In the age of data breaches and ever-evolving data protection and privacy regulations, it is more important than ever for organizations to be confident that their databases are secure. However, it can be difficult to know whether the databases are configured correctly, who has access to it, and where sensitive data is stored. The Oracle Database Security Assessment Tool (DBSAT) helps identify areas where your database configuration, operation, or implementation introduces risks. DBSAT will recommend changes and controls to help mitigate those risks.
Why the Need for a Security Assessment?
Misconfigured databases are a major contributor to database breaches. Human errors could leave your database open to everyone, or an attacker could maliciously exploit configuration mistakes to gain unauthorized access to sensitive data. This can have a devastating impact on your reputation and bottom line. Knowing where your database configuration introduces risk is the first step in minimizing that risk.
About the Oracle Database Security Assessment Tool
The Oracle Database Security Assessment Tool (DBSAT) analyzes the database configuration, users, their entitlements, security policies and identifies where sensitive data resides to uncover security risks and improve the security posture of Oracle Databases within your organization.
Benefits of Using Oracle Database Security Assessment Tool
Using DBSAT, you can:
-
Quickly and easily assess the current security status and identify sensitive data within the Oracle Database.
-
Reduce risk exposure using proven Oracle Database security best practices, CIS Benchmark recommendations and Security Technical Implementation Guides (STIG) rules.
-
Leverage security findings to accelerate compliance with EU GDPR and other regulations.
-
Improve the security posture of your Oracle Databases and promote security best practices.
Note:
DBSAT is a lightweight utility that will not impair system performance in a measurable way.
You can use DBSAT report findings to:
-
Minimize immediate short term risks
-
Implement a comprehensive security strategy
-
Support your regulatory compliance program
-
Promote security best practices
Oracle Database Security Assessment Tool Components
The DBSAT consists of the following components:
-
Collector:
The Collector executes SQL queries and runs operating system commands to collect data from the system to be assessed. It does this primarily by querying database dictionary views. The collected data is written to a JSON file that is used by the DBSAT Reporter in the analysis phase. Note that if the collector is executed remotely it will not collect operating system data. It is recommended to run it in the database server to collect all relevant data.
-
Reporter:
The Reporter analyzes the collected data and generates the Oracle Database Security Assessment Report in HTML, Excel, JSON, and Text formats. The Reporter can run on any machine: PC, laptop, or server. You are not limited to running the Reporter on the database server or the same machine as the Collector.
-
Discoverer:
The Discoverer executes SQL queries and collects metadata from the database to be assessed, based on the settings specified in the configuration files. It does this primarily by querying database dictionary views. The collected data is then used to generate the Oracle Database Sensitive Data Assessment Report in HTML and CSV formats. The Discoverer can run on any machine: PC, laptop, or server. You are not limited to running the Discoverer on the database server or the same machine as the Collector or Reporter.
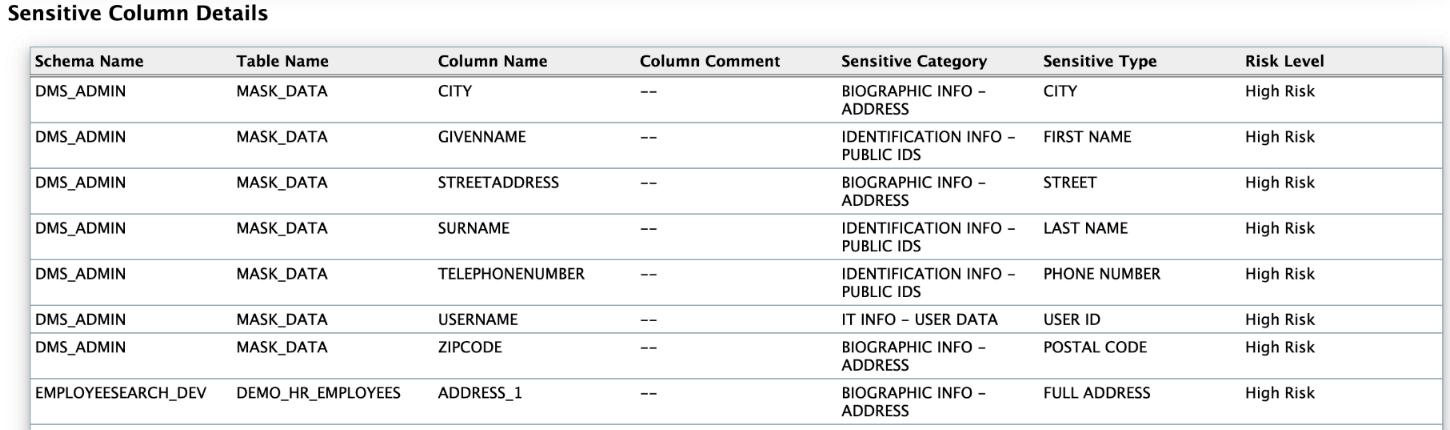
The following figure shows the components, sources, and reports of the Oracle Database Security Assessment Tool.
Figure 1-1 DBSAT Components, Sources, and Reports
Description of "Figure 1-1 DBSAT Components, Sources, and Reports"
For more information about the Collector, Reporter, and Discoverer, see Using the Collector and Reporter.
Prerequisites
The following sections outline the prerequisites for the Oracle Database Security Assessment Tool:
Supported Operating Systems
The database configuration collection queries run on most supported Oracle Database platforms. However, currently, DBSAT will skip OS data for databases running on Windows platforms.
DBSAT runs on:
- Linux x86-64 and Linux 64-bit Arm
- Windows x64
-
Solaris x64 and Solaris SPARC64
-
IBM AIX (64-bit) and Linux on zSeries (64-bit)
-
HP-UX IA (64-bit)
Supported Database Versions
You can run the DBSAT on Oracle Database 11.2.0.4 and later releases on-premises or in the Cloud, on Oracle Database Standard Edition 2 and Oracle Database Enterprise Edition. You can also run DBSAT against Autonomous Databases (Serverless, Dedicated, and Cloud@Customer), Autonomous JSON Database, Oracle Exadata Database Service (Dedicated and Cloud@Customer), and Oracle Base Database Service (BaseDB Enterprise Edition and Standard Edition). Some findings will do different checks and provide targeted remarks for these databases. For more information about the target-specific checks and recommendations, see Appendix A.
Security Requirements
-
Ensure that the directories holding these files are secured with the appropriate permissions.
-
Delete the files securely after you implement the recommendations they contain.
-
Share them with others in their (by default) encrypted form.
-
Grant user permissions to the DBSAT user on a short-term basis and revoke these when no longer necessary.
For more information about DBSAT user privileges, see Collector Prerequisites. For more information about DBSAT best practices, see: Best Practices
Caution:
This tool is intended to assist you in identifying potential sensitive data and vulnerabilities in your system. Further, the output generated by this tool may include potentially sensitive system configuration data and information that could be used by a skilled attacker to penetrate your system. You are solely responsible for ensuring that the output of this tool, including any generated reports, is handled in accordance with your company's policies.
Oracle Database Security Assessment Tool Prerequisites
DBSAT on Unix/Linux systems must execute under the BASH shell. If the server does not have this shell, you can install it or run DBSAT remotely from a different server that has it (or from a laptop running Windows, from where you can connect to the database).
Zip and UnZip
DBSAT uses Zip and Unzip to compress or decompress the generated files. DBSAT searches for Zip and Unzip utilities in the default locations shown below. In order to use other Zip and Unzip utilities, update the following lines in the relevant script.
Windows (dbsat.bat script):
SET ZIP_CMD=%ORACLE_HOME%\bin\zip.exe
SET UNZIP_CMD=%ORACLE_HOME%\bin\unzip.exeNote:
The Unzip utility is not included in Oracle Database 12.2 and higher. Ensure that you have installed a utility such as WinZip or WinRar, and add the path to the utility in theSET UNZIP_CMD
parameter.
All other platforms (dbsat script):
ZIP=/usr/bin/zip
UNZIP=/usr/bin/unzip
DBZIP=${ORACLE_HOME}/bin/zipThe following are the prerequisites for the components of the Oracle Database Security Assessment Tool:
Collector Prerequisites
To gather all necessary data, run the DBSAT Collector on the server that hosts the
database. The collector uses operating system commands to gather
process and file system information that the database alone cannot
provide. Besides, the Oracle DBSAT Collector must be run as an OS
user with read permissions on files and directories under
ORACLE_HOME using SQL*Plus (through Oracle
Database or Instant Client) to collect and process file system data
using OS commands.
The Oracle DBSAT Collector collects most of its data by querying database views. It must connect to the database as a user with sufficient privileges to select from these views. Grant the DBSAT user the following privileges:
-
CREATE SESSION -
READorSELECTonSYS.REGISTRY$HISTORY -
Role
SELECT_CATALOG_ROLE -
Role
DV_SECANALYST(if Database Vault is enabled or if Database Vault Operations Control is enabled) -
Role
AUDIT_VIEWER(12c and later) -
Role
CAPTURE_ADMIN(12c and later) -
READorSELECTonSYS.DBA_USERS_WITH_DEFPWD READonSYS.DBA_AUDIT_MGMT_CONFIG_PARAMSREADonSYS.DBA_CREDENTIALSEXECUTEonSYS.DBMS_SQL
Note:
If you plan to run only the Discoverer component, you can assign only the following privileges:
-
CREATE SESSION -
Role
SELECT_CATALOG_ROLE
In order to successfully collect Database Vault information in a Database Vault protected environment, you must connect as a non-SYS user with the DV_SECANALYST role.
Sample Script to Create a User with Minimum Privileges
You can create a user with required minimum privileges to run the Oracle Database Security Assessment Tool Collector with a script.
Purpose
Create a DBSAT user to run the DBSAT Collector script with required privileges.
Sample Script
create user dbsat_user identified by dbsat_user;
--If Database Vault is enabled, connect as DV_ACCTMGR to run this command
grant create session to dbsat_user;
grant select_catalog_role to dbsat_user;
grant select on sys.registry$history to dbsat_user;
grant read on sys.dba_audit_mgmt_config_params to dbsat_user;
grant select on sys.dba_users_with_defpwd to dbsat_user;
grant read on sys.dba_credentials to dbsat_user;
grant execute on sys.dbms_sql to dbsat_user;
grant audit_viewer to dbsat_user; // 12c and later
grant capture_admin to dbsat_user;// 12c and later covers sys.dba_priv_captures, sys.priv_capture$, sys.capture_run_log$
--If Database Vault is enabled, connect as DV_OWNER to run this command
grant DV_SECANALYST to dbsat_user;Reporter Prerequisites
The Reporter is a Java program and requires the Java Runtime Environment (JRE) 1.8 (jdk8-u172) or later to run.
The JAVA_HOME environment variable must be set and should point to
the installation directory on your system, which contains the bin and lib
directories. For example:
$ export JAVA_HOME=/u01/app/jdk1.8.0_201Discoverer Prerequisites
The Discoverer is a Java program and requires the Java Runtime Environment (JRE) 1.8 (jdk8-u172) or later to run.
JAVA_HOME environment variable must be set and should point to
the installation directory on your system, which contains the bin and lib
directories. For
example:$ export JAVA_HOME=/u01/app/jdk1.8.0_201The Discoverer collects metadata from database dictionary views and matches them against the patterns specified to discover sensitive data. The Discoverer must connect to the database as a user with sufficient privileges to select from these views. For more information about DBSAT user privileges, see Collector Prerequisites.
Note:
The Discoverer relies on table statistics to get row counts. In order to get accurate row count results,DBMS_STATS should be executed by the Database Administrator before the DBSAT user runs the Discoverer.
Installing the Oracle Database Security Assessment Tool
These commands are for Linux / Unix. If the installation takes place on Windows, you will use similar commands for Windows.
The DBSAT is installed on the database server.
You can run the Collector, Reporter, and Discoverer from the /home/oracle/dbsat directory.
You can also add this directory to your PATH and skip the step of going to the directory every time you want to run the tool.
Using the Collector and Reporter
You can generate the Oracle Database Security Assessment Report and the Oracle Database Sensitive Data Assessment Report with the Collector, Reporter, and Discoverer components.
Oracle Database Security Assessment Report
The Collector and Reporter components are used to generate the Oracle Database Security Assessment Report.
The following figure shows the components and architecture of the Collector and Reporter.
Figure 1-2 Collector and Reporter Components and Architecture

Description of "Figure 1-2 Collector and Reporter Components and Architecture "
Running the Collector
The Collector queries the database to collect data that will be analyzed by the Reporter.
Note:
The Collector connects to the database. Ensure that the target database and listener are running before running the Collector.Running the Reporter
The Reporter analyzes the data collected by the Collector and makes recommendations to improve the security of the database.
dbsat report.
Note:
DBSAT recommendations do not adjust for individual applications. In cases where the application requirements differ from DBSAT, you will frequently have to accept the finding as-is, possibly mitigating the finding through some other control. Unless the risk is too high for you to accept, the application requirements should usually supersede the DBSAT recommendation.Oracle Database Security Assessment Report
The Collector and Reporter components are used to generate the Oracle Database Security Assessment (DBSAT) Report in HTML, Excel, JSON, and Text formats. All reports contain similar information but in different formats.
The HTML report provides detailed assessment results in a format that is easy to navigate. The Excel format provides a high-level summary of each finding without the detailed output included in the HTML report. It also allows you to add columns for your tracking and prioritization purposes. A report in text format makes it convenient to copy portions of the output for other usages. Finally, a JSON document containing the report contents is provided for easier filtering, comparison, aggregation, and integration with other tools.
The following Database Security Assessment Report sections will use the HTML report as an example and highlight the findings along with the sections they belong to, the rule ID, and a short description.
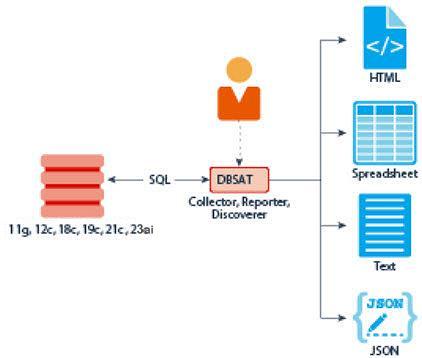
At the top of the report, you will find information about the Collector and Reporter run details, such as the data collection and report generation dates, along with the reporter version. Follows the Database Identity information, where you will find details about the target database. Then, the Summary table presents all the findings per section/domain and their severity level.
Findings
DBSAT reporter resulting analysis is reported in units called Findings, and in each Finding, you see:
- Rule ID: The Rule ID has two parts: the prefix identifies the report section, and the suffix identifies the specific rule.
- One-line summary: One-line summary highlighting the objective and context of each check.
-
Status: The Status helps you prioritize implementing DBSAT
recommendations. It indicates the level of risk associated with the finding,
allowing you to make informed decisions about remediation.
- High Risk
Needs immediate attention.
- Medium Risk
Plan to address these in the short term.
- Low Risk
Might be fixed during scheduled downtime or bundled with other maintenance activities.
- Evaluate
Needs manual analysis.
- Advisory
Poses an opportunity for improvement and raises awareness about other security controls available in the Oracle Database.
-
Pass
No risks were found.
- High Risk
- Summary: Provides a summary of the Finding. When the Finding is informational, the summary typically reports only the number of examined data elements.
- Details: Provides detailed information to explain the finding summary, typically results from the assessed database, followed by any recommendations for changes.
- Remarks: Explain the reason for the rule and recommended actions for remediation.
- References: If the finding is an Oracle Best Practice (OBP) related to an Oracle Database 12c STIG V2R8, CIS Oracle Database Benchmark 12c v2.0.0 recommendation, or related to a GDPR Article/Recitals, it will be mentioned here.
Security Frameworks and Best Practices
DBSAT integrates Oracle Best Practices, Center for Internet Security (CIS) Benchmark, and the US Department of Defense Information Systems Agency (DISA) Security Technical Implementation Guide (STIG) for the Oracle Database to identify potential security risks in Oracle databases.
Initially, DBSAT primarily focused on STIGs and CIS benchmarks, but with version 3.0 and later, it also highlights findings aligned or that are Oracle's own best practices.
Some checks are designated as Oracle Best Practices (OBP) only. This could be due to various factors, such as differences in release cycles or a deeper understanding of Oracle's inner workings. For example, while Oracle releases new features or capabilities, it can take years for standards to include them. For instance, Oracle introduced Gradual Password Rollover in Oracle Database 19c in 2021, but until April 2024, it wasn’t reflected in STIG or CIS.
Multiple security frameworks often cover similar requirements, and DBSAT tags findings accordingly. For instance, if both CIS and STIG recommend avoiding default passwords for database user accounts, DBSAT marks that finding with both frameworks' tags, and as this is an Oracle best practice, it would be as well flagged with the OBP tag.
DBSAT's tagging system lets users focus on findings relevant to their compliance standards. Whether seeking STIG compliance, adherence to CIS benchmark, or alignment with Oracle's best practices, users can easily find and prioritize findings based on their specific requirements.
- STIG V2R8
- Oracle Database 19c CIS Benchmark v1.2.
- Oracle Best Practices
- European Union General Data Protection Regulation (EU GDPR) 2016/679 articles and recitals
Note:
Recommendations reflect best practices for database security and should be part of any strategy for data protection by design and by default.
EU GDPR tagged findings highlight technology that may help you address EU GDPR articles and recitals and other data privacy regulations with similar requirements. Technical controls alone are not sufficient for compliance. Passing all findings does not guarantee compliance.
Sections
- Basic Information
- User Accounts
- Privileges and Role
- Authorization Control
- Fine-Grained Access Control
- Auditing
- Encryption
- Database Configuration
- Network Configuration
- Operating System
Oracle Database Security Assessment Report — Summary
The Oracle Database Security Assessment Report — Summary section contains the following information:
| Section | Description |
|---|---|
|
Assessment Time & Date |
Displays the date on which the data was collected and the date on which the final Database Security Assessment report was generated. The DBSAT Reporter version is also displayed. |
|
Database Identity |
Displays the details of the database assessed by DBSAT. |
|
Summary |
Displays a high level summary of the resulting analysis. |
Figure 1-3 Oracle Database Security Assessment Report — Summary
The Summary section is followed by the Basic Information section.
Oracle Database Security Assessment Report — Basic Information
The Oracle Database Security Assessment Report — Basic Information section contains the following information:
| Section | Finding ID | Description |
|---|---|---|
|
Database Version |
- |
Displays the version of the database assessed by the Collector and Reporter. |
|
Security Features Utilized |
- |
Displays the security features and indicates if they are in use. |
|
Patch Check |
INFO.PATCH |
Displays information about the patches installed. It is vital to keep the database software up-to-date with security fixes as they are released. Oracle issues comprehensive patches in the form of Release Updates on a regular quarterly schedule. Patch Set Updates and Bundle Patches were available for database versions up to 12.1.0.2. |
The following figure displays an example of the Oracle Database Security Assessment Report — Basic Information section.
Figure 1-4 Oracle Database Security Assessment Report —
Basic Information
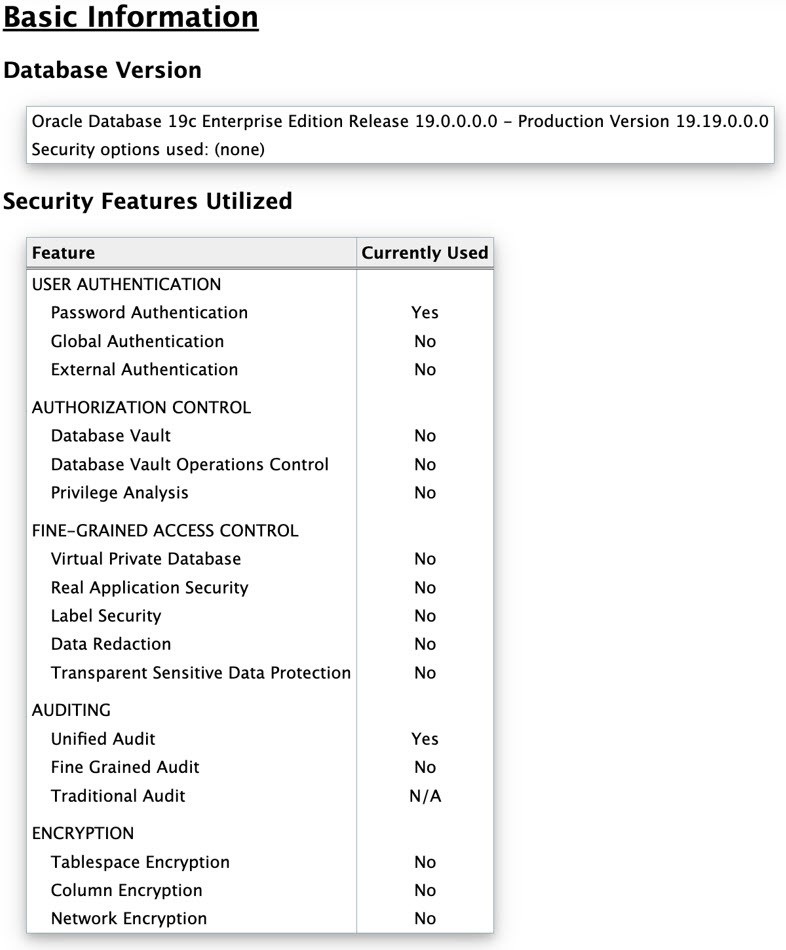
The Basic Information section is followed by the User Accounts section.
Oracle Database Security Assessment Report — User Accounts
The Oracle Database Security Assessment Report — User Accounts section displays the following information:
| Name | Finding ID | Description |
|---|---|---|
|
User Accounts |
- |
Displays the user accounts and the following information about each account:
|
|
Users with DEFAULT Profile |
USER.DEFAULTPROFILE | Displays the DEFAULT user profile password and resource parameters and the number of users in it. |
|
Users with Default Passwords |
USER.DEFPWD |
Displays information about the user accounts with default passwords. Default account passwords for predefined Oracle accounts are well known. Active accounts with default passwords provide a trivial means of entry for attackers, but well-known passwords should be changed for locked accounts as well. |
|
Users with Expired Passwords |
USER.EXPIRED |
Displays information about the user accounts with expired passwords. Password expiration is used to ensure that users change their passwords regularly. Unlocked accounts with an expired password can present a security risk, especially as those accounts age. Although the password is expired, because the account is unlocked, it can easily be used by anyone who knows the old password. You should investigate accounts that have been unused for an extended period to determine whether they should remain active. |
|
Inactive Users |
USER.INACTIVE |
Displays information about the user accounts that are not in use and also accounts that are not configured to be locked when inactive. If a user account is no longer in use, it increases
the attack surface of the system unnecessarily while providing
no corresponding benefit. Furthermore, unauthorized use is less
likely to be noticed when no one is regularly using the account.
Accounts that have been unused for more than 30 days should be
investigated to determine whether they should remain active. A
solution is to set |
|
Sample Schemas |
USER.SAMPLE |
Displays information about the user accounts that
use sample schemas such as Sample schemas are well-known accounts provided by Oracle to serve as simple examples for developers. They generally serve no purpose in a production database and should be removed because they unnecessarily increase the attack surface of the database. |
|
Application Owner Account |
USER.APPOWNER |
Checks the database for the account that could be
considered the application owner and for objects accessible by
the application owner. Any user not "oracle maintained" that
owns most objects in the database is considered the Application
Owner. This check:
|
|
Shared Accounts |
USER.SHARED |
Displays users that have multiple administrative privileges and proxy users. |
|
Users with Objects |
USER.OBJOWNER |
Displays application users who own objects and can grant access to those objects to other users |
|
Users Authorized for Object Ownership |
USER.OBJAUTHZ | Displays non-oracle maintained users who own objects |
|
Users with Security Objects |
USER.SECURITYOBJS |
Displays users who own security objects |
|
Users with Grant Option |
USER.GRANTOPTION |
Checks for users that have been granted privileges
with |
|
Users with Sensitive Data |
USER.SENSITVEDATA |
Displays users that own tables with columns marked as sensitive with TSDP and users that can access those tables. To ensure secure access to sensitive information, review these users. It is best to grant access to data through roles rather than directly to individual accounts. |
|
User Schemas in SYSTEM or SYSAUX Tablespace |
USER.TABLESPACE |
Displays information about the regular user accounts that use the reserved Oracle-supplied tablespaces. The |
|
Case-Sensitive Passwords |
USER.PASSWORDCASE |
Displays whether case-sensitive passwords are enabled. Case-sensitive passwords are recommended because including both upper and lower-case letters greatly increases the set of possible passwords that must be searched by an attacker who is attempting to guess a password by exhaustive search. Setting Note: In 21c USER.PASSWORDCASE isn't expected to be shown asSEC_CASE_SENSITIVE_LOGON is
desupported
|
|
Legacy Password Versions |
USER.AUTHLEGACY |
Displays information about the user accounts with obsolete password verifiers. For each user account, the database may store
multiple verifiers, which are hashes of the user password. Each
verifier supports a different version of the password
authentication algorithm. Every user account should include a
verifier for the latest password version supported by the
database so that the user can be authenticated using the latest
algorithm supported by the client. When all clients have been
updated, the security of user accounts can be improved by
removing the obsolete verifiers. HTTP password verifiers are
used for XML Database authentication. Use the |
|
User Profiles |
- |
Displays information about the user profiles. |
|
Users with no Password Complexity Requirements |
USER.PASSWORDFUNCTION |
Displays information about profiles with and without a password complexity verification function. Users not subject to password complexity verification are also displayed. Password verification functions are used to ensure that user passwords meet minimum requirements for complexity, which may include factors such as length, use of numbers or punctuation characters, difference from previous passwords, etc. Oracle supplies several predefined functions, or a custom PL/SQL function can be used. Every user profile should include a password verification function. |
|
Account Locking after Failed Login Attempts |
USER.NOLOCK |
Displays information about user profile failed login attempt enforcement. Attackers sometimes attempt to guess a user's
password by simply trying all possibilities from a set of common
passwords. To defend against this attack, it is advisable to use
the |
|
Users with Unlimited Password Lifetime |
USER.NOEXPIRE |
Displays information about user profile password expiration enforcement. Password expiration is used to ensure that users change their passwords on a regular basis. It also provides a mechanism to automatically disable temporary accounts. Passwords that never expire may remain unchanged for an extended period of time. When passwords do not have to be changed regularly, users are also more likely to use the same passwords for multiple accounts. |
|
Users with Unlimited Concurrent Sessions |
USER.SESSIONS |
Displays all users that have a Profile Resource Limit for
|
|
Unlimited Session Idle Time |
USER.IDLETIME |
This check lists users with UNLIMITED IDLE TIME |
| Users with Gradual Password Rollover | USER.PASSWORDROLLOVER |
Displays information about the Gradual Password Rollover. Gradual Password Rollover allows administrators to
change database passwords for applications without having to
schedule downtime. Prior to the advent of the gradual password
rollover feature, the database administrator needed to take the
application down while the database password was being rotated.
This was because the password update required changes on both
the database and the application side. With gradual database
password rollover, the application can continue to use the older
password until the new password is configured in the
application. To accomplish this, the database administrator can
associate a profile having a non-zero limit for the
|
|
Temporary Users |
USER.TEMP |
Displays users associated with the DEFAULT profile. Users specifically created to execute temporary tasks should be on a profile tailored for that purpose. |
|
Development Users in Production Databases |
USER.DEV |
There should not be developer accounts in production systems. Verify if such accounts exist in your database. |
|
Advanced Replication Users |
USER.REPCAT |
Checks if Oracle Advanced Replication is being used and lists the dblinks used for replication. Checks to see if
|
|
Minimum Client Authentication Version |
USER.AUTHVERSION |
Displays information about the user accounts that do
not have minimum client version specified in the
Over time, Oracle releases have added support for
increasingly secure versions of the algorithm used for password
authentication of user accounts. In order to remain compatible
with older client software, the database continues to support
previous password versions as well. The
|
Note:
Predefined Oracle accounts which are schema-only or locked are not included in this report. To include all user accounts, run the report with the-a option.
The following figure displays an example of the Oracle Database Security Assessment Report — User Accounts section.
Figure 1-5 Oracle Database Security Assessment Report — User Accounts
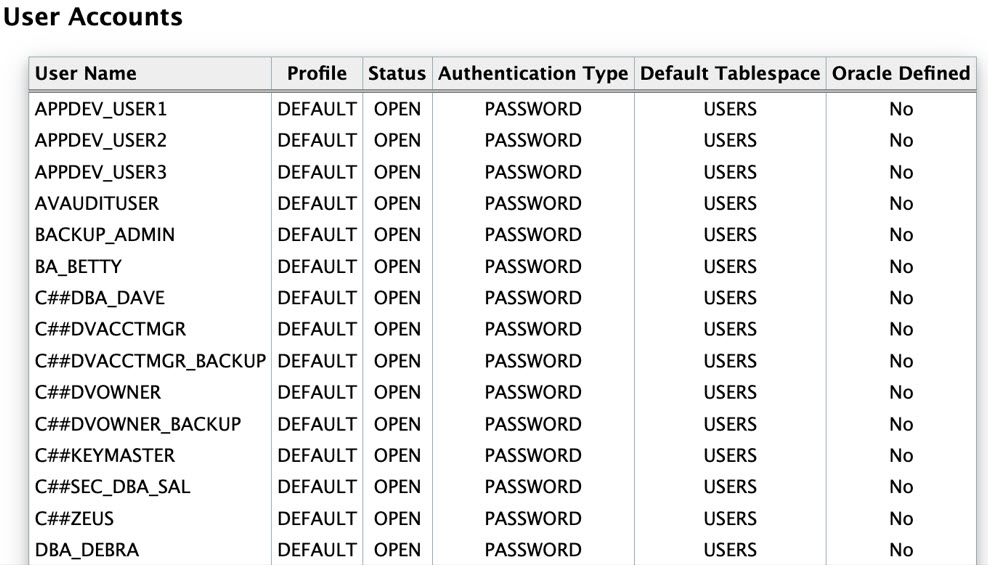
The User Accounts section is followed by the Privileges and Roles section.
Oracle Database Security Assessment Report — Privileges and Roles
The Oracle Database Security Assessment Report — Privileges and Roles section displays the following information:
| Name | Finding ID | Description |
|---|---|---|
|
Access to Password Verifier Tables |
PRIV.ACCESSVERIFIERS |
Displays access to password verifier tables granted to users. Users with these privileges can access objects that contain user password verifiers. The verifiers can be used in offline attacks to discover user passwords. |
|
Users with Administrative Privileges SYS* Privileges |
PRIV.SYSADMIN |
Displays the administrative privileges granted to user accounts. Administrative privileges allow a user to perform
maintenance operations, including some that may occur while the
database is not open. The |
|
Users with DBA Role |
PRIV.DBA |
Displays the user accounts that have been granted the DBA or PDB_DBA role. The DBA role is very powerful and can be used to bypass many security protections. It should be granted to only a small number of trusted administrators. Furthermore, each trusted user should have an individual account for accountability reasons. As with any powerful role, avoid granting the DBA role with admin option unless absolutely necessary. |
|
Users with Powerful Roles |
PRIV.BIGROLES |
Displays the user accounts that have been granted roles with maximum data access privileges. Like the DBA role, these roles
( |
|
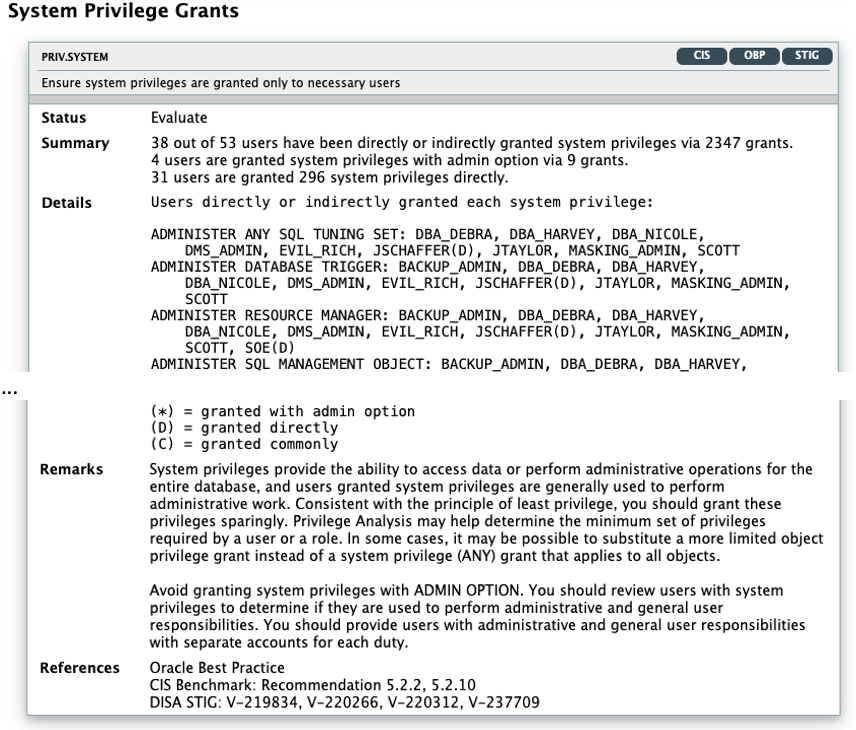
System Privilege Grants |
PRIV.SYSTEM |
Displays the system privileges granted to users. System privileges provide the ability to access data or perform administrative operations for the entire database. Consistent with the principle of least privilege, these privileges should be granted sparingly. System privileges should be granted with admin option only when the recipient needs the ability to grant the privilege to others.
|
|
System Privileges Granted to PUBLIC |
PRIV.SYSPUBLIC |
Displays the system privileges granted to
Privileges granted to |
|
Roles Granted to PUBLIC |
PRIV.ROLEPUBLIC |
Displays the roles granted to
Roles granted to |
|
Column Privileges Granted to PUBLIC |
PRIV.COLPUBLIC |
Displays the column access privileges granted to
Privileges granted to |
|
Objects Accessible by PUBLIC |
PRIV.OBJPUBLIC |
Displays objects that are accessible by PUBLIC. |
|
Encryption Packages Granted to PUBLIC |
PRIV.ENCRYPTPACKAGEPUBLIC |
Displays DBMS_CRYPTO, DBMS_OBFUSCATION_TOOLKIT, and DBMS_RANDOM grants to PUBLIC. |
|
Scheduler Job Packages Granted to PUBLIC |
PRIV.JOBSCHPACKAGEPUBLIC |
Display DBMS_SCHEDULER and DBMS_JOB EXECUTE grants to PUBLIC and Scheduler/Job system privileges (CREATE JOB, MANAGE SCHEDULER, CREATE EXTERNAL JOB, CREATE ANY JOB) grants to PUBLIC. |
|
Credential Package Granted to PUBLIC |
PRIV.CREDPACKAGEPUBLIC |
Displays EXECUTE grant on DBMS_CREDENTIAL package to PUBLIC. Also checks for privilege grants of CREATE CREDENTIAL and CREATE ANY CREDENTIAL to users. |
|
File System Packages Granted to PUBLIC |
PRIV.FILESYSTEMPACKAGEPUBLIC |
Displays EXECUTE grant on DBMS_LOB, UTL_FILE, and DBMS_ADVISOR packages to PUBLIC. Also checks for system privilege grants of CREATE ANY DIRECTORY and DROP ANY DIRECTORY to users. |
|
Network Packages Granted to PUBLIC |
PRIV.NETPACKAGEPUBLIC |
Displays EXECUTE grant on DBMS_LDAP, UTL_HTTP, UTL_INADDR, UTL_SMTP, and UTL_TCP packages to PUBLIC. Also checks for users that are authorized to execute packages via ACLs. |
|
SQL Packages Granted to PUBLIC |
PRIV.QUERYPACKAGEPUBLIC |
Displays EXECUTE grant on DBMS_XMLQUERY, DBMS_XMLSAVE, DBMS_XMLSTORE, DBMS_REDACT, DBMS_XMLGEN, and DBMS_SQL packages to PUBLIC. |
|
JAVA Permissions Granted to PUBLIC |
PRIV.JAVAPACKAGEPUBLIC |
Displays EXECUTE grant on DBMS_JAVA and DBMS_JAVA_TEST packages to PUBLIC. Also checks for grants of JAVA_ADMIN role to users. |
|
All Roles |
PRIV.ALLROLES |
Displays all roles granted to users. Roles are a convenient way to manage groups of related privileges, especially when the privileges are required for a particular task or job function. Beware of broadly defined roles, which may confer more privileges than an individual recipient requires. Roles should be granted with admin option only when the recipient needs the ability to modify the role or grant it to others. |
|
Account Management Privileges |
PRIV.ACCOUNTMGMT |
Displays account management privileges granted to users. User management privileges ( |
|
Role and Privilege Management Privileges |
PRIV.ROLEPRIVMGMT |
Displays privilege management privileges granted to users. Users with privilege management privileges ( |
|
Database Management Privileges |
PRIV.DBMGMT |
Displays database management privileges granted to users. Database management privileges ( |
|
Audit Management Package |
PRIV.AUDITMGMTPKG |
Displays audit management tool access granted to users. The |
|
Audit Management Privileges |
PRIV.AUDITMGMT |
Displays audit management privileges granted to users. Audit management privileges ( |
|
Access to Audit Objects |
PRIV.ACCESSAUDITOBJ |
Displays access to audit objects granted to users. Users with these privileges can directly access and modify objects containing audit information. Access to these objects may allow a malicious user deduce privilege settings for other users and to manipulate the audit information by replacing or deleting audit records. |
|
Access Control Exemption Privileges |
PRIV.ACCESSEXEMPT |
Displays access control exemption privileges that are enforced. Users with exemption privileges ( |
|
Write Access to Restricted Objects |
PRIV.RESTRICTEDOBJ |
Displays access to restricted objects granted to users. Users with these privileges can directly modify objects in the |
|
Users Who Can Impersonate Other Users |
PRIV.IMPERSONATEUSER |
Displays the user accounts that have been granted rights to impersonate other users. The |
|
Privilege for Data Exfiltration in Bulk |
PRIV.EXFILTRATION |
Displays the user accounts that have been granted rights to access or copy any data from a client or server. These PL/SQL packages ( |
|
Code Based Access Control |
PRIV.CBAC |
Displays all program units granted CBAC roles. Code Based Access Control(CBAC) can be used to grant additional privileges on program units. CBAC allows you to attach database roles to a PL/SQL function, procedure, or package. These database roles are enabled at run time, enabling the program unit to execute with the required privileges in the calling user's environment. |
|
Java Permissions |
PRIV.JAVAPERMISSIONS |
Displays the user accounts that have been granted privileges to execute Java classes within the database. Java permission grants control the ability of database users to execute Java classes within the database server. A database user executing Java code must have both Java security permissions and database privileges to access resources within the database. These resources include database resources, such as tables and PL/SQL packages, operating system resources, such as files and sockets, Oracle JVM classes, and user-loaded classes. Make sure that these permissions are limited to the minimum required by each user. |
The following figure displays an example of the Oracle Database Security Assessment Report — Privileges and Roles section.
Figure 1-6 Oracle Database Security Assessment Report — Privileges and Roles
The Privileges and Roles section is followed by the Authorization Control section.
Oracle Database Security Assessment Report — Authorization Control
The Oracle Database Security Assessment Report — Authorization Control section displays the following information:
| Name | Finding ID | Description |
|---|---|---|
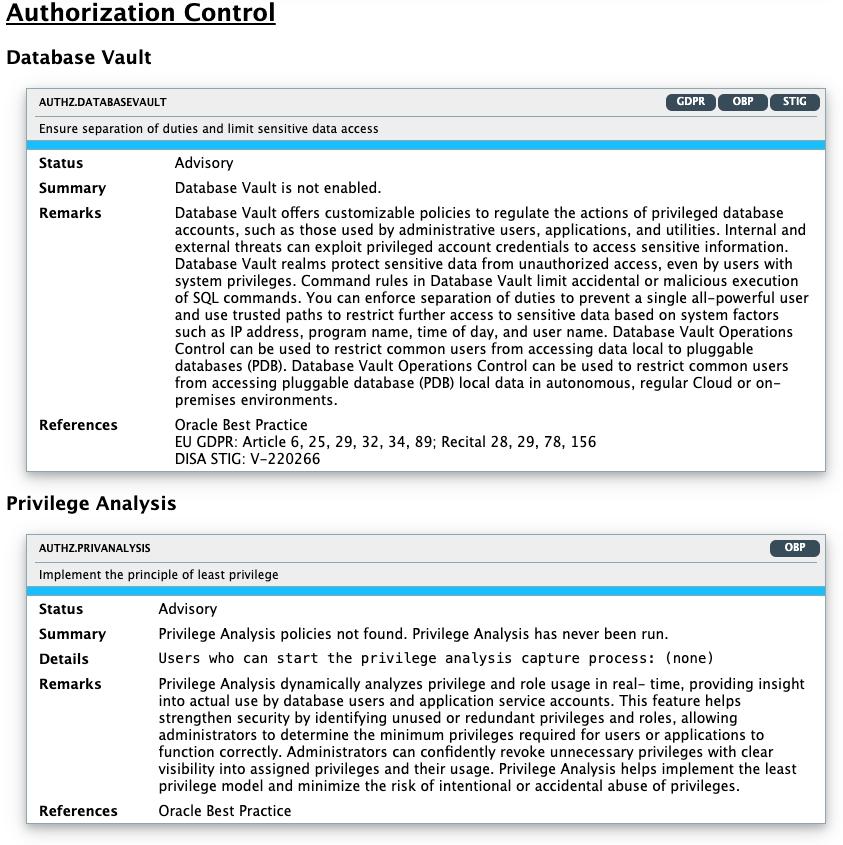
|
Database Vault |
AUTHZ.DATABASEVAULT |
Displays whether Oracle Database Vault is enabled and details existing protected objects, realms, command rules, and users granted Database Vault specific roles. Database Vault provides for configurable policies to control the actions of database accounts with elevated privileges such as those accounts used by administrative users, applications and utilities. Attacks (originating from external as well as internal sources) leverage privileged account credentials to access sensitive information. Database Vault realms prevent unauthorized access to sensitive data objects, even by user accounts with system privileges. Database Vault Command rules limit the accidental or malicious execution of SQL commands. You can use Database Vault to enforce separation of duties to prevent a single all powerful user. Also it provides trusted paths to further restrict access to sensitive data using system factors such as IP address, program name, time of day and user name. Database Vault operations control can be used to restrict common users from accessing pluggable database (PDB) local data in autonomous, regular Cloud, or on-premises environments. |
|
Privilege Analysis |
AUTHZ.PRIVANALYSIS |
Displays Privilege Analysis policies and users with privileges to start the capture proces. Privilege Analysis records the privileges used during a real or simulated workload. After collecting data about the privileges that are actually used, this information can be used to revoke privilege grants that are no longer needed or to create roles with only the privileges that are used by the user or role. This helps implement Least Privilege Model and minimizes risk from intentional or accidental abuse of privileges. |
|
Authentication for Client Scripts |
AUTHZ.PASSWORDSCRIPTS |
Lists password-authenticated users whose passwords can potentially be embedded in client scripts, jobs, and application source code to connect to the database server. |
| Data Masking | AUTHZ.DATAMASKING |
Lists tables with sensitive data that should be masked when transferred to non-production systems. This check lists tables marked sensitive by TSDP or in
|
| PKI Based Authentication | AUTHZ.PKI | List user accounts identified externally where the authentication method is TCPS. This finding is targeting mostly customers looking for STIG compliance. |
The following figure displays an example of the Oracle Database Security Assessment Report — Authorization Control section.
Figure 1-7 Oracle Database Security Assessment Report — Authorization Control
The Authorization Control section is followed by the Fine-Grained Access Control section.
Oracle Database Security Assessment Report — Fine-Grained Access Control
The Oracle Database Security Assessment Report — Fine-Grained Access Control section displays the following information:
| Name | Finding ID | Description |
|---|---|---|
|
Data Redaction |
ACCESS.DATAREDACTION |
Displays information on Data Redaction policies, exempted users, and execute grants on the DBMS_REDACT package. Data Redaction automatically masks sensitive data found in the results of a database query. |
|
Virtual Private Database |
ACCESS.VPD |
Displays information on Virtual Private Database policies, exempted users, and execute grants on the DBMS_RLS package. VPD allows for fine-grained control over the rows and columns of a table are visible to a SQL statement. |
|
Real Application Security |
ACCESS.RAS |
Displays information on Real Application Security policies, exempted users, and users granted ADMIN_SEC_POLICY and APPLY_SEC_POLICY. Real Application Security (RAS) is a more modern, advanced version of Virtual Private Database and provides fine-grained control over the rows and columns of a table that are visible to a SQL statement. |
|
Label Security |
ACCESS.LABELSECURITY |
Displays whether Oracle Label Security is enabled. Oracle Label Security provides the ability to tag data with a data label or a data classification. Access to sensitive data is controlled by comparing the data label with the requesting user's label or security clearance. |
|
Transparent Sensitive Data Protection |
ACCESS.TSDP |
Displays information on Transparent Sensitive Data policies and the users that can manage it. TSDP was introduced in Oracle Database 12.1, and allows a data type to be associated with each column that contains sensitive data. TSDP can then apply various data security features to all instances of a particular type so that protection is uniform and consistent. |
The following figure displays an example of the OracleDatabase Security Assessment Report — Fine-Grained Access Control section.
Figure 1-8 Oracle Database Security Assessment Report — Fine-Grained Access Control
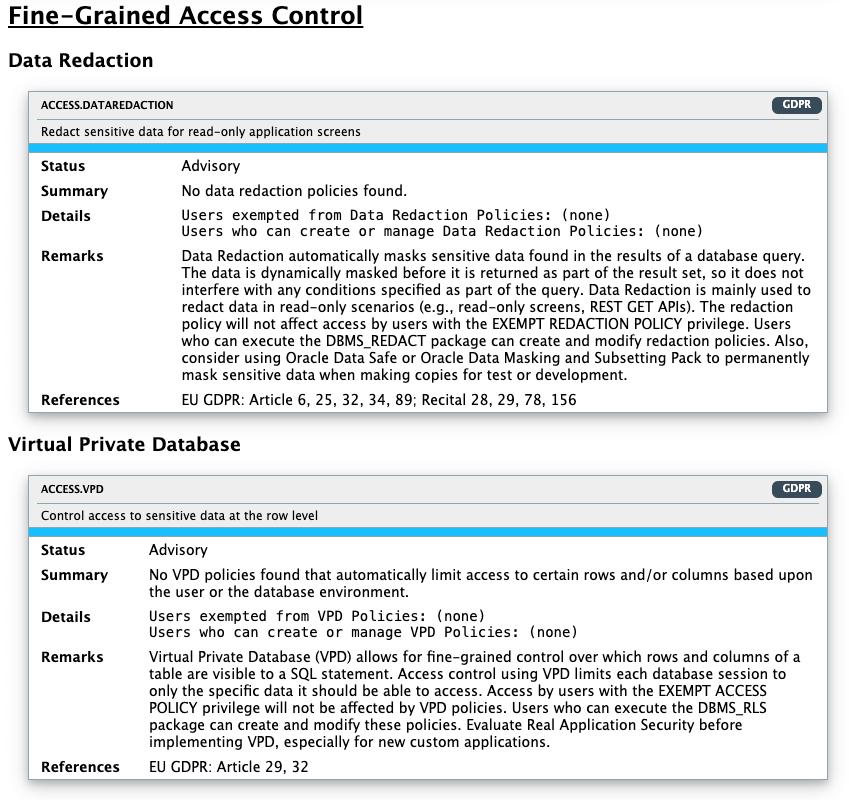
Description of "Figure 1-8 Oracle Database Security Assessment Report — Fine-Grained Access Control"
The Fine-Grained Access Control section is followed by the Auditing section.
Oracle Database Security Assessment Report — Auditing
The Oracle Database Security Assessment Report — Auditing section displays the following information:
| Name | Finding ID | Description |
|---|---|---|
|
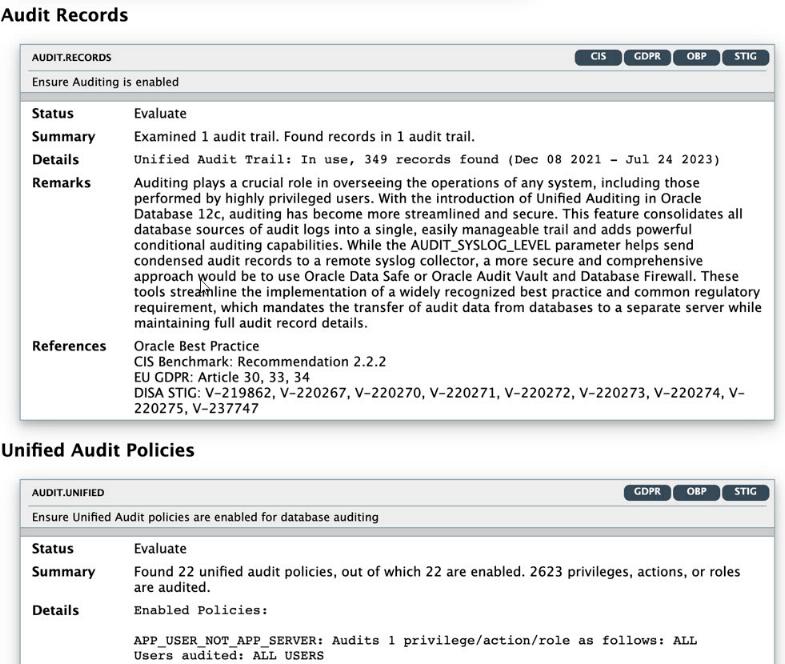
Audit Management Configuration Parameters |
- |
Displays information on audit management configuration parameters |
|
Audit Records |
AUDIT.ENABLED |
Displays information about audit trails. Auditing is an essential component for securing any system. The audit trail allows for monitoring the activities of highly privileged users. |
|
Unified Audit Policies |
AUDIT.UNIFIEDPOLICIES |
Displays whether unified audit policies are enabled. Unified Audit, available in Oracle Database 12.1 and later releases, combines multiple audit trails into a single unified view. It also introduces new syntax for specifying effective audit policies. |
|
Fine Grained Audit |
AUDIT.FGA |
Displays whether fine grained audit policies are enabled. Fine Grained Audit policies can record highly specific activity, such as access to particular table columns or access that occurs under specified conditions. This is a useful way to monitor unexpected data access while avoiding unnecessary audit records that correspond to normal activity. |
|
Audit Administrative (SYS*) Users |
AUDIT.ADMINACTIONS |
Displays whether the actions of the
It is important to audit administrative actions
performed by the |
|
Audit User Logon and Logoff |
AUDIT.CONNECTIONS |
Displays whether Database connections are audited by enabled audit policies. Successful user connections to the database should be audited to assist with future forensic analysis. Unsuccessful connection attempts can provide early warning of an attacker's attempt to gain access to the database. |
|
Audit Database Management Activities |
AUDIT.DBMGMT |
Displays whether the actions related to database management are audited by enabled audit policies. Actions that affect the management of database features should always be audited. Each action or privilege listed should be included in at least one enabled audit policy. |
|
Audit Account Management Activities |
AUDIT.ACCOUNTMGMT |
Displays whether account management activities are audited. |
|
Audit System Privileges |
AUDIT.SYSTEMPRIVS |
Displays information on whether system privileges are audited by enabled audit policies. |
|
Audit Roles with System Privileges |
AUDIT.ROLESYSTEMPRIVS | Displays information about unified audit policies that audit roles with system privileges. |
|
Audit Privilege Management |
AUDIT.PRIVMGMT |
Displays whether the actions related to privilege management are audited by enabled audit policies. Granting additional privileges to users or roles potentially affects most security protections and should be audited. Each action or privilege listed should be included in at least one enabled audit policy. |
|
Audit SQL Statements |
AUDIT.STATEMENT |
Displays information about SQL statements audited by enabled audit policies. Applies to targets with Traditional Auditing policies. |
|
Audit Object Actions |
AUDIT.SENSITIVEOBJS |
Displays information about the object access audited by enabled audit policies. |
|
Audit Synonym Management Activities |
AUDIT.SYNONYMS |
Displays information on whether synonym management activities (CREATE ANY SYNONYM, CREATE PUBLIC SYNONYM, CREATE SYNONYM, DROP PUBLIC SYNONYM, DROP SYNONYM) are audited. |
|
Audit Conditions |
AUDIT.CONDITION |
Lists all audit policies with conditions and, if enabled, lists users/roles it's enabled for. |
|
Audit Shared Accounts |
AUDIT.SHAREDPROXY |
Checks to see if users listed in USER.SHARED are being audited. |
|
Audit Storage |
AUDIT.TABLESPACE |
Displays information about tablespaces used by
different audit trails. Checks include:
|
|
Audit Trail Cleanup |
AUDIT.CLEANUPJOBS |
Lists enabled jobs that cleanup audit trails and checks cleanup jobs that are not present |
|
Audit Data Pump |
AUDIT.DATAPUMP |
Displays whether data pump exports and imports are being audited. |
|
Audit STIG Actions |
AUDIT.STIGPOLICY |
Oracle provides out-of-the-box audit policies that
aim to answer DoD- auditable events requirements -
|
|
Audit Database Vault |
AUDIT.DATABASEVAULT |
Displays users that can administer Database Vault but are not audited and lists policies enabled to audit Database Vault actions |
|
Audit Oracle Label Security |
AUDIT.LABELSECURITY |
Displays information regarding enabled audit policies used to audit OLS.
|
Note:
The details of the audit findings can vary depending on whether the database has unified audit or traditional audit in place. Starting in Oracle Database 12.2, the best practice is to use Unified Audit.The following figure displays an example of the Oracle Database Security Assessment Report — Auditing section.
Figure 1-9 Oracle Database Security Assessment Report — Auditing
The Auditing section is followed by the Encryption section.
Oracle Database Security Assessment Report — Encryption
The Oracle Database Security Assessment Report — Encryption section displays the following information:
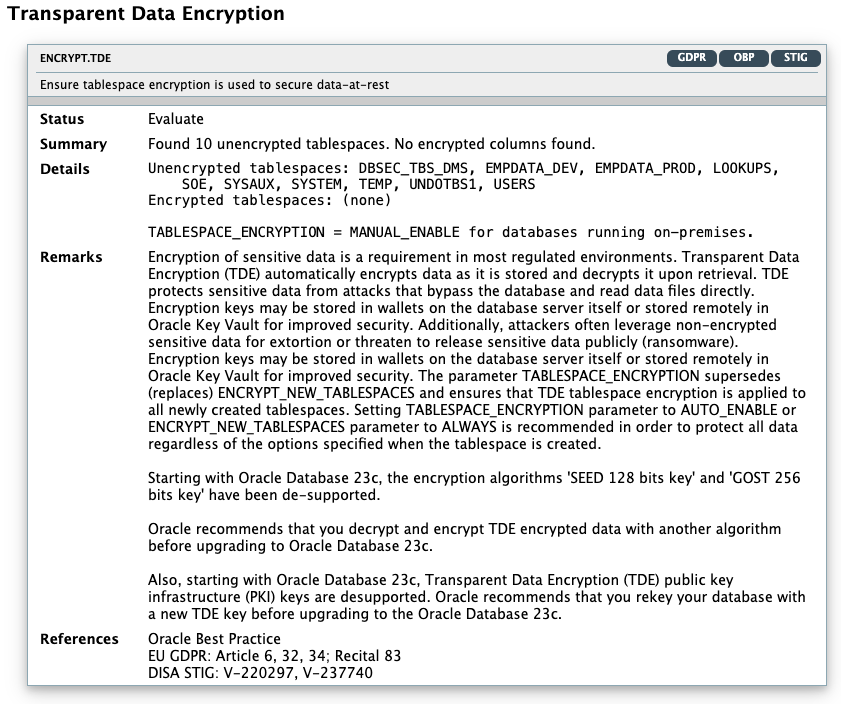
| Name | Finding ID | Description |
|---|---|---|
|
Transparent Data Encryption |
ENCRYPT.TDE |
Displays whether column or tablespace encryption is in use. Also, shows encrypted and unencrypted tablespaces along with the number of days since the master encryption key was last rotated. Encryption of sensitive data is a requirement in most regulated environments. Transparent Data Encryption automatically encrypts data as it is stored and decrypts it upon retrieval. This protects sensitive data from attacks that bypass the database and read data files directly. |
|
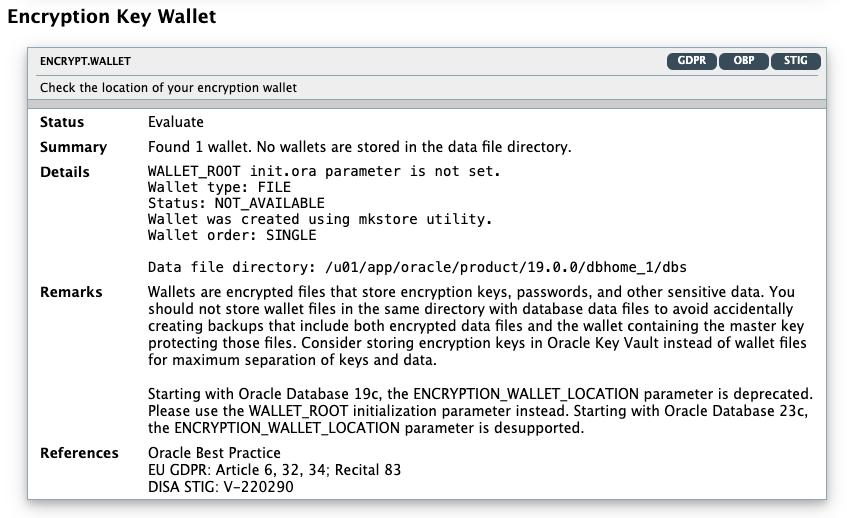
Encryption Key Wallet |
ENCRYPT.WALLET |
Displays wallet information. Wallets are encrypted files used to store encryption keys, passwords, and other sensitive data. Wallet files should not be stored in the same directory with database data files, to avoid accidentally creating backups that include both encrypted data files and the wallet containing the master key protecting those files. For maximum separation of keys and data, consider storing encryption keys in Oracle Key Vault instead of wallet files. |
| FIPS Mode for TDE and DBMS_CRYPTO | ENCRYPT.DBFIPS |
Displays information whether TDE and DBMS_CRYPTYO run in a FIPS-compliant mode. Federal Information Processing Standard (140-2) is a U.S. government security standard that specifies security requirements. It is used to approve cryptographic modules. Setting parameter DBFIPS_140 = TRUE enables Transparent Data Encryption (TDE) and DBMS_CRYPTO PL/SQL package program units to run in a FIPS-compliant mode. FIPS mode is mostly used by departments and agencies of the United States federal government looking to meet FIPS and/or STIG compliance. Be aware that this setting and thus using the underlying FIPS-certified library incurs a slight amount of overhead when the library is first loaded. This is due to the verification of the library signature and the execution of the self-test. |
| FIPS mode for TLS | ENCRYPT.TLSFIPS |
Federal Information Processing Standard (140-2) is a U.S. government security standard that specifies security requirements. The SSLFIPS_140 parameter configures the Transport Layer Security (TLS) adapter to run in FIPS mode. SSLFIPS_LIB sets the location of the FIPS library. |
The following figure displays an example of the Oracle Database Security Assessment Report — Encryption section.
Figure 1-10 Oracle Database Security Assessment Report — Encryption and Encryption Key Wallets
The Encryption section is followed by the Database Configuration section.
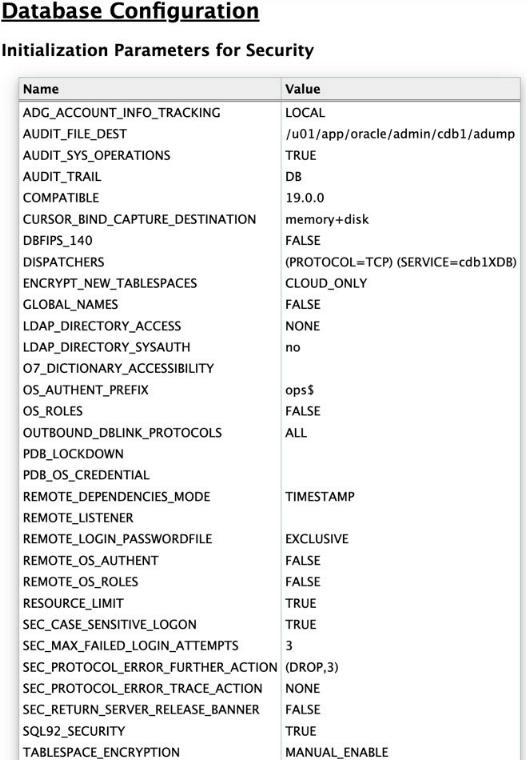
Oracle Database Security Assessment Report — Database Configuration
The Oracle Database Security Assessment Report — Database Configuration section displays the following information:
| Name | Finding ID | Description |
|---|---|---|
|
Initialization Parameters for Security |
- |
Displays security related Database initialization parameters and their values. |
|
Pre-Authenticated Request URL |
CONF.PREAUTHREQUESTURL |
Displays pre-authenticated URL information for
Autonomous Database Serverless databases including who can
manage them via the |
|
Authentication Configuration |
CONF.AUTHN |
Displays information about the user account initialization parameters.
|
|
PDB OS User |
CONF.DEFAULTPDBOSUSER | Checks if the highly privileged Oracle OS user is set for the PDB_OS_CREDENTIAL parameter. |
|
Control Files |
CONF.CONTROLFILES |
Checks if control files are multiplexed and lists all the control file locations. The |
|
PDB OS User |
CONF.DEFAULTPDBOSUSER | Checks if the highly privileged Oracle OS user is set for the PDB_OS_CREDENTIAL parameter. |
|
Redo Log Files |
CONF.REDOLOGS | Checks if the defined redo log files follow best practices and lists their location. Redo logs should be multiplexed and stored on different physical disks. |
|
Archive Log Mode |
CONF.ARCHIVELOG |
Checks if the database is in
|
|
Database Backup |
CONF.BACKUP |
Displays information about Database backup records. Database should be backed up regularly to prevent loss of data in the event of a system failure. Oracle Recovery Manager (RMAN) allows performing backup and recovery tasks on your databases. Unencrypted backup data should not be transported on tape or disk to offsite storage for safekeeping. |
|
Instance Name Check |
CONF.INSTANCENAME |
Displays whether the instance name contains the Database version number. Instance names should not contain Oracle version numbers. Service names may be discovered by unauthenticated users. If the service name includes version numbers or other database product information, a malicious user may use that information to develop a targeted attack. |
|
SQL Firewall |
CONF.SQLFIREWALL |
Checks if SQL Firewall is enabled and displays the users that are affected by the policy and whether the policy is in observing, blocking, or enforcing mode. Also, details if the SQL and context allow-lists are in enforcement mode or not. Only applicable to Oracle Database versions >=23ai. |
|
Read-only ORACLE_HOME |
CONF.READONLYHOME |
Checks if the |
|
Access to Dictionary Objects |
CONF.SYSOBJ |
Displays whether access to dictionary objects is properly limited. When |
|
Inference of Table Data |
CONF.SQL92SECURITY |
Displays whether data inference attacks are properly blocked. When SQL92_SECURITY is set to TRUE, UPDATE and DELETE statements that refer to a column in their WHERE clauses will succeed only when the user has the privilege to SELECT from the same column. This parameter should be set to TRUE so that this requirement is enforced in order to prevent users from inferring the value of a column which they do not have the privilege to view. |
|
Access to Password File |
CONF.PASSWORDFILE |
Displays whether the password file is configured correctly. The |
|
Network Communication |
CONF.NETWORK |
Displays information about initialization parameters that determine the database server response to malformed packets. Also, includes details on usage of a remote listener and if database server version information is hidden from unauthenticated client requests.
|
|
External OS Authentication |
CONF.EXTERNALOSAUTH |
Displays whether the Oracle Database roles are defined and managed by the database itself or by the host operating system (for local and remote authentication). The |
|
Unused Components |
CONF.DBCOMPONENTS | Checks to see if components like XOQ, CONTEXT, SDO, DV, OLS are installed/enabled and not being used. |
|
Job Details |
CONF.JOBS |
Checks the scheduled database jobs and users who can
administer them. Checks include:
|
|
Triggers |
CONF.TRIGGERS |
Displays information about logon triggers. A trigger is code that executes whenever a specific event occurs, such as inserting data in a table or connecting to the database. Disabled triggers are a potential cause for concern because whatever protection or monitoring they may be expected to provide is not active. |
|
Disabled Constraints |
CONF.CONSTRAINTS |
Displays information about disabled constraints. Constraints are used to enforce and guarantee specific relationships between data items stored in the database. Disabled constraints are a potential cause for concern because the conditions they ensure are not enforced. |
|
External Procedures |
CONF.EXTERNALPROCS |
Displays information about external procedures and services. External procedures allow code written in other
languages to be executed from PL/SQL. Note that modifications to
external code cannot be controlled by the database. Be careful
to ensure that only trusted code libraries are available to be
executed. Although the database can spawn its own process to
execute the external procedure, it is advisable to configure a
listener service for this purpose so that the external code can
run as a less-privileged OS user. The listener configuration
should set |
|
Source Code Analysis |
CONF.SOURCEANALYSIS | Checks DBA_SOURCE for non-oracle
maintained procedures and functions using
RAISE_APPLICATION_ERROR and
DBMS_OUTPUT.PUT_LINE. |
|
Directory Objects |
CONF.DIRECTORYOBJ |
Displays information about directory objects. Directory objects allow access to the server's file system from PL/SQL code within the database. Access to files that are used by the database kernel itself should not be permitted, as this may alter the operation of the database and bypass its access controls. |
|
Database Links |
CONF.DATABASELINKS |
Displays information about database links. Database links allow users to execute SQL statements
that access tables in other databases. This allows for both
querying and storing data on the remote database. It is
advisable to set |
|
Network Access Control |
CONF.NETWORKACL |
Displays information about Network Access Control Lists (ACLs). Network ACLs control the external servers that
database users can access using network packages such as UTL_TCP
and UTL_HTTP. Specifically, a database user needs the connect
privilege to an external network host computer if he or she is
connecting using the |
|
XML Database Access Control |
CONF.XMLACL |
Displays information about XML Database Access Control Lists (ACLs). XML ACLs control access to database resources using the XML DB feature. Every resource in the Oracle XML DB Repository hierarchy has an associated ACL. The ACL mechanism specifies a privilege-based access control for resources to principals, which are database users or roles. Whenever a resource is accessed, a security check is performed, and the ACL determines if the requesting user has sufficient privileges to access the resource. Make sure that these privileges are limited to the minimum required by each user. |
|
File System Access |
CONF.FILESYS |
Checks for |
|
Trace Files |
CONF.TRACEFILELIMIT |
Displays information about the initialization parameters for trace files. The hidden parameter |
The following figure displays an example of the Oracle Database Security Assessment Report — Database Configuration section.
Figure 1-11 Oracle Database Security Assessment Report — Database Configuration
The Database Configuration section is followed by the Network Configuration section.
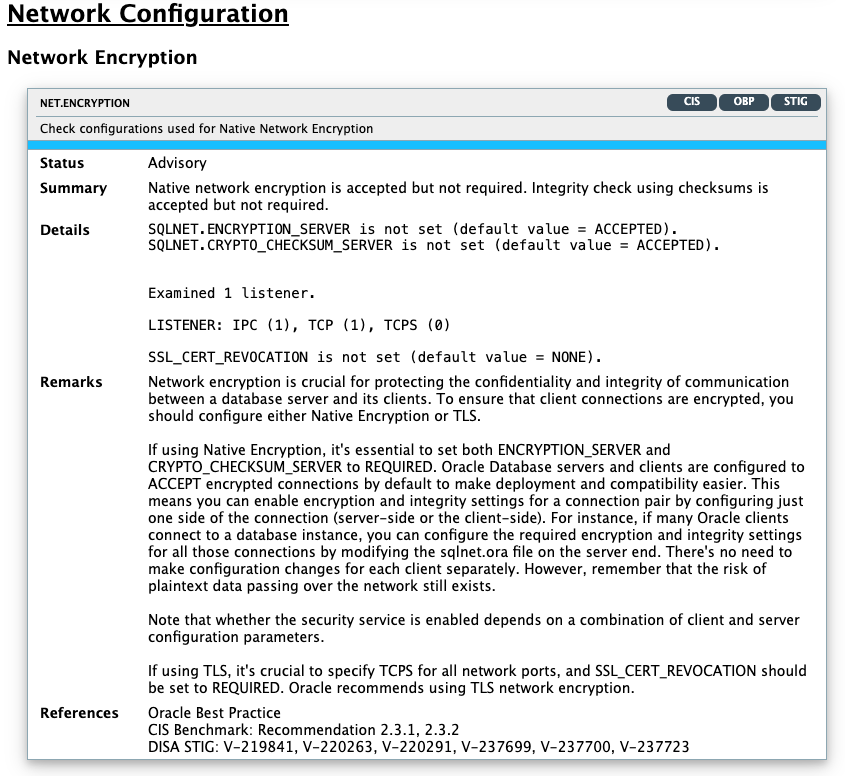
Oracle Database Security Assessment Report — Network Configuration
The Oracle Database Security Assessment Report — Network Configuration section displays the following information:
| Name | Finding ID | Description |
|---|---|---|
|
Network Encryption |
NET.ENCRYPTION |
Displays information about network encryption. Network encryption protects the confidentiality and integrity of communication between the database server and its clients. Either Native Encryption or TLS should be enabled. For Native Encryption, both |
|
Client Nodes |
NET.INVITEDNODES |
Displays whether the database accepts connections from any client.
|
|
Connection Limits Configuration |
NET.CONNECTIONLIMITS | Check value of parameters governing termination of
unauthenticated connections:
|
|
Network Listener Configuration |
NET.LISTENERCONFIG |
Displays information about network listener configuration. These parameters are used to limit changes to the network listener configuration.
|
|
Listener Logging Control |
NET.LISTENERLOG |
Displays information about network listener logging configuration. The |
The following figure displays an example of the Oracle Database Security Assessment Report — Network Configuration section.
Figure 1-12 Oracle Database Security Assessment Report — Network Configuration
The Network Configuration section is followed by the Operating System section.
Oracle Database Security Assessment Report — Operating System
The Oracle Database Security Assessment Report — Operating System section displays the following information:
| Name | Finding ID | Description |
|---|---|---|
|
Installation Account |
OS.INSTALLATIONUSER |
This check specifies the Oracle installation owner. |
|
OS Authentication |
OS.AUTH |
Displays information about operating system group names and users that can exercise administrative privileges. OS authentication allows operating system users within the specified user group to connect to the database with administrative privileges. This shows the OS group names and users that can exercise each administrative privilege. OS users with administrative privileges should be reviewed to prevent any unauthorized, malicious or unintentional access to the database. |
|
Segregation of Production and Development Databases |
OS.MULTIDB |
Checks for databases/instances running on the same server. If there are multiple databases/instances running on the same server ensure that it is not hosting production and test/development databases. |
|
Process Monitor Processes |
OS.PMON |
Displays whether Process Monitor (PMON) processes are running under the The PMON process monitors user processes and frees resources when they terminate. This process should run with the user ID of the |
|
Agent Processes |
OS.AGENT |
Displays whether Agent processes owners overlap with Listener or Process Monitor (PMON) process owners. Agent processes should run with a user ID separate from the database and listener processes. These processes should run under a user ID separate from the database and listener processes. |
|
Listener Processes |
OS.LISTENER |
Displays whether Listener process owners overlap with Agent or Process Monitor (PMON) process owners. Listener processes accept incoming network connections and connect them to the appropriate database server process. These processes should run with a user ID separate from the database and agent processes. These processes should be administered only through local OS authentication. |
|
CMAN Remote Admin |
OS.CMANLOCAL |
Checks if Oracle Connection Manager is installed in the server and if yes, if CMAN remote administration is configured. |
|
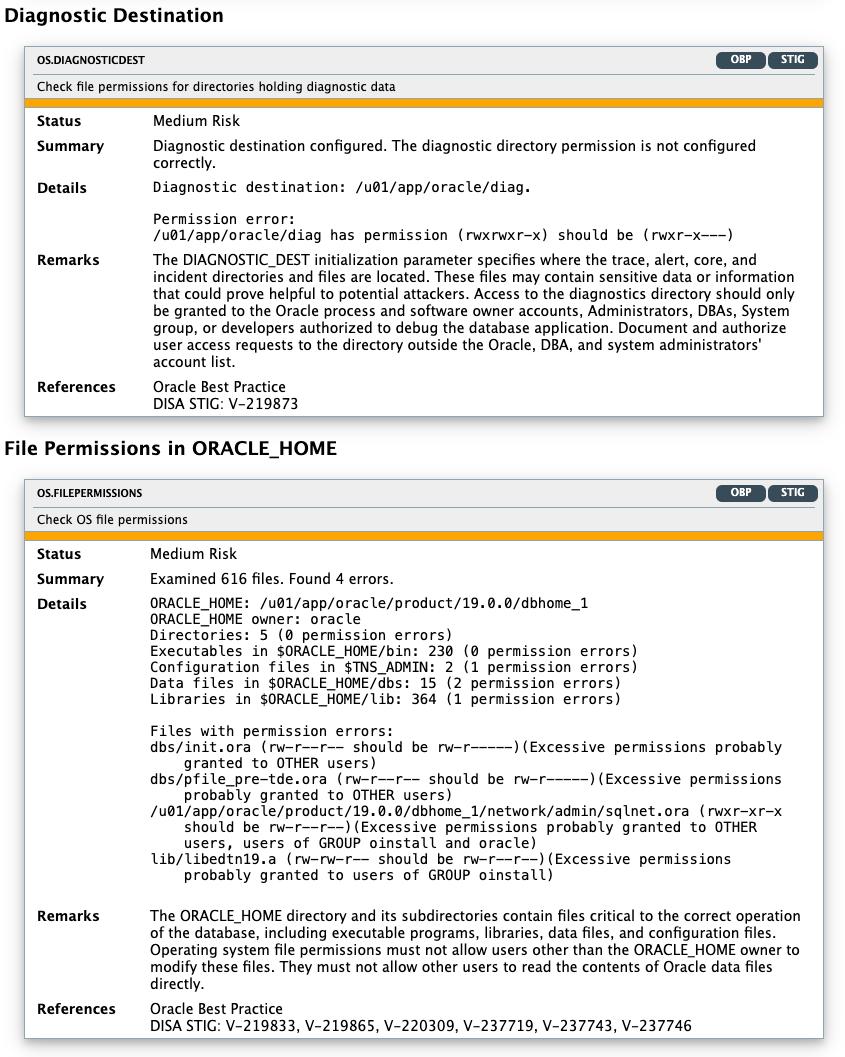
Diagnostic Destination |
OS.DIAGNOSTICDEST |
Checks permissions of
DIAGONSTIC_DEST:
|
|
File Permissions in ORACLE_HOME |
OS.FILEPERMISSIONS |
Displays information about file permissions errors in the
The |
Note:
On Windows, the DBSAT Collector collects data only from SQL queries. Since the data from the operating system commands is missing, the DBSAT Reporter runs a subset of rules on this data. Operating System findings are not available for databases running on Windows platform.The following figure displays an example of the Oracle Database Security Assessment Report — Operating System section.
Figure 1-13 Oracle Database Security Assessment Report — Operating System
The Operating System section is followed by the Diagnostics section.
Oracle Database Security Assessment Report — Diagnostics
The Diagnostics section displays the checks which could not be executed.
Note:
This report provides information and recommendations that may be helpful in securing your Oracle database system. These recommendations reflect best practices for database security and should be part of any strategy for Data Protection by Design and by Default. These practices may help in addressing Articles 25 and 32 of the EU General Data Protection Regulation as well as other data privacy regulations. Technical controls alone are not sufficient for compliance. Passing all findings does not guarantee compliance.
Oracle Database Vault, Oracle Advanced Security, Oracle Label Security, Oracle Data Masking and Subsetting Pack are database licensed options. Oracle Key Vault and Oracle Audit Vault and Database Firewall require separate licensing as well.
The report provides a view on the current status. The results shown are provided for informational purposes only and should not be used as a substitute for a thorough analysis or interpreted to contain any legal or regulatory advice or guidance.
You are solely responsible for your system, and the data and information gathered during the production of this report. You are also solely responsible for the execution of software to produce this report, and for the effect and results of the execution of any mitigating actions identified herein.
Oracle provides this analysis on an "as is" basis without warranty of any kind and Oracle hereby disclaims all warranties and conditions whether express, implied or statutory.
Using the Discoverer
You can generate the Oracle Database Sensitive Data Assessment Report with the Discoverer component.
Oracle Database Sensitive Data Assessment Report
The Discoverer component is used to generate the Oracle Database Sensitive Data Assessment Report. The Discoverer executes SQL queries and collects data from the system to be assessed, based on the settings specified in the configuration and pattern files.
The following figure shows the components and architecture of the Discoverer.
Figure 1-14 Discoverer Components and Architecture
Description of "Figure 1-14 Discoverer Components and Architecture"
Configuring dbsat.config
The settings in the configuration file determine the behavior of the Discoverer.
Configuration Settings
| Section | Key | Value | Description |
|---|---|---|---|
| [Database] | TNS_ADMIN |
|
Location from where network service names needs to be read |
| - | NET_SERVICE_NAME |
|
Network Service name to be used to make connection |
| - | WALLET_LOCATION |
|
Location of wallets for secured connections via SSL or SEPS (Secure External Password Store) |
| - | DB_HOSTNAME |
|
Hostname or IP Address of the target database server |
| - | DB_PORT |
The default is 1521. |
Listener port number for the target database. If a port number is not specified, the default port 1521 is used. |
| - | DB_SERVICE_NAME |
|
Service name for the target database |
| - | SSL_ENABLED |
The default is |
Specifies if SSL is enabled or disabled when connecting to the Database Server. This is an optional argument. It is recommended that the If |
| - | SSL_TRUSTSTORE |
Example: |
Specifies the absolute path to the TrustStore, and the TrustStore file name. Mandatory if |
| - | SSL_TRUSTSTORE_TYPE |
|
Specifies the type of TrustStore. Use Use Use |
| - | SSL_KEYSTORE |
Example: |
Specifies the absolute path to the KeyStore, and the KeyStore file name. If Mandatory if the Database server requires client authentication. |
| - | SSL_KEYSTORE_TYPE |
|
Specifies the type of KeyStore. Use Use Use |
| - | SSL_DN |
|
Distinguished Name (DN) of the target Database server. Specify the DN if the server’s DN needs to be checked. This is an optional argument. |
| - | SSL_VERSION |
The default is |
Specifies the version of the SSL protocol to use when connecting to the Database Server. This is an optional argument. Use Use Use |
| - | SSL_CIPHER_SUITES |
Example: |
Specifies the Cryptographic Algorithms to be used. Multiple entries can be specified as a comma-separated list. This is an optional argument. For information about supported cryptographic suites, see https://docs.oracle.com/javase/8/docs/technotes/guides/security/SunProviders.html. |
| [Discovery Parameters] | SENSITIVE_PATTERN_FILES |
The default is |
Specifies the pattern files to be used. Multiple files can be specified as a comma-separated list. The limit is 10 files. For more information about configuring the Sensitive Data Type pattern file, see Pattern File Configuration (Optional). |
| - | SCHEMA_SCOPE |
The default is |
Specifies the schemas to be scanned. Multiple schemas can be specified as a comma-separated list. |
| - | MINROWS |
The default is |
Specifies the minimum number of rows in a table for that table to be scanned. Tables with a number of rows less than what is specified in the |
| - | EXCLUSION_LIST_FILE |
|
Specifies the file to be used to exclude schemas, tables, or columns from the scan. For more information about configuring the Exclusion List file, see Configuring the Exclusion List File (Optional). |
| [Sensitive Categories] |
The [Sensitive Categories] section defines which Sensitive Categories are used. Valid risk levels are:
The types of sensitive data are defined in the Sensitive Data Type pattern file. For more information about configuring the Sensitive Data Type pattern file, see Pattern File Configuration (Optional). |
Pattern File Configuration (Optional)
The Oracle Database Security Assessment Tool searches for the types of sensitive data defined in the Pattern file(s).
About Sensitive Types
Pattern files contain the patterns to search for. A Pattern file is grouped into sections, defined by the section heading format [SENSITIVE_TYPE_NAME]. Each section constitutes a Sensitive Type.
The following example shows a sample Sensitive Type section for FULL NAME.
[FULL NAME]
COL_NAME_PATTERN = ^(?!.*(ITEM|TAX|BALANCE)).*(FULL.*NAME)|(^|[_-])(CUSTOMER|CUST|CLIENT|PATIENT|PERSON).?(NAME|NM)($|[_-])
COL_COMMENT_PATTERN = ^(?!.*(ITEM|TAX|BALANCE)).*(FULL.?NAME)|(CUSTOMER|CUST|CLIENT|PATIENT|PERSON).?NAME
SENSITIVE_CATEGORY = Identification Info - Public IDsThe Sensitive Type name [SENSITIVE_TYPE_NAME] is displayed in the Sensitive Type column of the Database Sensitive Data Assessment Report — Sensitive Column Details section. For more information about the Database Sensitive Data Assessment Report, see Oracle Database Sensitive Data Assessment Report.
Each Sensitive Type is defined by the following three parameters: COL_NAME_PATTERN, COL_COMMENT_PATTERN, and SENSITIVE_CATEGORY.
COL_NAME_PATTERN
The COL_NAME_PATTERN parameter specifies the text to search for in the Regular Expression (RegExp) patterns of the database column names.
(^LNAME$)|((LAST|FAMILY|SUR|PATERNAL).*NAME$)In the example above, the following text will be searched for in the RegExp patterns of the database column names:
-
(^LNAME$)— Searches for a column titledLNAME. -
((LAST|FAMILY|SUR|PATERNAL).*NAME$)— Searches for column names that containLAST,FAMILY,SUR, orPATERNAL, followed by any characters and ending withNAME. For example,LAST_NAMEorCUSTOMER_SURNAME.
COL_COMMENT_PATTERN
The COL_COMMENT_PATTERN parameter specifies the text to search for in the Regular Expression (RegExp) patterns of the database column comments.
SENSITIVE_CATEGORY
The SENSITIVE_CATEGORY parameter specifies the type of sensitive data. The risk levels associated with exposing types of sensitive data are specified in the sample_dbsat.config file. The risk levels are:
-
Low Risk -
Medium Risk -
High Risk
For more information about configuring the sample_dbsat.config file, see Configuration Settings.
Customizing the Pattern File
custom_dbsat.config file, see Configuring dbsat.config.
About Regular Expressions
The search parameters use regular expressions, sets of strings based on common characteristics shared by each string in the set. Regular expressions vary in complexity, but once you understand the basics of how they are constructed, you can decipher or create any regular expression. You can use character classes, capturing groups, quantifiers, boundary matchers, and logical operators to define regular expressions.
String Literals
The most basic form of pattern matching is the match of a string
literal. For example, if the regular expression is EMP and the
input string is EMP, the match succeeds because the strings are
identical. This regular expression also matches any string containing
EMP, such as EMPLOYEE, TEMP,
and TEMPERATURE.
Metacharacters
You can also use some special characters that affect the way a pattern
is matched. One of the most common ones is the dot (.) symbol,
which matches any character. For example, EMPLOYEE.ID matches
EMPLOYEE_ID and EMPLOYEE-ID, but not
EMPLOYEE_VERIFICATION_ID. Here, the dot is a metacharacter — a
character with special meaning interpreted by the matcher.
Some other metacharacters are: ^ $ ? + * \ - [ ] ( ) {
}.
If you want a metacharacter to be treated literally (as an ordinary
character), you can use a backslash (\) to escape it. For example,
the regular expression 9\+9 matches 9+9.
Character Classes
A character class is a set of characters enclosed within square brackets. It specifies the characters that successfully match a single character from a given input string.
The following table describes some common regular expression constructs.
| Construct | Description |
|---|---|
[abc] |
Matches one of the characters mentioned within square brackets. Example: |
[^abc] |
Matches any character except the ones mentioned within square brackets. Example: |
[A-Z0-9] |
Matches any character in the range mentioned within
square brackets. To specify a range, simply insert the dash
metacharacter " Example: |
Capturing Groups
You can use capturing groups to treat multiple characters as a single
unit. A capturing group is created by placing the characters to be grouped inside a
set of parentheses. For example, the regular expression (SSN)
creates a single group containing the letters S,
S, and N.
See Also:
Capturing GroupsQuantifiers
You can use quantifiers to specify the number of occurrences to match against.
The following table describes some common quantifiers.
| Quantifier | Description |
|---|---|
X? |
Matches zero or one occurrence of the specified character or group of characters. Example: |
X* |
Matches zero or more occurrences of the specified character or group of characters. Example: |
X+ |
Matches one or more occurrences of the specified character or group of characters. Example: |
X{n} |
Matches the specified character or group of
characters exactly Example: |
X{n,} |
Matches the specified character or group of
characters at least Example: |
X{n,m} |
Matches the specified character or group of
characters at least Example: |
An example of regular expression using character class is
SSN[0-9]+, which matches strings like SSN0,
SSN1, and SSN12. Here, [0-9]
is a character class and is allowed one or more times. The regular expression
however, does not match SSN.
See Also:
QuantifiersBoundary Matchers
You can use boundary matchers to make pattern matching more precise by specifying where in the string the match should take place. For example, you might be interested in finding a particular word, but only if it appears at the beginning or end of an input string.
The following table describes common boundary matchers.
| Boundary Construct | Description |
|---|---|
^ |
Matches the specified character or group of characters at the beginning of a string (starts with search). Example: |
$ |
Matches the specified character or group of characters at the end of a string (ends with search). Example: |
\b |
Marks a word boundary. Matches the character or
group of characters specified between a pair of
Example: |
If no boundary matcher is specified, a contains search is performed. For
example, ELECTORAL matches strings containing
ELECTORAL, such as ELECTORAL_ID,
ID_ELECTORAL, and ELECTORALID.
An exact match search can be performed by using ^ and
$ together. For example, ^ADDRESS$ searches
for the exact string ADDRESS. It matches the string
ADDRESS, but does not match strings like
PRIMARY_ADDRESS and ADDRESS_HOME.
See Also:
Boundary MatchersLogical Operators
You can use the pipe or vertical bar character (|) if
you want to match any one of the characters (or group of characters) separated by
pipe. For example, EMPLOY(EE|ER)_ID matches
EMPLOYEE_ID and EMPLOYER_ID.
Examples
^JOB.*(TITLE|PROFILE|POSITION)$ matches strings
beginning with JOB, followed by zero or more occurrences of any
character, and ending with TITLE, PROFILE, or
POSITION.
^[A-Z]{3}[0-9]{2}[A-Z0-9]$ matches strings beginning
with three letters, followed by two digits, and ending with a letter or digit.
BIRTH.?(COUNTRY|PLACE)|(COUNTRY|PLACE).*BIRTH matches
strings such as BIRTH COUNTRY,
PATIENT_BIRTH_PLACE, PLACE_OF_BIRTH, and
EMPLOYEE'S COUNTRY OF BIRTH.
See Also:
Regular ExpressionsConfiguring the Exclusion List File (Optional)
You can specify schemas, tables, or columns to exclude from the scan in the Exclusion List file.
Configuring Certificates and Wallets (Optional)
The Discoverer allows usage of Secure External Password Store to retrieve login credentials stored a wallet while connecting. Secure External Password Store can be used to connect to Database without entering the username and password. Secure External Password Store improves the security and allows automation of the execution of the Discoverer.
For increased security, Oracle Database provides Secure Sockets Layer
(SSL) support to encrypt the connection between clients and the server. If SSL (TLS)
encryption is configured on the Database Server, the Discoverer needs to be
configured in order to connect and discover data. Configuration parameters for SSL
can be found in the dbsat.config file.
To establish an SSL connection with the Discoverer, the Database Server sends its certificate, which is stored in its wallet. The client may or may not need a certificate or wallet, depending on the server configuration.
Note:
Configuring certificates and wallets is an optional step and needs to be performed only when using SSL to connect to the Oracle Database server.For more information about configuring certificates and wallets, see Support for SSL in the Oracle Database JDBC Developer's Guide.
Oracle Database Sensitive Data Assessment Report
The Discoverer component is used to generate the Oracle Database Sensitive Data Assessment Report in HTML and CSV formats.
The HTML report is the main report and contains the discovered sensitive data and its categories along with target database information and Discoverer parameters.
The CSV report can be loaded into Oracle Audit Vault and Database Firewall to add sensitive data context to the new Data Privacy reports. For more information about this functionality, see Importing Sensitive Data Into AVDF Repository in the Oracle Audit Vault and Database Firewall Auditor's Guide.
Oracle Database Sensitive Data Assessment Report — High-Level Summary
The Oracle Database Sensitive Data Assessment Report — High-Level Summary section contains the following information:
Table 1-1 Oracle Database Sensitive Data Assessment Report — High-Level Summary
| Section | Description |
|---|---|
| Assessment Time & Date | Displays when the Sensitive Data Assessment report was generated. The DBSAT Discoverer version is also displayed. |
| Database Identity | Displays the details of the database assessed by the Discoverer. |
| Database Version | Displays the version of the database assessed by the Discoverer. |
| Discovery Parameters | Displays the Discovery Parameters specified in the configuration file. For more information about Discovery Parameters, see Configuration Settings. |
The following figure displays the first four tables of the Oracle Database Sensitive Data Assessment Report — High-Level Summary section.
Figure 1-15 Oracle Database Sensitive Data Assessment Report — High-Level Summary
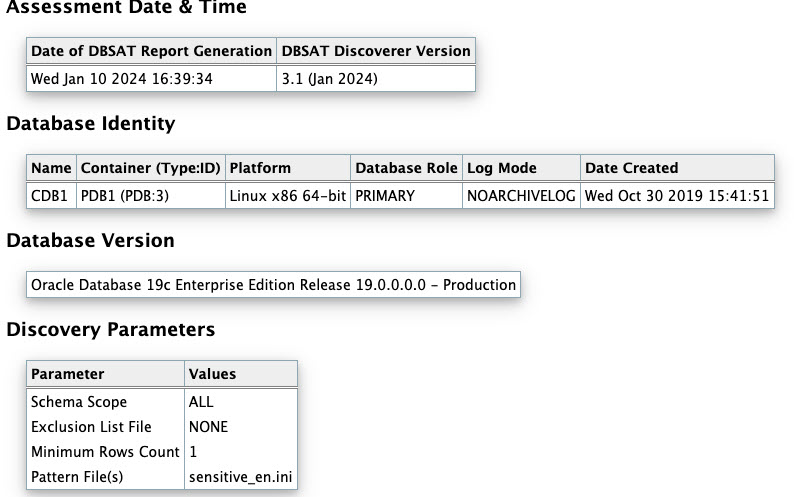
The High-Level Summary section is followed by the Summary section.
Oracle Database Sensitive Data Assessment Report — Summary
The Oracle Database Sensitive Data Assessment Report — Summary section displays information about the number of tables, columns, and rows identified as sensitive data, grouped by Sensitive Category.
The Database Sensitive Data Assessment Report — Summary section contains the following columns:
Table 1-2 Oracle Database Sensitive Data Assessment Report — Summary
| Column Name | Description |
|---|---|
|
Sensitive Category |
Displays the name of the Sensitive Category |
|
# Sensitive Tables |
Displays the number of tables detected that contain sensitive data |
|
# Sensitive Columns |
Displays the number of columns detected in the tables that contain sensitive data |
|
# Sensitive Rows |
Displays the number of rows detected in the tables that contain sensitive data |
The following figure displays the information displayed in the Oracle Database Sensitive Data Assessment Report — Summary section:
Figure 1-16 Oracle Database Sensitive Data Assessment Report — Summary
Note:
A single database table could contain columns or column comments that match more than one Sensitive Category, causing a higher number to be displayed in the# Sensitive Tables and # Sensitive Rows columns. However, the Total row displays the unique number of tables and rows identified as sensitive data.
For more information about configuring Sensitive Categories, see Pattern File Configuration (Optional).
The Summary section is followed by the Sensitive Data section.
Oracle Database Sensitive Data Assessment Report — Sensitive Data
The Oracle Database Sensitive Data Assessment Report — Sensitive Data section displays information about the schemas containing sensitive data.
The Oracle Database Sensitive Data Assessment Report — Sensitive Data section contains the following information:
Table 1-3 Oracle Database Sensitive Data Assessment Report — Sensitive Data
| Section | Description |
|---|---|
| Risk Level(s) | Displays the Risk Level(s) of the sensitive data identified in the schema of the database assessed by the Discoverer. |
| Summary | Displays a summary of the occurrence of sensitive data in the schema. |
| Location | Displays the names of the schemas containing sensitive data. |
The following figure shows the information displayed in the Oracle Database Sensitive Data Assessment Report — Sensitive Data section.
Figure 1-17 Oracle Database Sensitive Data Assessment Report — Sensitive Data
Findings belonging to each risk level are followed by a set of recommendations to secure the sensitive data. These recommendations lists various controls based on the Risk Levels, namely HIGH, MEDIUM, and LOW.
The following figure shows the information displayed in the Risk Level: High Risk section.
Figure 1-18 Sensitive categories grouped by Risk Level
Each Risk Level section is followed by a list of the tables detected that contain sensitive data. The following information is displayed:
Table 1-4 Tables Detected within Sensitive Category: <Sensitive Category Name>
| Name | Description |
|---|---|
|
Risk Level |
Displays the Risk Level |
|
Summary |
Displays a summary of the sensitive category data detected |
|
Location |
Displays the names of the tables that contain sensitive data |
The following figure shows the information displayed in the Tables Detected within each Sensitive Category: <Sensitive Category Name> subsection.
Figure 1-19 Tables Detected within Sensitive Category: <Sensitive Category Name>
The Sensitive Data section is followed by the Schema View section.
Oracle Database Sensitive Data Assessment Report — Schema View
The Oracle Database Sensitive Data Assessment Report — Schema View section displays information about the schemas, tables, columns, and rows containing sensitive data. The Sensitive Category is also displayed.
The Oracle Database Sensitive Data Assessment Report — Summary section contains the following columns:
| Column Name | Description |
|---|---|
|
Schema |
Displays the name of the schema |
|
Table Name |
Displays the name of the table |
|
Columns |
Displays the number of columns in the table |
|
Sensitive Columns |
Displays the number of columns detected that contain sensitive data |
|
Rows |
Displays the number of rows in the table |
|
Sensitive Category |
Displays the category of sensitive data detected in each column |
The following figure highlights the information displayed in the Oracle Database Sensitive Data Assessment Report — Schema View section:
Figure 1-20 Oracle Database Sensitive Data Assessment Report — Schema View
The Schema View section is followed by the Sensitive Column Details section.
Oracle Database Sensitive Data Assessment Report — Sensitive Column Details
The Oracle Database Sensitive Data Assessment Report — Sensitive Column Details section displays information about the columns containing sensitive data. The Sensitive Category and Type are also displayed.
| Column Name | Description |
|---|---|
|
Schema Name |
Displays the name of the schema |
|
Table Name |
Displays the name of the table |
|
Column Name |
Displays the name of the column |
|
Column Comment |
Displays the column comment |
|
Sensitive Category |
Displays the category of sensitive data detected in each column |
|
Sensitive Type |
Displays the type of sensitive data detected in each column |
|
Risk Level |
Displays the risk level |
The following figure displays the information displayed in the Oracle Database Sensitive Data Assessment Report — Sensitive Column Details section.
Figure 1-21 Oracle Database Sensitive Data Assessment Report — Sensitive Column Details
Best Practices
Collector - OS Commands
As a general best practice, you should not put username/password credentials in
cleartext in an application or file. When you
provide the password on the command line while
executing dbsat collect, someone
can retrieve credentials, either using history or
executing the ps Unix command or
any similar Windows command. Therefore, Oracle
recommends that you enter the password when
prompted.
Collector - Database User Account
It's advisable that you run DBSAT collect and discoverer with a user that has the minimum set of privileges required to execute the assessments. The user shall also have a strong password. This will help reduce the attack surface and the potential impact of stolen DBSAT user account credentials, account misuse, and human error.
You can create a user with the required minimum privileges to run the Oracle Database Security Assessment Tool with the script provided in the pre-requisites section.
Documentation Accessibility
For information about Oracle's commitment to accessibility, visit the Oracle Accessibility Program website at http://www.oracle.com/pls/topic/lookup?ctx=acc&id=docacc.
Access to Oracle Support
Oracle customer access to and use of Oracle support services will be pursuant to the terms and conditions specified in their Oracle order for the applicable services.
Appendix A
Improved DBSAT Target Specific Checks and Recommendations
DBSAT can be run against on-premises databases, Autonomous Databases (Serverless and Dedicated) and Oracle Cloud DBCS (DBSystems EE/HP/EP). Some findings will execute different checks and provide specific recommendations for these databases. The table below highlights which findings were improved.
Figure 1-22 DBSAT Target Specific Checks and Recommendations
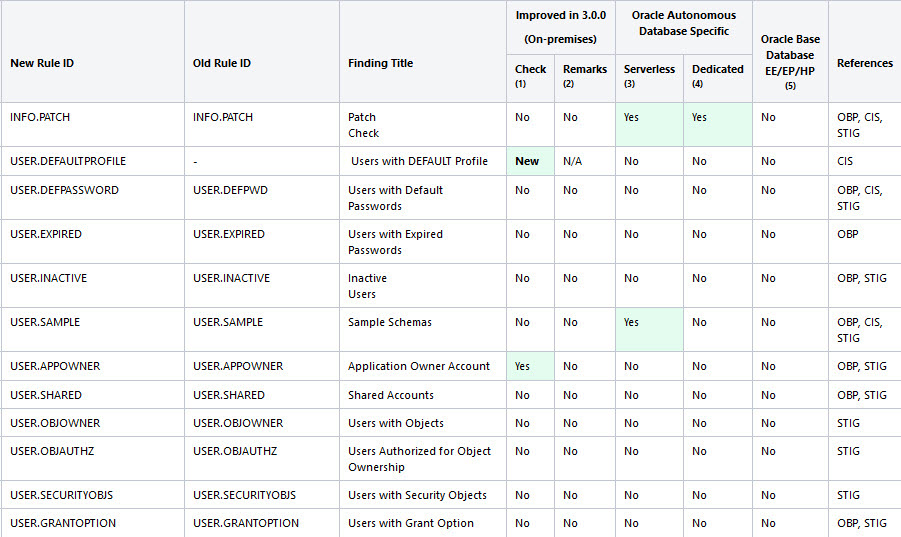
Figure 1-23 DBSAT Target Specific Checks and Recommendations (continued)
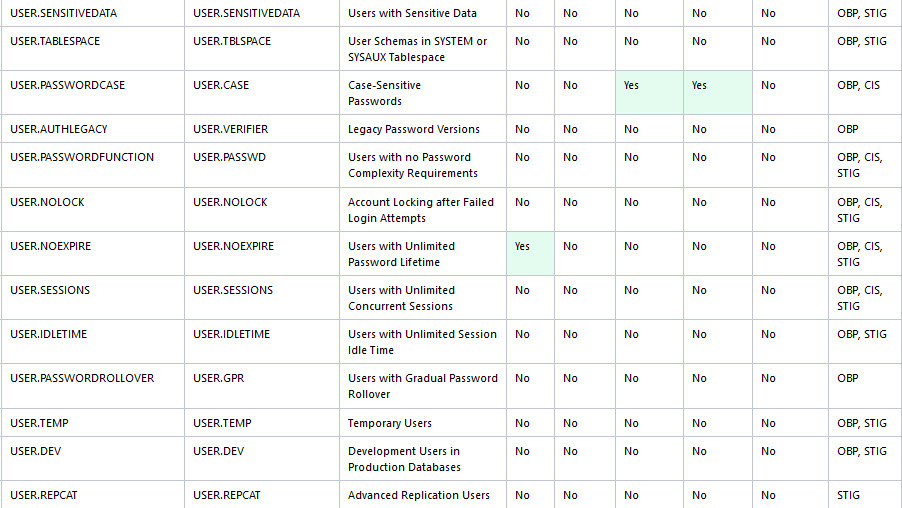
Figure 1-24 DBSAT Target Specific Checks and Recommendations (continued)
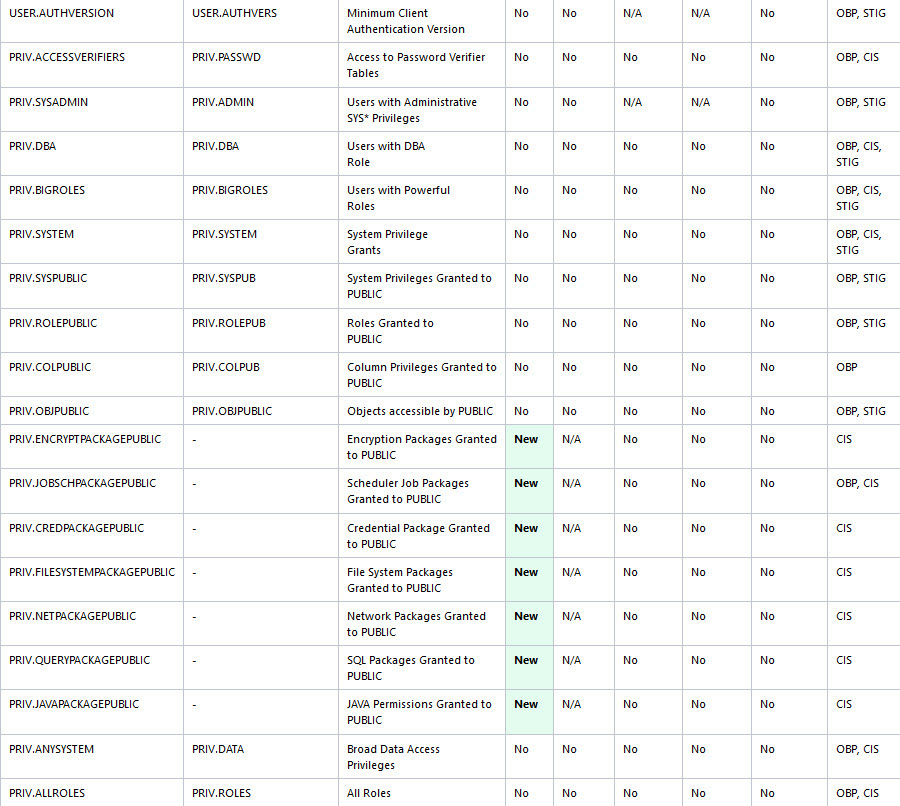
Figure 1-25 DBSAT Target Specific Checks and Recommendations (continued)
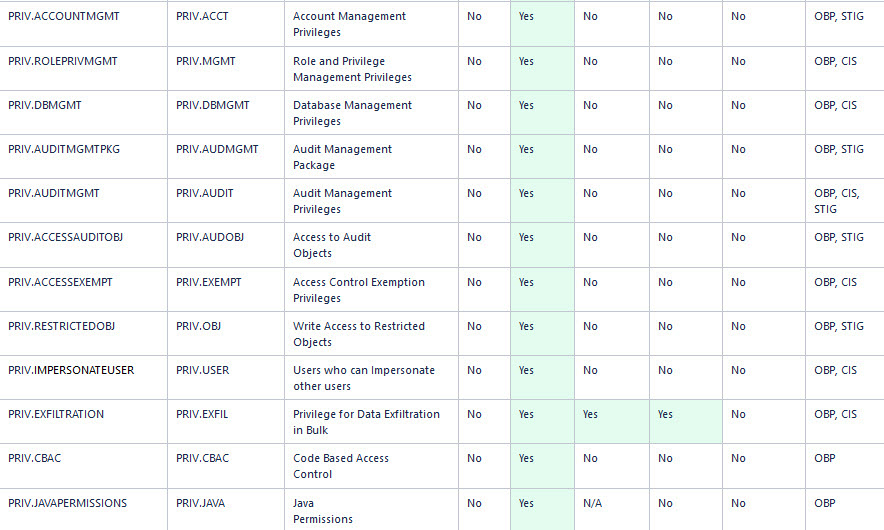
Figure 1-26 DBSAT Target Specific Checks and Recommendations (continued)
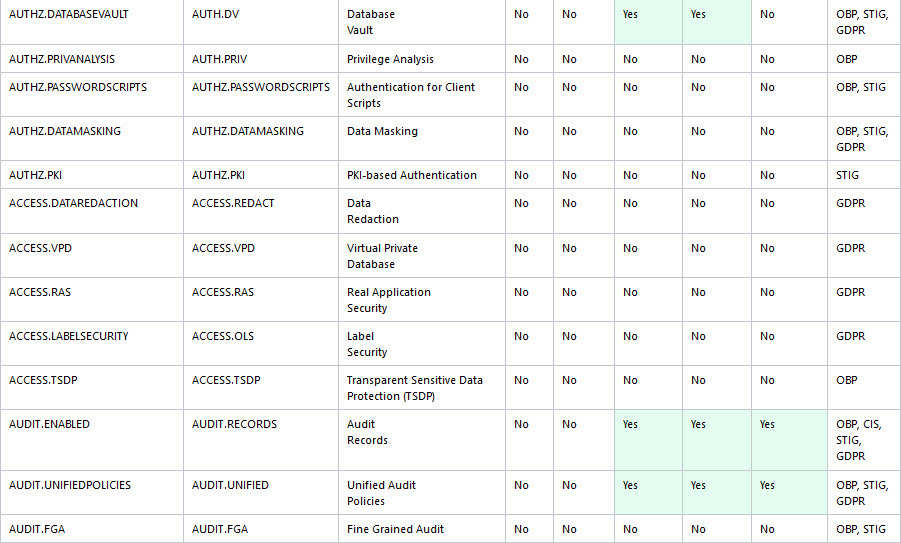
Figure 1-27 DBSAT Target Specific Checks and Recommendations (continued)
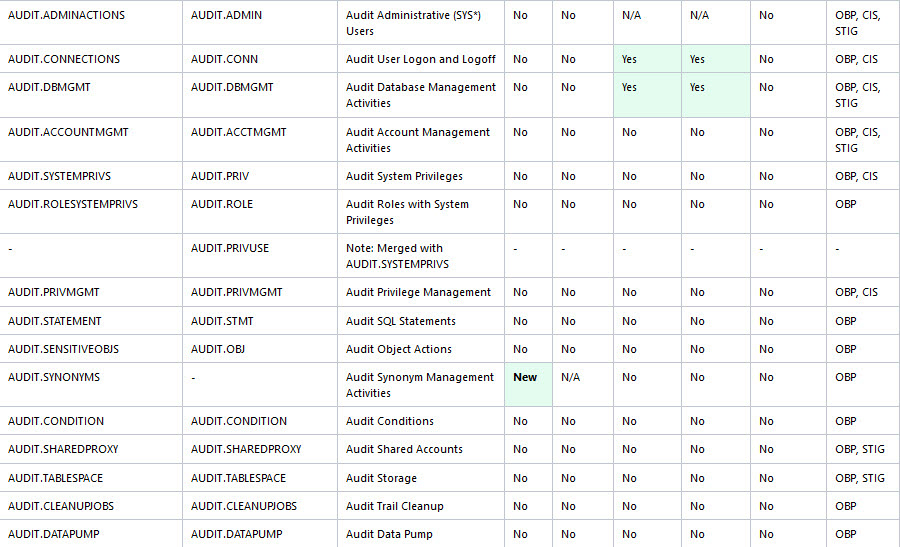
Figure 1-28 DBSAT Target Specific Checks and Recommendations (continued)
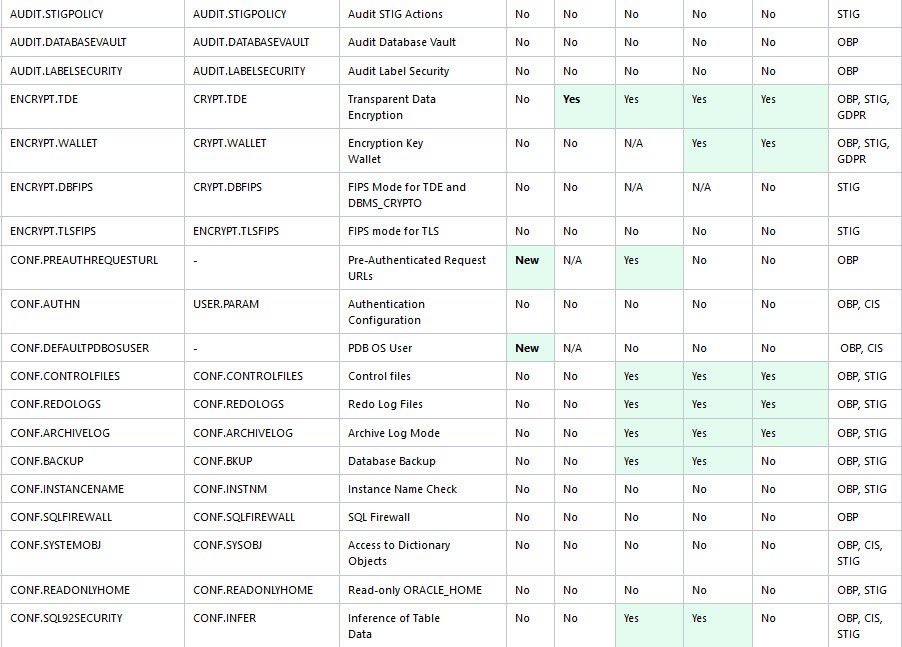
Figure 1-29 DBSAT Target Specific Checks and Recommendations (continued)
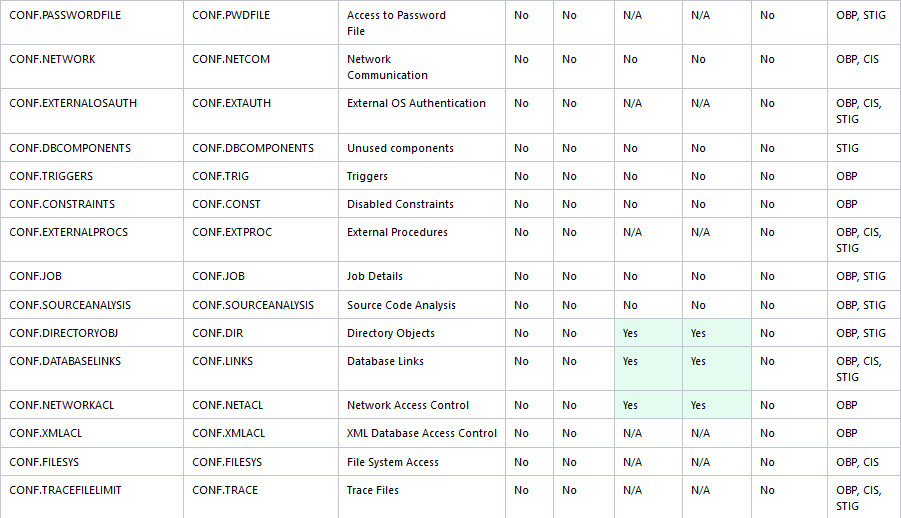
Figure 1-30 DBSAT Target Specific Checks and Recommendations (continued)
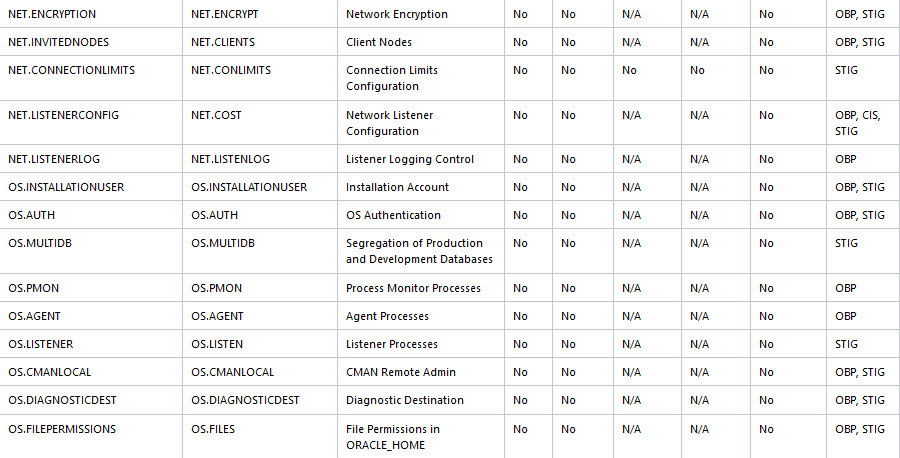
Figure 1-31 DBSAT Target Specific Checks and Recommendations (continued)
Appendix B
You can troubleshoot Oracle Database Security Assessment Tool by using diagnostics and log files.
B.1 Enabling DBSAT Diagnostics to diagnose Oracle Database Security Assessment Tool Errors
Output diagnostics, which the DBSAT generates, capture vital information to help you debug errors.
By default, DBSAT suppresses errors that do not impact the report
execution. To find details on errors that might affect your report
generation, please run dbsat report with the -d
option.
Example of a run with -d:
$ ./dbsat report -n -d orcl
Database Security Assessment Tool version 3.1 (Mar 2023)
This tool is intended to assist you in securing your Oracle database system. You are solely responsible for your system and the effect and results of the execution of this tool (including, without limitation, any damage or data loss). Further, the output generated by this tool may include potentially sensitive system configuration data and information that could be used by a skilled attacker to penetrate your system. You are solely responsible for ensuring that the output of this tool, including any generated reports, is handled in accordance with your company’s policies.
Traceback (most recent call last): File “<iostream>“, line 11865, in <module> File “<iostream>“, line 1161, in sec_feature_usage IndexError: index out of range: 1
DBSAT Reporter ran successfully.Example of a standard run:
$ ./dbsat report -n orcl
Database Security Assessment Tool version 3.0
This tool is intended to assist you in securing your Oracle database system. You are solely responsible for your system and the effect and results of the execution of this tool (including, without limitation, any damage or data loss). Further, the output generated by this tool may include potentially sensitive system configuration data and information that could be used by a skilled attacker to penetrate your system. You are solely responsible for ensuring that
the output of this tool, including any generated reports, is handled in accordance with your company’s policies.
DBSAT Reporter ran successfully.If execute on package
SYS.DBMS_SQL was revoked from
PUBLIC you can encounter this
issue.
$ ./dbsat report -a -n orcl
Database Security Assessment Tool version 3.0
This tool is intended to assist in you in securing your Oracle database system. You are solely responsible for your system and the effect and results of the execution of this tool (including, without limitation, any damage or data loss). Further, the output generated by this tool may include potentially sensitive system configuration data and information that could be used by a skilled attacker to penetrate your system. You are solely responsible for ensuring that the output of this tool, including any generated reports, is handled in accordance with yourcompany's policies.
... Unable to process input file: orcl.json No JSON object could be decoded Error: Unexpected error occurred while running DBSAT Reporter.To avoid this error, grant execute privilege on
DBMS_SQL to the DBSAT database user (and
not use PUBLIC privilege) used in dbsat collect
<user>@<service_name>
<output-file>
SQL> grant execute on sys.dbms_sql to <user> ;Run dbsat collect again to ensure the
data is collected appropriately and then run the
report.
./dbsat collect <user>@<service_name> <output-file>
./dbsat report <output-file>Note: make sure JSON is not invalid or corrupt. Review the json file and/or run the collector.
Occasionally, the source of the issue affecting the DBSAT report's successful execution is present in the collector-generated file. As a troubleshooting step, you can open the file (extract from the zip file) generated by DBSAT collect and search the file for errors.
AIX default shell is the Korn shell (ksh). DBSAT
needs to run under the bash shell. You can either change it to
bash or install it. DBSAT fails to run
under other shells. As an example, if you do not have
bash shell installed on AIX, and you try to
run DBSAT, you can encounter the
following:
oraprod>./dbsat
ksh: ./dbsat: not found
oraprod>pwd
/home/oraprod/dbsat300At this point, you can install bash on
AIX or run DBSAT collect remotely. You can execute DBSAT from
another server with bash (e.g., a linux server),
reaching the database running on
AIX:
./dbsat collect <user>@<service_name> <output-file>When collecting from a remote server, DBSAT will not include Operating System-related findings.
Appendix C
Attribution for Third-Party Licenses
For third party technology that you receive from Oracle in binary form which is licensed under an open source license that gives you the right to receive the source code for that binary, you can obtain a copy of the applicable source code from this page. If the source code for the technology was not provided to you with the binary, you can also receive a copy of the source code on physical media by submitting a written request to:
Oracle America, Inc. Attn: Associate General Counsel Development and Engineering Legal 500 Oracle Parkway, 10th Floor Redwood Shores, CA 94065
Or, you may send an email to Oracle using this form. Your request should include:
The name of the component or binary file(s) for which you are requesting the source code The name and version number of the Oracle product The date you received the Oracle product Your name Your company name (if applicable) Your return mailing address and email A telephone number in the event we need to reach you
We may charge you a fee to cover the cost of physical media and processing. Your request must be sent (i) within three (3) years of the date you received the Oracle product that included the component or binary file(s) that are the subject of your request, or (ii) in the case of code licensed under the GPL v3, for as long as Oracle offers spare parts or customer support for that product model
XlsxWriter, Version: 2.0
Copyright (c) 2013-2020, John McNamara
<jmcnamara@cpan.org>
All rights reserved.
Redistribution and use in source and binary forms, with or without modification, are permitted provided that the following conditions are met:
- Redistributions of source code must retain the above copyright notice, this list of conditions and the following disclaimer.
- Redistributions in binary form must reproduce the above copyright notice, this list of conditions and the following disclaimer in the documentation and/or other materials provided with the distribution.
THIS SOFTWARE IS PROVIDED BY THE COPYRIGHT HOLDERS AND CONTRIBUTORS "AS IS" AND ANY EXPRESS OR IMPLIED WARRANTIES, INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE ARE DISCLAIMED. IN NO EVENT SHALL THE COPYRIGHT OWNER OR CONTRIBUTORS BE LIABLE FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY, OR CONSEQUENTIAL DAMAGES (INCLUDING, BUT NOT LIMITED TO, PROCUREMENT OF SUBSTITUTE GOODS OR SERVICES; LOSS OF USE, DATA, OR PROFITS; OR BUSINESS INTERRUPTION) HOWEVER CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER IN CONTRACT, STRICT LIABILITY, OR TORT (INCLUDING NEGLIGENCE OR OTHERWISE) ARISING IN ANY WAY OUT OF THE USE OF THIS SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY OF SUCH DAMAGE.
The views and conclusions contained in the software and documentation are those of the authors and should not be interpreted as representing official policies, either expressed or implied, of the FreeBSD Project.
TERMS AND CONDITIONS FOR ACCESSING OR OTHERWISE USING JYTHON
PYTHON SOFTWARE FOUNDATION LICENSE VERSION 2
- This LICENSE AGREEMENT is between the Python Software Foundation ("PSF"), and the Individual or Organization ("Licensee") accessing and otherwise using this software ("Jython") in source or binary form and its associated documentation.
- Subject to the terms and conditions of this License Agreement, PSF hereby grants Licensee a nonexclusive, royalty-free, world-wide license to reproduce, analyze, test, perform and/or display publicly, prepare derivative works, distribute, and otherwise use Jython alone or in any derivative version, provided, however, that PSF's License Agreement and PSF's notice of copyright, i.e., "Copyright (c) 2007 Python Software Foundation; All Rights Reserved" are retained in Jython alone or in any derivative version prepared by Licensee.
- In the event Licensee prepares a derivative work
that is based on or incorporates Jython or any part thereof,
and wants to make the derivative work available to others as
provided herein, then Licensee hereby agrees to include in
any such work a brief summary of the changes made to
Jython.
The following changes were made:
- Updated the Third Party package guava@31.0.1-jre to guava@32.1.2-jre
- Removed pip@19.1 and setuptools@41.0.1 from binary distribution.
- PSF is making Jython available to Licensee on an "AS IS" basis. PSF MAKES NO REPRESENTATIONS OR WARRANTIES, EXPRESS OR IMPLIED. BY WAY OF EXAMPLE, BUT NOT LIMITATION, PSF MAKES NO AND DISCLAIMS ANY REPRESENTATION OR WARRANTY OF MERCHANTABILITY OR FITNESS FOR ANY PARTICULAR PURPOSE OR THAT THE USE OF JYTHON WILL NOT INFRINGE ANY THIRD PARTY RIGHTS.
- PSF SHALL NOT BE LIABLE TO LICENSEE OR ANY OTHER USERS OF JYTHON FOR ANY INCIDENTAL, SPECIAL, OR CONSEQUENTIAL DAMAGES OR LOSS AS A RESULT OF MODIFYING, DISTRIBUTING, OR OTHERWISE USING JYTHON, OR ANY DERIVATIVE THEREOF, EVEN IF ADVISED OF THE POSSIBILITY THEREOF.
- This License Agreement will automatically terminate upon a material breach of its terms and conditions.
- Nothing in this License Agreement shall be deemed to create any relationship of agency, partnership, or joint venture between PSF and Licensee. This License Agreement does not grant permission to use PSF trademarks or trade name in a trademark sense to endorse or promote products or services of Licensee, or any third party.
- By copying, installing or otherwise using Jython, Licensee agrees to be bound by the terms and conditions of this License Agreement.
PYTHON SOFTWARE FOUNDATION LICENSE VERSION 2.1
- Redistributions of source code must retain the above copyright notice, this list of conditions and the following disclaimer.
- Redistributions in binary form must reproduce the above copyright notice, this list of conditions and the following disclaimer in the documentation and/or other materials provided with the distribution.
- Neither the name of the Jython Developers nor the names of its contributors may be used to endorse or promote products derived from this software without specific prior written permission.
Note:
THIS SOFTWARE IS PROVIDED BY THE COPYRIGHT HOLDERS AND CONTRIBUTORS ``AS IS'' AND ANY EXPRESS OR IMPLIED WARRANTIES, INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE ARE DISCLAIMED. IN NO EVENT SHALL THE REGENTS OR CONTRIBUTORS BE LIABLE FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY, OR CONSEQUENTIAL DAMAGES (INCLUDING, BUT NOT LIMITED TO, PROCUREMENT OF SUBSTITUTE GOODS OR SERVICES; LOSS OF USE, DATA, OR PROFITS; OR BUSINESS INTERRUPTION) HOWEVER CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER IN CONTRACT, STRICT LIABILITY, OR TORT (INCLUDING NEGLIGENCE OR OTHERWISE) ARISING IN ANY WAY OUT OF THE USE OF THIS SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY OF SUCH DAMAGE.
JPython version 1.1.x
- This LICENSE AGREEMENT is between the Corporation for National Research Initiatives, having an office at 1895 Preston White Drive, Reston, VA 20191 ("CNRI"), and the Individual or Organization ("Licensee") accessing and using JPython version 1.1.x in source or binary form and its associated documentation as provided herein ("Software").
- Subject to the terms and conditions of this License Agreement,
CNRI hereby grants Licensee a non-exclusive,
non-transferable, royalty-free, world-wide license to
reproduce, analyze, test, perform and/or display publicly,
prepare derivative works, distribute, and otherwise use the
Software alone or in any derivative version, provided,
however, that CNRI's License Agreement and CNRI's notice of
copyright, i.e., "Copyright (c)1996-1999 Corporation for
National Research Initiatives; All Rights Reserved" are both
retained in the Software, alone or in any derivative version
prepared by Licensee.
Subject to the terms and conditions of this License Agreement, CNRI hereby grants Licensee a non-exclusive, non-transferable, royalty-free, world-wide license to reproduce, analyze, test, perform and/or display publicly, prepare derivative works, distribute, and otherwise use the Software alone or in any derivative version, provided, however, that CNRI's License Agreement and CNRI's notice of copyright, i.e., "Copyright (c)1996-1999 Corporation for National Research Initiatives; All Rights Reserved" are both retained in the Software, alone or in any derivative version prepared by Licensee.
- In the event Licensee prepares a derivative work that is based on or incorporates the Software or any part thereof, and wants to make the derivative work available to the public as provided herein, then Licensee hereby agrees to indicate in any such work, in a prominently visible way, the nature of the modifications made to CNRI's Software.
- Licensee may not use CNRI trademarks or trade name, including JPython or CNRI, in a trademark sense to endorse or promote products or services of Licensee, or any third party. Licensee may use the mark JPython in connection with Licensee's derivative versions that are based on or incorporate the Software, but only in the form "JPython-based ___________________," or equivalent.
- CNRI is making the Software available to Licensee on an "AS IS" basis. CNRI MAKES NO REPRESENTATIONS OR WARRANTIES, EXPRESS OR IMPLIED. BY WAY OF EXAMPLE, BUT NOT LIMITATION, CNRI MAKES NO AND DISCLAIMS ANY REPRESENTATION OR WARRANTY OF MERCHANTABILITY OR FITNESS FOR ANY PARTICULAR PURPOSE OR THAT THE USE OF THE SOFTWARE WILL NOT INFRINGE ANY THIRD PARTY RIGHTS.
- CNRI SHALL NOT BE LIABLE TO LICENSEE OR OTHER USERS OF THE SOFTWARE FOR ANY INCIDENTAL, SPECIAL OR CONSEQUENTIAL DAMAGES OR LOSS AS A RESULT OF USING, MODIFYING OR DISTRIBUTING THE SOFTWARE, OR ANY DERIVATIVE THEREOF, EVEN IF ADVISED OF THE POSSIBILITY THEREOF. SOME STATES DO NOT ALLOW THE LIMITATION OR EXCLUSION OF LIABILITY SO THE ABOVE DISCLAIMER MAY NOT APPLY TO LICENSEE.
- This License Agreement may be terminated by CNRI (i) immediately upon written notice from CNRI of any material breach by the Licensee, if the nature of the breach is such that it cannot be promptly remedied; or (ii) sixty (60) days following notice from CNRI to Licensee of a material remediable breach, if Licensee has not remedied such breach within that sixty-day period.
- This License Agreement shall be governed by and interpreted in all respects by the law of the State of Virginia, excluding conflict of law provisions. Nothing in this Agreement shall be deemed to create any relationship of agency, partnership, or joint venture between CNRI and Licensee.
- By clicking on the "ACCEPT" button where indicated, or by installing, copying or otherwise using the Software, Licensee agrees to be bound by the terms and conditions of this License Agreement.
Oracle Database Database Security Assessment Tool User Guide, Release 3.1.0
F90720-05
May 2024
Primary Author: Dominique Jeunot
Contributing Author: Usha Krishnamurthy
Contributor: Anant Bhasu, Anurag Barman, Gopal Mulagund, Chetankumar Vithlani, Scott Rotondo, Shyamsundar KG, Vishnu Priya Matha, Vivek PV, Pedro Lopez