Note:
- This tutorial requires access to Oracle Cloud. To sign up for a free account, see Get started with Oracle Cloud Infrastructure Free Tier.
- It uses example values for Oracle Cloud Infrastructure credentials, tenancy, and compartments. When completing your lab, substitute these values with ones specific to your cloud environment.
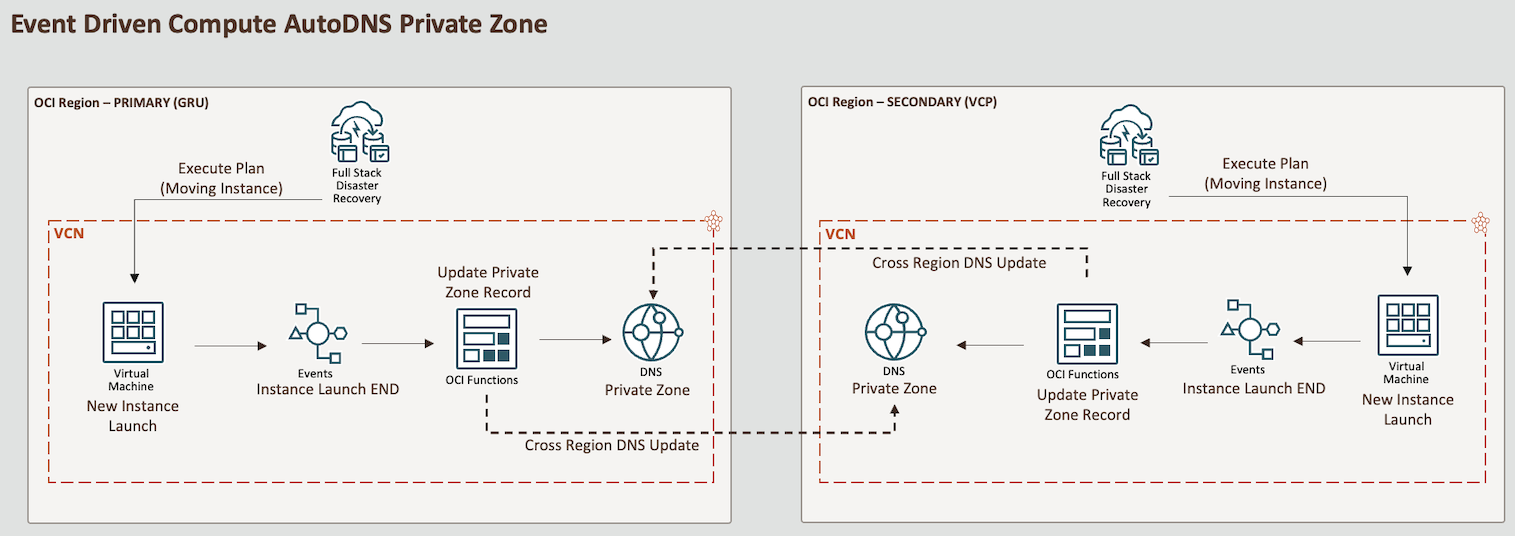
Use OCI Events Service Rule to Update Cross Region DNS Records for a Private Zone with OCI Functions
Introduction
In this tutorial, we will learn how to automatically update Domain Name System (DNS) records for compute instances in a private zone in both regions when a new compute instance is created, or when it is moved during a switchover scenario in an Oracle Cloud Infrastructure Full Stack Disaster Recovery (OCI Full Stack DR) plan. This tutorial covers two specific OCI services.
-
OCI Events Service Rule: A service that triggers automated responses to changes and events within your OCI environment.
-
OCI Functions: A serverless computing service that allows you to execute code in response to events without managing infrastructure.
This use case was initially envisioned for use during an OCI Full Stack DR switchover plan, where instances are moved between regions. Essentially, the Disaster Recovery (DR) switchover process involves creating a new instance in the new region and then terminating the instance in the previous region. Based on this scenario, this tutorial focuses on the Launch - Instance End event type, which triggers an OCI Functions to update the DNS records for private zones in both regions.
This solution can also serve as a default OCI DNS private zone automation. It creates a DNS record for each new instance created in the selected compartment or any other filters you specify to identify the target instances. For more information, see Services that Produce Events.
High Level Architecture
Note:
This tutorial is designed solely for educational and study purposes. It provides an environment for learners to experiment and gain practical experience in a controlled setting. It is crucial to note that the security configurations and practices employed in this tutorial might not be suitable for real-world scenarios.
Security considerations for real-world applications are often far more complex and dynamic. Therefore, before implementing any of the techniques or configurations demonstrated here in a production environment, it is essential to conduct a comprehensive security assessment and review. This review should encompass all aspects of security, including access control, encryption, monitoring, and compliance, to ensure that the system aligns with the organization’s security policies and standards.
Security should always be a top priority when transitioning from a lab environment to a real-world deployment.
Objectives
-
Set up an OCI Event Service rule to trigger a provided OCI Functions. This function will update a DNS private zone record in two regions whenever a new instance is created in the selected compartment.
Note: This tutorial will not cover the set up of OCI Full Stack DR. Instead, it will focus on automating DNS private zone in two or more regions. For more information, see Use OCI Full Stack Disaster Recovery Service with Oracle WebLogic Server domains.
Prerequisites
-
OCI Environment
-
OCI account with admin permissions.
-
A compartment to create your resources.
Note: Note the compartment name and compartment ID.
-
List of OCI DNS private zone Oracle Cloud Identifier (OCIDs) where newly launched instances will have a DNS record in each region you may need. In this tutorial, we have two DNS private zones: one for GRU region and one for VCP region.
-
-
Local Machine Environment
-
Set up local Oracle Cloud Infrastructure Command Line Interface (OCI CLI). For more information, see Installing the OCI CLI.
-
Local Docker to be able to build images. If you are using Oracle Linux, see Docker: Install Docker on Oracle Linux 8 (OL8).
-
Local Fn Project CLI to be able to deploy your function to OCI. For more information, see Installing the Fn Project CLI.
-
Task 1: Set up Dynamic Groups
Go to your domain, click Dynamic Groups and create the following groups.
Dynamic Group Name: MyFunctions.
ALL {resource.type = 'fnfunc', resource.compartment.id = 'pasteYourCompartmentOCID'}
Task 2: Create Policies
Go to Policies and create the following policies.
Policy Name: FunctionsPolicies.
Allow dynamic-group MyFunctions to read repos in compartment YOUR-COMPARTMENT-NAME
Allow dynamic-group MyFunctions to use instance-family in compartment YOUR-COMPARTMENT-NAME
Allow dynamic-group MyFunctions to read app-catalog-listing in compartment YOUR-COMPARTMENT-NAME
Allow dynamic-group MyFunctions to use volume-family in compartment YOUR-COMPARTMENT-NAME
Allow dynamic-group MyFunctions to use virtual-network-family in compartment YOUR-COMPARTMENT-NAME
Allow dynamic-group MyFunctions to manage dns-records in compartment YOUR-COMPARTMENT-NAME
Allow dynamic-group MyFunctions to use dns-zones in compartment YOUR-COMPARTMENT-NAME
Task 3: Create OCI Container Registry
-
Go to Developer Services, click Container registry and create a private repository for the Fn image.
Repository Name:
lab/fnpy-event-dns-update.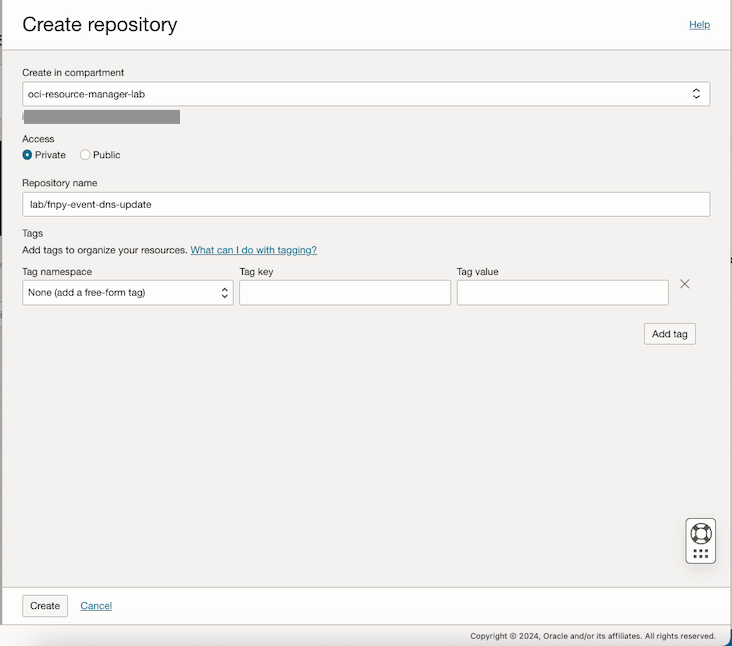
-
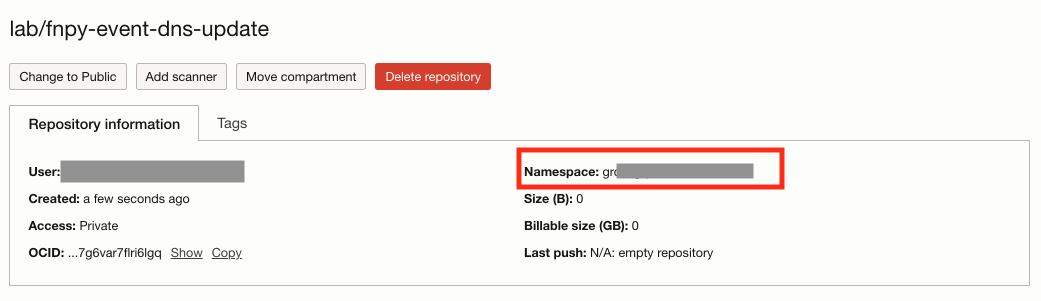
Check the repositories and note the Namespace.
-
Open the terminal shell where you have OCI CLI and Docker installed, and log in to the registry. Check the correct URL for your region. In this tutorial, we are using Brazil East (Sao Paulo) region where the registry URL is
gru.ocir.io.docker login gru.ocir.io Username: <your container namespace>/youruser Password: YOUR_AUTH_TOKEN_CREATED_EARLIER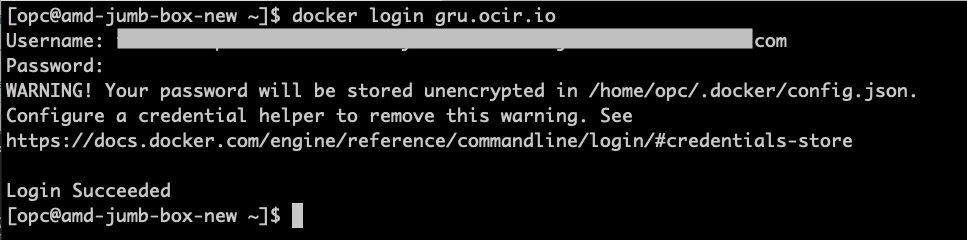
Task 4: Create the Python OCI Functions to Update the DNS on Private Zones
-
Go to the OCI Console and click Developer Services. Under Functions, click Applications and Create application.
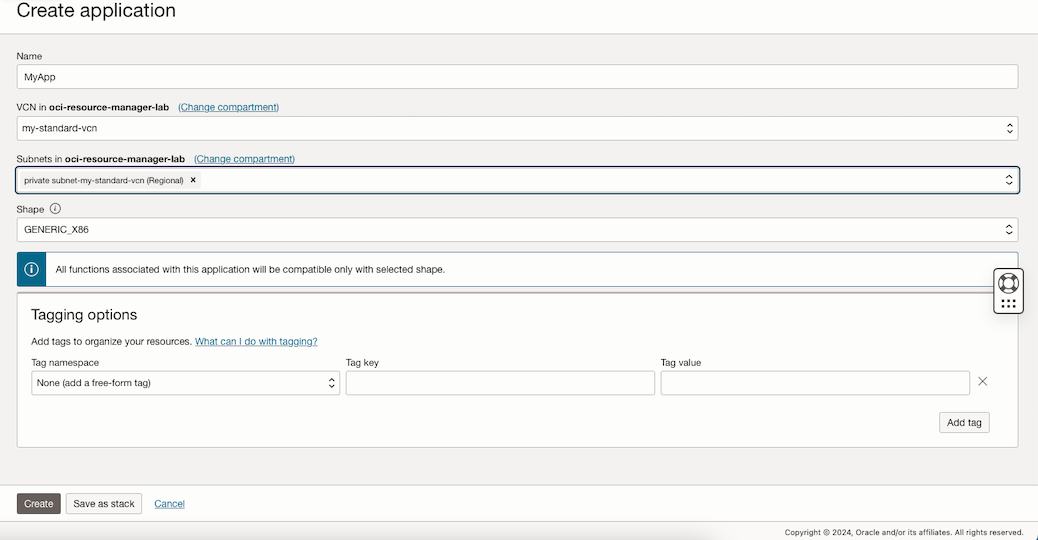
-
Create the configuration for the affected OCI DNS private zones.
Note: This configuration variable specifies the private zones OCIDs to be updated. You can list multiple OCIDs, separated by commas.
Secret Name Value TARGET_ZONES_OCID Set the list of PRIVATE ZONES OCIDs as comma-separated In this tutorial, we will set two private zones: one for the GRU region and one for the VCP region.
Sample:
ocid1.dns-zone.oc1.sa-saopaulo-1.xxxxocid1.dns-zone.oc1.sa-vinhedo-1.xxx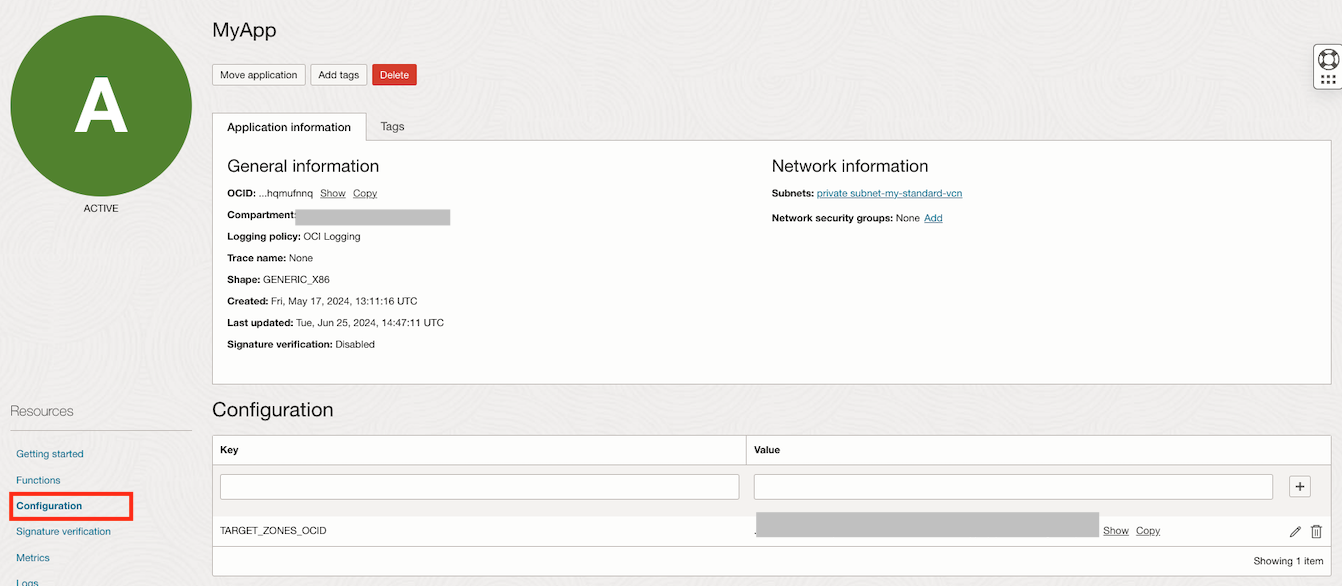
-
Go to the terminal shell where you have Docker, OCI CLI, Fn Project CLI installed and run the following commands to initialize the function.
Note: If you followed the tasks, your Docker log in command has already been executed by now, if not, proceed with the Docker log in Task 3.3.
mkdir lab cd lab fn create context oci-cloud --provider oracle fn use context oci-cloud fn update context oracle.compartment-id PASTE_YOUR_COMPARTMENT_OCID fn update context api-url https://functions.sa-saopaulo-1.oraclecloud.com fn update context registry gru.ocir.io/PASTE_YOUR_REGISTRY_NAMESPACE/lab fn init --runtime python fnpy-event-dns-update cd fnpy-event-dns-update ls -lrtNote: In this tutorial, we are using Brazil East(Sao Paulo) region, if you are using a different region, you need to change the
api-urlandregistrylocations.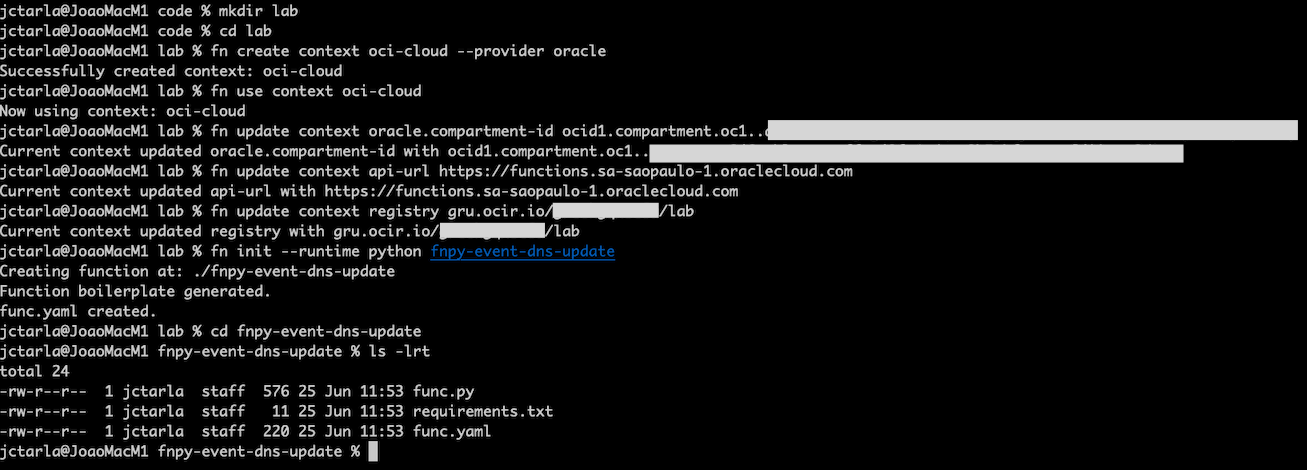
The
initcommand will create a hello world function onfunc.py. We will overwrite this code. -
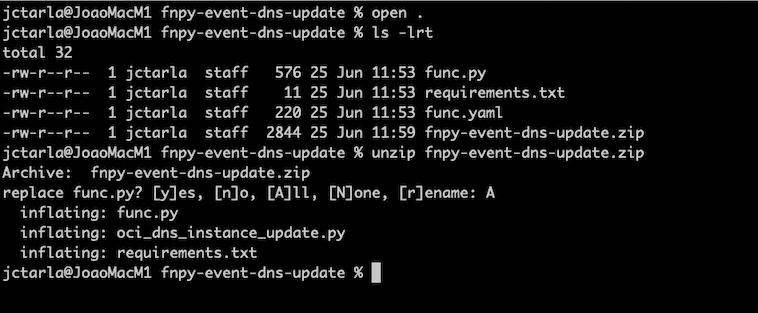
Get the Python function sample code from here: fnpy-event-dns-update.zip, unzip it and overwrite the files during the
initcommand.-
Copy the zip file into the lab directory where you executed the
fn initcommand and check for the files in the directory.ls -lrt -
Unzip the file and overwrite the existing files.
unzip fnpy-event-dns-update.zip
-
-
Build the new code and deploy the function.
ls -lrt fn deploy --app MyApp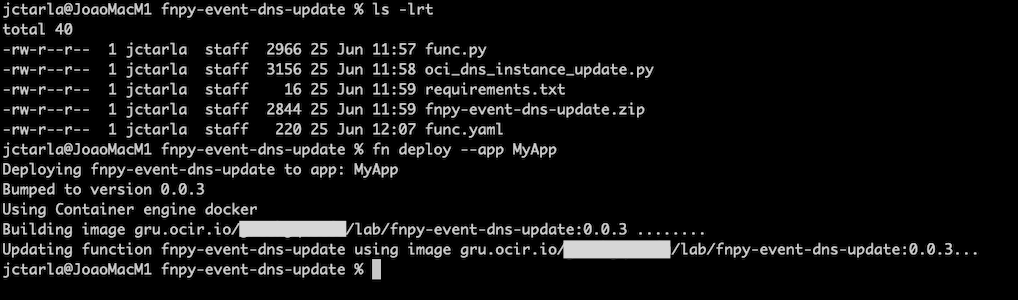
Task 5: Create the OCI Events Service Rule
-
Go to the OCI Console and click Observability & Management. Under Events Service, select Rules and click Create Rule.
-
Enter the following information.
- Name: Enter
MyAutoDNSRule. - Rule Conditions:
- Condition 1:
- Condition: Select
Event Type. - Service Name: Select
Compute. - Event Type: Select
Instance - Launch End.
- Condition: Select
- Condition 2:
- Condition: Select
Attribute. - Attribute Name: Select
compartmentId. - Attribute Values: Enter your compartment OCID.
- Condition: Select
- Condition 1:
- Actions:
- Action Type: Select
Functions. - Function Compartment: Select your compartment.
- Function Application: Select
MyApp. - Function: Select
fnpy-event-dns-update.
- Action Type: Select
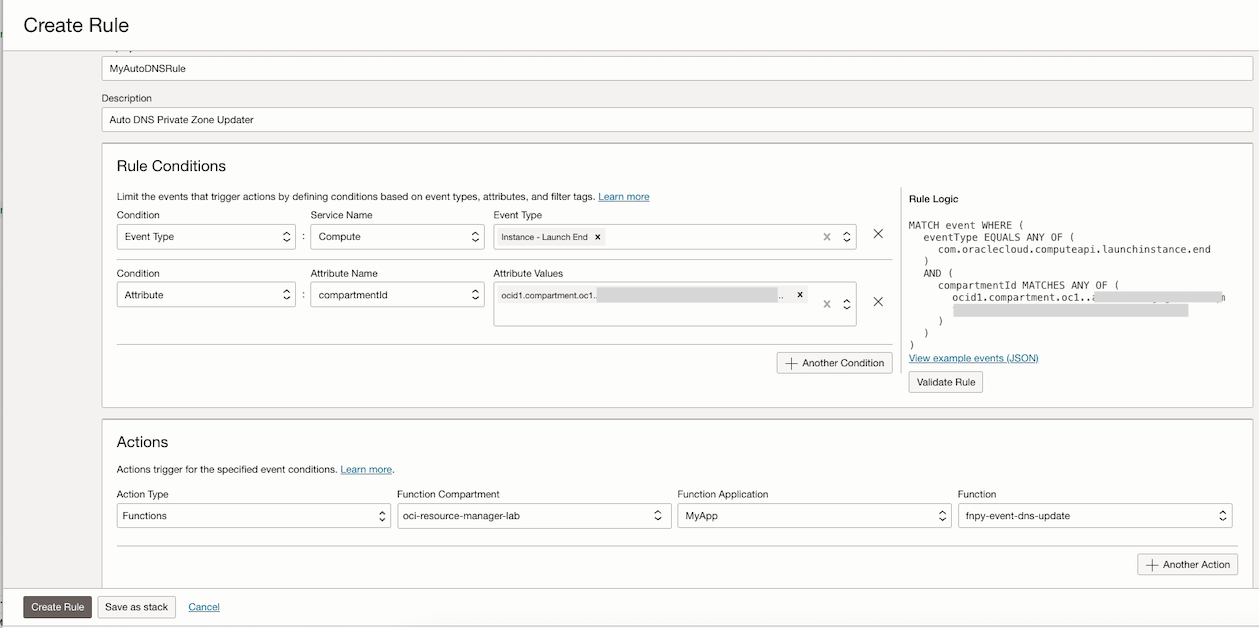
Note: In this example, we are filtering the instances by compartmentID, meaning that any newly launched instance in that compartment will trigger the selected function. You can specify different filters and conditions based on your needs.
- Name: Enter
Task 6: Validate the Solution
In this tutorial, we have established DNS private zones in both the GRU and VCP regions and documented the OCIDs for each DNS private zone. These OCIDs will be used for configuring the OCI Functions.
-
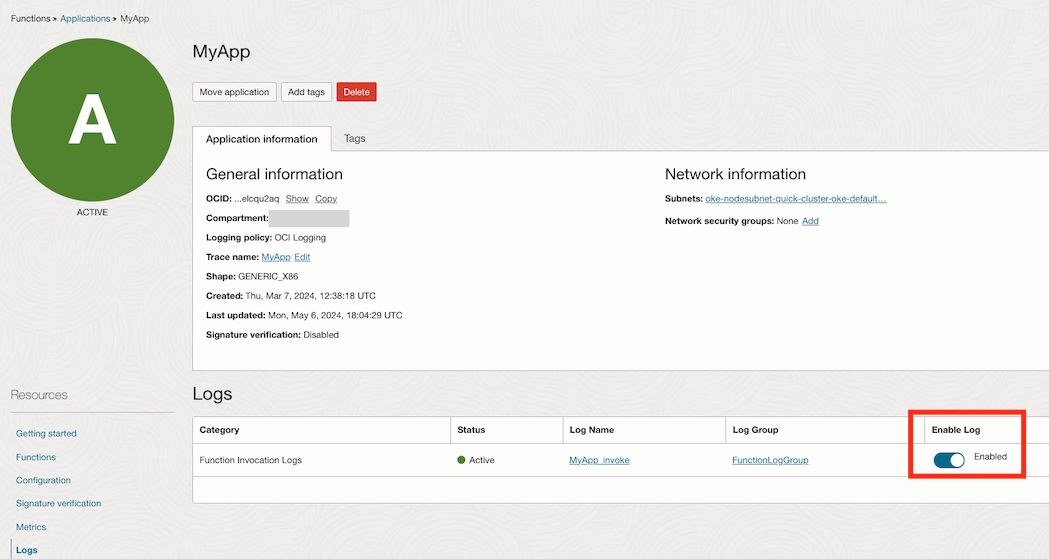
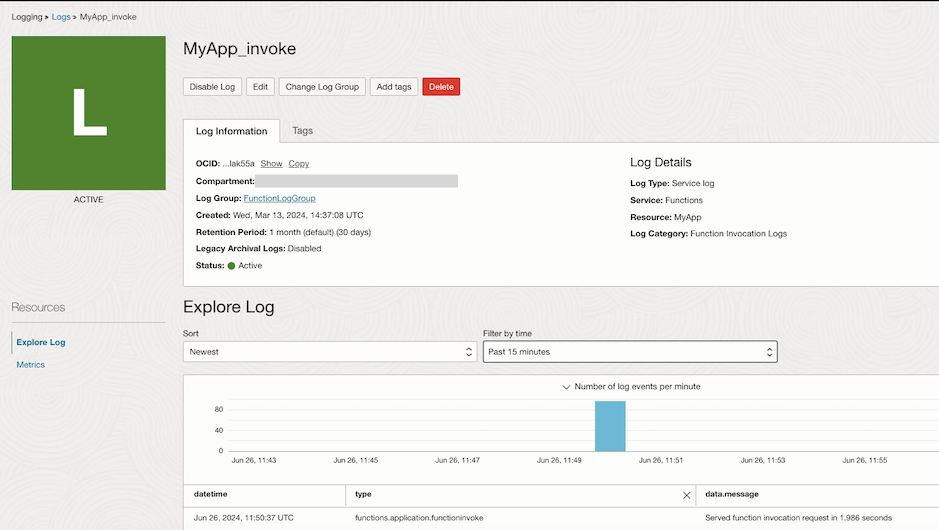
Ensure your OCI Functions is available and enable logging for it.
-
Go to the OCI Console and click Developer Services. Under Functions, click Applications and select your created application
MyApp.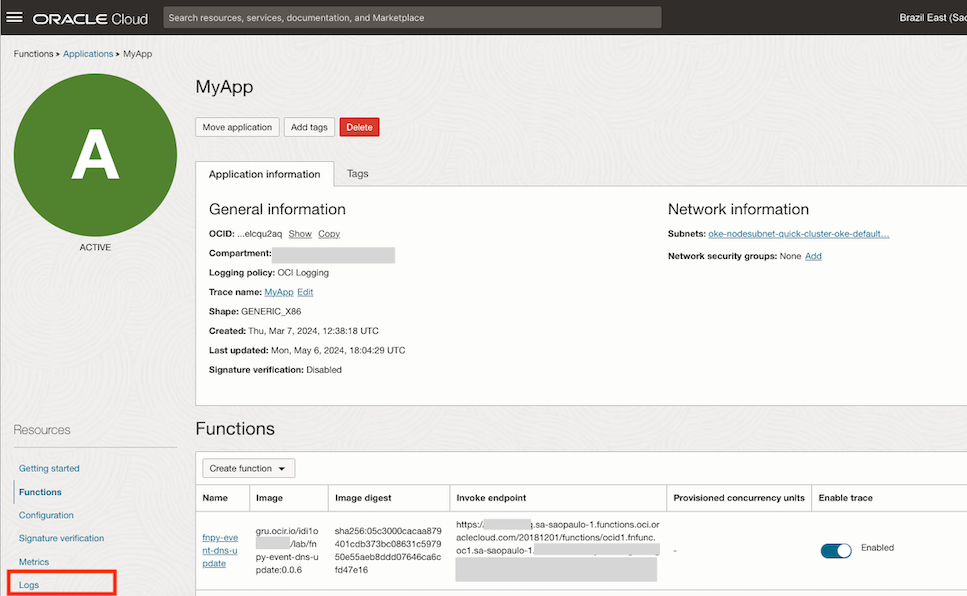
-
Click Logs and select Enable Log.
-
-
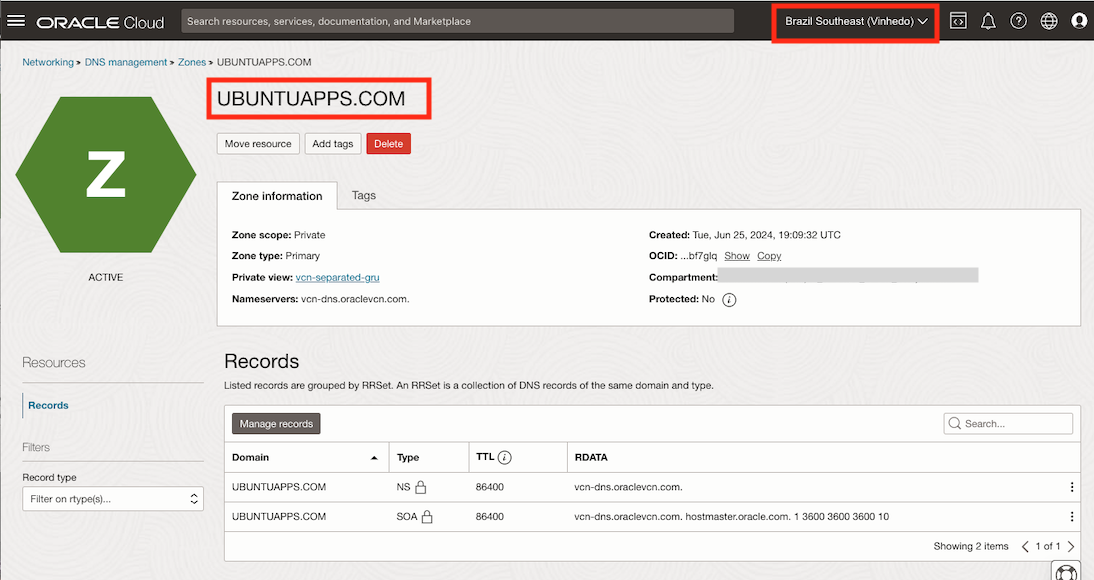
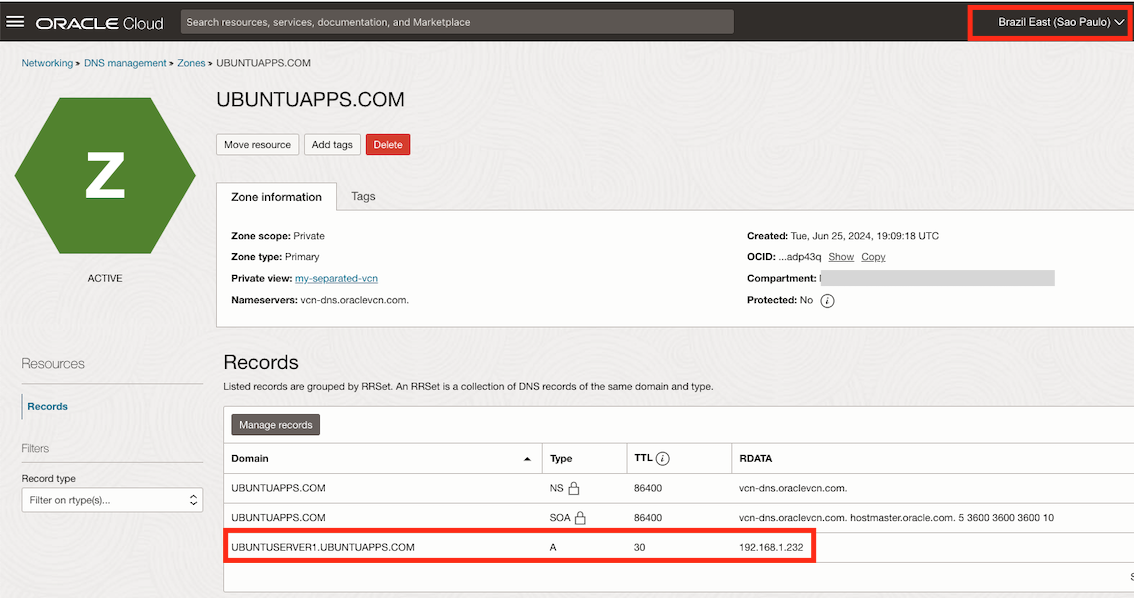
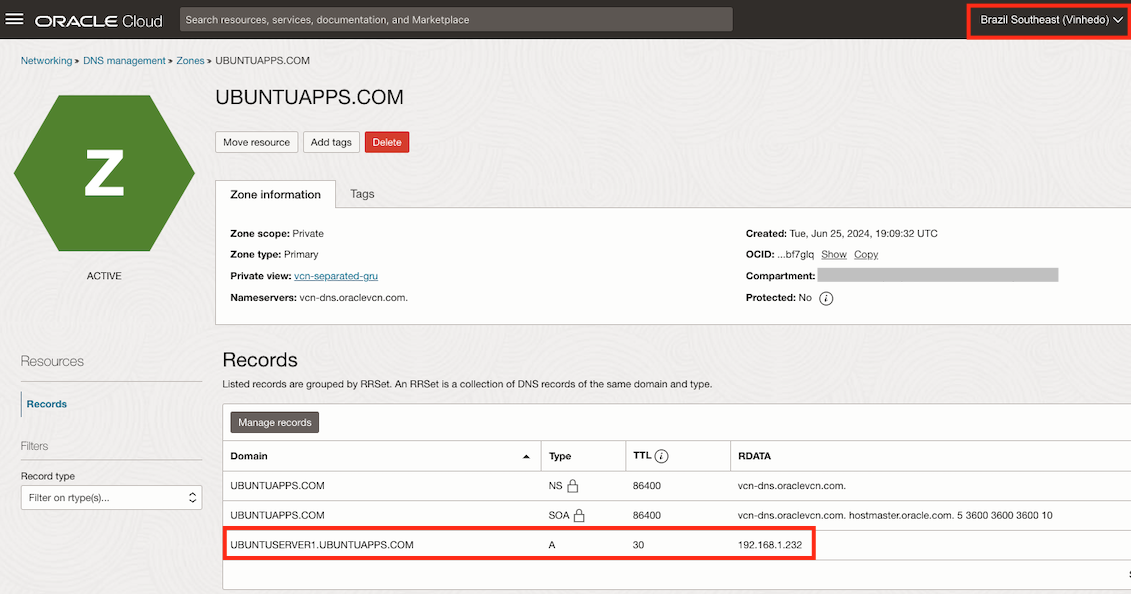
Check the current DNS private zones. We have set up a domain called
UBUNTUAPPS.COMin both regions, as shown in the following images.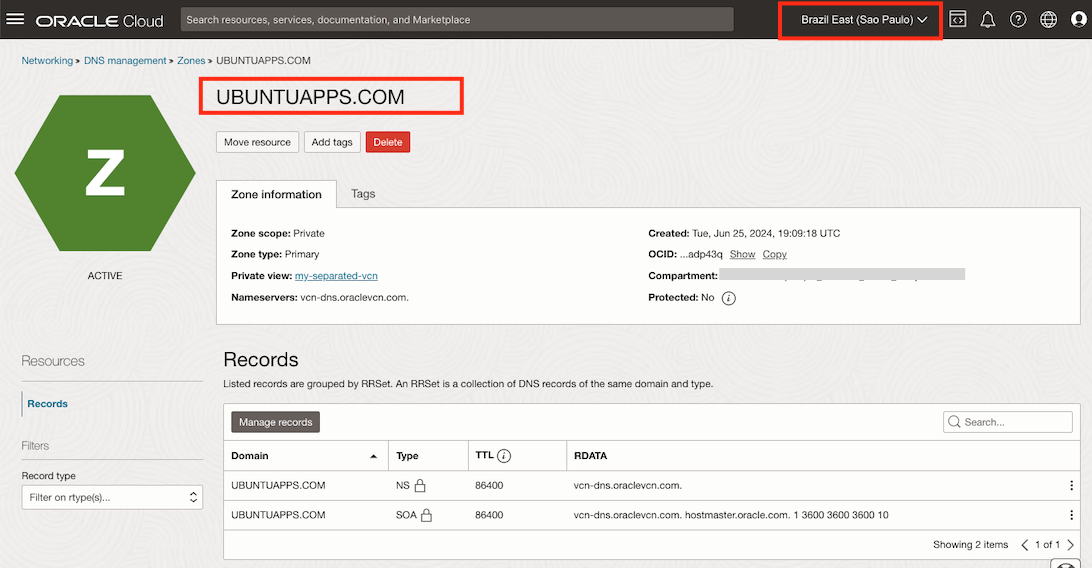
-
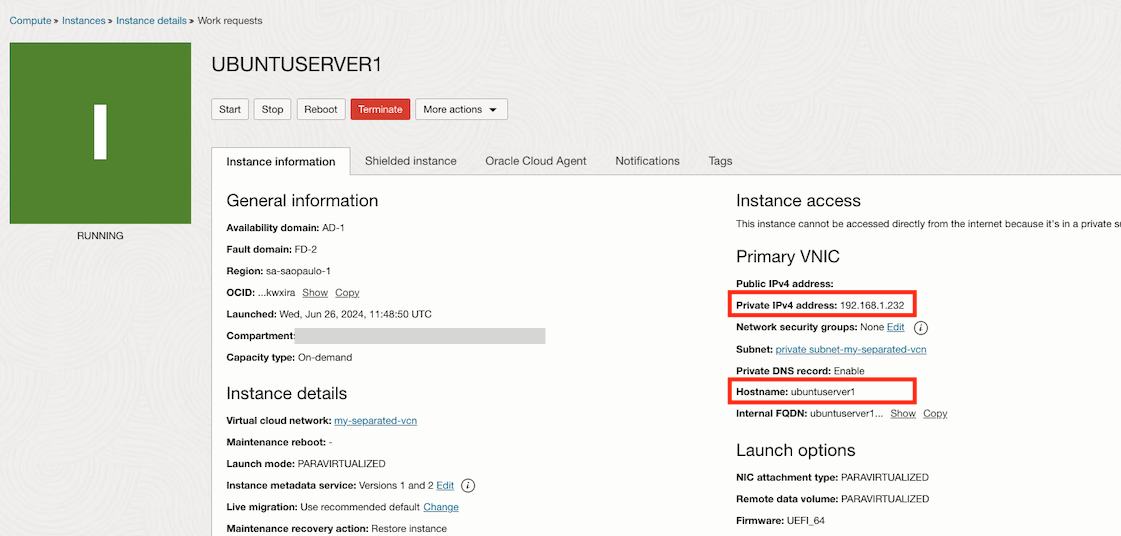
Create a new compute instance to simulate an OCI Full Stack DR switchover. This will trigger the
Instance Launch - ENDevent, which will then invoke the OCI Functions to update the DNS private zone in both regions.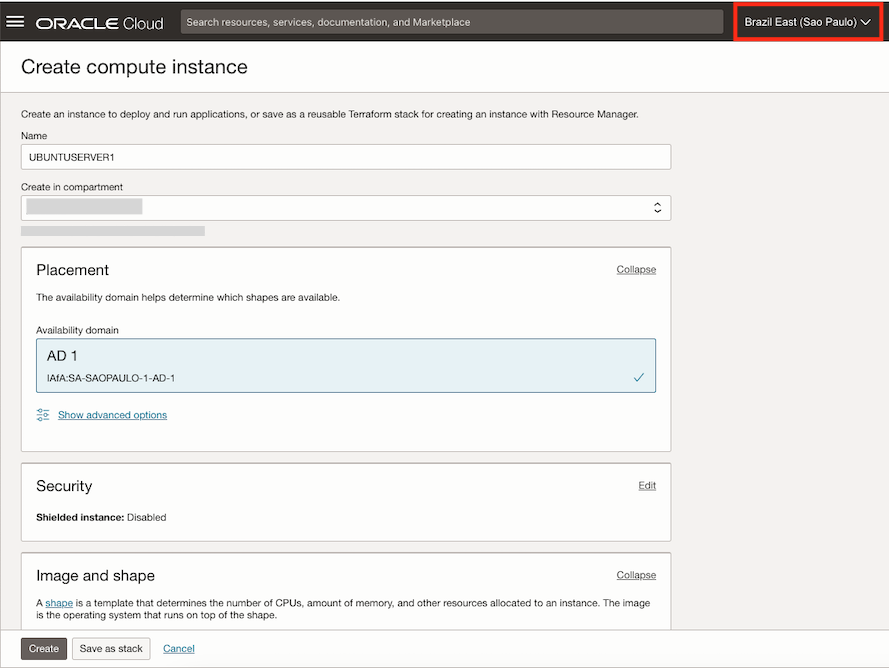
-
After the instance is created, verify that the DNS private zone has been properly updated in both regions.
-
Review the OCI Functions logs to verify the details of the executed function.
Related Links
Acknowledgments
- Author - Joao Tarla (Oracle LAD A-Team Solution Engineer)
More Learning Resources
Explore other labs on docs.oracle.com/learn or access more free learning content on the Oracle Learning YouTube channel. Additionally, visit education.oracle.com/learning-explorer to become an Oracle Learning Explorer.
For product documentation, visit Oracle Help Center.
Use OCI Events Service Rule to Update Cross Region DNS Records for a Private Zone with OCI Functions
G10966-01
July 2024