Connect Your On-Premises Network to Supported SaaS Services Using FastConnect
FastConnect allows customers to establish direct, dedicated connectivity between on-premises networks and Oracle Cloud Infrastructure. Although SaaS applications are usually exposed and accessed over the internet, occasionally, customers might prefer to restrict access to their corporate networks only, and provide a dedicated, high bandwidth connectivity to SaaS Applications running in Oracle Cloud.
- Higher Bandwidth
- SLAs that are not available with public internet
Architecture
This architecture shows how to use FastConnect to connect an on-premises network to an Oracle Cloud Infrastructure region. In this example, the customer uses Private Peering to access their VCN resources, along with the Oracle Services Network and Public Peering, leveraging the Oracle Cloud Infrastructure backbone when required, to access supported SaaS applications running in the same or a separate region.
Note that when you use FastConnect Public Peering for connectivity to an OCI region, the routes advertised over the public virtual circuit might include routes to other Oracle Cloud Infrastructure regions and to specific Oracle Cloud Infrastructure Classic regions. This means that customers can leverage a single public virtual circuit to access services in any of the advertised regions.
The following diagram illustrates this architecture.
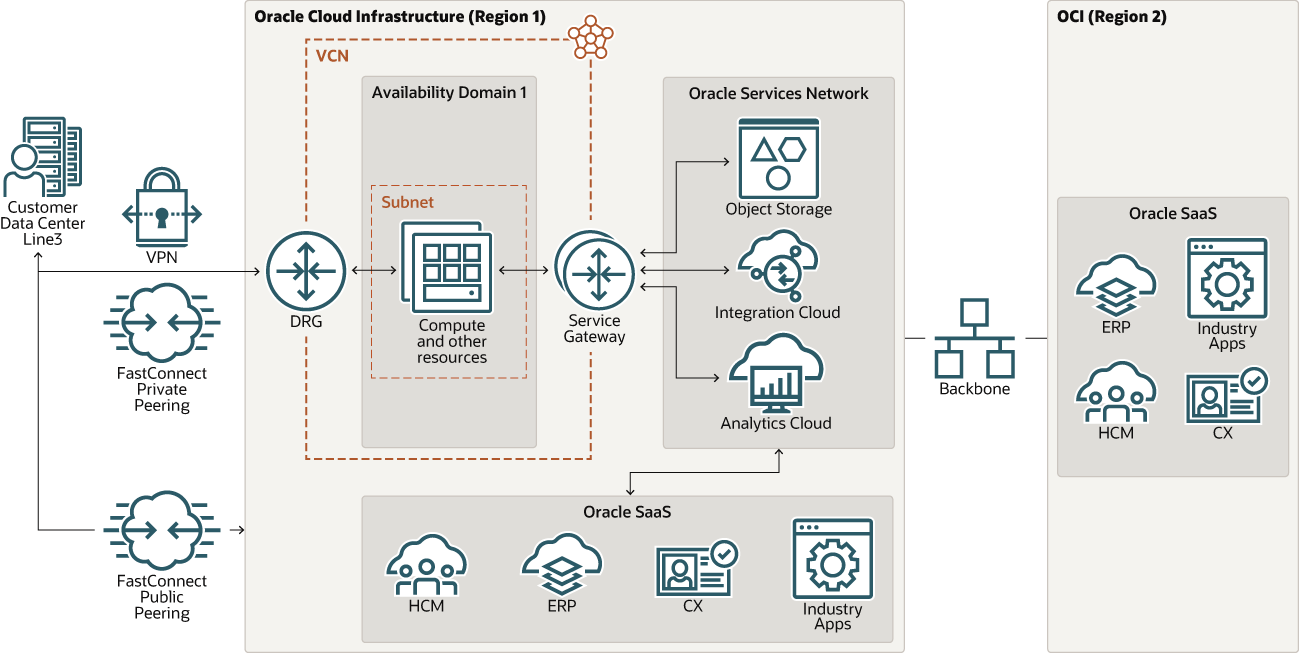
Description of the illustration fastconnect-saas-connect.png
- Region
An Oracle Cloud Infrastructure region is a localized geographic area that contains one or more data centers, called availability domains. Regions are independent of other regions, and vast distances can separate them (across countries or even continents).
- Availability domains
Availability domains are standalone, independent data centers within a region. The physical resources in each availability domain are isolated from the resources in the other availability domains, which provides fault tolerance. Availability domains don’t share infrastructure such as power or cooling, or the internal availability domain network. So, a failure at one availability domain is unlikely to affect the other availability domains in the region.
- Virtual cloud network (VCN) and subnets
A VCN is a customizable, software-defined network that you set up in an Oracle Cloud Infrastructure region. Like traditional data center networks, VCNs give you complete control over your network environment. A VCN can have multiple non-overlapping CIDR blocks that you can change after you create the VCN. You can segment a VCN into subnets, which can be scoped to a region or to an availability domain. Each subnet consists of a contiguous range of addresses that don't overlap with the other subnets in the VCN. You can change the size of a subnet after creation. A subnet can be public or private.
- Dynamic Routing Gateway (DRG)
A virtual router added to your VCN to provide a path for private network traffic between your VCN and on-premises network.
- Private peering
Extends existing infrastructure by using private IP addresses.
- Public peering
Allows public Oracle Cloud Infrastructure services to be accessed using a private connection instead of the internet.
- Service Gateway
A service gateway lets resources in your VCN privately and securely access Oracle services in the Oracle Services Network, without exposing your data on the internet.
- Backbone
Dedicated, secure network for interconnecting Oracle Cloud services running in different regions.
Recommendations
- VCN
When you create a VCN, determine the number of CIDR blocks required and the size of each block based on the number of resources that you plan to attach to subnets in the VCN. Use CIDR blocks that are within the standard private IP address space.
Select CIDR blocks that don't overlap with any other network (in Oracle Cloud Infrastructure, your on-premises data center, or another cloud provider) to which you intend to set up private connections.
After you create a VCN, you can change, add, and remove its CIDR blocks.
When you design the subnets, consider your traffic flow and security requirements. Attach all the resources within a specific tier or role to the same subnet, which can serve as a security boundary.
Use regional subnets.
- Security
Use Oracle Cloud Guard to monitor and maintain the security of your resources in Oracle Cloud Infrastructure proactively. Cloud Guard uses detector recipes that you can define to examine your resources for security weaknesses and to monitor operators and users for risky activities. When any misconfiguration or insecure activity is detected, Cloud Guard recommends corrective actions and assists with taking those actions, based on responder recipes that you can define.
For resources that require maximum security, Oracle recommends that you use security zones. A security zone is a compartment associated with an Oracle-defined recipe of security policies that are based on best practices. For example, the resources in a security zone must not be accessible from the public internet and they must be encrypted using customer-managed keys. When you create and update resources in a security zone, Oracle Cloud Infrastructure validates the operations against the policies in the security-zone recipe, and denies operations that violate any of the policies.
- Connectivity
When you deploy resources to Oracle Cloud Infrastructure, you might start small, with a single connection to your on-premises network.
To plan for redundancy, consider all the components (hardware devices, facilities, circuits, and power) between your on-premises network and Oracle Cloud Infrastructure. Also consider diversity, to ensure that facilities are not shared between the paths.
Considerations
Consider the following points when deploying this reference architecture.
- Performance
For Fusion SaaS, Oracle enables Akamai's Content Delivery Network (CDN) by default as a way to optimise the delivery of static and dynamic content. In particular, Akamai servers deliver several types of content: static and dynamic content over HTTP and HTTPS, and streaming audio and video over major streaming protocols. HTTP and HTTPS request to those content are forwarded to Akamai CDN. When customers opt to enable connectivity to their SaaS applications over FastConnect, a crucial step is to engage support to have Akamai disabled and thus direct access to the SaaS origin in the Oracle Cloud.
Customers should consider the performance impacts of disabling Akamai if their users are to continue to access SaaS applications over the internet.
- Security
FastConnect is a dedicated, private, and secure network connectivity option for connecting your on-premises locations to Oracle Cloud.
- Availability
When provisioning a FastConnect connection, it’s critical to ensure that each connection terminates on a different FastConnect router in Oracle Cloud to avoid any single points of failure. If you’re using FastConnect in a region that has two FastConnect POP locations, the redundant FastConnect can optionally be terminated at a router in the second FastConnect location. Pay special attention to the physical connectivity to ensure that it’s redundant and diverse. As you work with partners and carriers, ensure that they understand the physical connectivity of your existing connection so they can provide the diversity that you require.
- Cost
FastConnect ports are billed per hour. There is no charge for egress or ingress traffic. The cost of the virtual circuit or cross-connects (Direct or Colocated options) is not included with the port.