Steps in the SASL Cycle
The following diagram shows steps in the SASL life cycle. The client actions are shown on the left of the diagram and the server actions on the right side. The arrows in the middle show interactions between the client and server over an external connection.
Figure 7-2 SASL Life Cycle
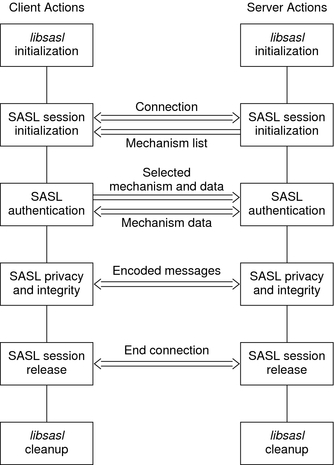
The sections that follow illustrate the steps in the life cycle.
libsasl Initialization
The client calls sasl_client_init() to initialize libsasl for the client's use. The server calls sasl_server_init() to initialize libsasl for server use.
When sasl_client_init() is run, the SASL client, the client's mechanisms and the client's canonicalization plug-in are loaded. Similarly, when sasl_server_init() is called, the SASL server, the server's mechanisms, the server's canonicalization plug-in, and the server's auxprop plug-in are loaded. After sasl_client_init() has been called, additional client plug–ins can be added by using sasl_client_add_plugin() and sasl_canonuser_add_plugin(). On the server side, after sasl_server_init() has been called, additional server plug–ins can be added through sasl_server_add_plugin(), sasl_canonuser_add_plugin(), and sasl_auxprop_add_plugin().
32-bit SPARC architecture: /usr/lib/sasl
32-bit x86 architecture: /usr/lib/sasl
64-bit SPARC architecture: /usr/lib/sasl/sparcv9
x64 architecture: /usr/lib/sasl/amd64
SASL mechanisms are provided in the Oracle Solaris software in the following directories according to the architecture:
The SASL_CB_GETPATH callback can be used to override the default location.
SASL_CB_GETOPT
SASL_CB_LOG
SASL_CB_GETPATH
SASL_CB_VERIFYFILE
At this point, any required global callbacks are set. SASL clients and servers might include the following callbacks:
A SASL server might additionally include the SASL_CB_GETCONF callback.
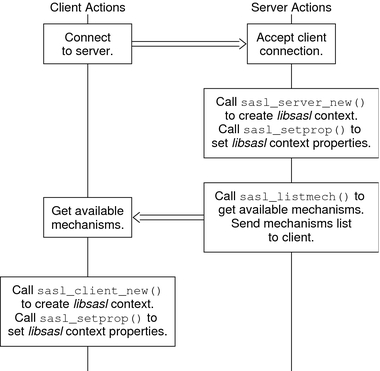
SASL Session Initialization
The server and client use establish the connection through the protocol. To use SASL for authentication, the server and client create SASL connection contexts by using sasl_server_new() and sasl_client_new() respectively. The SASL client and server can use sasl_setprop() to set properties that impose security restrictions on mechanisms. This approach enables a SASL consumer application to decide the minimum SSF, the maximum SSF, and the security properties for the specified SASL connection context.
#define SASL_SEC_NOPLAINTEXT 0x0001 #define SASL_SEC_NOACTIVE 0x0002 #define SASL_SEC_NODICTIONARY 0x0004 #define SASL_SEC_FORWARD_SECRECY 0x0008 #define SASL_SEC_NOANONYMOUS 0x0010 #define SASL_SEC_PASS_CREDENTIALS 0x0020 #define SASL_SEC_MUTUAL_AUTH 0x0040
Note - Authentication and a security layer can be provided by the client-server protocol or by some other mechanism that is external to libsasl. In such a case, sasl_setprop() can be used to set the external authentication ID or the external SSF. For example, consider the case in which the protocol uses SSL with client authentication to the server. In this case, the external authentication identity can be the client's subject name. The external SSF can be the key size.
For the server, libsasl determines the available SASL mechanisms according to the security properties and the external SSF. The client obtains the available SASL mechanisms from the SASL server through the protocol.
For a SASL server to create a SASL connection context, the server should call sasl_server_new(). An existing SASL connection context that is no longer in use can be reused. However, the following parameters might need to be reset:
#define SASL_DEFUSERREALM 3 /* default realm passed to server_new or set with setprop */ #define SASL_IPLOCALPORT 8 /* iplocalport string passed to server_new */ #define SASL_IPREMOTEPORT 9 /* ipremoteport string passed to server_new */ #define SASL_SERVICE 12 /* service passed to sasl_*_new */ #define SASL_SERVERFQDN 13 /* serverFQDN passed to sasl_*_new */
You can modify any of the parameters to sasl_client_new() and sasl_server_new() except the callbacks and protocol flags.
The server and client can also establish security policy and set connection specific parameters by using sasl_setprop() to specify the following properties:
#define SASL_SSF_EXTERNAL 100 /* external SSF active (sasl_ssf_t *) */ #define SASL_SEC_PROPS 101 /* sasl_security_properties_t */ #define SASL_AUTH_EXTERNAL 102 /* external authentication ID (const char *) */
SASL_SSF_EXTERNAL – For setting the strength factor, that is, the number of bits in the key
SASL_SEC_PROPS – For defining security policy
SASL_AUTH_EXTERNAL – The external authentication ID
The server can call sasl_listmech() to get a list of the available SASL mechanisms that satisfy the security policy. The client can generally get the list of available mechanisms from the server in a protocol-dependent way.
The initialization of a SASL session is illustrated in the following diagram. In this diagram and subsequent diagrams, data checks after transmission over the protocol have been omitted for the sake of simplicity.
Figure 7-3 SASL Session Initialization
SASL Authentication
Authentication takes a variable number of client and server steps depending on the security mechanism that is used. The SASL client calls sasl_client_start() with a list of security mechanisms to use. This list typically comes from the server. libsasl selects the best mechanism to use for this SASL session, according to the available mechanisms and the client's security policy. The client's security policy controls which mechanisms are permitted. The selected mechanism is returned by sasl_client_start(). Sometimes the security mechanism for the client sometimes needs additional information for authentication. For registered callbacks, libsasl calls the specified callback unless the callback function is NULL. If the callback function is NULL, libsasl returns SASL_INTERACT and a request for needed information. If SASL_INTERACT is returned, then sasl_client_start() should be called with the requested information.
If sasl_client_start() returns SASL_CONTINUE or SASL_OK, the client should send the selected mechanism with any resulting authentication data to the server. If any other value is returned, an error has occurred. For example, no mechanism might be available.
The server receives the mechanism that has been selected by the client, along with any authentication data. The server then calls sasl_server_start() to initialize the mechanism data for this session. sasl_server_start() also processes any authentication data. If sasl_server_start() returns SASL_CONTINUE or SASL_OK, the server sends authentication data. If sasl_server_start() returns any other value, an error has occurred such as an unacceptable mechanism or an authentication failure. The authentication must be aborted. The SASL context should be either freed or reused.
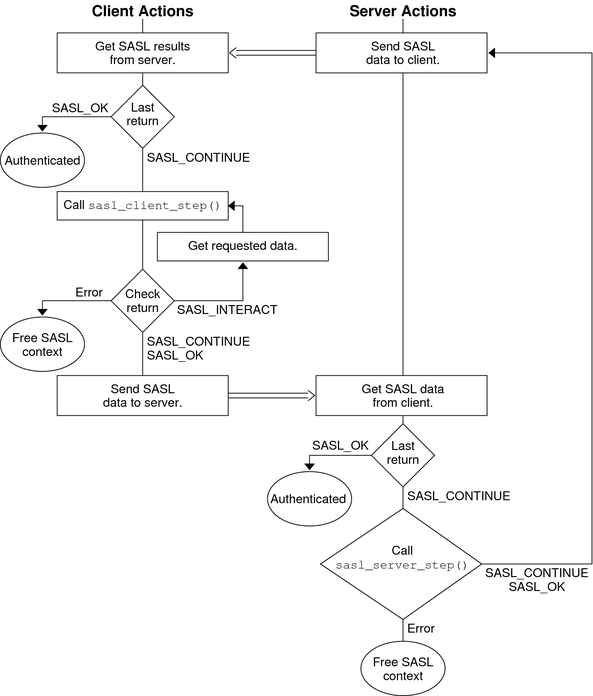
This part of the authentication process is illustrated in the following diagram.
Figure 7-4 SASL Authentication: Sending Client Data

If the server call to sasl_server_start() returns SASL_CONTINUE, the server continues to communicate with the client to get all the necessary authentication information. The number of subsequent steps depends on the mechanism. If needed, the client calls sasl_client_step() to process the authentication data from the server and to generate a reply. Similarly, the server can call sasl_server_step() to process the authentication from the client and to generate a reply in turn. This exchange continues until the authentication is complete or until an error has occurred. SASL_OK is returned to indicate that the authentication has successfully completed for the client or server. The SASL mechanism might still have additional data to send to the other side so the other side can complete authentication. When authentication has been achieved on both sides, the server and client can inquire about each other's properties.
The following diagram shows the interactions between the server and client to transfer the additional authentication data.
Figure 7-5 SASL Authentication: Processing Server Data
SASL Confidentiality and Integrity
To check for a security layer, use the sasl_getprop(3SASL) function to see if the security strength factor (SSF) has a value that is greater than 0. If a security layer has been negotiated, the client and server must use the resulting SSF after successful authentication. Data is exchanged between the client and server in a similar fashion to authentication. sasl_encode() is applied to data before the data is sent by the protocol to the client or server. On the receiving end, data is decoded by sasl_decode(). If a security layer has not been negotiated, the SASL connection context is not needed. The context can then be disposed of or reused.
Releasing SASL Sessions
A SASL connection context should only be freed when the session is not to be reused. sasl_dispose() frees the SASL connection context and all associated resources and mechanisms. The SASL connection contexts must be disposed before calling sasl_done(). sasl_done() is not responsible for releasing context resources for the SASL connection. See libsasl Cleanup.
When a SASL session is freed, the associated mechanisms are informed that all state can be freed. A SASL session should only be freed when the session is not to be reused. Otherwise, the SASL state can be reused by another session. Both the client and server use sasl_dispose() to free the SASL connection context.
libsasl Cleanup
This step releases all the resources in the SASL library and the plug-ins. The client and server call sasl_done() to release libsasl() resources and to unload all the SASL plug-ins. sasl_done() does not release SASL connection contexts. Note that if an application is both a SASL client and a SASL server, sasl_done() releases both the SASL client and SASL server resources. You cannot release the resources for just the client or the server.
 | Caution - Libraries should not call sasl_done(). Applications should exercise caution when calling sasl_done() to avoid interference with any libraries that might be using libsasl. |