IPsec Packet Flow
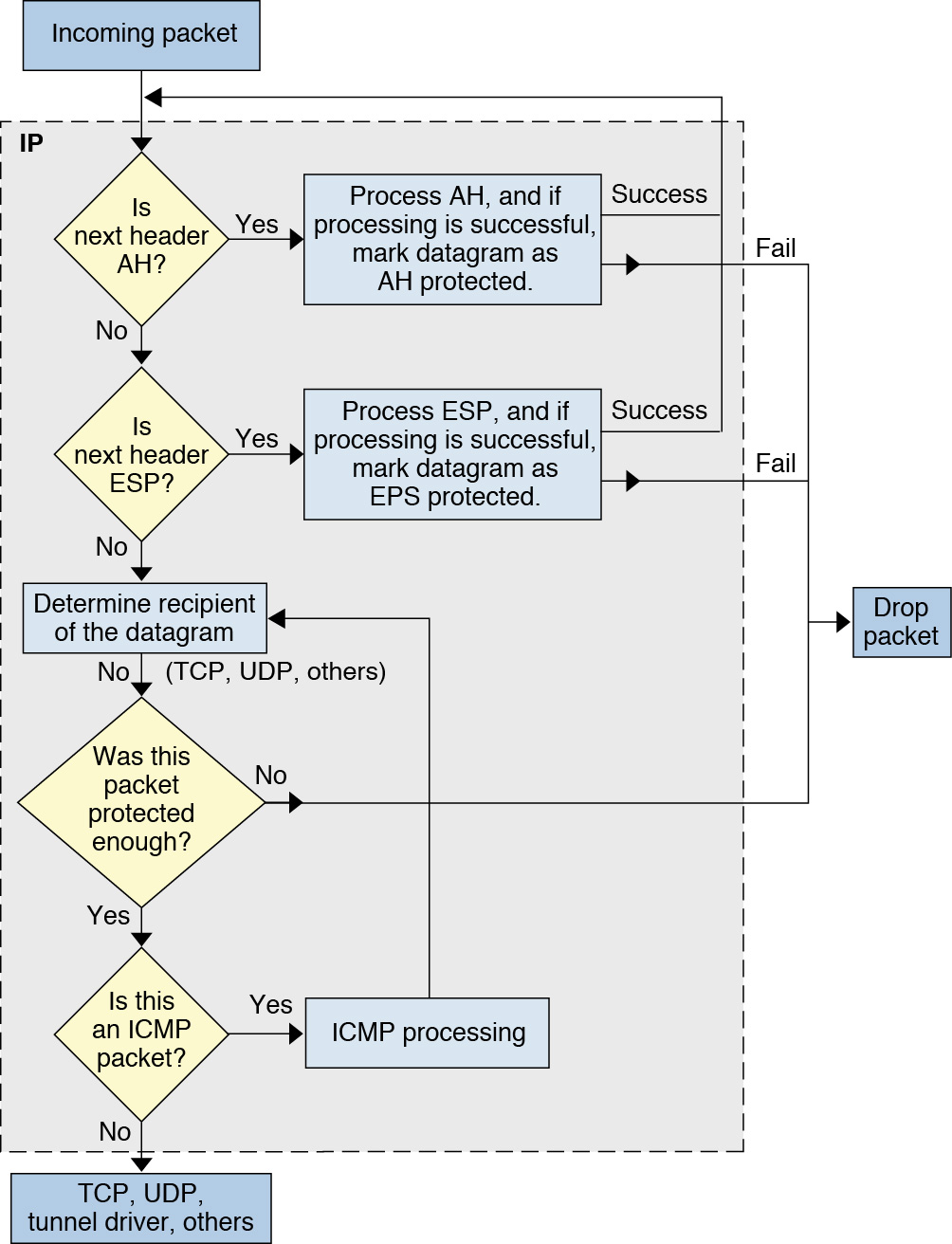
Figure 6–1 shows how an IP packet proceeds when IPsec has been invoked on an outbound packet. The flow diagram illustrates where authentication header (AH) and encapsulating security payload (ESP) entities can be applied to the packet. Subsequent sections describe how to apply these entities, as well as how to choose the algorithms.
Figure 6–2 shows the IPsec inbound process.
Figure 6-1 IPsec Applied to Outbound Packet Process
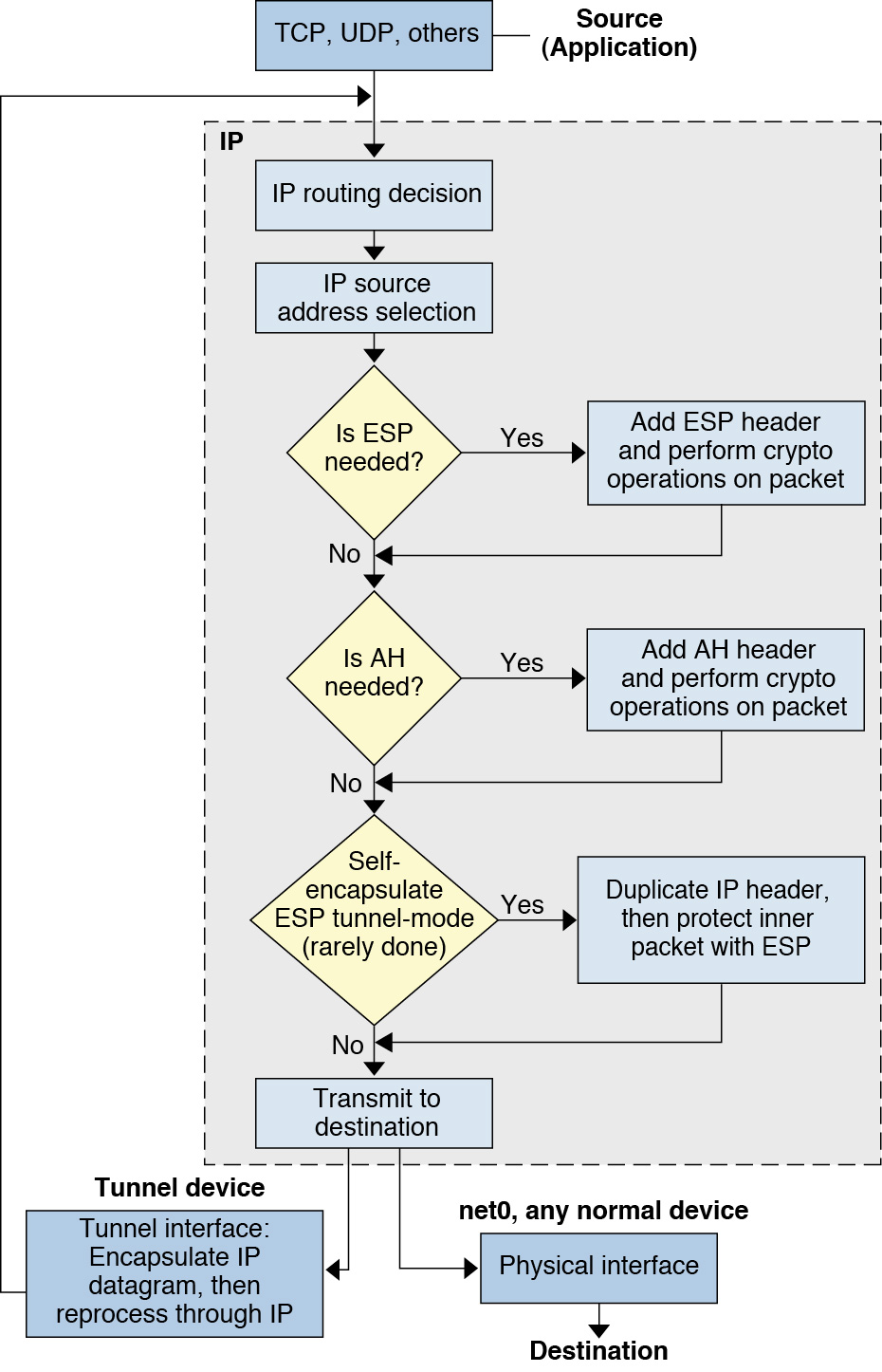
Figure 6-2 IPsec Applied to Inbound Packet Process