1 About the Connector
Note:
In this guide, the term target system collectively refers to both SAP R/3 and SAP CUA. Where information is specific to either SAP R/3 or SAP CUA, the name of the target system has been used.
In the account management (target resource) mode of the connector, data about users created or modified directly on the target system can be reconciled into Oracle Identity Manager. This data is used to provision (allocate) new resources or update resources already assigned to OIM Users. In addition, you can use Oracle Identity Manager to provision or update SAP R/3 or SAP CUA resources assigned to OIM Users. These provisioning operations performed on Oracle Identity Manager translate into the creation of or updates to target system accounts.
This chapter contains the following sections:
1.1 Certified Components
These are the software components and their versions required for installing and using the connector.
Table 1-1 lists certified components for the connector.
Table 1-1 Certified Components
| Component | Requirement |
|---|---|
|
Oracle Identity Governance or Oracle Identity Manager |
You can use one of the following releases of Oracle Identity Governance or Oracle Identity Manager:
|
|
Target systems |
The target system can be any one of the following:
|
| Other Considerations |
In general:
|
|
Connector Server |
11.1.2.1.0 and 12.2.1.3.0 |
|
Connector Server JDK |
JDK 1.6 Update 24 or later and JKD1.7 or later, or JRockit 1.6 or later |
|
External Code |
The connector works with SAP JCo 3.0.2 or later. The following SAP custom code files are required:
Note: There are different distribution packages (JCo) 3.0 available for various supported platforms and processors. See, JCo documentation for more information about using JCo 3.0 packages as per your environment. |
|
SAP Governance, Risk and Compliance Access Control (GRC AC) |
If you want to configure and use the Access Risk Analysis or Access Request Management feature of this target system, then install one of the following:
|
1.2 Usage Recommendation
Depending on the Oracle Identity Manager version that you are using, you must deploy and use one of the following connectors:
Note:
-
In Oracle Identity Manager, you can install and configure both SAP User Management and SAP User Management Engine connectors.
You can configure the connectors with SAP GRC AC target system to use either the Access Risk Analysis or the Access Request Management feature.
- At some places in this section, SAP User Management connector releases 9.1.2.x and 9.0.4.x have been referred to as release 9.x.
- If you are using Oracle Identity Governance 12cPS4(12.2.1.4.0), 12cPS3 Release BP02 (12.2.1.3.2) and any later BP in this release track, SAP NetWeaver 7.5 SPS 00 with SAP S/4 HANA 1610 and SAP BusinessObjects AC 10.1 or later, then you must use the SAP User Management 11.1.1.7.1 (one-off p28807748_111170_Generic.zip) or latest 12.2.1.x version of this connector.
-
If you are using Oracle Identity Manager 11g Release 1 PS1 BP07 (11.1.1.5.7) and any later BP in this release track (such as Oracle Identity Manager 11g Release 1 PS1 BP08 (11.1.1.5.8) or later, or Oracle Identity Manager 11g Release 2 BP05 (11.1.2.0.5)), or Oracle Identity Manager 11g Release 2 PS3 (11.1.2.3.0), then use the latest 11.1.1.x version of this connector.
-
If you are using an Oracle Identity Manager release 9.1.0.2 BP04 or later and earlier than Oracle Identity Manager 11g Release 1 PS1 BP07 (11.1.1.5.7), then you must use the 9.1.2 version of this connector.
-
If you are using an Oracle Identity Manager release 9.1.0.1 or later and earlier than Oracle Identity Manager 9.1.0.2 BP04, then you must use the 9.0.4 version of this connector.
1.3 Certified Languages
The connector supports the following languages:
-
Arabic
-
Chinese (Simplified)
-
Chinese (Traditional)
-
Czech
-
Danish
-
Dutch
-
English
-
Finnish
-
French
-
German
-
Greek
-
Hebrew
-
Hungarian
-
Italian
-
Japanese
-
Korean
-
Norwegian
-
Polish
-
Portuguese
-
Portuguese (Brazilian)
-
Romanian
-
Russian
-
Slovak
-
Spanish
-
Swedish
-
Thai
-
Turkish
1.4 Connector Architecture and Supported Deployment Configurations
The SAP UM connector is implemented by using the Identity Connector Framework (ICF).
In its basic mode of operation, the connector sets up Oracle Identity Manager as the front end for sending account creation or modification provisioning requests to either SAP R/3 or SAP CUA. While deploying the connector, you can opt for enabling either direct provisioning or request-based provisioning in Oracle Identity Manager. In direct provisioning, only Oracle Identity Manager administrators can create and manage target system resources. In request-based provisioning, users can raise requests for creating and managing their accounts. Other users designated as administrators or approvers act upon these requests.
An access policy change is the third form of provisioning operation supported by the connector. If a change in an access policy requires corresponding changes in resources provisioned to a set of users, then the required provisioning operations on the target system are automatically initiated from Oracle Identity Manager.
Account data added or modified through provisioning operations performed directly on the target system can be reconciled into Oracle Identity Manager.
Figure 1-1 shows the connector integrating SAP R/3 with Oracle Identity Manager.
Figure 1-1 Connector Integrating SAP R/3 with Oracle Identity Manager
Description of "Figure 1-1 Connector Integrating SAP R/3 with Oracle Identity Manager"
Figure 1-2 shows the connector integrating SAP CUA with Oracle Identity Manager.
Figure 1-2 Connector Integrating SAP CUA with Oracle Identity Manager
Description of "Figure 1-2 Connector Integrating SAP CUA with Oracle Identity Manager"
As shown in these figures, either SAP R/3 or SAP CUA is configured as a target resource of Oracle Identity Manager. Through provisioning operations performed on Oracle Identity Manager, accounts are created and updated on the target system for OIM Users. Through reconciliation, account data that is created and updated directly on the target system is fetched into Oracle Identity Manager and stored against the corresponding OIM Users.
Note:
The connector does not support direct administration of accounts on child systems in SAP CUA. As shown in Figure 1-2, all connector operations are performed between Oracle Identity Manager and the SAP R/3 parent system. When required, user data changes resulting from these connector operations are propagated from the parent system to the child system.
During provisioning, adapters carry provisioning data submitted through the process form to the target system. Standard BAPIs on the target system accept provisioning data from the adapters, carry out the required operation on the target system, and return the response from the target system to the adapters. The adapters return the response to Oracle Identity Manager.
During reconciliation, a scheduled task establishes a connection with the target system and sends reconciliation criteria to the BAPIs. The BAPIs extract user records that match the reconciliation criteria and hand them over to the scheduled task, which brings the records to Oracle Identity Manager.
Each record fetched from the target system is compared with SAP UM resources that are already provisioned to OIM Users. If a match is found, then the update made to the SAP record from the target system is copied to the SAP UM resource in Oracle Identity Manager. If no match is found, then the user ID of the record is compared with the user ID of each OIM User. If a match is found, then data in the target system record is used to provision an SAP UM resource to the OIM User.
Besides enabling direct integration with the target system, the connector can also be used to act as an interface with the Access Risk Analysis and Access Request Management modules of SAP BusinessObjects AC. The target system (SAP R/3 or SAP CUA) and these two modules of SAP BusinessObjects AC together provide various deployment configurations. The following sections provide information about the supported deployment configurations of the connector:
1.4.1 Basic User Management
When you configure the connector for basic user management, the connector accepts provisioning data submitted through Oracle Identity Manager and propagates this data to the target system. For example, when a Create User provisioning operation is performed on Oracle Identity Manager, the outcome is the creation of an account on the target system.
Account data added or modified through provisioning operations performed directly on the target system can be reconciled into Oracle Identity Manager.
Figure 1-1 and Figure 1-2 show the architecture of the connector in this deployment configuration.
The steps performed during a provisioning operation can be summarized as follows:
-
The provisioning operation is initiated through direct provisioning, request-based provisioning, or an access policy change.
-
Provisioning data is sent to the target system.
-
The required change is made on the target system, and the outcome of the operation is sent back to and stored in Oracle Identity Manager.
1.4.2 User Management with SoD
You might have the Access Risk Analysis module of SAP BusinessObjects AC configured to implement segregation of duties (SoD) in your SAP operating environment. In this scenario, the connector can be used as the interface between Oracle Identity Manager and the SoD module. You can configure the connector so that provisioning requests sent from Oracle Identity Manager are first run through the SoD validation process of SAP BusinessObjects AC Access Risk Analysis. Provisioning requests that clear this validation process are then propagated from Oracle Identity Manager to the target system.
Reconciliation does not involve SAP BusinessObjects AC Access Risk Analysis. Account data added or modified through provisioning operations performed directly on the target system can be reconciled into Oracle Identity Manager.
In this guide, the phrase configuring SoD is used to mean configuring the integration between Oracle Identity Manager and SAP BusinessObjects AC Access Risk Analysis.
Figure 1-3 shows data flow in this mode of the connector.
Figure 1-3 Data Flow During the SoD Validation Process
Description of "Figure 1-3 Data Flow During the SoD Validation Process"
The steps performed during a provisioning operation can be summarized as follows:
See Also:
Using Segregation of Duties (SoD) in Oracle Fusion Middleware Developing and Customizing Applications for Oracle Identity Manager for detailed information about the provisioning process flow
-
The provisioning operation is initiated through direct provisioning, request-based provisioning, or an access policy change.
-
The resource approval workflow of Oracle Identity Manager sends this request to the SoD engine (SAP BusinessObjects AC Access Risk Analysis).
-
The SoD engine uses predefined rules to check if the entitlement assignment would lead to SoD violations. The outcome of this check is then sent back to Oracle Identity Manager.
-
If the request fails SoD validation, then the approval workflow can be configured to take remediation steps. If the request passes SoD validation and if the approver in Oracle Identity Manager approves the request, then the resource provisioning workflow is initiated.
-
This resource provisioning workflow can be configured to perform the SoD validation again. This is to ensure SoD compliance of the entitlement assignment immediately before the entitlement assignment is provisioned to the target system. You can also configure the SoD validation check in the resource provisioning workflow to be bypassed if this validation has been passed in the resource approval workflow.
-
The resource provisioning workflow performs the required change on the target system, and the outcome of the operation is sent back to and stored in Oracle Identity Manager.
Summary of the account management process:
-
Data from a provisioning operation on Oracle Identity Governance is first sent to the SAP BusinessObjects Access Risk Analysis module for SoD validation.
-
After the SoD validation checks are cleared, the provisioning request is sent to SAP BusinessObjects Access Request Management.
-
After the SAP BusinessObjects Access Request Management workflow clears the request, the provisioning request is implemented on the target system.
-
Scheduled tasks run from Oracle Identity Governance to reconcile the outcome of the operation from the target system into Oracle Identity Governance.
1.4.3 Audit Trail Details in Connector Logs
The audit trail details can be captured in the connector logs when Access Request Management is configured.
Here are a few samples of Audit trail in the connector logs:
-
Create User
logAuditTrial : Audit Trial: {Result=[Createdate:20130409,Priority:HIGH,Requestedby:,johndoe (JOHNDOE),Requestnumber:9000001341,Status:Decision pending,Submittedby:,johndoe (JOHNDOE),auditlogData:{,ID:000C290FC2851ED2A899DA29DAA1B1E2,Description:,Display String:Request 9000001341 of type New Account Submitted by johndoe ( JOHNDOE ) for JK1APRIL9 JK1APRIL9 ( JK1APRIL9 ) with Priority HIGH}], Status=0_Data Populated successfully} -
Request Status Schedule Job
logAuditTrial : Audit Trial: {Result=[Createdate:20130409,Priority:HIGH,Requestedby:,johndoe (JOHNDOE),Requestnumber:9000001341,Status:Approved,Submittedby:,johndoe (JOHNDOE),auditlogData:{,ID:000C290FC2851ED2A899DA29DAA1B1E2,Description:,Display String:Request 9000001341 of type New Account Submitted by johndoe ( JOHNDOE ) for JK1APRIL9 JK1APRIL9 ( JK1APRIL9 ) with Priority HIGH,ID:000C290FC2851ED2A899DAF9961C91E2,Description:,Display String:Request is pending for approval at path GRAC_DEFAULT_PATH stage GRAC_MANAGER,ID:000C290FC2851ED2A89A1400B60631E2,Description:,Display String:Approved by JOHNDOE at Path GRAC_DEFAULT_PATH and Stage GRAC_MANAGER,ID:000C290FC2851ED2A89A150972D091E2,Description:,Display String:Auto provisioning activity at end of request at Path GRAC_DEFAULT_PATH and Stage GRAC_MANAGER,ID:000C290FC2851ED2A89A150972D111E2,Description:,Display String:Approval path processing is finished, end of path reached,ID:000C290FC2851ED2A89A150972D151E2,Description:,Display String:Request is closed}], Status=0_Data Populated successfully} -
Modify User
logAuditTrial : Audit Trial: {Result=[Createdate:20130409,Priority:HIGH,Requestedby:,johndoe (JOHNDOE),Requestnumber:9000001342,Status:Decision pending,Submittedby:,johndoe (JOHNDOE),auditlogData:{,ID:000C290FC2851ED2A89A3ED3B1D7B1E2,Description:,Display String:Request 9000001342 of type Change Account Submitted by johndoe ( JOHNDOE ) for JK1FirstName JK1APRIL9 ( JK1APRIL9 ) with Priority HIGH}], Status=0_Data Populated successfully}
1.4.4 User Management with Access Request Management
Access Request Management is a module in the SAP BusinessObjects AC suite. In an SAP environment, you can set up Access Request Management as the front end for receiving account creation and modification provisioning requests. In Access Request Management, workflows for processing these requests can be configured and users designated as approvers act upon these requests.
Note:
In this guide, (for the SAP UM AC Connector that uses the SAPUM-AC-Connector-CI.xml file) the phrase configuring Access Request Management has been used to mean configuring the integration between Oracle Identity Manager and SAP BusinessObjects AC Access Request Management.
This connector works as a normal SAP UM connector as there is no interaction with GRC target.
In your operating environment, the Access Request Management module might be directly linked with the Access Risk Analysis module. In other words, provisioning requests are first sent from Access Request Management to Access Risk Analysis for SoD validation. Only requests that clear the validation process are implemented on the target system. In this scenario, it is recommended that you do not configure the SoD feature of the connector.
Reconciliation does not involve SAP BusinessObjects AC Access Request Management. Scheduled tasks on Oracle Identity Manager fetch data from the target system to Oracle Identity Manager.
Figure 1-4 shows data flow in this mode of the connector.
Figure 1-4 Connector Integrating SAP BusinessObjects AC Access Request Management with Oracle Identity Manager and the Target System
Description of "Figure 1-4 Connector Integrating SAP BusinessObjects AC Access Request Management with Oracle Identity Manager and the Target System"
The following is the detailed sequence of steps performed during a provisioning operation:
-
The provisioning operation is initiated through direct provisioning, request-based provisioning, or an access policy change.
Figure 1-5 IT Resource Configuration Showing GRC in the SAP AC UM Flow
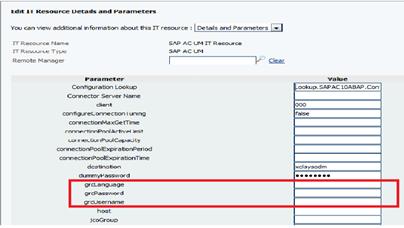
Description of "Figure 1-5 IT Resource Configuration Showing GRC in the SAP AC UM Flow" -
The connector sends requests and receives responses through the following Web services of SAP BusinessObjects AC:
-
SAPGRC_AC_IDM_SUBMITREQUEST: This Web service is used to submit requests.
-
SAPGRC_AC_IDM_REQUESTSTATUS: This Web service is used to fetch request statuses.
-
SAPGRC_AC_IDM_AUDITTRAIL: This Web service is used to check if there are error messages in the SAP BusinessObjects AC Access Request Management logs.
The process form holds fields for both basic user management and Access Request Management. However, for a Create User operation, Access Request Management fields (attributes) on the process form are also used. Mappings for these fields are stored in the Lookup.SAPAC10ABAP.UM.ProvAttrMap lookup definition based on GRC target version.
If you specify values for any attribute that is not present in these lookup definitions, then the connector ignores those attributes during the Create User operation.
Note:
SAP BusinessObjects AC Access Request Management does not process passwords. Therefore, any value entered in the Password field is ignored during Create User provisioning operations.
See Guidelines on Performing Provisioning for information about setting passwords when you configure Access Request Management.
In a Modify User operation, you can specify values for attributes that are mapped with SAP BusinessObjects AC Access Request Management.
-
-
When the request is created on SAP BusinessObjects AC Access Request Management, data sent back by Access Request Management is stored in the following read-only fields in Oracle Identity Manager:
-
AC Request ID: This field holds the request ID that is generated on SAP BusinessObjects AC Access Request Management. The AC Request ID does not change during the lifetime of the request.
-
AC Request Status: This field holds the status of the request on SAP BusinessObjects AC Access Request Management. You configure and run the SAP AC Request Status scheduled job to fetch the latest status of the request from the target system.
-
AC Request Type: This field holds the type of request, such as New Account, Change Account, Delete Account, New, and Change.
-
-
The request is passed through the workflow defined in SAP BusinessObjects AC Access Request Management. The outcome is one of the following:
-
If Access Request Management clears the request, then the outcome is the creation or modification of a user's account on the target system (SAP R/3 or SAP CUA). The status of the request is set to OK in case of SAP BusinessObjects AC 10. Then, a message is recorded in the Oracle Identity Manager logs.
-
If Access Request Management rejects the provisioning request, then the status of the request is set to Failed in case of SAP BusinessObjects AC 10. Then, a message is recorded in the Oracle Identity Manager logs.
-
If Access Request Management cancels the provisioning request, then the status of the request is set to ABORTED in case of SAP BusinessObjects AC 10. Then, a message is recorded in the Oracle Identity Manager logs.
-
If an error occurs during communication between Access Request Management and the target system, then the request remains in the Open state. A message stating that the operation has failed is recorded in the audit log associated with the request. An error message is displayed on the console.
-
Summary of the account management process:
- Data from a provisioning operation on Oracle Identity Governance is sent to SAP BusinessObjects Access Request Management.
- The workflow defined in SAP BusinessObjects Access Request Management sends the request to the SAP BusinessObjects Access Risk Analysis module for SoD validation.
- After the SoD validation checks are cleared, the provisioning request is implemented on the target system.
- Scheduled tasks run from Oracle Identity Governance reconcile the outcome of the operation from the target system into Oracle Identity Governance.
1.4.5 User Management with Both SoD and Access Request Management
You might have both SAP BusinessObjects AC Access Risk Analysis and Access Request Management configured in your SAP operating environment. You should configure the connector features for both SoD and Access Request Management at the same time only if the Access Risk Analysis and Access Request Management modules are separately configured, such as User Management with SoD and Access Request Management (that is, not linked) modules are separately configured in your operating environment.
Note:
If SAP BusinessObjects AC Access Request Management is configured to send provisioning requests to SAP BusinessObjects AC Access Risk Analysis for SoD validation, then you must not configure the SoD feature of the connector.
1.4.6 Guidelines on Using a Deployment Configuration
These are the guidelines that you must apply while performing provisioning operations.
When you integrate Oracle Identity Manager with your SAP operating environment, you might have one of the following requirements in mind:
-
Use Oracle Identity Manager as the provisioning source for account management on SAP resources.
-
Leverage workflows and access policies configured in SAP BusinessObjects AC Access Request Management, with Oracle Identity Manager as the provisioning source for account management on SAP resources.
-
Use SAP BusinessObjects AC Access Risk Analysis for SoD enforcement and SAP BusinessObjects AC Access Request Management for user approval of provisioning requests sent through Oracle Identity Manager. Overall account management on SAP resources is performed through Oracle Identity Manager.
The following sections describe guidelines on the supported deployment configurations:
Note:
You must separately configure User Management with SoD, and Access Request Management.
1.4.6.1 User Management with SoD and Access Request Management
The following are deployment guidelines that you must apply for a scenario in which SAP BusinessObjects AC Access Risk Analysis and SAP BusinessObjects AC Access Request Management are enabled and discretely configured modules:
-
Configure both SoD and Access Request Management features of the connector.
-
On SAP BusinessObjects AC Access Request Management, configure the no-stage approval for account creation. In other words, account creation requests must be auto-approved on Access Request Management.
If a role or profile is provisioned on Oracle Identity Manager but rejected on SAP BusinessObjects AC Access Request Management, then the role or profile is revoked from Oracle Identity Manager at the end of the next user reconciliation run. Therefore, you can have approval workflows defined for role and profile provisioning requests on SAP BusinessObjects AC Access Request Management.
Summary of the account management process:
-
Data from a provisioning operation on Oracle Identity Manager is first sent to the SAP BusinessObjects AC Access Risk Analysis module for SoD validation.
-
After the SoD validation checks are cleared, the provisioning request is sent to SAP BusinessObjects AC Access Request Management.
-
After the SAP BusinessObjects AC Access Request Management workflow clears the request, the provisioning request is implemented on the target system.
-
Scheduled tasks run from Oracle Identity Manager reconcile the outcome of the operation from the target system into Oracle Identity Manager.
1.4.6.2 User Management with Access Request Management
The following are deployment guidelines that you must apply for a scenario in which SAP BusinessObjects AC Access Request Management is configured and enabled in your SAP operating environment:
Note:
SAP BusinessObjects AC Access Risk Analysis is either configured as a linked module of SAP BusinessObjects AC Access Request Management or it is not used at all.
You must separately configure User Management with SoD, and Access Request Management.
-
On SAP BusinessObjects AC Access Request Management, configure the no-stage approval for account creation. In other words, account creation requests must be auto-approved on Access Request Management.
The scenario described earlier in this section explains this guideline.
-
Configure the Access Request Management feature of the connector.
-
Do not configure the SoD feature of the connector.
Summary of the account management process:
-
Data from a provisioning operation on Oracle Identity Manager is sent to SAP BusinessObjects AC Access Request Management.
-
The workflow defined in SAP BusinessObjects AC Access Request Management sends the request to the SAP BusinessObjects AC Access Risk Analysis module for SoD validation.
-
After the SoD validation checks are cleared, the provisioning request is implemented on the target system.
-
Scheduled tasks run from Oracle Identity Manager reconcile the outcome of the operation from the target system into Oracle Identity Manager.
1.4.7 Considerations to Be Addressed When You Enable Access Request Management
These are the consideration you must keep in mind when you enable the Access Request Management feature of the connector:
-
Multiple requests are generated from Oracle Identity Manager in response to some provisioning operations. For example, if you assign multiple roles to a user in a particular provisioning operation, then one request is created and sent to Access Request Management for each role.
-
For a particular account, Oracle Identity Manager keeps track of the latest request only. This means, for example, if more than one attribute of an account has been modified in separate provisioning operations, then Oracle Identity Manager keeps track of data related to the last operation only.
-
A Modify User operation can involve changes to multiple process form fields or child form fields. For each field that is modified, one request is created and sent to SAP BusinessObjects AC Access Request Management. Only information about the last request sent to Access Request Management is stored in Oracle Identity Manager.
-
Only parent or child form requests can be submitted in a single operation. You cannot submit both parent and child form requests at the same time.
-
Enable linking of SAP HRMS and SAP R/3 or SAP CUA accounts only if a no-stage workflow has been defined for the Create User provisioning operations.
Linking of SAP HRMS and SAP R/3 or SAP CUA Accounts describes the feature of the connector that stores the link between an SAP HRMS account created for an individual and the corresponding SAP R/3 or SAP CUA account created for the same individual. When you configure the Access Request Management feature, you should enable linking only if a no-stage approval has been defined for the Create User request type in SAP BusinessObjects AC Access Request Management. A no-stage approval is one in which no approvers are involved. All requests sent through a no-stage approval are automatically approved.
1.4.8 Guidelines on Configuring Security
These are the guidelines that you must apply while configuring security.
-
Secure communication
It is important to protect sensitive data by securing the communication between Oracle Identity Manager and the SAP system.
If you are using SAP User Management as the target system, then you must configure SNC (Secure Network Communication). See Configuring SNC to Secure Communication Between Oracle Identity Manager and the Target System for more information.
If you are using SAP BusinessObjects AC as the target system, then you must enable SSL between Oracle Identity Manager and SAP BusinessObjects AC. See Enabling SSL Communication in Oracle Fusion Middleware Developing and Customizing Applications for Oracle Identity Manager for the instructions.
-
Password management
For accounts created through Oracle Identity Manager, you can configure the connector so that users with newly created accounts are prompted to change their passwords at first logon or the password set while creating the account on Oracle Identity Manager is set as the new password on the target system.
See Configuring Password Changes for Newly Created Accounts for more information.
1.5 Features of the SAP UM Connector
The following are features of the connector:
-
Support for SAP Governance, Risk, and Compliance Version 10 or Later
-
Mapping Standard and Custom Attributes for Reconciliation and Provisioning
-
Routing of Provisioning Requests Through SAP BusinessObjects AC Access Request Management
-
SNC Communication Between the Target System and Oracle Identity Manager
-
Specifying the Use of a Logon Group on the Target System for Connector Operations
1.5.1 Support for SAP Governance, Risk, and Compliance Version 10 or Later
You can use this connector for risk analysis and remdiation and for provisioning and managing users.
The connector supports the following new components:
-
Risk Analysis and Remediation, also known as Access Risk Analysis (ARA)
-
Compliant User Provisioning, also known as Access Request Management (ARM)
Throughout this guide, SAP GRC Access Risk Analysis refers to Risk Analysis and Remediation and SAP GRC Access Request Management refers to Compliant User Provisioning.
1.5.2 Support for Connector Server
Connector Server is a component provided by ICF.
By using one or more connector servers, the connector architecture permits your application to communicate with externally deployed bundles. In other words, a connector server enables remote execution of an Oracle Identity Manager connector. See the following sections for more information:
1.5.3 Mapping Standard and Custom Attributes for Reconciliation and Provisioning
You can create mappings for attributes that are not included in the list of default attribute mappings. These attributes can be part of the standard set of attributes provided by the target system or custom attributes that you add on the target system.
See Extending the Functionality of the Connector for more information.
1.5.4 SoD Validation of Entitlement Requests
You can validate an entitlement request in Oracle Identity Manager with an SoD Engine.
The connector supports the SoD feature introduced in Oracle Identity Manager release 9.1.0.2. The following are the focal points of this software update:
-
The SoD Invocation Library (SIL) is bundled with Oracle Identity Manager. The SIL acts as a pluggable integration interface with any SoD engine.
-
The SAP User Management connector can be configured to work with SAP BusinessObjects AC as the SoD engine. To enable this, changes have been made in the approval and provisioning workflows of the connector.
Note:
The default approval workflow and associated object form are configured for the SoD validation capabilities of SAP BusinessObjects AC. You can use them to develop your own approval workflows and object forms.
In Oracle Identity Manager release 11.1.1, object forms have been replaced by request datasets. A request dataset is an XML file that specifies information to be submitted by the requester during a provisioning operation. Predefined request datasets are shipped with this connector. The default approval workflow and associated request dataset are configured for the SoD validation capabilities of SAP BusinessObjects AC. You can use them to develop your own approval workflows and request datasets.
-
The SoD engine processes role and profile entitlement requests that are sent through the connector. This preventive simulation approach helps identify and correct potentially conflicting assignment of entitlements to a user, before the requested entitlements are granted to users.
See Configuring SoD (Segregation of Duties) for detailed information about the SoD feature.
Note:
If you are using SAP User Management with SOD, ensure to request entitlements from the Entitlements tab.1.5.5 Routing of Provisioning Requests Through SAP BusinessObjects AC Access Request Management
You can configure the connector to work with SAP BusinessObjects AC Access Request Management.
See User Management with Access Request Management for detailed information about this feature.
1.5.6 Full and Incremental Reconciliation
In full reconciliation, all records are fetched from the target system to Oracle Identity Manager. In incremental reconciliation, only records that are added or modified after the last reconciliation run are fetched into Oracle Identity Manager.
At the end of a reconciliation run, an attribute of the scheduled task holds the time stamp at which the reconciliation run began.
You can switch from incremental to full reconciliation at any time after you deploy the connector. See Full Reconciliation and Incremental Reconciliation for more information.
1.5.7 Limited (Filtered) Reconciliation
To limit or filter the records that are fetched into Oracle Identity Governance during a reconciliation run, you can specify the subset of added or modified target system records that must be reconciled.
See Limited Reconciliation for more information.
1.5.8 Batched Reconciliation
You can break down a reconciliation run into batches by specifying the number of records that must be included in each batch.
See the description of the Batch Size attribute in Batched Reconciliation for more information.
1.5.9 Enabling and Disabling Accounts
Valid From and Valid Through are two user attributes on the target system. For a particular user in SAP, if the Valid Through date is less than the current date, then the account is in the Disabled state. Otherwise, the account is in the Enabled state. The same behavior is duplicated in Oracle Identity Manager through reconciliation. In addition, you can set the value of the Valid Through date to a current date or a date in the past through a provisioning operation.
Note:
The Enabled or Disabled state of an account is not related to the Locked or Unlocked status of the account.
1.5.10 Linking of SAP HRMS and SAP R/3 or SAP CUA Accounts
An SAP HRMS account created for an individual can be linked with the SAP R/3 or SAP CUA account created for the same user. For a particular user, an attribute of SAP HRMS holds the user ID of the corresponding SAP R/3 or SAP CUA account.
You can duplicate this link in Oracle Identity Manager by using the following entries of the Lookup.SAPABAP.Configuration lookup definition:
-
validatePERNR
-
overwriteLink
See Linking of SAP HRMS and SAP R/3 or SAP CUA Accounts for more information.
1.5.11 SNC Communication Between the Target System and Oracle Identity Manager
You can configure Secure Network Communication (SNC) to secure communication between Oracle Identity Manager and the target system.
See Configuring SNC to Secure Communication Between Oracle Identity Manager and the Target System for more information.
1.5.12 Configuring Password Changes for Newly Created Accounts
When you log in to SAP by using a newly created account, you are prompted to change your password at first logon. For accounts created through Oracle Identity Manager, password management can be configured using one of the following approaches:
-
Configure the connector so that users with newly created accounts are prompted to change their passwords at first logon.
-
Configure the connector so that the password set while creating the account on Oracle Identity Manager is set as the new password on the target system. The user is not prompted to change the password at first logon.
This feature is configured using the dummyPassword parameter of Basic Configuration Parameters and the ChangePasswordAtNextLogon entry of Advanced Settings parameters.
1.5.13 Specifying a SAP JCo Trace Level
The connector uses the SAP JCo for reconciliation and provisioning operations. The JCo trace level is a numeric specification of the level of trace data that must be logged when the SAP JCo is used. You can specify the trace level as a parameter of the IT resource.
See Table 2-5 for more information.
1.5.14 Connection Pooling
A connection pool is a cache of objects that represent physical connections to the target system. Oracle Identity Manager connectors can use these connections to communicate with target systems. At run time, the application requests a connection from the pool. If a connection is available, then the connector uses it and then returns it to the pool. A connection returned to the pool can again be requested for and used by the connector for another operation. By enabling the reuse of connections, the connection pool helps reduce connection creation overheads like network latency, memory allocation, and authentication.
One connection pool is created for each IT resource. For example, if you have three IT resources for three installations of the target system, then three connection pools are created, one for each target system installation. Setting up the Lookup Definition for Connection Pooling provides information about setting up the connection pool.
1.5.15 Specifying the Use of a Logon Group on the Target System for Connector Operations
In SAP, a logon group is used as a load-sharing mechanism. When a user logs in to a logon group, the system internally routes the connection request to the logon group member with the least load. You can configure the connector to use a logon group for logging in to the target system for reconciliation and provisioning operations.
See Parameters for Enabling the Use of a Logon Group for more information.
1.5.16 Transformation and Validation of Account Data
You can configure validation of account data that is brought into or sent from Oracle Identity Manager during reconciliation and provisioning. In addition, you can configure transformation of account data that is brought into Oracle Identity Manager during reconciliation. The following sections provide more information:
1.5.17 Support for Resource Exclusion Lists
You can specify a list of accounts that must be excluded from reconciliation and provisioning operations. Accounts whose user IDs you specify in the exclusion list are not affected by reconciliation and provisioning operations.
See Validation Groovy Script for Resource Exclusion in Oracle Fusion Middleware Performing Self Service Tasks with Oracle Identity Governance for more information about configuring resource exclusion lists.
1.6 Lookup Definitions Used During Connector Operations
Lookup definitions used during reconciliation and provisioning are preconfigured. Preconfigured lookup definitions are automatically created in Oracle Identity Manager after you deploy the connector. These lookup definitions are either prepopulated with values or values must be manually entered in them after the connector is deployed.
Lookup definitions used during connector operations can be categorized as follows:
1.6.1 Lookup Definitions Synchronized with the Target System
Lookup field synchronization involves copying additions or changes made to specific fields in the target system to lookup definitions in Oracle Identity Manager.
During a provisioning operation, you use a lookup field on the process form to specify a single value from a set of values. For example, you use the Date Format lookup field to select a date format from the list of supported date formats. When you deploy the connector, lookup definitions corresponding to the lookup fields on the target system are automatically created in Oracle Identity Manager. Lookup field synchronization involves copying additions or changes made to the target system lookup fields into the lookup definitions in Oracle Identity Manager.
The following lookup definitions are populated with values fetched from the target system by the scheduled jobs for lookup field synchronization, for the SAP UM and the SAP AC UM connectors:
-
For the SAP UM Connector
-
Lookup.SAPABAP.CommType
-
Lookup.SAPABAP.Company
-
Lookup.SAPABAP.ContractualUserType
-
Lookup.SAPABAP.DateFormat
-
Lookup.SAPABAP.DecimalNotation
-
Lookup.SAPABAP.LangComm
-
Lookup.SAPABAP.Parameter
-
Lookup.SAPABAP.Priority
-
Lookup.SAPABAP.Profile
-
Lookup.SAPABAP.Roles
-
Lookup.SAPABAP.System
-
Lookup.SAPABAP.TimeZone
-
Lookup.SAPABAP.UserGroups
-
Lookup.SAPABAP.UserLock
-
Lookup.SAPABAP.UserTitle
-
Lookup.SAPABAP.UserType
-
-
For the SAP AC UM Connector
-
Lookup.SAPACABAP.CommType
-
Lookup.SAPACABAP.Bproc
-
Lookup.SAPACABAP.Company
-
Lookup.SAPACABAP.ContractualUserType
-
Lookup.SAPACABAP.DateFormat
-
Lokup.SAPACABAP.Funcarea
-
Lookup.SAPACABAP.DecimalNotation
-
Lookup.SAPACABAP.LangComm
-
Lookup.SAPACABAP.Parameter
-
Lookup.SAPACABAP.Priority
-
Lookup.SAPACABAP.Profile
-
Lookup.SAPACABAP.ReqInitSystem
-
Lookup.SAPACABAP.Roles
-
Lookup.SAPACABAP.System
-
Lookup.SAPACABAP.Status.ReconAttrMap
-
Lookup.SAPACABAP.TimeZone
-
Lookup.SAPACABAP.UserGroups
-
Lookup.SAPACABAP.UserLock
-
Lookup.SAPACABAP.UserTitle
-
Lookup.SAPACABAP.UserType
-
The scheduled jobs for lookup field synchronization are used to synchronize values of these lookup definitions, in the preceding list, with the target system. See Scheduled Jobs for Lookup Field Synchronization for more information about scheduled jobs for lookup field synchronization.
After lookup definition synchronization, data is stored in the following format:
-
Code Key format: IT_RESOURCE_KEY~LOOKUP_FIELD_ID_OR_NAME
In this format:
-
IT_RESOURCE_KEY is the numeric code assigned to the IT resource in Oracle Identity Manager.
-
LOOKUP_FIELD_ID_OR_NAME is the target system code or name assigned to the lookup field entry.
The following is a sample value for the Code Key column in the Lookup.SAPABAP.UM.DateFormat lookup definition:
22~6 -
-
Decode format: IT_RESOURCE_NAME~LOOKUP_FIELD_ENTRY
In this format:
-
IT_RESOURCE_NAME is the name of the IT resource in Oracle Identity Manager.
-
LOOKUP_FIELD_ENTRY is the value or description of the lookup field entry on the target system.
The following is a sample value for the Decode column in the Lookup.SAPABAP.DateFormat lookup definition:
SAPUM63~YYYY-MM-DD -
While performing a provisioning operation on Oracle Identity System Administration, you select the IT resource for the target system on which you want to perform the operation. When you perform this action, the lookup definitions on the page are automatically populated with values corresponding to the IT resource (target system installation) that you select.
During lookup field synchronization, new entries are appended to the existing set of entries in the lookup definitions. You can switch from an SAP R/3 target to a SAP CUA target, or you can switch between multiple installations of the same target system. Because the IT resource key is part of each entry created in each lookup definition, only lookup field entries that are specific to the IT resource you select during a provisioning operation are displayed.
1.6.2 Preconfigured Lookup Definitions
Preconfigured lookup definitions are the other lookup definitions that are created in Oracle Identity Manager when you deploy the connector. These lookup definitions are either prepopulated with values or values must be manually entered in them after the connector is deployed.
The other lookup definitions are as follows:
1.6.2.1 Lookup.SAPABAP.Configuration
The Lookup.SAPABAP.Configuration lookup definition holds connector configuration entries that are used during target resource reconciliation and provisioning operations.
Table 1-2 lists the default entries in this lookup definition.
Table 1-2 Entries in the Lookup.SAPABAP.Configuration Lookup Definition
| Code Key | Decode | Description |
|---|---|---|
|
aliasUser |
none |
This entry holds the logon user alias. |
|
batchSize |
100 |
Enter the number of records in each batch that must be included fetched from the target system during a reconciliation run. |
|
Bundle Name |
org.identityconnectors.sap |
This entry holds the name of the connector bundle package. Do not modify this entry. |
|
Bundle Version |
1.0.11170 |
This entry holds the version of the connector bundle class. Do not modify this entry. |
|
changePasswordAtNextLogon |
no |
See Configuring Password Changes for Newly Created Accounts for information about the value to be specified for this entry. |
|
codePage |
none |
This entry holds initial codepage in SAP notation. |
|
compositeRoles |
yes/no |
Enter Note: Both singleRoles and compositeRoles decode values cannot be "no", at least one of the values should be "yes". |
|
Connector Name |
org.identityconnectors.sap.SAPConnector |
This entry holds the name of the connector class. Do not modify this entry. |
|
cuaChildInitialPasswordChangeFuncModule |
ZXLCBAPI_ZXLCUSR_PW_CHANGE |
Name of the Remote Enabled function module that changes the initial password for a user on all CUA child systems. This attribute is not used unless CUA is enabled. If the value is not set, then the password changes will only apply to the CUA system. Setting productive passwords on CUA child systems will also automatically fail without this setting. Do not modify this entry. |
|
cuaChildPasswordChangeFuncModule |
ZXLCBAPI_ZXLCUSR_PASSWORDCHNGE |
Name of the Remote Enabled function module which changes the productive password for a user on a CUA child system. This attribute is not used unless CUA is enabled. Note: If the default value is used, then only the password stored on the CUA central system will be changed. |
|
disableLockStatus |
64 |
Lock Status of an SAP User |
|
enableCUA |
no |
Enter |
|
entitlementRiskAnalysisAccessURL |
None |
This entry holds the URL for Entitlement Risk Analysis web service. |
|
entitlementRiskAnalysisWS |
oracle.iam.grc.sod.scomp.impl.grcsap.util.webservice.sap.ac10.RiskAnalysisWithoutNo |
This entry holds the Webservice client class to get risk analysis for an user account. |
|
gatewayHost |
none |
This entry holds the name or IP address of the gateway host. |
|
gatewayService |
none |
This entry holds the name of the gateway service. |
|
getSSO2 |
none |
Get or do not get a SSO ticket after logon. The value of this entry can be |
|
groups |
GROUPS~USERGROUP |
This field is an embedded object defined in the attribute mapping. In the decode entry, GROUPS is a table name and USERGROUP is a field name on the target system. |
|
lCheck |
none |
Enable or disable logon check at open time. The value of this entry can be set to |
|
mySAPSSO2 |
none |
Specifies the SAP Cookie Version 2 to be used as logon ticket. |
|
overwriteLink |
no |
See Linking of SAP HRMS and SAP R/3 or SAP CUA Accounts for information about the value to be specified for this entry. |
|
parameters |
PARAMETER1~PARID;PARVA |
This field is an embedded object defined in the attribute mapping. In the decode entry, PARAMETER1 is a table name, and PARID and PARVA are field names on the target system. |
|
passwordPropagateToChildSystem |
no |
Enter |
|
ProfileAttributeLabel |
Profile Name |
This field holds the label name of the profile name field in the child form. |
|
Profile attribute name |
USERPROFILE |
This field holds a list of field names for the Profile duty type. The values of this list are separated by a semicolon (;). |
|
Profile form names |
UD_SPUMPC_P;UD_SPUM_PRO |
This field holds a list of all profile child form names used during direct and request-based provisioning. |
|
profiles |
PROFILES~SUBSYSTEM;PROFILE |
This field is an embedded object defined in the attribute mapping. In the decode entry, PROFILES is a table name, and SUBSYSTEM and PROFILE are field names on the target system. |
|
reconcilefuturedatedroles |
yes |
Enter |
|
reconcilepastdatedroles |
yes |
Enter |
|
repositoryDestination |
none |
Specifies the destination to be used as repository. |
|
repositoryPassword |
none |
Specifies the password for a repository user. This entry is mandatory if a repository user is used. |
|
repositorySNCMode |
none |
This entry is optional. If SNC is used for this destination, you can turn off SNC for repository connections by setting this entry to |
|
repositoryUser |
none |
This entry is optional. If the repository destination is not set, and this entry is set, this entry will be used as user for repository calls. With this entry, you can use a different user for repository lookups. |
|
riskLevel |
3 |
In SAP BusinessObjects AC target, each business risk is assigned a criticality level. You can control the risk analysis data returned by the target by specifying a risk level in this entry. |
|
RoleAttributeLabel |
USERROLE |
This entry holds the label name of the role name field in the child form |
|
Role attribute name |
Profile Name |
This field holds a list of field names for the Role duty type. The values of this list are separated by a semicolon (;). |
|
Role form names |
UD_SPUMRC_P;UD_SAPRL |
This field holds a list of all role child form names used during direct and request-based provisioning. |
|
roles |
ACTIVITYGROUPS~SUBSYSTEM;AGR_NAME;TO_DAT;FROM_DAT;ORG_FLAG |
This field is an embedded object defined in the attribute mapping. In the decode entry, ACTIVITYGROUPS is a table name on the target system. SUBSYSTEM, TO_DAT, FROM_DAT, and AGR_NAME are field names on the target system. |
|
sapSystemTimeZone |
PST |
This entry holds the SAP target system time zone. |
|
singleRoles |
yes/no |
Enter |
|
SOD Configuration lookup |
Lookup.SAPABAP.Configuration |
This entry holds the name of the lookup definition that contains SoD configuration properties. |
|
tpHost |
none |
This entry holds the host name of the external server program. |
|
tpName |
none |
This entry holds the program ID of the external server program. |
|
type |
none |
This entry holds the type of the remote host. This entry can have the following values:
|
|
User Configuration Lookup |
Lookup.SAPABAP.UM.Configuration |
This entry holds the name of the lookup definition that contains user-specific configuration properties. Do not modify this entry. |
|
validatePERNR |
no |
See Linking of SAP HRMS and SAP R/3 or SAP CUA Accounts for information about the value to be specified for this entry. |
|
wsdlFilePath |
< file directory> |
Enter the absolute path of the directory containing the following file: GRAC_RISK_ANALYSIS_WOUT_NO_WS.WSDL. Note:
|
|
ApplicationType |
none |
This entry holds the name of the type of application. |
|
BusinessProcess |
none |
This entry holds the name of the business process. |
|
OrgLevel |
none |
This entry holds the name of the organization. |
|
ReportFormat |
none |
This entry holds the format of the report. |
|
RiskLevel |
none |
This entry holds the value of the risk level. |
|
RoleType |
none |
This entry holds the name of the type of role. |
|
RuleId |
none |
This entry holds the name of the rule id. |
|
RuleSetId |
none |
This entry holds the value of the rule set id. |
|
SimulationRiskOnly |
none |
This entry holds the value that is set for the SimulationriskOnly parameter. |
|
UserGroup |
none |
This entry holds the name of the user group. |
|
UserType |
none |
This entry holds the name of the type of user. |
|
HitCount |
none |
This entry supports an interger type value. It hold the value of the hit count. |
|
AdditionalAttr |
none |
This is a multivalued attribute. Note: If you want to configure more than one value for multi valued attribute, separate the Decode values with a comma (,). |
|
OrgRule |
none |
This is a multivalued attribute. Note: If you want to configure more than one value for multi valued attribute, separate the Decode values with a comma (,). |
|
OrgVal |
none |
This is a multivalued attribute. Note: If you want to configure more than one value for multi valued attribute, separate the Decode values with a comma (,). |
|
ReportType |
none |
This is a multivalued attribute. Note: If you want to configure more than one value for multi valued attribute, separate the Decode values with a comma (,). |
|
RiskId |
none |
This is a multivalued attribute. Note: If you want to configure more than one value for multi valued attribute, separate the Decode values with a comma (,). |
1.6.2.2 Lookup.SAPABAP.UM.Configuration
The Lookup.SAPABAP.UM.Configuration lookup definition holds configuration entries that are specific to the user object type. This lookup definition is used during user management operations when your target system is configured as a target resource.
Table 1-3 lists the default entries in this lookup definition.
Table 1-3 Entries in the Lookup.SAPABAP.UM.Configuration Lookup Definition
| Code Key | Decode | Description |
|---|---|---|
|
Provisioning Attribute Map |
Lookup.SAPABAP.UM.ProvAttrMap |
This entry holds the name of the lookup definition that maps process form fields and target system attributes. See Lookup.SAPABAP.UM.ProvAttrMap for more information about this lookup definition. |
|
Provisioning Validation Lookup |
Lookup.SAPABAP.UM.ProvValidation |
This entry holds the name of the lookup definition that is used to configure validation of attribute values entered on the process form during provisioning operations. See Configuring Validation of Data During Reconciliation and Provisioning for more information about adding entries in this lookup definition. |
|
Recon Attribute Map |
Lookup.SAPABAP.UM.ReconAttrMap |
This entry holds the name of the lookup definition that maps resource object fields and target system attributes. See Lookup.SAPABAP.UM.ReconAttrMap for more information about this lookup definition. |
|
Recon Transformation Lookup |
Lookup.SAPABAP.UM.ReconTransformation |
This entry holds the name of the lookup definition that is used to configure transformation of attribute values that are fetched from the target system during user reconciliation. See Configuring Transformation of Data During User Reconciliation for more information about adding entries in this lookup definition. |
|
Recon Validation Lookup |
Lookup.SAPABAP.UM.ReconValidation |
This entry holds the name of the lookup definition that is used to configure validation of attribute values that are fetched from the target system during reconciliation. See Configuring Validation of Data During Reconciliation and Provisioning for more information about adding entries in this lookup definition. |
1.6.2.3 Lookup.SAPABAP.UM.ProvAttrMap
The Lookup.SAPABAP.UM.ProvAttrMap lookup definition holds mappings between process form fields and target system attributes. This lookup definition is used during provisioning. This lookup definition is preconfigured. Table 1-14 lists the default entries.
You can add entries in this lookup definitions if you want to map new target system attributes for provisioning. See Extending the Functionality of the Connector for more information.
1.6.2.4 Lookup.SAPABAP.UM.ReconAttrMap
The Lookup.SAPABAP.UM.ReconAttrMap lookup definition holds mappings between resource object fields and target system attributes. This lookup definition is used during reconciliation. This lookup definition is preconfigured. Table 1-10 lists the default entries.
You can add entries in this lookup definitions if you want to map new target system attributes for reconciliation. See Extending the Functionality of the Connector for more information.
1.6.2.5 Lookup.SAPABAP.UM.ReconTransformation
The Lookup.SAPABAP.UM.ReconTransformation lookup definition is used to configure transformation of attribute values that are fetched from the target system during user reconciliation. See Configuring Transformation of Data During User Reconciliation for more information about adding entries in this lookup definition.
1.6.2.6 Lookup Definitions for Validation of Data
The Lookup.SAPABAP.UM.ProvValidation and Lookup.SAPABAP.UM.ReconValidation lookup definitions are used to configure validation of attribute values entered on the process form during provisioning and reconciliation operations. See Configuring Validation of Data During Reconciliation and Provisioning for more information about adding entries in this lookup definition.
1.6.2.7 Lookup Definitions for Exclusion Lists
This section describes the lookup definitions that hold resources for which you do not want to perform provisioning and reconciliation operations. Exclusions can be applied to any attribute in the process form or reconciliation profile. The Code Key value must be one of the Code Key values in Lookup.SAPABAP.UM.ReconAttrMap or Lookup.SAPABAP.UM.ProvAttrMap lookup definitions.
You can use one of the following lookups:
-
Lookup.SAPABAP.ReconExclusionList
-
Lookup.SAPABAP.ProvExclusionList
The following is the format of the values stored in these lookups:
| Code Key | Decode | Sample Values |
|---|---|---|
|
User Name |
User ID of a user |
Code Key: userName Decode: User001 |
|
User Name with the [PATTERN] suffix |
A regular expression supported by the representation in the |
Code Key: userName[PATTERN] To exclude users matching any of the user ID 's User001, User002, User088, then: Decode: User001|User002|User088 To exclude users whose user ID 's start with 00012, then: Decode: 00012* See Also: For information about the supported patterns, visit |
See Configuring Resource Exclusion Lists for more information about adding entries in this lookup definition.
1.6.2.8 Lookup.SAPABAP.UM.RoleChildformMappings
The Lookup.SAPABAP.UM.RoleChildformMappings lookup definition contains information about the actual and dummy child form mapped fields that are used during request-based provisioning of role entitlements. This lookup definition is preconfigured. Do not add or modify entries in this lookup definition.
If you are using a cloned connector for request-based provisioning of entitlements, then you must update the respective child form field names manually in this lookup definition.
This lookup definition contains the following entries:
| Code Key | Decode |
|---|---|
|
UD_SPUMRC_P_SYSTEMNAME |
UD_SAPRL_SYSTEMNAME |
|
UD_SPUMRC_P_STARTDATE |
UD_SAPRL_STARTDATE,DATE |
|
UD_SPUMRC_P_ENDDATE |
UD_SAPRL_ENDDATE,DATE |
|
UD_SPUMRC_P_USERROLE |
UD_SAPRL_USERROLE |
1.6.2.9 Lookup.SAPABAP.UM.ProfileChildformMappings
The Lookup.SAPABAP.UM.ProfileChildformMappings lookup definition contains information about the actual and dummy child form mapped fields that are used during request-based provisioning of profile entitlements. This lookup definition is preconfigured. Do not add or modify entries in this lookup definition.
If you are using a cloned connector for request-based provisioning of entitlements, then you must update the respective child form field names manually in this lookup definition.
This lookup definition contains the following entries:
| Code Key | Decode |
|---|---|
|
UD_SPUMPC_P_SYSTEMNAME |
UD_SPUM_PRO_SYSTEMNAME |
|
UD_SPUMPC_P_USERPROFILE |
UD_SPUM_PRO_USERPROFILE |
1.6.2.10 Preconfigured Lookup Definitions for Access Request Control
This section discusses the other lookup definitions that are created in Oracle Identity Manager when you deploy the Access Request Control connector. These lookup definitions are either prepopulated with values or values must be manually entered in them after the connector is deployed. The other lookup definitions are as follows:
1.6.2.10.1 Lookup.SAPACABAP.Status.Configuration
The Lookup.SAPACABAP.Status.Configuration lookup definition holds status configuration entries that are specific to the user object type. This lookup definition is used during user management operations when your target system is configured as a target resource.
Table 1-4 Entries in the Lookup.SAPACABAP.Status.Configuration Lookup Definition
| Code | Decode | Description |
|---|---|---|
|
Provisioning Attribute Map |
Lookup.SAPACABAP.Status.ProvAttrMap |
This entry holds the name of the lookup definition that maps process form fields and target system attributes |
|
Provisioning Validation Lookup |
Lookup.SAPACABAP.Status.ProvValidation |
This entry holds the name of the lookup definition that is used to configure validation of attribute values entered on the process form during provisioning operations |
|
Recon Attribute Map |
Lookup.SAPACABAP.Status.ReconAttrMap |
This entry holds the name of the lookup definition that maps resource object fields and target system attributes. See Lookup.SAPACABAP.Status.ReconAttrMap for more information about this lookup definition. |
1.6.2.10.2 Lookup.SAPACABAP.Status.ReconAttrMap
The Lookup.SAPACABAP.Status.ReconAttrMap lookup definition holds mappings between resource object fields and target system attributes. This lookup definition is used during reconciliation. This lookup definition is preconfigured.
Table 1-5 Entries in the Lookup.SAPACABAP.Status.ReconAttrMap Lookup Definition
| Code | Decode |
|---|---|
|
AC Request ID |
__UID__ |
|
AC Request Status |
RequestStatus |
|
AC Request Type |
RequestType |
|
User ID |
User ID |
1.6.3 Preconfigured Lookup Definitions for SAP BusinessObjects AC 10
Preconfigured lookup definitions are the other lookup definitions that are created in Oracle Identity Manager when you deploy the connector. These lookup definitions are either prepopulated with values or values must be manually entered in them after the connector is deployed.
This section discusses the lookup definitions for SAP BusinessObjects AC 10 that are created in Oracle Identity Manager when you deploy the connector. The lookup definitions are as follows:
1.6.3.1 Lookup.SAPAC10ABAP.Configuration
The Lookup.SAPAC10ABAP.Configuration lookup definition holds connector configuration entries that are used during target resource reconciliation and provisioning operations.
Table 1-6 lists the default entries in this lookup definition.
Table 1-6 Entries in the Lookup.SAPAC10ABAP.Configuration Lookup Definition
| Code Key | Decode | Description |
|---|---|---|
|
aliasUser |
None |
This entry holds the logon user alias |
|
appLookupAccessURL |
None |
URL for Application Lookup web service |
|
appLookupWS |
oracle.iam.ws.sap.ac10.SelectApplication |
Web service client to get all applications configured in SAP BusinessObjects AC |
|
assignRoleReqType |
002~Change Account~002~006 |
Name of the request type to be used for assign role request in SAP BusinessObjects AC The format of the decode value is as follows:
The value of RequestType is available in Lookup.SAPAC10ABAP.RequestType. The values of ItemProvActionForSystem and ItemProvActionForRole are available in Lookup.SAPAC10ABAP.ItemProvAction. |
|
auditLogsAccessURL |
None |
URL for Audit Logs web service |
|
auditLogsWS |
oracle.iam.ws.sap.ac10.AuditLogs |
Web service client to get audit logs |
|
batchSize |
100 |
Enter the number of records in each batch that must be fetched from the target system during a reconciliation run |
|
Bundle Name |
org.identityconnectors.sapacum |
Name of the connector bundle package |
|
Bundle Version |
1.0.11170 |
Version of the connector bundle class |
|
changePasswordAtNextLogon |
No |
See Linking of SAP HRMS and SAP R/3 or SAP CUA Accounts for information about the value that must be specified for this entry |
|
codePage |
None |
This entry holds the initial code page in SAP notation |
|
compositeRoles |
No |
Enter Note: Both singleRoles and compositeRoles decode values cannot be "no", at least one of the values should be "yes". |
|
Connector Name |
org.identityconnectors.sapacum.SAPACUMConnector |
Name of the connector class |
|
createUserReqType |
001~New Account~001 |
Name of the request type to use for create user request in SAP BusinessObjects AC The format of the decode value is as follows:
The value of RequestType is available in Lookup.SAPAC10ABAP.RequestType. The value of ItemProvActionForSystem is available in Lookup.SAPAC10ABAP.ItemProvAction. |
|
cuaChildInitialPasswordChangeFuncModule |
ZXLCBAPI_ZXLCUSR_PW_CHANGE |
Name of the Remote Enabled function module that changes the initial password for a user on all CUA child systems This attribute is not used unless CUA is enabled. If the value is not set, then the password changes will only apply to the CUA system. Setting productive passwords on CUA child systems will also automatically fail without this setting. Do not modify this entry. |
|
cuaChildPasswordChangeFuncModule |
ZXLCBAPI_ZXLCUSR_PASSWORDCHNGE |
Name of the Remote Enabled function module that changes the productive password for a user on a CUA child system. This attribute is not used unless CUA is enabled. Note: If the default value is used, then only the password stored on the CUA central system will be changed. |
|
deleteUserReqType |
003~Delete Account~003 |
Name of the request type to use for delete user request in SAP BusinessObjects AC |
|
disableLockStatus |
64 |
Lock Status of an SAP User |
|
enableCUA |
No |
Enter |
|
gatewayHost |
None |
This entry holds the name or IP address of the gateway host |
|
gatewayService |
None |
This entry holds the name of the gateway service |
|
getSSO2 |
None |
This entry specifies whether to get or not get an SSO ticket after logon. The value of this entry can be |
|
groups |
GROUPS~USERGROUP |
This field is an embedded object that is defined in the attribute mapping. In the decode entry, GROUPS is a table name and USERGROUP is a field name on the target system. |
|
ignoreOpenStatus |
Yes |
Specify whether new requests can be sent for a particular user, even if the last request for the user is in the Open status |
|
lCheck |
None |
Enable or disable logon check at open time. The value of this entry can be set to |
|
lockUserReqType |
004~Lock Account~004 |
Name of the request type to use for lock user request in SAP BusinessObjects AC |
|
logAuditTrial |
Yes |
Specify whether complete audit trial needs to be logged whenever status request web service is invoked |
|
modifyUserReqType |
002~Change Account~002 |
Name of the request type to use for modify user request in SAP BusinessObjects AC |
|
mySAPSSO2 |
None |
Specifies the SAP Cookie Version 2 that must be used as a logon ticket |
|
otherLookupAccessURL |
None |
URL for Other Lookup web service |
|
otherLookupWS |
oracle.iam.ws.sap.ac10.SearchLookup |
Web service client to get other lookup field details |
|
overwriteLink |
No |
See Linking of SAP HRMS and SAP R/3 or SAP CUA Accounts Accounts" for information about the value that must be specified for this entry. |
|
parameters |
PARAMETER1~PARID;PARVA |
This field is an embedded object that is defined in the attribute mapping. In the decode entry, PARAMETER1 is a table name, and PARID and PARVA are the field names on the target system. |
|
passwordPropagateToChildSystem |
No |
Enter |
|
profiles |
PROFILES~SUBSYSTEM;PROFILE |
This field is an embedded object defined in the attribute mapping. In the decode entry, PROFILES is a table name, and SUBSYSTEM and PROFILE are the field names on the target system. |
|
provActionAttrName |
provAction;ReqLineItem |
Name of the Provision Action target system attribute |
|
provItemActionAttrName |
provItemAction;ReqLineItem |
Name of the Provision Item Action target system attribute |
|
reconcilefuturedatedroles |
Yes |
Enter |
|
reconcilepastdatedroles |
Yes |
Enter |
|
removeRoleReqType |
002~Change Account~002~009 |
Name of the request type to use for remove user request in SAP BusinessObjects AC |
|
ReportFormat |
No |
This entry holds the format of the report. Note: For webService grac_risk_analysis_wout_no_ws, ReportFormat is a mandatory field from SP17 onwards. Default Value: Note: This parameter is applicable only for SAP UM with SoD. |
|
repositoryDestination |
None |
Specifies the destination to be used as repository. |
|
repositoryPassword |
None |
Specifies the password for a repository user. This entry is mandatory if a repository user is used. |
|
repositorySNCMode |
None |
This entry is optional. If SNC is used for this destination, you can turn off SNC for repository connections by setting the value of this entry to |
|
repositoryUser |
None |
This entry is optional. If the repository destination is not set, and this entry is set, this entry will be used as user for repository calls. With this entry, you can use a different user for repository lookups. |
|
requestStatusAccessURL |
None |
URL for Status Request web service |
|
requestStatusValue |
OK |
The value that gets updated in the AC Request Status field on the process form. |
|
requestStatusWS |
oracle.iam.ws.sap.ac10.RequestStatus |
Web service client to get status of provisioning request |
|
requestTypeAttrName |
Reqtype;Header |
Name of the request type attribute used to differentiate request flows from the SAPUMCREATE adapter |
|
riskLevel |
High |
In SAP BusinessObjects AC, each business risk is assigned a criticality level. You can control the risk analysis data returned by SAP BusinessObjects by specifying a risk level. |
|
roleLookupAccessURL |
None |
URL for Role Lookup web service |
|
roleLookupWS |
oracle.iam.ws.sap.ac10.SearchRoles |
Web service client to get all roles |
|
roles |
ACTIVITYGROUPS~SUBSYSTEM;AGR_NAME;TO_DAT;FROM_DAT;ORG_FLAG |
This field is an embedded object defined in the attribute mapping. In the decode entry, ACTIVITYGROUPS is a table name on the target system. SUBSYSTEM, TO_DAT, FROM_DAT, AGR_NAME and ORG_FLAG are the field names on the target system. |
|
sapSystemTimeZone |
PST |
This entry holds the SAP target system time zone. |
|
singleRoles |
yes |
Enter |
|
Status Configuration Lookup |
Lookup.SAPACABAP.Status.Configuration |
This entry holds the name of the lookup definition that contains user-specific configuration properties. Do not modify this entry. |
|
tpHost |
None |
This entry holds the host name of the external server program. |
|
tpName |
None |
This entry holds the program ID of the external server program. |
|
type |
None |
This entry holds the type of the remote host. This entry can hold the following values:
|
|
unlockUserReqType |
005~unlock user~005 |
Name of the request type to use for unlock user request in SAP BusinessObjects AC |
|
userAccessAccessURL |
None |
URL for User Access web service |
|
userAccessWS |
oracle.iam.ws.sap.ac10.UserAccess |
Web service client to get status of user access |
|
User Configuration Lookup |
Lookup.SAPAC10ABAP.UM.Configuration |
Name of the lookup definition that contains user-specific configuration properties See Lookup.SAPAC10ABAP.Configuration for more information. |
|
validatePERNR |
No |
See Linking of SAP HRMS and SAP R/3 or SAP CUA Accounts for information about the value that must be specified for this entry. |
|
wsdlFilePath |
Absolute path of the files |
Enter the absolute path of the directory containing the following files: GRAC_USER_ACCESS_WS.WSDL GRAC_SEARCH_ROLES_WS.WSDL GRAC_SELECT_APPL_WS.WSDL GRAC_REQUEST_STATUS_WS.WSDL GRAC_LOOKUP_WS.WSDL GRAC_AUDIT_LOGS_WS.WSDL Note:
|
1.6.3.2 Lookup.SAPAC10ABAP.Configuration
The Lookup.SAPABAP.AC10.UM.Configuration lookup definition holds configuration entries that are specific to the user object type. This lookup definition is used during user management operations when your target system is configured as a target resource.
Table 1-7 lists the default entries in this lookup definition.
Table 1-7 Entries in the Lookup.SAPAC10ABAP.Configuration Lookup Definition
| Code Key | Decode | Description |
|---|---|---|
|
Provisioning Attribute Map |
Lookup.SAPAC10ABAP.UM.ProvAttrMap |
This entry holds the name of the lookup definition that maps process form fields and target system attributes. See Lookup.SAPAC10ABAP.UM.ProvAttrMap for more information about this lookup definition. |
|
Provisioning Validation Lookup |
Lookup.SAPAC10ABAP.UM.ProvValidation |
This entry holds the name of the lookup definition that is used to configure validation of attribute values entered on the process form during provisioning operations. See Lookup.SAPAC10ABAP.UM.ProvValidation for more information about this lookup definition. |
|
Recon Attribute Map |
Lookup.SAPAC10ABAP.UM.ReconAttrMap |
This entry holds the name of the lookup definition that maps resource object fields and target system attributes. See Lookup.SAPAC10ABAP.UM.ReconAttrMap for more information about this lookup definition. |
|
Recon Transformation Lookup |
Lookup.SAPAC10ABAP.UM.ReconTransformation |
This entry holds the name of the lookup definition that is used to configure transformation of attribute values that are fetched from the target system during user reconciliation. See Configuring Transformation of Data During User Reconciliation for more information about adding entries in this lookup definition. |
|
Recon Validation Lookup |
Lookup.SAPAC10ABAP.UM.ReconValidation |
This entry holds the name of the lookup definition that is used to configure validation of attribute values that are fetched from the target system during reconciliation. See Configuring Validation of Data During Reconciliation and Provisioning for more information about adding entries in this lookup definition. |
1.6.3.3 Lookup.SAPAC10ABAP.UM.ProvAttrMap
The Lookup.SAPAC10ABAP.UM.ProvAttrMap lookup definition holds mappings between process form fields and target system attributes. This lookup definition is used during provisioning. This lookup definition is preconfigured. Table 1-8 lists the default entries.
You can add entries in this lookup definitions if you want to map new target system attributes for provisioning. See Extending the Functionality of the Connector for more information.
Table 1-8 Entries in the Lookup.SAPAC10ABAP.UM.ProvAttrMap Lookup Definition
| Code Key | Decode |
|---|---|
|
AC Business Process[Lookup] |
bproc;Header |
|
Accounting Number |
accno;UserInfo |
|
AC Functional Area[Lookup] |
funcarea;Header |
|
AC Manager |
manager;UserInfo |
|
AC Manager email |
managerEmail;UserInfo |
|
AC Manager First Name |
managerFirstname;UserInfo |
|
AC Manager Last Name |
managerLastname;UserInfo |
|
AC Priority[Lookup] |
priority;Header |
|
AC Request Due Date[Date] |
reqDueDate;Header |
|
AC Request Id[WRITEBACK] |
RequestId |
|
AC Requestor email |
email;Header |
|
AC Requestor ID |
requestorId;Header |
|
AC Request Reason |
requestReason;Header |
|
AC Request Status[WRITEBACK] |
RequestStatus |
|
AC Request Type[WRITEBACK] |
RequestType |
|
AC System[Lookup] |
reqInitSystem;Header |
|
Alias |
alias;UserInfo |
|
Building |
BUILDING_P;ADDRESS;BUILDING_P;ADDRESSX |
|
Communication Type |
commMethod;UserInfo |
|
Company[Lookup] |
COMPANY;COMPANY;COMPANY;COMPANYX |
|
Contractual User Type[Lookup] |
LIC_TYPE;UCLASS;UCLASS;UCLASSX |
|
Cost Center |
costcenter;UserInfo |
|
Date Format |
dateFormat;UserInfo |
|
Decimal Notation |
decNotation;UserInfo |
|
Department |
DEPARTMENT;ADDRESS;DEPARTMENT;ADDRESSX |
|
E Mail |
email;UserInfo |
|
Fax Extension |
FAX_EXTENS;ADDRESS;FAX_EXTENS;ADDRESSX |
|
Fax Number |
fax;UserInfo |
|
First Name |
fname;UserInfo |
|
Floor |
FLOOR_P;ADDRESS;FLOOR_P;ADDRESSX |
|
Function |
FUNCTION;ADDRESS;FUNCTION;ADDRESSX |
|
Group Name[Lookup] |
CLASS;LOGONDATA;CLASS;LOGONDATAX |
|
Language Communication[Lookup] |
LANGU_P;ADDRESS;LANGU_P;ADDRESSX |
|
Last Name |
lname;UserInfo |
|
Logon Language |
logonLang;UserInfo |
|
Password |
__PASSWORD__ |
|
Personnel Number |
PERNR |
|
Room Number |
ROOM_NO_P;ADDRESS;ROOM_NO_P;ADDRESSX |
|
Start Menu |
startMenu;UserInfo |
|
Telephone Extension |
TEL1_EXT;ADDRESS;TEL1_EXT;ADDRESSX |
|
Telephone Number |
telnumber;UserInfo |
|
Time Zone[Lookup] |
TZONE;LOGONDATA;TZONE;LOGONDATAX |
|
Title[Lookup] |
title;UserInfo |
|
UD_UMAC_GRP~User Group[Lookup] |
userGroup;UserGroup |
|
UD_UMAC_PRM~Parameter ID[Lookup] |
Parameter~parameter~parameter;Parameter |
|
UD_UMAC_PRM~Parameter Value |
Parameter~parameter~parameterValue;Parameter |
|
UD_UMAC_ROL~End Date[Date] |
roles~ACTIVITYGROUPS~ValidTo;ReqLineItem |
|
UD_UMAC_ROL~Role Name[Lookup] |
roles~ACTIVITYGROUPS~itemName;ReqLineItem |
|
UD_UMAC_ROL~Role System Name[Lookup] |
roles~ACTIVITYGROUPS~connector;ReqLineItem |
|
UD_UMAC_ROL~Start Date[Date] |
roles~ACTIVITYGROUPS~validFrom;ReqLineItem |
|
UD_UMAC_PRO~Profile Name[Lookup] |
profile~PROFILES~itemName;ReqLineItem |
|
UD_UMAC_PRO~Profile System Name[Lookup] |
profile~PROFILES~connector;ReqLineItem |
|
Unique ID |
__UID__ |
|
User Group[Lookup] |
userGroup;UserInfo |
|
User ID |
userId;UserInfo |
|
User Lock |
userLock;None |
|
User Type |
userType;UserInfo |
|
Valid From[Date] |
validFrom;UserInfo |
|
Valid Through[Date] |
validTo;UserInfo |
1.6.3.4 Lookup.SAPAC10ABAP.UM.ReconAttrMap
The Lookup.SAPAC10ABAP.UM.ReconAttrMap lookup definition holds mappings between resource object fields and target system attributes. This lookup definition is used during reconciliation. This lookup definition is preconfigured. Table 1-9 lists the default entries.
You can add entries in this lookup definitions if you want to map new target system attributes for reconciliation. See Extending the Functionality of the Connector for more information.
Table 1-9 Entries in the Lookup.SAPAC10ABAP.UM.ReconAttrMap Lookup Definition
| Code Key | Decode |
|---|---|
|
Accounting Number |
ACCNT;LOGONDATA |
|
Alias |
USERALIAS;ALIAS |
|
Building |
BUILDING_P;ADDRESS |
|
Communication Type[Lookup] |
COMM_TYPE;ADDRESS |
|
Company[Lookup] |
COMPANY;COMPANY |
|
Contractual User Type[Lookup] |
LIC_TYPE;UCLASS|UCLASSSYS |
|
Cost Center |
KOSTL;DEFAULTS |
|
Date Format[Lookup] |
DATFM;DEFAULTS |
|
Decimal Notation[Lookup] |
DCPFM;DEFAULTS |
|
Department |
DEPARTMENT;ADDRESS |
|
E Mail |
E_MAIL;ADDRESS |
|
Fax Extension |
FAX_EXTENS;ADDRESS |
|
Fax Number |
FAX_NUMBER;ADDRESS |
|
First Name |
FIRSTNAME;ADDRESS |
|
Floor |
FLOOR_P;ADDRESS |
|
Function |
FUNCTION;ADDRESS |
|
Group~User Group[Lookup] |
groups~GROUPS~USERGROUP |
|
Group Name[Lookup] |
CLASS;LOGONDATA |
|
Language Communication[Lookup] |
LANGU_P;ADDRESS |
|
Last Name |
LASTNAME;ADDRESS |
|
Logon Language |
LANGU;DEFAULTS |
|
Parameter~Parameter ID[Lookup] |
parameters~PARAMETER1~PARID |
|
Parameter~Parameter Value |
parameters~PARAMETER1~PARVA |
|
Profile~Profile Name[Lookup] |
profiles~PROFILES~PROFILE |
|
Profile~Profile System Name[Lookup] |
profiles~PROFILES~SUBSYSTEM |
|
Role~End Date[Date] |
roles~ACTIVITYGROUPS~TO_DAT |
|
Role~Role Name[Lookup] |
roles~ACTIVITYGROUPS~AGR_NAME |
|
Role~Role System Name[Lookup] |
roles~ACTIVITYGROUPS~SUBSYSTEM |
|
Role~Start Date[Date] |
roles~ACTIVITYGROUPS~FROM_DAT |
|
Room Number |
ROOM_NO_P;ADDRESS |
|
Start Menu |
START_MENU;DEFAULTS |
|
Status |
__ENABLE__ |
|
Telephone Extension |
TEL1_EXT;ADDRESS |
|
Telephone Number |
TEL1_NUMBR;ADDRESS |
|
Time Zone[Lookup] |
TZONE;LOGONDATA |
|
Title[Lookup] |
TITLE_P;ADDRESS |
|
Unique ID |
__UID__ |
|
User ID |
__UID__ |
|
User Lock |
__LOCK_OUT__ |
|
User Type |
USTYP;LOGONDATA |
|
Valid From[Date] |
GLTGV;LOGONDATA |
|
Valid Through[Date] |
GLTGB;LOGONDATA |
1.6.3.5 Lookup.SAPAC10ABAP.UM.ProvValidation
The Lookup.SAPAC10ABAP.UM.ProvValidation lookup definition is used to configure validation of attribute values entered on the process form during provisioning operations. See Configuring Validation of Data During Reconciliation and Provisioning for more information.
1.6.3.6 Lookup.SAPAC10ABAP.ItemProvAction
The Lookup.SAPABAP.AC10.ItemProvAction lookup definition holds Item provision action code from SAP BusinessObjects AC 10. This code used to create a request in SAP BusinessObjects AC 10 to add or remove roles.
The Item provision action is used to configure the Decode values of the following Code Key entries in the Lookup.SAPAC10ABAP.Configuration lookup definition:
-
assignRoleReqType
-
removeRoleReqType
The Lookup.SAPAC10ABAP.ItemProvAction lookup definition is populated by the SAP AC ItemProvAction Lookup Reconciliation scheduled job. By default, there are no entries in the lookup definition.
1.6.3.7 Lookup.SAPAC10ABAP.RequestType
The Lookup.SAPAC10ABAP.RequestType lookup definition is used to configure the Decode values of the following Code Key entries in the Lookup.SAPAC10ABAP.Configuration lookup definition:
-
assignRoleReqType
-
createUserReqType
-
deleteUserReqType
-
lockUserReqType
-
modifyUserReqType
-
removeRoleReqType
-
unlockUserReqType
The Lookup.SAPAC10ABAP.RequestType lookup definition is populated by the SAP AC RequestType Lookup Reconciliation scheduled job. By default, there are no entries in the lookup definition.
1.6.3.8 Lookup.SAPAC10ABAP.UM.ReconTransformation
The Lookup.SAPAC10ABAP.UM.ReconTransformation lookup definition is used to configure transformation of attribute values that are fetched from the target system during user reconciliation.
See Configuring Transformation of Data During User Reconciliation for more information.
1.6.3.9 Lookup.SAPAC10ABAP.UM.ReconValidation
The Lookup.SAPAC10ABAP.UM.ReconValidation lookup definition is used to configure validation of attribute values that are entered on the process form during reconciliation operations.
See Configuring Validation of Data During Reconciliation and Provisioning for more information.
1.6.4 Lookup Definitions Synchronized with the Target System for SAP AC
Lookup field synchronization involves copying additions or changes made to specific fields in the target system to lookup definitions in Oracle Identity Manager.
During a provisioning operation, you use a lookup field on the process form to specify a single value from a set of values. For example, you use the Date Format lookup field to select a date format from the list of supported date formats. When you deploy the connector, lookup definitions corresponding to the lookup fields on the target system are automatically created in Oracle Identity Manager. Lookup field synchronization involves copying additions or changes made to the target system lookup fields into the lookup definitions in Oracle Identity Manager.
The following lookup definitions are populated with values fetched from the target system by the scheduled jobs for lookup field synchronization
-
Lookup.SAPACABAP.Bproc
-
Lookup.SAPACABAP.CommType
-
Lookup.SAPACABAP.Company
-
Lookup.SAPACABAP.ContractualUserType
-
Lookup.SAPACABAP.DateFormat
-
Lookup.SAPACABAP.DecimalNotation
-
Lookup.SAPACABAP.Funcarea
-
Lookup.SAPACABAP.LangComm
-
Lookup.SAPACABAP.Parameter
-
Lookup.SAPACABAP.Priority
-
Lookup.SAPACABAP.Profile
-
Lookup.SAPACABAP.ReqInitSystem
-
Lookup.SAPACABAP.Roles
-
Lookup.SAPACABAP.System
-
Lookup.SAPACABAP.TimeZone
-
Lookup.SAPACABAP.UM.ProvExclusionList
-
Lookup.SAPACABAP.UM.ReconExclusionList
-
Lookup.SAPACABAP.UserGroups
-
Lookup.SAPACABAP.UserLock
-
Lookup.SAPACABAP.UserTitle
-
Lookup.SAPACABAP.UserType
The scheduled jobs for lookup field synchronization are used to synchronize values of these lookup definitions, in the preceding list, with the target system. See Scheduled Jobs for Lookup Field Synchronization for more information about scheduled jobs for lookup field synchronization.
After lookup definition synchronization, data is stored in the following format:
-
Code Key format: IT_RESOURCE_KEY~LOOKUP_FIELD_ID_OR_NAME
In this format:
-
IT_RESOURCE_KEY is the numeric code assigned to the IT resource in Oracle Identity Manager.
-
LOOKUP_FIELD_ID_OR_NAME is the target system code or name assigned to the lookup field entry.
The following is a sample value for the Code Key column in the Lookup.SAPABAP.UM.DateFormat lookup definition:
22~6 -
-
Decode format: IT_RESOURCE_NAME~LOOKUP_FIELD_ENTRY
In this format:
-
IT_RESOURCE_NAME is the name of the IT resource in Oracle Identity Manager.
-
LOOKUP_FIELD_ENTRY is the value or description of the lookup field entry on the target system.
The following is a sample value for the Decode column in the Lookup.SAPABAP.DateFormat lookup definition:
SAPUM63~YYYY-MM-DD -
While performing a provisioning operation on the Oracle Identity System Administration, you select the IT resource for the target system on which you want to perform the operation. When you perform this action, the lookup definitions on the page are automatically populated with values corresponding to the IT resource (target system installation) that you select.
During lookup field synchronization, new entries are appended to the existing set of entries in the lookup definitions. You can switch from an SAP R/3 target to a SAP CUA target, or you can switch between multiple installations of the same target system. Because the IT resource key is part of each entry created in each lookup definition, only lookup field entries that are specific to the IT resource you select during a provisioning operation are displayed.
1.7 Connector Objects Used During Target Resource Reconciliation
Target resource reconciliation involves fetching data about newly created or modified accounts on the target system and using this data to add or modify resources assigned to OIM users.
The SAP UM User Recon scheduled job is used to initiate a reconciliation run. This scheduled job is discussed in SAP UM User Recon.
See Also:
Managing Reconciliation in Oracle Fusion Middleware Administering Oracle Identity Manager for conceptual information about reconciliation
This section discusses the following topics:
1.7.1 User Attributes for Reconciliation
The Lookup.SAPABAP.UM.ReconAttrMap lookup definition maps resource object fields and target system attributes.
The Code Key column stores the names of resource object fields.
The format of the Decode column for single-valued attribute is as follows:
FIELD_NAME;STRUCTURE_NAME
The format of the Decode column for multivalued attributes is as follows:
EMBEDDED_OBJECT_NAME~OBJECT_CLASS~TARGET_FIELD_NAME
Table 1-10 lists entries in this lookup definition.
Table 1-10 Entries in the Lookup.SAPABAP.UM.ReconAttrMap Lookup Definition
| Resource Object Field | Target System Attribute |
|---|---|
|
Accounting Number |
ACCNT;LOGONDATA |
|
Alias |
USERALIAS;ALIAS |
|
Building |
BUILDING_P;ADDRESS |
|
Communication Type[Lookup] |
COMM_TYPE;ADDRESS |
|
Company[Lookup] |
COMPANY;COMPANY |
|
Contractual User Type[Lookup] |
LIC_TYPE;UCLASS|UCLASSSYS |
|
Cost Center |
KOSTL;DEFAULTS |
|
Date Format[Lookup] |
DATFM;DEFAULTS |
|
Decimal Notation[Lookup] |
DCPFM;DEFAULTS |
|
Department |
DEPARTMENT;ADDRESS |
|
E Mail |
E_MAIL;ADDRESS |
|
Fax Extension |
FAX_EXTENS;ADDRESS |
|
Fax Number |
FAX_NUMBER;ADDRESS |
|
First Name |
FIRSTNAME;ADDRESS |
|
Floor |
FLOOR_P;ADDRESS |
|
Function |
FUNCTION;ADDRESS |
|
Group~User Group[Lookup] |
groups~GROUPS~USERGROUP |
|
Group Name[Lookup] |
CLASS;LOGONDATA |
|
Language Communication[Lookup] |
LANGU_P;ADDRESS |
|
Last Name |
LASTNAME;ADDRESS |
|
Logon Language[Lookup] |
LANGU;DEFAULTS |
|
Parameter~Parameter ID[Lookup] |
parameters~PARAMETER1~PARID |
|
Parameter~Parameter Value |
parameters~PARAMETER1~PARVA |
|
Profile~Profile Name[Lookup] |
profiles~PROFILES~PROFILE |
|
Profile~Profile System Name[Lookup] |
profiles~PROFILES~SUBSYSTEM |
|
Role~End Date[Date] |
roles~ACTIVITYGROUPS~TO_DAT |
|
Role~Role Name[Lookup] |
roles~ACTIVITYGROUPS~AGR_NAME |
|
Role~Role System Name[Lookup] |
roles~ACTIVITYGROUPS~SUBSYSTEM |
|
Role~Start Date[Date] |
roles~ACTIVITYGROUPS~FROM_DAT |
|
Room Number |
ROOM_NO_P;ADDRESS |
|
Start Menu |
START_MENU;DEFAULTS |
|
Status |
__ENABLE__ |
|
Telephone Extension |
TEL1_EXT;ADDRESS |
|
Telephone Number |
TEL1_NUMBR;ADDRESS |
|
Time Zone[Lookup] |
TZONE;LOGONDATA |
|
Title[Lookup] |
TITLE_P;ADDRESS |
|
User ID |
__UID__ |
|
User Lock |
__LOCK_OUT__ |
|
User Type[Lookup] |
USTYP;LOGONDATA |
|
Valid From[Date] |
GLTGV;LOGONDATA |
|
Valid Through[Date] |
GLTGB;LOGONDATA |
|
Unique ID |
__UID__ |
1.7.2 Reconciliation Rules
The connector uses reconciliation rules to determine the identity to which Oracle Identity Governance must assign a resource.
See Also:
Reconciliation Engine in Oracle Fusion Middleware Developing and Customizing Applications for Oracle Identity Manager for generic information about reconciliation matching and action rules
The following sections provide information about the reconciliation rules for this connector:
1.7.2.1 Reconciliation Rule
The following is the process-matching rule:
Rule name: SAP UM Recon Rule
Rule element: User Login Equals User ID
In this rule element:
-
User Login is the User ID field of the OIM User form.
-
User ID is the user ID of the SAP account.
1.7.2.2 Viewing Reconciliation Rules in the Design Console
You can view reconciliation rules by using Oracle Identity Manager Design Console.
After you deploy the connector, you can view the reconciliation rule for reconciliation by performing the following steps:
Note:
Perform the following procedure only after the connector is deployed.
1.7.3 Reconciliation Action Rules
Note:
No action is performed for rule conditions that are not predefined for this connector. You can define your own action rule for such rule conditions. See Setting a Reconciliation Action Rule in Oracle Fusion Middleware Developing and Customizing Applications for Oracle Identity Manager for information about modifying or creating reconciliation action rules.
The following sections provide information about the reconciliation rules for this connector:
1.7.3.1 Reconciliation Action Rules for Reconciliation
Reconciliation action rules define that actions the connector must perform based on the reconciliation rules defined for Users.
Table 1-11 lists the action rules for reconciliation.
Table 1-11 Action Rules for Reconciliation
| Rule Condition | Action |
|---|---|
|
No Matches Found |
Assign to Administrator With Least Load |
|
One Entity Match Found |
Establish Link |
|
One Process Match Found |
Establish Link |
1.7.3.2 Viewing Reconciliation Action Rules in the Design Console
You can view reconciliation action rules on the Object Reconciliation tab of a resource object in Oracle Identity Manager Design Console.
After you deploy the connector, you can view the reconciliation action rules for reconciliation by performing the following steps:
1.8 Connector Objects Used During Provisioning
Connector objects such as adapters are used for performing provisioning operations on the target system. These adapters perform provisioning functions on the fields defined in the lookup definition for provisioning.
This section discusses the following topics:
1.8.1 User Provisioning Functions
These are the supported provisioning functions and the adapters that perform these functions for the connector.
Table 1-12 and Table 1-13 list the user provisioning functions supported by the SAP UM and SAP AC UM connectors, and the adapters that perform these functions. The functions listed in the table correspond to either a single or multiple process tasks.
See Also:
Using the Adapter Factory in Oracle Fusion Middleware Developing and Customizing Applications for Oracle Identity Manager for generic information about process tasks and adapters
Table 1-12 User Provisioning Functions Supported by SAP UM
| Function | Adapter |
|---|---|
|
Create a user account |
adpSAPUMCREATE |
|
Update a user account |
adpSAPUMUPDATE |
|
Delete a user account |
adpSAPUMDELETE |
|
Enable a user account |
adpSAPUMENABLE |
|
Disable a user account |
adpSAPUMDISABLE |
|
Update multivalued attribute (for example, role or parameter) |
adpSAPUMUPDATECHILD |
|
Add multivalue attribute |
adpSAPUMADDCHILD |
|
Remove multivalue attribute |
adpSAPUMREMOVECHILD |
|
Prepopulates SAPUM form |
adpSAPUMPREPOPULATE |
|
request entitlement for SAP UM |
adpSAPUMREQUESTENTITLEMENT |
Table 1-13 User Provisioning Functions Supported by SAP AC UM
| Function | Adapter |
|---|---|
|
Create a user account |
adpSAPACUMCREATEUSER |
|
Update a user account |
adpSAPACUMUPDATEUSER |
|
Delete a user account |
adpSAPACUMDELETEUSER |
|
Enable a user account |
adpSAPACUMENABLEUSER |
|
Disable a user account |
adpSAPACUMDISABLEUSER |
|
Update multivalued attribute (for example, role or parameter) |
adpSAPACUMUPDATECHILD |
|
Add multivalue attribute |
adpSAPACUMADDCHILD |
|
Remove multivalue attribute |
adpSAPACUMREMOVECHILD |
|
Prepopulate SAP AC UM Form |
adpSAPACUMPREPOPULATE |
1.8.2 User Attributes for Provisioning
The Lookup.SAPABAP.UM.ProvAttrMap lookup definition maps process form fields with single-valued target system attributes. The Code Key column holds the names of process form fields.
The format of the Decode column for single-valued attributes is as follows:
FIELD_NAME;STRUCTURE_NAME;FIELD_NAME_X;STRUCTURE_NAME_X
In this format:
-
FIELD_NAMEis the name of the field. -
STRUCTURE_NAMEis the name of the structure. -
FIELD_NAME_Xis the name of the field used to indicate whether or not the value inFIELD_NAMEmust be applied. -
STRUCTURE_NAME_Xis the name of the structure that holdsFIELD_NAME_X.
The format of the Decode column for multivalued attributes is as follows:
EMBEDDED_OBJECT_NAME~OBJECT_CLASS~TARGET_FIELD_NAME
Table 1-14 lists the entries in this lookup definition.
Table 1-14 Entries in the Lookup.SAPABAP.UM.ProvAttrMap Lookup Definition
| Process Form Field | Target System Attribute |
|---|---|
|
Accounting Number |
ACCNT;LOGONDATA;ACCNT;LOGONDATAX |
|
Alias |
USERALIAS;ALIAS;BAPIALIAS;ALIASX |
|
Building |
BUILDING_P;ADDRESS;BUILDING_P;ADDRESSX |
|
Communication Type[Lookup] |
COMM_TYPE;ADDRESS;COMM_TYPE;ADDRESSX |
|
Company[Lookup] |
COMPANY;COMPANY;COMPANY;COMPANYX |
|
Contractual User Type[Lookup] |
LIC_TYPE;UCLASS;UCLASS;UCLASSX |
|
Cost Center |
KOSTL;DEFAULTS;KOSTL;DEFAULTSX |
|
Date Format[Lookup] |
LOOKUP;DATFM;DEFAULTS;DATFM;DEFAULTSX |
|
Decimal Notation[Lookup] |
DCPFM;DEFAULTS;DCPFM;DEFAULTSX |
|
Department |
DEPARTMENT;ADDRESS;DEPARTMENT;ADDRESSX |
|
E Mail |
E_MAIL;ADDRESS;E_MAIL;ADDRESSX |
|
Fax Extension |
FAX_EXTENS;ADDRESS;FAX_EXTENS;ADDRESSX |
|
Fax Number |
FAX_NUMBER;ADDRESS;FAX_NUMBER;ADDRESSX |
|
First Name |
FIRSTNAME;ADDRESS;FIRSTNAME;ADDRESSX |
|
Floor |
FLOOR_P;ADDRESS;FLOOR_P;ADDRESSX |
|
Function |
FUNCTION;ADDRESS;FUNCTION;ADDRESSX |
|
Group Name[Lookup] |
CLASS;LOGONDATA;CLASS;LOGONDATAX |
|
Language Communication[Lookup] |
LANGU_P;ADDRESS;LANGU_P;ADDRESSX |
|
Last Name |
LASTNAME;ADDRESS;LASTNAME;ADDRESSX |
|
Logon Language[Lookup] |
LANGU;DEFAULTS;LANGU;DEFAULTSX |
|
Password |
__PASSWORD__ |
|
Personnel Number |
PERNR |
|
Room Number |
ROOM_NO_P;ADDRESS;ROOM_NO_P;ADDRESSX |
|
Start Menu |
START_MENU;DEFAULTS;START_MENU;DEFAULTSX |
|
Telephone Extension |
TEL1_EXT;ADDRESS;TEL1_EXT;ADDRESSX |
|
Telephone Number |
TEL1_NUMBR;ADDRESS;TEL1_NUMBR;ADDRESSX |
|
Time Zone[Lookup] |
TZONE;LOGONDATA;TZONE;LOGONDATAX |
|
Title[Lookup] |
TITLE_P;ADDRESS;TITLE_P;ADDRESSX |
|
UD_SAP_GP~User Group[Lookup] |
groups~GROUPS~USERGROUP |
|
UD_SAP_PARA~Parameter ID[Lookup] |
parameters~PARAMETER1~PARID |
|
UD_SAP_PARA~Parameter Value |
parameters~PARAMETER1~PARVA |
|
UD_SAPRL~End Date[Date] |
roles~ACTIVITYGROUPS~TO_DAT |
|
UD_SAPRL~Role Name[Lookup] |
roles~ACTIVITYGROUPS~AGR_NAME |
|
UD_SAPRL~Start Date[Date] |
roles~ACTIVITYGROUPS~FROM_DAT |
|
UD_SPUM_PRO~Profile Name[Lookup] |
profiles~PROFILES~PROFILE |
|
Unique ID |
__UID__ |
|
User ID |
__NAME__ |
|
User Lock |
User Lock;NONE;NONE;NONE |
|
User Type[Lookup] |
USTYP;LOGONDATA;USTYP;LOGONDATAX |
|
Valid From[Date] |
GLTGV;LOGONDATA;GLTGV;LOGONDATAX |
|
Valid Through[Date] |
GLTGB;LOGONDATA;GLTGB;LOGONDATAX |
1.9 Roadmap for Deploying and Using the Connector
The following is the organization of information in the rest of this guide:
- Deploying the Connector describes procedures that you must perform on Oracle Identity Manager and the target system during each stage of connector deployment.
- Using the Connector describes guidelines on using the connector and the procedure to configure reconciliation runs and perform provisioning operations.
- Extending the Functionality of the Connector describes procedures that you can perform if you want to extend the functionality of the connector.
- Known Issues and FAQs lists known issues and FAQs associated with this release of the connector.
- Troubleshooting the Connector describes the procedure to troubleshoot the connector.
- Files and Directories in the SAP UM Connector Package provides information about files and directories on the installation media.
- Standard BAPIs Used During Connector Operations provides information about standard BAPIs used during connector operations.