| Skip Navigation Links | |
| Exit Print View | |
|
Oracle VM Server for SPARC 3.1 Security Guide |
Chapter 1 Oracle VM Server for SPARC Security Overview
Security Features Used by Oracle VM Server for SPARC
Applying General Security Principles to Oracle VM Server for SPARC
Security in a Virtualized Environment
Securing the Execution Environment
Threat: Unintentional Misconfiguration
Countermeasure: Creating Operational Guidelines
Threat: Errors in the Architecture of the Virtual Environment
Countermeasure: Carefully Assigning Guests to Hardware Platforms
Countermeasure: Planning an Oracle VM Server for SPARC Domain Migration
Countermeasure: Correctly Configuring Virtual Connections
Countermeasure: Using VLAN Tagging
Countermeasure: Using Virtual Security Appliances
Threat: Side Effects of Sharing Resources
Evaluation: Side Effects Through Shared Resources
Countermeasure: Carefully Assigning Hardware Resources
Countermeasure: Carefully Assigning Shared Resources
Summary: Side Effects Through Shared Resources
Threat: Manipulation of the Execution Environment
Evaluation: Manipulation of the Execution Environment
Countermeasure: Securing Interactive Access Paths
Countermeasure: Minimizing the Oracle Solaris OS
Countermeasure: Hardening the Oracle Solaris OS
Countermeasure: Using Role Separation and Application Isolation
Countermeasure: Configuring a Dedicated Management Network
Threat: Complete System Denial-of-Service
Evaluation: Complete System Denial-of-Service
Countermeasure: Securing the ILOM
Threat: Breaking the Isolation
Evaluation: Breaking the Isolation
Countermeasure: Validating Firmware and Software Signatures
Countermeasure: Validating Kernel Modules
Threat: Control Domain Denial-of-Service
Evaluation: Control Domain Denial-of-Service
Countermeasure: Securing Console Access
Threat: Unauthorized Use of Configuration Utilities
Evaluation: Unauthorized Use of Configuration Utilities
Countermeasure: Applying the Two-Person Rule
Countermeasure: Using Rights for the Logical Domains Manager
Countermeasure: Hardening the Logical Domains Manager
Countermeasure: Auditing the Logical Domains Manager
Threat: Manipulation of a Service Domain
Evaluation: Manipulation of a Service Domain
Countermeasure: Granularly Segregating Service Domains
Countermeasure: Isolating Service Domains and Guest Domains
Countermeasure: Restricting Access to Virtual Consoles
Threat: Experiencing a Denial-of-Service of an I/O Domain or a Service Domain
Evaluation: Experiencing a Denial-of-Service of an I/O Domain or a Service Domain
Countermeasure: Granularly Configuring I/O Domains
Countermeasure: Configuring Redundant Hardware and Root Domains
Threat: Manipulation of an I/O Domain
Evaluation: Manipulation in an I/O Domain
Countermeasure: Protecting Virtual Disks
Countermeasure: Securing the Guest Domain OS
Chapter 2 Secure Installation and Configuration of Oracle VM Server for SPARC
Oracle VM Server for SPARC provides highly efficient, enterprise-class virtualization capabilities for Oracle's SPARC T-Series servers as well as the SPARC M5 server and Fujitsu M10 systems. Using the Oracle VM Server for SPARC software, you can create many virtual servers, called logical domains, on a single system. This kind of configuration enables you to take advantage of the massive thread scale offered by these SPARC servers and the Oracle Solaris OS.
A logical domain is a virtual machine that contains a discrete logical grouping of resources. A logical domain has its own operating system and identity within a single computer system. Each logical domain can be created, destroyed, reconfigured, and rebooted independently, without requiring you to perform a power cycle of the server. You can run a variety of application software in different logical domains and keep them independent for performance and security purposes.
For information about using the Oracle VM Server for SPARC software, see Oracle VM Server for SPARC 3.1 Administration Guide and Oracle VM Server for SPARC 3.1 Reference Manual . For information about the required hardware and software, see Oracle VM Server for SPARC 3.1 Release Notes .
Figure 1 - Hypervisor Supporting Two Logical Domains
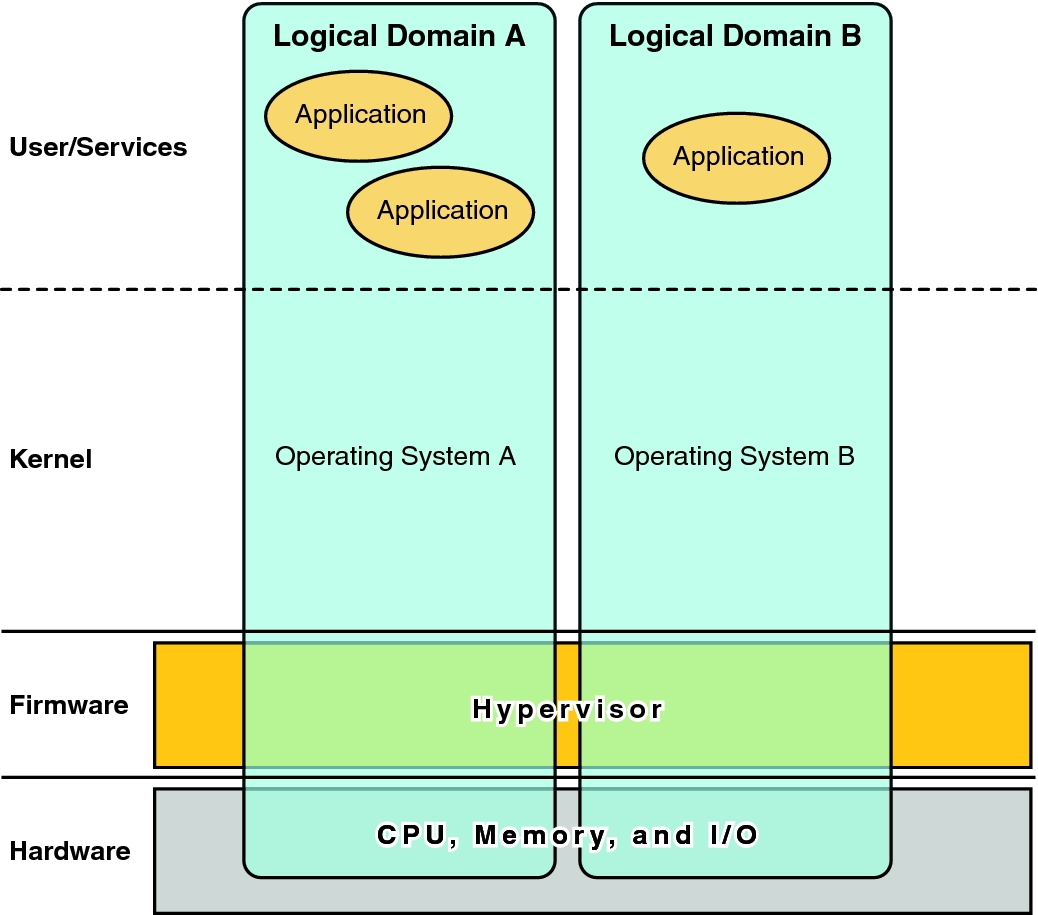
The Oracle VM Server for SPARC software uses the following components to provide system virtualization:
Hypervisor. The hypervisor is a small firmware layer that provides a stable virtualized machine architecture to which an operating system can be installed. Oracle's Sun servers that use the hypervisor provide hardware features to support the hypervisor's control over the operating system activities on a logical domain.
The number of domains and the capabilities of each domain that a specific SPARC hypervisor supports are server-dependent features. The hypervisor can allocate subsets of the server's CPU, memory, and I/O resources to a given logical domain. This allocation enables the support of multiple operating systems simultaneously, each within its own logical domain. Resources can be rearranged between separate logical domains with an arbitrary granularity. For example, CPUs are assignable to a logical domain with the granularity of a CPU thread.
The service processor (SP), also known as the system controller (SC), monitors and runs the physical machine. The Logical Domains Manager, and not the SP, manages the logical domains themselves.
Control domain. The Logical Domains Manager runs in this domain and enables you to create and manage other logical domains and to allocate virtual resources to other domains. You can have only one control domain per server. The control domain is the first domain that is created when you install the Oracle VM Server for SPARC software. The control domain is named primary.
Service domain. A service domain provides virtual device services to other domains such as a virtual switch, a virtual console concentrator, and a virtual disk server. Any domain can be configured as a service domain.
I/O domain. An I/O domain has direct access to physical I/O devices such as a network card in a PCI EXPRESS (PCIe) controller. An I/O domain can own a PCIe root complex or it can own a PCIe slot or on-board PCIe device by using the direct I/O (DIO) feature. See Creating an I/O Domain by Assigning PCIe Endpoint Devices in Oracle VM Server for SPARC 3.1 Administration Guide .
An I/O domain can share physical I/O devices with other domains in the form of virtual devices when the I/O domain is also used as a service domain.
Root domain. A root domain has a PCIe root complex assigned to it. This domain owns the PCIe fabric of that root complex and provides all fabric-related services such as fabric error handling. A root domain is also an I/O domain, as it owns and has direct access to physical I/O devices.
The number of root domains that you can have depends on your platform architecture. For example, if you are using a SPARC T4-4 server from Oracle, you can have up to four root domains.
Guest domain. A guest domain is a non-I/O domain that consumes virtual device services that are provided by one or more service domains. A guest domain does not have any physical I/O devices. It has only virtual I/O devices such as virtual disks and virtual network interfaces.
Often, an Oracle VM Server for SPARC system has only a control domain that provides the services that are performed by I/O domains and service domains. To improve redundancy and platform serviceability, consider configuring more than one I/O domain on your Oracle VM Server for SPARC system.