3 Configuring the SAP SuccessFactors Connector
While creating an application, you must configure connection-related parameters that the connector uses to connect Oracle Identity Governance with your target system and perform connector operations. In addition, you can view and edit attribute mappings between the process form fields in Oracle Identity Governance and target system columns, predefined correlation rules, situations and responses, and reconciliation jobs.
This section contains the following topics:
3.1 Basic Configuration Parameters
These are the connection-related parameters that Oracle Identity Governance requires to connect to the SAP SuccessFactor target application.
Note:
-
Unless specified, the parameters in the table are applicable to both target and authoritative applications.
-
In the following table, attributes marked as mandatory are applicable only for
Basic authentication. Foroauth_samlauthentication, all attributes are mandatory except thepassword,portandConnector Server Nameattributes. -
To use the proxy server, apply one-off patch SuccessFactors-12.2.1.3.0A or later.
Table 3-1 Parameters in the Basic Configuration
| Parameter | Mandatory? | Description |
|---|---|---|
|
authenticationType |
Yes |
Type of authentication used by your target system. This connector supports the target system OAuth2.0 client credentials. Default value: oauth_saml Note: Based on requirement, the default value can be modified to |
|
companyId |
Yes |
Enter the company ID for user provisioning. During licensing of SuccessFactors solution, a unique company ID is provided. The OData API uses the company ID attribute to validate your access token. |
|
Host |
Yes |
Enter the host name of the computer hosting your target system. Sample value: apisalesdemo4.successfactors.com |
|
sslEnabled |
Yes |
If the target system requires SSL connectivity, then set the value of this parameter to true. Otherwise set the value to false. Default value: true |
|
username |
Yes |
Enter the username which has permissions to perform all the Identity Management features using APIs. When you purchase a Sandbox, this username is provided by the SAP SuccessFactors organization. Sample value: johnsmith |
|
authenticationServerUrl |
No |
Enter the URL of the authentication server that validates the client ID and client secret for your target system. Sample value: https://apisalesdemo4.successfactors.com/oauth/token? |
|
authorizationUrl |
No |
Authorization URL is the URL which returns the access token. Ensure that you provide correct parameters and their values to receive an access token. Sample value:https://apisalesdemo4.successfactors.com/oauth/idp |
|
clientId |
No |
Enter the client identifier (a unique string) issued by the authorization server to your client application during the registration process. You obtained the client ID while performing. |
|
clientUrl |
No |
This is the attribute that provides the Sandbox URL. This Sandbox URL needs to be registered with the target resource. Sample value: https://apisalesdemo4.successfactors.com |
|
privateKeyLocation |
No |
Enter location of the certificate. During the client application creation process, a certificate gets stored. |
|
Connector Server Name |
No |
If you have deployed the SuccessFactors connector in the Connector Server, then enter the name of the IT resource for the Connector Server. |
|
grantType |
No |
The most important step for an application in the OAuth flow is how the application receives an access token (and optionally a refresh token). A grant type is the mechanism used to retrieve the token. OAuth defines several different access grant types that represent different authorization mechanisms. Default value: urn:ietf:params:oauth:grant-type:saml2-bearer |
| Password | Yes | Enter the password of the computer hosting your target system. |
|
Port |
No |
Enter the port number at which the target system is listening. Sample value: 443 |
|
proxyHost |
No |
Enter the name of the proxy host used to connect to an external target. |
|
proxyPassword |
No |
Enter the password of the proxy user ID of the target system user account that Oracle Identity Governance uses to connect to the target system. |
|
proxyPort |
No |
Enter the proxy port number. |
|
proxyUser |
No |
Enter the proxy user name of the target system user account that Oracle Identity Governance uses to connect to the target system. Sample value:
|
3.2 Advanced Setting Parameters
The advanced setting parameters for the SAP SuccessFactors configuration vary depending on whether you are creating a target application or an authoritative application These are the configuration-related entries that the connector uses during reconciliation and provisioning operations.
Note:
-
Unless specified, the parameters in the table are applicable to both target and authoritative applications.
-
All parameters in the below table are mandatory.
Table 3-2 Advanced Setting Parameters for the SAP SuccessFactors
| Parameter | Description |
|---|---|
|
lookupUrl |
This the endpoint URL used to reconcile lookup data from the target system. Default value: "jobLevel=/odata/v2/FOJobCode?$select=externalCode,name,jobFunction,jobLevel","groupName=/odata/v2/DynamicGroup?&$filter=staticGroup+eq+true" Note: In case you want to reconcile dynamic groups from the target system as well, change the following:
However, you cannot add or remove a user to dynamic groups. In case a dynamic group is provisioned or removed for an user, then an error will be automatically displayed. |
|
upsertUrl |
This entry holds the value of endpoint URL that is used for performing any upsert operation on the user account. Default value: User=/odata/v2/upsert","addGroup=/odata/v2/updateStaticGroup?groupId=groupNameL&action='add'&userIds=Username","removeGroup=/odata/v2/updateStaticGroup?groupId=groupNameL&action='remove'&userIds=Username |
|
reconUrl |
This entry holds the value of endpoint URL that is used to reconcile users from the target resource. Default value: /odata/v2/User?$format=JSON&$filter=status%20ne%20'p' The default value supported from Release 12.2.1.3.0J: /odata/v2/User?$format=json&$expand=empInfo,empInfo/jobInfoNav,empInfo/personNav/personalInfoNav&$filter=status+ne+'p' For more information, see the "one-off README.txt" file. |
|
userUrl |
This entry holds the value of endpoint URL that is used to perform the create user operation. Default value: /odata/v2/User |
|
Bundle Name |
This entry holds the name of the connector bundle. Default value: org.identityconnectors.successfactors |
|
Bundle Version |
This entry holds the version of the connector bundle. Default value: 12.3.0 |
|
Connector Name |
This entry holds the name of the connector. Default value: org.identityconnectors.successfactors.SuccessFactorsConnector |
|
customURIs |
This entry holds the customURIs of the connector. Default value:
The default value supported from Release 12.2.1.3.0J: "groupId=/odata/v2/getDynamicGroupsByUser?userId='(Username)'&groupSubType='permission'" |
|
objectMetadatas |
This entry holds a comma separated list of object metadata information. During provisioning, each object requires a metadata entry in the payload. The metadata value is unique for each object entity. Default value: "UserEntity={\"uri\": \"User('Username')\"}","PerPerson={\"uri\": \"PerPerson('Username')\"}","EmpEmployment={\"uri\":\"EmpEmployment(personIdExternal='Username',userId='Username')\"}","EmpJob={\"uri\":\"EmpJob(userId='Username',startDate=datetime'DateTime')\"}","PerPersonal={\"uri\":\"PerPersonal(personIdExternal='Username',startDate=datetime'DateTime')\"}" |
|
childFields |
This attribute holds child data mapping. Default value: "groupId=groupId" The default value supported from Release 12.2.1.3.0J:"futureDatedHire=true" To mask the user information that can be PII (Personal Identifiable Information) or any security data printing in logs, add a new attribute: maskedAttributeList="empInfo/personNav/nationalIdNav/nationalId","empInfo/jobInfoNav" For more information, see the "one-off README.txt" file. |
3.3 Attribute Mappings
The attribute mappings on the Schema page vary depending on whether you are creating a target application or a trusted application.
3.3.1 Attribute Mappings for the Target Application
The schema page for a target application displays the default schema (provided by the connector) that maps Oracle Identity Governance attributes to target system columns. The connector uses these mappings during reconciliation and provisioning operations.
Default Attributes for SAP SuccessFactors Target Application
Table 3-3 lists the user-specific attribute mappings between the process form fields in Oracle Identity Governance and SAP SuccessFactors target application columns.
If required, you can edit the default attribute mappings by adding new attributes or deleting existing attributes as described in Creating a Target Application in Oracle Fusion Middleware Performing Self Service Tasks with Oracle Identity Governance.
Table 3-3 Default Attributes for SAP SuccessFactors Target Application
| Display Name | Target Attribute | Data Type | Mandatory Provisioning Property? | Provision Field? | Recon Field? | Key Field? | Case Insensitive? |
|---|---|---|---|---|---|---|---|
| Username | __NAME__ |
String |
Yes |
Yes |
Yes |
Yes |
Yes |
| Password | UserEntity.password | String |
No |
Yes |
No |
No |
NA |
| Server | Long |
Yes |
No |
Yes |
Yes |
NA |
|
| First Name | PerPersonal.firstName |
String |
Yes |
Yes |
Yes |
No |
NA |
| Last Name | PerPersonal.lastName |
String |
Yes |
Yes |
Yes |
No |
NA |
| UserEntity.email | String |
No |
Yes |
Yes |
No |
NA |
|
| Country | UserEntity.country |
String |
No |
Yes |
Yes |
No |
NA |
| State | UserEntity.state | String |
No |
Yes |
Yes |
No |
NA |
| City | UserEntity.city | String |
No |
Yes |
Yes |
No |
NA |
| Citizenship | UserEntity.citizenship | String |
No |
Yes |
Yes |
No |
NA |
| Employee Id | UserEntity.empId |
String |
No |
Yes |
Yes |
No |
NA |
| HR | UserEntity.hr | String |
No |
Yes |
Yes |
No |
NA |
| Job Level | UserEntity.jobLevel | String |
No |
Yes |
Yes |
No |
NA |
| Gender | PerPersonal.gender | String |
No |
Yes |
Yes |
No |
NA |
| Company | EmpJob.company |
String |
Yes |
Yes |
Yes |
No |
NA |
| Department | EmpJob.department |
String |
No |
Yes |
Yes |
No |
NA |
| JobClassification | EmpJob.jobCode |
String |
Yes |
Yes |
Yes |
No |
NA |
| Division | EmpJob.division |
String |
No |
Yes |
Yes |
No |
NA |
| Location | EmpJob.location |
String |
No |
Yes |
Yes |
No |
NA |
| Event Reason | EmpJob.eventReason | String |
Yes |
Yes |
Yes |
No |
NA |
| Business Unit | EmpJob.businessUnit |
String |
Yes |
Yes |
Yes |
No |
NA |
| Supervisor | EmpJob.managerId |
String |
Yes |
Yes |
Yes |
No |
NA |
| Hire Date | EmpEmployment.startDate |
String |
Yes |
Yes |
Yes |
No |
NA |
| Termination Date | EmpEmployment.endDate |
String |
No |
No |
Yes |
No |
NA |
| Person Id | __UID__ | String |
No |
Yes |
Yes |
No |
NA |
| Married | UserEntity.married | String |
No |
Yes |
Yes |
No |
NA |
| Status | __ENABLE__ | String |
No |
No |
Yes |
No |
NA |
Figure 3-1 Default Attribute Mappings for SAP SuccessFactors Target User Account
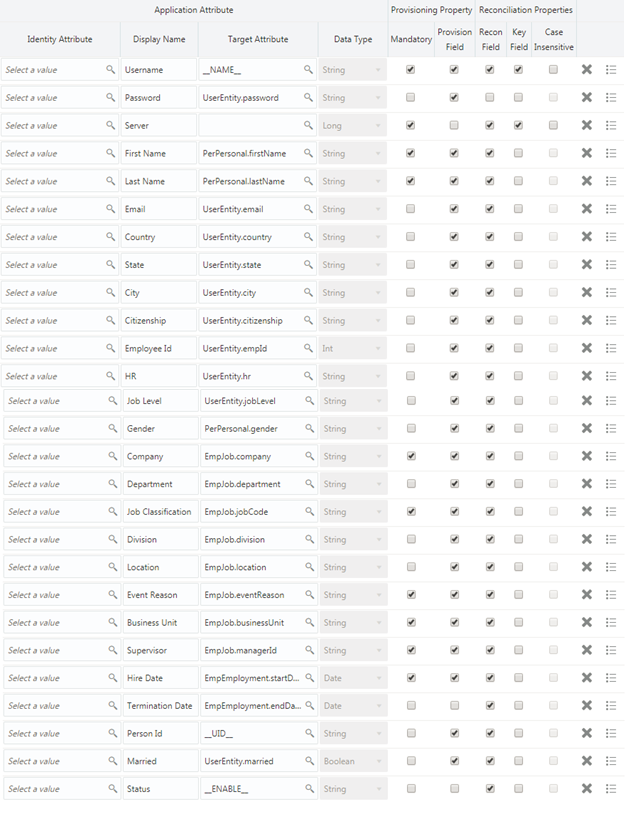
Description of "Figure 3-1 Default Attribute Mappings for SAP SuccessFactors Target User Account "
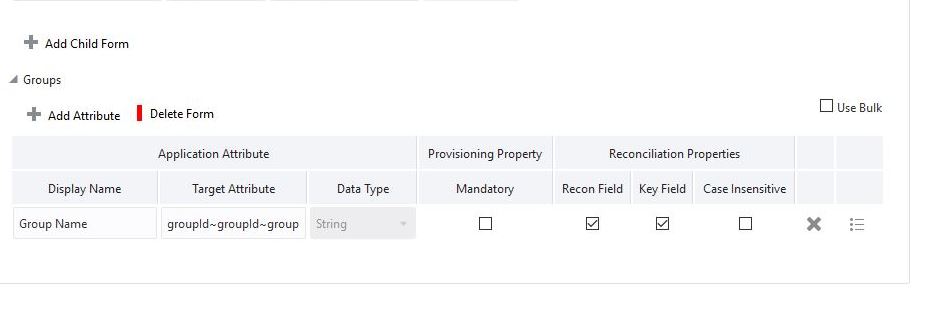
Table 3-4 Default Attributes for SAP SuccessFactors Group Management Child Form
| Display Name | Target Attribute | Data Type | Mandatory Provisioning Property? | Recon Field | Key Field | Case Insensitive |
|---|---|---|---|---|---|---|
|
Group Name |
gropId~groupId~groupId |
String |
No |
Yes |
Yes |
No |
Figure 3-2 shows the Group child form attribute mappings.
Figure 3-2 Group Child Form Attribute Mapping
3.3.2 Attribute Mappings for the Authoritative Application
The Schema page for an authoritative application displays the default schema (provided by the connector) that maps Oracle Identity Governance attributes to target system columns. The connector uses these mappings during reconciliation operations.
Table 3-5 lists the user-specific attribute mappings between the reconciliation fields in Oracle Identity Governance and SAP SuccessFactors columns. The table also lists the data type for a given attribute and specified whether it is a mandatory attribute for reconciliation.
If required, you can edit the default attribute mappings by adding new attributes or deleting existing attributes as described in Creating an Authoritative Application in Oracle Fusion Middleware Performing Self Service Tasks with Oracle Identity Governance.
You may use the default schema that has been set for you or update and change it before continuing to the next step.
The Organization Name, Xellerate Type, and Role identity attributes are mandatory fields on the OIG User form. They cannot be left blank during reconciliation. The target attribute mappings for these identity attributes are empty by default because there are no corresponding columns in the target system.
Table 3-5 Default Attributes for SAP SuccessFactors Authoritative Application
| Identity Display Name | Target Attribute | Data Type | Mandatory Recon Property? | Recon Field? | Default Value for Identity Display Name |
|---|---|---|---|---|---|
| End Date |
EmpEmployment.endDate |
Date |
No |
Yes |
NA |
| Hire Date |
EmpEmployment.startDate |
Date |
No |
Yes |
NA |
| Role |
String |
No |
Yes |
Full-Time |
|
| Organization Name |
String |
No |
Yes |
Xellerate Users |
|
| Xellerate Type |
String |
No |
Yes |
End-User |
|
| First Name |
PerPersonal.firstName |
String |
No |
Yes |
NA |
| Last Name |
PerPersonal.lastName |
String |
No |
Yes |
NA |
| User Login |
__NAME__ |
String |
No |
Yes |
NA |
| Display Name |
__UID__ |
String |
No |
Yes |
NA |
| Status |
__ENABLE__ |
String |
No |
Yes |
NA |
|
UserEntity.email |
String |
No |
Yes |
NA |
Figure 3-3 shows the default User account attribute mappings.
Figure 3-3 Default Attributes for SAP SuccessFactors Authoritative Application
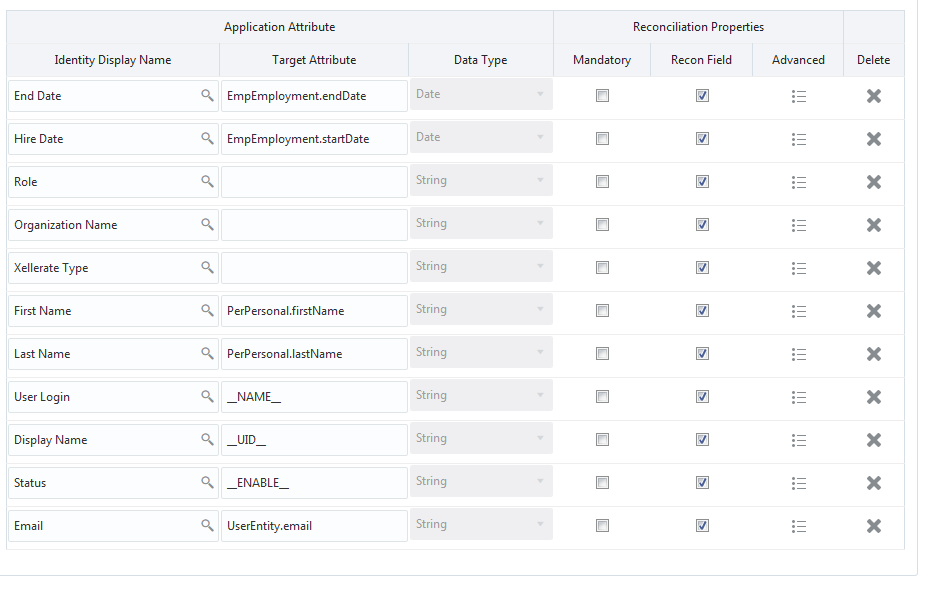
Description of "Figure 3-3 Default Attributes for SAP SuccessFactors Authoritative Application"
3.4 Correlation Rules
Learn about the predefined rules, responses and situations for Target and Trusted applications. The connector use these rules and responses for performing reconciliation.
3.4.1 Correlation Rules for the Target Application
When you create a target application, the connector uses correlation rules to determine the identity to which Oracle Identity Governance must assign a resource.
Predefined Identity Correlation Rules
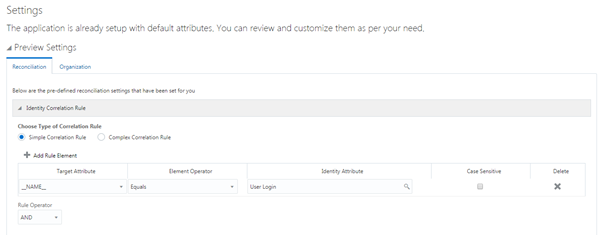
By default, the SAP SuccessFactors connector provides a simple correlation rule when you create a target application. The connector uses this correlation rule to compare the entries in Oracle Identity Governance repository and the target system repository, determine the difference between the two repositories, and apply the latest changes to Oracle Identity Governance.
Table 3-6 lists the default simple correlation rule for SAP SuccessFactors connector. If required, you can edit the default correlation rule or add new rules. You can create complex correlation rules also. For more information about adding or editing simple or complex correlation rules, see Creating a Target Application in Oracle Fusion Middleware Performing Self Service Tasks with Oracle Identity Governance.
Table 3-6 Predefined Identity Correlation Rule for SAP SuccessFactors Connector
| Target Attribute | Element Operator | Identity Attribute | Case Sensitive? |
|---|---|---|---|
|
__NAME__ |
Equals |
User Login |
No |
-
__NAME__ is a single-valued attribute on the target system that identifies the user account.
-
User Login is the field on the OIM User form.
-
Rule operator: AND
Figure 3-4 shows the simple correlation rule for SAP SuccessFactors target application.
Figure 3-4 Simple Correlation Rule for SAP SuccessFactors Application
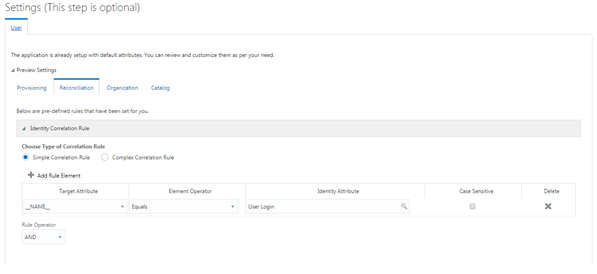
Description of "Figure 3-4 Simple Correlation Rule for SAP SuccessFactors Application"
Predefined Situations and Responses
The SAP SuccessFactors connector provides a default set of situations and responses when you create a target application. These situations and responses specify the action that Oracle Identity Governance must take based on the result of a reconciliation event.
Table 3-7 lists the default situations and responses for SAP SuccessFactors target application. If required, you can edit these default situations and responses or add new ones. For more information about adding or editing situations and responses, see Creating a Target Application in Oracle Fusion Middleware Performing Self Service Tasks with Oracle Identity Governance
Table 3-7 Predefined Situations and Responses for SAP SuccessFactors Target Application
| Situation | Response |
|---|---|
|
No Matches Found |
None |
|
One Entity Match Found |
Establish Link |
|
One Process Match Found |
Establish Link |
Figure 3-5 shows the situations and responses for SAP SuccessFactors that the connector provides by default.
Figure 3-5 Predefined Situations and Responses for SAP SuccessFactors Target Application
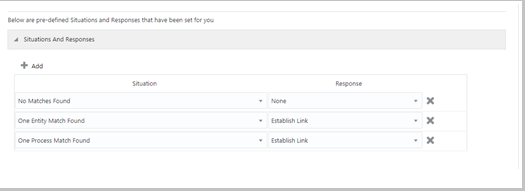
Description of "Figure 3-5 Predefined Situations and Responses for SAP SuccessFactors Target Application"
3.4.2 Correlation Rules for an Authoritative Application
When you create an authoritative application, the connector uses correlation rules to determine the identity to which Oracle Identity Governance must assign a resource.
Predefined Identity Correlation Rules
By default, the SAP SuccessFactors connector provides a simple correlation rule when you create an authoritative application. The connector uses this correlation rule to compare the entries in Oracle Identity Governance repository and the authoritative application repository, determine the difference between the two repositories, and apply the latest changes to Oracle Identity Governance.
Table 3-8 lists the default simple correlation rule for SAP SuccessFactors connector. If required, you can edit the default correlation rule or add new rules. You can create complex correlation rules also. For more information about adding or editing simple or complex correlation rules, see Creating a Target Application in Oracle Fusion Middleware Performing Self Service Tasks with Oracle Identity Governance.
Table 3-8 Predefined Identity Correlation Rule for SAP SuccessFactors Authoritative Application
| Authoritative Attribute | Element Operator | Identity Attribute | Case Sensitive? |
|---|---|---|---|
| _Name_ | Equals |
User Login |
No |
-
__Name__ is an attribute on the target system that uniquely identifies the user account.
-
User Login is the field on the OIM User form.
-
Rule operator: AND
Figure 3-6 shows the simple correlation rule for SAP SuccessFactors Authoritative application.
Figure 3-6 Simple Correlation Rule for SAP SuccessFactors Authoritative Application
Description of "Figure 3-6 Simple Correlation Rule for SAP SuccessFactors Authoritative Application"
Predefined Situations and Responses
The SAP SuccessFactors connector provides a default set of situations and responses when you create an authoritative application. These situations and responses specify the action that Oracle Identity Governance must take based on the result of a reconciliation event.
Table 3-9 lists the default situations and responses for SAP SuccessFactors Authoritative Application. If required, you can edit these default situations and responses or add new ones. For more information about adding or editing situations and responses, see Creating a Target Application in Oracle Fusion Middleware Performing Self Service Tasks with Oracle Identity Governance.
Table 3-9 Predefined Situations and Responses for SAP SuccessFactors Authoritative Application
| Situation | Response |
|---|---|
|
No Matches Found |
Create User |
|
One Entity Match Found |
Establish Link |
|
One Process Match Found |
Establish Link |
Figure 3-7 shows the situations and responses for SAP SuccessFactors that the connector provides by default.
Figure 3-7 Predefined Situations and Responses for the SAP SuccessFactors Authoritative Application
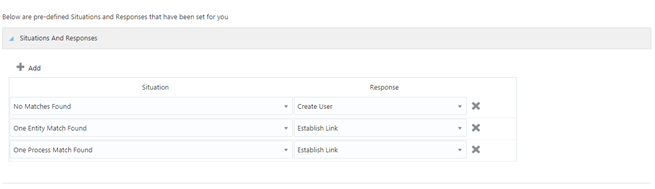
Description of "Figure 3-7 Predefined Situations and Responses for the SAP SuccessFactors Authoritative Application"
3.5 Reconciliation Jobs
These are the reconciliation jobs that are automatically created in Oracle Identity Governance after you create the application.
Depending on whether you want to implement authoritative source or target resource reconciliation, you must specify values for the attributes of one of the following user reconciliation scheduled jobs.
-
SAP SuccessFactors Target Resource User Reconciliation
This scheduled job is used to reconcile user data in the target resource (account management) mode of the connector.
-
SAP SuccessFactors Authoritative User Reconciliation
This scheduled job is used to reconcile user data in an authoritative source (identity management) mode of the connector.
User Reconciliation Job
Table 3-11 describes the parameters of Target User Reconciliation job.
Table 3-10 Parameters of the Scheduled Job for Target User Reconciliation
| Attribute | Description |
|---|---|
|
Application Name |
Name of the application you created for your target system. This value is the same as the value that you provided for the Application Name field while creating your target application. Do not modify this value. |
|
Object Type |
Type of object you want to reconcile. Default value: |
|
Filter Suffix |
Enter the search filter for fetching user records from the target system during a reconciliation run. Sample value: Note: This sample value is not mandatory and is used for limited reconciliation. |
|
Scheduled Task Name |
Name of the scheduled job. Note: For the scheduled job included with this connector, you must not change the value of this attribute. However, if you create a new job or create a copy of the job, then enter the unique name for that scheduled job as the value of this attribute. |
|
Incremental Recon Attribute |
Name of the target system column that holds holds the timestamp at which the user record was modified. Default value: |
|
Latest Token |
The parameter holds the value of the target system column that is specified as the value of the Incremental Recon Attribute parameter. The Latest Token parameter is used for internal purposes. By default, this value is empty. |
Table 3-11 describes the parameters of Authoritative User Reconciliation job.
Table 3-11 Parameters of the Scheduled Job for Authoritative User Reconciliation
| Attribute | Description |
|---|---|
|
Application Name |
Name of the application you created for your trusted application. This value is the same as the value that you provided for the Application Name field while creating your trusted application. Do not modify this value. |
|
Scheduled Task Name |
This parameter holds the name of the scheduled task. Default value: |
|
Filter Suffix |
Enter the search filter for fetching user records from the target system during a reconciliation run. Sample value: |
|
Object Type |
Type of object you want to reconcile. Default value: |
|
Incremental Recon Attribute |
Name of the target system column that holds holds the timestamp at which the user record was modified. Default value: |
|
Latest Token |
The parameter holds the value of the target system column that is specified as the value of the Incremental Recon Attribute. The Latest Token parameter is used for internal purposes. By default, this value is empty. |
Reconciliation Jobs for Lookup Field Synchronization
These lookup definitions are used as an input source for lookup fields in Oracle Identity Governance.
-
SuccessFactors HR Lookup Reconciliation Scheduled Job
-
SuccessFactors JobLevel Lookup Reconciliation Scheduled Job
-
SuccessFactors Supervisor Lookup Reconciliation Scheduled Job
-
SuccessFactors Group Lookup Reconciliation Scheduled Job
These reconciliation jobs are available only for a target application. The parameters for all the reconciliation jobs are the same.
The parameters for all the scheduled jobs for lookup field synchronization are the same. Table 3-12 describes the parameters of the scheduled jobs.
Table 3-12 Parameters of the Scheduled Jobs for Lookup Field Synchronization
| Attribute | Description |
|---|---|
|
Application Name |
Name of the application you created for your target system. This value is the same as the value that you provided for the Application Name field while creating your target application. Do not modify this value. |
|
Lookup Name |
Enter the name of the lookup definition in Oracle Identity Governance that must be populated with values fetched from the target system. |
|
Object Type |
Type of object you want to reconcile. Sample values: |
| Code Key Attribute | Name of the connector attribute that is used to populate the Code Key column of the lookup definition (specified as the value of the Lookup Name attribute).
Default value: __UID__ |
| Decode Attribute | Name of the connector attribute that is used to populate the Decode column of the lookup definition (specified as the value of the Lookup Name attribute).
Default value :__NAME__ |