Learn About Using SDKs to Authenticate Applications
Oracle Identity Cloud Service provides identity management, single sign-on (SSO), and identity governance for your applications. It also provides the security platform for Oracle Cloud, which allows you to securely and easily access, develop, and deploy your applications.
Oracle Identity Cloud Service can function as an identity provider, centralizing the authentication mechanism, handling all password management responsibilities, and providing SSO for your applications. In addition, you can enhance the security for your applications by enabling Multi-Factor Authentication (MFA) and by implementing policies that enforce a remediation action, such as allowing or denying users access to the applications.
When you want to develop applications that use the Oracle Identity Cloud Service authentication mechanism, use SDKs. Oracle Identity Cloud Service's SDKs are based on industry-standard protocols and layers, such as OAuth 2.0 and OpenID Connect 1.0. The SDKs make your work easier by encapsulating all the necessary REST API endpoint calls for authenticating users with Oracle Identity Cloud Service.
Oracle Identity Cloud Service SDKs support the following flows for OAuth 2.0 and OpenID Connect 1.0:
-
Three-legged flow: Users interact with Oracle Identity Cloud Service directly. After a user signs in, Oracle Identity Cloud Service issues an authorization code which is exchanged for a user access token by the SDK. This access token is used to grant the user access to the protected resources in the application. The three-legged flow uses the authorization code grant type.
Oracle recommends that you use three-legged flows to integrate your web applications with Oracle Identity Cloud Service for authentication. Also, by using the authorization code grant type, you can access other applications that are protected by Oracle Identity Cloud Service without the need to reauthenticate.
-
Two-legged flow: Users don't interact with Oracle Identity Cloud Service directly. Instead, all communication happens between trusted applications and Oracle Identity Cloud Service. These applications request and receive user access tokens from Oracle Identity Cloud Service to grant users access to the protected resources in the applications. Two-legged flows use the client credentials or resource owner grant types.
Architecture
The following architecture diagrams illustrate a web application that uses the SDK library to perform two-legged and three-legged authentication flows for OAuth 2.0 and OpenID Connect 1.0. The three-legged flow uses the authorization code grant type, and the two-legged flows use the client credentials and resource owner grant types.
Authorization Code Grant Type
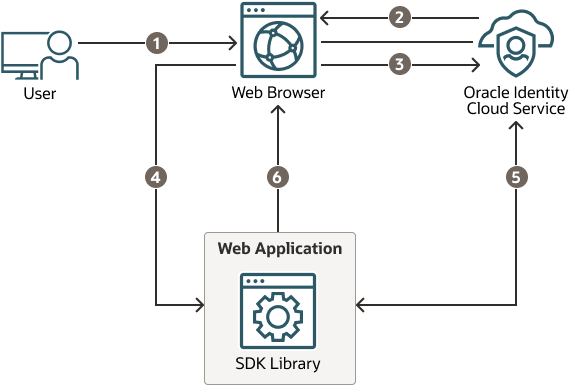
Description of the illustration authorization-code-grant-type.png
The data flow consists of the following steps:
-
The user requests a protected URL.
-
Oracle Identity Cloud Service displays the Sign In page.
-
The user submits their login credentials.
-
Oracle Identity Cloud Service issues an authorization code to the web application through the web browser.
-
The web application uses the SDK to exchange the authorization code for a user access token.
-
The web application displays content for the user.
Client Credentials Grant Type
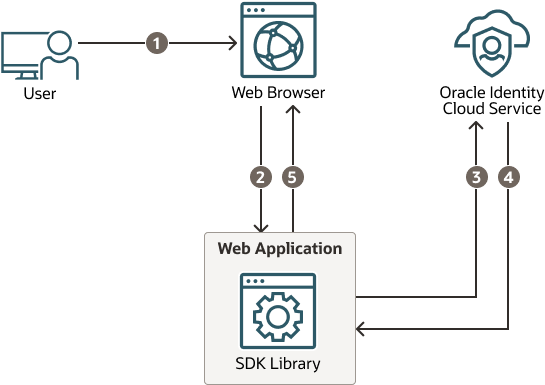
Description of the illustration client-credentials-grant-type.png
The data flow consists of the following steps:
-
The user requests a protected URL.
-
The request is forwarded to the web application.
-
The web application uses the SDK to submit the Client ID and Secret to Oracle Identity Cloud Service for validation.
-
Oracle Identity Cloud Service issues an access token to the web application.
-
The web application displays content for the user.
You can also use the client credentials grant type if the web application needs to access Oracle Identity Cloud Service's REST APIs. The user access token that’s issued by Oracle Identity Cloud Service doesn't carry any user information.
Resource Owner Grant Type
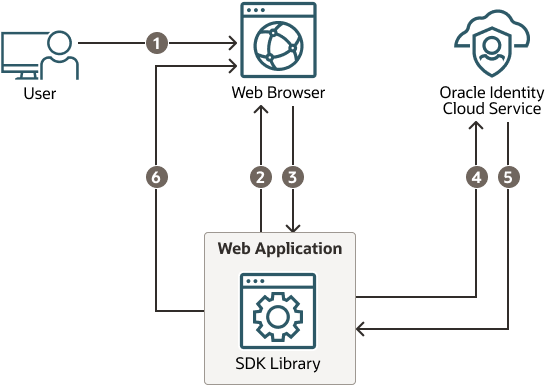
Description of the illustration resource-owner-grant-type.png
The data flow consists of the following steps:
-
The user requests a protected URL.
-
The application displays the Sign In page.
-
The user submits their login credentials.
-
The application uses the SDK to submit the user's credentials, and the application's Client ID and Secret, to Oracle Identity Cloud Service for validation.
-
Oracle Identity Cloud Service issues a user access token to the application.
-
The application displays content for the user.
Note:
In the resource owner grant type, the application can't participate in the SSO process provided by Oracle Identity Cloud Service. If you want your application to use the Oracle Identity Cloud Service authentication mechanism, then use the three-legged authorization code grant type.About Required Services and Roles
This solution requires Oracle Identity Cloud Service.
These are the roles required.
| Role | Required to... |
|---|---|
Security administrator |
Access the Downloads page of the Oracle Identity Cloud Service console. From this page, you can download the Java SDK. |
Application administrator |
Manage applications in Oracle Identity Cloud Service. This includes registering the sample Java application with Oracle Identity Cloud Service. |
See Oracle Products, Solutions, and Services to get what you need.