Creating Policies for BYOK Access
Create Identity and Access Management (IAM) policies to allow Oracle Fusion Cloud Enterprise Performance Management to access your Oracle Cloud Infrastructure (OCI) Vault and encryption keys.
These policies do the following:
- Allow Cloud EPM database resources to access vaults and keys using instance principals
- Enable secure integration between Cloud EPM and OCI Vault for Bring Your Own Key (BYOK)
Prerequisites
Ensure you have the following information from Oracle (provided via your service request):
- EPM Cloud tenancy OCID
- Database dynamic group OCID
- Instance principal dynamic group OCID
Creating Policies for BYOK Access
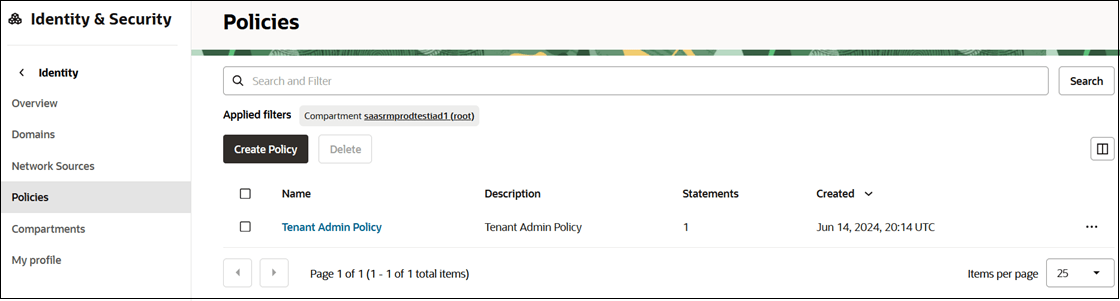
To create policies:- Go to the Navigation menu, search for Identity, and select
Policies.
- Click Create Policy.
Note:
These policies must be created in the root compartment, regardless of which compartment the vaults are created in. - In the Create Policy page:
- Enter a Name and a Description for the policy.
- Select Manual Editor (instead of Policy Builder).
- In the Policy Builder, enter the policy statements. See Policy Statements.
- Click Create.
Policy Statements
Case 1: Vault and Keys in Root Compartment
Enter the following statements:
define tenancy EPM-Tenancy as '<EPM tenancy OCID>'
define dynamic-group adb-dg as '<DB dynamic group OCID>'
define dynamic-group instancePrincipal-dg as '<Instance Principal dynamic group OCID>'
admit dynamic-group adb-dg of tenancy EPM-Tenancy to use vaults in tenancy
admit dynamic-group adb-dg of tenancy EPM-Tenancy to use keys in tenancy
admit dynamic-group instancePrincipal-dg of tenancy EPM-Tenancy to read keys in tenancy
admit dynamic-group instancePrincipal-dg of tenancy EPM-Tenancy to read vaults in tenancyCase 2: Vault and Keys in a Sub-Compartment
If vaults and keys are not in root compartment, replace in
tenancy with:
in compartment <compartment_name>
Example:
define tenancy EPM-Tenancy as '<EPM tenancy OCID>'
define dynamic-group adb-dg as '<DB dynamic group OCID>'
define dynamic-group instancePrincipal-dg as '<Instance Principal dynamic group OCID>'
admit dynamic-group adb-dg of tenancy EPM-Tenancy to use vaults in compartment <compartment_name>
admit dynamic-group adb-dg of tenancy EPM-Tenancy to use keys in compartment <compartment_name>
admit dynamic-group instancePrincipal-dg of tenancy EPM-Tenancy to read keys in compartment <compartment_name>
admit dynamic-group instancePrincipal-dg of tenancy EPM-Tenancy to read vaults in compartment <compartment_name>