Connect Oracle Data Safe to Oracle Databases on multicloud and hybrid cloud environments
Oracle Data Safe delivers essential security services for Oracle Autonomous Database and databases running in OCI. Data Safe also supports on-premises databases, Oracle Exadata Cloud@Customer, and multicloud Oracle database deployments. All Oracle Database customers can reduce the risk of a data breach and simplify compliance by using Data Safe to assess configuration and user risk, monitor and audit user activity, and discover, classify, and mask sensitive data.
Compliance laws, such as the European Union (EU) General Data Protection Regulation (GDPR) and the California Consumer Privacy Act (CCPA), require companies to safeguard the privacy of their customers. Oracle Data Safe helps you understand data sensitivity, evaluate risks to data, mask sensitive data, implement and monitor security controls, assess user security, monitor user activity, and address data security compliance requirements.
- Security parameters
- Security controls in use
- User roles and privileges
- Center for Internet Security (CIS) Configuration - available for Oracle Database 12.2 and later.
- Security Technical Implementation Guidelines (STIG) - available for Oracle Database 21c and later.
- EU GDPR - European Union General Data Protection Regulation
- PCI-DSS - The Payment Card Industry Data Security Standard, and
- HIPPA- Health Insurance Portability and Accountability Act
Architecture
- Data Safe connecting to multicloud database deployments in non Microsoft Azure cloud environments
- Data Safe connecting to databases in Microsoft Azure using Database Service (ODSA)
- Well-architected framework for Oracle Cloud Infrastructure
- Deploy a secure landing zone that meets the CIS Foundations Benchmark for Oracle Cloud
- CIS Compliant OCI Landing Zones (GitHub repository)
Note:
Please refer to "Explore More", below, for access to these resources.Data Safe connecting to databases in a multicloud environment
When Oracle Databases are deployed in a multicloud environment then they can be seen as databases deployed on-premises. Either the private end-point or on-premises connector can be used. The following diagram shows the connection options for databases deployed on e.g. AWS and/or Microsoft Azure. Any cloud provider that can host Oracle databases can be used in this setup. By connecting to the databases deployed in a cloud provider using either private endpoint or the on-premises Data Safe connector enables Data Safe to inspect the databases.
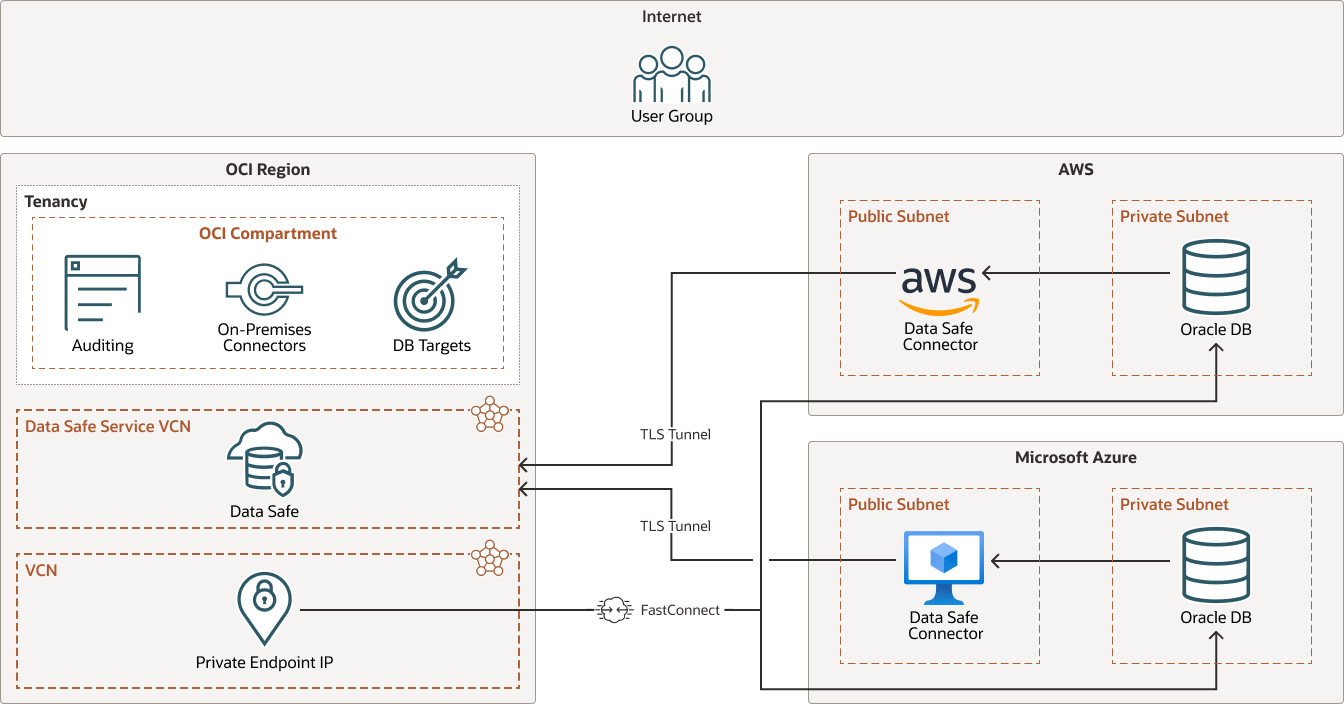
Description of the illustration datasafe-multi-odsa-01.png
datasafe-multi-odsa-01-oracle.zip
Data Safe connecting to databases in Microsoft Azure using Database Service (ODSA)
Connecting Data Safe to the databases that are part of Oracle Database Service for Azure (ODSA) is the same as for other OCI based databases. There are however some details you should consider when using the ODSA service. The following diagram illustrates the architecture for ODSA:
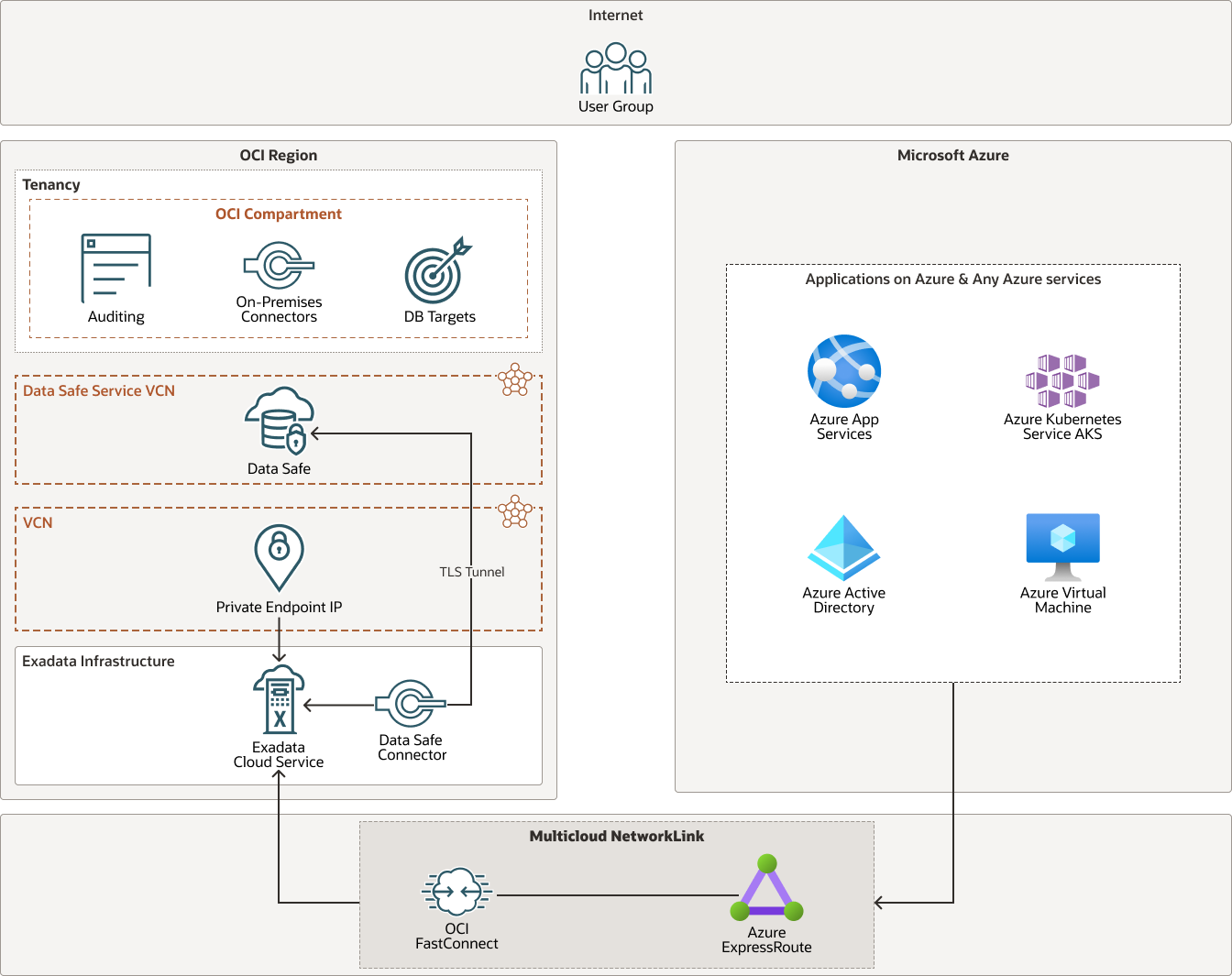
Description of the illustration datasafe-multi-odsa-02.png
datasafe-multi-odsa-02-oracle.zip
Because the databases are setup in a separate ODSA compartment some adjustments to policies may be necessary to provide access to these resources.
With Oracle Database Service for Microsoft Azure (ODSA) the database resources reside in an OCI tenancy that is linked to a Microsoft Azure account. In OCI, the databases and infrastructure resources are maintained in an ODSA compartment. This compartment is automatically created for ODSA resources during the sign up process. The ODSA Multicloud NetworkLink (see the diagram ) and account linking will be setup during the sign up process as well.
One of the prerequisites for ODSA is that your tenancy must support Identity Domains. Additionally, regional availability must be checked. The ODSA database resources need to be provisioned in these regions.
See The Multicloud Service Model, accessible from the Explore More topic, below for additional information on ODSA.
- Tenancy
A tenancy is a secure and isolated partition that Oracle sets up within Oracle Cloud when you sign up for OCI . You can create, organize, and administer your resources in Oracle Cloud within your tenancy. A tenancy is synonymous with a company or organization. Usually, a company will have a single tenancy and reflect its organizational structure within that tenancy. A single tenancy is usually associated with a single subscription, and a single subscription usually only has one tenancy.
- Region
An Oracle Cloud Infrastructure region is a localized geographic area that contains one or more data centers, called availability domains. Regions are independent of other regions, and vast distances can separate them (across countries or even continents).
- Compartment
Compartments are cross-region logical partitions within an Oracle Cloud Infrastructure tenancy. Use compartments to organize your resources in Oracle Cloud, control access to the resources, and set usage quotas. To control access to the resources in a given compartment, you define policies that specify who can access the resources and what actions they can perform..
- Availability domains
Availability domains are standalone, independent data centers within a region. The physical resources in each availability domain are isolated from the resources in the other availability domains, which provides fault tolerance. Availability domains don’t share infrastructure such as power or cooling, or the internal availability domain network. So, a failure at one availability domain is unlikely to affect the other availability domains in the region.
- Fault domains
A fault domain is a grouping of hardware and infrastructure within an availability domain. Each availability domain has three fault domains with independent power and hardware. When you distribute resources across multiple fault domains, your applications can tolerate physical server failure, system maintenance, and power failures inside a fault domain.
- Virtual cloud network (VCN) and subnets
A VCN is a customizable, software-defined network that you set up in an Oracle Cloud Infrastructure region. Like traditional data center networks, VCNs give you complete control over your network environment. A VCN can have multiple non-overlapping CIDR blocks that you can change after you create the VCN. You can segment a VCN into subnets, which can be scoped to a region or to an availability domain. Each subnet consists of a contiguous range of addresses that don't overlap with the other subnets in the VCN. You can change the size of a subnet after creation. A subnet can be public or private.
- Load balancer
The Oracle Cloud Infrastructure Load Balancing service provides automated traffic distribution from a single entry point to multiple servers in the back end. The load balancer provides access to different applications.
- Service gateway
The service gateway provides access from a VCN to other services, such as Oracle Cloud Infrastructure Object Storage. The traffic from the VCN to the Oracle service travels over the Oracle network fabric and never traverses the internet.
- Cloud Guard
You can use Oracle Cloud Guard to monitor and maintain the security of your resources in Oracle Cloud Infrastructure. Cloud Guard uses detector recipes that you can define to examine your resources for security weaknesses and to monitor operators and users for risky activities; for example, Cloud Guard can notify you when you have a database in your tenancy that is not registered with Data Safe. When any misconfiguration or insecure activity is detected, Cloud Guard recommends corrective actions and assists with taking those actions, based on responder recipes that you can configure.
- FastConnect
Oracle Cloud Infrastructure FastConnect provides an easy way to create a dedicated, private connection between your data center and Oracle Cloud Infrastructure. FastConnect provides higher-bandwidth options and a more reliable networking experience when compared with internet-based connections; for example, Cloud Guard can notify you if you have a database in your tenancy that is not registered with Data Safe.
- Autonomous Transaction Processing Autonomous Transaction Processing delivers a self-driving, self-securing, self-repairing database service that can instantly scale to meet demands of a variety of applications: mission-critical transaction processing, mixed transactions and analytics, IoT, JSON documents, and so on. When you create an Autonomous Database, you can deploy it to one of three kinds of Exadata infrastructure:
- Shared; a simple and elastic choice. Oracle autonomously operates all aspects of the database life cycle from database placement to backup and updates.
- Dedicated on Public Cloud; a private cloud in public cloud choice. A completely dedicated compute, storage, network and database service for only a single tenant, providing for the highest levels of security isolation and governance.
- Dedicated on Cloud@Customer; Autonomous Database on dedicated infrastructure running on on Exadata Database Machine system in your data center, together with the networking configuration that connects it to Oracle Cloud.
- Exadata DB system
Exadata Cloud Service enables you to leverage the power of Exadata in the cloud. You can provision flexible X8M systems that allow you to add database compute servers and storage servers to your system as your needs grow. X8M systems offer RoCE (RDMA over Converged Ethernet) networking for high bandwidth and low latency, persistent memory (PMEM) modules, and intelligent Exadata software. You can provision X8M or X9M systems by using a shape that's equivalent to a quarter-rack X8 system, and then add database and storage servers at any time after provisioning.
Recommendations
- Security
Use Oracle Cloud Guard to monitor and maintain the security of your resources in Oracle Cloud Infrastructure proactively. Cloud Guard uses detector recipes that you can define to examine your resources for security weaknesses and to monitor operators and users for risky activities. When any misconfiguration or insecure activity is detected, Cloud Guard recommends corrective actions and assists with taking those actions, based on responder recipes that you can define.
For resources that require maximum security, Oracle recommends that you use security zones. A security zone is a compartment associated with an Oracle-defined recipe of security policies that are based on best practices. For example, the resources in a security zone must not be accessible from the public internet and they must be encrypted using customer-managed keys. When you create and update resources in a security zone, Oracle Cloud Infrastructure validates the operations against the policies in the security-zone recipe, and denies operations that violate any of the policies.
- Cloud Guard
Clone and customize the default recipes provided by Oracle to create custom detector and responder recipes. These recipes enable you to specify what type of security violations generate a warning and what actions are allowed to be performed on them. For example, you might want to detect Object Storage buckets that have visibility set to public.
Apply Cloud Guard at the tenancy level to cover the broadest scope and to reduce the administrative burden of maintaining multiple configurations.
You can also use the Managed List feature to apply certain configurations to detectors.
- Network security groups (NSGs)
You can use NSGs to define a set of ingress and egress rules that apply to specific VNICs. We recommend using NSGs rather than security lists, because NSGs enable you to separate the VCN's subnet architecture from the security requirements of your application.
- Load balancer bandwidth
While creating the load balancer, you can either select a predefined shape that provides a fixed bandwidth, or specify a custom (flexible) shape where you set a bandwidth range and let the service scale the bandwidth automatically based on traffic patterns. With either approach, you can change the shape at any time after creating the load balancer.
Explore More
Learn more about connecting Oracle Data Safe to Oracle databases running on multicloud and hybrid cloud environments.
Review these additional resources:
- Well-architected framework for Oracle Cloud Infrastructure
- What is multicloud?
- Register an Oracle Database on a Compute Instance
- Deploy a secure landing zone that meets the CIS Foundations Benchmark for Oracle Cloud
- Implement Oracle Data Safe for your on-premises and OCI deployed databases
- The Multicloud Service Model
- oci-landing-zones / terraform-oci-core-landingzone (OCI Core Landing Zone) on GitHub.
- oci-landing-zones / oci-landing-zone-operating-entities (Operating Entities Landing Zone) on GitHub