Understanding Oracle RightNow Adapter Security Management
The Oracle RightNow adapter uses the Credentials Store Framework to store credentials captured during the configuration of connections within the Oracle RightNow adapter configuration wizard. This ensures that the credentials captured during configuration are stored in secured form and are not stored with the SOA Composite or Oracle Service Bus flow.
At runtime, the adapter automatically retrieves the credentials from the Credentials Store Framework based on the CSF_KEY that was specified during design time. These credentials are injected into the SOAP header of the document that is sent to the RightNow Cx Server for authentication.
Authenticating on the Oracle RightNow Cx Server with Account Passwords
The following section provides information about authenticating on the Oracle RightNow Cx Server with account passwords. This section includes:
Oracle Cloud Connect Web Services for SOAP Site Configuration
Access to the Oracle Cloud Connect Web Services for SOAP is available only on those sites that have it enabled. If Oracle Cloud Connect Web Services for SOAP is not enabled, contact your Oracle account manager, as the API will not function and a request error will be returned.
Request errors are generated any time there is a validation failure or a data related error of the inbound request. The exception code will be ACCESS_DENIED and the message will be the message base string for SOAP_SERVER_DISABLED.
For complete information on request errors and exception codes, see Oracle Connect Web Services for SOAP.
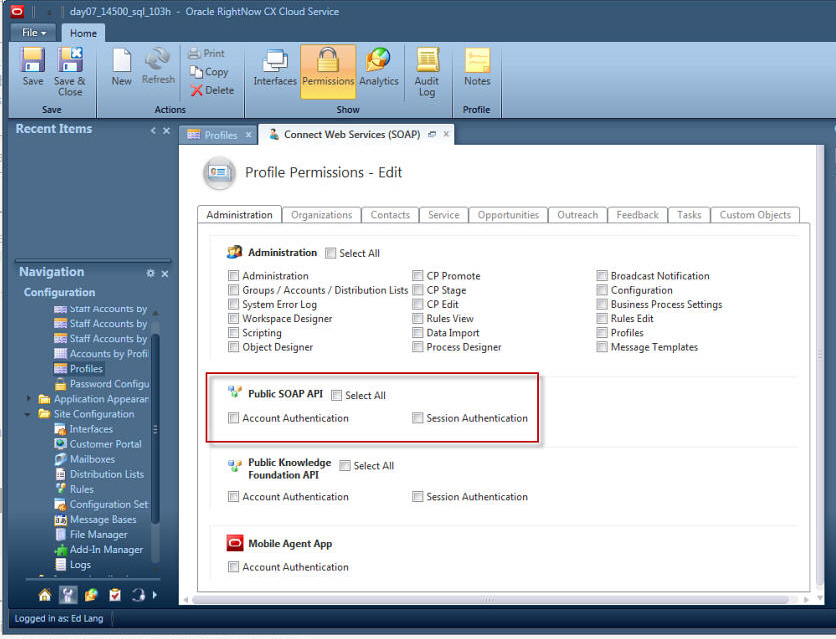
Before staff accounts can be authenticated through Oracle RightNow Cx, their profile(s) must be updated on the Profile Permissions editor in Oracle RightNow Cx. The permissions check boxes are located at Staff Management > Profiles > Permissions.
Figure 4-5 Location of Permissions Checkboxes
In addition, RightNow Cx administrators can restrict access to Oracle Cloud Connect Web Services for SOAP integrations by IP address using the configuration settings in the Oracle RightNow Cx platform. The following setting is located at Site Configuration > Configuration Setting.
-
SEC_PAPI_INTEG_HOSTS_SOAP: Defines which hosts are allowed to access the SOAP interface. Valid entries include a comma-separated list of domain names with wild cards, specific IP addresses, or IP subnet masks (for example, *.rightnow.com,1.2.3.4, 10.11.12.0/255.255.255.0).Only users logging in from hosts matching entries in this list are allowed access to the SOAP interface. The default is blank.
Validating Account Credentials
When a request is sent to the API and the site configuration has been validated, the next step is to validate the account credentials. If the credentials do not verify, a request error is returned. The exception code will be INVALID_LOGIN, and the message will be the message base string LOGIN_ID_PASSWD_COMBINATION_INV_MSG.
Profile Configuration
The profile for the staff account which is used in the security header must have the Public SOAP API profile bit enabled. If this bit is not enabled, a request error is returned. The exception code will be ACCESS_DENIED, and the message will be the message base string PROFILE_NO_SOAP_ACCESS_MSG.
Password-based Authentication
Oracle Cloud Connect Web Service for SOAP utilizes Web Services Policy 1.2 is defined by http://specs.xmlsoap.org/ws/2004/09/policy/ws-policy.pdf for client authentication.
The supporting XSD for the security policy is located at http://schemas.xmlsoap.org/ws/2004/09/policy/ws-policy.xsd.
To authenticate with single sign-on, refer to Authenticating with SAML 2.0.
The WS-Security specification calls for a Security tag in the SOAP Header with a namespace of
http://docs.oasis-open.org/wss/2004/01/oasis-200401-wss-wssecurity-secext-1.0.xsd.
Inside the Security tag is a UsernameToken tag (part of the WS-Security UsernameToken Profile 1.0 specification). The UsernameToken tag contains elements for Username, Password, Nonce, and Created. The Password element has a Type attribute which specifies if the content of the Password element is PasswordText. Oracle Cloud Connect Web Services for SOAP does not support PasswordDigest.
The Nonce and Created elements are not supported. If a request is received that contains the PasswordDigest type or the Created/Nonce elements, the server rejects the request as a malformed request.
The following is an example SOAP request with username and password credentials:
Example 4-1 Example SOAP Request with Username and Password Credentials
soapenv:Envelope xmlns:soapenv="http://schemas.xmlsoap.org/soap/envelope/">
<soapenv:Header>
<wsse:Security xmlns:wsse="http://docs.oasis-open.org/wss/2004
/01/oasis-200401-wss-wssecurity-secext-1.0.xsd"
soapenv:mustUnderstand="1">
<wsse:UsernameToken
xmlns:wsu="http://docs.oasis-open.org/wss/2004/01/
oasis-200401-wss-wssecurity-utility-1.0.xsd"
wsu:Id="UsernameToken-3902281">
<wsse:Username>comland</wsse:Username>
<wsse:Password Type=
"http://docs.oasis-open.org/wss/2004
/01/oasis-200401-wss-username-token-profile-1.0
#PasswordText">Connect1</wsse:Password>
</wsse:UsernameToken>
</wsse:Security>
</soapenv:Header>
</soapenv:Envelope>