Protect Exadata Database
Learn about various data protection methods available for Oracle Exadata Database Service on Dedicated Infrastructure on Oracle AI Database@Azure.
Data in Transit Encryption
Oracle Exadata Database Service on Dedicated Infrastructure is protected with encryption of data in transit by default. This ensures that data moving between application and the database is secured from unauthorized interception or tampering. Oracle Net Services supports multiple industry-standard encryption algorithms including AES, DES, 3DES, and RC4 for securing data in transit. It also offers MD5, SHA-1, and SHA-2 hashing algorithms to verify data integrity.
- TCPS (Secure TCP) Connections
- Uses TLS 1.2 or TLS 1.3.
- Requires a downloadable connection wallet.
- Ensures symmetric encryption via secure handshake using the wallet.
- TLS 1.3 support is available starting with Oracle AI Database 26ai.
- TCP Connections with Native Network Encryption
- Uses Oracle’s built-in encryption protocol.
- Negotiates encryption during connection (AES-256, AES-192, AES-128).
- No wallet is required but connection details such as
tnsnames.oramust be known.
By default, database deployments on Oracle Exadata Database Service on Dedicated Infrastructure is configured to enable native Oracle Net Services encryption and integrity. Additionally, Oracle Net Services clients are configured to enable native encryption and integrity when connecting to an appropriately configured server. If your Oracle Net Services client is explicitly configured to reject the use of native encryption and integrity, connection attempts will fail.
sqlnet.ora parameters are set by default in Oracle Exadata Database Service on Dedicated Infrastructure.
- ENCRYPTION_TYPES_SERVER = (AES256, AES192, AES128)
- ENCRYPTION_SERVER = requested
- CRYPTO_CHECKSUM_SERVER = accepted
- CRYPTO_CHECKSUM_TYPES_SERVER = (SHA256, SHA384, SHA512)
/var/opt/oracle/dbaas_acfs/grid/tcps_wallets. The following sqlnet.ora parameters are set by default in Oracle Exadata Database Service on Dedicated Infrastructure.
- SSL_CIPHER_SUITES = (SSL_ECDHE_ECDSA_WITH_AES_128_GCM_SHA256,
- SSL_ECDHE_ECDSA_WITH_AES_256_GCM_SHA384,
- SSL_ECDHE_RSA_WITH_AES_128_GCM_SHA256,
- SSL_ECDHE_RSA_WITH_AES_256_GCM_SHA384)
Encryption at Rest for Oracle AI Database@Azure
Oracle AI Database@Azure supports encryption at rest to safeguard sensitive data residing in database files, backups, and configuration files. This protection is enabled by transparent data encryption (TDE), which ensures that data is encrypted whenever it is written to persistent storage and transparently decrypted when accessed by authorized Oracle processes with no customer configuration is required. The master key encrypts tablespace keys, which in turn encrypt the data.
Transparent Data Encryption (TDE)
Encryption at rest is provided through TDE, a feature included in Oracle Advanced Security. TDE automatically encrypts tablespaces, redo logs, and undo logs, ensuring that all database data is written to disk in encrypted form and transparently decrypted for authorized users and applications. Database backups created using Oracle Recovery Manager (RMAN) or managed backup solutions adopt these encryption settings, protecting all database copies stored on persistent media.
Key Management
- Oracle-managed keys: The master encryption key is automatically generated and stored in an Oracle Wallet, which is secured within the database environment. Oracle handles all key lifecycle tasks, including backups and restores.
- Customer-managed keys: You can integrate with services like OCI Vault to generate and store the master encryption key outside the database, enabling centralized key control, lifecycle management, rotation, and auditing of key usage events. With customer-managed keys, you control the encryption keys used to protect your data. You can enable customer-managed keys when creating databases, switch from Oracle-managed to customer-managed keys, and rotate keys to meet security and compliance requirements.
- Oracle-managed Key (OMK)
- Oracle Wallet
- Customer-managed Key (CMK)
- OCI Vault
- Oracle Key Vault (OKV)
- Azure Key Vault (AKV)
Oracle-Managed Keys (OMK) are the default method for securing data encryption in Oracle AI Database@Azure. In Oracle AI Database, data encryption at rest is enabled by transparent data encryption (TDE). When you choose OMKs, the database system automatically manages all key operations, including key generation, secure storage, and rotation required by TDE. There are no prerequisites or additional configuration steps required to use Oracle-Managed Keys in Oracle AI Database@Azure.
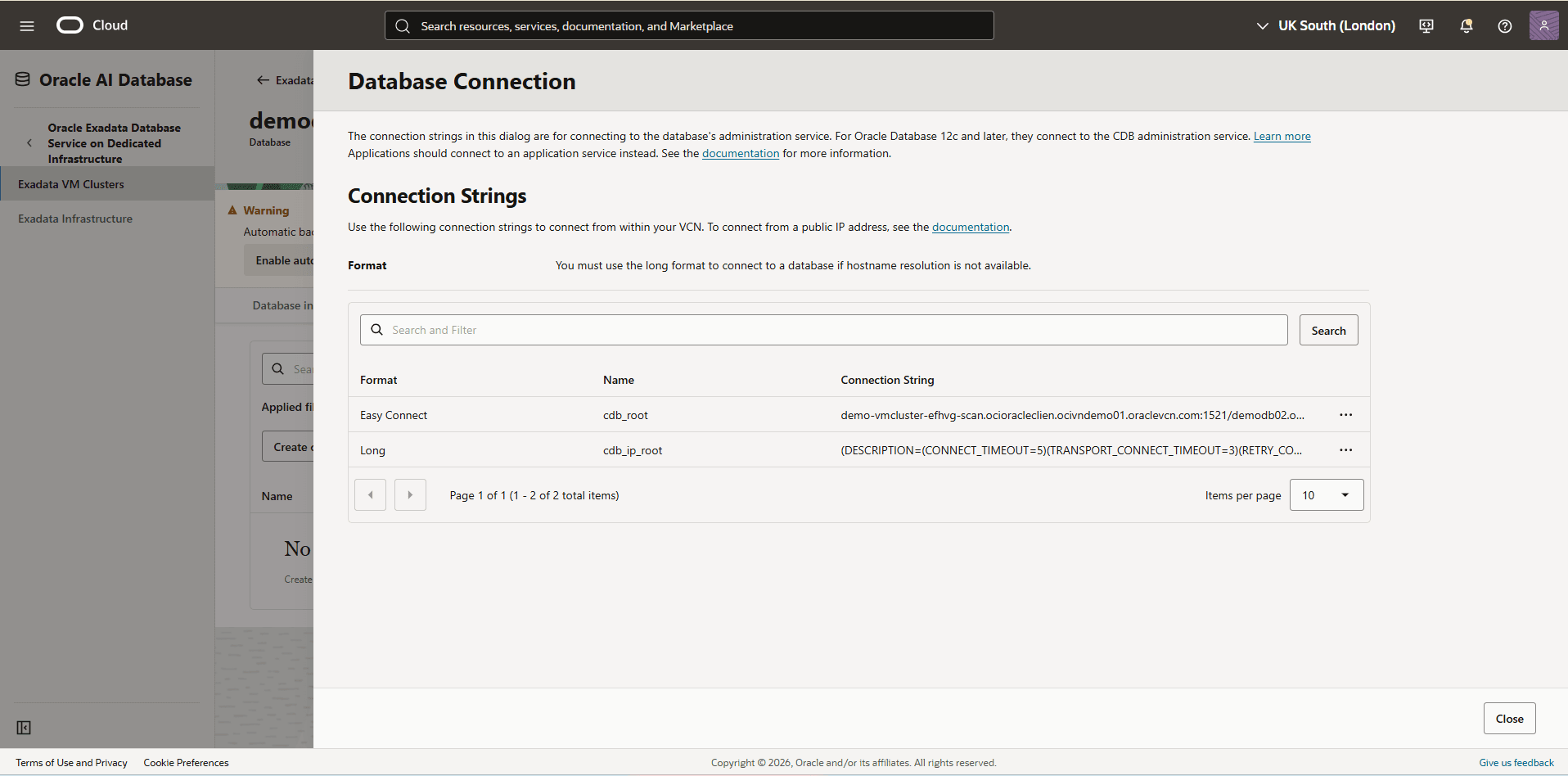
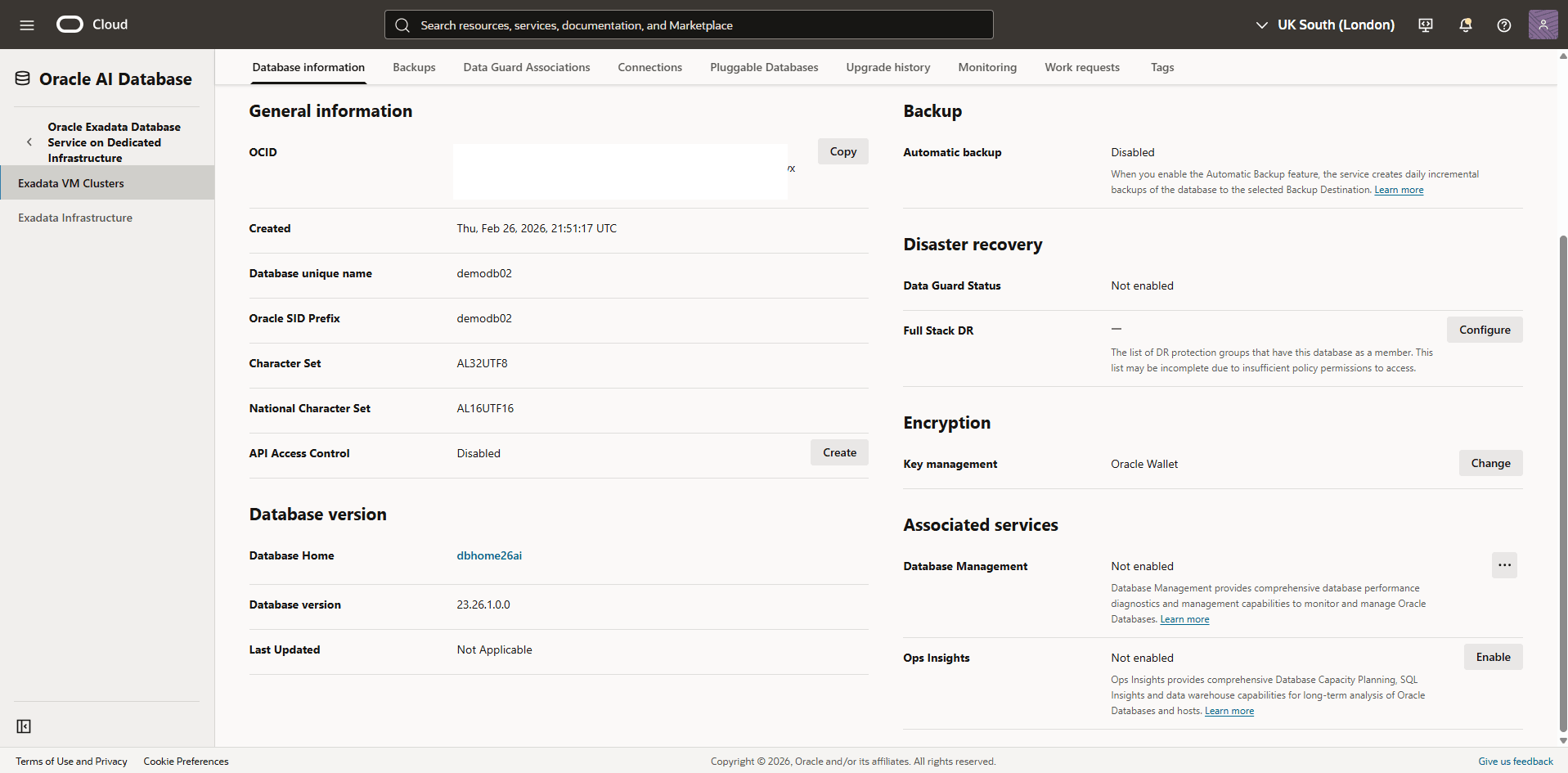
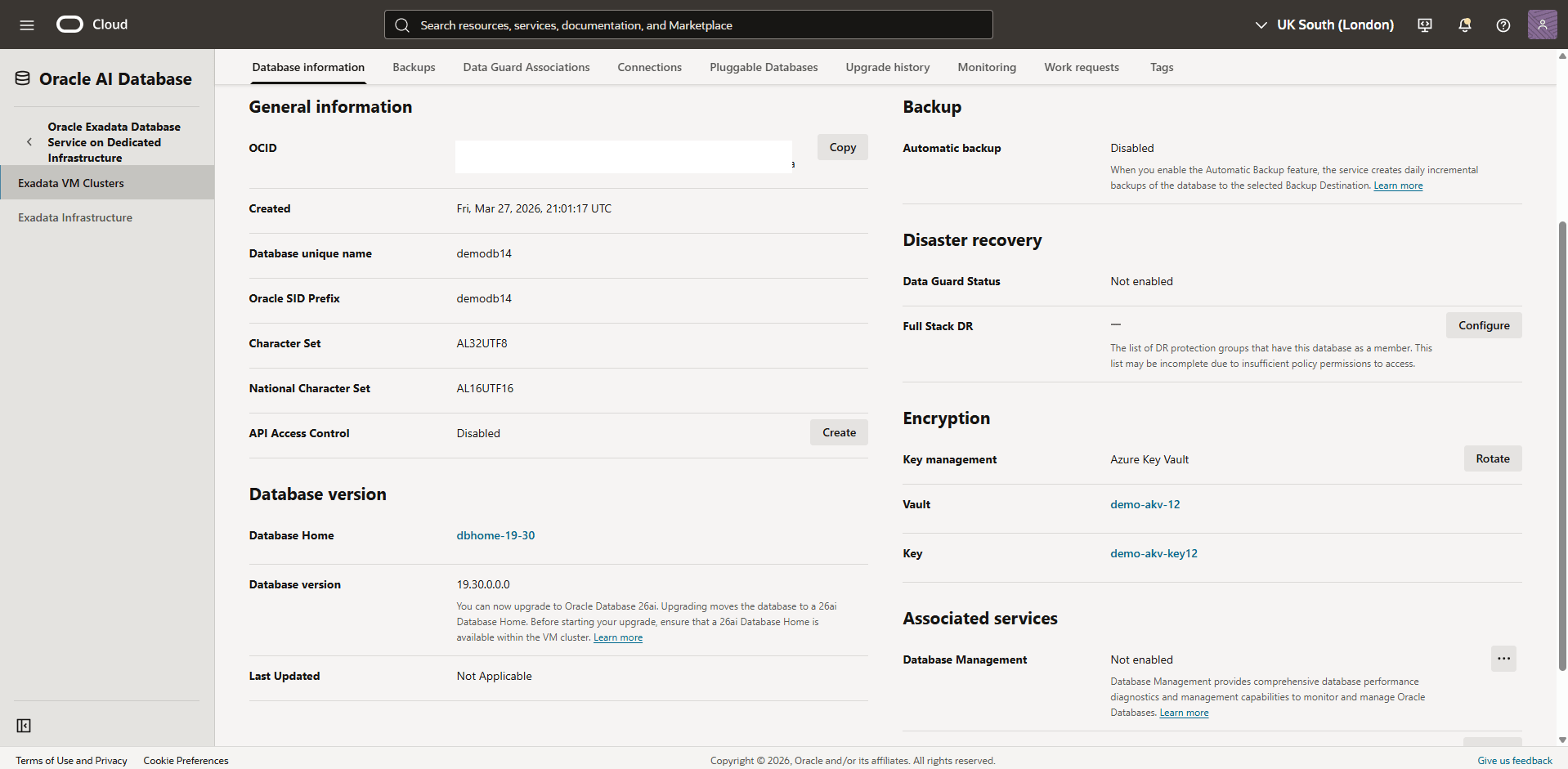
View Encryption Details
- Navigate to the Oracle AI Database@Azure portal.
- From the left menu, select Oracle Exadata Database Service on Dedicated Infrastructure, and then select Oracle Exadata VM Clusters tab.
- .From the list, select the Name of your Exadata VM Cluster to open the Overview page.
- From the Essentials section, select the Go to OCI link which redirects you to the OCI console
- From the OCI console, select the Databases tab and then select the name of the database you want to check the key management.
- Select the Database information tab, and then navigate to the Encryption section to view the Encryption key details. By default, it is set to Oracle Wallet.
There is currently no content for this page. The Oracle AI Database@Azure team intends to add content here, and this placeholder text is provided until that text is added.
The Oracle AI Database@Azure team is excited about future new features, enhancements, and fixes to this product and this accompanying documentation. We strongly recommend you watch this page for those updates.
There is currently no content for this page. The Oracle AI Database@Azure team intends to add content here, and this placeholder text is provided until that text is added.
The Oracle AI Database@Azure team is excited about future new features, enhancements, and fixes to this product and this accompanying documentation. We strongly recommend you watch this page for those updates.
Oracle Exadata Database Service on Dedicated Infrastructure supports integration with Azure Key Vault (AKV). This capability allows you to manage transparent data encryption (TDE) master encryption keys (MEKs) using Azure customer-managed keys.
To configure Azure Key Vault to encrypt your database, complete the following steps.
- Enable Advanced Network Features
You must first complete the registration required for delegated subnets to use the advanced network features mentioned in Network planning for Oracle AI Database@Azure, and then create an Azure Virtual Network with one delegated subnet to be used by the Exadata VM Cluster.
Note
Enable advanced networking to support the Azure Private Link connectivity required for Managed HSM and Azure Arc. - Create an Azure Key Vault
For step-by-step instructions, see the CMK - AKV tab in the Prerequisites section.
- Create a Key on Azure Key Vault
For step-by-step instructions, see the CMK - AKV tab in the Prerequisites section.
- Create an Exadata VM Cluster
For step-by-step instructions, see Exadata VM Cluster.
- Disable Azure Key Vault Public Access
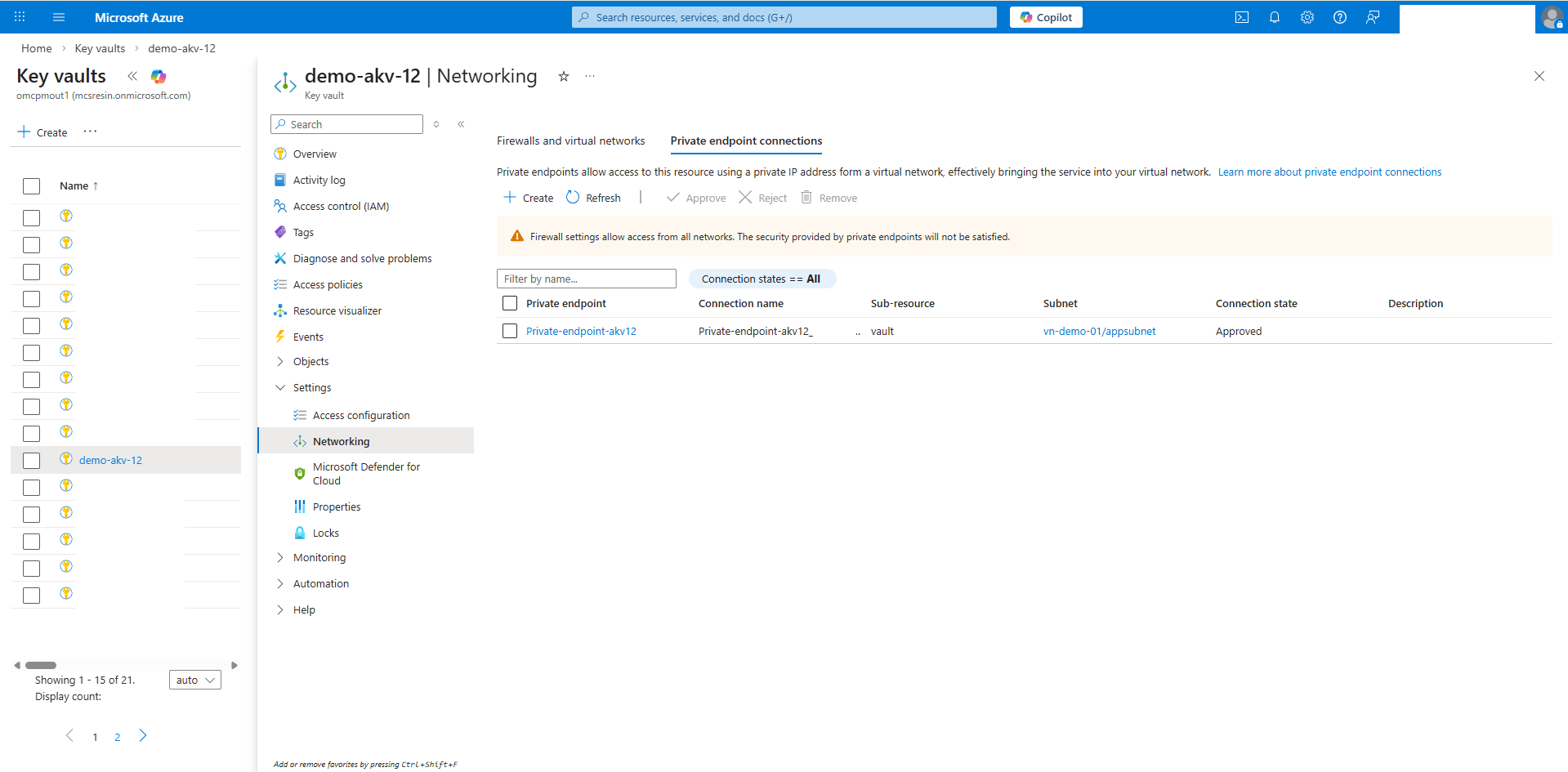
- From the Azure portal, select Key vaults.
- Select the Name field of the Key vault that you want to use.
- Expand the Settings section, and then select Networking.
- From the Firewalls and virtual networks tab, choose the Disable public access option.
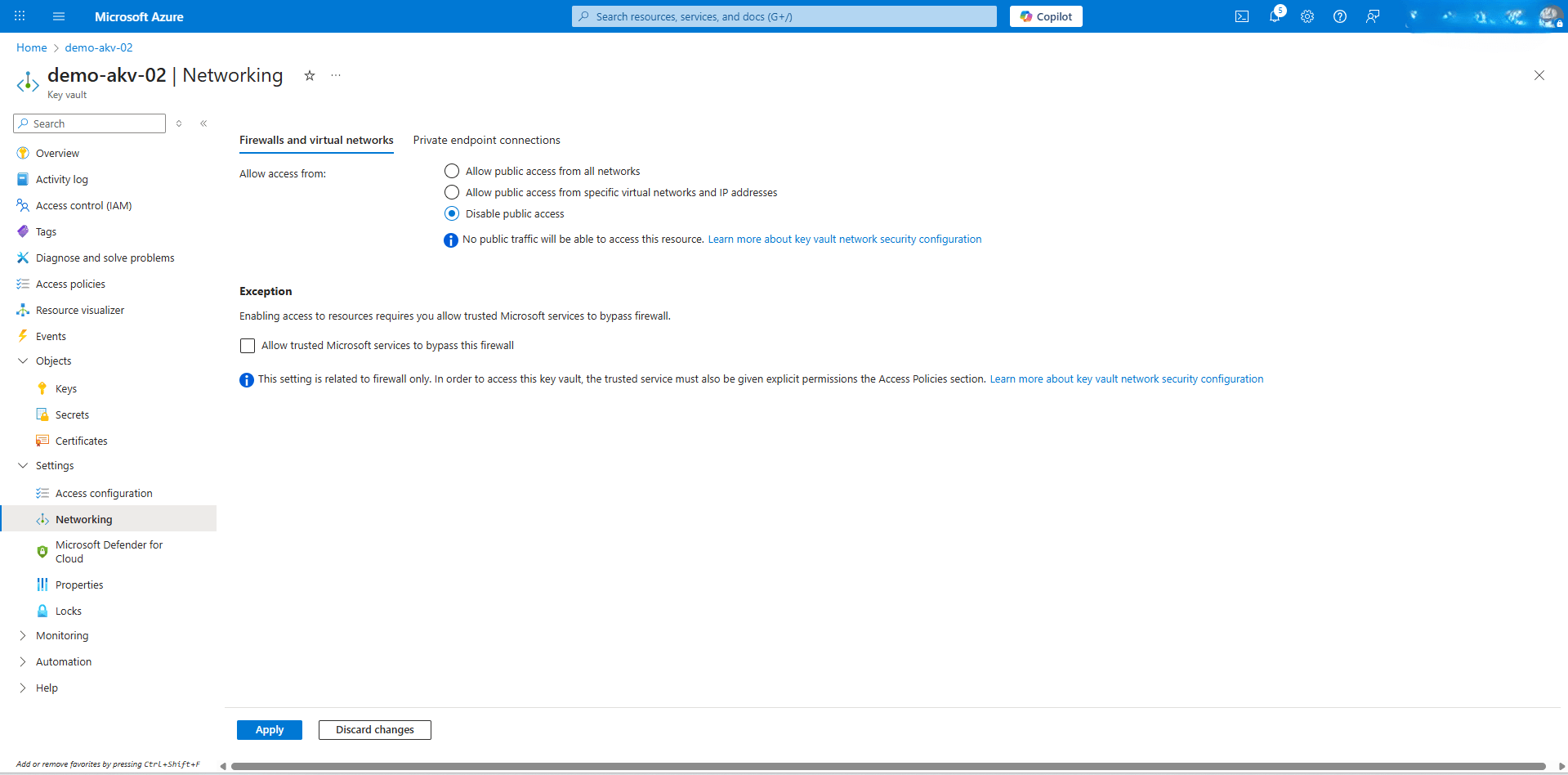 Note
Note
After the public access is disabled, Azure Key Vault is accessible only through a Private Endpoint. - Select the Apply button to save the changes.
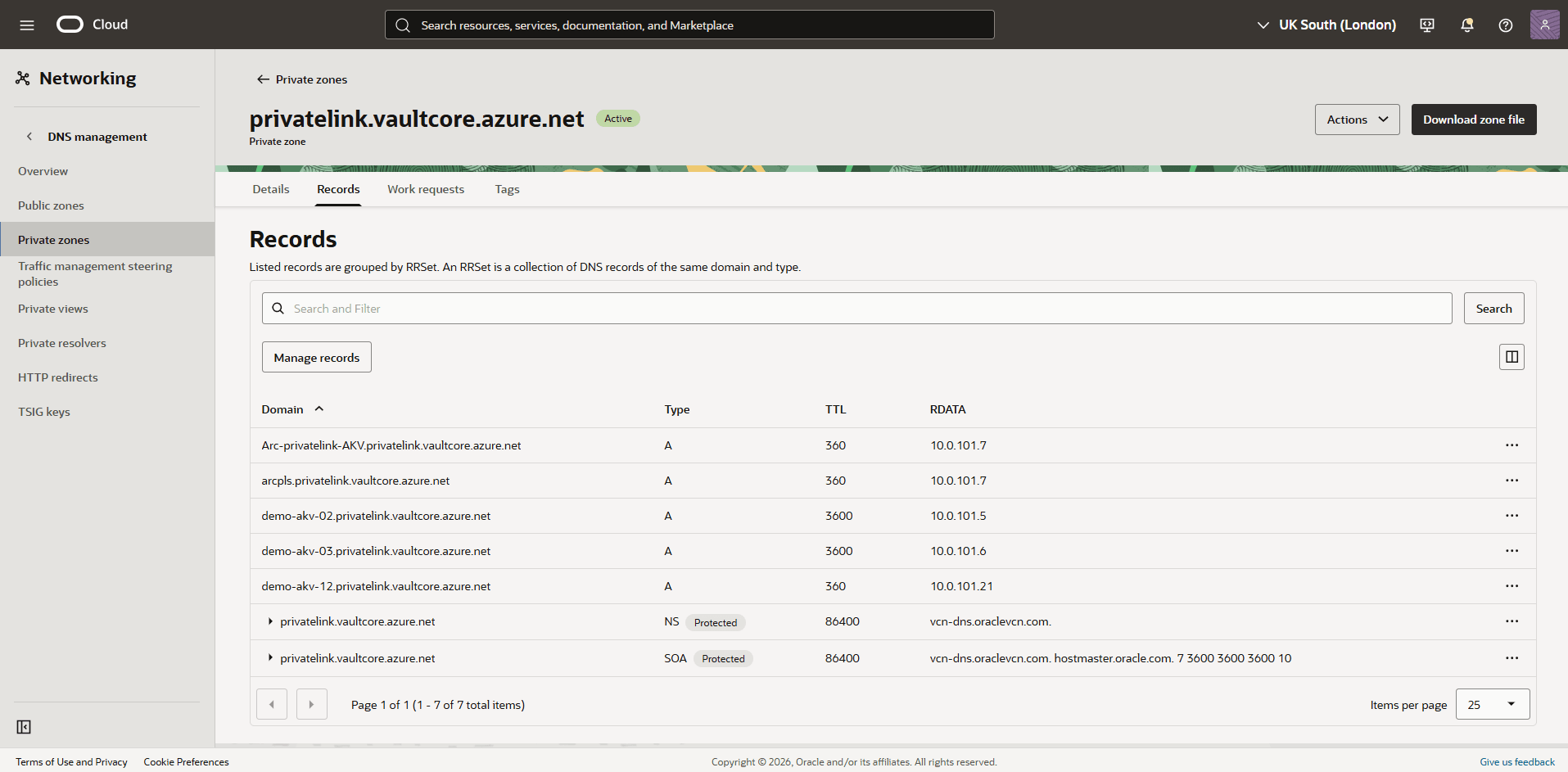
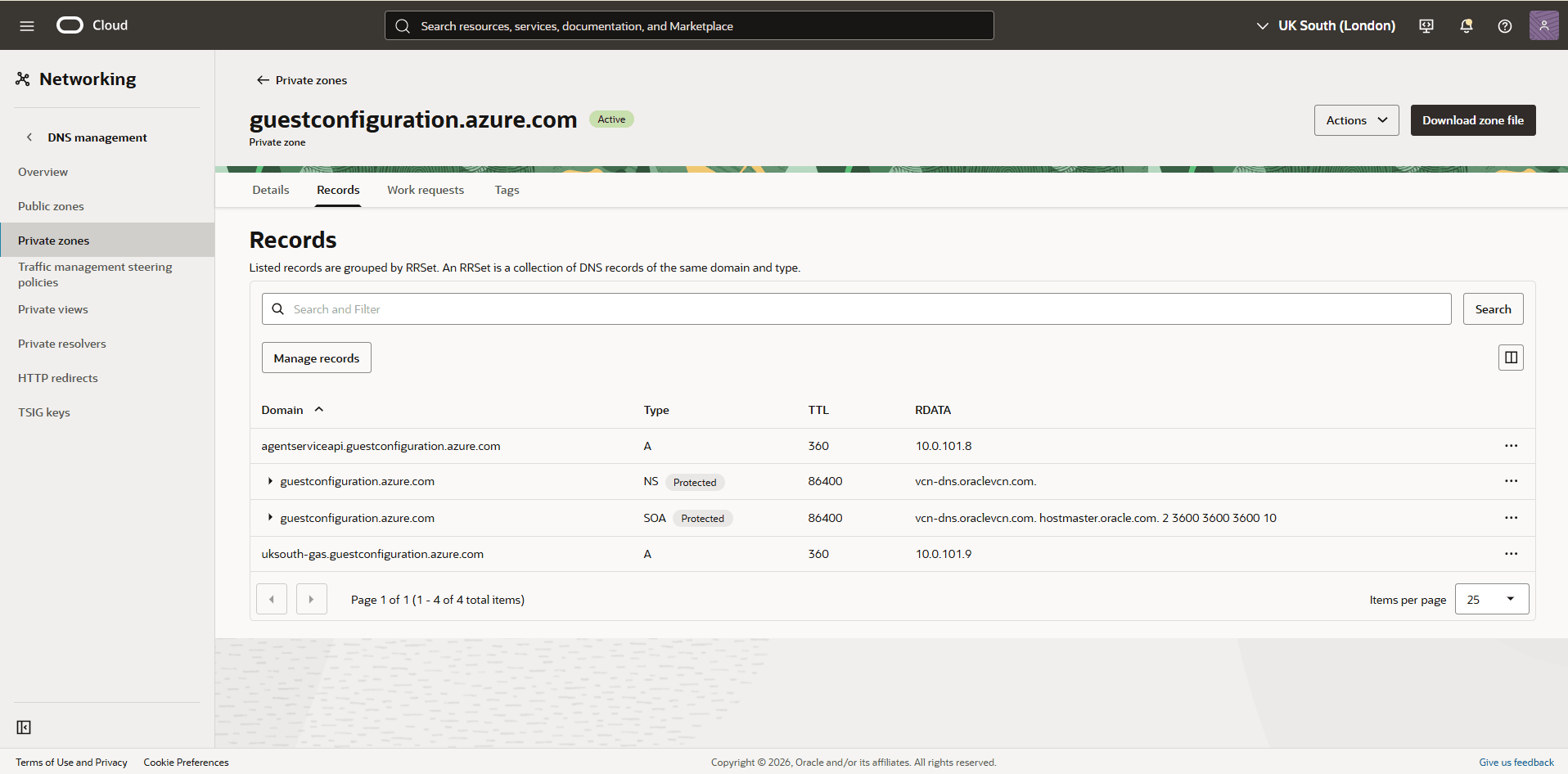
- Obtain Azure Key Vault DNS Zones InformationNote
During Azure Key Vault creation, when the private endpoint (privatelink.vaultcore.azure.net) is set up, a private DNS zone is created by the workflow. Two Private DNS Zones need to be added in OCI to allow the Exadata Database to resolve private endpoint URLs to the correct private IP addresses.- From the Azure portal, select Key vaults.
- Select the Name field of the Key vault that you want to use.
- Expand the Settings section, and then select Networking.
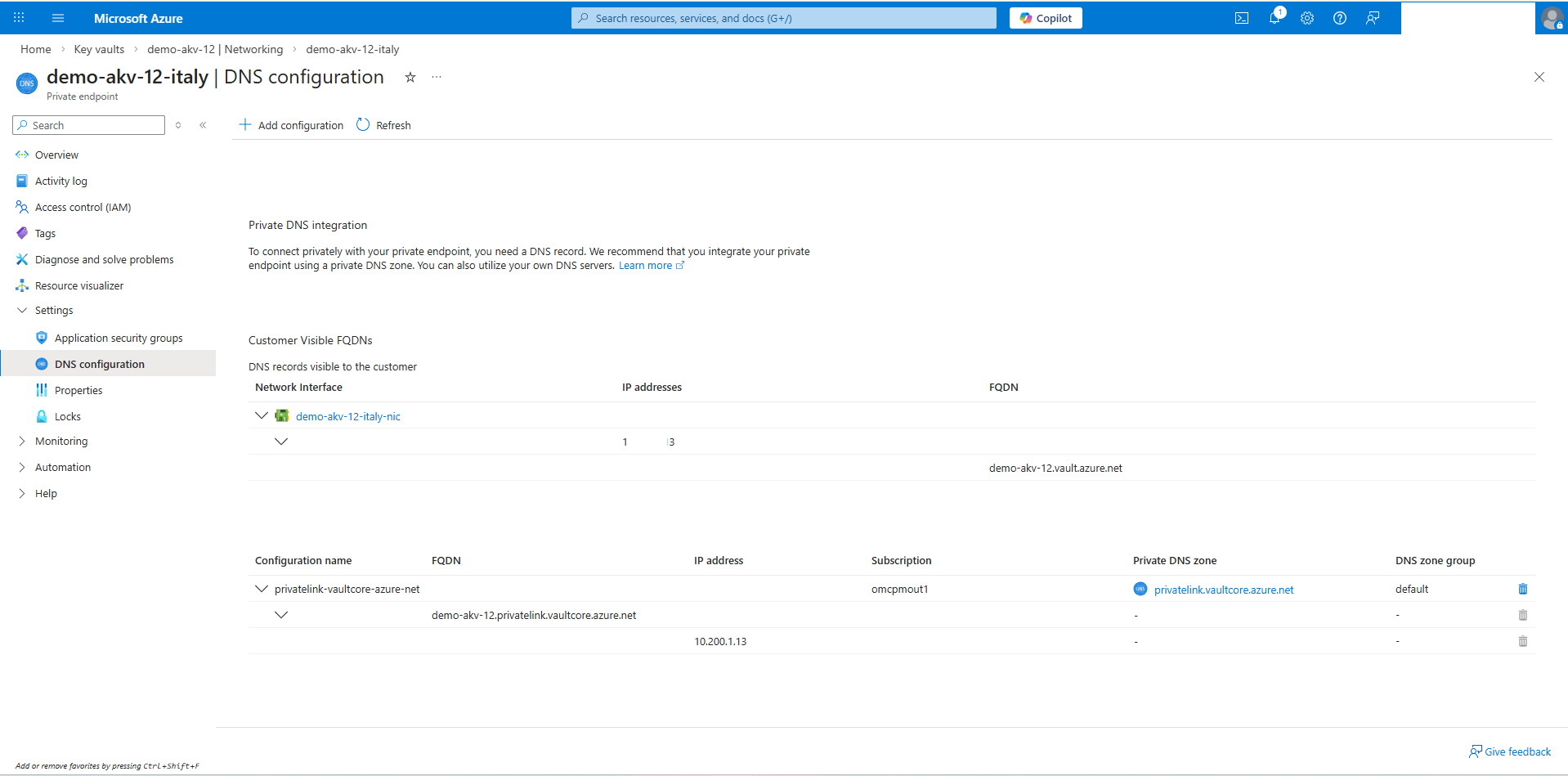
- From the Private endpoint connections tab, select the Private endpoint name.
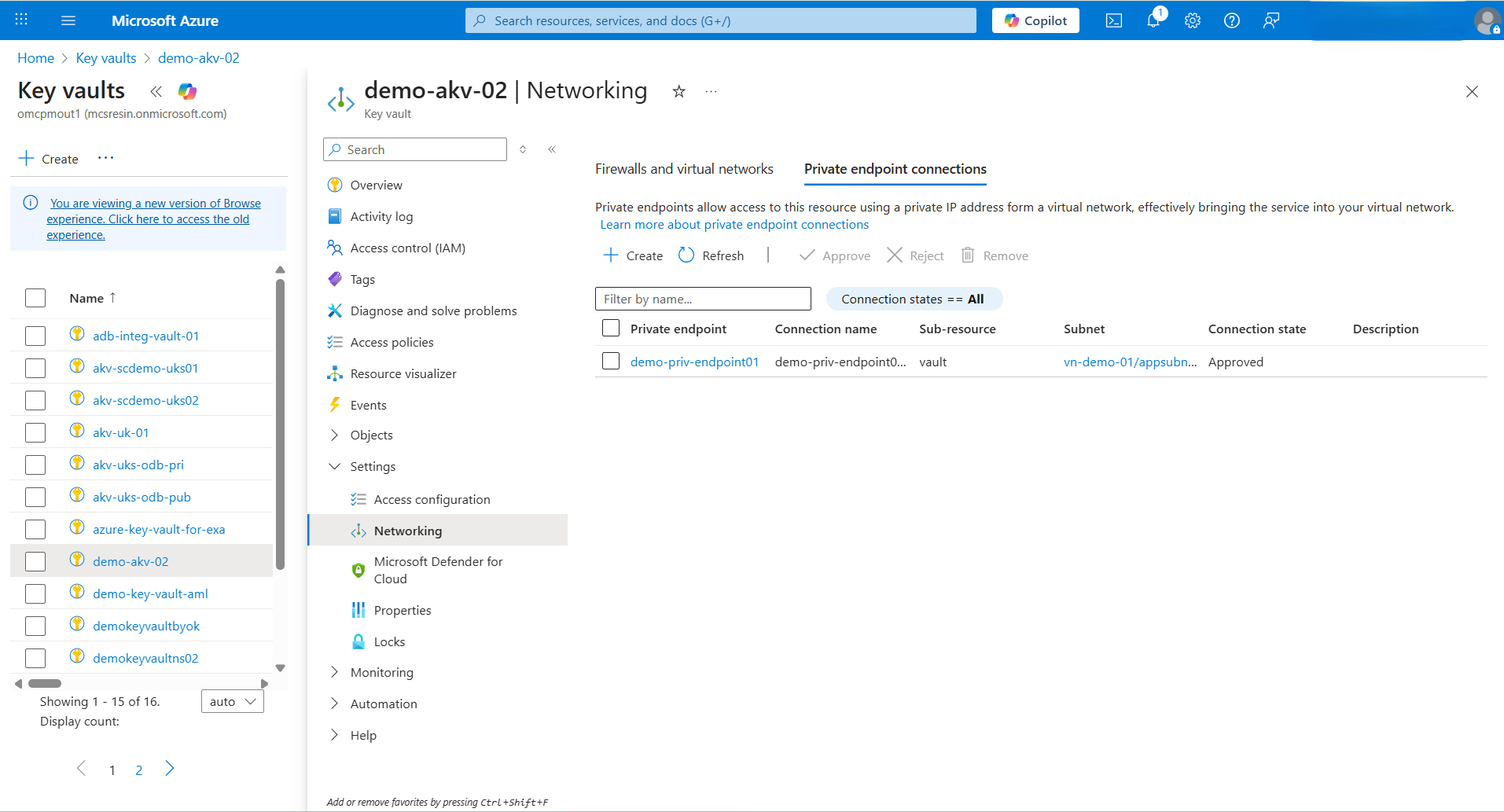
- From the left menu, expand the Settings section, and then select DNS configuration. Note the FQDN and IP addresses information.
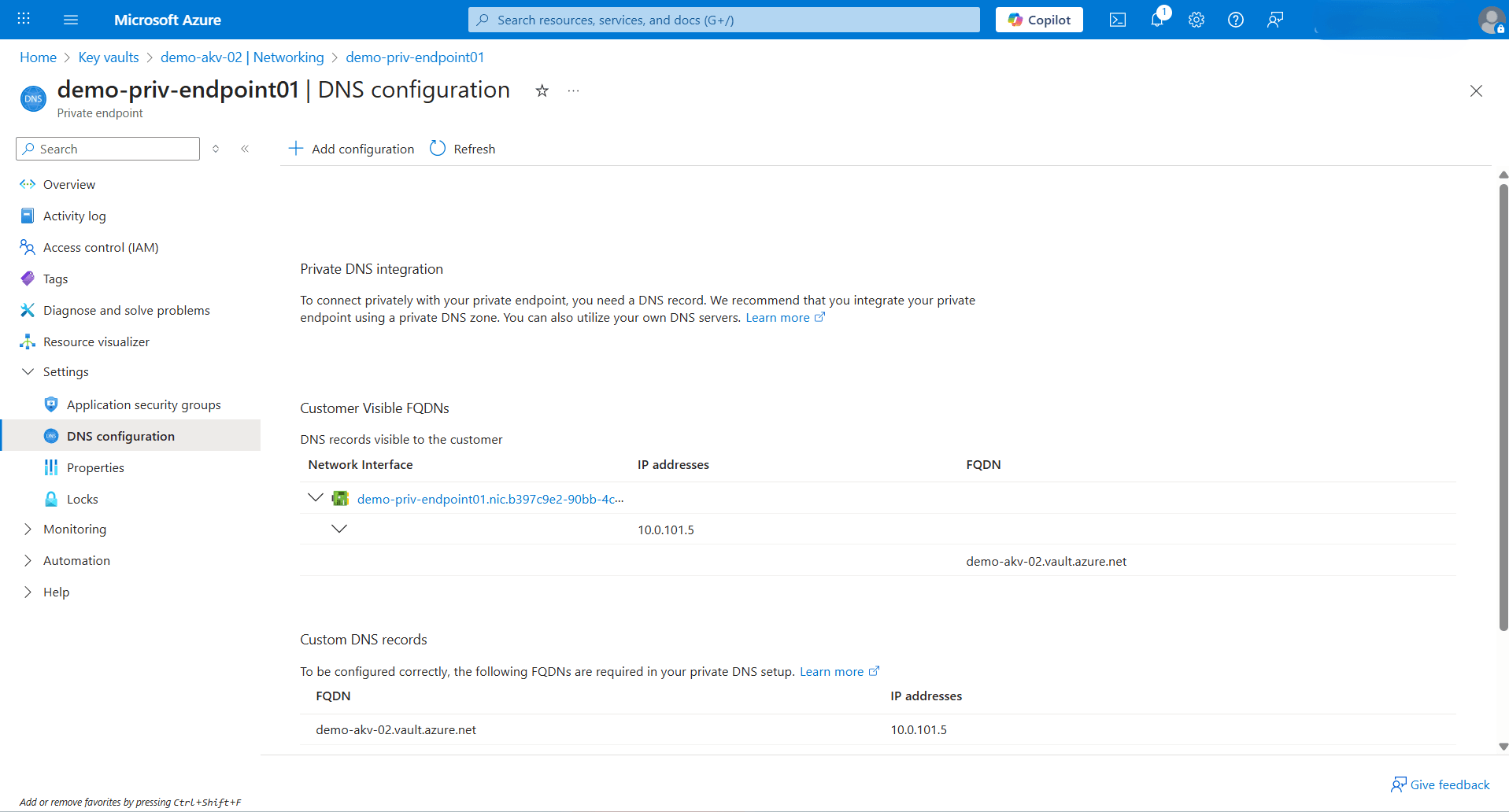
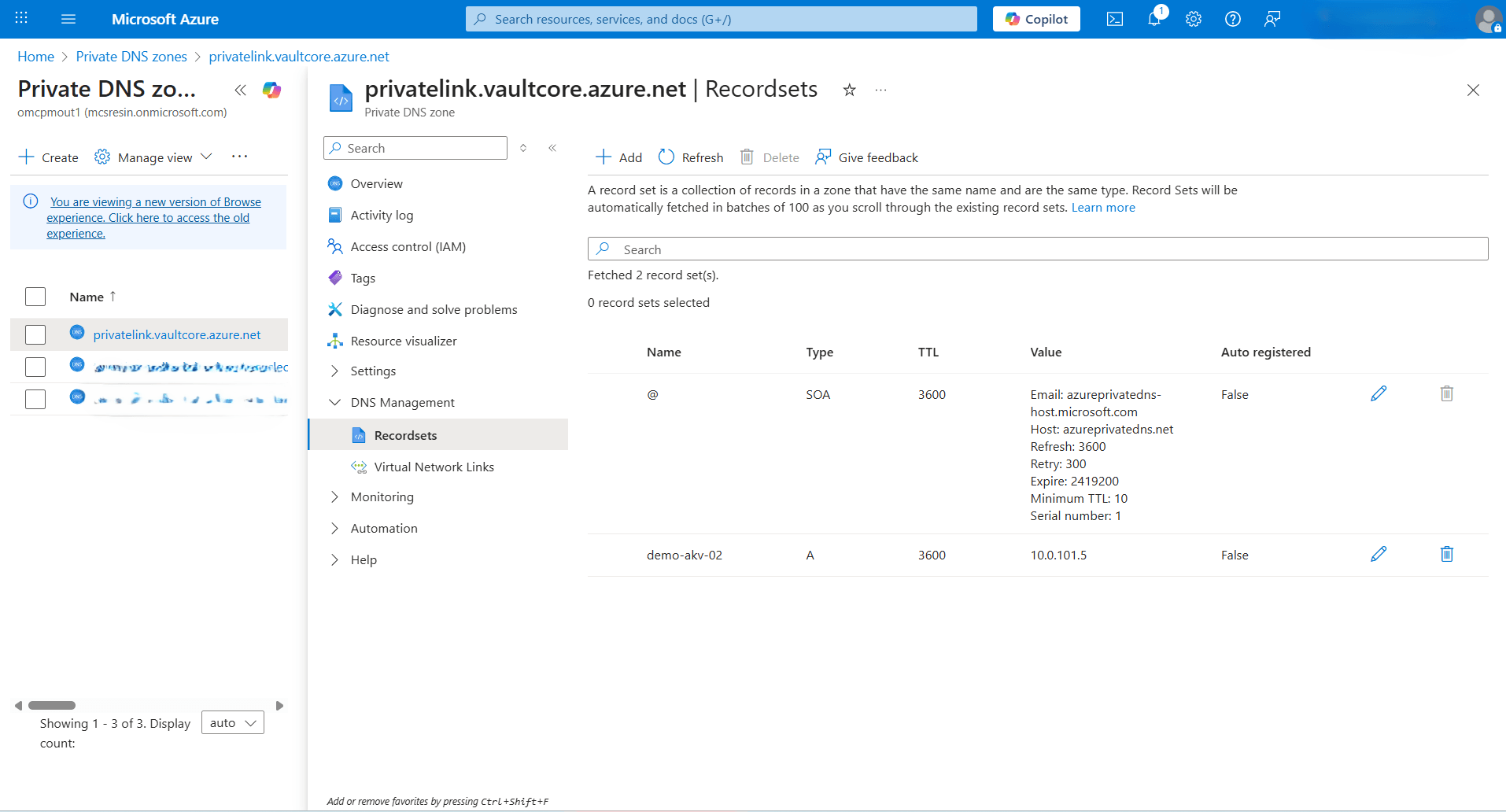
- Navigate to Azure portal, and then select Private DNS zones.
- From the list, select the
privatelink.vaultcore.azure.netDNS zone. Expand the DNS Management section, and then select Recordsets. - Note the A record created for Azure Key Vault.
- Add Private AKV DNS Zones in OCI
- From the OCI console, select Oracle AI Database, and then select Oracle Exadata Database Service on Dedicated Infrastructure .
- From the left menu, select Exadata VM Clusters and then select your Exadata VM Cluster.
- Select the Databases tab and then select the database that you are using.
- Navigate to Network section, and then select Virtual Cloud Network.
- From the Details tab, select DNS Resolver link.
- From the Private resolvers page, select the Default private view link..
- In the Private view page, select the Private zones tab.
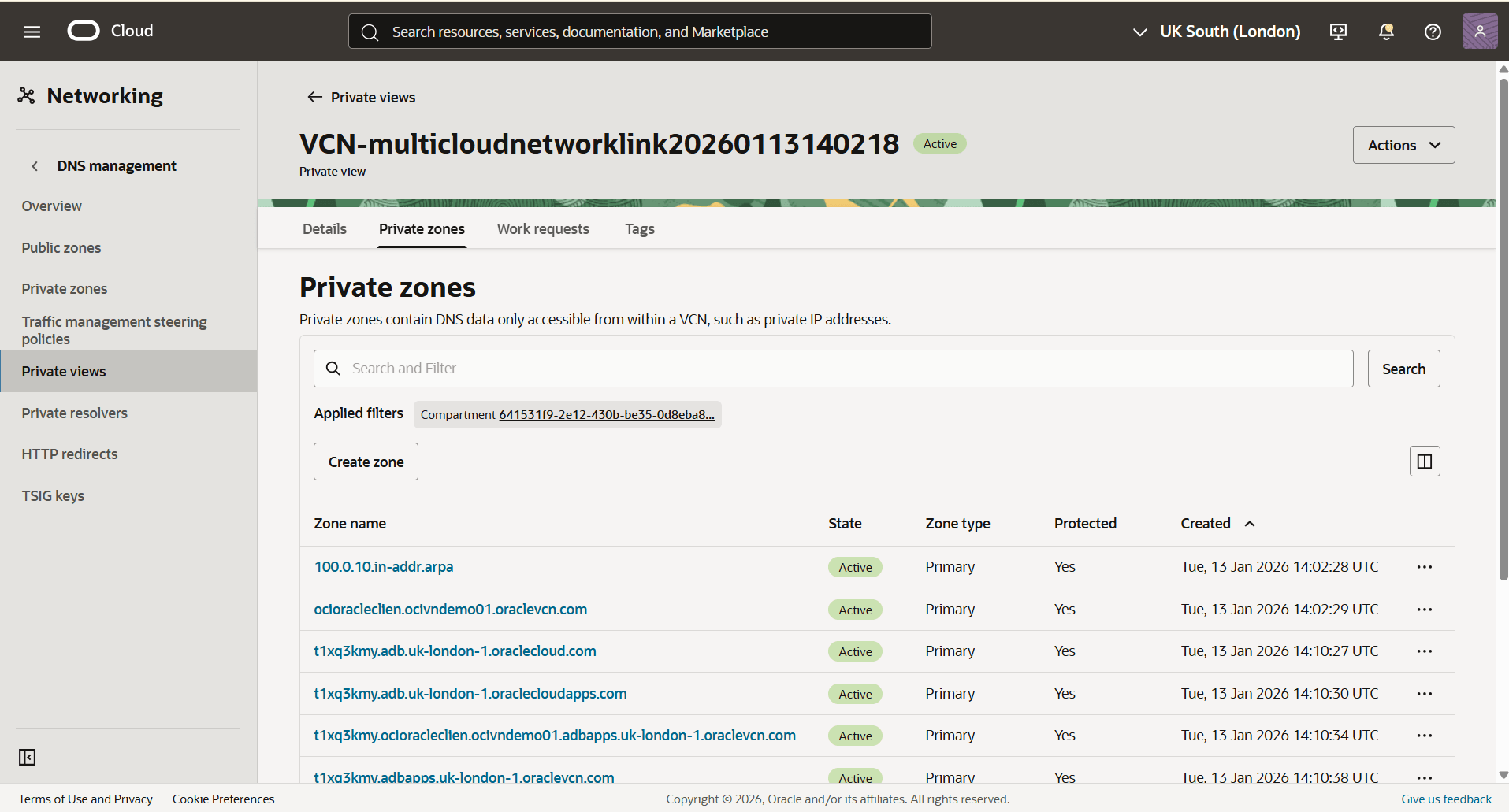 Note
Note
If the DNS Zone already exists in your environment, add the record to your existing Private Zone. - In the Private Zones section, select the Create zone button to create the first private zone.
- The Zone type field is set to Primary by default.
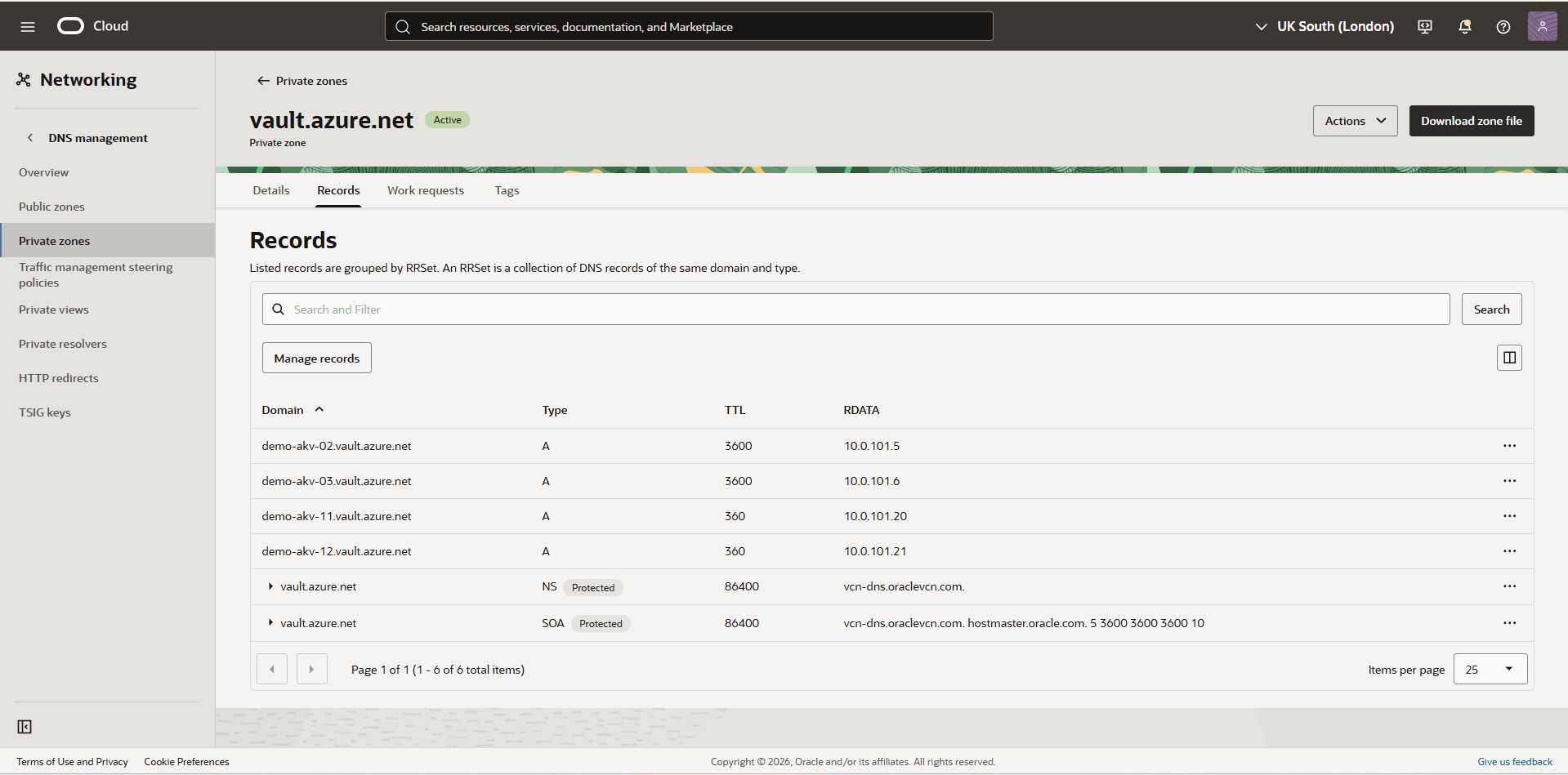
- Enter a descriptive Zone name. Select the zone name that matches the domain FQDN copied in the previous step. For example,
vault.azure.net. - From the dropdown list, select the Compartment in which you want to create a private zone.
- The Tags section is optional.
- Select the Create.
- Select the Zone name field of the zone that you previously created, and then select the Records tab.
- Select the Manage records button.
- From the Manage records page, select the Add record button.
- For the Name field, enter the FQDN name that you previously noted.
- Select the A- IPv4 address option as your Type.
- Adjust the TTL in seconds based on your requirements.
- Select your RDATA mode.
- In the Address field, enter the IP address that you previously noted , then select the Save changes button.
- Select the Review changes button, then select the Publish Changes button.
- To create a second zone, select the Create zone button.
- The Zone type field is set to Primary by default.
- In the Zone name field, enter a zone name based on your Private DNS Zone domain. For example,
privatelink.vaultcore.azure.net. - From the dropdown list, select the Compartment in which you want to create a private zone.
- The Tags section is optional.
- Select the Create button.
- Select the Zone name field of the zone that you previously created, and then select the Records tab.
- Select the Manage records button.
- From the Manage records page, select the Add record button.
- For the Name field, enter your Azure Private zone record set name.
- Select the A- IPv4 address option as your Type.
- Adjust the TTL in seconds based on your requirements.
- Select your RDATA mode.
- In the Address field, enter the IP address that you previously noted, then select the Save changes button.
- Select the Review changes button, then select the Publish Changes button.
- Create the Network Requirements for Creating an Identity ConnectorAzure Key Management Service (KMS) resources support both public and private connectivity. Azure Key Vault Managed HSM requires private connectivity, whereas Azure Key Vault Premium and Standard tiers support both public and private connectivity options.
- Configuration Using Private Network
To create an Identity Connector over a private network, you must configure an Azure Arc Private Link Scope and a Private Endpoint through the Azure Portal.
- Create Azure Arc Private Link Scopes
- From the Azure portal, navigate to Azure Arc.
- Expand the Additional setup section, and then select Private link scopes.
- Select the + Create button to start the creation process.
- From the Basics tab of the Create an Azure Arc Private Link Scope flow, enter the following information.
- Select the Subscription that you want to use, and then select the Resource group.
- Enter a descriptive Name for the private link scope. The private link scope name can contain only alphanumeric characters and the following symbols: hyphen (-), period (.) , and underscore (_). The name can not begin with underscore (_) or end with period (.) or hyphen (-).
- Select the Region.
- Select the Next: Private endpoint > button to proceed.
- From the Private endpoint tab of the Create an Azure Arc Private Link Scope flow, enter the following information.
- Select the + Create button to create a private endpoint.
- The Subscription field populates automatically.
- Select the Resource group.
- For the Location field, select the region corresponding to your Exadata VM Cluster deployment.
- Enter a descriptive Name for your private endpoint. The name must begin with a letter or number, end with a letter, number or underscore, and may contain only letters, numbers, underscores, periods, or hyphens.
- From the Networking section, select your Virtual network and Subnet.
- Choose the Yes option to integrate with private DNS zone. This automatically creates a new private DNS zone.
- Select the OK button.
- Select the Next: Tags > button to proceed.
- The Tags section is optional. To manage and create custom views of your resources, assign tags. Select the Next: Review + create > button.
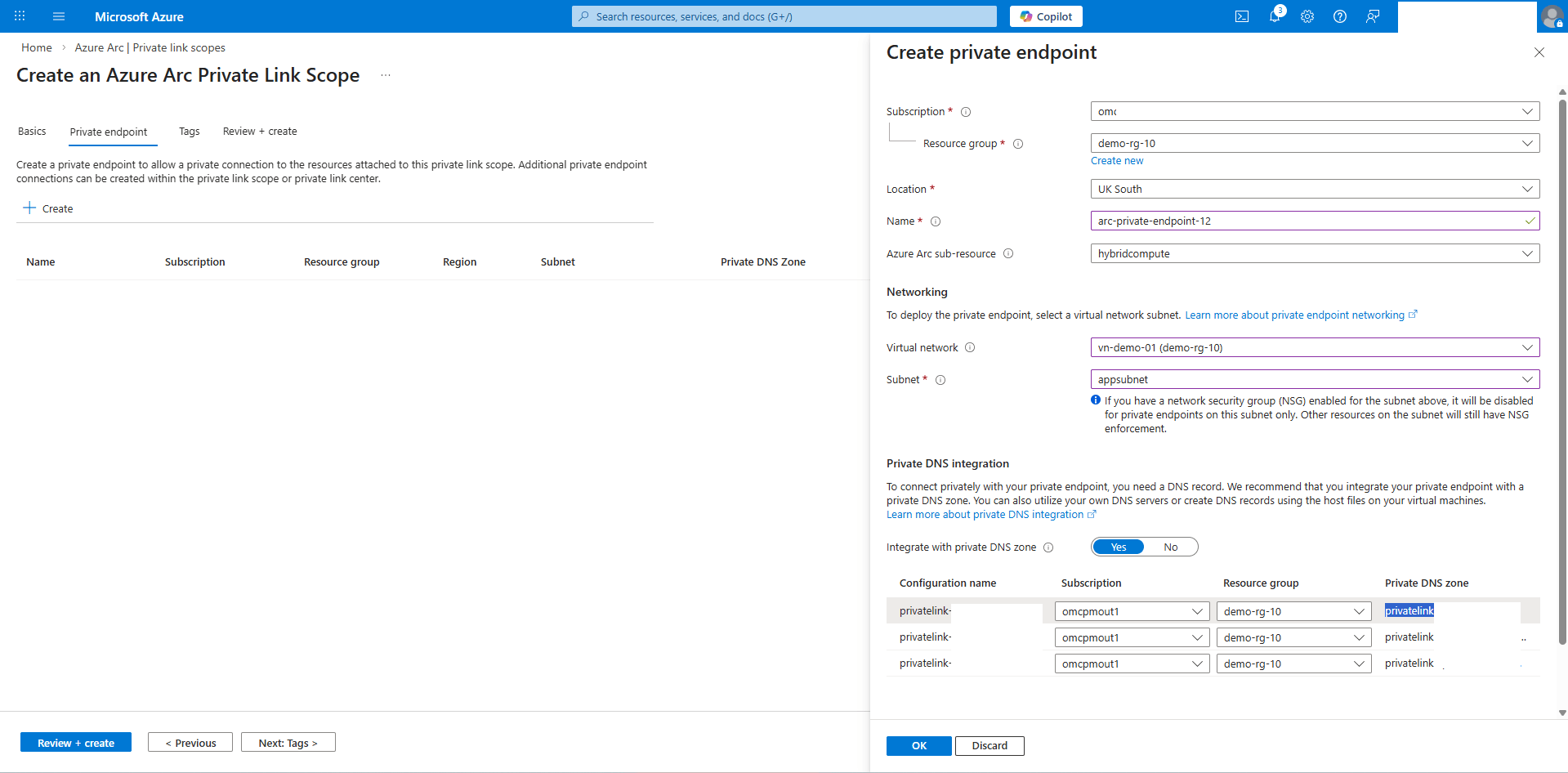
- Once you review your information, select the Create button.
- Obtain Azure Arc Private Link DNS Zones Information
- From the Azure portal, navigate to Private endpoints.
- Expand the Private link section, and then select Private endpoints.
- Select your private endpoint from the list and then expand the Settings section.
- Select the DNS configuration.
- Take a note of the FQDN and IP addresses information.
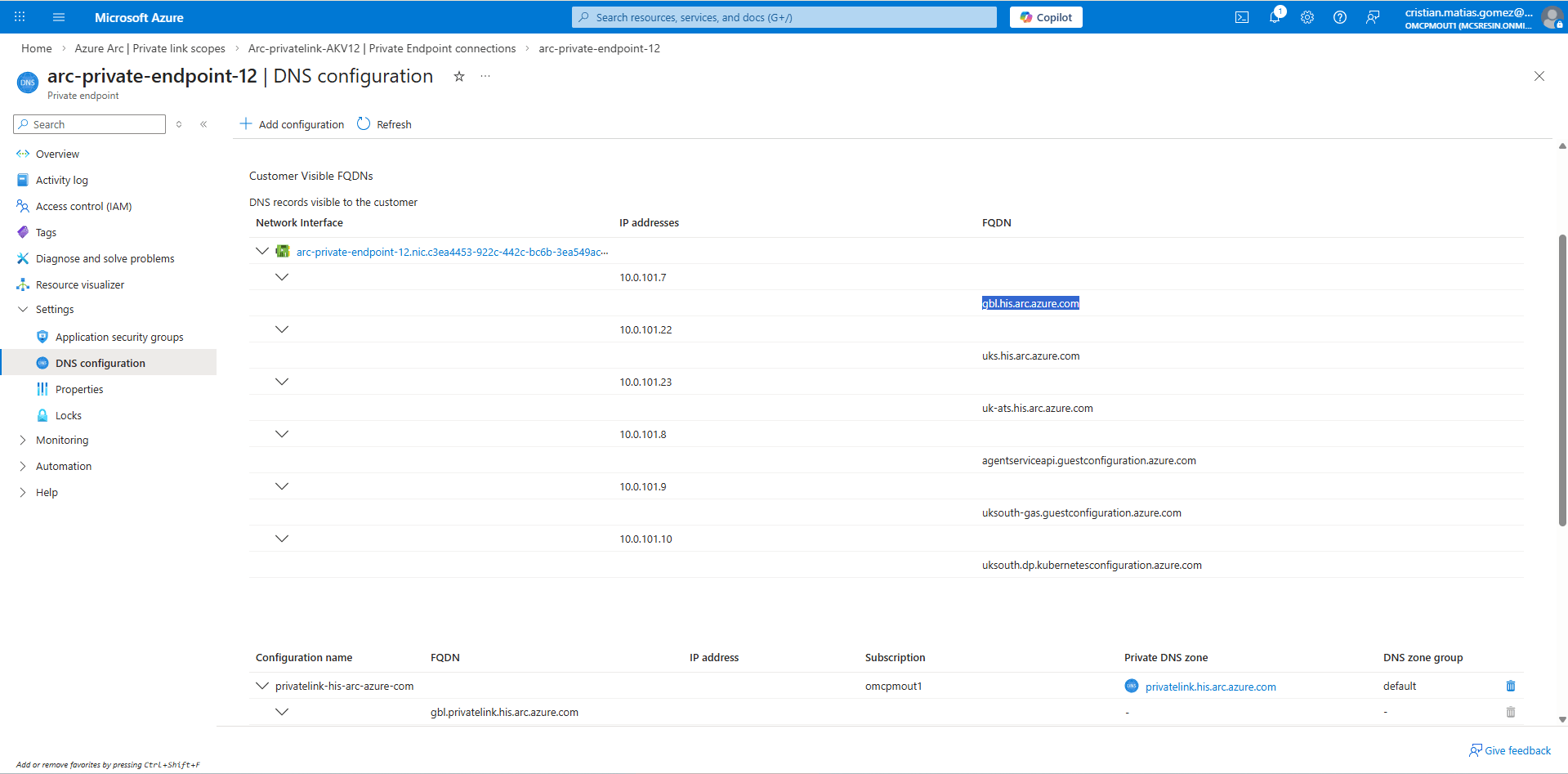
Note
The DNS configuration for the Private Endpoint associated with the Private Link Scope must include the necessary private agent resource addresses. For more information, see URLs. - Create OCI Private Zone
- From the OCI console, select Oracle AI Database and then select Oracle Exadata Database Service on Dedicated Infrastructure. Select the name of your Exadata VM Cluster.
- Scroll down to the Network section, then select the Virtual Cloud Network.
- In the VCN information section, under DNS Resolver, select DNS Resolver Name.
- From the Private Resolver section, select the Default Private view name.
- In the Private view page, select Private zones tab.
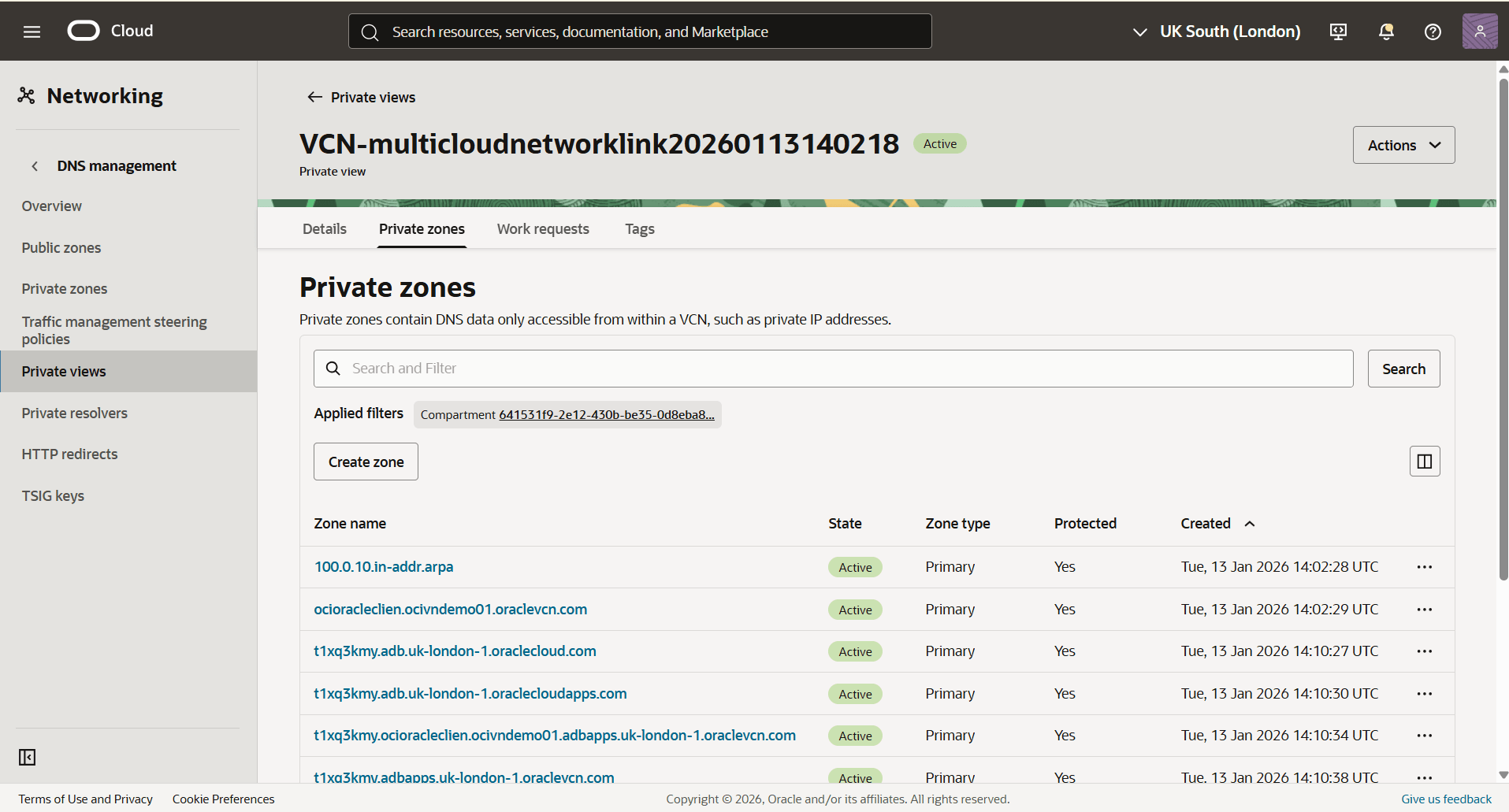
- From the Private zones page, select the Create zone button to create the first private zone.
- In the Zone name, select the name according with your domain FQDN which you copied in the previous step. For example,
arc.azure.com). - Select the Create button.
- Select the name field of the zone that you created in the previous step.
- Select the Records tab, and then select Manage records button.
- Select the Add record button.
- For the name field, paste your FQDN name. For example,
gbl. - Select A- IPv4 address as your type.
- In the Address field, enter the IP addresses that you copied in the previous step. Then, select the Save changes button.
- For the name field, paste your FQDN name. For example,
- Select the Review changes button, then select Publish Changes button.
- Repeat the previous step until you have added all records to the specified Private Zone.
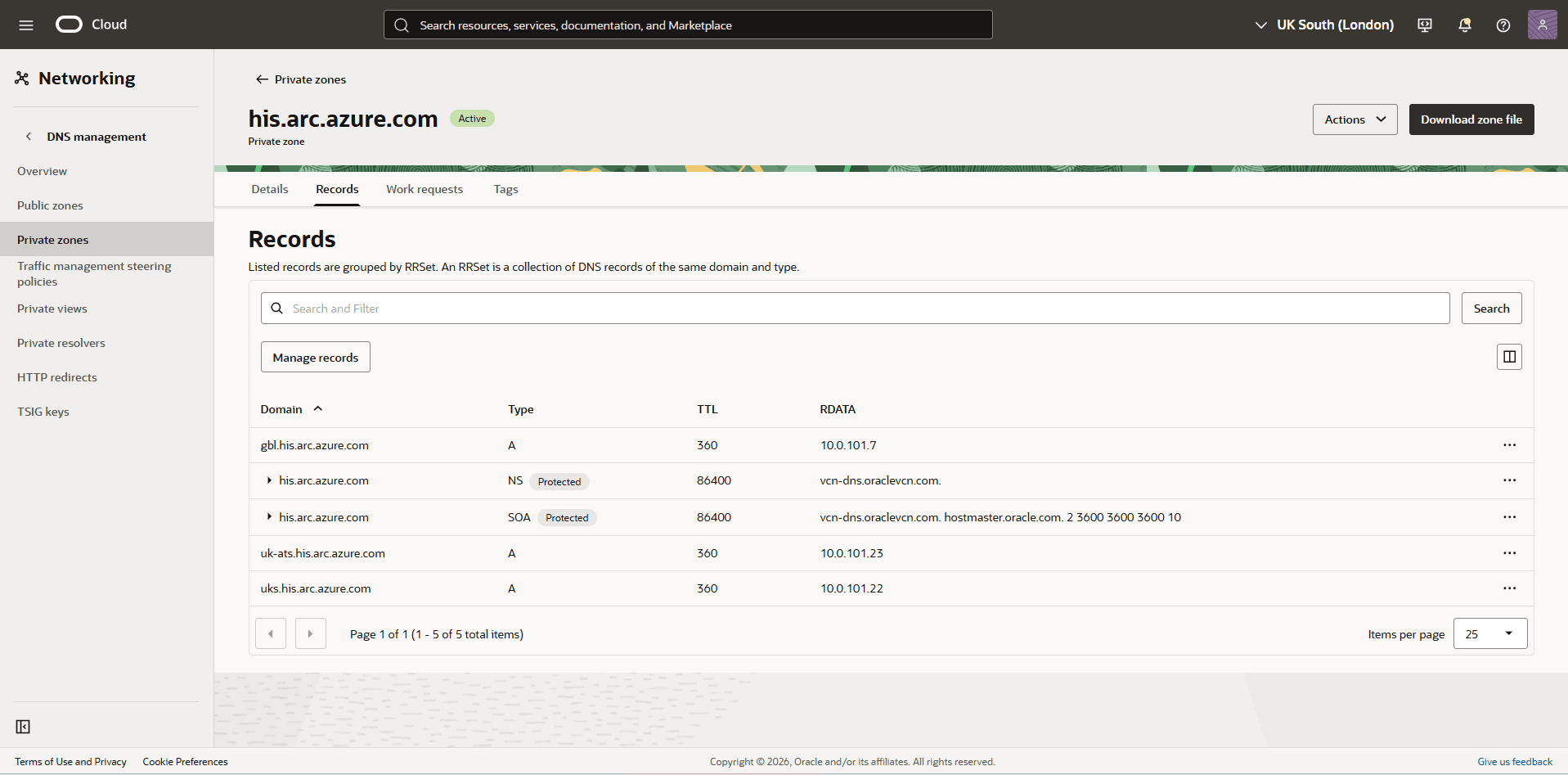
- In the Zone name, select the name according with your domain FQDN which you copied in the previous step. For example,
- Create all the Private zones, and add the records obtained from the Obtain Azure Arc Private Link DNS Zones Information step.
Note
Even with Private Connectivity, the following endpoints must be routed through the Azure NAT gateway.Agent resources:packages.microsoft.comlogin.microsoftonline.compas.windows.netmanagement.azure.com
You must ensure the connectivity to these endpoints. Otherwise, the Identity Connector creation will fail.
- Create a NAT Gateway in Azure Portal
- From the Azure Portal, select NAT Gateways.
- Choose the Subscription that you want to use, then select the Resource group.
- Enter a name for your NAT gateway, select the Region corresponding to your VNET, then select the Next button.
- In the Outbound IP tab, select the Add Public IP addresses or prefixes button.
- You can select an existing public IP address or prefix or both to associate with the NAT gateway and enable outbound connectivity.
- To create a new public IP for the NAT gateway, select the Create a public IP address button. Enter a Name, and then select the OK button.
- To create a new public IP prefix for the NAT gateway, select the Create a new public IP prefix button. Enter a Name, select a Prefix size, then select the OK button.
- Once you enter your information, select the Next button.
- You can select an existing public IP address or prefix or both to associate with the NAT gateway and enable outbound connectivity.
- In Networking tab, select your Virtual Network, then select the subnet that you want to associate the NAT gateway.
- Select the Review + Create button, and then select the Createbutton.
- Create an Identity Connector from the OCI Console
Creating an Identity Connector installs the Azure Arc agent on the Exadata VM Cluster VMs, registering them as Azure Arc-enabled virtual machines.
This enables secure communication with the Azure Key Management Service (KMS) using the Azure identity generated by the Arc agent. The Azure Arc agent can communicate with Azure services over either a public network or a private connectivity setup. For more information, see Azure Arc.
Each Exadata VM Cluster must have an identity connector enabled to access Azure resources. The identity connector establishes either a public or private connection between the Exadata VM Cluster and Azure Key Management resources, depending on the roles assigned.
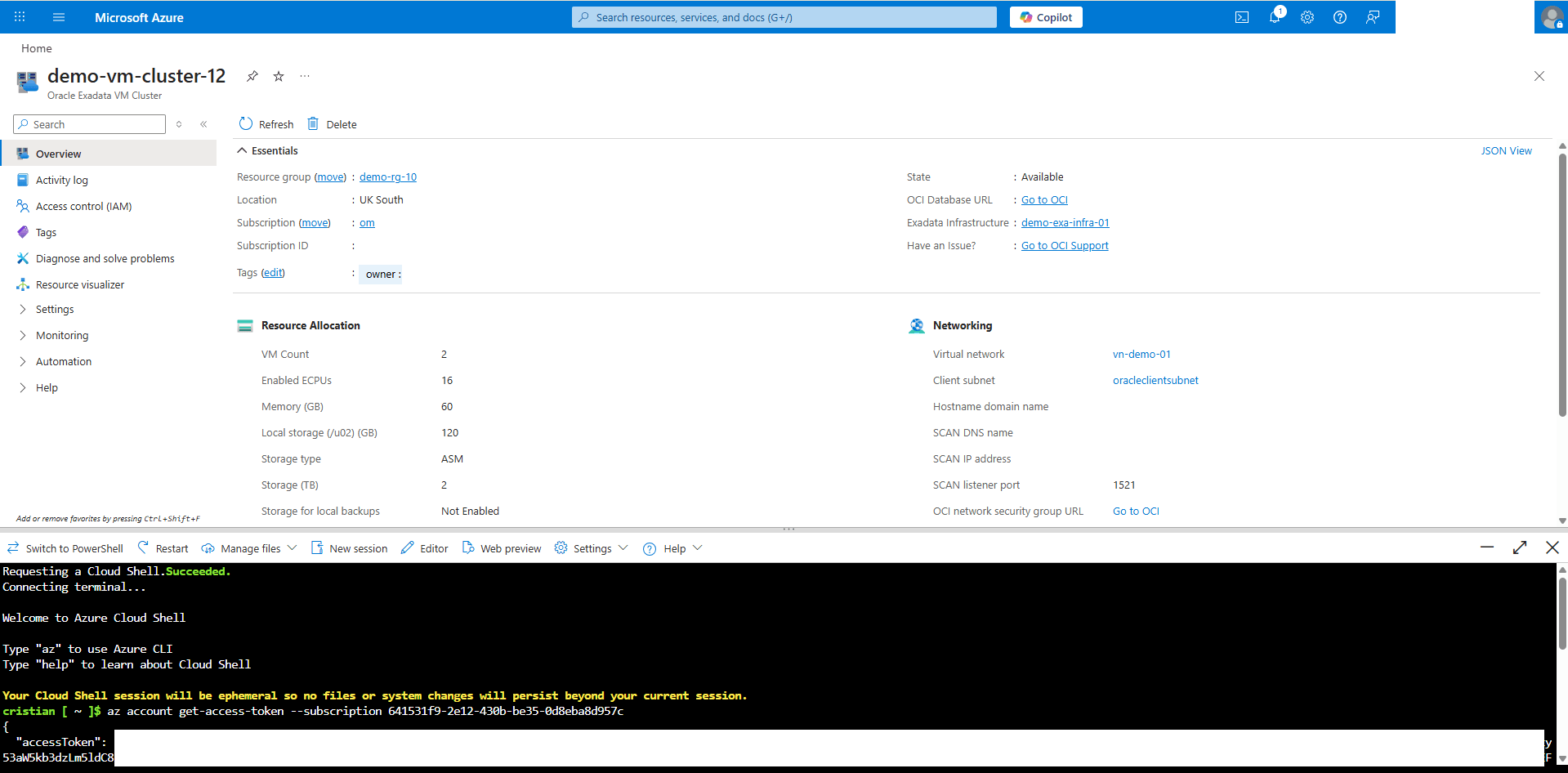
- Generate an Access Token for your Azure Account
- From the Azure Portal, select the Cloud shell button.
- In the Cloud Shell, run the following command. Replace
<Azure_subscription_ID>with your actual Azure Subscription ID.az account get-access-token --subscription <Azure_subscription_ID> - The command will return a JSON object similar to the example below. Take a note of the accessToken value as it is required for the next steps.
{ "accessToken": "eyJ0eXAiOiJKV1QiLCJhbGciOiJ................yrdbX3l8B0IxzgvXdQ", "expiresOn": "2026-03-25 14:35:43.000000", "expires_on": 1774449343, "subscription": "641531f9-2e12-430b-be35-0d8eba8d957c", "tenant": "6798aca3-9d44-4ba7-8a36-39770fe4ab9e", "tokenType": "Bearer" }
- Create an Identity Connector
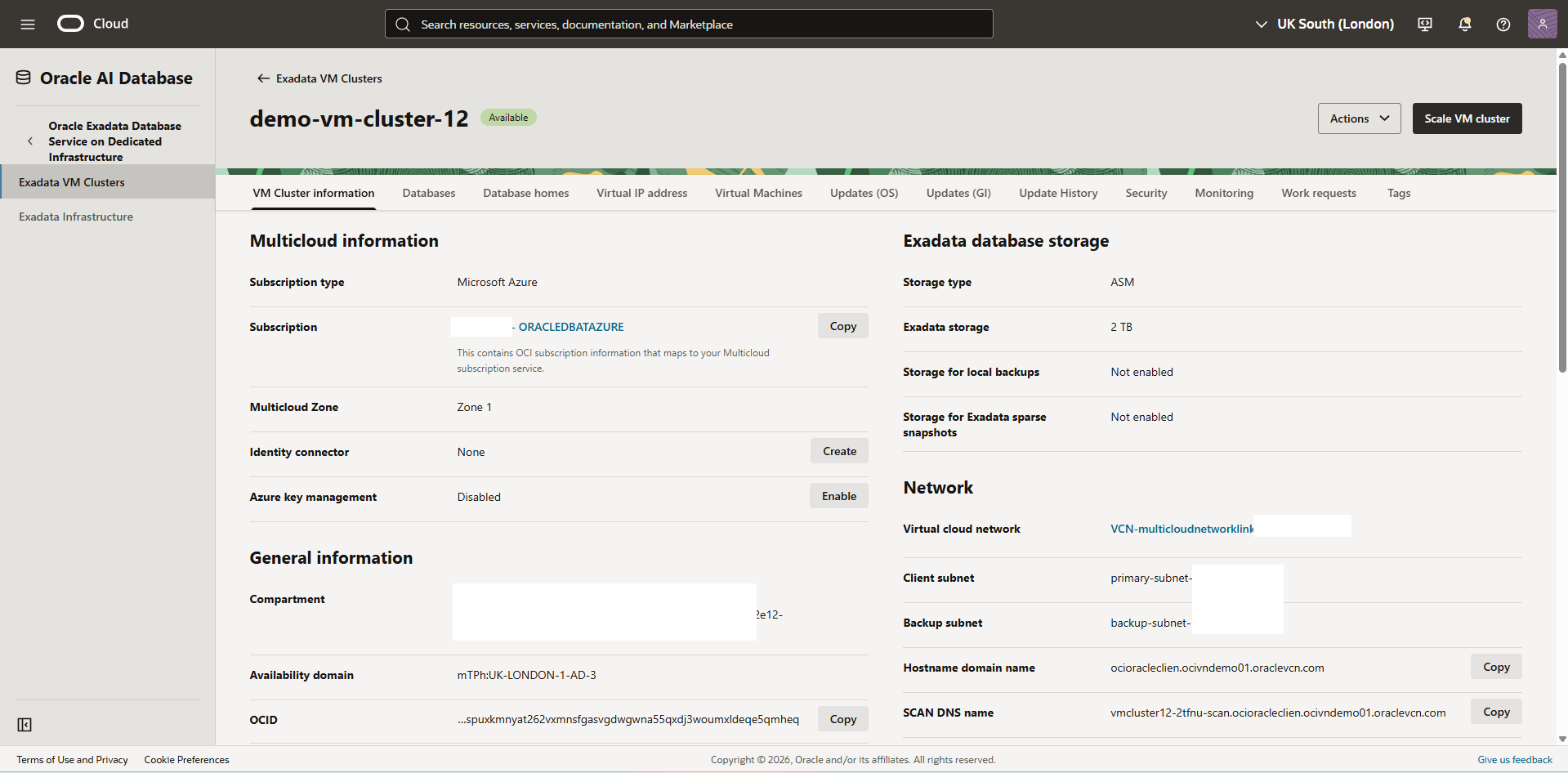
- From the OCI console, select Oracle AI Database, then select Oracle Exadata Database Service on Dedicated Infrastructure.
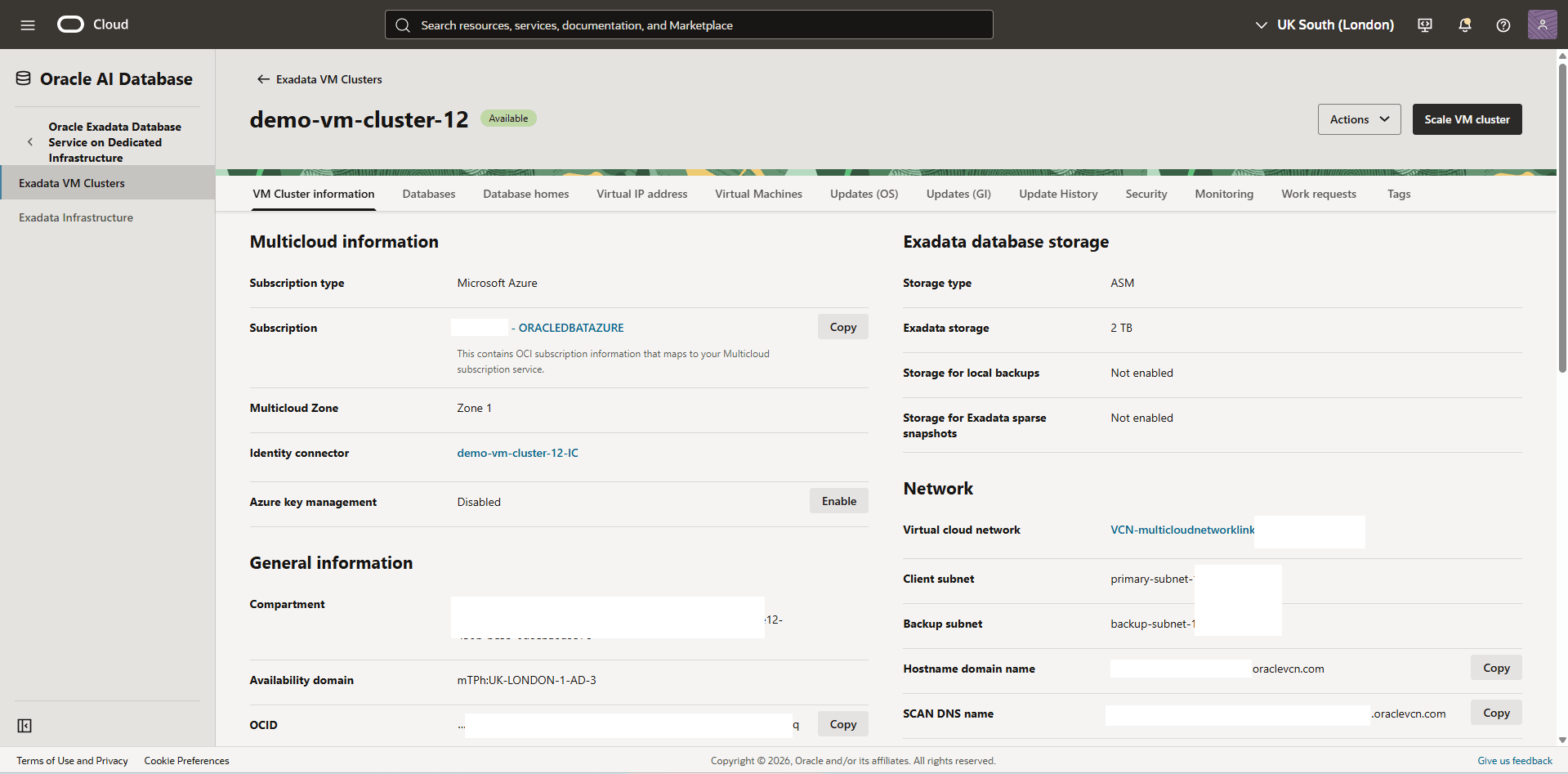
- From the left menu, select Exadata VM Clusters, and then select your Exadata VM Cluster.
- From the Multicloud information section, scroll down to the Identity connector section, and then select the Create button.
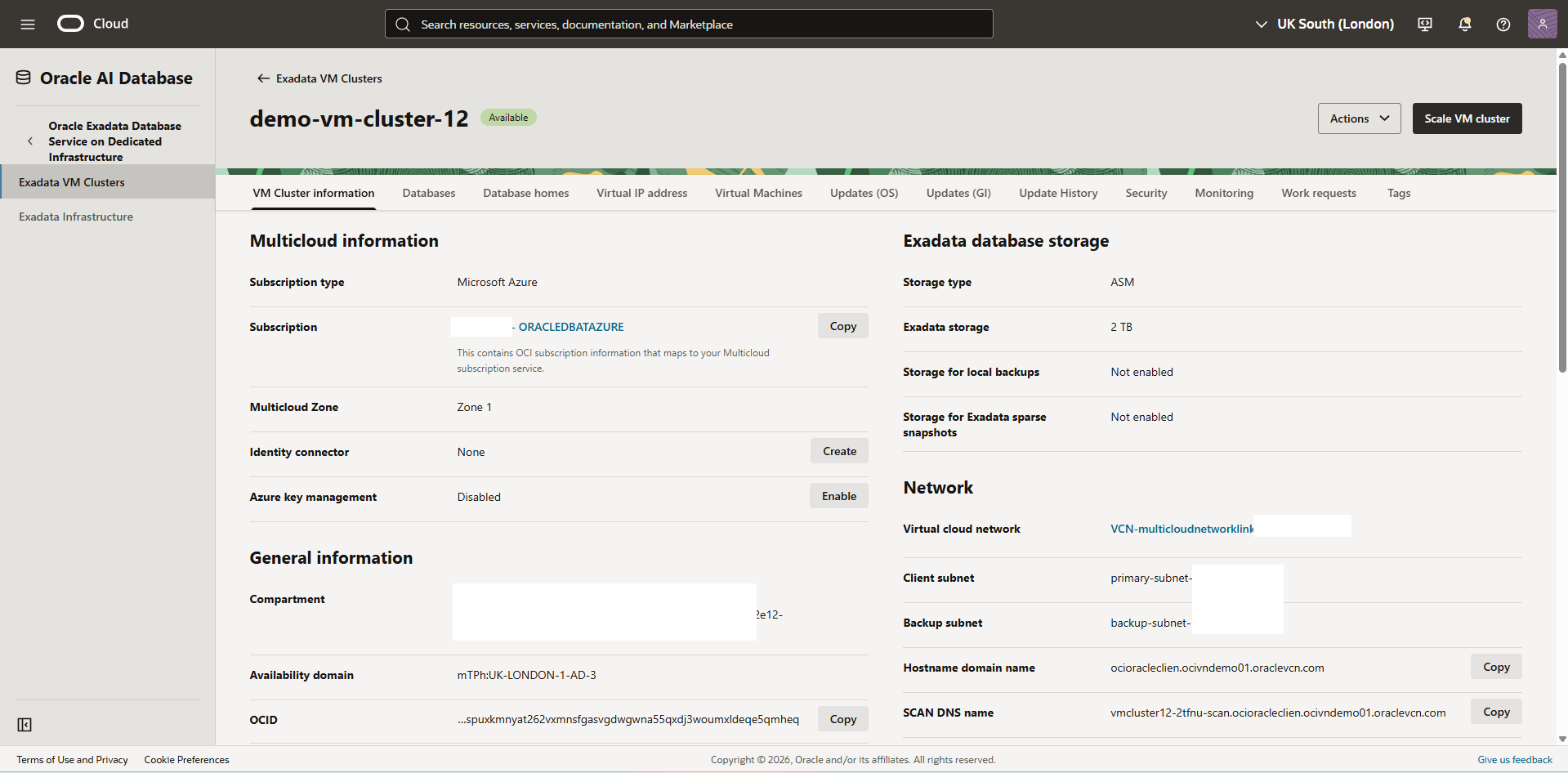
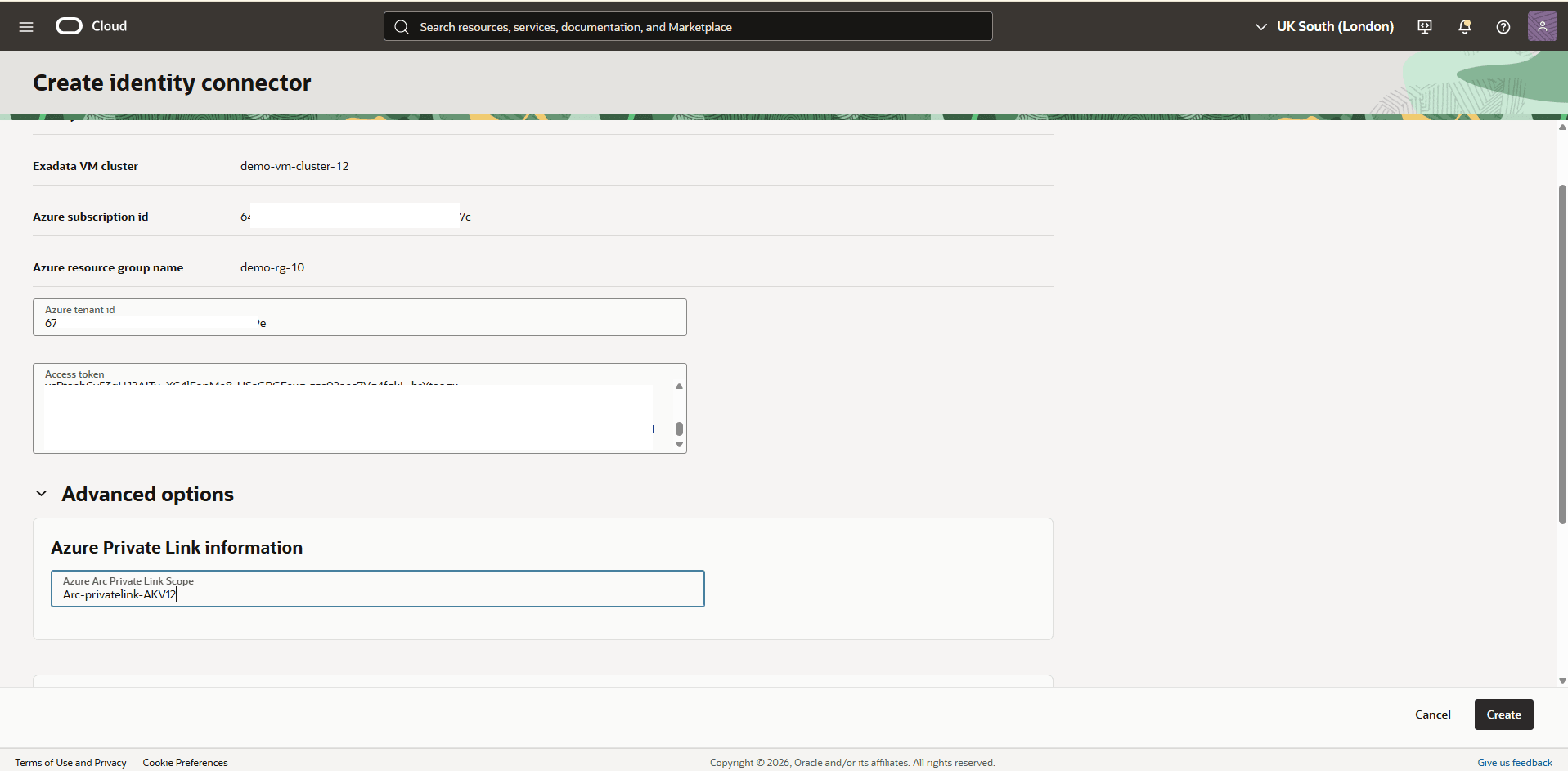
- From the Create identity connector page, enter the following information.
- Enter the Azure Tenant id.
- Paste the Access token that you copied in the previous step.
- Expand the Advanced Options menu, then enter the name of your Azure Arc Private Link Scope that you previously created.
- Review your information and then select the Create button.
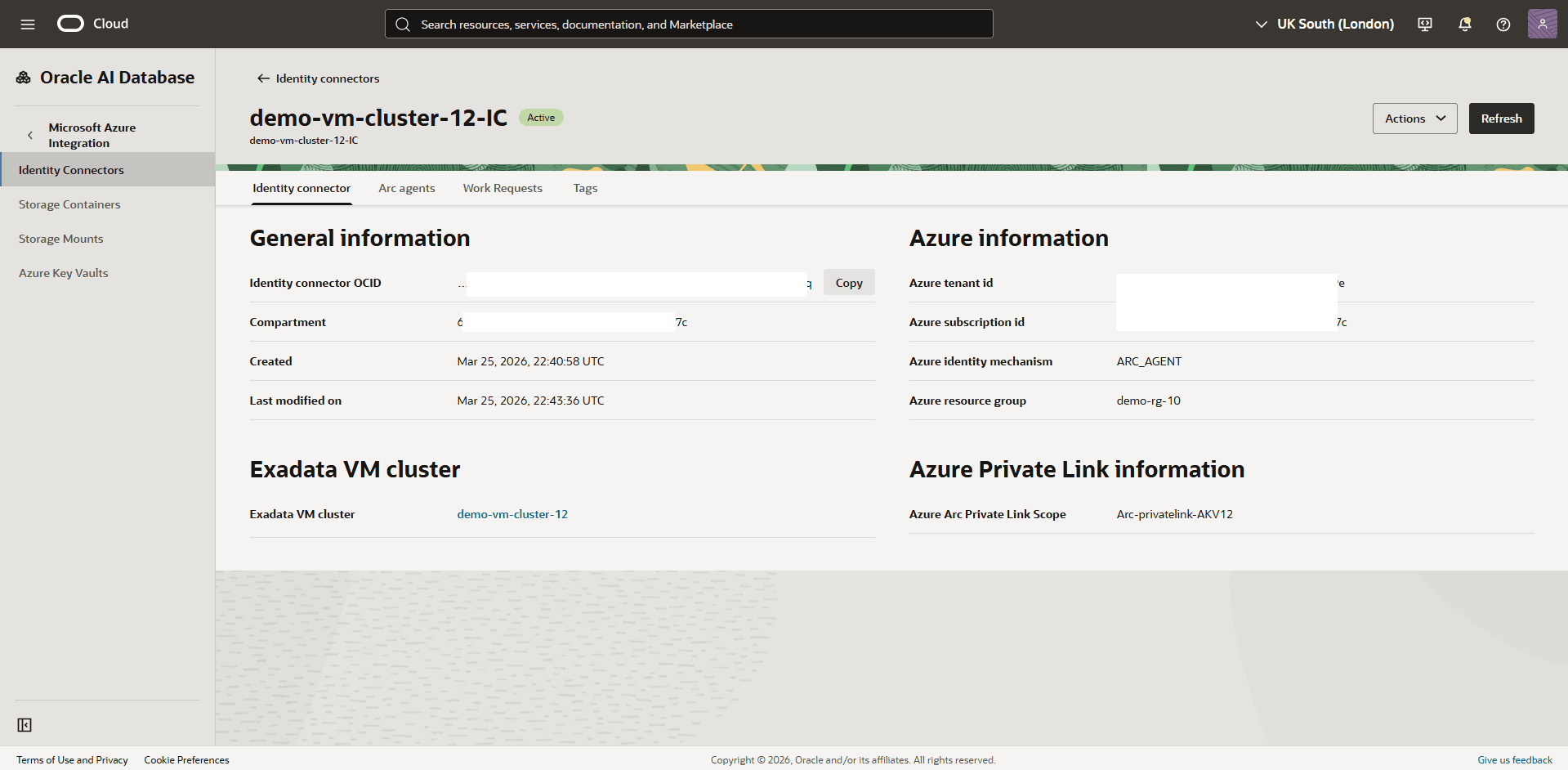
- Validate the Identity Connector Status
- From the OCI console, select Oracle AI Database, then select Oracle Exadata Database Service on Dedicated Infrastructure.
- From the left menu, select Exadata VM Clusters, and then select your Exadata VM Cluster.
- In the VM Cluster information tab, locate the Multicloud information section. Under Identity connector, select the Identity connector link. This will redirect you to the Identity Connector Information page, where you can verify the status. Ensure that the status is shown as Active.
- Generate an Access Token for your Azure Account
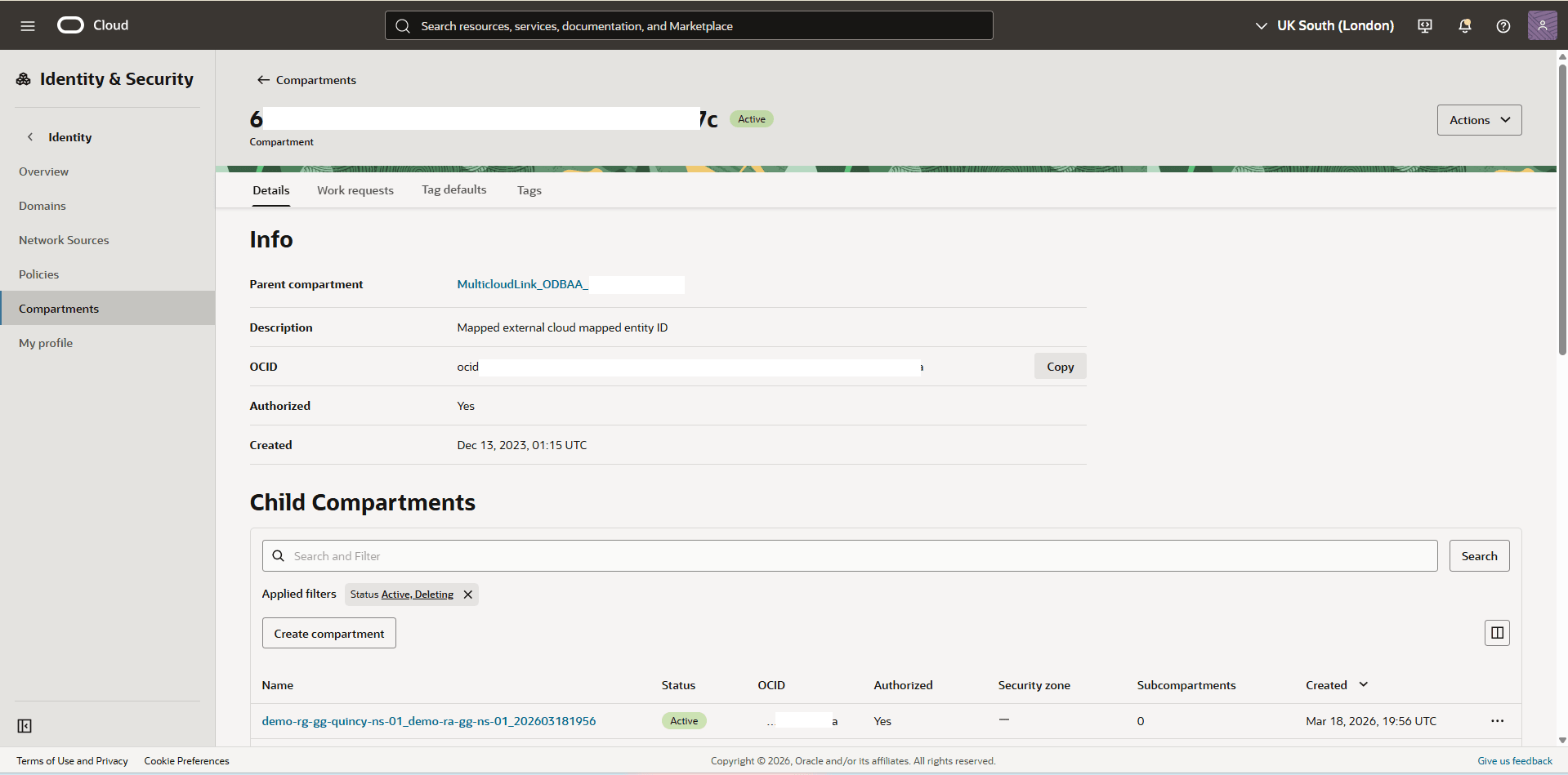
- Create an IAM Policy for Accessing Azure AKV Key Resources
he database uses the cluster resource principal to securely retrieve Azure Cloud key resources. To enable this functionality, you must define the appropriate IAM policies in your OCI tenancy.
To create the appropriate IAM policies, complete the following steps.
- From the OCI console, select Oracle AI Database, then select Oracle Exadata Database Service on Dedicated Infrastructure.
- From the left menu, select Exadata VM Clusters, and then select your Exadata VM Cluster.
- In the VM Cluster information tab, scroll down to the General information section and take a note of the Compartment information.
- From the left menu , select Identity & Security, and then select Compartments.
- Locate the Compartment that you previously recorded. From the Details tab, take a note of the compartment OCID information.
- From the left menu , select Identity & Security, and then select Policies. Select the Create Policy button.
- Enter a policy Name.
- Select the root compartment.
- Select the show manual editorbutton, paste the following policy, and replace the
<your-compartment-OCID>with the compartment OCID that you previously copied.allow any-user to manage oracle-db-azure-vaults in compartment id <your-compartment-OCID> where ALL { request.principal.type in ('cloudvmcluster') } - Select the Create button.
Note
To implement Cross-Region Data Guard with Azure Key Vault (AKV) as your encryption method, you must configure the following additional policies:allow any-user to read oracle-db-azure-keys in compartment id <your-compartment-OCID> where ALL { request.principal.type in ('cloudvmcluster') } allow any-user to manage db-multi-cloud-family in compartment id <your-compartment-OCID> where ALL { request.principal.type in ('cloudvmcluster') }
- Enable the Azure Key Management
- From the OCI console, select Oracle AI Database, then select Oracle Exadata Database Service on Dedicated Infrastructure.
- From the left menu, select Exadata VM Clusters, and then select your Exadata VM Cluster.
- In the VM Cluster information tab, scroll down to the Azure key management section, and select the Enable button. The confirmation message appears, select the Enable button to confirm it.
Note
- When you provision an Exadata VM Cluster, Azure key management is disabled by default.
- If you do not want to use Azure key management, you can disable it by selecting the Disable button. This action will disable Azure key management at the VM Cluster level. Disabling it will impact the availability of the databases using Azure key management. Ensure that no database is currently using Azure key management.
- Azure key management is configured at the VM cluster level, requiring all databases in the cluster to use the same key management solution. However, databases that use Oracle Wallet can coexist alongside those that use Azure Key Vault within the same VM cluster.
- Configure Microsoft Entra ID Permissions for Key Vault Access
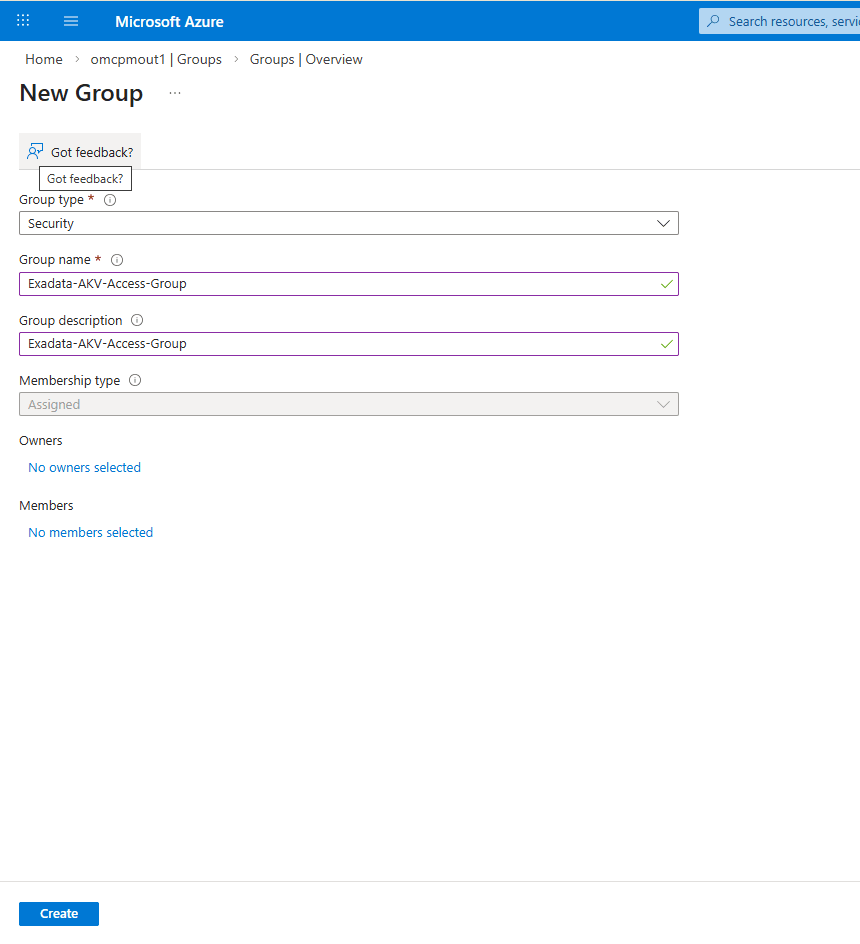
- Create a Azure Group in Microsoft Entra ID
- In the Azure portal, select Microsoft Entra ID.
- From the left menu, select Groups, and then select the New Group button.
- From the New Group page, enter the following information.
- Group type: Security
- Group name: Enter a descriptive name in the field.
- Group description: Enter a description in the field.
- Membership type: Assigned
- Review your information and then select the Create button.
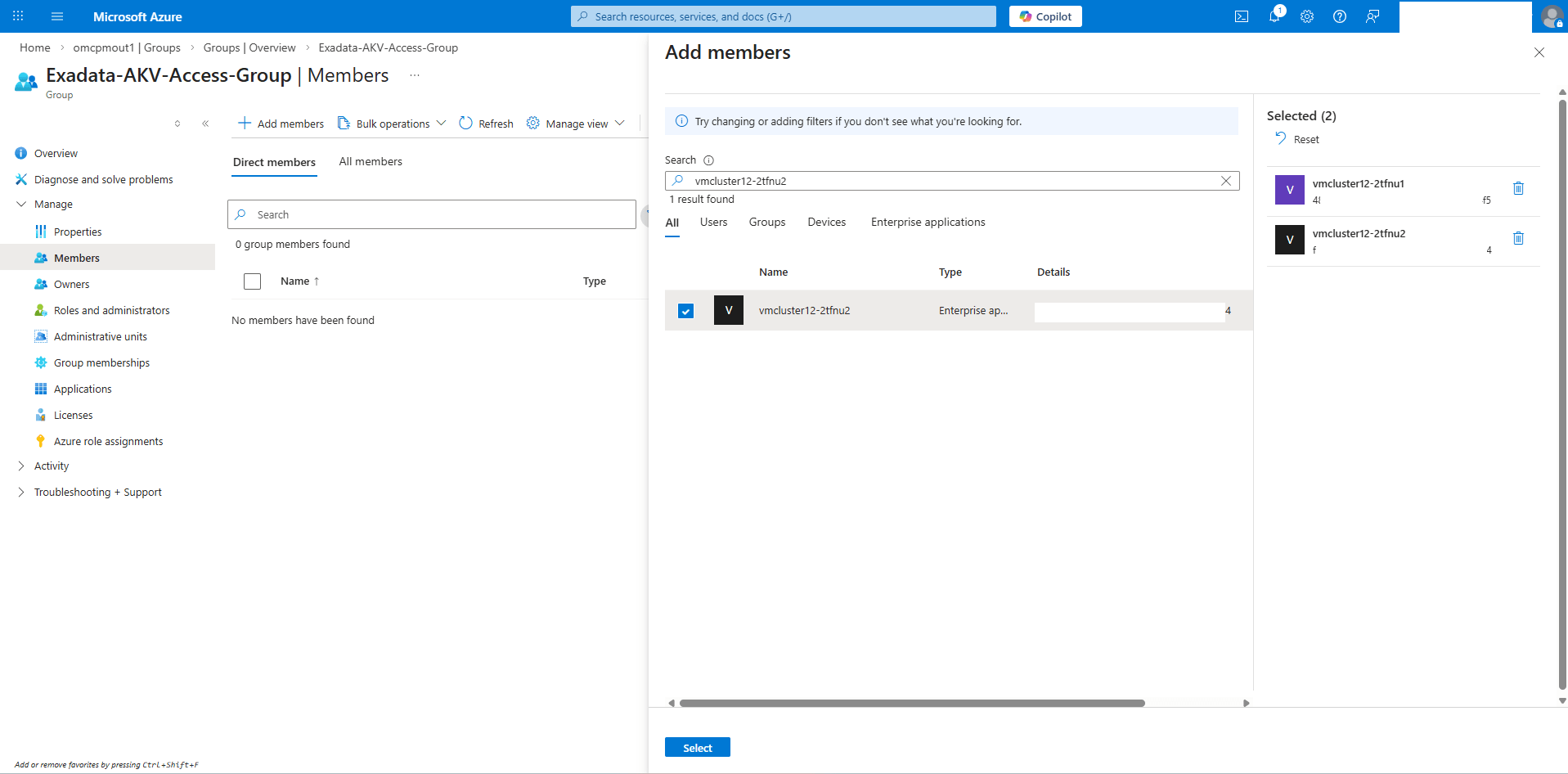
- From the Azure portal, select Microsoft Entra ID and then select Groups.
- Locate the group name that you previously created and then select it.
- In the Group Memberships section, select the View group members link.
- Select the + Add member button.
- Add the Azure Arc name of each node of your Exadata VM Cluster node, then choose the select button.
- Assign Permission to the Azure Key Vault
- From the Azure portal, select Key vaults and then select the Key vault that you want to use.
- From the left menu, select Access control (IAM).
- Select the + Add button, then select the Add role assignment option.
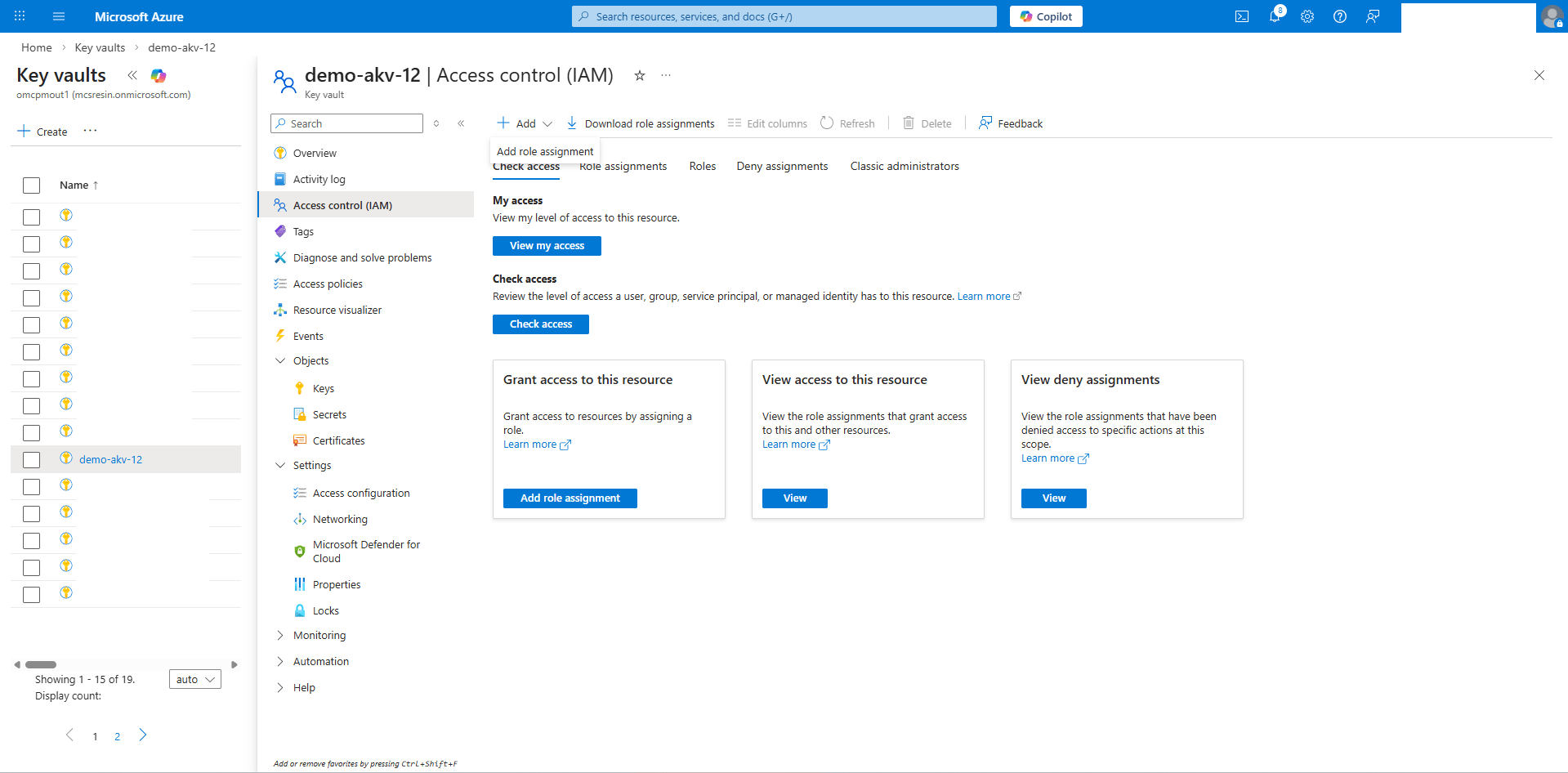
- From the Role tab, search for the Reader role, then select the Next button.
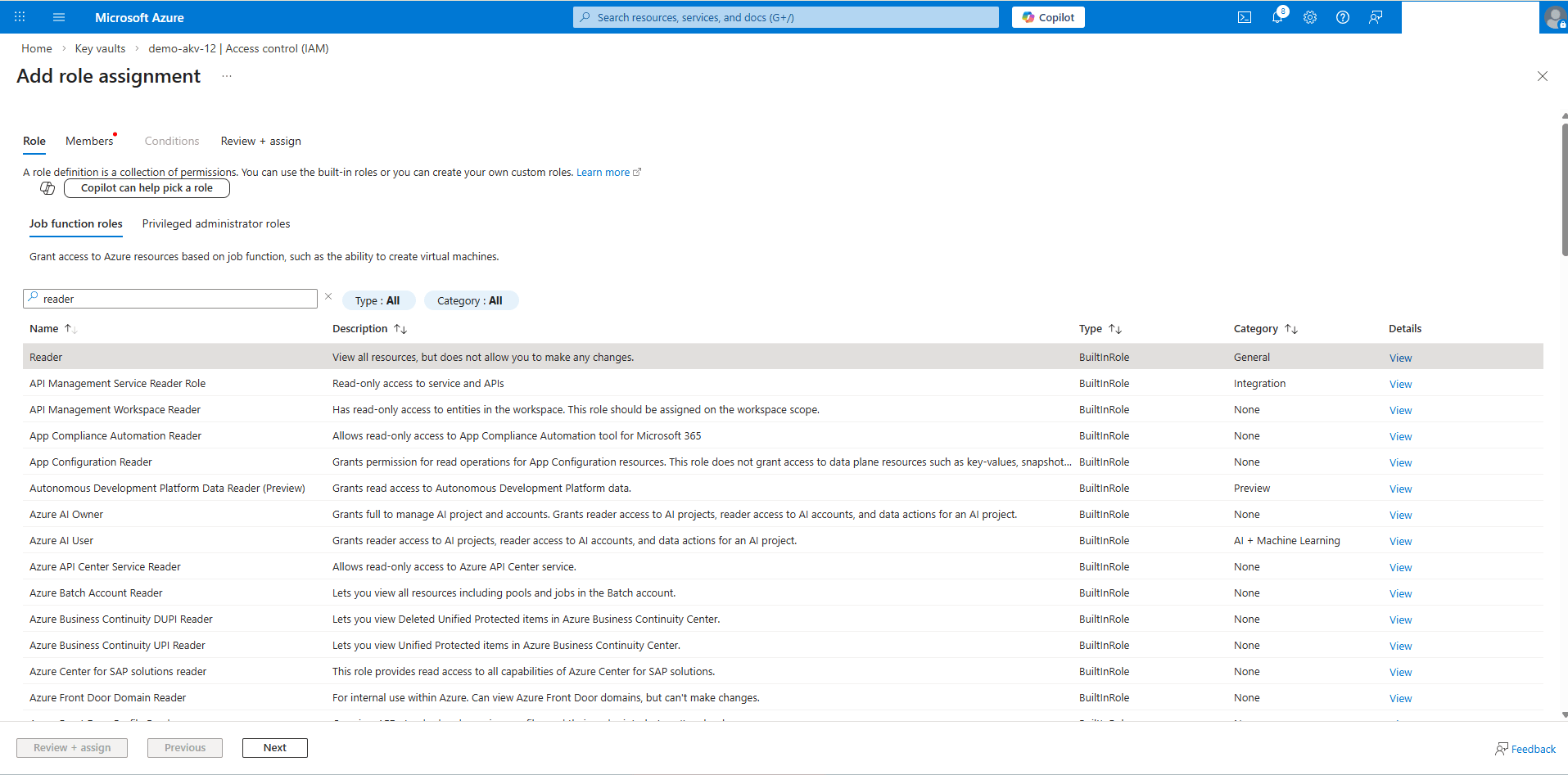
- In the Members tab, select the User, group, or service principal option, then choose the Select members link.
- Search for the Group Name that you previously created. It contains the Azure Arc Names of your Exadata VM Cluster nodes, then choose the Select button.
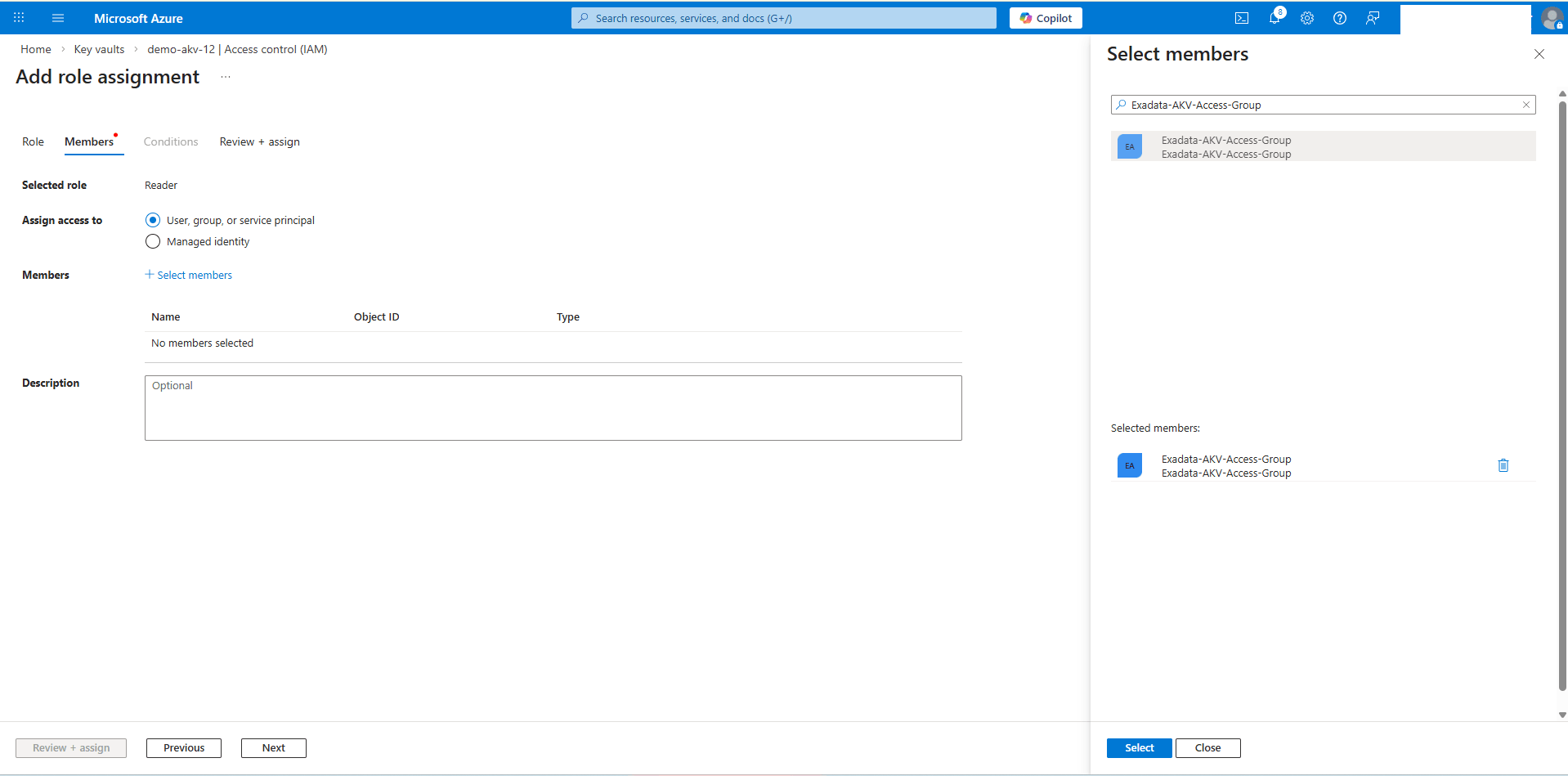
- Review your information and then select the Review + assign button.
- Repeat the step to assign the Key Vault Crypto Officer role.
Note
The Reader and Key Vault Crypto Officer roles must be assigned to the group to grant the necessary permissions to access and manage Azure Key Vault Premium and Azure Key Vault Standard resources.
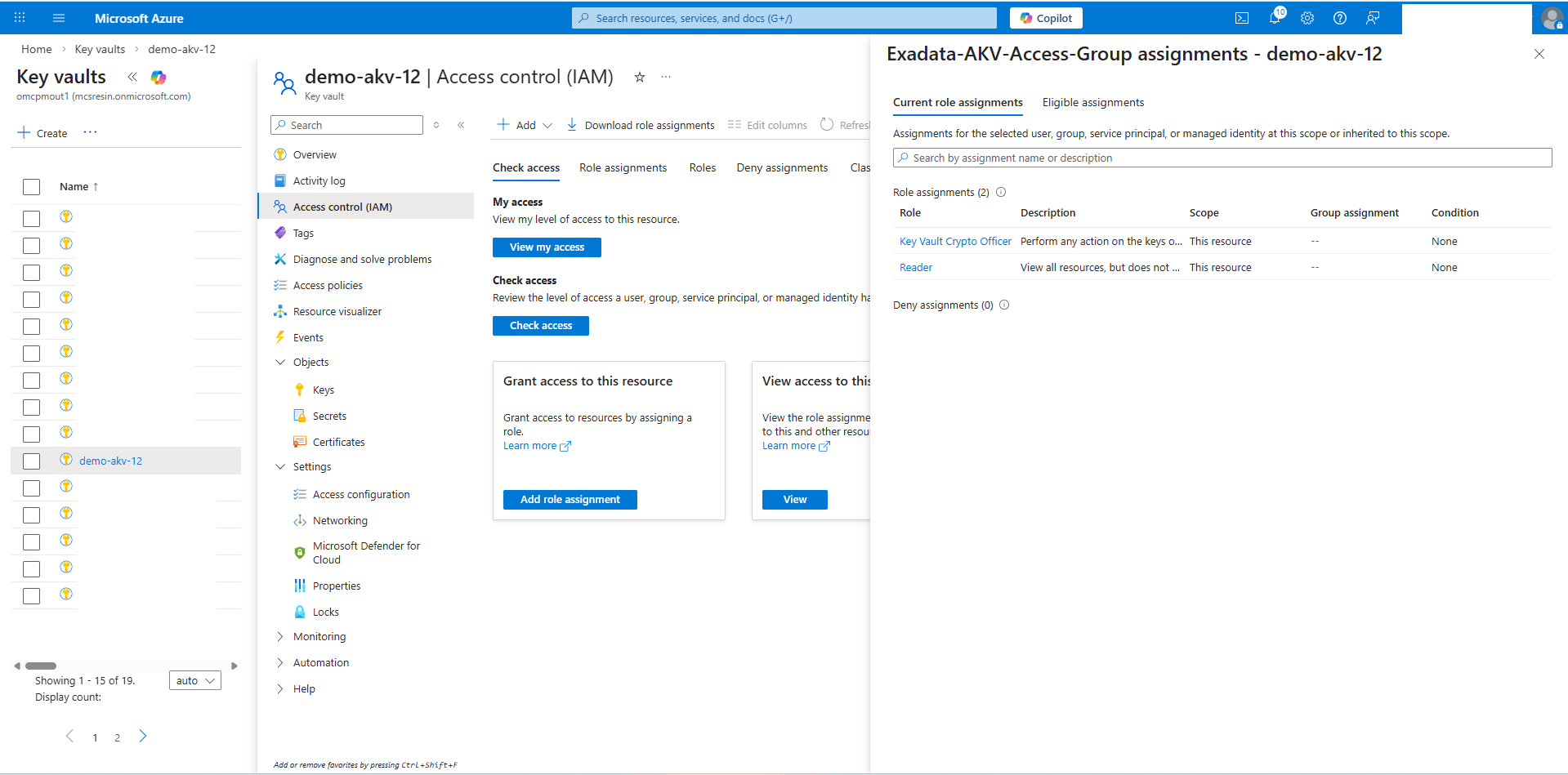
- Validate the Key Vault Permissions
- From the Azure portal, select Key vaults and then select the Key vault that you want to use.
- From the left menu, select Access control (IAM).
- From the Check access section, select the Check access button.
- Search for your Azure Arc Group name that you previously created, then select the Group Name.
- Create a Azure Group in Microsoft Entra ID
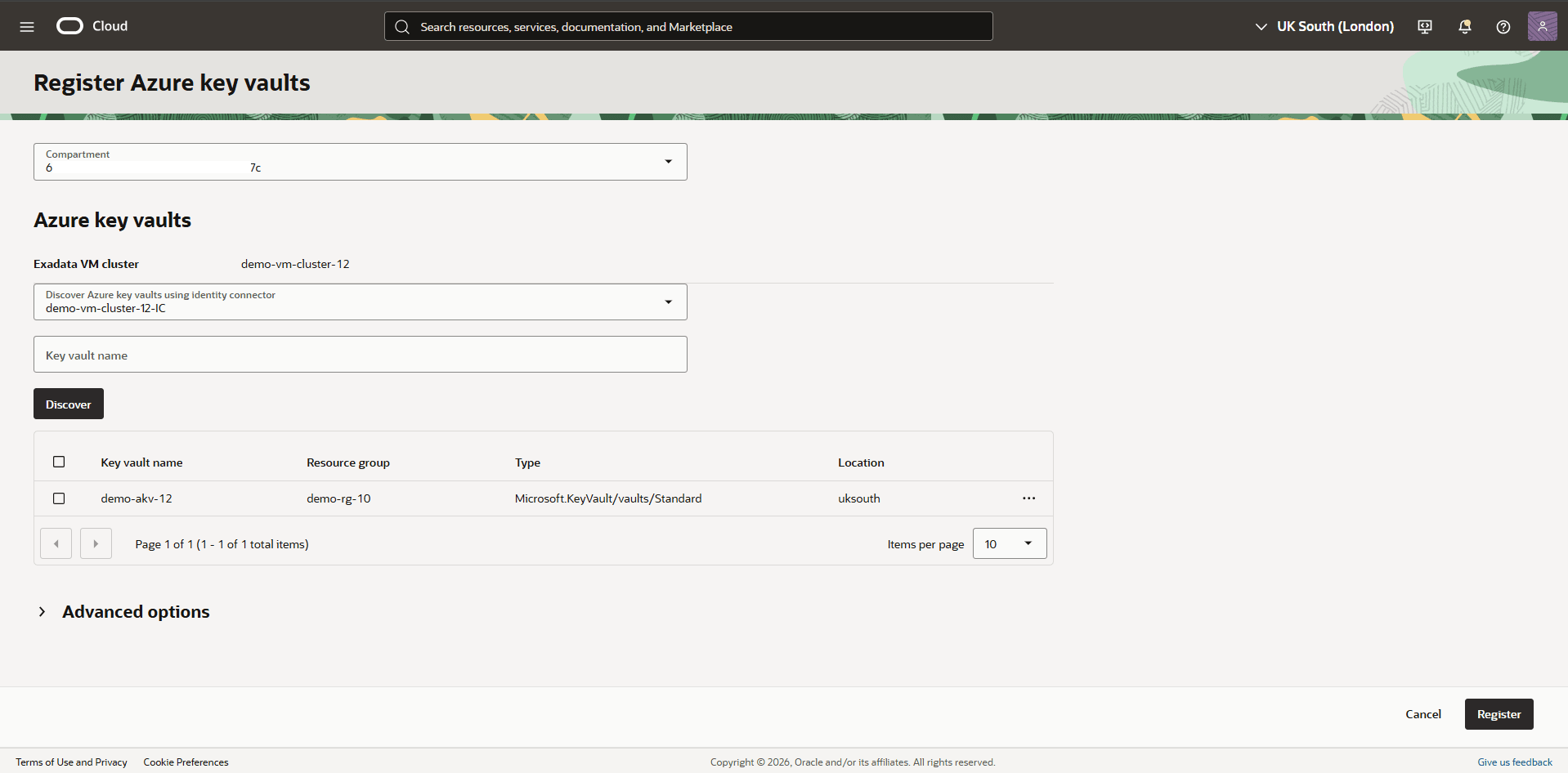
- Register Azure Key Vault in the OCI Console
To enable Azure key management for your Exadata VM Cluster, you must first register your Azure Key Vault in the OCI Console
- From the OCI Console, select Oracle AI Database, and then select Database Multicloud Integrations.
- From the left menu, select Microsoft Azure Integration, then select Azure Key Vaults.
- Select the Register Azure key vaults button, and then complete the following substeps.
- From the dropdown list, select the Compartment in which your Exadata VM Cluster resides.
- Select your identity connector from the dropdown list.
- The Key Vault Name field is optional.
- Select the Discover button.
- Once the key is discovered, select the Key vault checkbox, then select the Register button to register the key in OCI.
Note
Ensure the Azure Key Vault contains at least one valid key. Otherwise, the discovery process will not return any information.
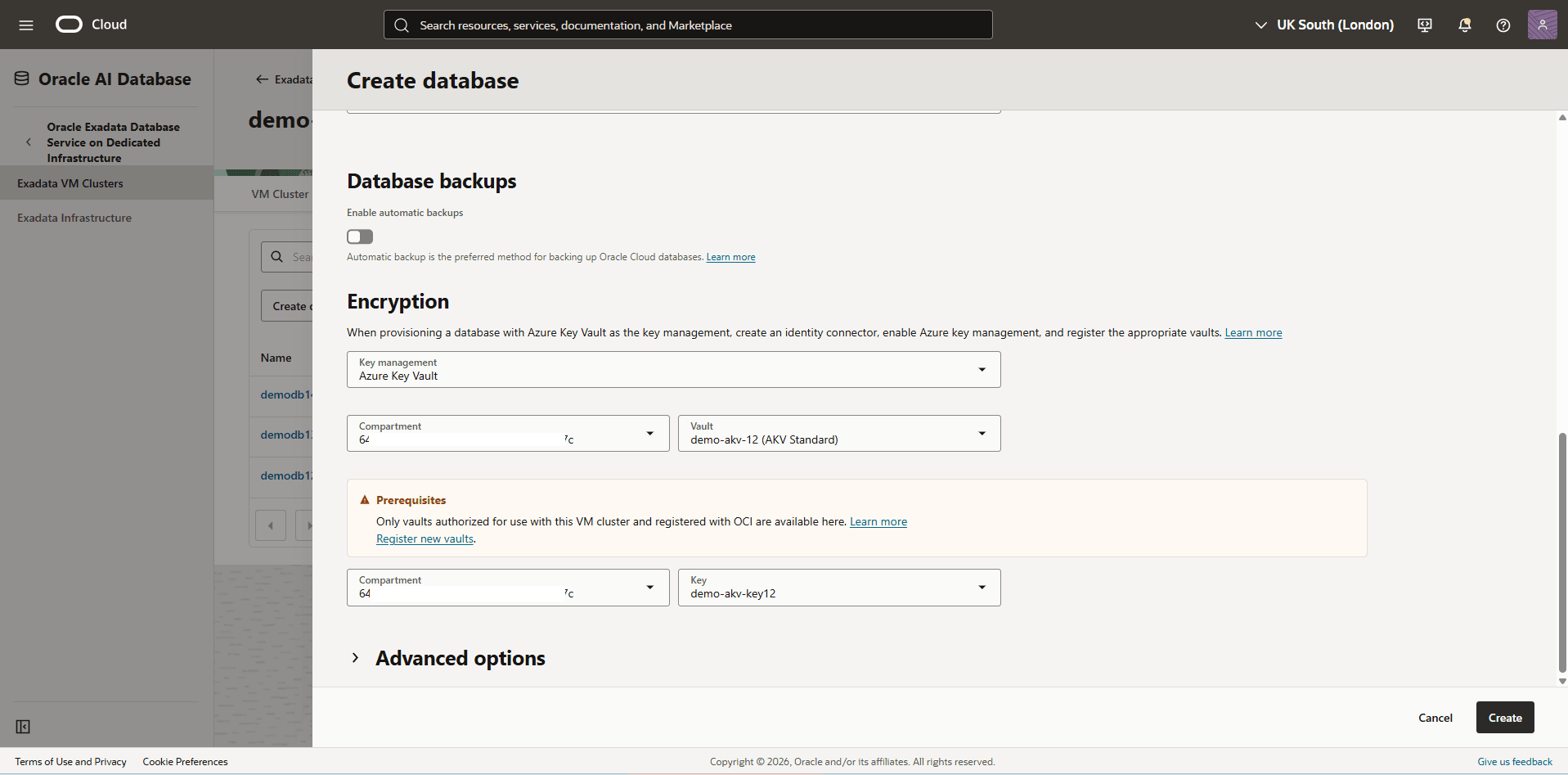
- Create a Database and Use Azure Customer-Managed Key (CMK) as the Key Management Solution
- Complete the following steps described in the Create Exadata Database documentation to create an Exadata Database.
- Navigate to the Encryption section which provides two options. These options include Oracle Wallet and Azure Key Vault.
- Select the Azure Key Vault as the key management. Select the Compartment and the Azure Key Vault from the dropdown list, then select the Key from the dropdown list.
- Review your information, and then select the Create button.
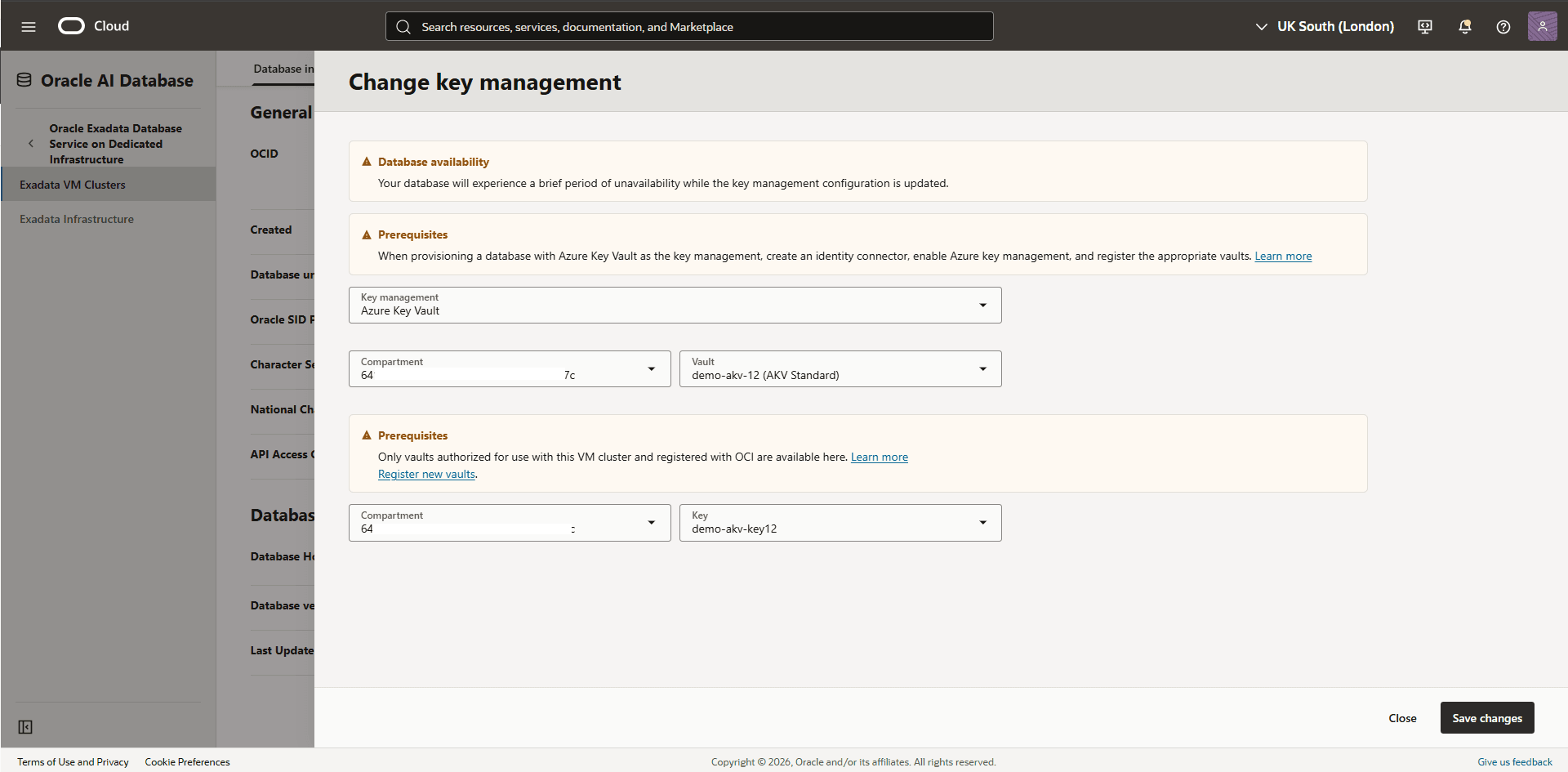
- Modify the Key Management from Oracle Wallet to Azure Customer-Managed Key (CMK)
To update key management from Oracle Wallet to Azure Customer-Managed Key, complete the following steps:
- From your Exadata VM Clusters, navigate to Databases tab, and then select the database that you are using.
- From the Encryption section, confirm that Key management is set to Oracle Wallet, and then select the Change button.
- From the Change key management page, enter the following information.
- Select your Key management as Azure Key Vault from the dropdown list.
- Select the key compartment you are using, and select the desired Azure Key Vault from the dropdown list, then select the key from the dropdown list.
- Select the Save changes button.
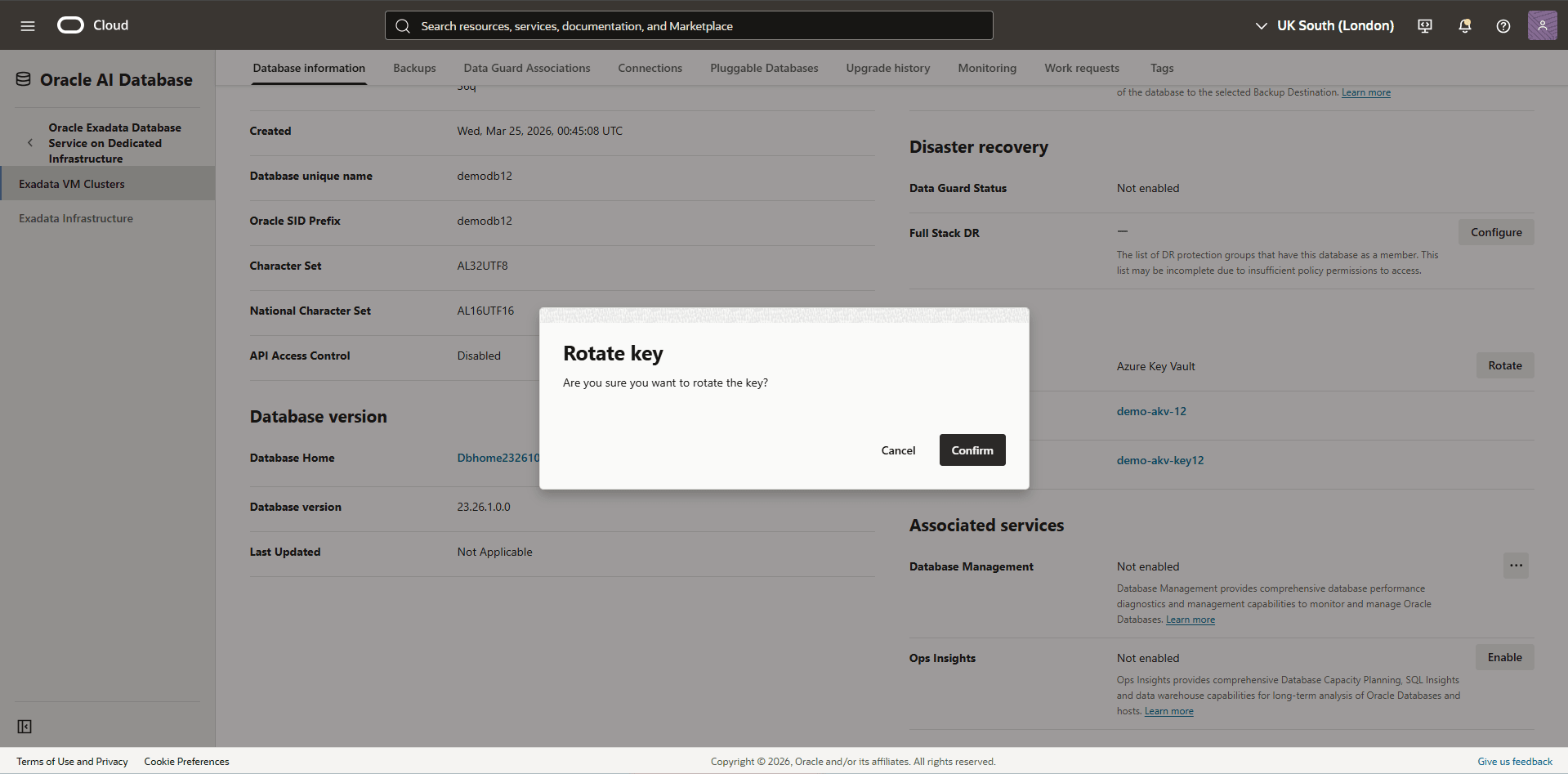
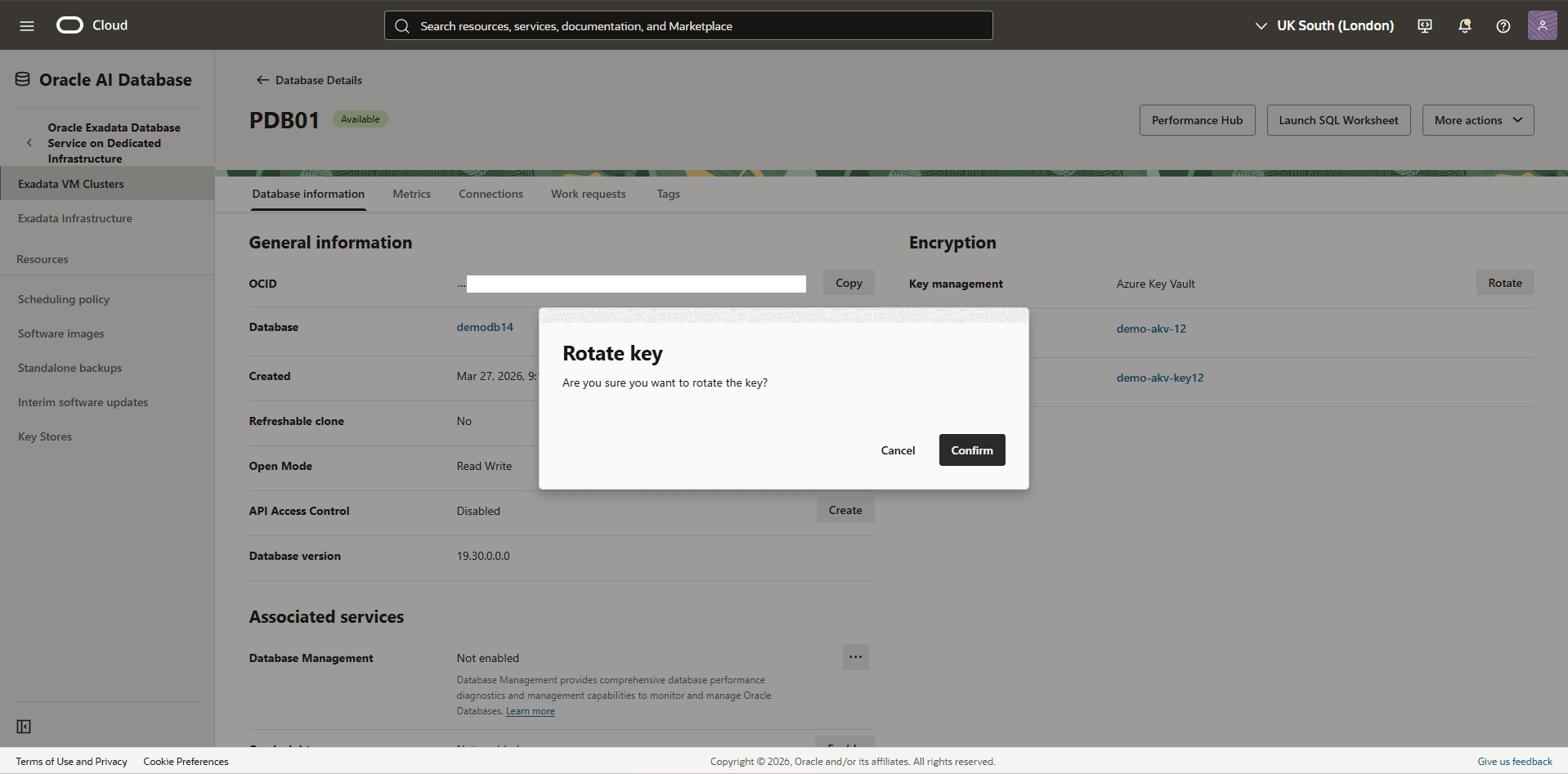
Azure Customer-Managed Key allows you to rotate the key at both Container Database (CDB) and Pluggable Database (PDB) levels to meet your security compliance requirements. Complete the following steps to rotate the key:
Rotate the Azure Customer-Managed Key of a Container Database (CDB)- From the OCI console, select Oracle AI Database, and then select Oracle Exadata Database Service on Dedicated Infrastructure.
- From the left menu, select Exadata VM Clusters, and then select your Exadata VM Cluster that you want to rotate encryption keys.
- Select the Databases tab, and then select the name of the database that you want to rotate encryption keys.
- From the Encryption section, verify that the Key Management is set to Azure Key Vault, then select the Rotate button.
- Select the Confirm button to save the changes.
- From the OCI console, select Oracle AI Database, and then select Oracle Exadata Database Service on Dedicated Infrastructure.
- Select your Exadata VM Cluster, and then select Databases tab.
- Select the Name field of your database you are using, then select Pluggable Databases tab
- Select the Name field of the Pluggable Database you want to use.
- The Encryption section displays that the Key management is set as Azure Key Vault. Select the Rotate button, and then select the Confirm button to save the changes.
Cross-Zone Data Guard with Azure Key Vault
Oracle Exadata Database Service on Dedicated Infrastructure supports cross-zone Data Guard configuration using Azure Key Management Service. This enhancement allows you to maintain a unified security by using Azure customer-managed keys to protect Transparent Data Encryption (TDE) master keys.
To configure cross-zone Data Guard with Azure Key Vault as your customer-managed key method, complete the following steps:
Prerequisites
- Ensure that you meet all prerequisites from the - CMK - AKV tab.
- Ensure that you complete the steps 1 through 15 on both the source and target Exadata Databases from the Protect - Exadata Database - CMK - AKV tab.
- Ensure that you configure Microsoft Entra ID permissions for Key Vault access for both the Primary and Standby Exadata Databases. For step-by-step instructions, see the step 12 (Configure Microsoft Entra ID Permissions for Key Vault Access).
- Ensure connectivity between the two zones. For more information, see the Cross-Zone documentation.
Configure Cross-Zone Data Guard on Exadata Database in Oracle AI Database@Azure
For step-by-step instructions to configure Data Guard on an Exadata Database, see Configure Oracle Data Guard on Exadata Database in Oracle AI Database@Azure.
Cross-Region Data Guard with Azure Key Vault
Oracle Exadata Database Service on Dedicated Infrastructure supports cross-region Data Guard configuration using Azure Key Management Service. This enhancement allows organizations to maintain a unified security posture by using Azure customer-managed keys to protect Transparent Data Encryption (TDE) master keys across geographically distributed database environments.
To configure cross-region Data Guard with Azure Key Vault as your customer-managed key method, complete the following steps:
Prerequisites
- Ensure that you meet all prerequisites from the - CMK - AKV tab.
- Ensure that you complete the steps 1 through 15 on both the source and target Exadata Databases from the Protect - Exadata Database - CMK - AKV tab.
- Ensure that you configure Microsoft Entra ID permissions for Key Vault access for both the Primary and Standby Exadata Databases. For step-by-step instructions, see the step 12 (Configure Microsoft Entra ID Permissions for Key Vault Access).
- Ensure connectivity between the two regions. For more information, see the Cross-Region documentation.
- Validate Azure Key Vault as the Customer-managed Key Method
- From Azure Portal, select Oracle AI Database@Azure.
- From the left menu, select Oracle Exadata Database Service on Dedicated Infrastructure, and then select the Oracle Exadata VM Cluster tab. Select the name of your Exadata VM Cluster.
- Select the name of your Exadata VM Cluster from the Essential section.
- Select the Go to OCI link which redirects you to the OCI Console.
- In the OCI Console, select the Databases tab, and then select the database that you want to check the key management.
- From the Database information tab, navigate to the Encryption section. Verify that the Key management is set to Azure Key Vault with the Vault and Key used in the encryption process.
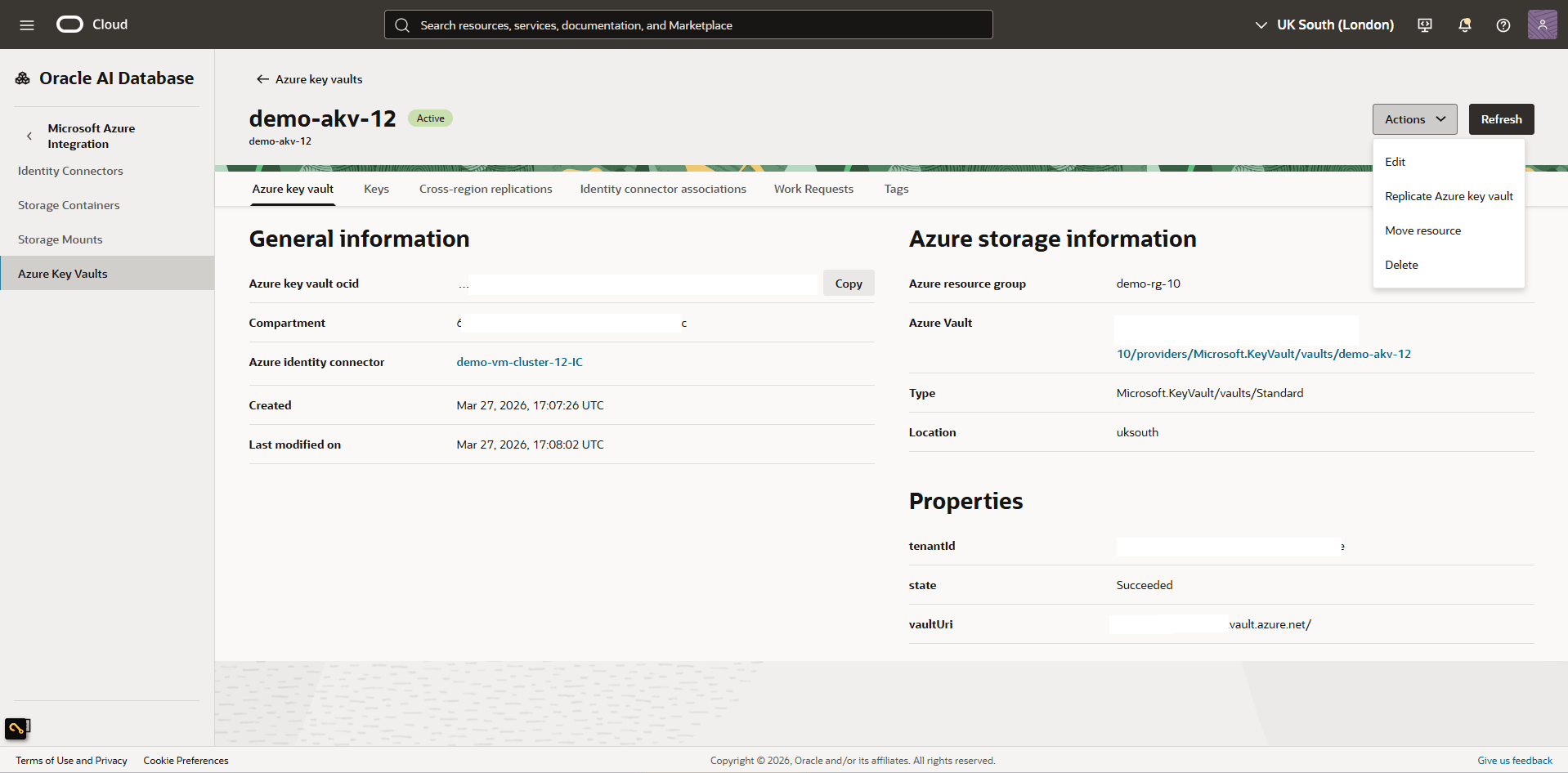
- Enable the OCI Cross-Region Replication to the Azure Key Vault Key Ring
- From the OCI Console, select Oracle AI Database, and then select Database Multicloud Integrations.
- From the left menu, select Microsoft Azure Integration, then select Azure Key Vaults
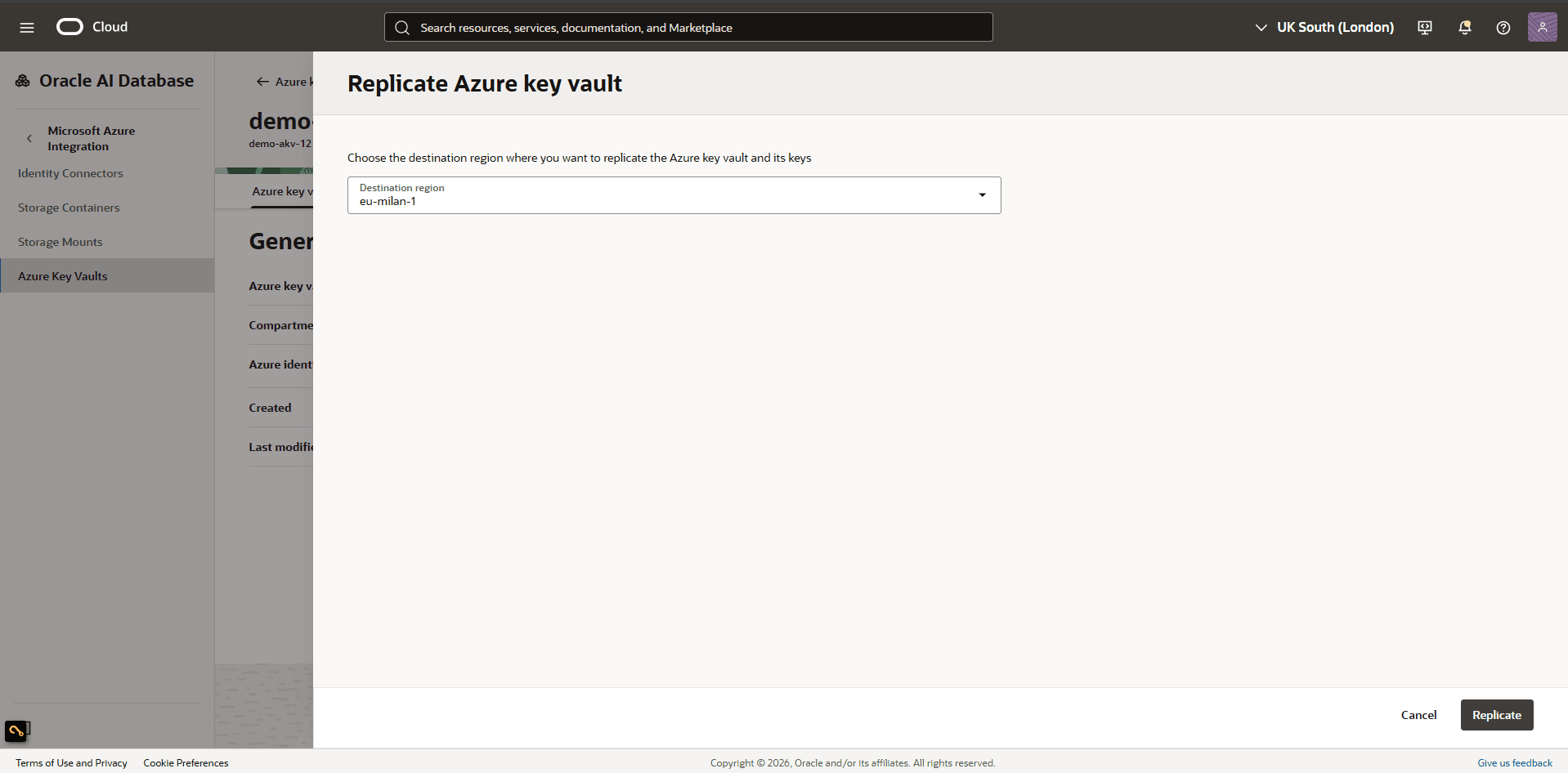
- Select the name of the Azure Key Vault that you want to use, and then select the Actions button. From the dropdown list, select the Replicate Azure Key Vault option.
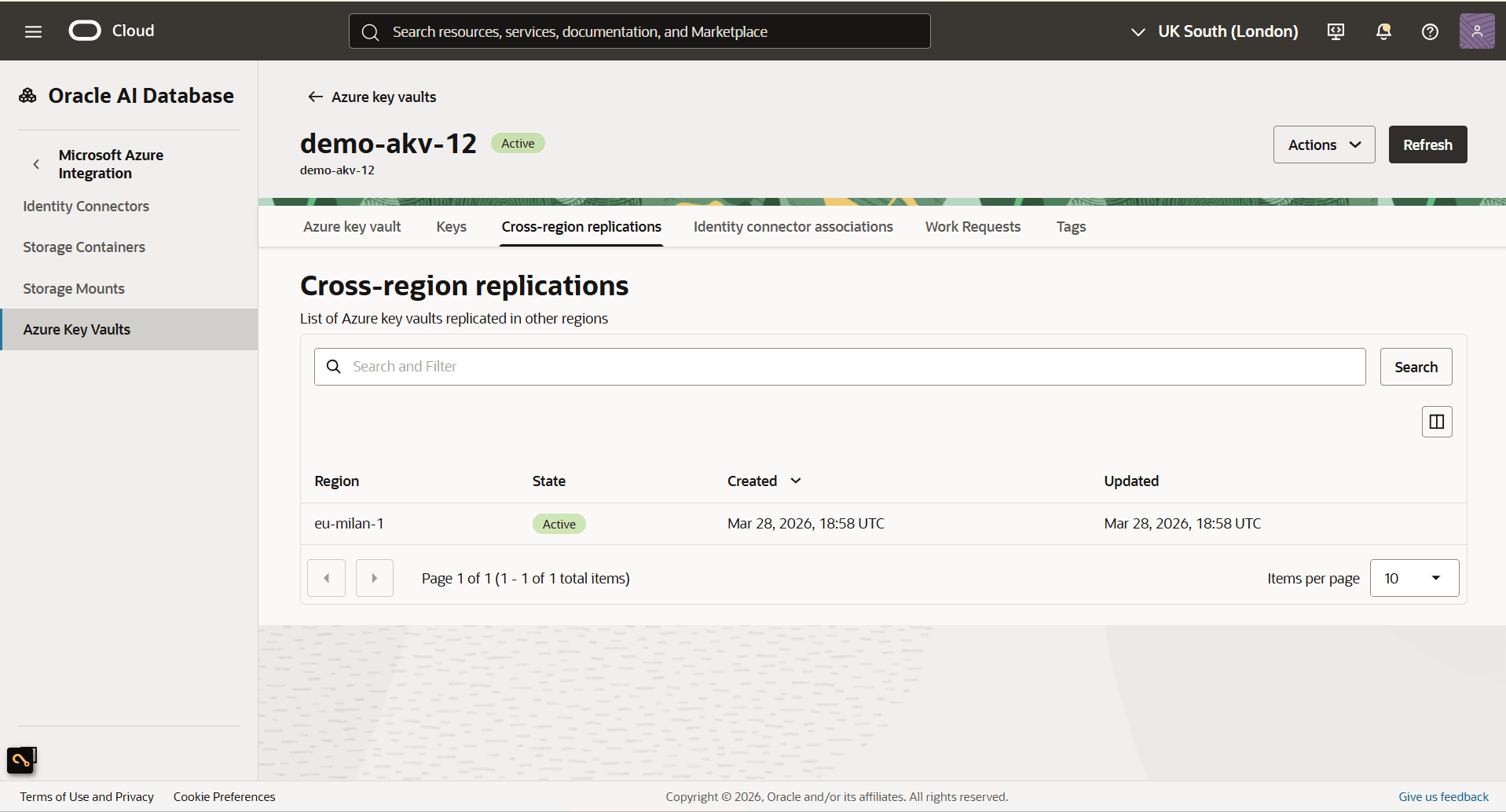
- From the Destination region dropdown list, select the region where you wish to replicate the key ring, then select the Replicate button.
- Once the process is complete, navigate to the Cross-region replications tab. Ensure the key ring appears as Active within the specific region you selected for replication.
- Create Azure Key Vault Endpoint in the Standby Region
- From the Azure portal, select Key vaults and then select the Name field of the key vault that you replicated in the previous step.
- Expand the Settings section, and then select Networking.
- Select the Private endpoints connections tab, then select the Create button.
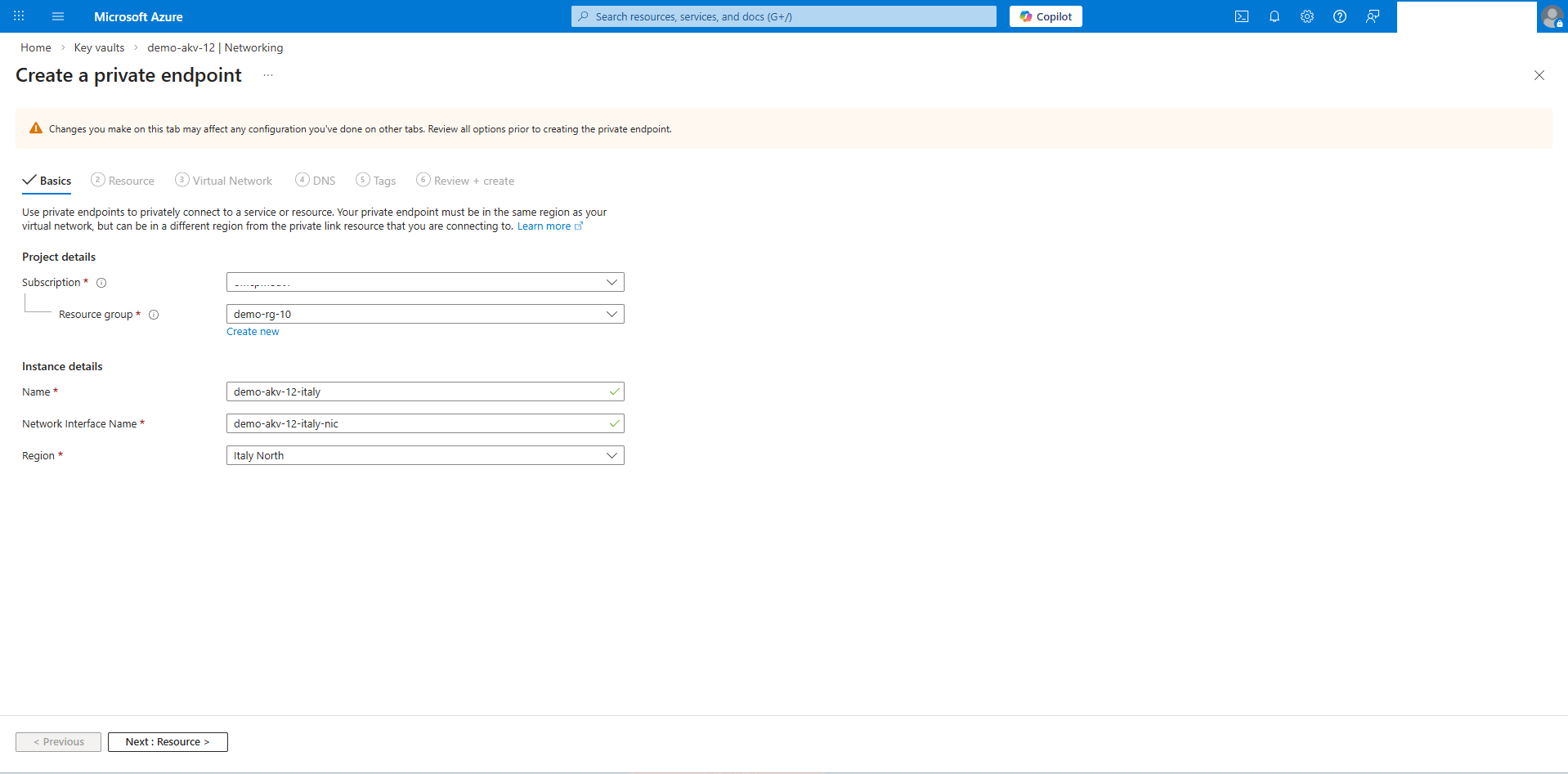
- From the Create a private endpoint page, complete the following substeps:
- In the Basics tab, enter the following information.
- Choose the Subscription that you want to use, then select the Resource group.
- Enter a descriptive Name for your private endpoint.
- Enter a descriptive name in the Network Interface Name field.
- Select a Region (Standby) from the dropdown list.
- Select the Next: Resource > button.
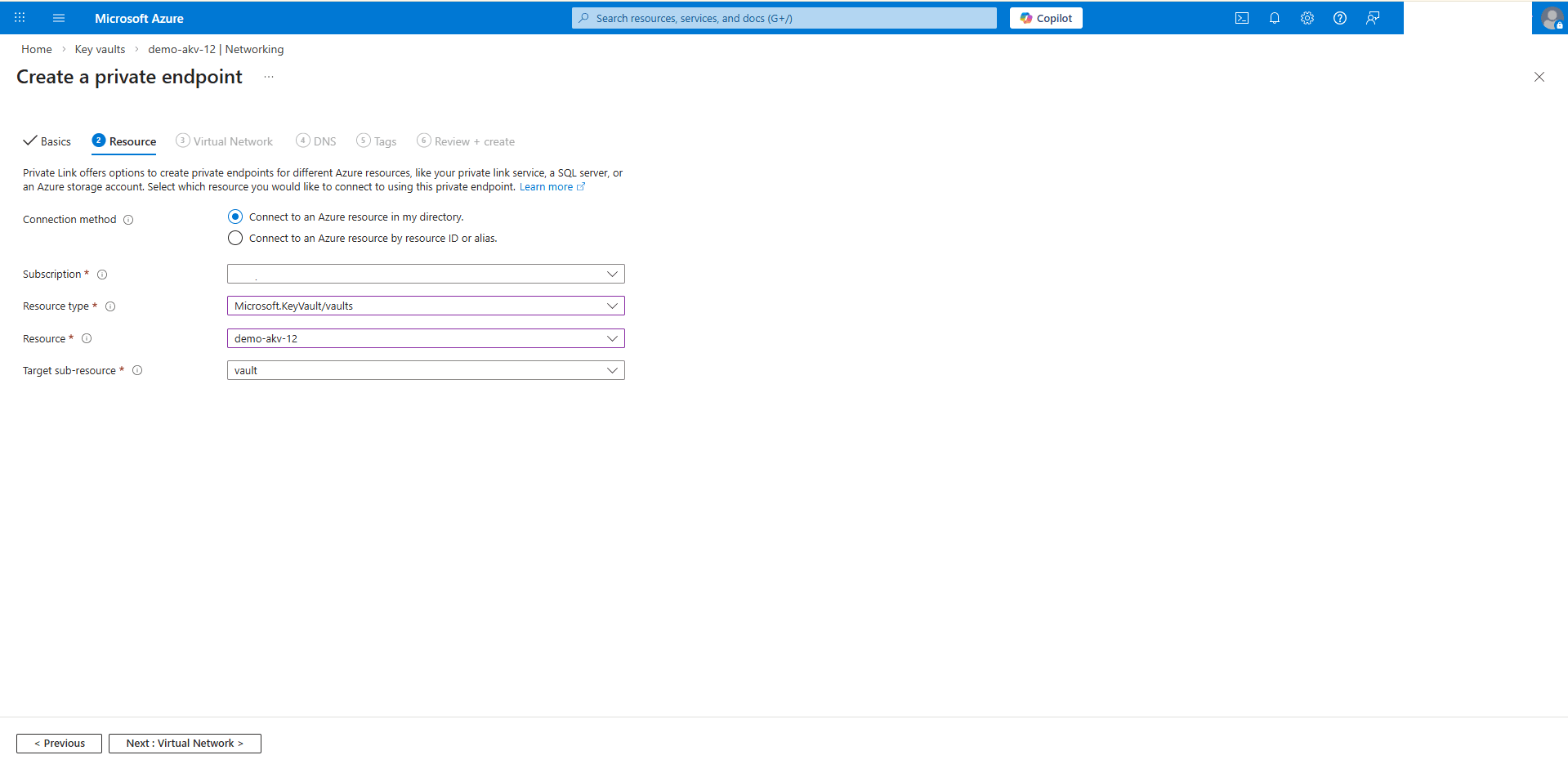
- In the Resource tab, enter the following information.
- Choose the Connect to an Azure resource in my directory option as your Connection method.
- Choose the Subscription that you wish to use.
- Select Microsoft.KeyVault/Vaults as your Resource type.
- From the Resource dropdown list, select the key that you wish to use and replicate .
- Select your Target sub-resource.
- Select the Next: Virtual Network > button.
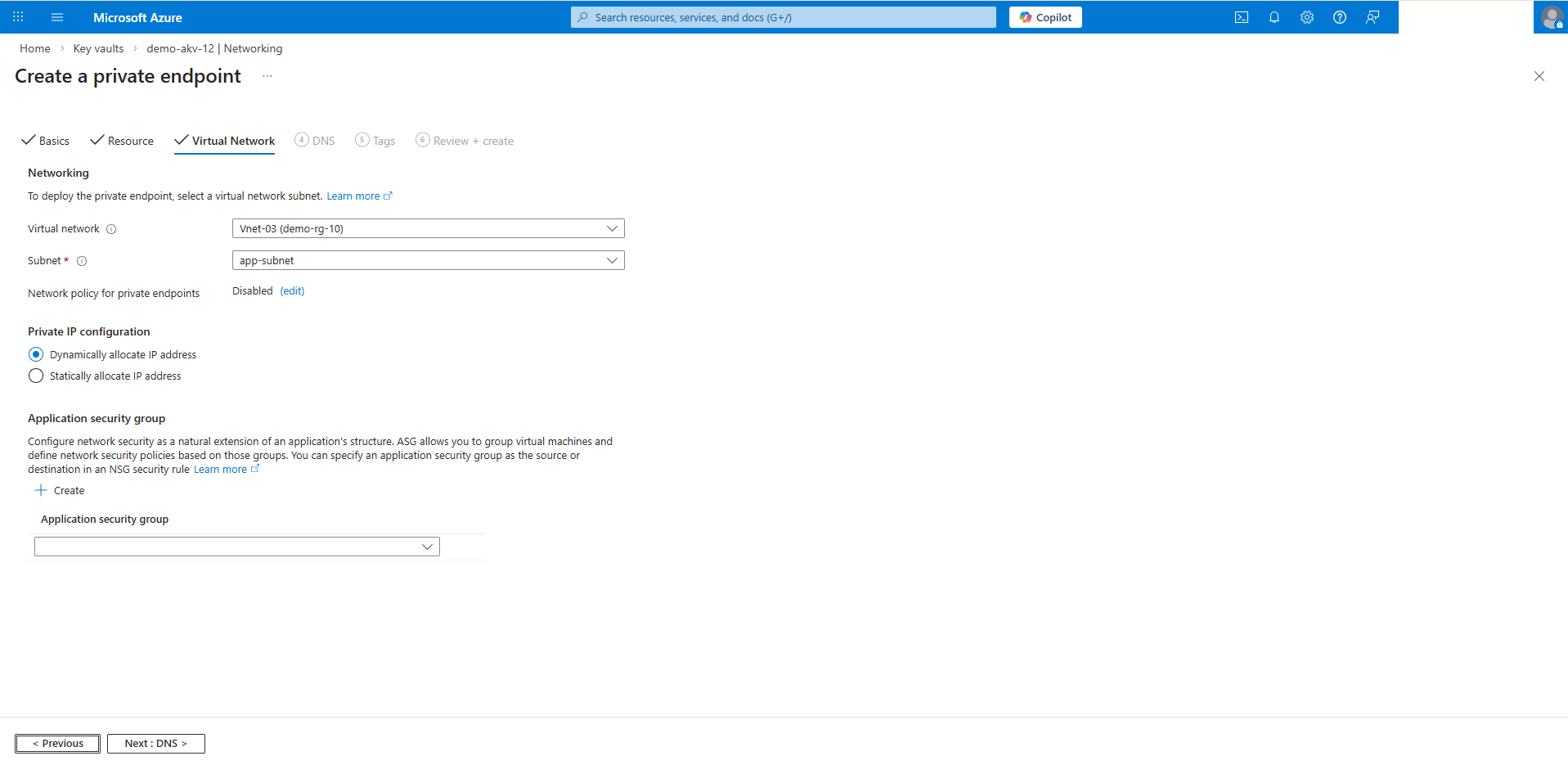
- In the Virtual Network tab, enter the following information.
- From the dropdown list, select the Virtual network in your standby region.
- From the dropdown list, select the Subnet where you want to deploy your private endpoint.
- Choose the Dynamically allocate IP address option from the Private IP configuration.
- Select the Next: DNS > button.
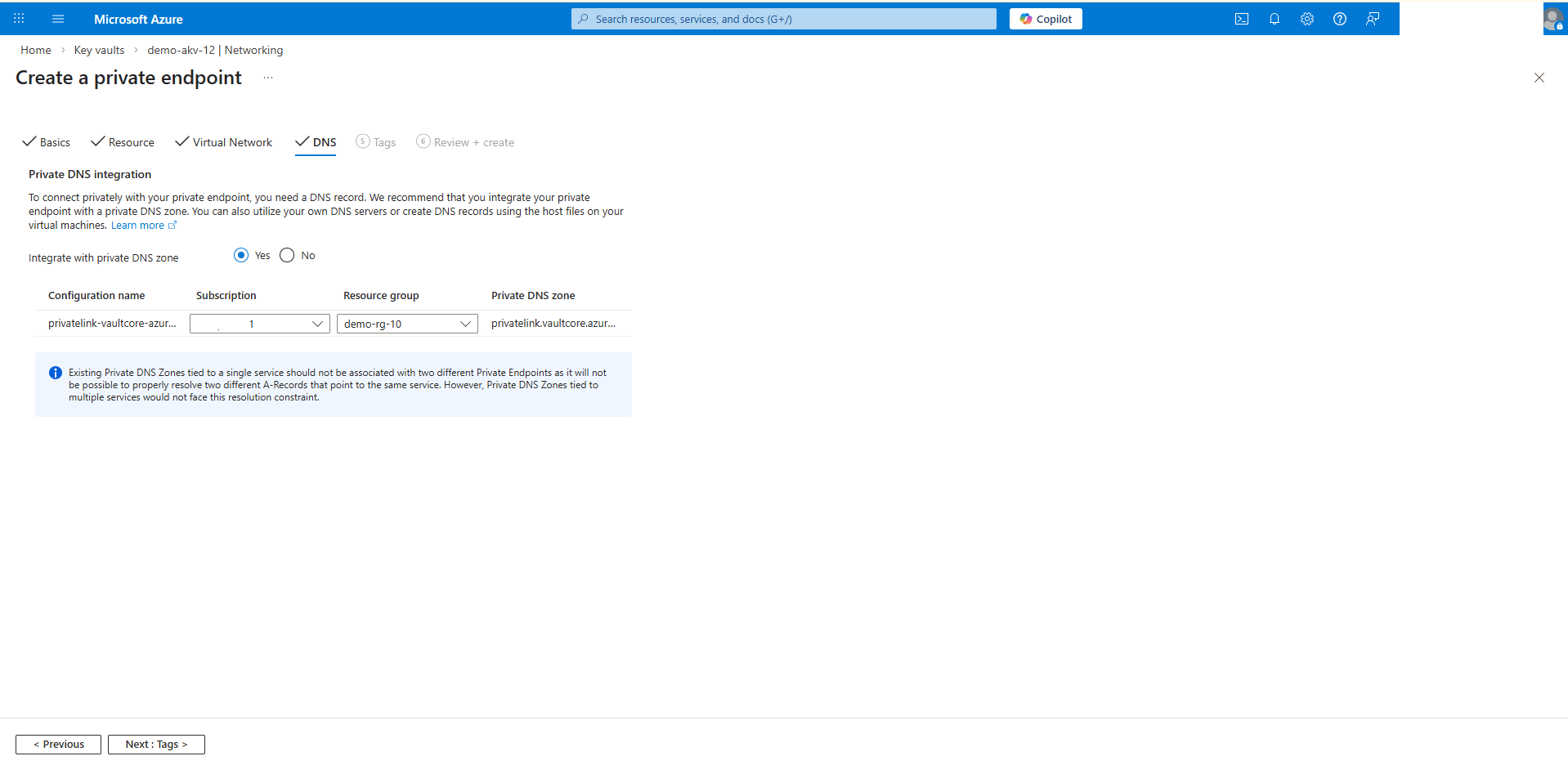
- In the DNS tab, enter the following information.
- Choose the Yes option from the Integrate with private DNS zone section.
- Select your Subscription and Resource group.
- Select the Next: Tags > button.
- In the Tags tab, you can enter Key and Value information. This section is optional. Select the Next: Review + create > button.
- In the Review + create tab, review your information, and then select the Create button.
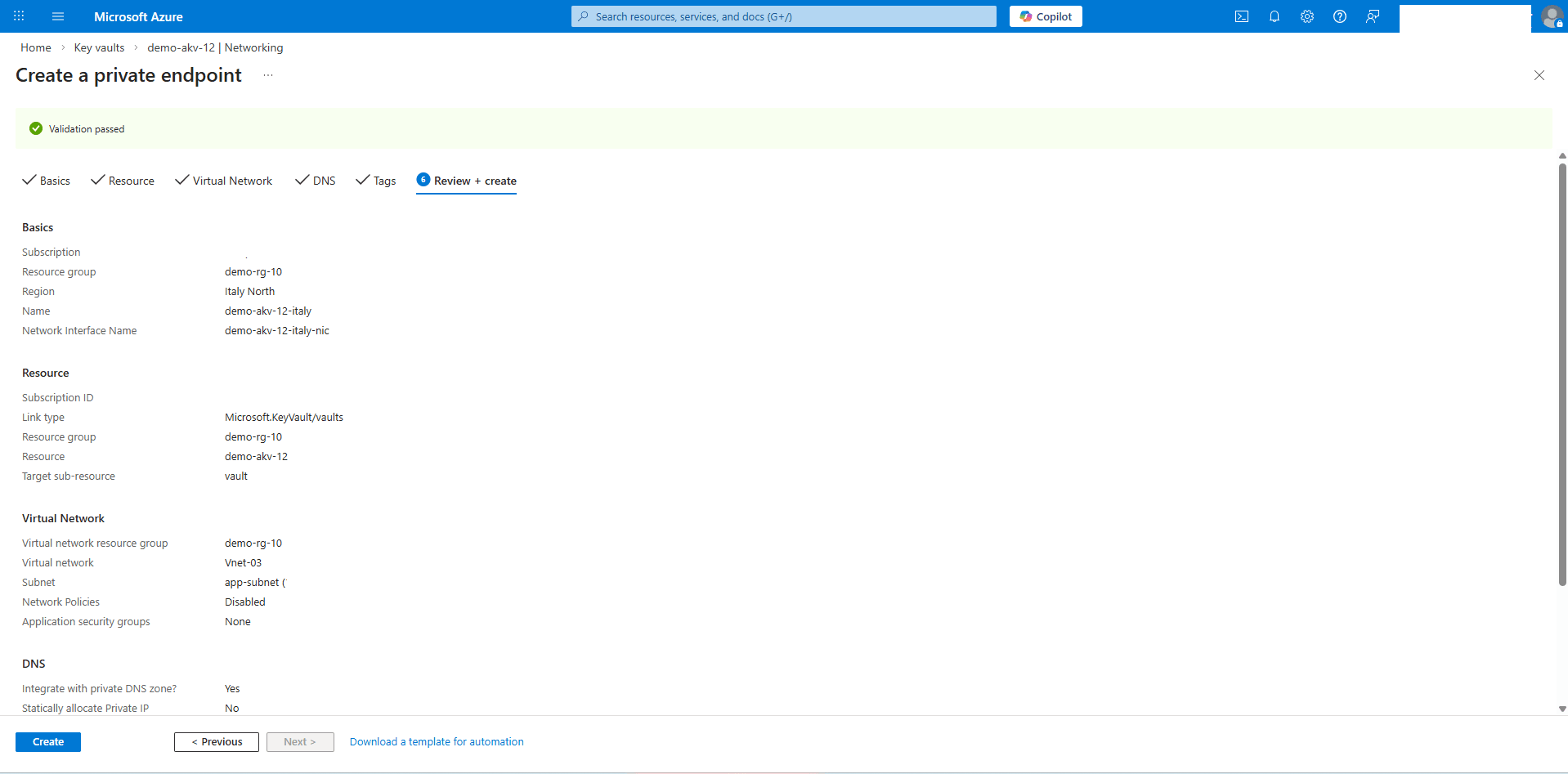
- In the Basics tab, enter the following information.
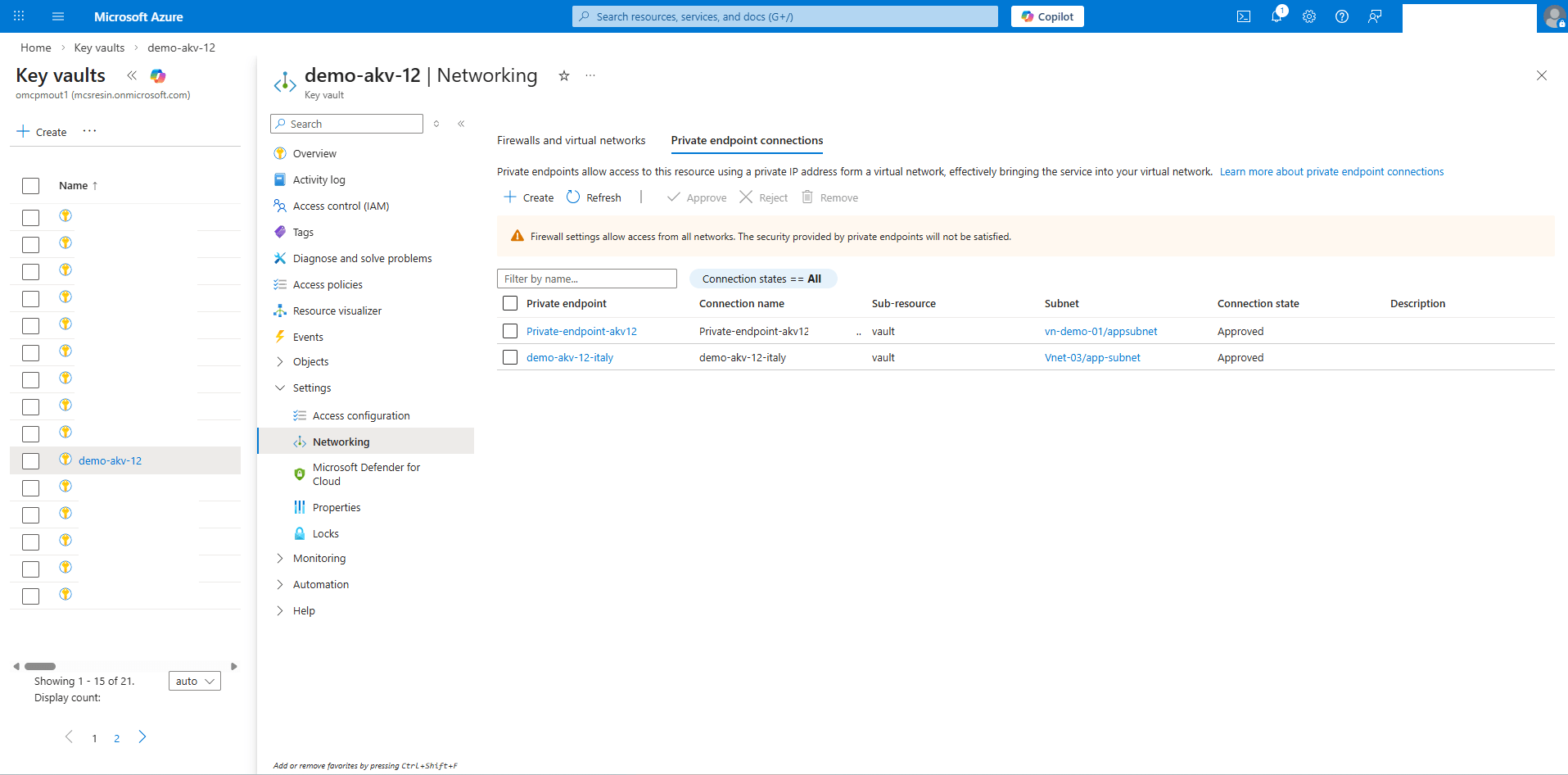
- Identify Azure Key Vault DNS Records from the Standby Private Endpoint
- From the Azure portal, select Key vaults and then select the Name field of the key vault that you replicated in the previous step.
- Expand the Settings section, and then select Networking.
- Select the Private endpoints connections tab, then select name field of the Private endpoint that you previously for the Standby region.
- From the left menu, expand the Settings section, and then select DNS configuration. Take a note of the FQDN and IP addresses information.
- Configure Private DNS Resolution for Azure Key Vault in OCI Standby Region
Complete the steps outlined in the step 7 to add the Private Azure Key Vault DNS Zones, using the Standby Endpoint information that you previously obtained.
Note
If the DNS Zone already exists in your environment, add the record to your existing Private Zone. - Configure Cross-Region Data Guard on Exadata Database in Oracle AI Database@Azure
For step-by-step instructions to configure Oracle Data Guard on an Exadata Database, see Configure Oracle Data Guard on Exadata Database in Oracle AI Database@Azure.
- Enable Advanced Network Features