3 Configuring the Identity Cloud Service Connector
While creating an application, you must configure connection-related parameters that the connector uses to connect Oracle Identity Governance with your target system and perform connector operations. In addition, you can view and edit attribute mappings between the process form fields in Oracle Identity Governance and target system columns, predefined correlation rules, situations and responses, and reconciliation jobs.
Basic Configuration Parameters
These are the connection-related parameters that Oracle Identity Governance requires to connect to the Identity Cloud Service.
Table 3-1 Basic Configuration Parameters for Identity Cloud Service
| Parameter | Mandatory? | Description |
|---|---|---|
|
acceptType |
Yes |
The accept type for the header denotes how the request body must be parsed. The request body should only be parsed as JSON if the Content-Type header is application/json. Sample value: |
|
authenticationServerUrl |
Yes |
The URL of the authentication server if authentication type is “BASIC”. Sample value: |
|
baseURI |
Yes |
The base URI is the base relative URL of the Identity Cloud Service target system. Sample value: If the target system URL is |
|
contentType |
Yes |
The content type for the header denotes the format of the request being sent to the target system. The request body should only be parsed as JSON if the Content-Type header is application or JSON. Sample value: |
|
customAuthHeaders |
Yes |
Client identifier and client secret values used for authorization with your target system. Enter a value for this parameter in the following format:
In this format, replace Sample value: |
|
grantType |
Yes |
Type of authentication used by your target system. Sample value: |
|
host |
Yes |
Host name or IP address of the computer hosting the target system. Sample value: |
|
port |
Yes |
Port number at which the target system is listening. Sample value: |
|
scope |
Yes |
Scope is required to authenticate request based on “OAuth2.0 Resource Owners Password or Client Credentials” authentication type. Sample value: |
|
sslEnabled |
Yes |
If the target system requires SSL connectivity, set the value of this parameter to |
|
Connector Server Name |
No |
Name of the IT resource of type “Connector Server”. By default, this field is blank. If you have deployed the connector in a Java Connector Server, then enter the name of the IT resource for the Connector Server. |
|
username |
No |
User name or User ID used if authentication type is “basic” or “password”. Sample value: |
|
password |
No |
Password used if authentication type is “basic” or “password”. Sample value: |
Advanced Settings Parameters
These are the configuration-related entries that the connector uses during reconciliation and provisioning operations.
Table 3-2 Advanced Settings Parameters for Identity Cloud Service
| Parameter | Mandatory? | Description |
|---|---|---|
|
relURLs |
No |
This entry holds the relative URL of every object class supported by this connector and the connector operations that can be performed on these object classes. Default value: Note: You can update this parameter to delete a user that is associated with one or more entities (Groups or Applications) in Identity Cloud Service. To do so, add the The updated sample value is: If you do not update this entry and try to delete the user, an error message is displayed. For details on the error message, see Troubleshooting the Identity Cloud Service Connector. |
|
Bundle Name |
No |
This entry holds the name of the connector bundle package. Default value: |
|
Bundle Version |
No |
This entry holds the version of the connector bundle. Default value: |
|
Connector Name |
No |
This entry holds the name of the connector class. Default value: |
|
nameAttributes |
Yes |
This entry indicates the attributes that need to be treated as the __NAME__ attribute for an Object class. Default value: |
|
uidAttributes |
Yes |
This entry holds the UID attribute for the objects that are handled by the connector. For example, the UID attribute is ID for User accounts. Default value: |
|
statusAttributes |
No |
This entry lists the name of the target system attribute that holds the status of an account. This entry indicates the status field: The __ENABLE__ field on the target for an object class. Default value: |
|
passwordAttributes |
No |
This entry indicates the attributes that need to be treated as the __PASSWORD__ attribute for an object class. Default value: |
|
attrToOClassMapping |
No |
This entry denotes that the groups attribute of the __ACCOUNT__ object class is mapped to the Groups object class on the target. Default value: |
|
scimVersion |
Yes |
This indicates the SCIM version on which the target is implemented. Default value: |
|
jsonResourcesTag |
No |
This JSON tag value is used during reconciliation for parsing multiple entries in a single response payload. Default value: |
|
customPayload |
No |
This entry holds the payloads for all operations that are not in the standard format. Default value: |
|
Any Incremental Recon Attribute Type |
No |
By default, during incremental reconciliation, Oracle Identity Governance accepts time stamp information sent from the target system only in Long datatype format. A decode value of True for the Incremental Recon Attribute Type entry indicates that Oracle Identity Governance will accept time stamp information in any datatype format. Default value: |
|
httpOperationTypes |
No |
This entry indicates that for a Password Update operation, the target needs a PUT operation instead of PATCH. Default value: |
|
reconSortByAttrs |
No |
This entry holds the attribute used for sorting the records during a reconciliation operation. Default value: |
|
managedObjectClasses |
No |
This entry holds the value of object classes used by the target system. Operations related to users and groups use this parameter to store the corresponding object classes of the target system. Default value: |
|
hashPasswordEnabled |
No |
This entry specifies whether hashing must be enabled on the default password that is sent to the target system when a new account is created. Default value: This implies that hashing is not enabled and the default password is sent in a plain text format. Note: To enable hashing on the default password, set the value of this parameter to For more information on enabling hashing during the Create User provisioning operation, see Guidelines on Performing Provisioning Operations. |
|
hashAlgorithm |
No |
This entry holds the value of hash algorithm that the connector uses if the hashPasswordEnabled parameter is set to Default value: The supported algorithms are:
|
Attribute Mappings
The Schema page for a Target application displays the default schema (provided by the connector) that maps Oracle Identity Governance attributes to target system attributes. The connector uses these mappings during reconciliation and provisioning operations.
Identity Cloud Service User Account Attributes
Table 3-3 lists the user-specific attribute mappings between the process form fields in Oracle Identity Governance and Identity Cloud Service attributes. The table also lists whether a specific attribute is used during provisioning or reconciliation and whether it is a matching key field for fetching records during reconciliation.
If required, you can edit the default attribute mappings by adding new attributes or deleting existing attributes as described in Creating a Target Application of Oracle Fusion Middleware Performing Self Service Tasks with Oracle Identity Governance.
Table 3-3 Default Attribute Mappings for the Identity Cloud Service User Account
| Display Name | Target Attribute | Data Type | Mandatory Provisioning Property? | Provision Field? | Recon Field? | Key Field? | Case Insensitive? |
|---|---|---|---|---|---|---|---|
|
Id |
__UID__ |
String |
No |
Yes |
Yes |
Yes |
Not Applicable |
|
User Name |
__NAME__ |
String |
Yes |
Yes |
Yes |
No |
Not Applicable |
|
First Name |
name.givenName |
String |
Yes |
Yes |
Yes |
No |
Not Applicable |
|
Last Name |
name.familyName |
String |
Yes |
Yes |
Yes |
No |
Not Applicable |
|
Middle Name |
name.middleName |
String |
No |
Yes |
Yes |
No |
Not Applicable |
|
Manager |
manager.value |
String |
No |
Yes |
Yes |
No |
Not Applicable |
|
Employee Number |
employeeNumber |
String |
No |
Yes |
Yes |
No |
Not Applicable |
|
|
__ACCOUNT__.emails.value,type:work,primary:true |
String |
Yes |
Yes |
Yes |
No |
Not Applicable |
|
User Type |
userType |
String |
No |
Yes |
Yes |
No |
Not Applicable |
|
Organization |
organization |
String |
No |
Yes |
Yes |
No |
Not Applicable |
|
Password |
__PASSWORD__ |
String |
No |
Yes |
No |
No |
Not Applicable |
|
Creation Mechanism |
creationMechanism |
String |
No |
Yes |
No |
No |
Not Applicable |
|
Status |
__ENABLE__ |
String |
No |
Yes |
Yes |
No |
Not Applicable |
Figure 3-1 shows the default user account attribute mappings.
Figure 3-1 Default Attribute Mappings for the Identity Cloud Service User Account
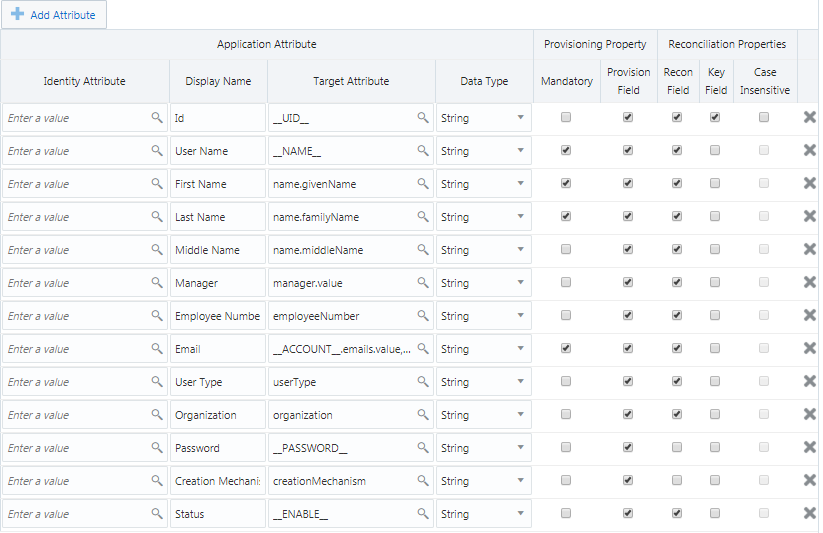
Description of "Figure 3-1 Default Attribute Mappings for the Identity Cloud Service User Account"
Group Names Child Attributes
Table 3-4 lists the attribute mappings for group names between the process form fields in Oracle Identity Governance and Identity Cloud Service attributes. The table lists whether a given attribute is mandatory during provisioning. It also lists whether a given attribute is used during reconciliation and whether it is a matching key field for fetching records during reconciliation.
If required, you can edit the default attribute mappings by adding new attributes or deleting existing attributes as described in Creating a Target Application of Oracle Fusion Middleware Performing Self Service Tasks with Oracle Identity Governance.
Table 3-4 Default Attribute Mappings for the Identity Cloud Service Group Names
| Display Name | Target Attribute | Data Type | Mandatory Provisioning Property? | Recon Field | Key Field? | Case Insensitive? |
|---|---|---|---|---|---|---|
|
Group Value |
__ACCOUNT__.groups~__ACCOUNT__.groups~value |
String |
No |
Yes |
Yes |
Not Applicable |
Figure 3-2 shows the default group name attribute mappings.
Figure 3-2 Default Attribute Mappings for the Identity Cloud Service Group Names
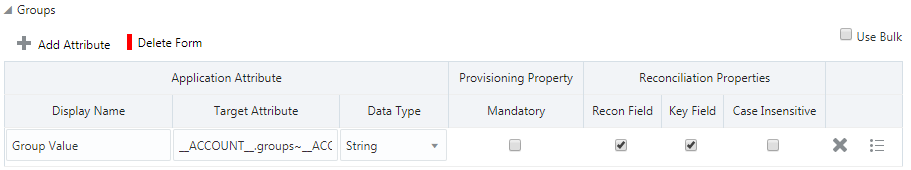
Description of "Figure 3-2 Default Attribute Mappings for the Identity Cloud Service Group Names"
Correlation Rules, Situations, and Responses
Learn about the predefined rules, responses and situations for an Identity Cloud Service Target application. The connector use these rules and responses for performing reconciliation.
Predefined Identity Correlation Rules
By default, the Identity Cloud Service connector provides a simple correlation rule when you create a Target application. The connector uses this correlation rule to compare the entries in Oracle Identity Governance repository and the target system repository, determine the difference between the two repositories, and apply the latest changes to Oracle Identity Governance.
Table 3-5 Predefined Identity Correlation Rule for an Identity Cloud Service Target Application
| Target Attribute | Element Operator | Identity Attribute | Case Sensitive? |
|---|---|---|---|
|
__NAME__ |
Equals |
User Login |
No |
-
__NAME__ is a single-valued attribute on the target system that identifies the user account.
-
User Login is the field on the OIG User form.
Figure 3-3 shows the simple correlation rule for the Identity Cloud Service connector.
Figure 3-3 Simple Correlation Rule for an Identity Cloud Service Target Application
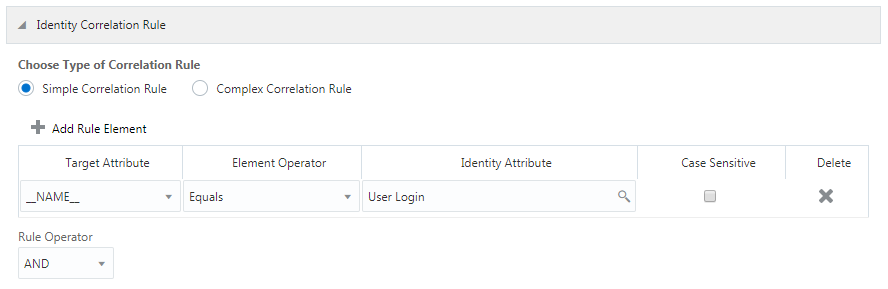
Description of "Figure 3-3 Simple Correlation Rule for an Identity Cloud Service Target Application"
Predefined Situations and Responses
The Identity Cloud Service connector provides a default set of situations and responses when you create a Target application. These situations and responses specify the action that Oracle Identity Governance must take based on the result of a reconciliation event.
Table 3-6 lists the default situations and responses for the Identity Cloud Service connector. If required, you can edit these default situations and responses or add new ones. For more information about adding or editing situations and responses, see Creating a Target Application in Oracle Fusion Middleware Performing Self Service Tasks with Oracle Identity Governance.
Table 3-6 Predefined Situations and Responses for an Identity Cloud Service Target Application
| Situation | Response |
|---|---|
|
No Matches Found |
None |
|
One Entity Match Found |
Establish Link |
|
One Process Match Found |
Establish Link |
Figure 3-4 shows the default situations and responses for the Identity Cloud Service connector.
Figure 3-4 Default Situations and Responses for an Identity Cloud Service Target Application
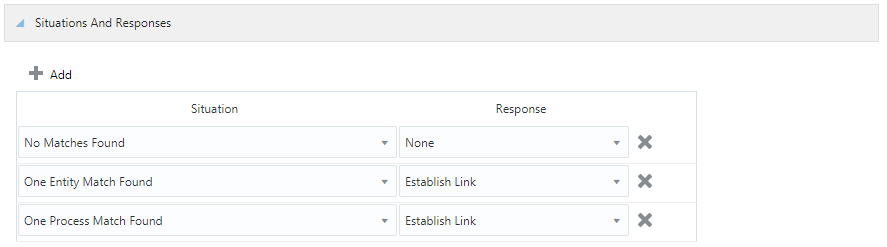
Description of "Figure 3-4 Default Situations and Responses for an Identity Cloud Service Target Application"
Reconciliation Jobs
Learn about the reconciliation jobs that are automatically created in Oracle Identity Governance after you create the application for your target system.
You can either use these predefined jobs or edit them to meet your requirements. Alternatively, you can create custom reconciliation jobs. For information about editing these predefined jobs or creating new ones, see Updating Reconciliation Jobs in Oracle Fusion Middleware Performing Self Service Tasks with Oracle Identity Governance.
IDCS Target Resource User Reconciliation Job
You use the IDCS Target Resource User Reconciliation job to perform full or incremental reconciliation, which involves reconciling all user records from a target application into Oracle Identity Governance.
Table 3-7 Parameters of the IDCS Target Resource User Reconciliation Job
| Parameter | Description |
|---|---|
|
Application Name |
Name of the application you created for your target system. This value is the same as the value that you provided for the Application Name field while creating your target application. Note: Do not modify this value. |
|
Batch Size |
Enter the number of records that must be included in each batch fetched from the target system during reconciliation. By default, the value of this attribute is empty, indicating that all records are included for reconciliation. |
|
Filter |
Enter the search filter for fetching records from the target system during a reconciliation run. See Performing Limited Reconciliation for more information about filtered reconciliation. |
|
Incremental Recon Attribute |
This attribute holds the value of the target system attribute that is specified as the value of the Incremental Recon Attribute attribute. Default value: Note: Do not modify this value. |
|
Object Type |
This attribute holds the name of the object type for the reconciliation run. Default value: Note: User is the only object that is supported. Therefore, do not change the value of this attribute. |
|
Latest Token |
Attribute that holds the date on which the token record is modified. The Latest Token attribute is used for internal purposes. By default, this value is empty. Note: Do not enter a value for this attribute. The reconciliation engine automatically enters a value in this attribute. Sample value: |
|
Scheduled Task Name |
Name of the scheduled job. Note: For the scheduled job included with this connector, you must not change the value of this attribute. However, if you create a new job or create a copy of the job, then enter the unique name for that scheduled job as the value of this attribute. |
IDCS Target Resource User Delete Reconciliation Job
You use the IDCS Target Resource User Delete Reconciliation job to reconcile deleted user account data from the target system.
Table 3-8 Parameters of the IDCS Target Resource User Delete Reconciliation Job
| Parameter | Description |
|---|---|
|
Application Name |
Name of the application you created for your target system. This value is the same as the value that you provided for the Application Name field while creating your target application. Note: Do not modify this value. |
|
Object Type |
This attribute holds the name of the object type for the reconciliation run. Default value: Note: User is the only object that is supported. Therefore, do not change the value of this attribute. |
|
Batch Size |
Enter the number of records that must be included in each batch fetched from the target system during reconciliation. By default, the value of this attribute is empty, indicating that all records are included for reconciliation. |
Reconciliation Jobs for Entitlements
-
IDCS Group Lookup Reconciliation: Use this job to reconcile all group data in the target system into lookup fields in Oracle Identity Governance.
-
IDCS Manager Lookup Reconciliation: Use this job to reconcile all manager data in the target system into lookup fields in Oracle Identity Governance.
The parameters for all the reconciliation jobs are the same.
Table 3-9 Parameters of the Reconciliation Jobs for Entitlements
| Parameter | Description |
|---|---|
|
Application Name |
Name of the application you created for your target system. This value is the same as the value that you provided for the Application Name field while creating your target application. Note: Do not modify this value. |
|
Lookup Name |
This parameter holds the name of the lookup definition that maps each lookup definition with the data source from which values must be fetched. Depending on the reconciliation job you are using, the default values are as follows:
|
|
Object Type |
Enter the type of object whose values must be synchronized. Depending on the scheduled job you are using, the default values are as follows:
Note: Do not modify this value. |
|
Code Key Attribute |
Enter the name of the connector or target system attribute that is used to populate the Code Key column of the lookup definition (specified as the value of the Lookup Name attribute). Default value: Note: Do not modify this value. |
|
Decode Attribute |
Enter the name of the connector or target system attribute that is used to populate the Decode column of the lookup definition (specified as the value of the Lookup Name attribute). Default value: |