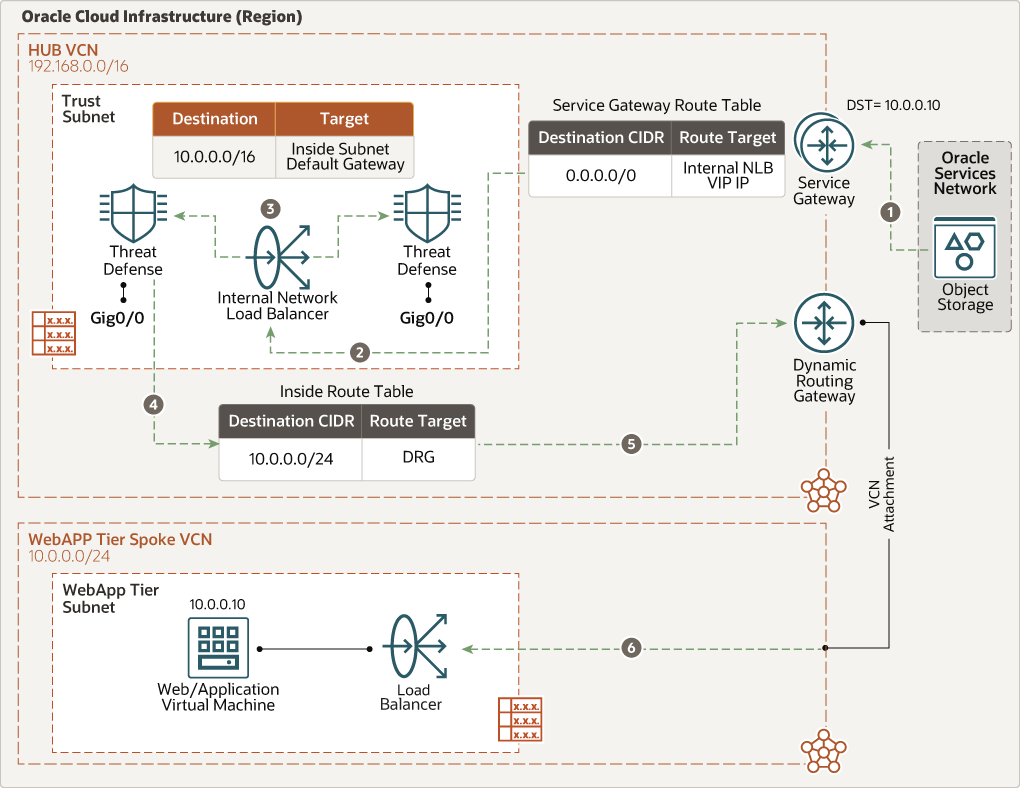
Description of the illustration cisco_nlb_east_west_osn_webapp.png
- Cisco Secure Firewall Threat Defense Virtual
The Cisco Secure Firewall Threat Defense Virtual offers the same functionalities of a physical firewall in a virtual machine (VM) form, delivering inline network security and threat prevention to consistently protect public and private clouds.
- Oracle E-Business Suite or PeopleSoft application tier
Composed of Oracle E-Business Suite or PeopleSoft application servers and file system.
- Oracle E-Business Suite or PeopleSoft database tier
Composed of Oracle Database, but not limited to Oracle Exadata Database Cloud service or Oracle Database services.
- Region
An OCI region is a localized geographic area that contains one or more data centers, called availability domains. Regions are independent of other regions, and vast distances can separate them (across countries or even continents).
- Availability domain
Availability domains are standalone, independent data centers within a region. The physical resources in each availability domain are isolated from the resources in the other availability domains, which provides fault tolerance. Availability domains don’t share infrastructure such as power or cooling, or the internal availability domain network. So, a failure at one availability domain is unlikely to affect the other availability domains in the region.
- Fault domain
A fault domain is a grouping of hardware and infrastructure within an availability domain. Each availability domain has three fault domains with independent power and hardware. When you distribute resources across multiple fault domains, your applications can tolerate physical server failure, system maintenance, and power failures inside a fault domain.
- Virtual cloud network (VCN) and subnet
A VCN is a customizable, software-defined network that you set up in an OCI region. Like traditional data center networks, VCNs give you complete control over your network environment. A VCN can have multiple non-overlapping CIDR blocks that you can change after you create the VCN. You can segment a VCN into subnets, which can be scoped to a region or to an availability domain. Each subnet consists of a contiguous range of addresses that don't overlap with the other subnets in the VCN. You can change the size of a subnet after creation. A subnet can be public or private.
- Hub VCN
The hub VCN is a centralized network where Cisco Threat Defense firewalls are deployed. It provides secure connectivity to all spoke VCNs, OCI services, public endpoints and clients, and on-premises data center networks.
- Application tier spoke VCN
The application tier spoke VCN contains a private subnet to host Oracle E-Business Suite or PeopleSoft components.
- Database tier spoke VCN
The database tier spoke VCN contains a private subnet for hosting Oracle databases.
- Load balancer
OCI Load Balancing service provides automated traffic distribution from a single-entry point to multiple servers in the backend end.
- Flexible network Load balancer
OCI's flexible network load balancer provides automated traffic distribution from one entry point to multiple backend servers in your virtual cloud networks. It operates at the connection level and load balancers incoming client connections to healthy backend servers based on Layer3/Layer4 (IP protocol) data.
- Security list
For each subnet, you can create security rules that specify the source, destination, and type of traffic that must be allowed in and out of the subnet.
- Route table
Virtual route tables contain rules to route traffic from subnets to destinations outside a VCN, typically through gateways. In the hub VCN, you have the following route tables:
- Management route table attached to the management subnet which has a default route connected to internet gateway.
- Outside route table attached to the outside subnet or
default VCN for routing traffic from the hub VCN to internet or
on-premises targets.
- This route table also has entry pointing to your on-premises subnets using dynamic route gateway. This configuration ensures that no traffic disruption occurs during future native network address translation support.
- This route table also has entries for each Spoke VCNs CIDR block route through dynamic routing gateways.
- Inside route table attached to the inside subnet pointing to the CIDR block of the spoke VCNs through dynamic routing gateways.
- Diagnostic route table attached to the diagnostic subnet to the CIDR block where you want to send the traffic.
- NLB route table attached to the nlb subnet pointing to the CIDR block of on-premises subnet through dynamic routing gateways.
- Hub VCN Ingress route table is attached to hub VCN attachment to send any incoming traffic from spoke VCNs through the dynamic routing gateway to internal network load balancer.
- For each spoke attached to the hub through dynamic routing gateways, a distinct route table is defined and attached to an associated subnet. That route table forwards all traffic (0.0.0.0/0) from the associated spoke VCN to dynamic routing gateways through the internal flexible network load balancer, or you can define it at granular level too.
- Oracle service gateway route table attached to the Oracle service gateway for Oracle Service Network communication. That route forwards all traffic (0.0.0.0/0) to the Cisco Threat Defense Firewall inside interface IPs.
- To maintain traffic symmetry, routes are also added to each Cisco Threat Defense Firewall to point the CIDR block of spoke traffic to inside (internal) subnet’s default gateway IP (default gateway IP available in the inside subnet on the hub VCN) and default CIDR block (0.0.0.0/0) pointing to the outside subnet default gateway IP.
- Internet gateway
The internet gateway allows traffic between the public subnets in a VCN and the public internet.
- NAT gateway
The NAT gateway enables private resources in a VCN to access hosts on the internet, without exposing those resources to incoming internet connections.
- Dynamic routing gateway (DRG)
The DRG is a virtual router that provides a path for private network traffic between a VCN and a network outside the region, such as a VCN in another OCI region, an on-premises network, or a network in another cloud provider.
- Service gateway
The service gateway provides access from a VCN to other services, such as OCI Object Storage. The traffic from the VCN to the Oracle service travels over the Oracle network fabric and never traverses the internet.
- FastConnect
OCI FastConnect provides an easy way to create a dedicated, private connection between your data center and OCI. FastConnect provides higher-bandwidth options and a more reliable networking experience when compared with internet-based connections.
- Virtual network interface card (VNIC)
The services in OCI data centers have physical network interface cards (NICs). VM instances communicate using virtual NICs (VNICs) associated with the physical NICs. Each instance has a primary VNIC that's automatically created and attached during launch and is available during the instance's lifetime. DHCP is offered to the primary VNIC only. You can add secondary VNICs after instance launch. Set static IPs for each interface.
- Private IPs
A private IPv4 address and related information for addressing an instance. Each VNIC has a primary private IP, and you can add and remove secondary private IPs. The primary private IP address on an instance is attached during instance launch and doesn’t change during the instance’s lifetime. Secondary IPs also belong to the same CIDR of the VNIC’s subnet. The secondary IP is used as a floating IP because it can move between different VNICs on different instances within the same subnet. You can also use it as a different endpoint to host different services.
- Public IPs
The networking services define a public IPv4 address chosen by Oracle that's mapped to a private IP. Public IPs have the following types:
- Ephemeral: This address is temporary and exists for the lifetime of the instance.
- Reserved: This address persists beyond the lifetime of the instance. It can be unassigned and reassigned to another instance.
- Source and destination check
Every VNIC performs the source and destination check on its network traffic. Disabling this flag enables Cisco Threat Defense Firewall to handle network traffic that's not targeted for the firewall.
- Compute shape
The shape of a Compute instance specifies the number of CPUs and amount of memory allocated to the instance. The Compute shape also determines the number of VNICs and maximum bandwidth available for the compute instance.
Recommendations
- VCN
When you create a VCN, determine the number of CIDR blocks required and the size of each block based on the number of resources that you plan to attach to subnets in the VCN. Use CIDR blocks that are within the standard private IP address space.
Select CIDR blocks that don't overlap with any other network (in Oracle Cloud Infrastructure, your on-premises data center, or another cloud provider) to which you intend to set up private connections.
After you create a VCN, you can change, add, and remove its CIDR blocks.
When you design the subnets, consider your traffic flow and security requirements. Attach all the resources within a specific tier or role to the same subnet, which can serve as a security boundary.
Use regional subnets.
Attach your spoke VCNs as needed so you can send traffic to your hub VCN Cisco Threat Defense firewall. Define the to and from firewall route tables to each VCN attachment of dynamic routing gateways.
- Cisco Firewall Management Center
- When choosing a management center model, consider the number of threat defense devices it manages.
- Estimate the volume of logs that the threat defense device generates at the same time and ensure that the management center is designed to handle that volume.
- To determine the right model for your deployment, see the data sheet.
- Cisco Secure Threat Defense firewall
- A threat defense requires a minimum of four interfaces.
- Deploy an active-active cluster and, if needed, add more instances.
- Select an appropriate OCI shape. A shape is a template that determines
the number of CPUs, amount of memory, and other resources that are
allocated to an instance. The FTDv support the following OCI shape
types:
*In OCI, 1 oCPU is equal to 2 vCPU.OCI Shape OCPUs* RAM Interfaces VM.Standard2.4 4 60 GB Min 4, Max 4 VM.Standard2.8 8 120 GB Min 4, Max 8
- Firewall connectivity
- A secure firewall management center and a threat defense use TCP port 8305 to communicate with each other. Ensure that the port is open for internal management communication.
- If you’re creating a deployment hosted in OCI, create a dedicated subnet for management.
- Use security lists or NSGs to restrict inbound access to ports 443 (for GUI access) and 22 (for CLI access) sourced from the internet for administration of the security policy and to view logs and events.
- By default, Firepower appliances are configured to connect to the internet on ports 443/tcp (HTTPS) and 80/tcp (HTTP). If you don't want your appliances to have direct access to the internet, you can configure a proxy server.
- Firewall policies
For the most up-to-date information on required security policies, ports, and protocols, refer to the firewall documentation in the Explore More section. Staying up to date ensures that you have configured required network address translation policies enabled on Cisco Threat Defense firewall instances.
Considerations
When securing Oracle E-Business Suite or PeopleSoft workloads on OCI using Cisco Threat Defense firewall, consider the following factors:
- Performance
- Selecting the proper instance size, which is determined by the Compute shape, determines the maximum available throughput, CPU, RAM, and number of interfaces.
- Organizations need to know what types of traffic traverses the environment, determine the appropriate risk levels, and apply proper security controls as needed. Different combinations of enabled security controls impact performance.
- Consider adding dedicated interfaces for FastConnect or VPN services.
- Consider using large compute shapes for higher throughput and access to more network interfaces.
- Run performance tests to validate the design can sustain the required performance and throughput.
- Use these metrics as a guideline:
To better understand these performance numbers, see "Cisco Threat Defense Datasheet", referenced in the Explore More topic of this Reference Architecture.
Metric FTDv5 FTDv10 FTDv20/30 FTDv50/100 OCI Shape Types VM.Standard2.4 VM.Standard2.4 VM.Standard2.4 VM.Standard2.4 Throughput: FW + AVC (1024B) 100 Mbps 1 Gbps 1.2 Gbps 2.4 Gbps Throughput: FW + AVC + IPS (1024B) 100 Mbps 1 Gbps 1.2 Gbps 2.4 Gbps Throughput: FW + AVC (450B) 100 Mbps 410 Mbps 410 Mbps 920 Mbps Throughput: FW + AVC + IPS (450B) 100 Mbps 390 Mbps 390 Mbps 910 Mbps Maximum concurrent sessions 250,000 250,000 250,000 2M Maximum new sessions per second 4900 4900 4900 10,000 Maximum VPN peers 250 250 250 10,000 IPSec VPN Throughput (1024B) TCP w/Fastpath) 100 Mbps 1 Gbps 1.2 Gbps 1.5 Gbps
- Security
Deploying Cisco Firepower Management Center in OCI allows for centralized security policy configuration and monitoring of all physical and virtual Cisco Threat Defense firewalls
- Availability
- Deploy your architecture to distinct geographic regions for greatest redundancy.
- Configure site-to-site VPNs with relevant organizational networks for redundant connectivity with on-premises networks.
- Cost
Cisco Threat Defense firewalls and Cisco Firepower Management Center are available in bring-your-own-license (BYOL). Configure all license entitlements for the security services from the Firepower Management Center. For more information about how to manage licenses, see Licensing the Firepower System in the Firepower Management Center configuration guide.
Deploy
- Deploy using the stack in Oracle Cloud
Marketplace:
- Set up the required networking infrastructure as shown in the architecture diagram.
- Deploy the application (Oracle E-Business Suite or PeopleSoft) on your environment.
- Oracle Cloud Marketplace has multiple listings for different configurations and licensing requirements. For example, the following listings feature bring your own licensing (BYOL). For each listing you choose, click Get App and follow the on-screen prompts:
- Deploy using the Terraform code in GitHub:
- Go to the GitHub Repository.
- Clone or download the repository to your local computer.
- Follow the instructions in the
READMEdocument.