Secure Cloud Workloads with Check Point CloudGuard Network Security
Move or extend application workloads from Oracle E-Business Suite or PeopleSoft in the cloud using Check Point CloudGuard Network Security (CGNS) to augment native security options without significant configuration, integration, or business process changes.
Security in the cloud is based on a shared responsibility model. Oracle is responsible for the security of the underlying infrastructure, such as data center facilities, and hardware and software to manage cloud operations and services. Customers are responsible for securing their workloads and configure their services and applications securely to meet their compliance obligations.
Oracle Cloud Infrastructure offers best-in-class security technology and operational processes to secure its enterprise cloud services. Check Point CloudGuard Network Security for Oracle Cloud Infrastructure provides advanced, multi-layered security to protect applications from attacks while enabling secure connectivity from enterprise and hybrid cloud networks.
Together, they protect applications across on-premises data centers and cloud environments delivering scalable performance and bringing advanced security orchestration and unified threat protection.
The security controls include the following:
- Access controls (firewall)
- Logging
- Application control
- Intrusion prevention (IPS)
- Advanced threat prevention (anti-virus/anti-bot/SandBlast Zero-Day Protection)
- Site-to-site virtual private network (VPN) for communication with the on-premises network
- Remote access VPN for communication with roaming users
- Network address translation for internet bound traffic
Architecture
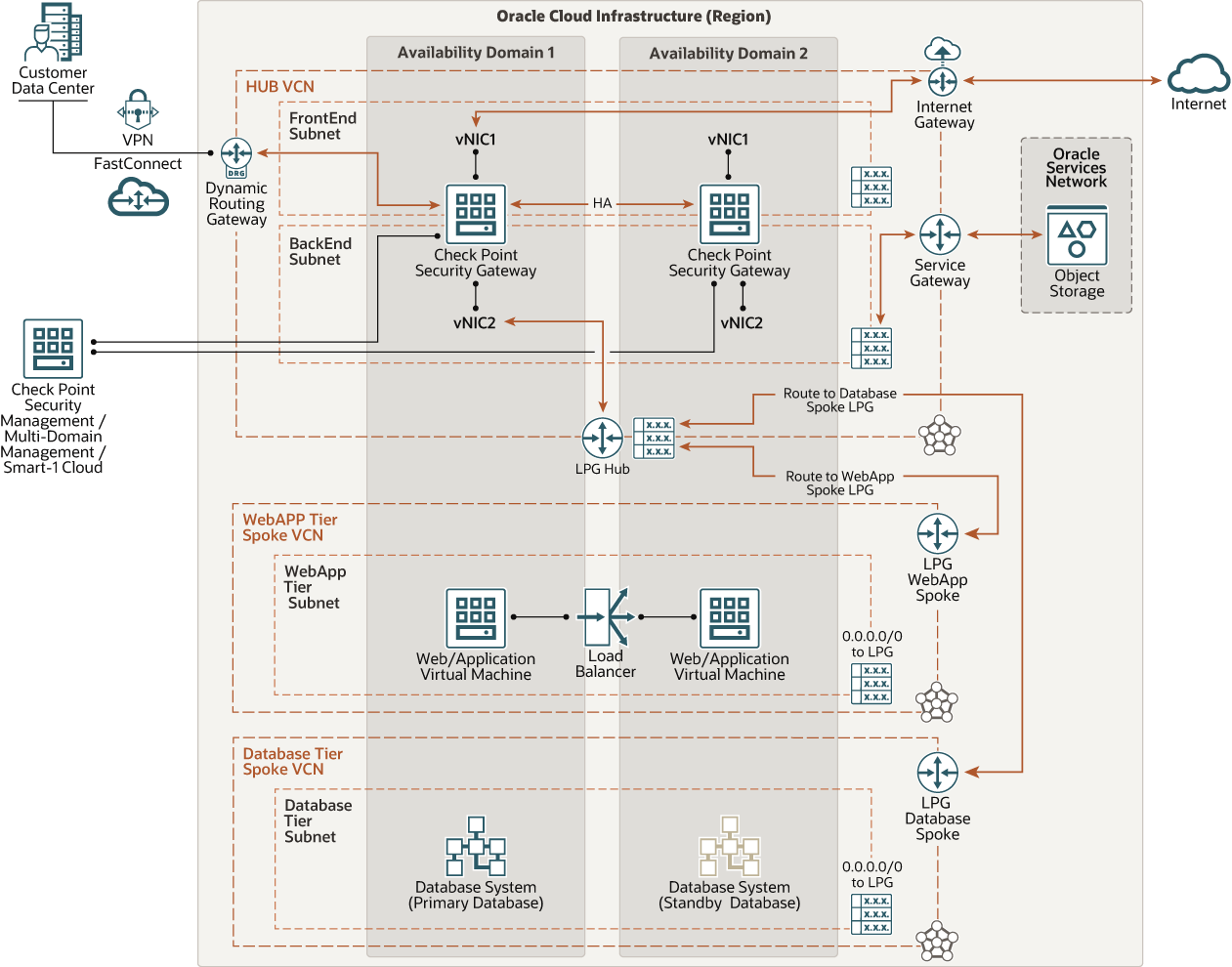
This reference architecture illustrates how organizations can protect Oracle applications like Oracle E-Business Suite and PeopleSoft deployed in Oracle Cloud Infrastructure using Check Point CloudGuard Network Security (CGNS) gateways.
To protect these traffic flows, Check Point recommends segmenting the network using a hub and spoke topology where traffic is routed through a central hub and is connected to multiple distinct networks (spokes). All traffic between spokes, whether to and from the internet, to and from on-premises, or to the Oracle Services Network is routed through the hub and inspected with Check Point CloudGuard Network Security’s multilayered threat prevention technologies.
Deploy each tier of your application in its own virtual cloud network (VCN), which acts as a spoke. The hub VCN contains a Check Point CGNS high availability cluster, Oracle internet gateway, dynamic routing gateway (DRG), Oracle Service Gateway, and local peering gateways (LPGs).
The hub VCN connects to the spoke VCNs through LPGs or by attaching secondary virtual network interface cards (VNIC) to the CGNS gateways. All spoke traffic uses route table rules to route traffic through the LPGs to the hub for inspection by the Check Point CGNS high availability cluster.
Use one of the following methods to manage the environment:
- Centrally manage the environment with a Check Point security management server or multidomain management server, deployed either in its own subnet in the hub VCN or as a preexisting customer server that is accessible to the hub.
- Centrally manage the environment from Check Point’s Smart-1 Cloud Management-as-a-Service.
The following diagram illustrates this reference architecture.
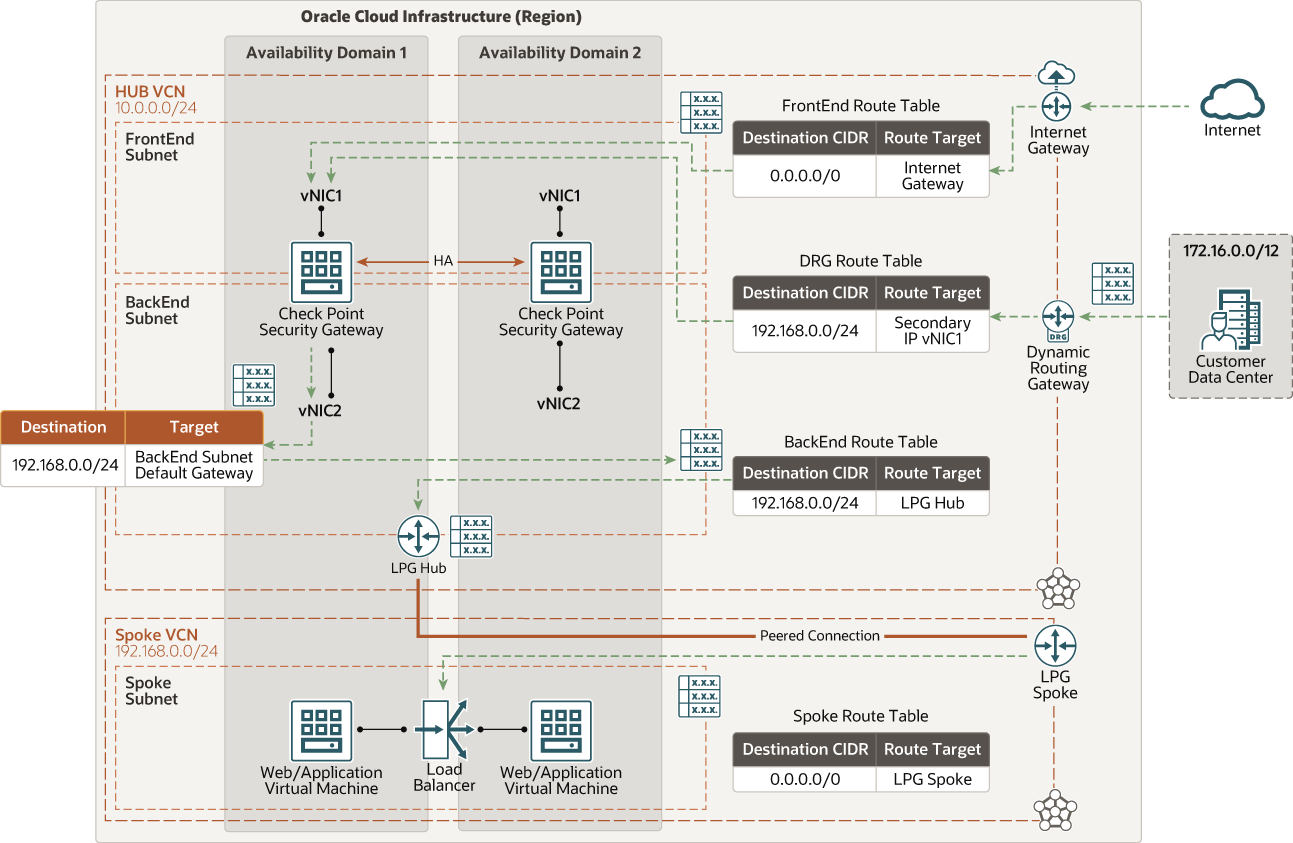
North-South Inbound Traffic
The following diagram illustrates how north-south inbound traffic accesses the web application tier from the internet and from remote data centers.
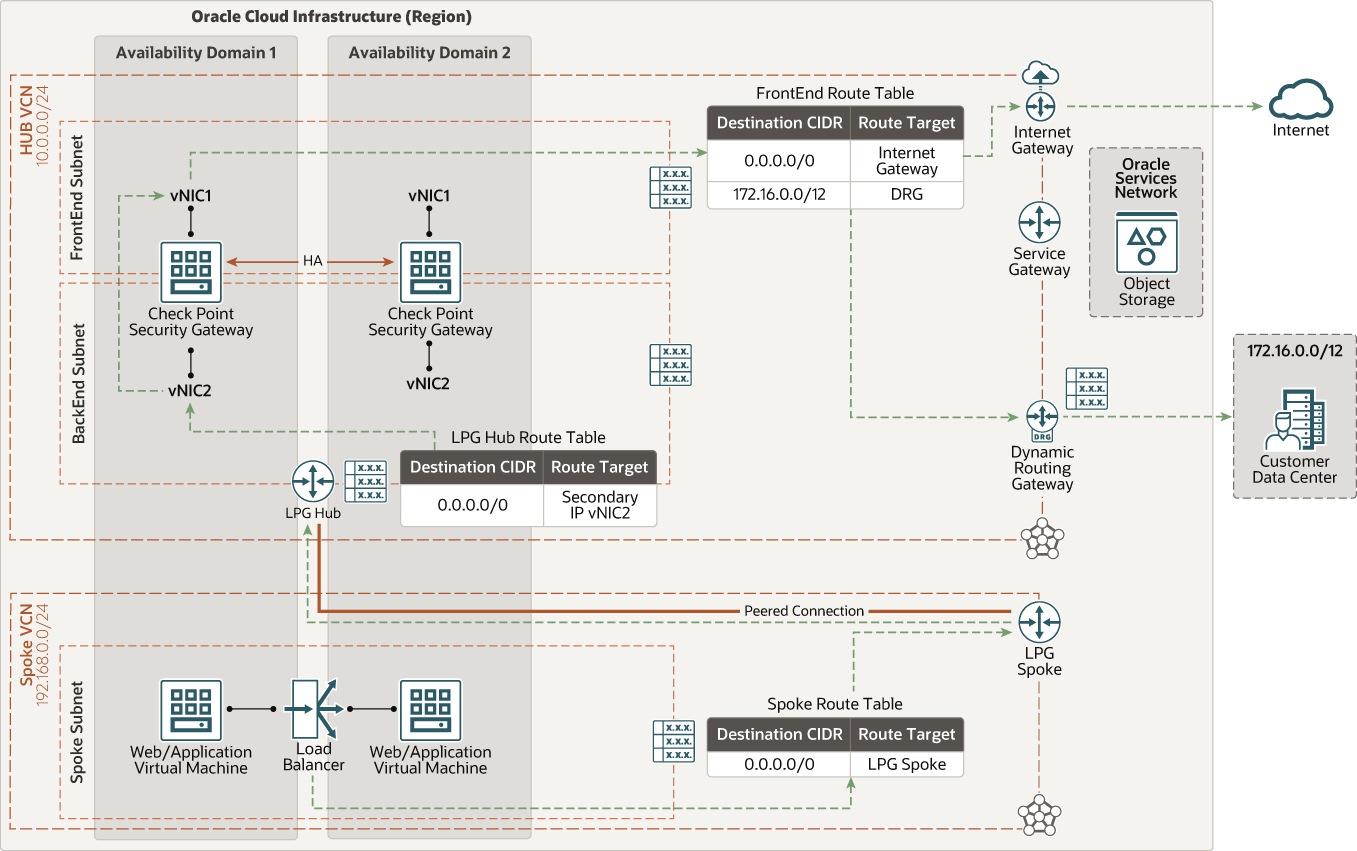
North-South Outbound Traffic
The following diagram illustrates how outgoing connections from the web application and database tiers to the internet provide software updates and access to external web services. Ensure that the hide NAT is configured in your Check Point security policy for the relevant networks.
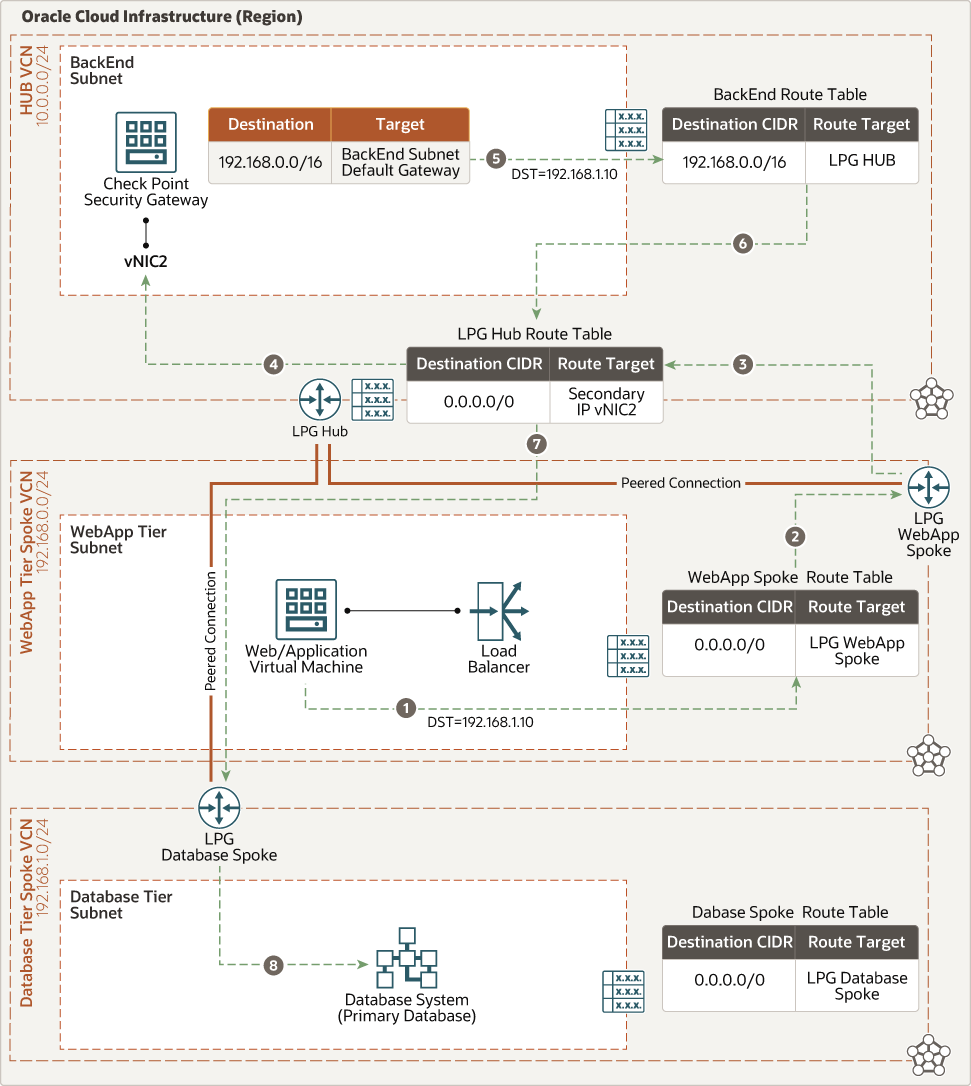
East-West Traffic (Web to Database)
The following diagram illustrates how traffic moves from the web application to the database tier.
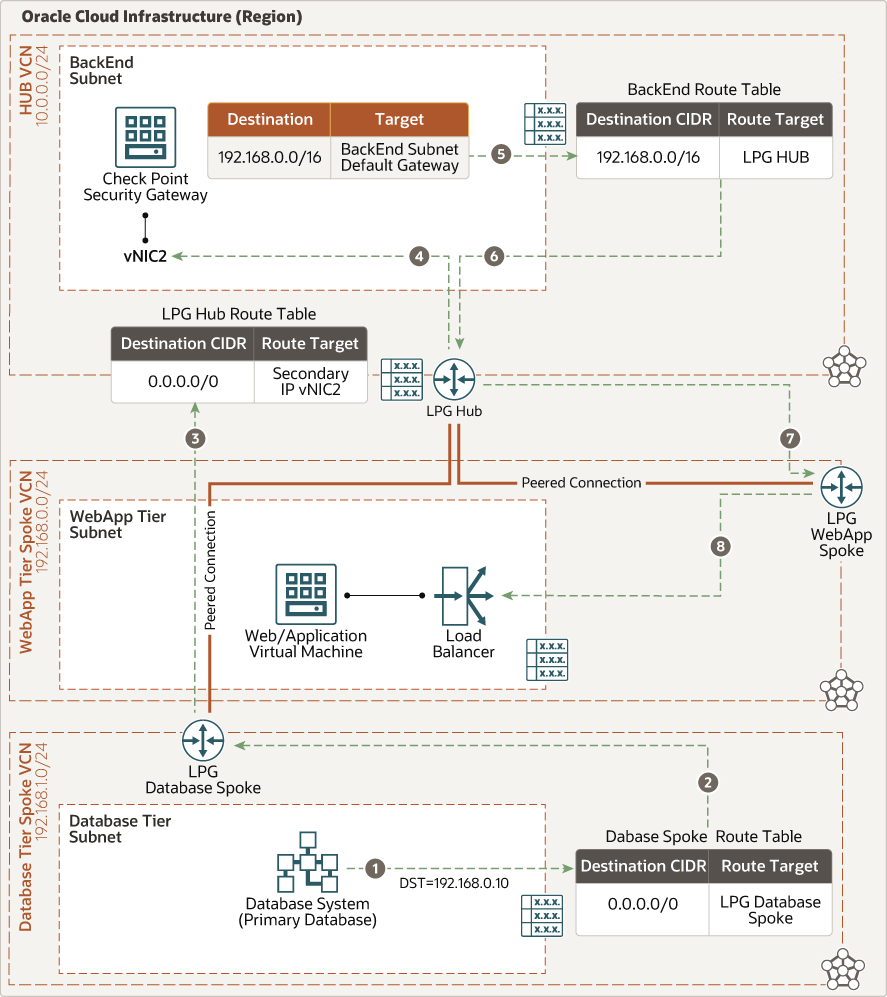
East-West Traffic (Database to Web)
The following diagram illustrates how traffic moves from the database tier to the web application.
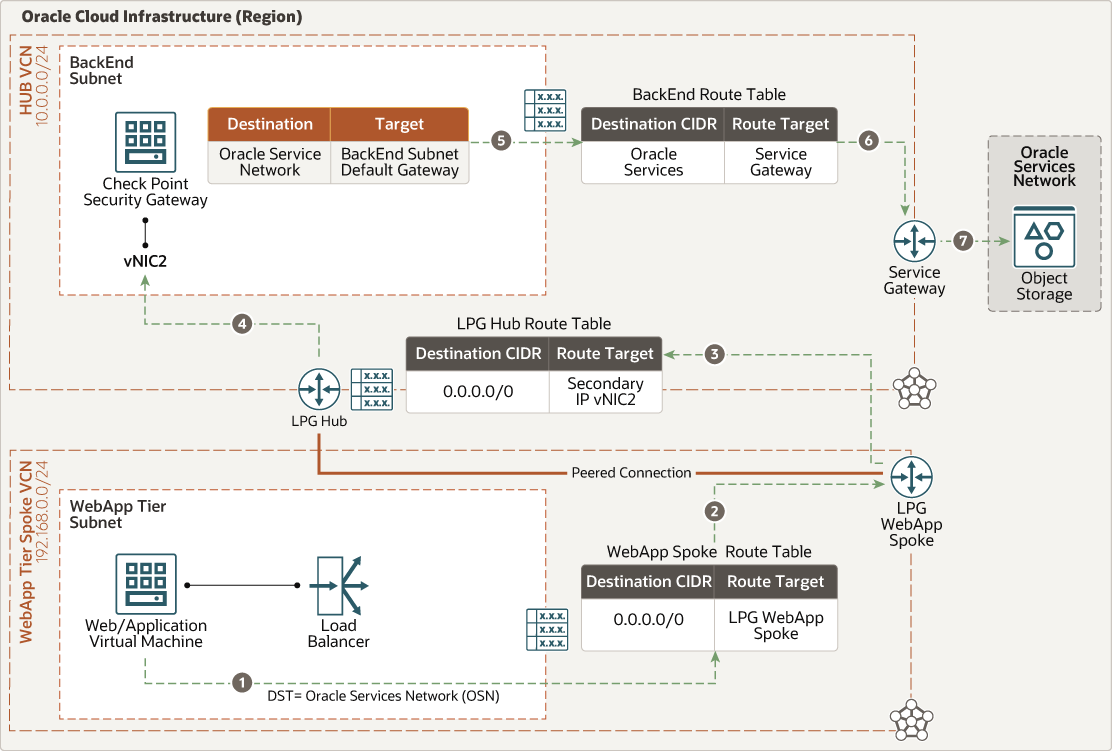
East-West Traffic (Web Application to Oracle Services Network)
The following diagram illustrates how traffic moves from the web application to the Oracle Services Network.
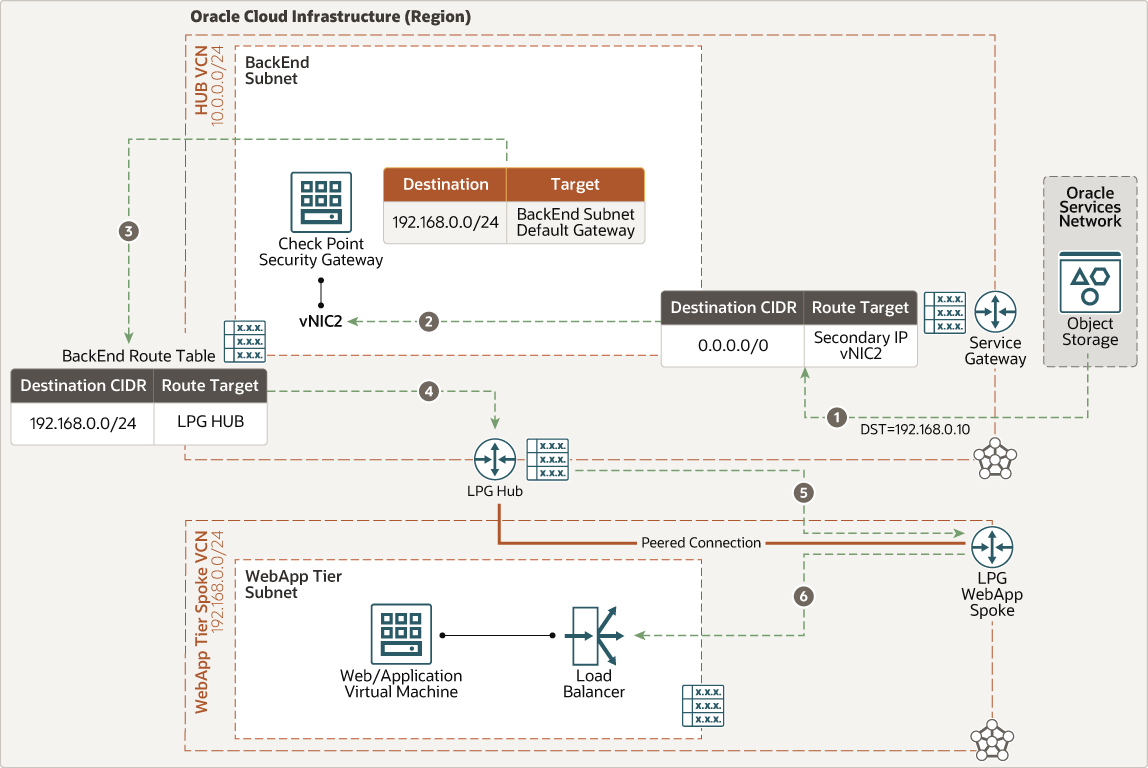
East-West Traffic (Oracle Services Network to Web Application)
The following diagram illustrates how traffic moves from the Oracle Services Network to the web application.
The architecture has the following components:
- Check Point CloudGuard network security gateways
Provides advanced threat prevention and cloud network security for hybrid clouds.
- Check Point Security Management
- Security Management Server
- Multi-Domain Management
- Smart-1 Cloud Management-as-a-Service
- Oracle E-Business Suite or PeopleSoft application tier
Composed of Oracle E-Business Suite or PeopleSoft application servers and file system.
- Oracle E-Business Suite or PeopleSoft database tier
Composed of Oracle Database, but not limited to Oracle Exadata Database Cloud service or Oracle Database services.
- Region
An Oracle Cloud Infrastructure region is a localized geographic area that contains one or more data centers, called availability domains. Regions are independent of other regions, and vast distances can separate them (across countries or even continents).
- Availability domain
Availability domains are standalone, independent data centers within a region. The physical resources in each availability domain are isolated from the resources in the other availability domains, which provides fault tolerance. Availability domains don’t share infrastructure such as power or cooling, or the internal availability domain network. So, a failure at one availability domain is unlikely to affect the other availability domains in the region.
- Fault domain
A fault domain is a grouping of hardware and infrastructure within an availability domain. Each availability domain has three fault domains with independent power and hardware. When you distribute resources across multiple fault domains, your applications can tolerate physical server failure, system maintenance, and power failures inside a fault domain.
- Virtual cloud network (VCN) and subnet
A VCN is a customizable, software-defined network that you set up in an Oracle Cloud Infrastructure region. Like traditional data center networks, VCNs give you complete control over your network environment. A VCN can have multiple non-overlapping CIDR blocks that you can change after you create the VCN. You can segment a VCN into subnets, which can be scoped to a region or to an availability domain. Each subnet consists of a contiguous range of addresses that don't overlap with the other subnets in the VCN. You can change the size of a subnet after creation. A subnet can be public or private.
- Hub VCN
The hub VCN is a centralized network where Check Point CloudGuard NSGs are deployed. It provides secure connectivity to all spoke VCNs, Oracle Cloud Infrastructure services, public endpoints and clients, and on-premises data center networks.
- Application tier spoke VCN
The application tier spoke VCN contains a private subnet to host Oracle E-Business Suite or PeopleSoft components.
- Database tier spoke VCN
The database tier spoke VCN contains a private subnet for hosting Oracle databases.
- Load balancer
The Oracle Cloud Infrastructure Load Balancing service provides automated traffic distribution from a single entry point to multiple servers in the back end.
- Security list
For each subnet, you can create security rules that specify the source, destination, and type of traffic that must be allowed in and out of the subnet.
- Route Table
Virtual route tables contain rules to route traffic from subnets to destinations outside a VCN, typically through gateways.
In the hub VCN, you have the following route tables:
- Frontend route table attached to the frontend subnet or default VCN for routing traffic from the hub VCN to internet or on-premises targets.
- Backend route table attached to the backend subnet pointing to the CIDR block of the spoke VCNs through the associated LPGs.
- For each spoke attached to the hub, a distinct route table is defined and attached to an associated LPG. That route table forwards all traffic (0.0.0.0/0) from the associated spoke LPG through the Check Point CGNS backend floating IP.
- Oracle service gateway route table attached to the Oracle service gateway for Oracle Services Network communication. That route forwards all traffic (0.0.0.0/0) to the Check Point CGNS backend floating IP.
- To maintain traffic symmetry, routes are also added to each Check Point CGNS cluster member (Gaia OS) to point the CIDR block of Spoke traffic to backend (internal) subnet’s default gateway IP (first IP available in the backend subnet on Hub VCN).
- Internet gateway
The internet gateway allows traffic between the public subnets in a VCN and the public internet.
- NAT gateway
The NAT gateway enables private resources in a VCN to access hosts on the internet, without exposing those resources to incoming internet connections.
- Local peering gateway (LPG)
An LPG enables you to peer one VCN with another VCN in the same region. Peering means the VCNs communicate using private IP addresses, without the traffic traversing the internet or routing through your on-premises network.
- Dynamic routing gateway (DRG)
The DRG is a virtual router that provides a path for private network traffic between a VCN and a network outside the region, such as a VCN in another Oracle Cloud Infrastructure region, an on-premises network, or a network in another cloud provider.
- Service gateway
The service gateway provides access from a VCN to other services, such as Oracle Cloud Infrastructure Object Storage. The traffic from the VCN to the Oracle service travels over the Oracle network fabric and never traverses the internet.
- FastConnect
Oracle Cloud Infrastructure FastConnect provides an easy way to create a dedicated, private connection between your data center and Oracle Cloud Infrastructure. FastConnect provides higher-bandwidth options and a more reliable networking experience when compared with internet-based connections.
- Virtual network interface card (VNIC)
The services in Oracle Cloud Infrastructure data centers have physical network interface cards (NICs). Virtual machine instances communicate using virtual NICs (VNICs) associated with the physical NICs. Each instance has a primary VNIC that's automatically created and attached during launch and is available during the instance's lifetime. DHCP is offered to the primary VNIC only. You can add secondary VNICs after instance launch. You should set static IPs for each interface.
- Private IPs
A private IPv4 address and related information for addressing an instance. Each VNIC has a primary private IP and you can add and remove secondary private IPs. The primary private IP address on an instance is attached during instance launch and doesn’t change during the instance’s lifetime. Secondary IPs should also belong to the same CIDR of the VNIC’s subnet. The secondary IP is used as a floating IP because it can move between different VNICs on different instances within the same subnet. You can also use it as a different endpoint to host different services.
- Public IPs
The networking services define a public IPv4 address chosen by Oracle that's mapped to a private IP.
- Ephemeral: This address is temporary and exists for the lifetime of the instance.
- Reserved: This address persists beyond the lifetime of the instance. It can be unassigned and reassigned to another instance.
- Source and destination check
Every VNIC performs the source and destination check on its network traffic. Disabling this flag enables CGNS to handle network traffic that's not targeted for the firewall.
- Compute shape
The shape of a compute instance specifies the number of CPUs and amount of memory allocated to the instance. The compute shape also determines the number of VNICs and maximum bandwidth available for the compute instance.
Recommendations
Use the following recommendations as a starting point to secure Oracle E-Business Suite or PeopleSoft workloads on Oracle Cloud Infrastructure using Check Point CloudGuard Network Security.
- VCN
When you create a VCN, determine the number of CIDR blocks required and the size of each block based on the number of resources that you plan to attach to subnets in the VCN. Use CIDR blocks that are within the standard private IP address space.
Select CIDR blocks that don't overlap with any other network (in Oracle Cloud Infrastructure, your on-premises data center, or another cloud provider) to which you intend to set up private connections.
After you create a VCN, you can change, add, and remove its CIDR blocks.
When you design the subnets, consider your traffic flow and security requirements. Attach all the resources within a specific tier or role to the same subnet, which can serve as a security boundary.
Use regional subnets.
Verify the maximum number of LPGs per VCN in your service limits, in case you want to extend this architecture for multiple environments and applications.
- Check Point CloudGuard Network Security
- Deploy a high availability cluster.
- Whenever possible, deploy in distinct fault domains at a minimum or different availability domains.
- Ensure that MTU is set to 9000 on all VNICs.
- Utilize SRIOV and VFIO interfaces.
- Create a second hub-spoke topology in a separate region for disaster recovery or geo-redundancy.
- Don’t restrict traffic through security lists or NSGs because all traffic is secured by the security gateway.
- By default, ports 443 and 22 are open on the gateway, and more ports are open based on security policies.
- Check Point Security Management
- If you’re creating a new deployment hosted in Oracle Cloud Infrastructure, create a dedicated subnet for management.
- Deploy a secondary management server (management high availability) in a different availability domain or region.
- Use security lists or NSGs to restrict inbound access to ports 443, 22, and 19009 sourced from the internet for administration of the security policy and to view logs and events.
- Create either a security list or NSG allowing ingress and egress traffic to the security gateways from the security management server.
- Check Point Security Policies
Refer to the application documentation in the Explore More section for the most up-to-date information on required ports and protocols.
Considerations
When securing Oracle E-Business Suite or PeopleSoft workloads on Oracle Cloud Infrastructure using Check Point CloudGuard Network Security, consider the following:
- Performance
- Selecting the proper instance size, which is determined by the compute shape, determines the maximum available throughput, CPU, RAM, and number of interfaces.
- Organizations need to know what types of traffic traverses the environment, determine the appropriate risk levels, and apply proper security controls as needed. Different combinations of enabled security controls impact performance.
- Consider adding dedicated interfaces for FastConnect or VPN services.
- Consider using large compute shapes for higher throughput and access to more network interfaces.
- Run performance tests to validate the design can sustain the required performance and throughput.
- Security
- Deploying Check Point Security Management in Oracle Cloud Infrastructure allows for centralized security policy configuration and monitoring of all physical and virtual Check Point Security Gateway instances.
- For existing Check Point customers, migrating Security Management to Oracle Cloud Infrastructure is also supported.
- Define distinct Identity and Access Management (IAM) dynamic group or policy per cluster deployment.
- Availability
- Deploy your architecture to distinct geographic regions for greatest redundancy.
- Configure site-to-site VPNs with relevant organizational networks for redundant connectivity with on-premises networks.
- Cost
- Check Point CloudGuard is available in bring-your-own-license (BYOL) and pay-as-you-go license models for both Security Management and Security Gateways in the Oracle Cloud Marketplace.
- Check Point CloudGuard Network Security Gateway licensing is based on number of vCPUs (one OCPU is equivalent to two vCPUs).
- Check Point BYOL licenses are portable between instances. For example, if you’re migrating workloads from other public clouds that also use BYOL licenses, you don’t need to purchase new licenses from Check Point. Check with your Check Point representative if you have questions or need verification of your license status.
- Check Point Security Management is licensed per managed security gateway. For example, two clusters count as four toward the Security Management license.
Deploy
To secure Oracle E-Business Suite or PeopleSoft workloads on Oracle Cloud Infrastructure using Check Point CloudGuard Network Security, perform the following steps:
Explore More
Learn more about the features of this architecture and about related resources.