| Skip Navigation Links | |
| Exit Print View | |
|
System Administration Guide: Naming and Directory Services (NIS+) |
| Skip Navigation Links | |
| Exit Print View | |
|
System Administration Guide: Naming and Directory Services (NIS+) |
Part I About Naming and Directory Services
Part II NIS+ Setup and Configuration
4. Configuring NIS+ With Scripts
5. Setting Up the NIS+ Root Domain
8. Configuring an NIS+ Non-Root Domain
10. NIS+ Tables and Information
NIS+ Authentication and Credentials
NIS+ User and Machine Credentials
DES Credentials and LOCAL Credentials in NIS+
NIS+ User Types and Credential Types
Authorization Classes and the NIS+ Object Hierarchy
NIS+ Password, Credential, and Key Commands
12. Administering NIS+ Credentials
14. Administering Enhanced NIS+ Security Credentials
15. Administering NIS+ Access Rights
16. Administering NIS+ Passwords
18. Administering NIS+ Directories
20. NIS+ Server Use Customization
23. Information in NIS+ Tables
Common NIS+ Namespace Error Messages
NIS+ security is an integral part of the NIS+ namespace. You cannot set up security and the namespace independently. For this reason, instructions for setting up security are woven through the steps used to set up the other components of the namespace. Once an NIS+ security environment has been set up, you can add and remove users, change permissions, reassign group members, and all other routine administrative tasks needed to manage an evolving network.
The security features of NIS+ protect the information in the namespace, as well as the structure of the namespace itself, from unauthorized access. Without these security features, any NIS+ client could obtain and change information stored in the namespace or even damage it.
NIS+ security does two things:
Authentication. Authentication is used to identify NIS+ principals. Every time a principal (user or machine) tries to access an NIS+ object, the user's identity and Secure RPC password is confirmed and validated.
Authorization. Authorization is used to specify access rights. Every time NIS+ principals try to access NIS+ objects, they are placed in one of four authorization classes (owner, group, world, nobody). The NIS+ security system allows NIS+ administrators to specify different read, modify, create, or destroy rights to NIS+ objects for each class. Thus, for example, a given class could be permitted to modify a particular column in the passwd table but not read that column, or a different class could be allowed to read some entries of a table but not others.
In essence, then, NIS+ security is a two-step process:
Authentication. NIS+ uses credentials to confirm that you are who you claim to be.
Authorization. Once your identity is established by the authentication process, NIS+ determines your class. What you can do with a given NIS+ object or service depends on which class you belong to. This is similar in concept to the standard UNIX file and directory permissions system. (See NIS+ Authorization Classes for more information on classes.)
This process, for example, prevents someone with root privileges on machine A from using the su command to assume the identity of a second user and then accessing NIS+ objects with the second user's NIS+ access privileges.
Note, however, that NIS+ cannot prevent someone who knows another user's login password from assuming that other user's identity and NIS+ access privileges. Nor can NIS+ prevent a user with root privileges from assuming the identity of another user who is logged in from the same machine.
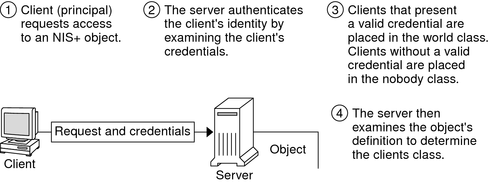
Figure 11-2 details this process.
Figure 11-2 Summary of the NIS+ Security Process
NIS+ principals are the entities (clients) that submit requests for NIS+ services. An NIS+ principal may be someone who is logged in to a client machine as a regular user, someone who is logged in as superuser, or any process that runs with superuser permission on an NIS+ client machine. Thus, an NIS+ principal can be a client user or a client machine.
An NIS+ principal can also be the entity that supplies an NIS+ service from an NIS+ server. Since all NIS+ servers are also NIS+ clients, much of this discussion also applies to servers.
NIS+ servers operate at one of two security levels. These levels determine the type of credential principals that must submit for their requests to be authenticated. NIS+ is designed to run at the most secure level, which is security level 2. Level 0 is provided only for testing, setup, and debugging purposes. These security levels are summarized in Table 11-1.
Table 11-1 List of NIS+ Security Levels
|
In Solaris releases 2.0 through 2.4, you used the nispasswd command to change your password. However, nispasswd could not function without credentials. (In other words, it could not function under security level 0 unless there were credentials existing from some previous higher level.) Starting with the Solaris 2.5 release, the passwd command must be used to change your own password regardless of security level or credential status.