1 About the Connector
Oracle Identity Manager automates access rights management, security, and provisioning of IT resources. Oracle Identity Manager connectors are used to integrate Oracle Identity Manager with external, identity-aware applications. This guide discusses the connector that enables you to use Google Apps as a managed (target) resource of Oracle Identity Manager.
Note:
At some places in this guide, the term target system has been used to refer to Google Apps.
In the account management (target resource) mode of the connector, data about users created or modified directly on the target system can be reconciled into Oracle Identity Manager. This data is used to provision (allocate) new resources or update resources already assigned to OIM Users. In addition, you can use Oracle Identity Manager to provision or update Google Apps resources (that is, accounts) assigned to OIM Users. These provisioning operations performed on Oracle Identity Manager translate into the creation of or updates to target system accounts.
This chapter contains the following sections:
1.1 Certified Components
These are the software components and their versions required for installing and using the connector.
Certified Components lists certified components for the connector.
Table 1-1 Certified Components
| Component | Requirement |
|---|---|
|
Oracle Identity Governance or Oracle Identity Manager |
You can use one of the following releases of Oracle Governance or Oracle Identity Manager:
|
|
Target systems |
Google Apps |
|
Connector Server |
1.4.0 |
|
Connector Server JDK |
JDK 1.6 or later |
1.2 Certified Languages
The connector supports the following languages:
-
Arabic
-
Chinese (Simplified)
-
Chinese (Traditional)
-
Czech
-
Danish
-
Dutch
-
English
-
Finnish
-
French
-
French (Canadian)
-
German
-
Greek
-
Hebrew
-
Hungarian
-
Italian
-
Japanese
-
Korean
-
Norwegian
-
Polish
-
Portuguese
-
Portuguese (Brazilian)
-
Romanian
-
Russian
-
Slovak
-
Spanish
-
Swedish
-
Thai
-
Turkish
1.3 Connector Architecture
The connector enables you to manage accounts on the target system. Managing accounts consists of the following processes:
-
Provisioning
Provisioning involves creating or updating users on the target system through Oracle Identity Manager. When you allocate (or provision) a Google Apps resource to an OIM User, the operation results in the creation of an account on Google Apps for that user. In the Oracle Identity Manager context, the term provisioning also covers updates made to the target system account through Oracle Identity Manager.
-
Target resource reconciliation
In target resource reconciliation, data related to newly created and modified target system accounts can be reconciled and linked with existing OIM Users and provisioned resources. A scheduled task is used for reconciliation.
Figure 1-1 shows Google Apps connector integration with Oracle Identity Manager.
Figure 1-1 Architecture of the Google Apps Connector
Description of "Figure 1-1 Architecture of the Google Apps Connector "
As shown in this figure, Google Apps is configured as a target resource of Oracle Identity Manager. Through provisioning operations performed on Oracle Identity Manager, accounts are created and updated on the target system for OIM Users. Through reconciliation, account data that is created and updated directly on the target system is fetched into Oracle Identity Manager and stored against the corresponding OIM Users.
Identity Connector Framework (ICF) is a component that is required in order to use Identity Connectors. ICF is distributed together with Oracle Identity Manager. You do not need to configure or modify ICF.
During provisioning, the Adapters invoke ICF operation, ICF inturn invokes create operation on Google Apps Identity Connector Bundle and then the bundle calls Google Apps Provisioning API. The Google Apps provisioning API on the target system accepts provisioning data from the bundle, carries out the required operation on the target system, and returns the response from the target system back to the bundle, which passes it to the adapters.
During reconciliation, a scheduled task invokes ICF operation, ICF inturn invokes create operation on Google Apps Identity Connector Bundle and then the bundle calls Google Apps Reconciliation API. The API extracts user records that match the reconciliation criteria and hands them over through the bundle and ICF back to the scheduled task, which brings the records to Oracle Identity Manager.
See Also:
Understanding the Identity Connector Framework in Oracle Fusion Middleware Developing and Customizing Applications for Oracle Identity Manager for more information about ICF
Each record fetched from the target system is compared with Google Apps resources that are already provisioned to OIM Users. If a match is found, then the update made to the Google Apps record from the target system is copied to the Google Apps resource in Oracle Identity Manager. If no match is found, then the user ID of the record is compared with the user ID of each OIM User. If a match is found, then data in the target system record is used to provision a Google Apps resource to the OIM User.
The Google Apps Identity Connector Bundle communicates with the Google Apps Admin SDK's Directory API using the HTTPS protocol. Internally, the library uses the java.net.HttpURLConnection class. When you deploy and start using the connector, it sets the following system properties for configuring the proxy for the connections created by the HttpURLConnection class:
-
https.proxyPort
-
https.proxyHost
Note:
Setting of these system properties might have an impact on the JVM and all other classes that use the HttpURLConnection class.
In addition, to support user name/password based proxy authentication, the connector provides and registers an implementation of the java.net.Authenticator class.
Depending on your application server configuration, it might be necessary to import google certificates to application server keystore/truststore.
1.4 Features of the Connector
The following are features of the connector:
1.4.1 Full Reconciliation
In full reconciliation, all records are fetched from the target system to Oracle Identity Manager.
Note:
The connector cannot support incremental reconciliation because the target system does not provide a way for tracking the time at which account data is created or modified.
For more information, see Full Reconciliation.
1.4.2 Batched Reconciliation
You can break down a reconciliation run into batches by specifying the number of records that must be included in each batch.
For more information, see Batched Reconciliation.
1.4.3 Support for the Connector Server
Connector Server is one of the features provided by ICF. By using one or more connector servers, the connector architecture permits your application to communicate with externally deployed bundles.
A Java connector server is useful when you do not want to execute a Java connector bundle in the same VM as your application. It can be beneficial to run a Java connector on a different host for performance improvements if the bundle works faster when deployed on the same host as the native managed resource.
See Also:
Using an Identity Connector Server in Oracle Fusion Middleware Developing and Customizing Applications for Oracle Identity Manager for information about installing and configuring connector server and running the connector server
1.4.4 Support for Reconciliation of Account Status
Support for reconciliation of account status is one of the features where the connector fetches the status information during a reconciliation operation.
During a reconciliation run, the connector can fetch status information along with the rest of the account data.
1.4.5 Support for Reconciliation of Deleted Account Data
The Google Apps Target Resource User Delete Reconciliation scheduled task can be used to fetch details of deleted target system users.
This information is used to revoke the corresponding Google Apps resources from OIM Users.
1.4.6 Support for Connector Operations in Multiple Domains
By default, this connector supports reconciliation and provisioning operations within a single domain. However, you can configure the connector for performing connector operations in more than one domain by specifying a value for the supportMultipleDomain entry of the Main configuration lookup definition.
For more information, see Lookup.Configuration.GoogleApps.
1.5 Lookup Definitions Used During Connector Operations
Lookup definitions used during reconciliation and provisioning are either preconfigured or can be synchronized with the target system.
Lookup definitions used during connector operations can be categorized as follows:
1.5.1 Lookup Definitions Synchronized with the Target System
Lookup field synchronization involves copying additions or changes made to specific fields in the target system to lookup definitions in Oracle Identity Manager.
During a provisioning operation, you use the Group Name lookup field on the process form to specify a group for the user for whom the provisioning operation is being performed. The Group Name lookup field is populated with values from the Lookup.GoogleApps.Groups lookup definition, which is automatically created on Oracle Identity Manager when you deploy the connector.
The Code Key and Decode columns contain values of the __NAME__ connector attribute. The __NAME__ attribute of both Code Key and Decode columns is mapped to Group email address in the target system.
When you perform lookup field synchronization, Groups on the target system are fetched to Oracle Identity Manager and populated in the Lookup.GoogleApps.Groups lookup definition. You use the Google Apps Lookup Recon scheduled task to perform lookup field synchronization. Configuring Scheduled Jobs describes this scheduled job.
1.5.2 Preconfigured Lookup Definitions
Preconfigured lookup definitions are the other lookup definitions that are created in Oracle Identity Manager when you deploy the connector. These lookup definitions are either prepopulated with values or values must be manually entered in them after the connector is deployed.
This section discusses the other lookup definitions that are created in Oracle Identity Manager when you deploy the connector. The other lookup definitions are as follows:
1.5.2.1 Lookup.Configuration.GoogleApps
The Lookup.Configuration.GoogleApps lookup definition contains the entries shown in Table 1-2.
Table 1-2 Entries in the Lookup.Configuration.GoogleApps Lookup Definition
| Code Key | Decode | Description |
|---|---|---|
|
Bundle Name |
org.identityconnectors.googleapps |
This entry holds the name of the connector bundle. Do not modify this entry. |
|
Bundle Version |
1.2.1 |
This entry holds the version of the connector bundle. Do not modify this entry. |
|
Connector Name |
org.identityconnectors.googleapps.GoogleAppsConnector |
This entry holds the name of the connector class. Do not modify this entry. |
|
Group Configuration Lookup |
Lookup.GoogleApps.GM.Configuration |
This entry holds the name of the lookup definition that contains group-specific configuration properties. Do not modify this entry. |
|
supportMultipleDomain |
false |
This entry specifies whether the connector is configured to perform connector operations in a single or multiple domain. By default, the connector performs connector operations only on the domain specified in IT resource. Set the value of this entry to |
|
User Configuration Lookup |
Lookup.GoogleApps.UM.Configuration |
This entry holds the name of the lookup definition that stores configuration information used during user management operations. Do not modify this entry. |
1.5.2.2 Lookup.GoogleApps.UM.Configuration
The Lookup.GoogleApps.UM.Configuration lookup definition holds configuration entries that are specific to the user object type. This lookup definition is used during user management operations.
Table 1-3 lists the default entries in this lookup definition.
Table 1-3 Entries in the Lookup.GoogleApps.UM.Configuration Lookup Definition
| Code Key | Decode | Description |
|---|---|---|
|
Provisioning Attribute Map |
Lookup.GoogleApps.UM.ProvAttrMap |
This entry holds the name of the lookup definition that stores attribute mappings between Oracle Identity Manager and the target system. This lookup definition is used during provisioning operations. |
|
Recon Attribute Map |
Lookup.GoogleApps.UM.ReconAttrMap |
This entry holds the name of the lookup definition that stores attribute mappings between Oracle Identity Manager and the target system. This lookup definition is used during reconciliation. |
1.5.2.3 Lookup.GoogleApps.UM.ProvAttrMap
The Lookup.GoogleApps.UM.ProvAttrMap lookup definitions hold mappings between process form fields (Code Key values) and target system attributes (Decode). This lookup definition is preconfigured and is used during provisioning. Table 1-4 lists the default entries.
Table 1-4 Entries in the Lookup.GoogleApps.UM.ProvAttrMap Lookup Definitions
| Code Key (Process Form Field) | Decode (Google Apps Field) |
|---|---|
|
Account Name |
__NAME__ |
|
Change Password At Next Login |
changePasswordAtNextLogin |
|
Family Name |
familyName |
|
Given Name |
givenName |
|
Is Admin |
isAdmin |
|
OrgUnit Path |
orgunitpath |
|
Password |
__PASSWORD__ |
|
UD_GA_GROUP~Group Name[Lookup] |
groups |
|
UD_GA_NICK~Nick Name |
aliases |
|
Unique Id |
__UID__ |
1.5.2.4 Lookup.GoogleApps.UM.ReconAttrMap
The Lookup.GoogleApps.UM.ReconAttrMap lookup definition holds mappings between resource object fields (Code Key values) and target system attributes (Decode). This lookup definition preconfigured and is used during reconciliation. Table 1-5 lists the default entries.
Table 1-5 Entries in the Lookup.GoogleApps.UM.ReconAttrMap Lookup Definition
| Code Key (Resource Object Field) | Decode (Google Apps Field) |
|---|---|
|
Account Name |
__NAME__ |
|
Change Password At Next Login |
changePasswordAtNextLogin |
|
Family Name |
familyName |
|
Given Name |
givenName |
|
Group Names~Group Name[Lookup] |
groups |
|
Is Admin |
isAdmin |
|
Nick Names~Nick Name |
aliases |
|
OrgUnit Path |
orgunitpath |
|
Status |
__ENABLE__ |
|
Unique Id |
__UID__ |
1.5.2.5 Lookup.GoogleApps.GM.Configuration
The Lookup.GoogleApps.GM.Configuration lookup definition holds configuration entries that are specific to the group object type. This lookup definition is used during group management operations when your target system is configured as a target resource.
Table 1-6 lists the default entries in this lookup definition.
Table 1-6 Entries in the Lookup.GoogleApps.GM.Configuration Lookup Definition
| Code Key | Decode | Description |
|---|---|---|
|
Provisioning Attribute Map |
Lookup.GoogleApps.GM.ProvAttrMap |
This entry holds the name of the lookup definition that stores attribute mappings between Oracle Identity Manager and the target system. This lookup definition is used during provisioning operations. |
|
Recon Attribute Map |
Lookup.GoogleApps.GM.ReconAttrMap |
This entry holds the name of the lookup definition that stores attribute mappings between Oracle Identity Manager and the target system. This lookup definition is used during reconciliation. |
1.5.2.6 Lookup.GoogleApps.GM.ProvAttrMap
The Lookup.GoogleApps.GM.ProvAttrMap lookup definition holds mappings between process form fields (Code Key values) and target system attributes (Decode). This lookup definition is preconfigured and is used during group provisioning operations. Table 1-7 lists the default entries.
Table 1-7 Entries in the Lookup.GoogleApps.GM.ProvAttrMap Lookup Definition
| Group Field on Oracle Identity Manager | Google Apps Field |
|---|---|
|
Allow External Members |
allowExternalMembers |
|
Description |
description |
|
Email Address |
|
|
Group Name |
name |
|
Is Archived |
isArchived |
|
Unique Id |
__UID__ |
|
Who Can Join |
whoCanJoin |
|
Who Can View Group |
whoCanViewGroup |
|
Who Can View Membership |
whoCanViewMembership |
1.5.2.7 Lookup.GoogleApps.GM.ReconAttrMap
The Lookup.ActiveDirectory.GM.ReconAttrMap lookup definition holds mappings between resource object fields (Code Key values) and target system attributes (Decode). This lookup definition is preconfigured and is used during target resource group reconciliation runs. Table 1-8 lists the default entries.
Table 1-8 Entries in the Lookup.GoogleApps.GM.ReconAttrMap Lookup Definition
| Group Field on Oracle Identity Manager | Google Apps Field |
|---|---|
|
Allow External Members |
allowExternalMembers |
|
Description |
description |
|
Email Address |
|
|
Group Name |
name |
|
Is Archived |
isArchived |
|
OIM Org Name |
Organization Name Note: This is a connector attribute. The value of this attribute is used internally by the connector to specify the organization of the groups in Oracle Identity Manager. |
|
Unique Id |
__UID__ |
|
Who Can Join |
whoCanJoin |
|
Who Can View Group |
whoCanViewGroup |
|
Who Can View Membership |
whoCanViewMembership |
1.6 Connector Objects Used During Target Resource Reconciliation
Target resource reconciliation involves fetching data about newly created or modified accounts on the target system and using this data to add or modify resources assigned to OIM Users.
The GoogleApps Target Resource User Reconciliation scheduled job is used to initiate a reconciliation run. This scheduled job is discussed in –------
This section discusses the following topics:
1.6.1 User Fields for Target Resource Reconciliation
The Lookup.GoogleApps.UM.ReconAttrMap lookup definition maps resource object fields with target system attributes. This lookup definition is used for performing target resource user reconciliation runs.
In this lookup definition, entries are in the following format:
- Code Key: Reconciliation field of the resource object
- Decode: Name of the target system attribute
Table 1-9 lists the entries in this lookup definition.
Table 1-9 Entries in the Lookup.GoogleApps.UM.ReconAttrMap Lookup Definition
| Code Key (Resource Object Field) | Decode (Google Apps Field) |
|---|---|
| Account Name | __NAME__ |
| Change Password At Next Login | changePasswordAtNextLogin |
| Family Name | familyName |
| Given Name | givenName |
| Group Names~Group Name[Lookup] | groups |
| Is Admin | isAdmin |
| Nick Names~Nick Name | aliases |
| OrgUnit Path | orgunitpath |
| Status | __ENABLE__ |
| Unique Id | __UID__ |
1.6.2 Group Fields for Reconciliation
The Lookup.GoogleApps.GM.ReconAttrMap lookup definition maps user resource object fields and target system attributes. This lookup definition is used for performing target resource group reconciliation runs.
Table 1-9 lists the group fields of the target system from which values are fetched during reconciliation. The GoogleApps Group Recon scheduled job is used to reconcile group data.
Table 1-10 Entries in the Lookup.GoogleApps.GM.ReconAttrMap Lookup Definition
| Group Field on Oracle Identity Manager | Google Apps Field |
|---|---|
| Google Apps Field | allowExternalMembers |
| Description | description |
| Email Address | |
| Group Name | name |
| Is Archived | isArchived |
| OIM Org Name |
Organization Name Note: This is a connector attribute. The value of this attribute is used internally by the connector to specify the organization of the groups in Oracle Identity Manager. |
| Unique Id | __UID__ |
| Who Can Join | whoCanJoin |
| Who Can View Group | whoCanViewGroup |
| Who Can View Membership | whoCanViewMembership |
1.6.3 Reconciliation Rules
The following sections provide information about the reconciliation rules for this connector:
1.6.3.1 Reconciliation Rule for Users
The following is the process-matching rule for users:
Rule name: GoogleApps User Recon Rule
Rule element: (GAPPS User GUID Equals Unique ID) OR (User Login Equals Tokenize(Account Name))
In this first rule component:
-
GAPPS User GUID is a UDF on the OIM User form that holds the unique ID of the Google Apps user.
-
Unique ID is the UID field of the Google Apps account.
In this second rule component:
-
User Login is the User ID field of the OIM User form.
-
Tokenize(Account Name) is the name part in the email address of the Google Apps account.
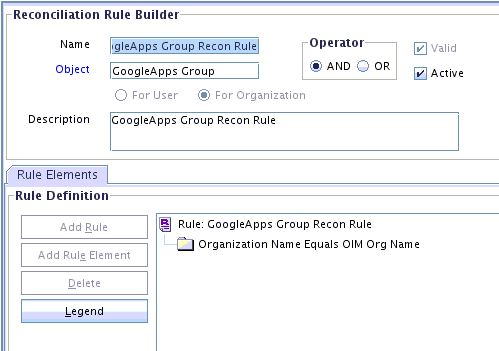
1.6.3.2 Reconciliation Rule for Groups
The following is the process-matching rule for groups:
Rule name: GoogleApps Groups Recon Rule
Rule element: Organization Name Equals OIM Org Name
In this rule element:
-
Organization Name is the Organization Name field of the OIM User form.
-
OIM Org Name is the organization name of the groups in Oracle Identity Manager. OIM Org Name is the value specified in the Organization Name attribute of the GoogleApps Group Recon scheduled job.
1.6.4 Reconciliation Action Rules
Reconciliation action rules specify actions that must be taken depending on whether or not matching Google Apps resources or OIM Users are found when the reconciliation rule is applied.
Note:
No action is performed for rule conditions that are not predefined for this connector. You can define your own action rule for such rule conditions.
The following sections provide information about the reconciliation rules for this connector:
1.6.4.1 Reconciliation Action Rules for User and Groups
Table 1-11 lists the action rules for both users and groups reconciliation.
Table 1-11 Action Rules for Reconciliation
| Rule Condition | Action |
|---|---|
|
No Matches Found |
Assign to Administrator With Least Load |
|
One Entity Match Found |
Establish Link |
|
One Process Match Found |
Establish Link |
1.7 Connector Objects Used During Provisioning
Provisioning involves creating or modifying user data on the target system through Oracle Identity Manager.
This section discusses the following topics:
1.7.1 Provisioning Functions
These are the supported provisioning functions and the adapters that perform these functions for the Google Apps connector.
Table 1-12 lists the supported provisioning functions and the adapters that perform these functions. The Adapter column gives the name of the adapter that is used when the function is performed.
See Also:
Process Task Adapters in Oracle Fusion Middleware Developing and Customizing Applications for Oracle Identity Manager for generic information about process tasks and adapters
Table 1-12 User Provisioning Functions
| Function | Adapter |
|---|---|
|
Create User |
adpGOOGLEAPPSCREATEOBJECT |
|
Update User |
adpGOOGLEAPPSUPDATEATTRIBUTEVALUE |
|
Delete user |
adpGOOGLEAPPSDELETEOBJECT |
|
Enable user |
adpGOOGLEAPPSENABLEUSER |
|
Disable user |
adpGOOGLEAPPSDISABLEUSER |
|
Change or reset password |
adpGOOGLEAPPSUPDATEATTRIBUTEVALUE |
|
Update child table values |
adpGOOGLEAPPSUPDATECHILDTABLEVALUE |
|
Add child table values |
adpGOOGLEAPPSADDCHILDTABLEVALUES |
|
Remove child table values for a user |
adpGOOGLEAPPSREMOVECHILDTABLEVALUES |
1.7.2 User Fields for Provisioning
The Lookup.GoogleApps.UM.ProvAttrMap lookup definition maps process form fields with Google Apps fields. This lookup definition is used for performing user provisioning operations.
In this lookup definition, entries are in the following format:
- Code Key: Name of the process form field
- Decode: Name of the target system attribute
Table 1-13 lists the entries in this lookup definition.
Table 1-13 Entries in the Lookup.GoogleApps.UM.ProvAttrMap Lookup Definitions
| Code Key (Process Form Field) | Decode (Google Apps Field) |
|---|---|
| Account Name | __NAME__ |
| Change Password At Next Login | changePasswordAtNextLogin |
| Family Name | familyName |
| Given Name | givenName |
| Is Admin | isAdmin |
| OrgUnit Path | orgunitpath |
| Password | __PASSWORD__ |
| UD_GA_GROUP~Group Name[Lookup] | groups |
| UD_GA_NICK~Nick Name | aliases |
| Unique Id | __UID__ |
1.7.3 Group Fields for Provisioning
The Lookup.GoogleApps.GM.ProvAttrMap lookup definition maps user resource object fields and target system attributes. This lookup definition is used for performing group provisioning operations.
Table 1-14 lists the group fields of the target system for which you can specify or modify values during provisioning operations.
Table 1-14 Entries in the Lookup.GoogleApps.GM.ProvAttrMap Lookup Definition
| Group Field on Oracle Identity Manager | Google Apps Field |
|---|---|
| Allow External Members | allowExternalMembers |
| Description | description |
| Email Address | |
| Group Name | name |
| Is Archived | isArchived |
| Unique Id | __UID__ |
| Who Can Join | whoCanJoin |
| Who Can View Group | whoCanViewGroup |
| Who Can View Membership | whoCanViewMembership |