1 About the Identity Cloud Service Connector
Oracle Identity Governance is a centralized identity management solution that provides self service, compliance, provisioning and password management services for applications residing on-premises or on the Cloud. Oracle Identity Governance connectors are used to integrate Oracle identity Governance with the external identity-aware applications.
Note:
In this guide, the connector that is deployed using the Applications option on the Manage tab of Identity Self Service is referred to as an AOB application. The connector that is deployed using the Manage Connector option in Oracle Identity System Administration is referred to as a CI-based connector (Connector Installer-based connector).Application onboarding is the process of registering or associating an application with Oracle Identity Governance and making that application available for provisioning and reconciliation of user information.
Note:
In this guide, Oracle Identity Cloud Service is sometimes referred to as the target system.
The following topics provide a high-level overview of the Identity Cloud Service connector:
Note:
In this guide, the term Oracle Identity Governance server refers to the computer on which Oracle Identity Governance is installed.Certified Components
These are the software components and their versions required for installing and using the Identity Cloud Service connector.
Note:
If you are using Oracle Identity Manager release 11.1.x, then you can install and use the connector only in the CI-based mode. If you want to use the AOB application, then you must upgrade to Oracle Identity Governance release 12.2.1.3.0 or later.Table 1-1 Certified Components
| Component | Requirement for AOB Application | Required for CI-Based Connector |
|---|---|---|
|
Oracle Identity Governance or Oracle Identity Manager |
You can use one of the following releases of Oracle Identity Governance or Oracle Identity Manager:
|
You can use one of the following releases of Oracle Identity Governance or Oracle Identity Manager:
|
|
Target System |
Oracle Identity Cloud Service 16.3.6 or later Note: It is recommended to use Oracle Identity Cloud Service 18.2.x or later because the new features (such as Password Hashing and Deleting Users Associated with Entities) are not supported in earlier versions. |
Oracle Identity Cloud Service 16.3.6 or later Note: It is recommended to use Oracle Identity Cloud Service 18.2.x or later because the new features (such as Password Hashing and Deleting Users Associated with Entities) are not supported in earlier versions. |
|
Connector Server |
12.2.1.3.1 or 12.2.1.3.0 Note: It is recommended to use Connector Server 12.2.1.3.0 or later if you want to configure Transport Layer Security (TLS) 1.2 connection. |
12.2.1.3.1 or 12.2.1.3.0 Note: It is recommended to use Connector Server 12.2.1.3.0 or later if you want to configure TLS 1.2 connection. |
|
Connector Server JDK |
|
|
Usage Recommendation
These are the recommendations for the Identity Cloud Service connector versions that you can deploy and use depending on the Oracle Identity Governance or Oracle Identity Manager version that you are using.
-
If you are using Oracle Identity Governance release 12c (12.2.1.3.0) or Oracle Identity Governance 14c (14.1.2.1.0) or later, then use the latest 12.2.1.x version of this connector. Deploy the connector using the Applications option on the Manage tab of Identity Self Service.
-
If you are using any of the Oracle Identity Manager releases listed in the “Requirement for CI-Based Connector” column of Certified Components, then use the 11.1.1.x version of the Identity Cloud Service connector. If you want to use the 12.2.1.x version of this connector, then you can install and use it only in the CI-based mode. If you want to use the AOB application, then you must upgrade to Oracle Identity Governance release 12c (12.2.1.3.0) or later.
Note:
If you are using the latest 12.2.1.x version of the Identity Cloud Service connector in the CI-based mode, then see Oracle Identity Manager Connector Guide for Oracle Identity Cloud Services, Release 11.1.1 for complete details on connector deployment, usage, and customization.Certified Languages
The connector supports the following languages:
-
Arabic
-
Chinese Simplified
-
Chinese Traditional
-
Danish
-
English
-
French
-
German
-
Italian
-
Japanese
-
Korean
-
Portuguese (Brazilian)
-
Spanish
Supported Connector Operations
These are the list of operations that the connector supports for your target system.
Table 1-2 Supported Connector Operations
| Operation | Supported? |
|---|---|
|
User Management |
|
|
Disable user |
Yes |
|
Add child data |
Yes |
|
Update object |
Yes |
|
Create object |
Yes |
|
Delete object |
Yes |
|
Enable user |
Yes |
|
Update child data |
Yes |
|
Remove child data |
Yes |
|
Group Management |
|
|
Add group |
Yes |
|
Update group |
Yes |
|
Remove group |
Yes |
Note:
All the connector artifacts required for managing groups (such as group attribute mappings, reconciliation rules, scheduled jobs, and so on) are available in the preconfigured templates (XML files) of the connector installation package. See Connector Objects Used For Group Management.Connector Architecture
You can configure the Identity Cloud Service connector to run in the Target (or account management) mode, and is implemented using the Identity Connector Framework (ICF) component.
The ICF is a component that provides basic reconciliation and provisioning operations that are common to all Oracle Identity Governance connectors. In addition, ICF provides common features that developers would otherwise need to implement on their own, such as connection pooling, buffering, time outs, and filtering. The ICF is shipped along with Oracle Identity Governance. Therefore, you need not configure or modify the ICF.
This connector enables management of target system accounts through Oracle Identity Governance. Figure 1-1 shows the integration of on-premise Oracle Identity Governance with Oracle Identity Cloud Service.
Figure 1-1 Architecture of the Identity Cloud Service Connector
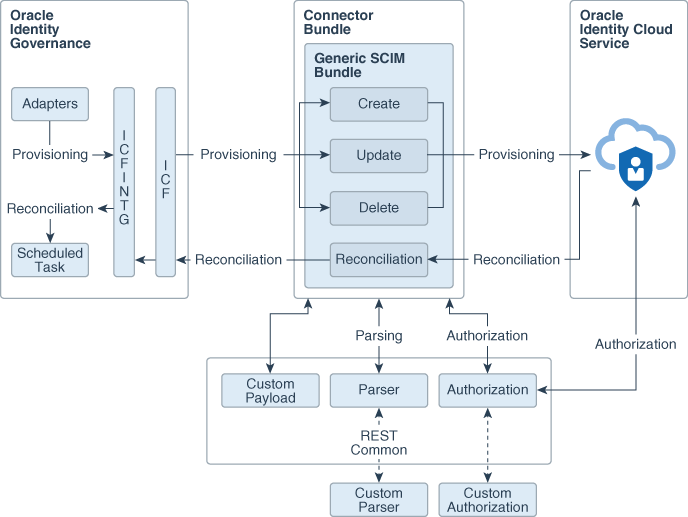
Description of "Figure 1-1 Architecture of the Identity Cloud Service Connector"
As shown in this figure, the Identity Cloud Service connector enables you to use the target system as a managed resource (target) of identity data for Oracle Identity Governance.
In the target mode of the connector, information about users created or modified directly on the target system can be reconciled into Oracle Identity Governance. In addition, you can use Oracle Identity Governance to perform provisioning operations on the target system.
Provisioning involves creating and managing user accounts. When you allocate (or provision) an Identity Cloud Service resource to an OIG User, the operation results in the creation of an account on the target system for that user. Similarly, when you update the resource on Oracle Identity Governance, the same update is made to the account on the target system.
The connector bundle is responsible for interacting with Identity Cloud Service, which is a SCIM compliant target. Therefore, the connector package uses the Generic SCIM bundle. Parsing and authorization is handled by the REST common bundle, which is a part of the Generic SCIM bundle. By default, it supports OAuth 2.0 Resource Owner Password authentication. In addition, custom parser and custom authorization can be implemented to enhance the connector.
Supported Use Cases
The promise of simplified deployment, reduced acquisition costs, reduced management overhead and quick time to value are driving organizations to adopt SaaS applications to meet the various business needs. Since recently, very large number of applications are being developed in the cloud. Identity Cloud Service provides a set of foundational services for Oracle’s Public Cloud applications and their customers by delivering simple, secure integration with Oracle and third party SaaS applications for customers interested in a Public Identity as a service offering from Oracle.
Similarly, many of Oracle’s existing customers using on-premise IDM are also moving their HCM, CRM, directories and other applications from on-premise to the Cloud. Customers also want to move their IDM services into cloud. To keep pace with the changing trends and to support customers who are adopting cloud, Oracle’s on-premise Identity Management software, Oracle Identity Governance provides a new integration called the Identity Cloud Service connector. This integration will not only facilitate customer’s migration from on-premise to cloud but it will also support the hybrid strategy where customers can have both on-premise IDM and cloud IDM working together to achieve greater value.
Let’s say ACME Corporation has been using Oracle Identity Governance for some time to manage its identities and various applications on premise. The long-term plan of ACME Corporation is to move into cloud but they want to achieve this in phases. At one point of time, they have both on-premise and cloud applications. As part of this move, they now have Identity Cloud Service to manage cloud applications but for the time being, they want to use only Oracle Identity Governance to manage identities in their ecosystem.
The Identity Cloud Service connector will facilitate ACME Corporation in achieving this use case by providing the Identity Cloud Service user and group management for the cloud applications.
After installing the Identity Cloud Service connector, customer can manage complete lifecycle of the users and groups in Identity Cloud Service from Oracle Identity Governance. Using this integration, ACME Corporation can create, update, enable, and disable the Identity Cloud Service users accessing the cloud applications. Also, it can assign or revoke Identity Cloud Service groups for a particular user accessing the cloud applications using Oracle Identity Governance.
With the RBAC policies defined in Oracle Identity Governance, granting or revoking appropriate groups using connector will ensure that user has proper, authorized access to the cloud applications registered with Identity Cloud Service.
Supported Connector Features Matrix
Provides the list of features supported by the AOB application and CI-based connector.
Table 1-3 Supported Connector Features Matrix
| Feature | AOB Application | CI-Based Connector |
|---|---|---|
|
Perform full and incremental reconciliation |
Yes |
Yes |
|
Provision the Identity Cloud Service user and group accounts |
Yes |
Yes |
|
Perform limited reconciliation |
Yes |
Yes |
|
Perform batched reconciliation |
Yes |
Yes |
|
Reconcile deleted user and group records into Oracle Identity Governance |
Yes |
Yes |
|
Configure validation and transformation of account data |
Yes |
Yes |
|
Clone applications or create new application instances |
Yes |
Yes |
|
Use connector server |
Yes |
Yes |
|
Provide secure communication to the target system through SSL |
Yes |
Yes |
Connector Features
The features of the connector include support for provisioning user and group accounts, target resource reconciliation, reconciliation of all existing or modified account data, reconciliation of deleted user and group records, limited and batched reconciliation, transformation and validation of account data during reconciliation and provisioning, support for the connector server, multiple installations of the target system, secure communication to the target system through SSL, and so on.
Support for User and Group Provisioning
You can use the connector for provisioning user and group accounts.
You perform provisioning operations in Oracle Identity Governance by using the Create User page. See Creating a User in Oracle Fusion Middleware Performing Self Service Tasks with Oracle Identity Governance for details about the fields on the Create User page.
Support for Full and Incremental Reconciliation
After you create the application, you can perform full reconciliation to bring all existing user data from the target system to Oracle Identity Governance. After the first full reconciliation run, incremental reconciliation is automatically enabled from the next run of the user reconciliation.
You can perform a full reconciliation run at any time. See Performing Full and Incremental Reconciliation.
Support for Limited Reconciliation
You can set a reconciliation filter as the value of the Filter attribute of the scheduled tasks.
To limit or filter the records that are fetched into Oracle Identity Governance during a reconciliation run, you can specify the subset of added or modified target system records that must be reconciled. See Performing Limited Reconciliation.
Support for Batched Reconciliation
Depending on the number of records to be reconciled, a batched reconciliation operation can be configured.
You can break down a reconciliation run into batches by specifying the number of records that must be included in each batch. See Performing Batched Reconciliation.
Reconciliation of Deleted User and Group Records
You can use the connector to reconcile user and group records that are deleted on the target system into Oracle Identity Governance.
For more information about reconciliation jobs used for reconciling these deleted records, see IDCS Target Resource User Delete Reconciliation Job and IDCS Group Delete Reconciliation Job.
Transformation and Validation of Account Data
You can configure transformation and validation of account data that is brought into or sent from Oracle Identity Governance during reconciliation and provisioning operations by writing Groovy scripts while creating your application.
For more information, see Validation and Transformation of Provisioning and Reconciliation Attributes in Oracle Fusion Middleware Performing Self Service Tasks with Oracle Identity Governance.
Support for Cloning Applications and Creating Instance Applications
You can configure this connector for multiple installations of the target system by cloning applications or by creating instance applications.
When you clone an application, all the configurations of the base application are copied into the cloned application. When you create an instance application, it shares all configurations as the base application.
For more information about these configurations, see Cloning Applications and Creating Instance Applications in Oracle Fusion Middleware Performing Self Service Tasks with Oracle Identity Governance.
Secure Communication to the Target System
To provide secure communication to the target system, SSL is required. You can configure SSL between Oracle Identity Governance and the Connector Server and between the Connector Server and the target system.
If you do not configure SSL, passwords can be transmitted over the network in clear text. For example, this problem can occur when you are creating a user or modifying a user's password.
Support for the Connector Server
Connector Server is one of the features provided by ICF. By using one or more connector servers, the connector architecture permits your application to communicate with externally deployed bundles.
A Java connector server is useful when you do not wish to execute a Java connector bundle in the same VM as your application. It can be beneficial to run a Java connector on a different host for performance improvements.
For information about installing, configuring, and running the Connector Server, and then installing the connector in a Connector Server, see Using an Identity Connector Server in Oracle Fusion Middleware Developing and Customizing Applications for Oracle Identity Governance.