OAuth Authentication in Oracle Integration
Oracle Integration supports OAuth authentication with Authorization Code grant type. This type of authentication is used for client applications that can access a browser. You don't need to share user names and passwords with clients, or manage user passwords that expire.
Oracle Integration REST APIs, integrations with REST adapters, and integrations with application adapters exposing REST endpoints are protected using OAuth.
- OAuth Authorization Code Credentials Flow
- Key Points About OAuth
- Authorization Flow with OAuth in Oracle Integration
OAuth Authorization Code Credentials Flow
The following steps are performed as part of OAuth authorization code credentials flow.
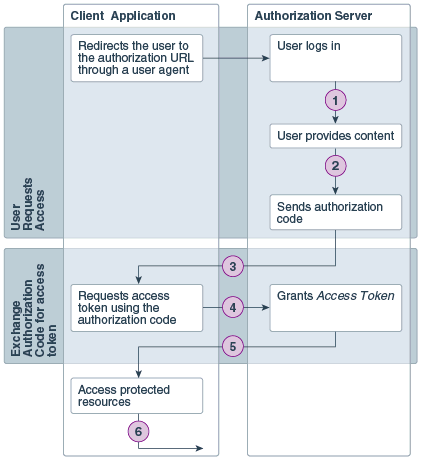
| Step | Description |
|---|---|
| 1 | The user specifies the authorization request URI. The user is redirected by the user agent (browser) to the authorization URI. |
| 2 | The resource owner logs in to authenticate and provide consent to the client application to access its resources. |
| 3 | The authorization server sends a callback request to the client application and sends the authorization code. |
| 4 | The client application extracts the authorization code from the request and uses it to send another request to the authorization server to get an access token. |
| 5 | The authorization server responds to the access token request by sending an access token to the client application. |
| 6 | The client application uses the access token to make requests for protected resources. |
Key Points About OAuth
-
The trusted application provides access to REST endpoints in Oracle Integration
You register a trusted application with Oracle Identity Cloud Service for each Oracle Integration instance. This trusted application provides access to the OAuth protected REST endpoints in Oracle Integration.
-
Clients use the trusted application client ID and secret
You provide clients with the client ID and client secret of your trusted application along with the Oracle Identity Cloud Service URL, and the Oracle Integration instance scope. The scope represents all the resources the trusted application can access. In the case of Oracle Integration, the scope provides access to all REST APIs and REST APIs exposed in integrations.
-
Clients get an authorization code and access token
With the information you provide clients, each client can request an authorization code and access token from Oracle Identity Cloud Service. The authorization code is short-lived. Once the client receives the authorization code, it exchanges the code for an access token. Each user has a different access token. The access token contains information about the client application and who the end user is.
-
Clients use the access token to access Oracle Integration REST APIs
The client application uses the access token it received from Oracle Identity Cloud Service to call Oracle Integration REST APIs or REST endpoints exposed in integrations.
-
Clients can refresh expired access tokens
If an access token expires, the client can refresh it. Access tokens expire after one hour by default, but you can change this in the trusted application configuration.
-
Identity Domain Administrators can revoke access tokens for users
If security issues arise, you can revoke the access token for a specific user.
Authorization Flow with OAuth in Oracle Integration
With OAuth, Oracle Identity Cloud Service is the identity provider and authorization server. Oracle Integration is the resource server.
The following table illustrates the OAuth authorization flow to use REST APIs in Oracle Integration.
Table -
| Client Application | Oracle Identity Cloud Service(Identity Provider and Authorization server) | Oracle Integration(Resource server) |
|---|---|---|
|
1. Request authorization code with client ID and secret |
|
|
|
|
2. Check client ID and secret, prompt for user name and password to access Oracle Integration. |
|
|
3. User logs in with user name and password used to access Oracle Integration. |
|
|
|
|
4. Check user credentials. If credentials are OK, return authorization code. |
|
|
5. Request access token by specifying authorization code. |
|
|
|
|
6. Validate and return access token. |
|
|
7. Use the access token to make API calls to Oracle Integration with the header |
|
|
|
|
|
8. Receive API calls and perform requested operations. |