| Skip Navigation Links | |
| Exit Print View | |
|
Oracle Identity Synchronization for Windows 6.0 Installation and Configuration Guide |
| Skip Navigation Links | |
| Exit Print View | |
|
Oracle Identity Synchronization for Windows 6.0 Installation and Configuration Guide |
Part I Installing Identity Synchronization for Windows
Opening the Identity Synchronization for Windows Console
To Open Identity Synchronization for Windows Console
Creating a Sun Java System Directory Source
To Create a New Sun Java System Directory Source
Preparing Sun Directory Source
To Prepare your Directory Server Source
Creating an Active Directory Source
To Configure and Create Windows Active Directory Servers in a Network
Creating a Windows NT SAM Directory Source
To Deploy Identity Synchronization for Windows on Windows NT
Selecting and Mapping User Attributes
Selecting and Mapping Attributes
To Select and Map Attributes for Synchronization
Creating Parameterized Default Attribute Values
To Change the Default Schema Source
Propagating User Attributes Between Systems
Specifying How Object Creations Flow
To Specify How Object Creations Should Flow Between Directory Server and Active Directory Systems
Specifying New Creation Attributes
Specifying How Object Modifications Flow
Configuring and Synchronizing Object Activations and Inactivations
Specifying Configuration Settings for Group Synchronization
Configuring and Synchronizing Account Lockout and Unlockout
Prerequisites for Account Lockout
Using the Account Lockout Feature
To Specify how Deleted Entries Flow Between Directory Server and Active Directory Systems
Creating Synchronization User Lists
To Identify and Link User Types Between Servers
To Save your Current Configuration from the Console Panels
6. Synchronizing Existing Users and User Groups
9. Understanding Audit and Error Files
Part II Identity Synchronization for Windows Appendixes
A. Using the Identity Synchronization for Windows Command Line Utilities
B. Identity Synchronization for Windows LinkUsers XML Document Sample
C. Running Identity Synchronization for Windows Services as Non-Root on Solaris
D. Defining and Configuring Synchronization User Lists for Identity Synchronization for Windows
E. Identity Synchronization for Windows Installation Notes for Replicated Environments
After you create and map the user attributes you want to synchronize, you must tell Identity Synchronization for Windows how to propagate (flow) the attribute creations, modifications, and deletions between your Directory Server and Windows Systems.
By default, Identity Synchronization for Windows:
Synchronizes from Windows to Directory Server only
Synchronizes the password attribute only (unless you specified significant attributes in the previous section)
Does not synchronize the creation or deletion of entries
This section explains how to configure attribute synchronization between systems. The information is organized as follows:
Figure 4-33 Selecting and Propagating Creations
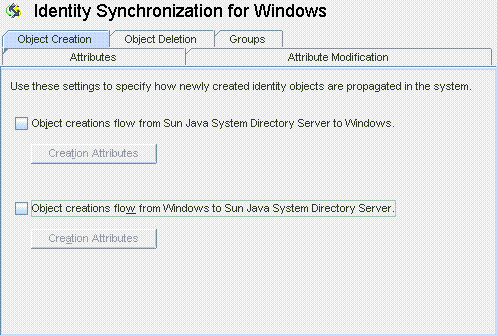
Enable Object creations flow from Sun Java System Directory Server to Windows to propagate creations from the Directory Server environment to your Windows servers.
Enable Object creations flow from Windows to Sun Java System Directory Server to propagate creations from the Windows environment to your Directory Servers.
Enable both options for bidirectional flow.
Disable both options to prevent user creations from propagating from one system to the other. (Default).
The Creation Attribute Mappings and Values dialog box displays.
Figure 4-34 Creation Attributes Mappings and Values: Directory Server to Windows
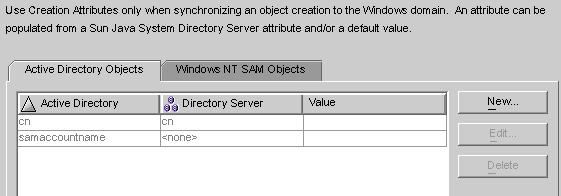
Figure 4-35 Creation Attributes Mappings and Values: Windows to Directory Server
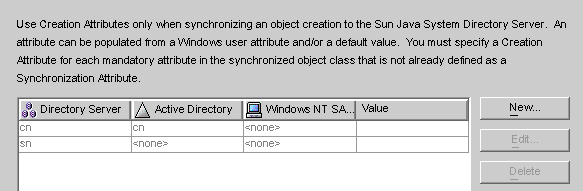
You can use either of the dialog boxes to specify new creation attributes, edit, or delete existing attributes. For more information, see Specifying New Creation Attributes.
Note - To satisfy schema constraints regarding required attributes for user object classes, you may have to specify additional attributes to flow through the system during a user creation.
Additional attributes are not necessary if you specified the required attributes as modification attributes (as described in Selecting and Mapping User Attributes).
The following instructions explain how to add and map creation attributes from Active Directory to Directory Server. (The procedure for adding and mapping creation attributes flowing from Directory Server to Windows and from Windows to Directory Server is similar.)
The Define Creation Attribute Mappings and Values dialog box is displayed.
Figure 4-36 Defining Creation Attribute Mappings and Values
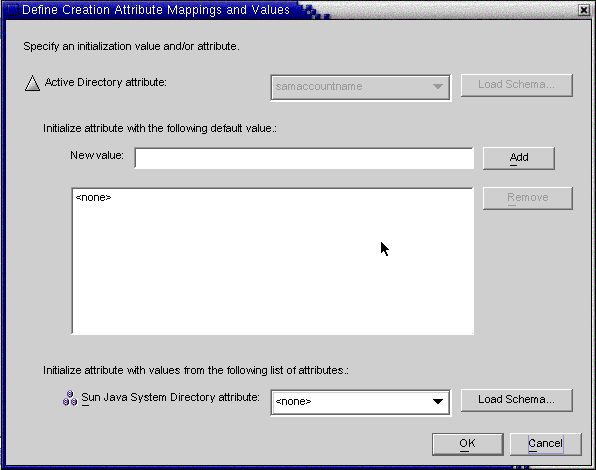
Figure 4-37 Selecting a New Active Directory Attribute

Identity Synchronization for Windows allows you to initialize an attribute with multiple values— if the attribute itself accepts multiple values.
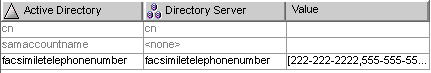
For example, if your company has three fax telephone numbers, you can specify the facsilimiletelephonenumber attribute for both Sun Java System Directory Server and Active Directory, and specify the three numbers.
You must know which attributes will accept multiple values. If you try adding multiple values to an attribute that does not accept them, an error will result during runtime when the program attempts to create the object.
The program adds the attribute value to the list pane. Repeat this step as many times as necessary to add multiple attribute values.
Figure 4-38 Specifying Multiple Values for a Creation Attribute
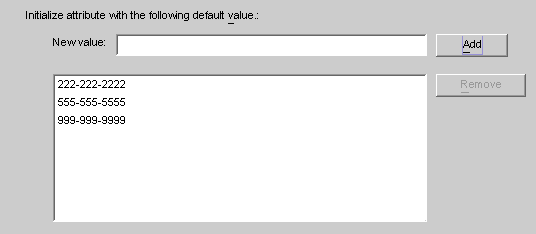
Figure 4-39 Mapping the Directory Server Attribute
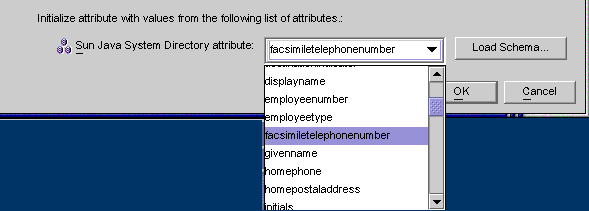
Based on the example, the finished Creation Attributes and Mappings table would look like the one in the following figure.
Figure 4-40 Completed Creation Attributes and Mappings Table
The Define Creation Mappings and Values dialog box is displayed.
For example, if you have Sun Java System Directory Server’s homephone attribute mapped to Active Directory’s othertelephone attribute. You could use the Active Directory attributes drop-down list to change the mapping to homephone.
The attribute is removed from the table immediately.
Use the Attribute Modification tab to control how modifications made to user attributes and passwords will be propagated (flow) between your Sun and Windows systems.
Figure 4-41 Attribute Modification Tab
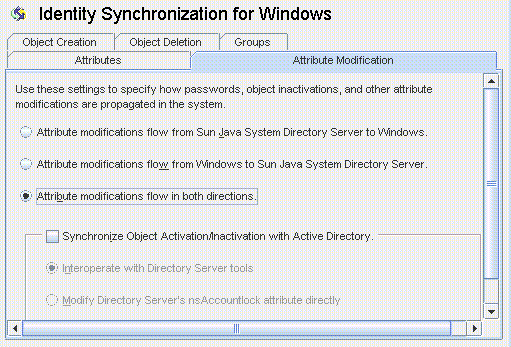
You use this tab to configure the following:
Specify the direction in which modifications flow between Directory Server and Windows directory sources.
Control whether object activations and inactivations ( enables and disables on Active Directory) will be synchronized between Directory Server and Active Directory sources, and specify the method in which user accounts are activated and inactivated.
Note - You cannot synchronize account statuses with Windows NT directory sources.
Select one of the following buttons to control how changes made in the Directory Server and Windows environments will be propagated between systems.
Attribute modifications flow from Sun Java System Directory Server to Windows: Propagates changes made in the Directory Server environment to your Windows servers.
Attribute modifications flow from Windows to Sun Java System Directory Server (Default): Propagates changes made in the Windows environment to your Directory Servers.
Attribute modifications flow in both directions : Propagates changes bidirectionally (from one environment to the other environment).
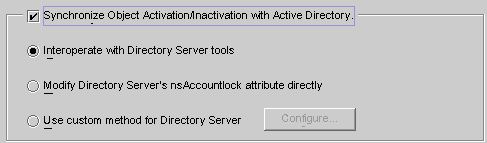
If you enable the Synchronize Object Activations/Inactivations with Active Directory box you can synchronize object activations and inactivations (known as enables and disables on Active Directory) between Directory Server and Active Directory sources.
Note - You cannot synchronize activations and inactivations with Windows NT directory sources.
Figure 4-42 Synchronizing Object Activations and Inactivations
Modifying Directory Server's NsAccountLock Attribute Directly
Note - These options are mutually exclusive.
Select this option if you use the Directory Server Console or command line tools to activate/inactivate an object. With this option selected Identity Synchronization for Windows cannot set or remove the nsAccountLock attribute directly. In addition, the program cannot detect objects that have been inactivated using other roles such as cn=nsdisabledrole, database suffix or roles that nest within other roles, such as cn=nsdisabledrole, database suffix or cn=nsmanageddisabledrole, database suffix .
To activate objects, Identity Synchronization for Windows will remove the cn=nsmanageddisabledrole, database suffix value from the nsroledn attribute.
To inactivate objects, Identity Synchronization for Windows will add the cn=nsmanageddisabledrole, database suffix value to the nsroledn attribute.
Note - If you enable the Interoperate with Directory Server Tools option, Identity Synchronization for Windows cannot set or remove the nsAccountLock attribute directly. In addition, Identity Synchronization for Windows cannot detect objects have been inactivated using other roles.
For example, cn=nsdisabledrole, database suffix or roles that nest within other roles such as cn=nsdisabledrole, database suffix or cn=nsmanageddisabledrole, database suffix.
Interoperating with Directory Server Tools describes how Identity Synchronization for Windows detects and synchronizes object activations/inactivations when you enable the Interoperate with Directory Server Tools option.
Table 4-1 Interoperating with Directory Server Tools
|
Use this method when Directory Server activations and inactivations are based on Directory Server’s operational attribute, nsAccountLock.
Note - When the Modify Directory Server’s nsAccountLock attribute option is enabled, Identity Synchronization for Windows will not detect objects that are activated/inactivated using the Directory Server Console or command line utilities.
This attribute controls object states as follows:
When nsAccountLock=true, the object is inactivated and the user cannot log in.
When nsAccountLock=false (or has no value), the object is activated.
Modifying Directory Server’s NsAccountLock Attribute Directly describes how Identity Synchronization for Windows detects and synchronizes object activations/inactivations when you enable the Modify Directory Server’s nsAccountLock Attribute Directly option.
Table 4-2 Modifying Directory Server’s nsAccountLock Attribute Directly
|
Use this method when Directory Server activations and inactivations are controlled exclusively by an external application such as Sun Java System Access Manager (formerly Sun JES Identity Server).
When you configure a custom method for Directory Server, you must specify the following:
How Identity Synchronization for Windows will detect that the external application has activated or inactivated an object in Directory Server.
How Identity Synchronization for Windows will activate or inactivate the object when synchronizing from Active Directory to Directory Server.
Note - If you enable the Use custom method for Directory Server option, Identity Synchronization for Windows cannot lock objects out of the directory unless access to the directory is controlled by an external application, such as Access Manager.
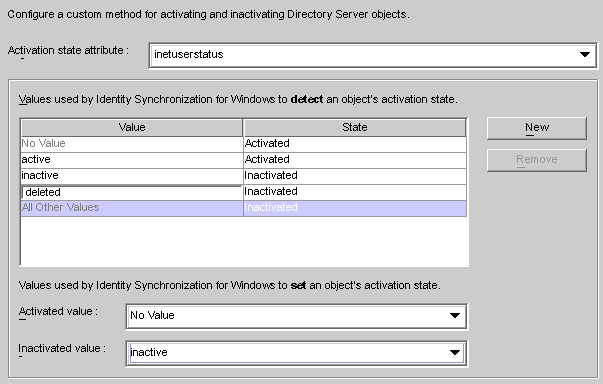
To configure a Custom method for activations and inactivations, click the Configure button and the Configure Custom Method for Directory Server dialog box is displayed.
Figure 4-43 Configuring a Custom Method for Activations and Inactivations
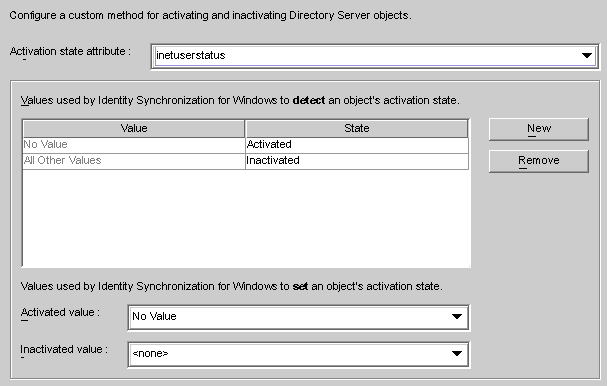
This dialog contains the following features:
Activation state attribute drop-down list : Use this list to specify an attribute that Identity Synchronization for Windows will use to synchronize activations and inactivations between Directory Server and Active Directory.
The list contains all attributes in the schema for the currently selected Directory Server structural and auxiliary objectclasses.
Value and State table: Use this table to specify when values associated with the selected attribute are activated or inactivated.
Value column: Use this column (in conjunction with the New and Remove buttons) to specify attribute values that will be used to indicate active or inactive states.
The program automatically provides two values in this column:
No Value: Where the Activation state attribute has no value.
All Other Values: Where the Activation state attribute has a value, but that value is not specified in this Value and State table.
State column: Use this column to specify whether the Value entry (in the same row) corresponds to an object that is activated or inactivated.
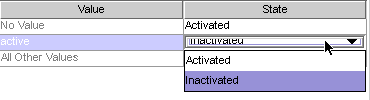
|
New button: Click this button to add new entries to the Value column.
Remove button: Select an entry in the Value column, and then click this button to remove that entry.
Activated value and Inactivated value drop-down lists: Use these two lists to specify values that Identity Synchronization for Windows will use to set an object’s state.
Synchronizing Activations and Inactivations
Figure 4-44 Selecting a State
For example, if you were using Access Manager:
No Value: Activated
active: Activated
inactive: Inactivated
deleted: Inactivated
All Other Values: Inactivated
Based on this example, Using a Custom Method for Directory Server describes how Identity Synchronization for Windows will detect and synchronize activations/inactivations when you enable the Use Custom Method for Directory Server option (using the inetuserstatus example).
|
Setting Activations and Inactivations
As you populate the Value and State table with entries, Identity Synchronization for Windows automatically populates the Activated value and Inactivated value drop-down lists as follows:
The Activated value list contains all values with an Activated status (for example No Value and active).
The Inactivated value list contains all values with an Inactivated status (for example inactive and deleted).
Neither list will contain the All Other Values value.
Select a value from the Activated value and/or the Inactivated value drop-down lists to specify how Identity Synchronization for Windows will activate and/or inactivate an object when synchronizing from Active Directory.
Activated value: Controls the object’s active state.
No Value: If the object contains the active value, Identity Synchronization for Windows will set the state to activated in Directory Server.
active: If the object contains the active value, Identity Synchronization for Windows will set the state to activated in Directory Server.
Inactivated value: Controls the object’s active state.
inactive or deleted: Identity Synchronization for Windows will set the object’s state to inactive in Directory Server.
none: Not a valid setting. You must select a value.
Note - You must specify an Inactivated value or your configuration will be invalid.
Using a Custom Method for Directory Server illustrates a completed Configure Custom Method for Directory Server dialog box.
Figure 4-45 Example: Completed Dialog
If you enable Group Synchronization between Directory Server and Active Directory, you can synchronize the creation of groups, deletion of groups, and the membership changes within that group .
Note - Group Synchronization is not supported on Windows NT directory sources.
Domain Global Security
Domain Global Distribution
Figure 4-46 Enable Group Synchronization
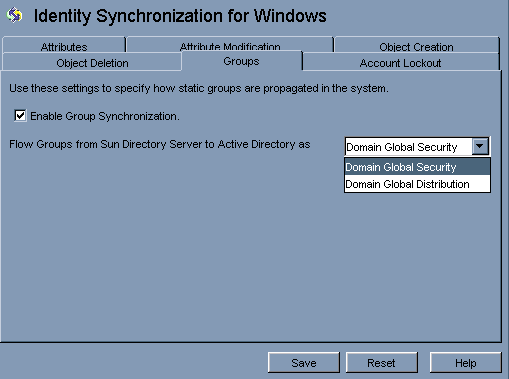
Note - For more information about Domain Global Security, Domain Global Distribution, and Active Directory; see the Microsoft Active Directory documentation.
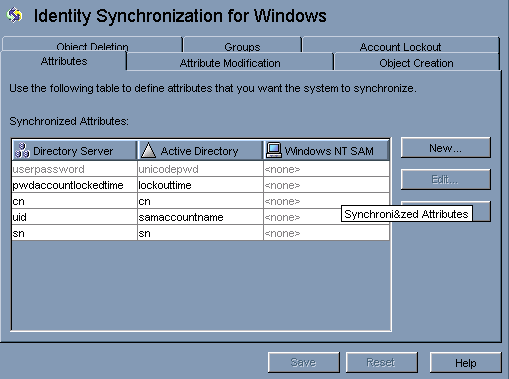
You do not need to map any attribute manually for the group synchronization. When you press Save, Identity Synchronization for Windows maps the attributes automatically.
Figure 4-47 Attribute Mapping for Group Synchronization
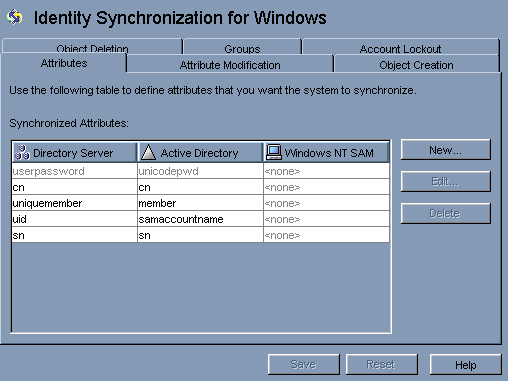
Note -
Do not modify the mapping between the userpasswordand unicodepwd attributes.
To disable the group synchronization, deselect the Disable Group Synchronization check box.
Alternatively, you can enable or disable group synchronization using command line idsync groupsync. For more information, see Appendix A, Using the Identity Synchronization for Windows Command Line Utilities.
To enable the Account Lockout feature, you must do the following:
Make the Password policies same on both Active Directory and Directory Server.
Enable Account Lockout.
Map certain attributes, which are different in Directory Server and in Active Directory
Identity Synchronization for Windows can synchronize the following events between Active Directory and Directory Server:
Lockout events from Active Directory to Directory Server
Lockout events from Directory Server to Active Directory
Manual unlockout events from Active Directory to Directory Server
Manual unlockout events from Directory Server to Active Directory
Note - Account lockout and unlockout synchronization is not supported on Windows NT directory servers.
The attribute lockoutDuration should be set to the same value at both the places before enabling the account lockout feature. Make sure that the system time is also uniform across the distributed setup. Otherwise, the lockout events can expire if the lockoutDuration is less than the difference in the system dates.
Note - Set the symmetric password policy at both ends. For example, if the password policy at Active Directory signifies a permanent lockout then the same password policy should be set at Directory Server.
Enable Account Lockout Synchronization between Directory Server and Active Directory.
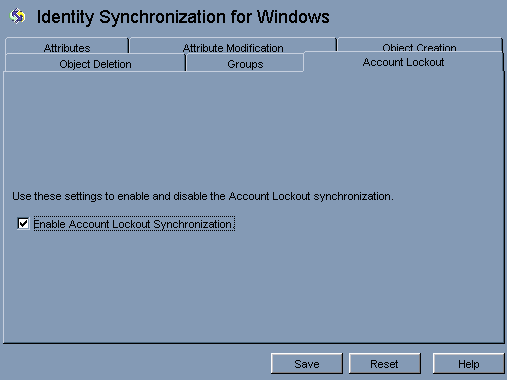
No explicit mapping of the pwdaccountlockedtime (Directory Server) and lockoutTime (AD) attributes is required to enable account lockout. Select Enable Account Lockout Synchronization from the Account Lockout tab in Identity Synchronization for Windows configuration panel.
Note - You can enable or disable the account lockout synchronization using command line tool idsync accountlockout. For more information, see Appendix A, Using the Identity Synchronization for Windows Command Line Utilities.
Use Object Deletions tab to specify how deleted user entries should flow between Directory Server and Active Directory systems.
Note - You cannot specify Object Deletions flow for Windows NT.
Figure 4-48 Propagating User Entry Deletions
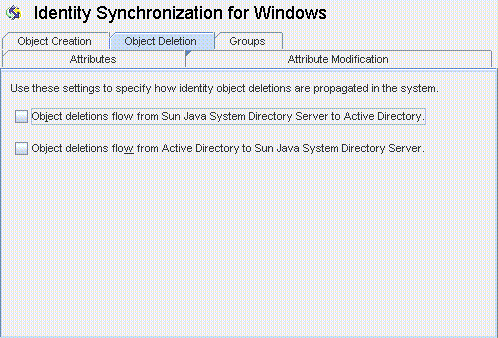
Enable Object deletions flow from Sun Java System Directory Server to Active Directory to propagate deletions from the Sun Directory Server environment to your Active Directory servers.
Enable Object deletions flow from Active Directory to Sun Java System Directory Server to propagate deletions from the Active Directory environment to your Sun Directory Servers.
Enable both options for bidirectional flow.
Disable both options to prevent user deletions from propagating from one system to the other (Default setting).