Use Direct Data Ingestion for Your Sensor Attributes
Your digital twin entities are now directly addressable over the network, using standard protocols, authentication mechanisms, and payload formats. Ingest IoT data from directly connected devices, gateways, and network servers directly into your asset and machine sensor attributes.
Choose direct ingestion to eliminate the need for registering devices and device models, and for creating IoT messages.
Use standard HTTP or MQTT protocol to send sensor data in JSON or CSV format. The application supports mutual authentication using certificates in addition to basic authentication.
The application lets you download ready-to-use schema samples for your entities. If you have custom payloads, use the interpreter editor interface to create the mappings and routing.
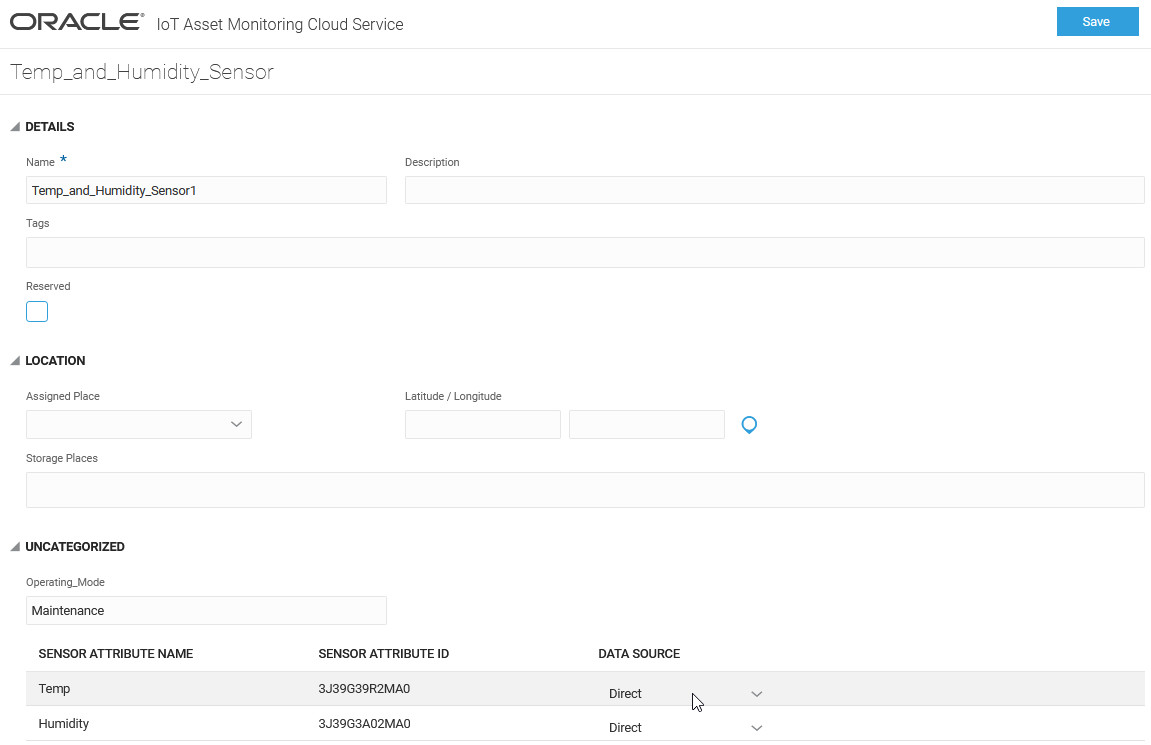
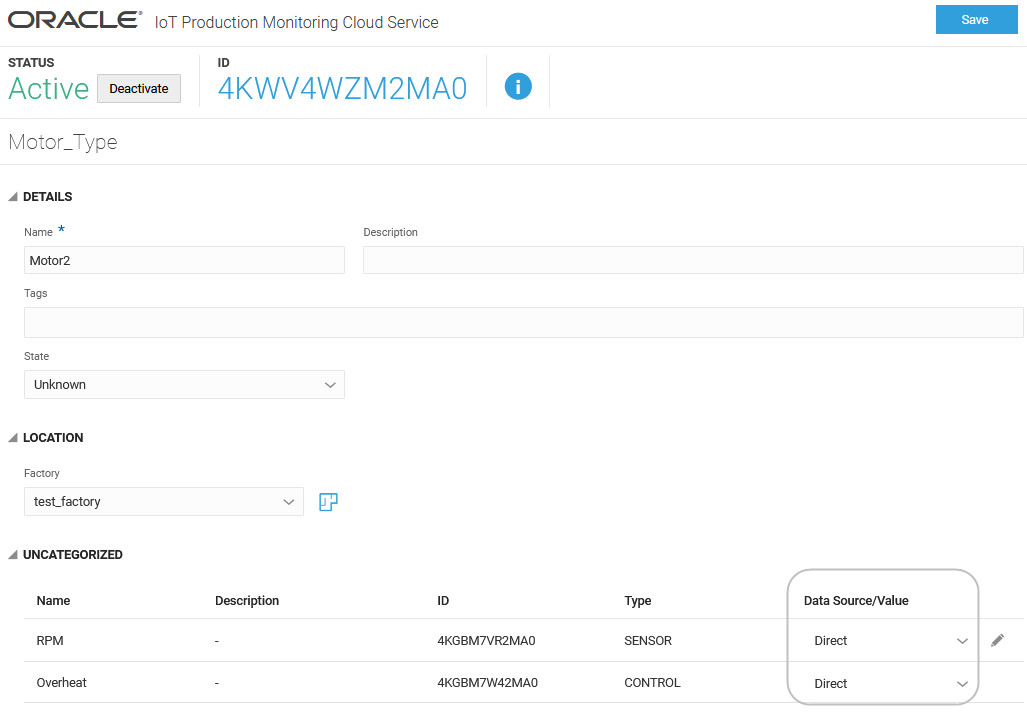
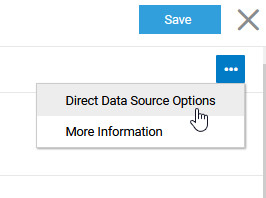
Set Direct Data Options for Your Entity
Use the Create Asset/Machine or Edit Asset/Machine page to set direct data options for the sensor attributes of an entity.
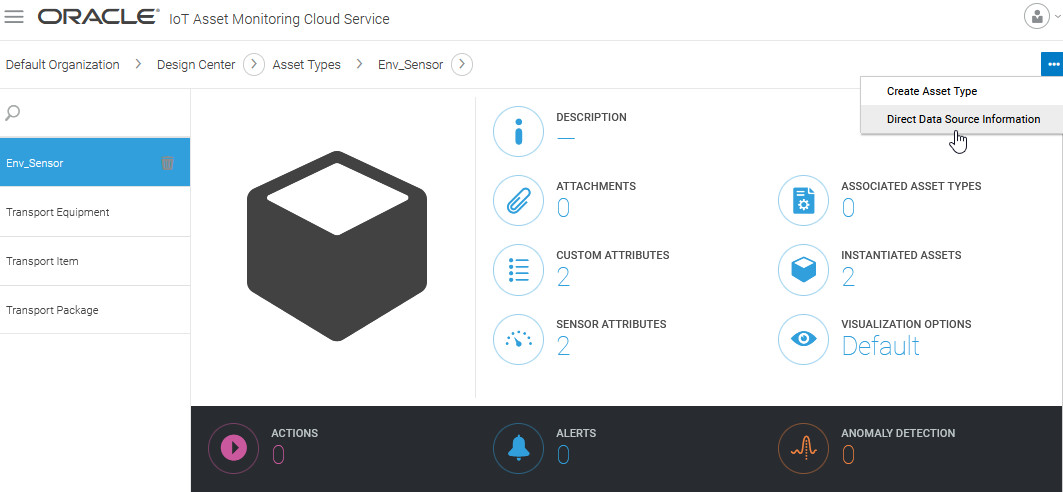
Download Schema for an Entity Type
Download the JSON or CSV schema for an entity type from the Asset Types page.
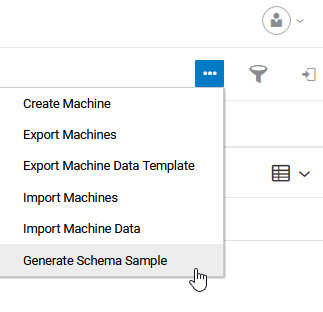
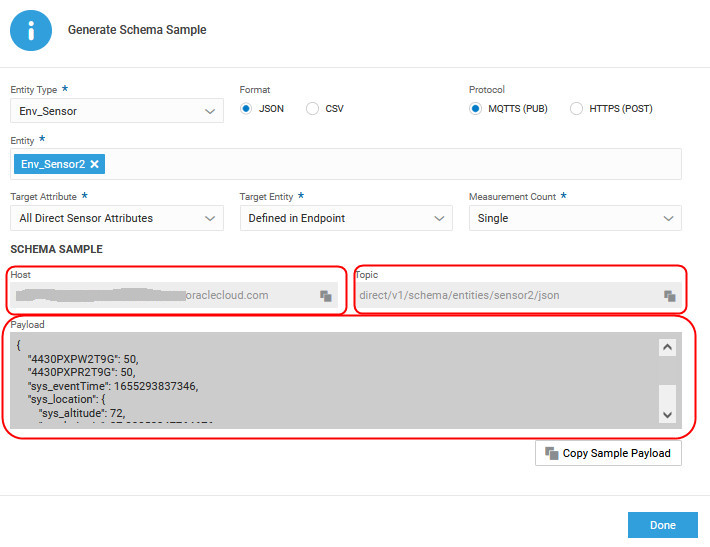
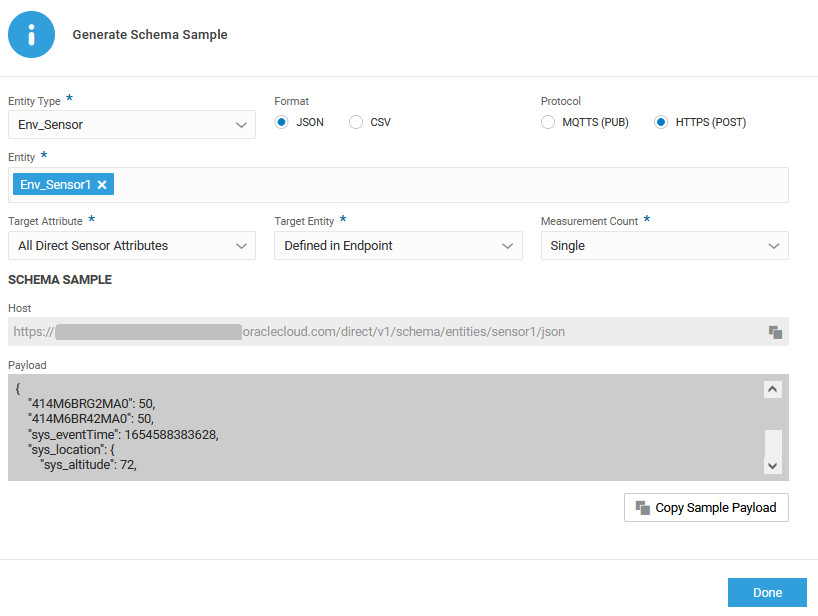
Generate Schema Sample for an Entity
Generate the sample schema for an entity to find connection details, such as host, endpoint, topic, and sample payload. You can edit the sample payload values to ingest data.
As shown in the following example for MQTTS, it is convenient to copy details, such as the host, topic, and sample payload from the Generate Schema Sample dialog.
The following example uses the HTTPS protocol:
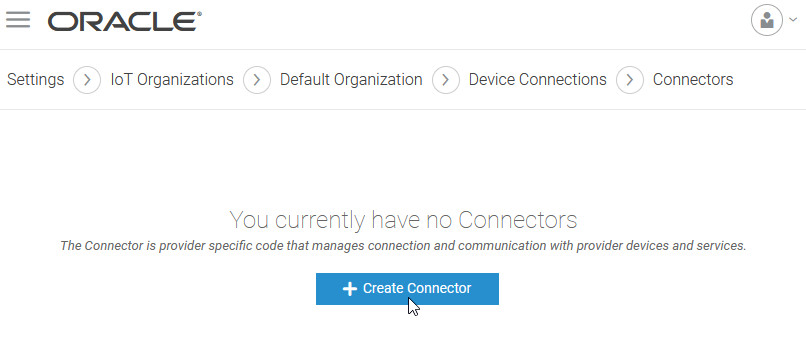
Create a Connector
Use a connector to directly ingest data from devices, which are not directly connected.
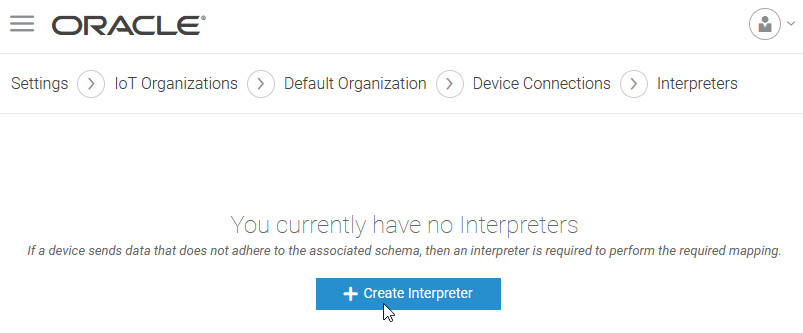
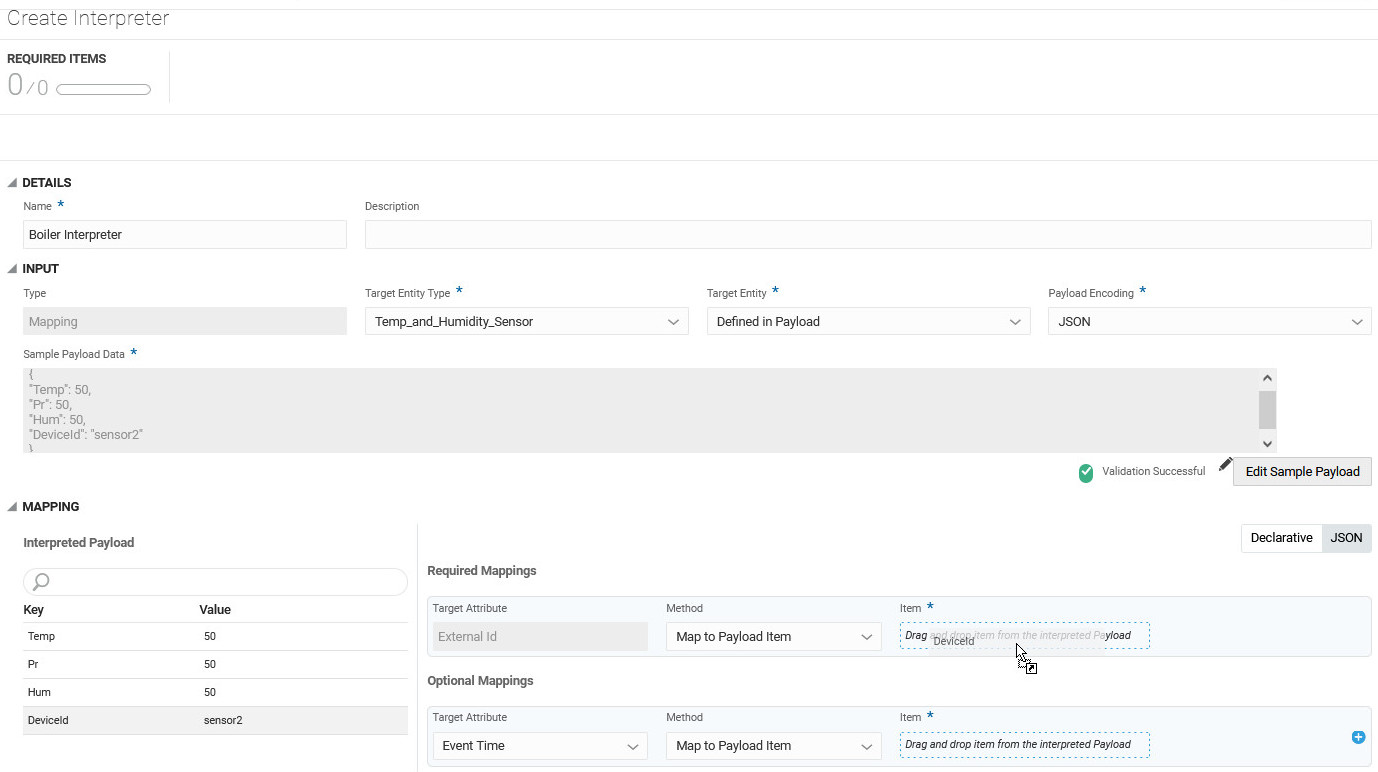
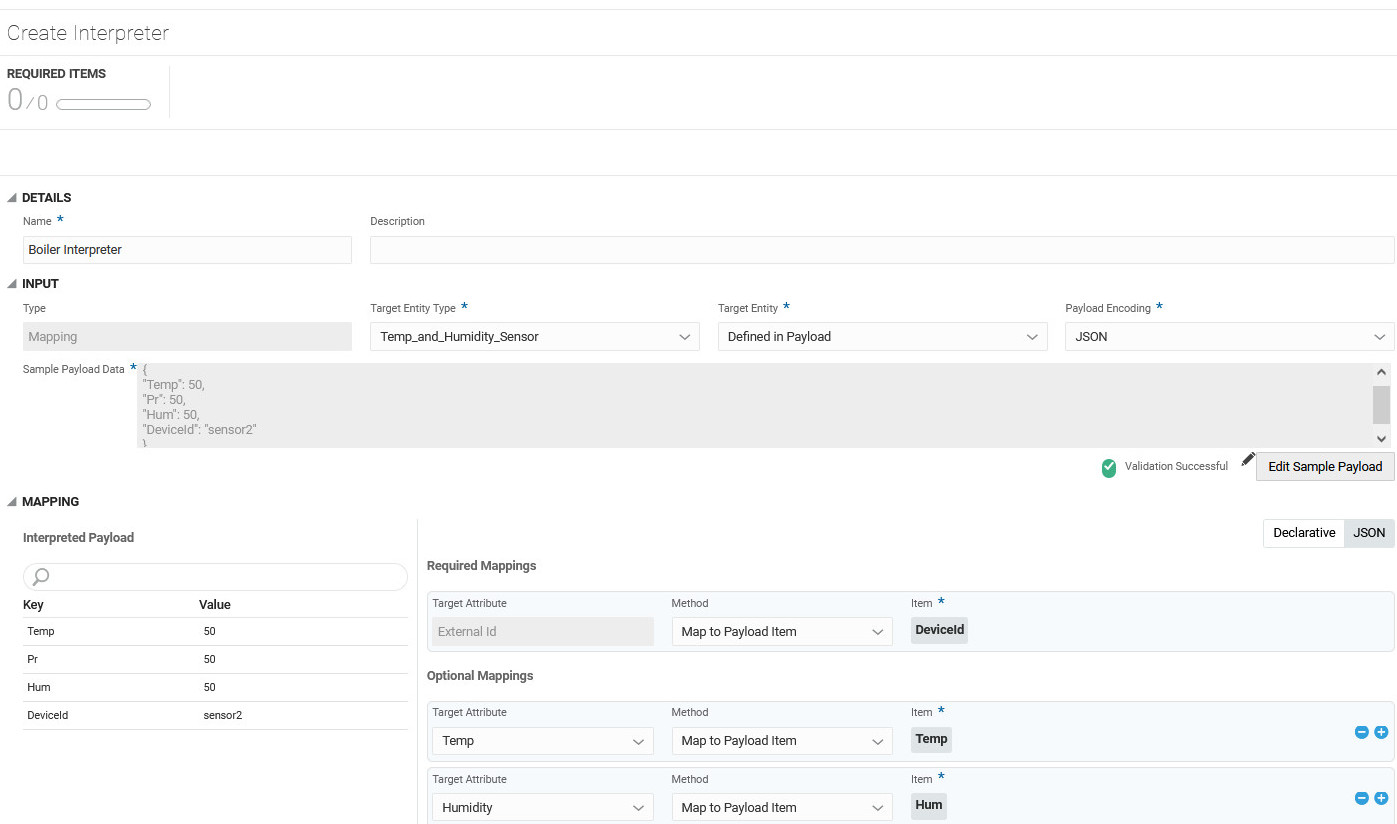
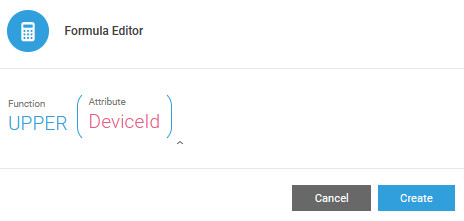
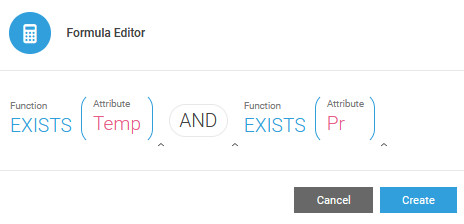
Create an Interpreter
If you are using a custom payload where the payload does not follow the schema, you can create an interpreter to map the payload for the connector.
Upload and Manage Certificates
As an integrator, you can upload your root certificate, and certificate hierarchy, to your IoT instance. The application can then authenticate your clients devices, gateways, and network servers using the certificate hierarchy. You can also manage your certificates, such as renew or revoke certificates in the application.
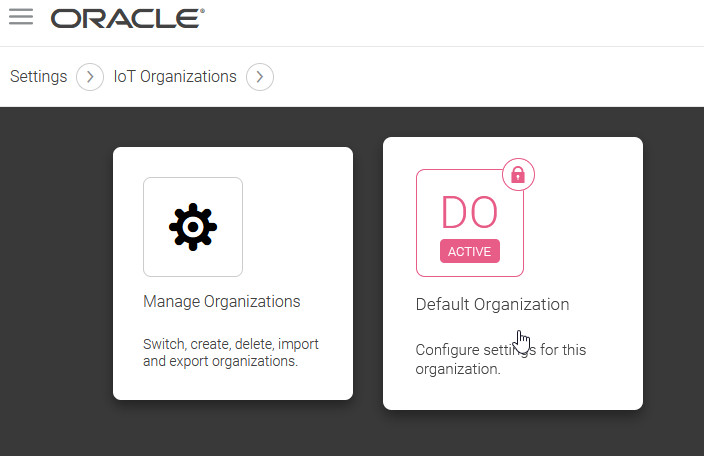
- Click Menu (
 ), and then click Settings.
), and then click Settings.
- Click Security on the Settings page.
- Click Certificates.
- Click Upload Certificate to upload a trusted certificate.
- Specify a Name, optional Description, and select the
PEMfile to upload. - Click Upload.
Oracle recommends that you use a CA certificate. Self-signed certificates are not recommended for production environments.
Note:
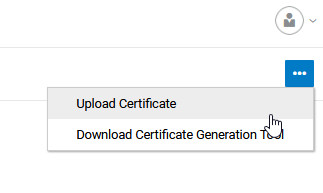
You can use the certificate generation tool to generate self-signed certificates. Select Download Certificate Generation Tool from the Certificates menu to use the same. Use./gencert.sh helpfor usage information on the tool.
The certificate must be verified before coming into effect. You can choose Verify Root Certificate from the Certificates menu to verify the certificate. A verification code is generated, and you need to upload the signed certificate.
You can delegate provisioning to trusted parties by creating intermediate certificates. Create leaf certificates for your devices where the common name is the Entity Id.