3 Migrate Your Oracle Visual Builder Instances to Oracle Cloud Infrastructure
Migrate Oracle Visual Builder Traditional Cloud Account instances to Oracle Cloud Infrastructure.
Create Your Service Instance
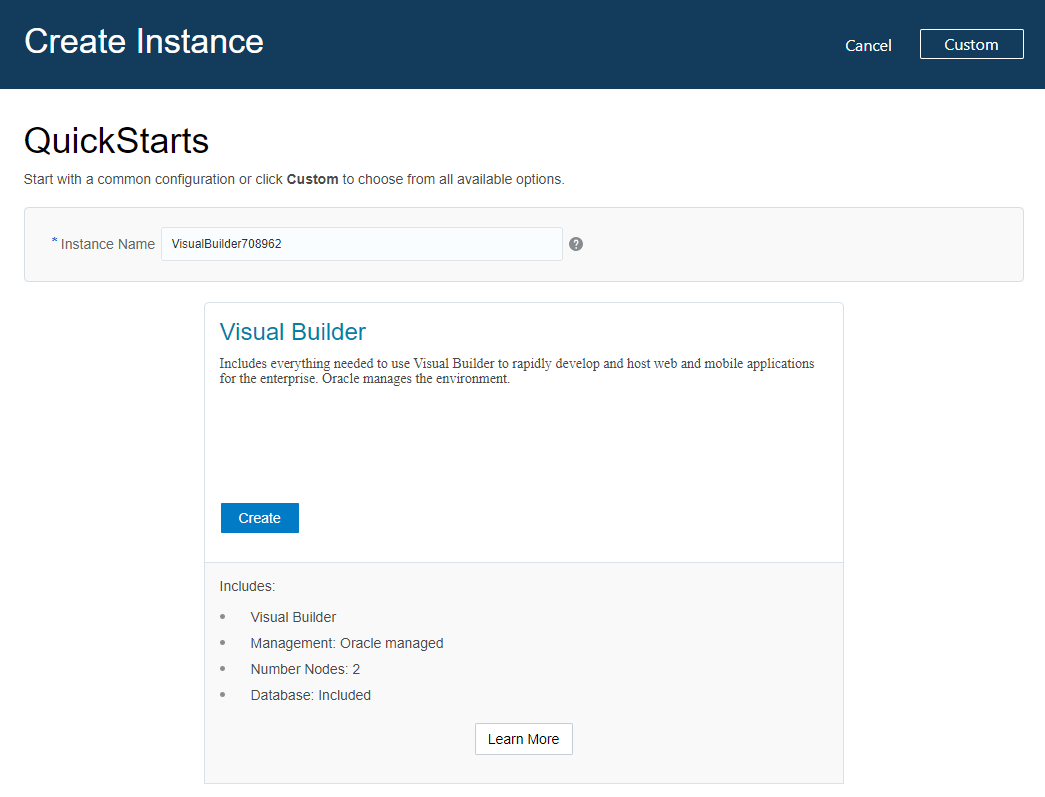
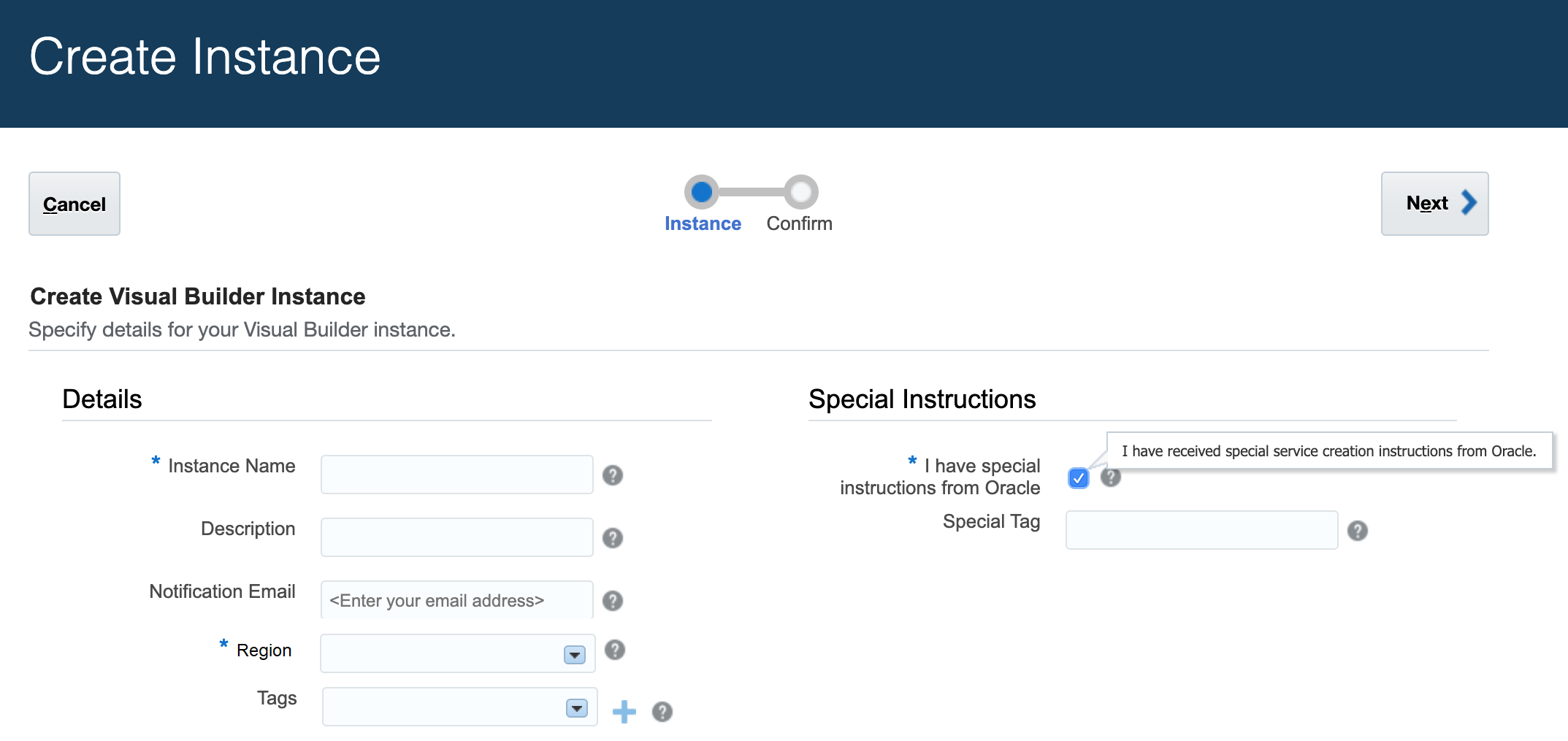
After subscribing to Oracle Visual Builder, you can provision instances of Oracle Visual Builder using the Quick Start or using the custom template.
Create a QuickStart Instance with a Single Click
After you sign up for your Oracle Cloud account and your services are available, you can create a QuickStart instance of Oracle Visual Builder with a single click from the Oracle Visual Builder console. A QuickStart instance does not include or support the creation of an Oracle Storage Cloud Service container. Without a container, database backups are not possible.
When your services are available, a link for creating a new instance is provided in the Oracle Visual Builder console. If you have already created some services for your account it might be more convenient for you to access the page for creating instances from the Dashboard in the Oracle Visual Builder console.
This QuickStart template automatically creates an instance with the following features:
-
Oracle Visual Builder.
-
Oracle-managed instance.
-
Two-node cluster.
-
An embedded database.
This instance does not include or support the use of an Oracle Storage Cloud Service container. On the overview page for the provisioned instance there is no Backup tab.
To create new instances using QuickStarts:
Migrate Users and Roles from Traditional Cloud Accounts’ Identity Management Systems
Traditional cloud account instances use different identity management services to those used by instances on Oracle Cloud Infrastructure.
As part of the migration process, you migrate users and roles so that users can access their Oracle Visual Builder instance on Oracle Cloud Infrastructure. The tasks to complete depend on the current identity management solution that you use with your traditional cloud account.
If you use shared identity management (SIM) to manage users and roles in the traditional cloud account, migrate users and roles to Oracle Identity Cloud Service as described in Migrating from Traditional Cloud Accounts to Cloud Accounts with Identity Cloud Service.
An alternative identity management implementation is where your traditional cloud account extends an Oracle Fusion Applications Cloud Service and federated single sign-on manages users maintained in the Oracle Fusion Applications Cloud Service’s identity provider that synchronizes user details to your traditional cloud account that uses SIM. Reconfigure your implementation so that user details can be synchronized to the Oracle Identity Cloud Service that Oracle Visual Builder instances on Oracle Cloud Infrastructure use. The tasks you need to complete depend on your current implementation. A starting point to identifying these tasks is to review the Learn About Federated SSO for Oracle PaaS with Oracle Fusion Applications Cloud Service article.
Manage Instance Settings
After your new instance is created, you configure the instance's settings to match the settings of the Oracle Visual Builder Traditional Cloud Account instance.
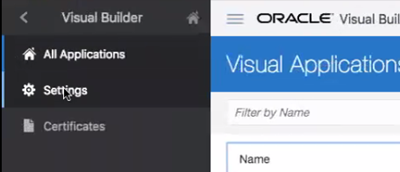
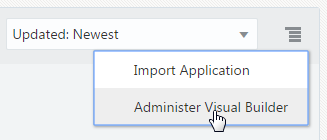
Access Instance Settings
Administrators can access a page for managing the instance’s global settings. The settings page contains panels for configuring security settings, specifying Access Denied messages and specifying Oracle Process Cloud Service details.
You can access the instance settings page from any Visual Builder page, but the steps for opening the page will depend on if you are developing visual applications or classic applications.
To open an instance’s settings page:
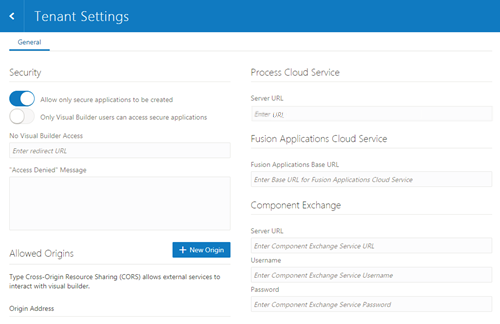
Description of the illustration admin-instance-tenant-settings.png
Configure Security Options for Applications
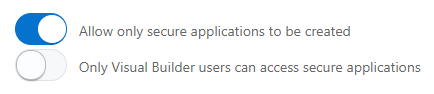
Administrators can use the Security panel in the settings page to require authentication for all applications in the instance.
When an administrator enables the Allow only secure applications to be created option, all published and staged applications in the instance will require user authentication. When the option is enabled, users must be assigned a role by the identity domain administrator and log in to access an application. When the option is not enabled, applications can be created that allow access to anonymous users.
When an application has the default security settings, any user with a valid login can access the pages in an application. A developer can modify the default security settings to define the roles that can access applications, pages and components. When the secure application option is enabled, an administrator can enable an option that users must be assigned the role of Visual Builder User in addition to any other roles used to secure access to staged and published applications. For example, security can be configured so that users assigned the role Visual Builder Developer can access the designer but can’t access the published application and data because they are not assigned the role Visual Builder User.
To block access by anonymous users to all applications in the instance:
Set Page Messages for Access Denied Errors
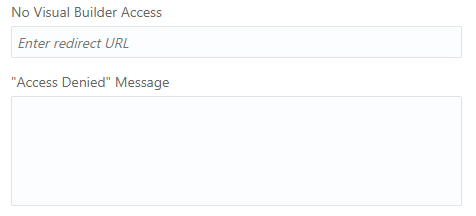
Administrators can use the instance’s settings page to specify a URL that users are navigated to when they are denied access to an application or page.
Authenticated users might see an Access Denied page or message when they attempt to access an application or page in an application that their user role is not permitted to access. Administrators can set the default page or message that users see when they are denied access to an application or page. Access Denied messages that are set at the application level in the General Settings of an application will override messages set in the instance’s settings page. The default Access Denied page and message is used if the message options in this panel are not set.
To specify an Access Denied page or message for applications in the instance:
Allow Other Domains Access to Services
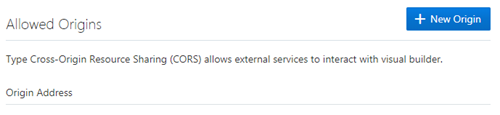
Use the Global Settings page to specify the domains that are permitted to interact with services in your instance.
Cross-Origin Resource Sharing (CORS) is a mechanism that enables you to specify the domains that are allowed to exchange data with applications in your instance. By default, incoming requests from domains not on your instance’s list of allowed origins are blocked from accessing application resources.
To add a domain to the list of allowed origins:
Add a Connection to Process Cloud Service
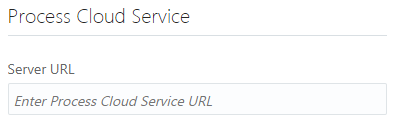
Administrators can use the instance’s settings page to add a connection to an Oracle Process Cloud Service instance.
If you are using multiple Visual Builder instances, for example, development and production instances, you might need to add connections to Oracle Process Cloud Service in more than one instance.
To add a connection to an Oracle Process Cloud Service instance:
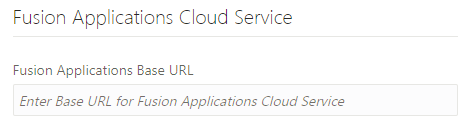
Add a Connection for Fusion Applications Services
The list of REST services in the service catalog of visual applications is retrieved from a Fusion Applications service. The URL of the Fusion Applications service can be specified in the Tenant Settings dialog box or in the Settings dialog box of a visual application.
All visual applications in the tenant space will use the Fusion Applications base URL specified in Tenant Settings, but a visual application can be configured to use a different Fusion Applications service by specifying its URL in the application’s Settings dialog box. The URL in Tenant Settings is ignored if a URL is specified in a visual application’s Settings dialog box.
To specify a Fusion Applications service for the tenant:
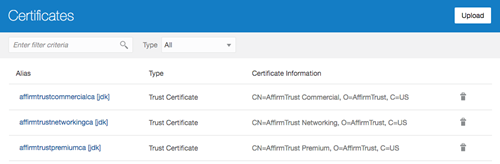
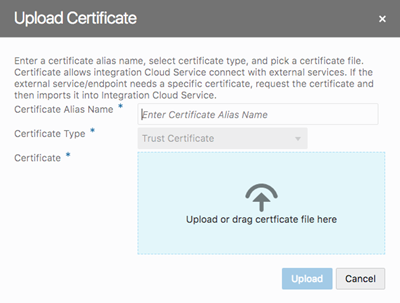
Manage Self-signed Certificates
Administrators can use the Certificates page to upload and manage the self-signed certificates used by the instance to enable inbound and outbound SSL communications to a service’s REST APIs
When creating connections to REST services that use self-signed certificates, you might need to add an API’s certificate to your Visual Builder instance to validate SSL connections to that service. You can use the Certificates page to upload and remove certificate files (.pem) for services. Uploading a service’s certificate file to the keystore will allow all applications in the instance to communicate with that service. The Certificates page displays a list of certificates that have been added. You can click the Delete button in a row to remove the certificate.
To upload a self-signed certificate: