2 Set Up the Service
Here’s what you need to know to get your team set up with Oracle Mobile Cloud Service (MCS), including activating the service, creating a service instance, and assigning team members. Be sure to go through this chapter carefully to make sure that you have fully configured the service for what your team needs.
Where Do I Sign Up?
If you haven't already purchased a subscription to Oracle Mobile Cloud Service (MCS) and would like to, you can do so in either of these ways:
-
Visit https://shop.oracle.com and enter Mobile Cloud Service into the Search field to display the purchase options.
-
Contact your sales representative. If you don’t know who that is, go to the Oracle Contact List and click Live Sales Chat.
You can purchase a metered or non-metered subscription. For an overview, see Overview of Oracle Cloud Subscriptions in Getting Started with Oracle Cloud.
You can also sign up for a trial by following these steps:
-
Navigate to https://cloud.oracle.com/en_US/tryit and click Get started for free.
-
Click Sign up.
-
Fill out the online form to create an Oracle account.
See Requesting a Free Oracle Cloud Promotion if you have any questions on how to fill out the form.
Once the request is approved, you will receive an email with details for logging in (and changing your password).
What Do I Need To Do?
| Task | Who Does It? | How Do I Do It? |
|---|---|---|
|
Activate the service and designate administrators |
Your company’s Oracle Cloud account administrator. This person is designated by your Oracle sales representative when you sign up with Oracle Cloud. |
|
|
Create one or more service instances (environments) and assign a service administrator |
For non-metered service, it is the account administrator or service administrator designated by the account administrator. For metered service, it is the service administrator. |
|
|
Assign MCS team member roles to define permissions |
A service administrator for the MCS environment. |
|
|
Set up mobile users, realms and roles |
A team member with the Oracle Cloud identity domain administrator role and the mobile user configuration ( |
|
|
Set up MCS for MAX |
Your company’s MCS service administrator. |
See Setting Up MAX Environments, Distinguishing Between MAX Team Member Roles for Business Users and for Mobile App Developers and Mobile Users for MAX |
|
Log in to MCS |
All MCS team members. |
See Get on Board |
Activate the Service
When your company submits an order for MCS, your sales representative designates an account administrator, who is the activator for the service. If you're that person, you’ll receive an activation email to get started. If this is your first time logging in to Oracle Cloud, you’ll be prompted to change your temporary password.
-
Open the activation email and click Cloud Account Services Setup.
If you have a non-metered subscription, you’ve subscribed to an entitlement to create service instances of MCS (environments), so your first task is to create those environments based on your business needs, described next in Create Mobile Environment Service Instances
If you have a metered subscription, your first task is to assign MCS roles to your team, described in Assign MCS Team Member Roles.
Create Mobile Environment Service Instances
MCS uses environments to define the behavior of artifacts and control access to development and administrative features. As an account or service administrator, you define these environments, assign predefined MCS team member roles, and configure environment policies. For example, if you have more than one environment, you could designate one as a development environment and one as a production environment.
-
Development could be an environment where you create your mobile backend, define your custom APIs, create new services using custom code, set up storage for your collections, and so on. It’s the primary environment where you’ll do most of your work.
-
Production could be a completely separate environment, into which you can promote your completed project code for testing or public access. Developers and team members with broad permissions and easy access to features in the development environment might have little or no access to a production (or staging) environment where specific testing can be done by another team. You could also further separate the production environment to promote fully tested code for use by applications.
To create your mobile environment service instances:
-
Open the welcome email you received after being assigned as the service entitlement administrator and click My Account.
You’ll be prompted to change your temporary password.
-
In the Oracle Cloud Infrastructure Classic Console, click the Create Instance button next to Mobile Cloud Service in the list of services and complete the wizard that appears.
Allow up to three hours for the instance to be created.
Upon creation of your first environment, an MCS Portal instance is also created and your environment is associated with it.
-
For any additional environments you want to create, repeat step 2 of this procedure and associate them with the MCS Portal instance using the Associations dropdown in the wizard.
If you need more detailed information on the wizard, see Creating Service Instances in Getting Started with Oracle Cloud.
Setting Up MCS Environments
- To assign team member roles, open the welcome email you received when you were assigned as service administrator and follow the link to Oracle Cloud My Services. From the Oracle Cloud Infrastructure Classic Console, click the navigation menu
 in the top left corner, and choose Users.
in the top left corner, and choose Users. - From the Users page you can assign team member roles for the environment as described in Assign MCS Team Member Roles.
- To monitor activity, access administrative features and define environment policies, go to MCS, click
 and open Administration from the side menu. For more information on using these features, see MCS Environments.
and open Administration from the side menu. For more information on using these features, see MCS Environments.
Setting Up MAX Environments
MAX (Mobile Application Accelerator) is a development tool that enables business users to create, test, and publish mobile apps without writing code. You can find out more about MAX and how it’s used in Creating APIs Fast with the Express API Designer.
-
A business user builds and tests apps in the MAX development environment. The
MobileEnvironment_BusinessUserrole in the development environment limits business users to the MAX UI only. MCS team members with theMobileEnvironment_Developrole in the environment also have access to MAX features. -
A business user or MCS team member can use MAX to publish apps by promoting them to the MAX production environment, making them available to other people in the organization. This requires the
MobileEnvironment_MAXApplicationDeployrole in the environment.
Tip:
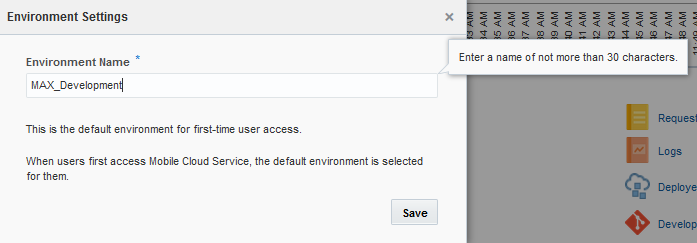
Instead of accepting the default names for the MAX development and production environments, choose names that make them easy to identify. You might consider a MAX-themed naming convention and choose simple names to help you associate MAX roles with the correct environment service instances.Assign MCS Team Member Roles
As a service administrator, you use the predefined MCS team member roles to grant permissions and capabilities to your team members in each environment. Team members and their roles are managed from Oracle Cloud Infrastructure Classic Console.
Note:
A service administrator can assign MCS roles to existing team members. To create new team members, you need to be assigned the identity domain administrator role in Oracle Cloud by the account administrator.As account administrator, be judicious about granting the identity domain administrator role. It’s required to create team members and mobile users, but it also grants broader permissions over your MCS instance in Oracle Cloud.
To add users and assign them roles:
-
Sign in to your Oracle Cloud account.
-
On the Oracle Cloud Infrastructure Classic Console, click the navigation menu
 in the top left corner, and choose Users.
in the top left corner, and choose Users.
-
For each team member, click Add and fill in the name, email, and other required information.
-
In the Simple Role Selection section, select roles for each user.
For development environments, it's generally a good idea to assign team members all of the MCS roles described below in development environments (except for the
MobileEnvironment_BusinessUserrole) to make sure that they can complete all of the development activities. (Use theMobileEnvironment_BusinessUseronly for team members you want to go straight to Mobile Application Accelerator (MAX) without seeing the rest of the MCS interface.)For production environments, most team members should have more limited access.
If you need more detailed instructions, see Adding Users and Assigning Roles in Getting Started with Oracle Cloud.
MCS Team Member Roles
MCS team member roles are predefined and can’t be created or customized. Team members must be assigned at least one of the roles in the table below in each environment they should have access to.
| Role Name | Privileges | Available Actions |
|---|---|---|
MCS Team Member (MobilePortal_TeamMember)
|
Access to the MCS UI. All team members.
The MCS UI is represented by an environment in Oracle Cloud, called the MCS UI service. All team members must be granted this role in the MCS UI service in addition to roles granted in other MCS environments. |
|
Mobile Analytics (MobileEnvironment_Analytics)
|
Read-only access to analytics data for the environment. |
|
Mobile Database Management (MobileEnvironment_DbMgmt)
|
Use the Database Management API to to view, create, and drop tables. |
|
Mobile Deploy (MobileEnvironment_Deploy)
|
Control artifact versions deployed within the environment and configure artifact policies and instance data. |
|
Mobile Develop (MobileEnvironment_Develop)
|
Create, configure and publish new artifacts, such as mobile APIs and custom code. Create and test mobile apps using MAX. This role is only useful in development environments. |
|
Mobile Location Management (MobileEnvironment_LocationMgmt)
|
Create, configure and delete location artifacts such as assets, devices and places so applications can query location data. |
|
Mobile System (MobileEnvironment_System)
|
Access the Location Management API from custom code. |
|
Mobile User Configuration (MobileEnvironment_MobileUserConfig)
|
Define realms and roles for mobile users so applications can use role-based access policies.
You must also be granted the role of identity domain administrator in Oracle Cloud to manage roles and realms. |
|
Mobile User Management (MobileEnvironment_MobileUserMgmt)
|
Manage mobile users within a realm, including creating mobile users and assigning roles.
You must also be granted the role of identity domain administrator in Oracle Cloud to manage users. |
|
Mobile Monitor (MobileEnvironment_Monitor)
|
Read-only access to diagnostics data for the environment. |
|
Mobile Notifications (MobileEnvironment_Notifications)
|
Send and receive notifications in the environment. |
|
Business User (MobileEnvironment_BusinessUser)
|
Access to the Mobile Application Accelerator (MAX) development UI. Blocks access to the rest of the MCS UI.
Never grant the Business User role to a MCS mobile app or service developer or assign it to a production environment. |
|
MAX Mobile App Deployment (MobileEnvironment_MAXApplicationDeploy)
|
Access to the MAX production environment and MAX application deployment features. |
|
The naming convention for Oracle Cloud roles that correspond to MCS team member roles is: {serviceName}.{rolename}. For example, in the environment with service name paid1247mobsvc002dev the name of the Oracle Cloud role for the MobileEnvironment_Deploy team member role would be paid1247mobsvc002dev.MobileEnvironment_Deploy. Service names for MCS environments are listed on the Oracle Cloud Infrastructure Classic Console.
You might see some extra roles in the list in Oracle Cloud, including a Mobile Team Management role in several environments and extra Mobile Monitor and Mobile User Management roles in the UI environment. You don’t need to assign those roles to anyone, as they aren’t used in this release.
Team member roles are different from the mobile user roles that you assign to end users of your apps. For details on mobile user roles, see Creating and Managing Mobile User Roles.
Distinguishing Between MAX Team Member Roles for Business Users and for Mobile App Developers
MAX (Mobile Application Accelerator) is a development tool for business users, but MCS mobile app and service developers can also use MAX to test custom code. You can find out more about MAX and how it’s used in Creating APIs Fast with the Express API Designer.
MobilePortal_TeamMember role to access the mobile portal, but these two types of users access MAX differently.
-
The
MobileEnvironment_BusinessUserrole must only be assigned to a business user in the MAX development environment so they can bypass the rest of MCS. Business users with this role are MAX-only users and can’t even see the MCS UI. Never assign this role to a MCS mobile app or service developer or to a production environment. -
The
MobileEnvironment_Developrole grants access to MAX from within the MCS UI. To make sure that MCS mobile app and service developers can open the Applications page and aren’t trapped in MAX, always assign them theMobileEnvironment_Developrole, and not theMobileEnvironment_BusinessUserrole. -
The
MobileEnvironment_MAXApplicationDeployrole in the MAX production environment enables both business users and MCS developers to publish apps using MAX. When this role is assigned, MAX is included on the Applications page for the environment.
To find out more about accessing MAX, see Who Uses MAX?
Example Team Member Role Assignments
MobilePortal_TeamMember role in the MCS UI service.
Caution:
When creating team member accounts for Mobile Application Accelerator (MAX), be sure to keep the roles and their associated environments straight. Do not grant the MAXBusinessUser role to MCS mobile app or service developers or they will be limited to the MAX UI and won’t have access to MCS development features. Also, the MAX development environment is identified by the MobileEnvironment_BusinessUser role, so take care when choosing the service instance name in the Oracle Cloud Infrastructure Classic Console. Do not assign this role to the MAX production environment.
| Job | Development Environment Roles | Staging Environment Roles | Production Environment Roles |
|---|---|---|---|
|
enterprise architect |
MobileEnvironment_Analytics, MobileEnvironment_DbMgmt, MobileEnvironment_Deploy, MobileEnvironment_Develop, MobileEnvironment_LocationMgmt, MobileEnvironment_System, MobileEnvironment_MobileUserConfig, MobileEnvironment_MobileUserMgmt, MobileEnvironment_Monitor, MobileEnvironment_Notifications |
MobileEnvironment_Analytics, MobileEnvironment_DbMgmt, MobileEnvironment_Deploy, MobileEnvironment_LocationMgmt, MobileEnvironment_System, MobileEnvironment_MobileUserConfig, MobileEnvironment_MobileUserMgmt, MobileEnvironment_Monitor, MobileEnvironment_Notifications |
MobileEnvironment_Notifications |
|
mobile cloud administrator |
MobileEnvironment_Analytics, MobileEnvironment_DbMgmt, MobileEnvironment_Deploy, MobileEnvironment_Develop, MobileEnvironment_LocationMgmt, MobileEnvironment_System, MobileEnvironment_MobileUserConfig, MobileEnvironment_MobileUserMgmt, MobileEnvironment_Monitor, MobileEnvironment_Notifications |
MobileEnvironment_Analytics, MobileEnvironment_DbMgmt, MobileEnvironment_Deploy, MobileEnvironment_LocationMgmt, MobileEnvironment_System, MobileEnvironment_MobileUserConfig, MobileEnvironment_MobileUserMgmt, MobileEnvironment_Monitor, MobileEnvironment_Notifications |
MobileEnvironment_Analytics, MobileEnvironment_DbMgmt, MobileEnvironment_Deploy, MobileEnvironment_LocationMgmt, MobileEnvironment_System, MobileEnvironment_MobileUserConfig, MobileEnvironment_MobileUserMgmt, MobileEnvironment_Monitor, MobileEnvironment_Notifications |
|
mobile app developer and service developer |
MobileEnvironment_Analytics, MobileEnvironment_DbMgmt, MobileEnvironment_Deploy, MobileEnvironment_Develop, MobileEnvironment_LocationMgmt, MobileEnvironment_System, MobileEnvironment_MobileUserConfig, MobileEnvironment_MobileUserMgmt, MobileEnvironment_Monitor, MobileEnvironment_Notifications, |
MobileEnvironment_Analytics, MobileEnvironment_MobileUserMgmt, MobileEnvironment_Monitor, MobileEnvironment_Notifications |
MobileEnvironment_Notifications, MobileEnvironment_MAXApplicationDeploy |
|
mobile program manager |
MobileEnvironment_Analytics, MobileEnvironment_DbMgmt, MobileEnvironment_Deploy, MobileEnvironment_Develop, MobileEnvironment_LocationMgmt, MobileEnvironment_System, MobileEnvironment_MobileUserConfig, MobileEnvironment_MobileUserMgmt, MobileEnvironment_Monitor, MobileEnvironment_Notifications |
MobileEnvironment_Analytics, MobileEnvironment_Notifications |
MobileEnvironment_Analytics, MobileEnvironment_Notifications |
|
business user |
MobileEnvironment_BusinessUser |
N/A | MobileEnvironment_MAXApplicationDeploy |
Remember, to create new team members or mobile users, a team member also needs to be granted the identity domain administrator role in Oracle Cloud.
Set Up Mobile Users, Realms and Roles
Mobile users are your customers — the ones who use the mobile apps built with MCS. Organize your mobile users by setting up realms that define the user schema, and creating roles to grant access permissions. It’s a good idea to define some realms and roles before app developers start working with MCS. You can also set up some initial mobile users for testing and maybe import larger groups of mobile users.
Note:
To manage mobile users, roles and realms, you need to be assigned the mobile user configuration (MobileEnvironment_MobileUserConfig) and mobile user management (MobileEnvironment_MobileUserMgmt) MCS team member roles in the environment, as well as the identity domain administrator role in Oracle Cloud.
Manage mobile users, realms and roles in MCS from Applications > Mobile User Management.
Creating Realms
-
user name
-
password
-
first name
-
last name
-
e-mail
- Make sure you're in the development environment where you want to create the realm.
- Click
 to open the side menu and select Applications > Mobile User Management.
to open the side menu and select Applications > Mobile User Management. - Click the Realms navigation link.
- To create a realm, click New Realm.
- Enter a unique name and an optional description. The realm name can’t be changed after the realm is created.
- If you want to add a custom property to the user schema, click New Field.
- When you’ve finished, click Save to save your changes to the realm and return to the Realms tab.
Setting the Default Realm for an Environment
- Make sure you're in the environment where you want to set the default realm.
- Click
 to open the side menu and select Applications > Mobile User Management.
to open the side menu and select Applications > Mobile User Management. - Click the Realms navigation link.
- Select the realm that you want to make the new default. Click More and select Make default realm.
Creating and Managing Mobile User Roles
Mobile user roles allow you to define permissions for your apps and assign them to mobile users. You can define as many roles as you need, and you can assign multiple roles to the same mobile user.
A mobile app can allow different access to mobile users with different roles. You could assign a Technician role to a mobile technician to grant access to specific features of the company's mobile app, and a Salesperson role to a sales rep to grant access to different features. The same mobile technician could have a Customer role in the company’s supply ordering app where the sales rep has no role assigned.
-
Make sure you're in the environment where you want to create the role(s).
-
Click
 to open the side menu and select Applications > Mobile User Management.
to open the side menu and select Applications > Mobile User Management.
Note:
Though it's possible to create and delete mobile user roles from My Services in Oracle Cloud, you should handle all operations on mobile user roles from Mobile User Management in the MCS UI. -
Click the Roles page. From here you can view and edit available mobile user roles and create new roles. As soon as you create a role, it’s added to the list on the Roles page and you can define access permissions.
-
Role names are case-sensitive.
-
Roles are deployed automatically with any object that references them.
-
-
Assign roles to individual mobile users from the Mobile Users page in MCS, or use Oracle Cloud to batch assign roles to groups of mobile users, described in Importing Groups of Mobile Users Into MCS Using Oracle Cloud.
-
Assign specific permissions for objects and resources to the roles you’ve defined, as described in Adding Access Permissions to a Collection.
-
Restrict access to APIs and individual methods, as described in Setting Access to the API.
Creating Mobile Users and Assigning Roles
Note:
In all cases, when you a create mobile users, they are sent a temporary password. The new users need to use this temporary password to log into the Oracle Cloud Infrastructure Classic Console, change the password, and set up their challenge questions before they can be recognized as an MCS mobile user.Creating Individual Mobile Users for Testing
You can use the MCS UI to create individual mobile users and assign roles. Here are the steps for quickly creating a test user. Some steps include suggested values that will allow app developers to seamlessly complete the Get Started with Mobile Development tutorial on the MCS home page.
-
Make sure you're in the environment where you want to create the mobile user(s).
-
Click
 to open the side menu and select Applications > Mobile User Management.
to open the side menu and select Applications > Mobile User Management.
-
Click Mobile Users.
-
Select the Realm where you want to create the user.
-
Click the New User button.
-
Enter a unique user name and fill in the remaining fields in the dialog, including an email address where you can retrieve the generated password.
The available fields may vary depending on the realm where you’re creating the user. The Get Started with Mobile Development tutorial uses the user nameJoe.Note:
Both user name and email address must be unique across all services in Oracle Cloud. -
If you haven’t created the role you need yet, you can add a new role to the environment by clicking Create Role on the right side of the dialog.
The Get Started with Mobile Development tutorial uses the role name
Technicianfor the user Joe. -
Click Create again to create the new mobile user.
An email is sent from Oracle Cloud to the address you entered with a temporary password.
-
(Optional) Assign roles to an individual mobile user from the Mobile Users page in MCS.
You can only assign a mobile user to one realm via the MCS Mobile Users page, but you can associate mobile users with multiple realms using Oracle Cloud. For more thorough testing or for production, you’ll also probably want to import a group of mobile users.
Importing Groups of Mobile Users Into MCS Using Oracle Cloud
You can use Oracle Cloud to import a group of users into MCS or assign MCS roles to a group of users, using the steps below. MCS mobile user realms and roles are both represented by custom roles in Oracle Cloud. As with all mobile user operations in this section, you need the identity domain manager role in Oracle Cloud to complete these steps.
-
Create the MCS realm and mobile user roles you want to assign to the group of users, if you haven’t already. For detailed instructions, see Creating Realms and Creating and Managing Mobile User Roles.
-
Create a group of mobile users in Oracle Cloud using a comma-separated values (CSV) file.
For detailed information on batch importing users, including the related CSV files, see Importing a Batch of User Accounts in Getting Started with Oracle Cloud.
-
Import the users into MCS by assigning the group to the Oracle Cloud custom role that represents the MCS realm you created in step 1.
The naming convention for Oracle Cloud custom roles that represent MCS realms is:
{serviceName}_MobileEnvironment_{realmname}_{version with dots as underscores}_Realmwhere{serviceName}is the service name of the environment in Oracle Cloud. You can find the service names for all MCS environments on the Oracle Cloud Infrastructure Classic Console. For example, for the default realm version 1.0 in the environment with service name “3240930apod” the custom role in Oracle Cloud would be3240930apod_MobileEnvironment_Default_1_0_Realm, or for the MyCustomers realm version 2.5 in the environment with service name “poeo342ed” it would bepoeo342ed_MobileEnvironment_MyCustomers_2_5_Realm. For detailed instructions, see Assigning One Role to Many Users in Getting Started with Oracle Cloud. -
(Optional) Assign MCS mobile user roles to the group by assigning Oracle Cloud custom roles using the same process you did for the realm in the previous step.
The naming convention for Oracle Cloud custom roles that represent MCS mobile user roles is:
{serviceName}_MobileEnvironment_{rolename}. For example, for a role named “APIRole” in the environment with service name “poeo342ed” the custom role in Oracle Cloud would bepoeo342ed_MobileEnvironment_APIRole.
Mobile Users for MAX
| Role | Definition |
|---|---|
| test user | A test user account enables MAX users to preview apps using live data. It also enables them to generate the QR code that identifies the test version of an app. For more information on creating a test user account, see Creating Individual Mobile Users for Testing. |
| mobile user | Mobile user accounts enable everyone (business users, MCS developers, and mobile app users) to log in to MAX and use published mobile apps. Anyone who tests or uses a mobile app built using MAX needs a mobile user account. For more information, see Importing Groups of Mobile Users Into MCS Using Oracle Cloud. |
Changing a Mobile User Password
- Click
 to open the side menu and select Applications > Mobile User Management.
to open the side menu and select Applications > Mobile User Management. - Click Mobile Users.
- Select the mobile user on the Mobile Users page and click the Reset password button. MCS will send an email with a temporary password to the email address associated with the user.
Configuring Identity Management (SSO and OAuth)
-
If you want to use a third-party IdP as your identity store (without any corresponding accounts for your users in Oracle Cloud), you can use SAML and JWT tokens for authentication. See Third-Party SAML and JWT Tokens.
-
If you want to use a third-party IdP in conjunction with Oracle Cloud user accounts, configure the connection between Oracle Cloud and the identity provider from the Users page in Oracle Cloud Infrastructure Classic Console. For detailed instructions, see Managing Single Sign On in Administering Oracle Cloud Identity Management.
Configuring Oracle Cloud Applications as the Identity Provider
If your team will be creating mobile apps that are designed for users of Fusion Applications-based services such as Oracle Sales Cloud, Oracle HCM Cloud, and Oracle ERP Cloud, you will probably want to enable those users to sign in to the mobile app once and not have to re-enter credentials to access the Oracle Cloud application.
For your mobile app and service developers to be able to create such apps where the user only needs to sign in once, you need to get the following things in place:
-
Have your MCS instance provisioned in the same identity domain as the Oracle Cloud application service that your apps will access.
-
Enable SSO for the identity domain and set the Oracle Cloud application service as the identity provider.
-
Enable sign—on with identity domain credentials. This enables team members to sign in with their Oracle Cloud credentials. Otherwise, they would be prompted to log in with credentials for the Oracle Cloud application service (which they might not have).
The steps for this are:
-
In Oracle Cloud Infrastructure Classic Console, go to the SSO Configuration page.
-
Go to the Enable Sign In to Oracle Cloud Services with Identity Domain credentials section and click Enable.
-
Note:
You can only designate one identity provider to be used with SSO.Once the services are set up in the same identity domain and SSO has been enabled, the mobile app developer can do the following to enable the app user’s login credentials to propagate to the Oracle Cloud application:
-
Create a Fusion Applications connector API to connect to the Oracle Cloud application service.
-
Within the connector API, designate the appropriate security policy to handle authentication and authorization with the service.
-
Create a custom API that calls the connector API.
-
Create a mobile backend, enable it to use SSO, and associate the custom API with it.
Get on Board
Once you’re assigned a role in MCS, you can log in and get to work. To open MCS from the Oracle Cloud Infrastructure Classic Console, click the Open Service Console link in the MobilePortalService box. (This link is only accessible to team members with administrative roles.)
Note:
If you see an error when you try to access MCS, you probably don’t have all the roles you need. Ask your service administrator to assign you the necessary MCS roles.