Learn About Setting up SSO between Azure AD and Oracle Identity Cloud Service
When you move your E-Business Suite application to the cloud and provide access to the application through Microsoft Azure, then users have to sign in to Azure portal and also re-enter credentials to sign in to E-Business Suite applications.
Identity federation helps enterprises reduce cost, because user accounts don’t need to be created and managed separately in each identity management system. The user-synchronization process ensures that identities are propagated to all the federated systems.
Before You Begin
See Learn about interconnecting Oracle Cloud with Microsoft Azure.
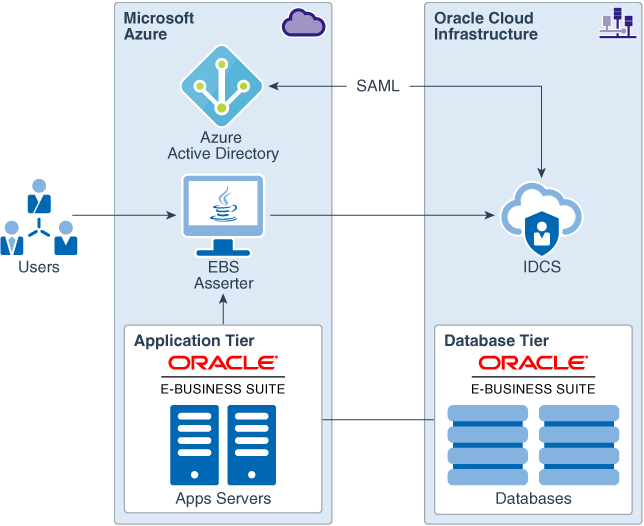
Architecture
This architecture diagram covers a pattern for setting up SSO with Oracle applications like E-Business Suite in which Oracle Identity Cloud Service acts as a bridge between the applications and Azure AD. This setup enables scenarios in which users can host Oracle Database in Oracle Cloud Infrastructure while using Azure AD as their identity provider.
The diagram shows how the E-Business Suite Asserter and E-Business Suite interacts with Oracle Identity Cloud Service. The E-Business Suite Asserter is deployed to a separate Oracle WebLogic Server instance and it interacts with Oracle Identity Cloud Service through OpenID Connect (OIDC). The E-Business Suite Asserter redirects the user's web browser to Oracle Identity Cloud Service and to E-Business Suite.
Authentication Flow
When you run an application in Microsoft Azure connected to a database in Oracle Cloud, Azure AD can be the identity provider (IDP) to hold user credentials.
The following diagram shows the user authentication flow. 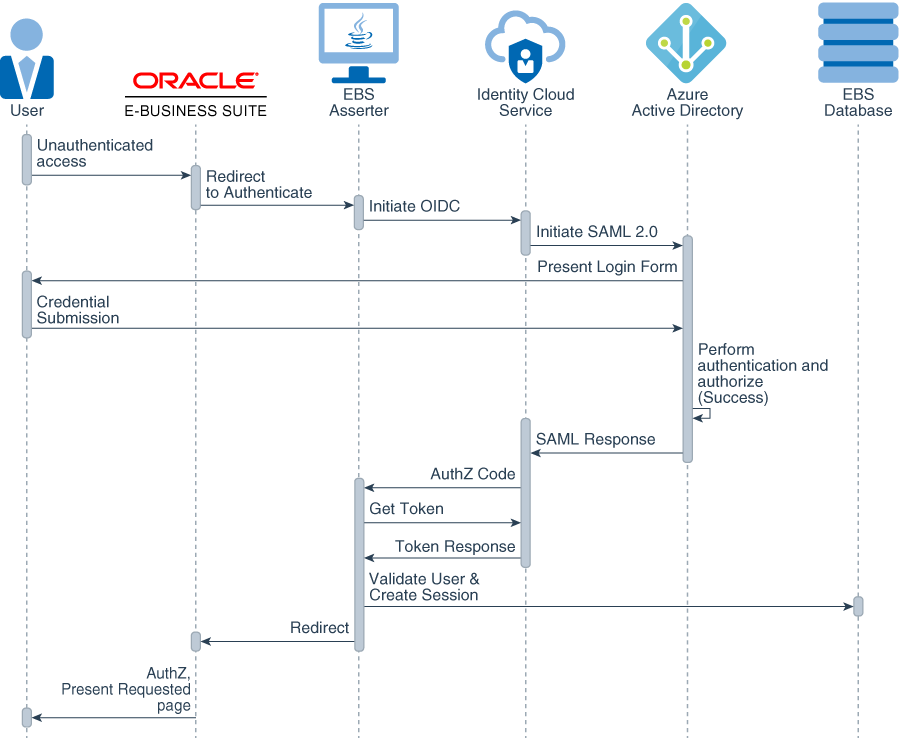
Description of the illustration ebs-auth-flow.png
A user accesses the E-Business Suite application directly by going to the E-Business Suite AppsLogin page or the My Apps portal. The following steps explain the authentication flow between the different components:
- The user requests access to an Oracle E-Business Suite protected resource.
- Oracle E-Business Suite redirects the user browser to the E-Business Suite Asserter application.
- The E-Business Suite Asserter uses an Oracle Identity Cloud Service SDK to generate the authorization URL and then redirects the browser to Oracle Identity Cloud Service.
- Oracle Identity Cloud Service redirects the user to Azure AD.
- The user provides the credentials needed to sign in to the application.
- After Azure AD performs user authentication, it generates a SAML token and sends it to Oracle Identity Cloud Service via browser.
- Oracle Identity Cloud Service consumes the authentication token, generates an OpenID Connect (OIDC) token, and issues the token to E-Business Suite Asserter.
- The E-Business Suite Asserter creates an Oracle E-Business Suite cookie and redirects the user browser to Oracle E-Business Suite.
- Oracle E-Business Suite presents the user requested protected resource.
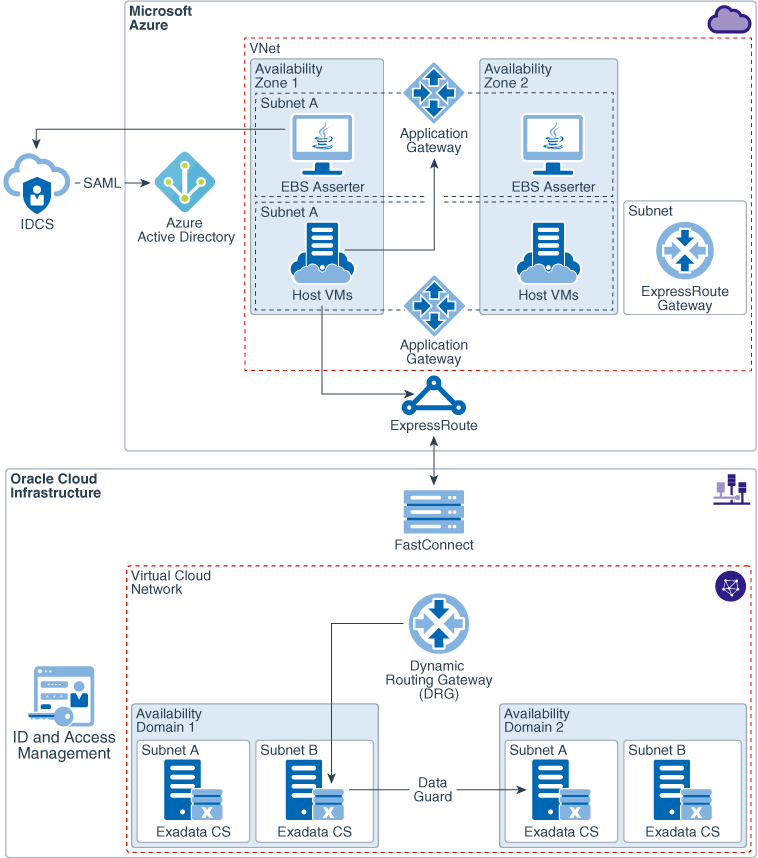
Network Security and High Availability of E-Business Suite Asserter
To communicate with Identity Cloud Service, check if your E-Business Suite Asserter VM has a public IP address or if your asserter is behind a public load balancer, then make sure that the asserter can reach the Oracle Identity Cloud Service token endpoint.
For added security, you should place the E-Business Suite Asserter virtual machine in its own subnet within the Azure Virtual Network (VNet) and configuring the network security group (NSG) to control the network traffic flow.
About Required Services, Products and Roles
An Oracle Identity Cloud Service administrator must be able to access the Oracle Identity Cloud Service console to configure and activate applications.
- Oracle Identity Cloud Service
- Oracle Cloud Infrastructure
- A fully functional Oracle's E-Business Suite instance deployed on Microsoft Azure
- Microsoft Azure
These are the roles needed for each service.
| Service Name: Role | Required to... |
|---|---|
| Server administrator | Configure E-Business Suite and change security settings |
| Identity domain administrator: Security administrator | Register an application |
| Azure contributor or greater privileged account | Get Azure subscription |
| Application administrator or Global administrator | Handle configuration and set up on the Azure side |
See Learn how to get Oracle Cloud services for Oracle Solutions to get the cloud services you need.