Learn How to Extend SaaS Applications With a Cloud Native Approach
As businesses adopt more SaaS, the ability to extend to meet changing business requirements becomes more important. Before Cloud Native, IT teams were faced with the realities of either selecting a set of vendors offered integration solutions, providing simplistic use cases, or setting up rather large stacks of infrastructures to support their more complex use-cases. Customers using Oracle Java Cloud Service - SaaS Extension often host SaaS UI extensions, which are typically built using the Oracle ADF Framework, or they use the service to host some code (a REST entry point) which is either called by Oracle Fusion Applications Cloud Service or another application. Oracle Java Cloud Service - SaaS Extension is a legacy cloud service lacking the features of modern Oracle Cloud Native offerings.
Cloud Native introduces capabilities such as containers, and serverless functions. By using these offerings, your development team can focus on completing their use case while offloading the complexity of the infrastructure to your cloud provider. Oracle Cloud Native Services provides the capabilities that your development team needs to extend your SaaS applications in a manner that is much easier to implement and maintain.
Architecture
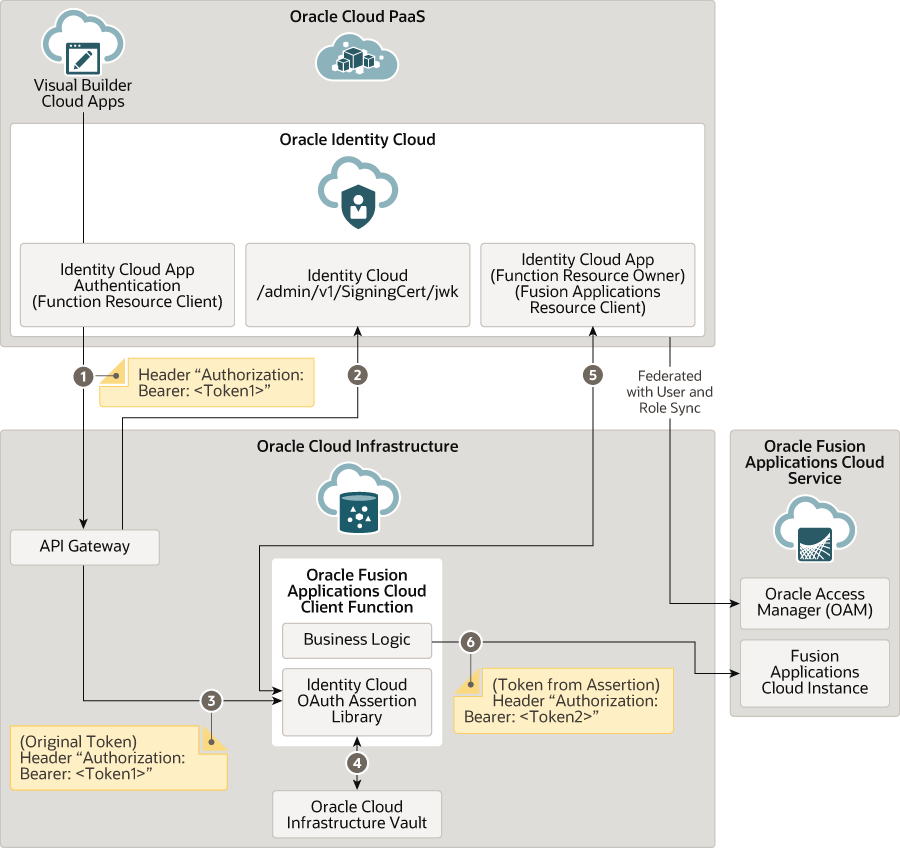
This architecture shows a high-level design for an extension of a SaaS application, built using a Cloud Native approach. You can use Oracle Functions as the backend implementation of a REST API, secured by Oracle Identity Cloud Service.
The implementation is accomplished by making use of the Oracle Cloud Infrastructure API Gateway. This solution playbook presents a use case for extending Oracle Fusion Applications Cloud Service, but the same techniques can be used with or without SaaS in the picture.
The following flow is depicted:
- Oracle Visual Builder connects to the API Gateway via an Identity Cloud App Authentication (Function Resource Client) application within Oracle Identity Cloud Service. An authentication token with the header "Authorization: Bearer; <Token1>" is included.
- API gateway connects back to Oracle Identity Cloud Service, connecting to the Identity Cloud /admin/v1/SigningCert/jwk component to validate the token.
- API Gateway connects to the Identity Cloud OAuth Assertion Library integrated with the Oracle Function, with the original token with the same header as the token for step 1.
- The Identity Cloud OAuth Assertion Library integrated with the Oracle Function connects to Oracle Cloud Infrastructure Vault, to look up stored, secure credentials for the next step.
- The Function connects back to Oracle Identity Cloud Service, to fetch a new token from the Identity Cloud App (Function Resource Owner) (Fusion Applications Resource Client) application. This token is valid for a user that exists in both Oracle Cloud PaaS and Oracle Fusion Applications.
- The Business Logic component within Oracle Fusion Applications Cloud Client Function connects to a Fusion Applications Cloud Instance, using a new authentication token (Token from Assertion) with the header "Authorization: Bearer; <Token2>"
API Gateway can either directly authenticate with Oracle Identity Cloud Service, or, optionally, execute a custom authentication function (not shown in the diagram).
Before You Begin
In order to make secured REST API calls from Oracle PaaS to Oracle Fusion Applications Cloud Service, you must configure an integration using Oracle Identity Cloud Service. Refer to these solution playbooks with comprehensive instructions for configuring such an integration:
- Integrate an Oracle SaaS application with Oracle PaaS
- Access PaaS data from a cloud application using web services
To use Oracle Functions with Oracle Cloud Infrastructure, you need to set up your environment:
- Review the Oracle Functions Quick Start Guides to quickly set up a development environment.
- Comprehensive client environment configuration is found in the Preparing for Oracle Functions section of the Oracle Cloud Infrastructure Documentation .
About the Design Requirements
As businesses adopt more cloud-based software (Software as a Service, or SaaS), the ability to extend to meet changing business requirements has become more important. Before Cloud Native, IT teams were faced with the realities of either selecting a set of vendor-offered integration solutions, which provide simplistic use cases; or setting up complex and unwieldy stacks of infrastructures to support their more complex use cases.
Cloud Native introduces new capabilities, such as containers and serverless functions. By using these offerings, your development teams can focus on completing their use case while offloading the complexity of the infrastructure to the cloud provider. Oracle Cloud Native Services provides the capabilities that your development teams need to extend their SaaS applications in a manner that is much easier to implement and maintain.
Oracle Functions is a functions-as-a-service (FaaS) offering from Oracle which allows developers the ability to execute code in the cloud and only pay for the processing power used, thus avoiding the need to run the service 24x7. The additional advantage is that the infrastructure needed to run the code is fully Oracle managed and does not require the customer/developer to maintain the run-time environment.
When using the new Oracle Cloud Infrastructure API Gateway service with Oracle Functions, development teams can create serverless APIs that unlock the power of serverless functions to applications such as Oracle Fusion Applications Cloud Service that easily integrate with RESTful APIs.
If you compare this to an Oracle Java Cloud Service or WebLogic Server Cloud instance, where you are responsible for the maintenance and management of the software, the associated operating system hosting the WebLogic Server, and often a database, this “Fully Oracle-Managed approach” is very attractive.
You may already be using Oracle Java Cloud Service - SaaS Extension. For example, you could be using the service to host SaaS UI Extensions, which are typically built using the Oracle ADF Framework. Another common use case is to host some code (a REST entry point) which is either called by Oracle Fusion Applications Cloud Service or another application. If you would like to move platform, then Oracle often recommends a migration to Oracle Visual Builder.
Let's consider the following design requirements, which may be similar to your own. A customer currently has their application deployed on Oracle Java Cloud Service - SaaS Extension and is using the Oracle ADF Faces framework. The customer wishes to migrate to a more modern platform and the platform must be Oracle managed – after all they are a SaaS customer and are used to things being managed for them. And of course, there is always the requirement that the implementation be secure.
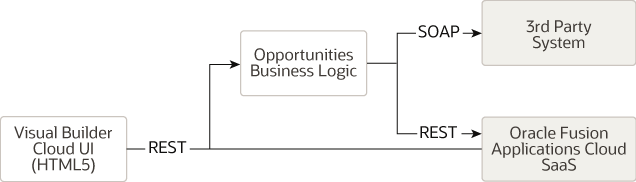
They have therefore decided to use Oracle Visual Builder to implement their UI. This customer may want to do some complex business logic before calling Oracle SaaS, such as caching, aggregation of data, complex logic, or perhaps protocol conversion (REST to SOAP). After some investigation they have determined that most of the network requests can go directly to Oracle SaaS, but some of the calls will need to go through a middle tier to handle the business logic rather than directly calling the API.
For this customer, Oracle presents an architecture that uses Oracle Functions as the middle tier for their custom business logic code.
Let's summarize the design requirements:
- Extend Oracle Fusion Applications Cloud Service with customizations and REST-based data access
- Use Oracle-managed Cloud platform
- Implement REST verbs (GET, POST, PUT, etc.)
- Use Oracle Visual Builder for simpler, low-code customization
- Cloud native serverless approach to run code without requiring infrastructure provisioning or management
- Efficient low-overhead Oracle Functions can handle calls that require complex business logic
- Handle identity propagation to the target SaaS system for secure, authenticated, authorized access control with SSO
- API endpoints must be secured
- Implement Cross-Origin Resource Sharing (CORS) to issue REST calls directly to the REST server.
To meet these requirements, four more services are included in the architecture:
- Oracle Identity Cloud Service: A global identity store.
- Oracle Functions: Customize SaaS APIs with your own code.
- Oracle Cloud Infrastructure API Gateway: An API gateway which will handle the REST to Functions mapping and enforce security.
- Oracle Cloud Infrastructure Vault: a key management mechanism used to encrypt passwords and client secrets.
Oracle Cloud Infrastructure API Gateway has built-in capability to communicate with Oracle Identity Cloud Service. However, to demonstrate how to use custom Oracle Functions code with API Gateway, we have provided a custom authentication function (AuthN) as an optional authentication mechanism.
About Required Services and Roles
This solution requires the following services and roles:
- Oracle Fusion Applications Cloud Service
- Oracle Visual Builder
- Oracle Cloud Infrastructure
- Oracle Identity Cloud Service
These are the roles needed for each service.
| Service Name: Role | Required to... |
|---|---|
| Oracle Fusion Applications Cloud Service: Administrator | Configure single sign-on between Oracle Fusion Applications Cloud Service and Oracle Identity Cloud Service. |
Oracle Visual Builder: The Visual Builder Developer predefined role that maps to the
ServiceDeveloper application-layer predefined
role.
|
Create, manage, secure, and publish web and mobile applications. |
| Oracle Cloud Infrastructure: Administrator | Deploy functions, and configure the API Gateway. |
| Oracle Identity Cloud Service: Security Administrator and Application Administrator | Manage identity providers and manage applications. |
See Learn how to get Oracle Cloud services for Oracle Solutions to get the cloud services you need.