Virtual Private Networks and IPsec
The term virtual private network (VPN) is often used to describe a private, secure, point-to-point network that is built over a more public network, for example, the Internet. The point-to-point network, or VPN, can be used to connect systems on private networks, or networks of systems on private networks together.
A configured tunnel is a point-to-point interface. The tunnel enables one IP packet to be encapsulated within another IP packet. A correctly configured tunnel requires both a tunnel source and a tunnel destination. For more information, see How to Create and Configure an IP Tunnel in Administering TCP/IP Networks, IPMP, and IP Tunnels in Oracle Solaris 11.2 .
A tunnel creates an apparent physical interface to IP. IP traffic that passes over the IP tunnel interface can be protected with IPsec.
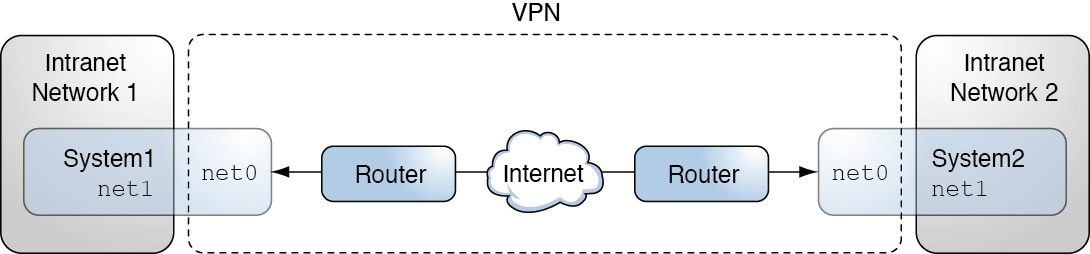
The tunnel interface in Oracle Solaris can be used to encapsulate, or tunnel, an IP packet from one system to another system. The tunneled packet adds an IP header in front of the original IP header. The added header uses addresses that are routable on the public network. These addresses are represented by the net0 interfaces in the following diagram.
The following figure illustrates how two sites can use IPsec to create a VPN between them. Traffic between Intranet 1 and Intranet 2 is tunneled over the Internet by using IP-in-ESP encapsulation. In this case, the net0 addresses are used in the outer IP headers, while the inner IP addresses are those of the tunneled packets from the intranet networks. Because the inner IP addresses are covered by ESP, they are protected from inspection as traffic crosses the Internet.
Figure 6-6 Virtual Private Network
For a detailed example of the setup procedure, see How to Protect the Connection Between Two LANs With IPsec in Tunnel Mode.