| Skip Navigation Links | |
| Exit Print View | |
|
Oracle Solaris Administration: Network Interfaces and Network Virtualization Oracle Solaris 11 Express 11/10 |
| Skip Navigation Links | |
| Exit Print View | |
|
Oracle Solaris Administration: Network Interfaces and Network Virtualization Oracle Solaris 11 Express 11/10 |
2. NWAM Configuration and Administration (Overview)
3. NWAM Profile Configuration (Tasks)
4. NWAM Profile Administration (Tasks)
5. About the NWAM Graphical User Interface
Part II Administering Single Interfaces
6. Overview of the Networking Stack
7. Datalink Configuration and Administration
8. Configuring an IP Interface
9. Configuring Wireless Interface Communications on Oracle Solaris
Part III Administering Interface Groups
11. Administering Link Aggregations
Part IV Network Virtualization and Resource Management
15. Introducing Network Virtualization and Resource Control (Overview)
16. Planning for Network Virtualization and Resource Control
Network Virtualization and Resource Control Task Map
Planning and Designing a Virtual Network
Basic Virtual Network on a Single System
Best Uses for the Basic Virtual Network
Private Virtual Network on a Single System
Best Uses for a Private Virtual Network
Implementing Controls on Network Resources
Interface-based Resource Control for a Traditional Network
Best Use of Interface-based Resource Control on a Traditional Network
Flow Control for the Virtual Network
How to Create a Usage Policy for Applications on a Virtual Network
How to Create a Service Level Agreement for the Virtual Network
17. Configuring Virtual Networks (Tasks)
18. Using Link Protection in Virtualized Environments
19. Managing Network Resources
Network virtualization enables you to implement your network setup more efficiently at lower cost by constructing a network-in-a-box. To increase efficiency, you can also implement controls to determine how resources are being used by the networking processes. Link properties that are specifically related to network resources, such as rings, CPUs, and so on, can be customized to process network packets. In addition, you can also create flows to manage network usage. Network resource control is discussed in detail in Chapter 19, Managing Network Resources.
Figure 16-3 shows the network topology for a small business that needs to manage the bandwidth on its proxy server. The proxy server offers a public web site as well as a proxy for internal clients that require services from various servers on the site's internal network.
Note - This scenario does not show how to configure flow control for a virtual network, and consequentially does not include VNICs. For flow control on a virtual network, refer to Flow Control for a Virtual Network.
Figure 16-3 Resource Control for a Proxy Server on a Traditional Network
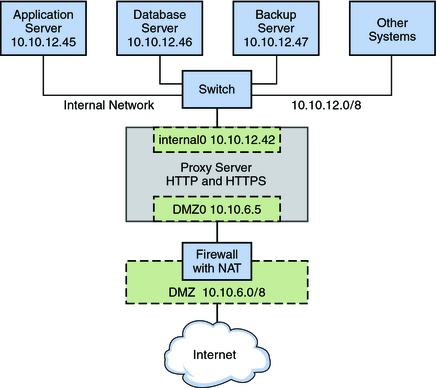
The figure shows that the company has a public network, 10.10.6.0/8, that also serves as a demilitarized zone (DMZ). A system on the DMZ provides name-to-address translation (NAT) through an IP Filter firewall. The company has a large system that functions as the proxy server. The system has two wired interfaces and 16 processor sets with IDs 0–16. This system is connected to the public network through the interface nge0, with IP address l0 10.6.5. The link name for the interface is DMZ0. Through DMZ0, the proxy server offers HTTP and HTTPS service through the company's public web site.
The figure also illustrates the company's internal network, 10.10.12.0/24. The proxy server connects to the internal 10.10.12.0/8 network through interface nge1, with the IP address 10.10.12.42. The link name for this interface is internal0. Through the internal0 datalink, the proxy server operates on behalf of internal clients that request the services of an application server, 10.10.12.45, database server, 10.10.12.46, and backup server, 10.10.12.47.
Consider establishing flow control for heavily used systems, especially those with newer GLDv3 interfaces with large amounts of available bandwidth. Interface-based flow control improves the efficiency of the interface, the system, and potentially the network. You can apply flow control to any system on any type of network. Furthermore, if your goal is to improve network efficiency, you can separate various services into individual flows. This action assigns separate hardware and software resources to the individual flows, thus isolating them from other services on a particular system. After you establish flows, you can observe traffic for each flow and gather statistics. Thereafter, you can assign bandwidth amount and priorities to control usage on the interfaces.
For tasks for implementing flow control, refer to Chapter 19, Managing Network Resources
For conceptual information about bandwidth management and resource control, refer to What Is Resource Control?
For detailed technical information, refer to the dladm(1M) and flowadm(1M)man pages.
This scenario shows how flow control is used within a virtual network, such as the basic virtual network that is introduced in Basic Virtual Network on a Single System.
Figure 16-4 Basic Virtual Network With Flow Controls
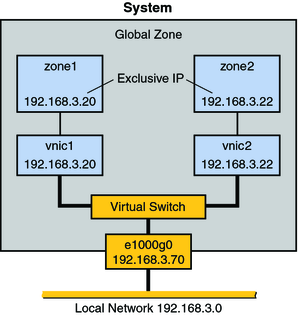
The topology is described in Basic Virtual Network on a Single System. Here a host has one network interface, e1000g0, with two VNICs, vnic1 and vnic2. zone1 is configured over vnic1, and zone2 is configured over vnic2. Resource management for the virtual network involves creating flows on a per-VNIC basis. These flows define and isolate packets with similar characteristics, such as port number or IP address of the sending host. You assign bandwidth based on the usage policy for the system.
Another very common usage for flow controls on VNIC traffic is by companies that rent out zones. You create different service level agreements for customers, and rent out zones with a guaranteed amount of bandwidth. When you create flows on a per-zone basis, you can isolate and observe each customer's traffic and monitor bandwidth usage. If your service level agreement is based strictly on usage, you can use statistics and accounting features to bill customers.
Flow controls are effective for any network that requires bandwidth management for traffic over zones. Larger organizations, such as application service providers (ASPs) or Internet service providers (ISP), can take advantage of resource control for VNICs for data centers and for multiprocessor systems. The individual zones can be rented out to customers for different levels of service. Therefore, you could rent out zone1 at the standard price and offer a standard bandwidth. Then, you could rent out zone2 at a premium price and give that customer a high level of bandwidth.
For example, the telnet application might not consume huge amounts of bandwidth on your system, but it could be heavily used. Conversely, database applications consume a huge amount of bandwidth, but might only be used on a sporadic basis. Consider monitoring traffic for these applications prior to assigning them to zones. You can use the statistical option of the dladm show-link command to gather statistics, as described in Gathering Statistics About Network Traffic on Links.
For example, you might create a basic, superior, and high levels of service, and price each level accordingly.
If you choose the latter pricing structure, you need to gather statistics on each customer's usage.
A very common implementation is to give each customer their own zone running over a VNIC.
To isolate all traffic for the zone, you use the IP address that is assigned to the zone's VNIC.