Zimperium: Mobile threat defense (MTD) solution deployment on Oracle Cloud Infrastructure
Helping companies defend their mobile applications against security threats is the #1 priority for Zimperium.
With its z9 machine learning engine, Zimperium's cloud-native mobile security platform helps protect mobile devices from network, phishing, and application attacks. As a member of Oracle PartnerNetwork, Zimperium is working with Oracle to offer its mobile threat defense (MTD) services in the Oracle Cloud Marketplace. Since moving its platform to Oracle Cloud Infrastructure, Zimperium has not only reduced its infrastructure costs by 20%, it has also increased its application's availability, tightened its security, and is able to more quickly resize its compute instances to match current workloads.
Architecture
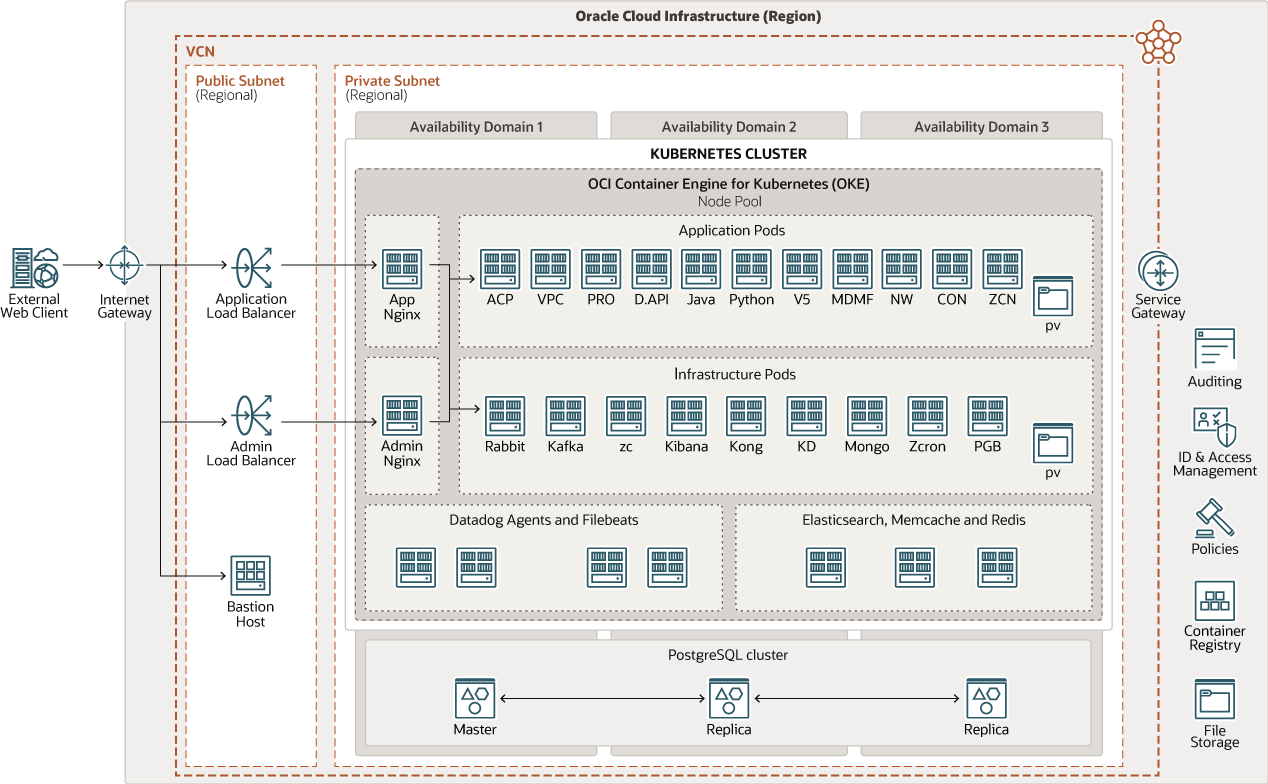
Zimperium deployed its application stack by using Oracle Cloud Infrastructure Container Engine for Kubernetes.
The application workload is deployed on a private subnet and is isolated from the public internet using a public load balancer for traffic intake.
Nginx is used as a private internal load balancer for directing traffic to different application components running on Docker containers.
For its customer data management layer, Zimperium has standardized on the PostGreSQL open source database, which it deploys on a multi-node cluster running on Oracle Cloud Infrastructure Compute instances. These compute instances are replicated across multiple availability domains and regions worldwide. The PostGreSQL cluster is deployed using Terraform scripts coupled with Ansible and a Python-based approach to make PostgreSQL highly available, including, etcd, pgbouncer, haproxy and keepalived for failure detection and VIP failover.
Other open source components include Elastic Search and MongoDB, also in a cluster configuration to support agility, scaling, and business continuity.
The same infrastructure architecture is deployed globally across other Oracle Cloud Infrastructure regions.
The following diagram illustrates this reference architecture.
The architecture has the following components:
- Region
An Oracle Cloud Infrastructure region is a localized geographic area that contains one or more data centers, called availability domains. Regions are independent of other regions, and vast distances can separate them (across countries or even continents).
- Availability domain
Availability domains are standalone, independent data centers within a region. The physical resources in each availability domain are isolated from the resources in the other availability domains, which provides fault tolerance. Availability domains don’t share infrastructure such as power or cooling, or the internal availability domain network. So, a failure at one availability domain is unlikely to affect the other availability domains in the region.
- Virtual cloud network (VCN) and subnets
A VCN is a customizable, software-defined network that you set up in an Oracle Cloud Infrastructure region. Like traditional data center networks, VCNs give you complete control over your network environment. A VCN can have multiple non-overlapping CIDR blocks that you can change after you create the VCN. You can segment a VCN into subnets, which can be scoped to a region or to an availability domain. Each subnet consists of a contiguous range of addresses that don't overlap with the other subnets in the VCN. You can change the size of a subnet after creation. A subnet can be public or private.
- Security list
For each subnet, you can create security rules that specify the source, destination, and type of traffic that must be allowed in and out of the subnet.
- Route table
Virtual route tables contain rules to route traffic from subnets to destinations outside a VCN, typically through gateways.
- Internet gateway
The internet gateway allows traffic between the public subnets in a VCN and the public internet.
- Service gateway
The service gateway provides access from a VCN to other services, such as Oracle Cloud Infrastructure Object Storage. The traffic from the VCN to the Oracle service travels over the Oracle network fabric and never traverses the internet.
- Load balancer
The Oracle Cloud Infrastructure Load Balancing service provides automated traffic distribution from a single entry point to multiple servers in the back end.
- File storage
The Oracle Cloud Infrastructure File Storage service provides a durable, scalable, secure, enterprise-grade network file system. You can connect to a File Storage service file system from any bare metal, virtual machine, or container instance in a VCN. You can also access a file system from outside the VCN by using Oracle Cloud Infrastructure FastConnect and IPSec VPN.
- Container Engine for Kubernetes
Oracle Cloud Infrastructure Container Engine for Kubernetes is a fully managed, scalable, and highly available service that you can use to deploy your containerized applications to the cloud. You specify the compute resources that your applications require, and Container Engine for Kubernetes provisions them on Oracle Cloud Infrastructure in an existing tenancy. Container Engine for Kubernetes uses Kubernetes to automate the deployment, scaling, and management of containerized applications across clusters of hosts.
- Registry
Oracle Cloud Infrastructure Registry is an Oracle-managed registry that enables you to simplify your development-to-production workflow. Registry makes it easy for you to store, share, and manage development artifacts, like Docker images. The highly available and scalable architecture of Oracle Cloud Infrastructure ensures that you can deploy and manage your applications reliably.
- Compute
The Oracle Cloud Infrastructure Compute service enables you to provision and manage compute hosts in the cloud. You can launch compute instances with shapes that meet your resource requirements for CPU, memory, network bandwidth, and storage. After creating a compute instance, you can access it securely, restart it, attach and detach volumes, and terminate it when you no longer need it.