Download Database Connection Information
If you are not an Autonomous Database administrator and your application requires a wallet to connect, then your administrator should provide you with the client credentials. You can also view TNS names and connection strings for your database.
- Download Client Credentials (Wallets)
To download client credentials you can use the Oracle Cloud Infrastructure Console or Database Actions. - Wallet README File
The walletREADMEfile contains the wallet expiration information and details for Autonomous Database tools and resources. - View TNS Names and Connection Strings for an Autonomous Database Instance
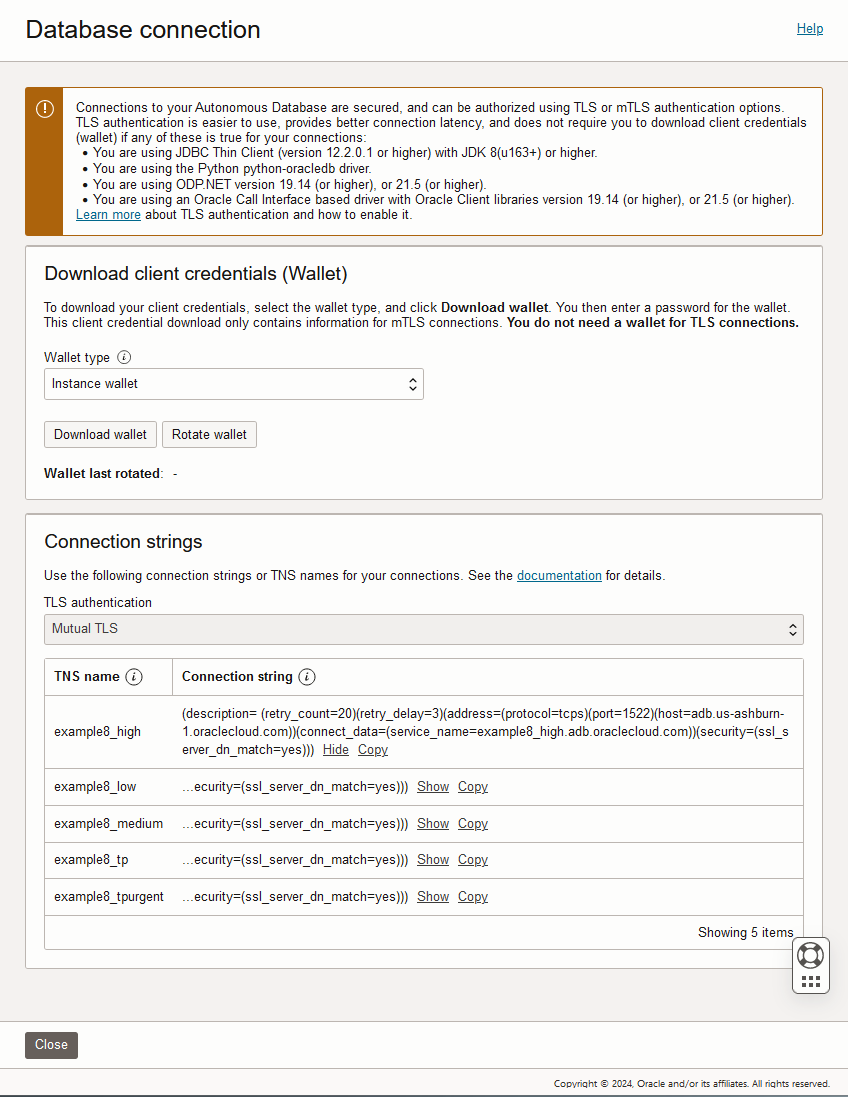
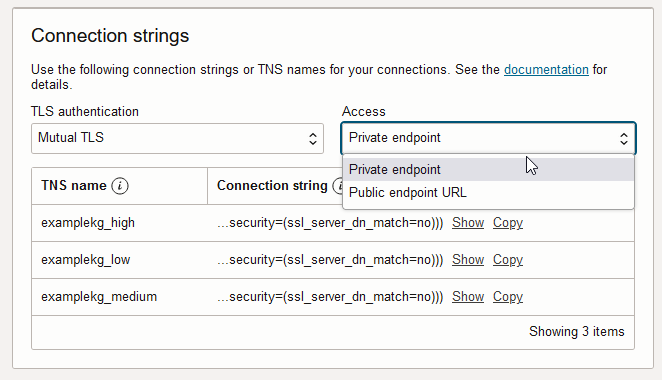
From the Database Connection page on the Oracle Cloud Infrastructure Console you can view Autonomous Database TNS names and connection strings.
Parent topic: Connect to Autonomous Database
Download Client Credentials (Wallets)
To download client credentials you can use the Oracle Cloud Infrastructure Console or Database Actions.
Note:
The password you provide when you download the wallet protects the downloaded Client Credentials wallet.For commercial regions, the wallet password complexity for the password you supply requires the following:
- Minimum of 8 characters
- Minimum of 1 letter
- Minimum of 1 numeric character or 1 special character
- Minimum of 15 characters
- Minimum of 1 lowercase letter
- Minimum of 1 uppercase letter
- Minimum of 1 numeric character
- Minimum 1 special character
To download client credentials from the Oracle Cloud Infrastructure Console:
To download client credentials from Database Actions:
First, access Database Actions as the ADMIN user. See Access Database Actions as ADMIN for more information.
-
Access Database Actions as the ADMIN user. See Access Database Actions as ADMIN for more information.
-
On the Database Actions Launchpad, under Administration, select Download Client Credentials (Wallet).
-
On the Download Client Credentials (Wallet) page, enter a wallet password in the Password field and confirm the password in the Confirm Password field.
-
Click Download to save the client security credentials zip file. By default the filename is:
Wallet_databasename.zip. You can save this file as any filename you want. You must protect this file to prevent unauthorized database access.
Note:
When you use Database Actions to download a wallet there is no Wallet type option on the Download Client Credentials (Wallet) page and you always download an instance wallet. If you need to download the regional wallet click Database connection on the Oracle Cloud Infrastructure Console.The zip file includes the following:
| File | Description |
|---|---|
cwallet.sso |
Auto-open SSO wallet |
ewallet.p12 |
PKCS12 file. The PKCS12 file is protected by the wallet password provided while downloading the wallet. |
ewallet.pem |
Encoded certificate file used to authenticate with certificate authority (CA) server certificate. |
keystore.jks |
Java keystore file. This file is protected by the wallet password provided while downloading the wallet. |
ojdbc.properties |
Contains the wallet related connection property required for JDBC
connection. This should be in the same path as
|
README |
Contains wallet expiration information and links for Autonomous Database tools and resources. See Wallet README
File for information on the contents of the
|
sqlnet.ora |
SQL*Net client side configuration. |
tnsnames.ora |
Network configuration file storing connect descriptors. |
truststore.jks |
Java truststore file. This file is protected by the wallet password provided while downloading the wallet. |
Notes for wallet files and the wallet password:
-
To invalidate database client certification keys associated with a wallet, see Rotate Wallets with Immediate Rotation.
-
Wallet files, along with the Database user ID and password provide access to data in your database. Store wallet files in a secure location. Share wallet files only with authorized users. If wallet files are transmitted in a way that might be accessed by unauthorized users (for example, over public email), transmit the wallet password separately and securely.
-
For better security, Oracle recommends using restricted permissions on wallet files. This means setting the file permissions to 600 on Linux/Unix. Similar restrictions can be achieved on Windows by letting the file owner have Read and Write permissions while all other users have no permissions.
-
Autonomous Database uses strong password complexity rules for all users based on Oracle Cloud security standards. For more information on the password complexity rules see Create Users on Autonomous Database - Connecting with a Client Tool.
-
The
READMEfile that contains wallet expiration information is not available in wallet zip files that were downloaded before April 2020. -
Starting six weeks before the wallet expiration date Autonomous Database sends notification emails each week, indicating the wallet expiration date. These emails provide notice before your wallet expires that you need to download a new wallet. You will receive these notification emails only if there is a connection that uses a wallet that is about to expire.
You can also use the
WalletExpirationWarningevent to be notified when a wallet is due to expire. You will receive these notification events only if you are subscribed to Critical events and there is a connection that uses a wallet that is about to expire. See About Events Based Notification and Automation on Autonomous Database for more information.
Parent topic: Download Database Connection Information
Wallet README File
The wallet
README file contains the wallet expiration information
and details for Autonomous Database tools
and resources.
The wallet expiration information at the top of the
README file shows the following
information:
-
The date when the wallet was downloaded.
-
The date when the wallet SSL certificate provided in the wallet expires. If your wallet is nearing expiration or is expired, then download a new wallet or obtain a new wallet from your Autonomous Database administrator. If you do not download a new wallet before the expiration date, you will no longer be able to connect to your database.
The Autonomous Database tools and resources area provides the following information:
| Tool or Resource | Description |
|---|---|
|
Database Actions |
Load, explore, transform, model, and catalog your data. Use an SQL worksheet, build REST interfaces and low-code apps, manage users and connections, build and apply machine learning models. Access Link: provides the link to use Database Actions. See Connect with Built-In Oracle Database Actions for more information. |
|
Graph Studio |
Oracle Graph Studio lets you create scalable property graph databases. Graph Studio automates the creation of graph models and in-memory graphs from database tables. It includes notebooks and developer APIs that allow you to execute graph queries using PGQL (an SQL-like graph query language) and over 50 built-in graph algorithms. Graph Studio also offers dozens of visualization, including native graph visualization. Access Link provides the link to use Graph Studio. See About Oracle Graph Studio on Autonomous Database for more information. |
|
Oracle APEX |
Oracle APEX is a low-code development platform that enables you to build scalable, secure enterprise apps that can be deployed anywhere. Access Link: provides the link to use Oracle APEX. See Access Oracle APEX Administration Services for more information. |
|
Oracle Machine Learning User Management |
Create new Oracle Machine Learning user accounts and manage the credentials for existing Oracle Machine Learning users. Access Link: provides the link to use Oracle Machine Learning User Management. See Create and Update User Accounts for Oracle Machine Learning Components on Autonomous Database for more information. |
|
Oracle Machine Learning User Notebooks |
Oracle Machine Learning notebooks provide easy access to Oracle's parallelized, scalable in-database implementations of a library of Oracle Advanced Analytics' machine learning algorithms (classification, regression, anomaly detection, clustering, associations, attribute importance, feature extraction, times series, and so on), SQL, PL/SQL and Oracle's statistical and analytical SQL functions. Access Link: provides the link to use Oracle Machine Learning User Notebooks. See Work with Oracle Machine Learning User Interface for Data Access, Analysis, and Discovery for more information. |
|
SODA Drivers |
Simple Oracle Document Access (SODA) is a set of APIs that let you work with JSON documents managed by the Oracle Database without needing to use SQL. SODA drivers are available for REST, Java, Node.js, Python, PL/SQL, and C. Access Link: provides the link to download the SODA drivers. See Work with Simple Oracle Document Access (SODA) in Autonomous Database for more information. |
Notes for wallet README file:
-
If you rename your Autonomous Database instance, the tools links change and the old links no longer work. To obtain valid tools links you must download a new Wallet zip file with an updated
READMEfile. The SODA drivers link is a resource link and this link does not change when you rename an instance. -
The
READMEin a regional wallet does not contain the Autonomous Database tools and resources links. -
If your Autonomous Database instance is on a private endpoint and you enable the Allow public access option, the
READMEfile includes two links for each tool: one link to use from the private endpoint when you are connecting from the same VCN where the database resides, and another link to use from specific public IP addresses or from specific VCNs if those VCNs are configured to privately connect to Autonomous Database using a Service Gateway. See Use a Private Endpoint with Public Access Allowed for more information.
Parent topic: Download Database Connection Information
View TNS Names and Connection Strings for an Autonomous Database Instance
From the Database Connection page on the Oracle Cloud Infrastructure Console you can view Autonomous Database TNS names and connection strings.
Note:
See Update your Autonomous Database Instance to Allow both TLS and mTLS Authentication for information on allowing TLS connections.Perform the following steps as necessary:
-
Open the Oracle Cloud Infrastructure Console by clicking the
 next to Oracle Cloud.
next to Oracle Cloud.
- From the Oracle Cloud Infrastructure left navigation menu click Oracle Database and then, depending on your workload click one of: Autonomous Data Warehouse, Autonomous JSON Database, or Autonomous Transaction Processing.
-
On the Autonomous Databases page select your Autonomous Database from the links under the Display name column.
To view the TNS names and connection strings, do the following:
Parent topic: Download Database Connection Information