5 Performing Oracle Identity and Access Management Deployment
After creating the deployment response file, use it to deploy the Oracle Identity and Access Management environment. This chapter describes how to deploy Oracle Identity and Access Management.
This chapter contains the following sections:
-
Section 5.1, "Understanding the Stages of an Oracle Identity Manager Automated Deployment"
-
Section 5.2, "About the Services and Servers Configured in Each Deployment Phase"
-
Section 5.4, "Running the Environment Health Check Utility Before Deployment"
-
Section 5.5, "Deploying Oracle Identity and Access Management Using the LCM Tools"
-
Section 5.6, "Reviewing Environment Health Check Utility Reports and Logs After Deployment"
5.1 Understanding the Stages of an Oracle Identity Manager Automated Deployment
When you use the LCM tools to deploy an Oracle Identity and Access Management environment, you run the deployment in stages. At the end of each stage, you can verify that the stage has completed successfully before advancing to the next stage.
To better prepare for and understand the automatic deployment process, Table 5-1 lists the deployment stages for an integrated Oracle Identity Manager, Oracle Access Manager, and Oracle Mobile Security Services deployment.
To give you an idea how long each stage can take to finish, the table also provides a time estimate for each stage when you are installing and deploying the integrated environment.
Note:
The specific time required for each stage will vary, depending upon the topology you have selected, whether you are using an existing LDAP directory or creating new one, and other factors, such as available system resources.Table 5-1 Summary of the Phases for an Integrated OIM-OAM-OMSS Deployment
| Phase Number | Phase Name | Description | Estimated Duration |
|---|---|---|---|
|
1 |
Preverify |
Verifies that the minimum prerequisites are met. For this phase, the LCM Tools use the Oracle Identity and Access Management Health Check Utility to check for various system requirements, including:
For more information about the items verified by the Health Check Utility, see Verifying Your Oracle Identity and Access Management Environment. If any mandatory plugins (plugins that check for mandatory parameters in the environment for the provisioning to be successfully completed) fail, it will stop you from going forward with the provisioning. If any optional plugins (plugins that check for recommended but not mandatory parameters in the environment) fail, it will warn you but you can still go forward with the provisioning by ignoring the warning. For more information, see "Analyzing Health Check Reports" in Oracle Fusion Middleware Verifying Your Oracle Identity and Access Management Environment. |
1 minute |
|
2 |
Install |
Invokes the required installers in the software repository, creates the required Middleware home directories, installs the software binary files on disk, and applies any required patches to the binary files. |
75 minutes |
|
3 |
Preconfigure |
Performs the following tasks in preparation for configuring the software:
|
75 Minutes |
|
4 |
Configure |
Configures the software by performing the following steps:
|
40 Minutes |
|
5 |
Configure - secondary |
Performs some required secondary configuration tasks:
|
20 Minutes |
|
6 |
PostConfigure |
Performs the following post-configuration tasks:
|
40 Minutes |
|
7 |
Startup |
Starts all the servers and services. |
45 Minutes |
|
8 |
Validate |
Validates the deployment using the Oracle Identity and Access Management Health Check Utility. The status of post install Health Check utility plugins are available at the following location:
|
2 Minutes |
5.2 About the Services and Servers Configured in Each Deployment Phase
If a deployment fails during one of the phases, you can use the Cleanup and Restore to roll back the deployment to the end of the Install phase. Alternatively, you can also stop the deployment at the end of each phase and back up the environment. That way, if the next phase should fail, you can easily restore your environment to its state at the end of the last successful deployment phase.
However, before you can back up your environment, you must first stop any servers or processes that are running and then restart them when the backup is complete.
Table 5-2 provides a list of servers and processes that you need to stop before you back up each phase of the deployment and then start again when the backup is complete.
The names of the Managed Servers in Table 5-2 can vary, depending on the names you selected for each server. However, for the purposes of this guide, the Managed Servers use the names shown in the topology diagrams in Section 1.3, "Oracle Identity and Access Management Topologies Supported by the LCM Tools".
Table 5-2 List of Servers to Stop Before Backing Up after Each Provisioning Phase
| Phase | OIM Deployment | OAM and OMSS with OUDFoot 1 Deployment | Integrated, OIM, OAM, OMSS, and OUD Deployment | |
|---|---|---|---|---|
|
1 |
Preverify |
None |
None |
None |
|
2 |
Install |
None |
None |
None |
|
3 |
Preconfigure |
Node Manager Administration Server Oracle HTTP Server |
Oracle Unified Directory (OUD)Node ManagerAdministration ServerOracle HTTP Server |
OUDNode ManagerAccess Administration Server Governance Administration Server Oracle HTTP Server |
|
4 |
Configure |
Node Manager Administration Server Oracle HTTP Server wls_oim1 |
OUD Node Manager Administration Server Oracle HTTP Server wls_oam1 wls_msm1 |
OUD Node Manager Access Administration Server wls_oam1 wls_msm1 Governance Administration Server wls_oim1 Oracle HTTP Server |
|
5 |
Configure - Secondary |
.Node Manager Administration Server Oracle HTTP Server wls_oim1 |
OUD Node Manager Administration Server Oracle HTTP Server wls_oam1 wls_msm1 |
OUD Node Manager Access Administration Server wls_oam1 wls_msm1 Governance Administration Server wls_oim1 Oracle HTTP Server |
|
6 |
Postconfigure |
Node Manager Administration Server Oracle HTTP Server wls_oim1 wls_soa1 |
OUD Node Manager Administration Server Oracle HTTP Server wls_oam1 wls_msm1 |
OUD Node Manager Access Administration Server wls_oam1 wls_msm1 Governance Administration Server wls_oim1 wls_soa1 Oracle HTTP Server |
|
7 |
Startup |
Node Manager Administration Server Oracle HTTP Server wls_oim1 wls_soa1 wls_bi1 |
OUD Node Manager Administration Server Oracle HTTP Server wls_oam1 wls_msm1 wls_ama1 MSAS |
OUD Node Manager Access Administration Server wls_oam1 wls_msm1 wls_ama1 Governance Administration Server wls_oim1 wls_soa1 wls_bi1 MSAS Oracle HTTP Server |
|
8 |
validate |
Node Manager Administration Server Oracle HTTP Server wls_oim1 wls_soa1 wls_bi1 |
OUD Node Manager Administration Server Oracle HTTP Server wls_oam1 wls_msm1 wls_ama1 MSAS |
OUD Node Manager Access Administration Server wls_oam1 wls_msm1 wls_ama1 Governance Administration Server wls_oim1 wls_soa1 wls_bi1 MSAS Oracle HTTP Server |
Footnote 1 This table assumes you are deploying an Oracle Unified Directory (OUD) instance; if you are deploying an Oracle Internet Directory (OID) instance, then replace any references to OUD with OID.
5.3 Manual Deployment Tasks When Using Microsoft Active Directory for an Integrated Topology
If you are using an existing Microsoft Active Directory instance as part of your Oracle Identity and Access Management deployment, then there are two important steps you must perform during and after the Oracle Identity and Access Management deployment.
These steps apply only if are using Active Directory and you are deploying the integrated OIM, OAM, and OMSS topology:
-
Section 5.3.1, "Extending the OIM Schema for Active Directory After the Install Phase"
-
Section 5.3.2, "Disabling the LDAPAddMissingObjectClasses Event Handler After the Configure Phase"
5.3.1 Extending the OIM Schema for Active Directory After the Install Phase
If you are using Active Directory as part of an integrated OIM, OAM, and OMSS deployment, then you must perform the following procedure after the Install phase completes successfully and before the Preconfigure phase:
-
Change directory to the following directory in the Middleware home, which was created during the Install phase:
cd MW_HOME/oracle_common/modules/oracle.ovd_11.1.1/oimtemplates/This directory contains the
extendsadschemascript, which automatically loads the following LDIF files, which are also installed into theoimtemplatesdirectory:-
adOAMDisable.ldif -
adOAMEnable.ldif -
adOIMLanguageSubtype.ldif -
adOIMSchema.ldif
-
-
Run the following command to extend Active Directory schema:
./extendadschema.sh -h AD_host -p AD_port -D administrator@example.com -AD dc=example,dc=com> -OAM true
Note:
Theextendadschema script is certified only for Active Directory 2003, 2008, 2008R2, and 2012.5.3.2 Disabling the LDAPAddMissingObjectClasses Event Handler After the Configure Phase
If you are using Active Directory as part of an integrated OIM, OAM, and OMSS deployment, then you should disable the LDAPAddMissingObjectClasses Oracle Identity Manager event handler after the Configure or Configure - Secondary phase and before the Post-Configure phase.
For more information, see "Disabling the LDAPAddMissingObjectClasses for Users and Roles" in the Integration Guide for Oracle Identity Management Suite.
Be sure to restart the OIM Managed Server after you complete this task.
5.4 Running the Environment Health Check Utility Before Deployment
Before you deploy Oracle Identity and Access Management using the Deployment Wizard, Oracle recommends that you run the Environment Health Check Utility to verify that your environment meets the minimum requirements for running the deployment wizard and deploying the software.
To perform the system verification before deploying Oracle Identity and Access Management:
-
Set the
JAVA_HOMEenvironment variable to the full path of your JDK directory. -
Change directory to the following directory where you downloaded and unpacked the Environment Health Check Utility:
cd IDMLCM_HOME/healthcheck/bin -
Run the following command to perform the pre-installation validation checks:
./idmhc.sh -manifest ../config/PreInstallChecks_mandatory_manual.xml
Note:
For more information about the pre-installation checks performed by the Environment Health Check Utility, see "PreInstallChecks_mandatory_manual.xml" in Oracle Fusion Middleware Verifying Your Oracle Identity and Access Management Environment. -
If any health checks fail, refer to the output in the Health Check Utility log files and reports to find the corrective actions. Note that the log file location will be printed on the screen after the utility is executed.
The reports provide the status of each check and a list of corrective actions for any checks that fail validation. You can manually fix the issues and rerun the utility any number of times to ensure all checks are successful. For more information about the log files and reports, see "Analyzing Health Check Reports" in Oracle Fusion Middleware Verifying Your Oracle Identity and Access Management Environment.
5.5 Deploying Oracle Identity and Access Management Using the LCM Tools
After you have created a response file, you can deploy the Oracle Identity and Access Management software using the deployment tool command line or the Oracle Identity and Access Management Deployment Wizard.
Note:
Before you start the deployment, make sure all unnecessary processes are shut down on the host. One way to do this is to reboot the host before performing Oracle Identity and Access Management deployment.This section contains the following topics:
-
Section 5.5.1, "Deploying Oracle Identity and Access Management Using the Deployment Wizard"
-
Section 5.5.2, "Deploying Oracle Identity and Access Management Using the LCM Tools Command Line"
5.5.1 Deploying Oracle Identity and Access Management Using the Deployment Wizard
If you want to use the Oracle Identity and Access Management Deployment Wizard to perform deployment,
-
Ensure that the environment JAVA_HOME variable is set to the directory where you unpacked the
jdk.zipfile from the installers directory in the software repository.For example:
REPOS_HOME/jdk. -
Start the Oracle Identity and Access Management Deployment Wizard, as follows:
cd IDMLCM_HOME/provisioning/bin ./iamDeploymentWizard.sh -
On the Choose IAM Installation Options screen:
-
Select Deploy an Identity and Access Management Environment.
-
In the Response File field, specify the path name of the file you want to use, either by typing it in the field or by clicking the Browse button, navigating to the desired file, and selecting it.
This is the deployment response file that you created in Chapter 4, "Creating a Deployment Response File."
-
-
On the Describe Response File screen, review the information about the response file that you created earlier as part of the Deployment Profile.
For more information, see 5 in Creating a Deployment Response File for an Oracle Identity Manager (OIM) Topology.
-
On the Select Installation and Configuration Locations screen, review the information about the Oracle Identity and Access Management installation and configuration directories that you had provided when creating the Deployment Profile.
For more information, see 9 in Creating a Deployment Response File for an Oracle Identity Manager (OIM) Topology.
-
On the Review Deployment Configuration screen, select the configurations you want to review.
This is an optional step. If you want to view or modify the configuration details of any component, then select that component and click Next. Based on the options that you select, the corresponding configuration screens are displayed.
-
OUD Configuration
-
OHS Configuration
-
SOA Configuration
-
OIM Configuration
-
OAM Configuration
-
OIM DB Configuration
-
OAM DB Configuration
-
-
On the Summary screen, review your selections to ensure that the installation details are what you intend.
Click Next to start the deployment process. The wizard displays a screen for each phase of the deployment process. Each screen corresponds to the phases described in Section 5.1.
-
Monitor the Wizard screens to track the progress of the deployment process.
The status icon at the top of screen shows the status of the stage:
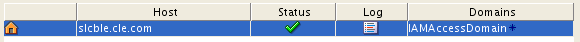
-
The block icon indicates that processing of the current stage has not yet started.
-
The clock icon indicates that the current stage is in progress.
-
The green check mark indicates that the current stage completed successfully.
When a stage finishes successfully, the Wizard pauses until you click Next to advance to the next stage.
-
An "x" icon in a red circle indicates that the current stage has failed. You must correct the errors before you can continue.
Click the x icon to display information about the failures. Click a Log file to see details specific to the stage.
For information about how to recover from a failed stage, see Appendix A, "Cleaning Up an Environment Before Rerunning IAM Deployment".
-
-
At the end of each successful stage, consider backing up the environment.
If you back up your environment after each phase and a stage fails, then you can easily restore your environment to the state it was in after the last successful stage. For more information, see Section 5.2, "About the Services and Servers Configured in Each Deployment Phase".
Note:
If you are using Microsoft Active Directory for an integrated deployment, then there are mandatory steps you must perform on the directory after the Install phase and after the Configure phase.For more information, see Section 5.3, "Manual Deployment Tasks When Using Microsoft Active Directory for an Integrated Topology".
-
If all deployment stages are successful, the Wizard displays the Install Complete screen, which shows a summary of the products that have been installed and configured.
Click Finish to save the summary and exit the Oracle Identity and Access Management Deployment Wizard.
5.5.2 Deploying Oracle Identity and Access Management Using the LCM Tools Command Line
To use the command line deployment tool, you must run the runIAMDeployment.sh script a number of times, specifying the deployment stage with the -target option. You MUST complete each command, in order, before running the next command.
Note:
If you are using Microsoft Active Directory for an integrated deployment, then there are mandatory steps you must perform on the directory after the Install phase and after the Configure phase.For more information, see Section 5.3, "Manual Deployment Tasks When Using Microsoft Active Directory for an Integrated Topology".
Before running the deployment tool, ensure that the environment variable JAVA_HOME is set to the directory where REPOS_HOME/installers/jdk/jdk.zip was extracted. For example, REPOS_HOME/jdk.
The command syntax for the deployment tool on UNIX is:
runIAMDeployment.sh -responseFile RESPONSE_FILE -target STAGE
In this example, note the following:
-
RESPONSE_FILEis the complete path to the location of the deployment response file. You specified the file name and directory on the Summary screen when you ran the wizard to create the deployment response file.On Unix, the default value is:
IDMLCM_HOME/provisioning/bin/provisioning.rsp -
It is important that you perform the deployment commands for each deployment phase in the correct order.
For example, review Example 5-1, which shows each of the commands in the proper order, by deployment phase.
Example 5-1 Example of Running the LCM Tools Command Line Actions for a Complete Deployment
runIAMDeployment.sh -responseFile IDMLCM_HOME/provisioning/bin/provisioning.rsp -target preverify runIAMDeployment.sh -responseFile IDMLCM_HOME/provisioning/bin/provisioning.rsp -target install runIAMDeployment.sh -responseFile IDMLCM_HOME/provisioning/bin/provisioning.rsp -target preconfigure runIAMDeployment.sh -responseFile IDMLCM_HOME/provisioning/bin/provisioning.rsp -target configure runIAMDeployment.sh -responseFile IDMLCM_HOME/provisioning/bin/provisioning.rsp -target configure-secondary runIAMDeployment.sh -responseFile IDMLCM_HOME/provisioning/bin/provisioning.rsp -target postconfigure runIAMDeployment.sh -responseFile IDMLCM_HOME/provisioning/bin/provisioning.rsp -target startup runIAMDeployment.sh -responseFile IDMLCM_HOME/provisioning/bin/provisioning.rsp -target validate
5.6 Reviewing Environment Health Check Utility Reports and Logs After Deployment
After you finish automatic deployment Oracle Identity and Access Management using the LCM Tools, review the log files and reports that were generated by the Oracle Identity and Access Environment Health Check Utility.
The log files and HTML reports are saved to the following location during a deployment with the LCM Tools:
IDMLCM_HOME/healthcheck/bin/logs/healthchecker/
The reports provide the status of each check and a list of corrective actions for any checks that fail validation. You can manually fix the issues and rerun the utility any number of times to ensure all checks are successful.
For more information about the log files and reports, see "Analyzing Health Check Reports" in Oracle Fusion Middleware Verifying Your Oracle Identity and Access Management Environment.
Note for HP-UX Users:
The following error in the logs or HTML reports can be safely ignored:ERROR: OIMHC-20024: SOAConfigCheck plugin failed. OIMHC-20137: Error occurred while trying to authenticate the user "weblogic_idm". Ensure that the configuration is correct.
To validate the deployment, use the standard validation URLs provided in Chapter 7