2 Introducing Oracle Audit Vault and Database Firewall
To begin using Oracle Audit Vault and Database Firewall (Oracle AVDF), perform preliminary tasks, such as downloading the latest version of this manual and understanding the basic Oracle AVDF concepts.
2.1 Downloading the Latest Version of This Manual
Learn how to download the latest documentation for Oracle Audit Vault and Database Firewall.
Download the latest version of this manual from the following website:
https://docs.oracle.com/en/database/oracle/audit-vault-database-firewall/20/sigad/index.html
Find documentation for other Oracle products at the following website:
2.2 Learning About Oracle Audit Vault and Database Firewall
Understanding the basic concepts of Oracle Audit Vault and Database Firewall is key to a successful Oracle AVDF deployment.
Oracle recommends that you read Oracle Audit Vault and Database Firewall Concepts Guide to understand the features, components, users, and deployment procedures of Oracle AVDF.
2.3 Supported Platforms for Oracle Audit Vault and Database Firewall
You can run Oracle Audit Vault and Database Firewall on various platforms.
Oracle Audit Vault and Database Firewall (Oracle AVDF) consolidates activity audit data from Oracle and non-Oracle databases, operating systems, and directories. It provides security and compliance reports through an accurate SQL grammar based engine. Database Firewall monitors SQL traffic and blocks unauthorized SQL.
See Oracle Audit Vault and Database Firewall Installation Guide for detailed platform support for the current release.
2.4 Oracle Audit Vault and Database Firewall System Features
Learn about the system features of Oracle Audit Vault and Database Firewall.
Topics
2.4.1 About Oracle Audit Vault and Database Firewall
Oracle Audit Vault and Database Firewall (Oracle AVDF) protects your IT infrastructure by monitoring activity, blocking intrusion attempts, collecting audit data, enacting customizable firewall rules, and assessing Oracle database configuration.
Oracle AVDF secures databases and other critical components of your IT infrastructure, such as operating systems, in the following ways:
- Provides a database firewall that monitors activity and can block SQL statements on the network based on your firewall policy.
- Collects audit data and presents the data in audit reports.
- Enables you to proactively configure alerts and notifications.
This section provides a brief overview of the administrative and auditing features of Oracle AVDF.
Oracle AVDF auditing features are described in detail in Oracle Audit Vault and Database Firewall Auditor's Guide.
We strongly recommend that you read Oracle Audit Vault and Database Firewall Concepts Guide for more information on the features, components, users, and deployment of Oracle AVDF.
2.4.2 Security Technical Implementation Guides for Oracle Audit Vault and Database Firewall
Oracle Audit Vault and Database Firewall (Oracle AVDF) is compliant with the Security Technical Implementation Guides (STIG) standards.
To learn about Oracle AVDF compliance with STIG standards see the Security Technical Implementation Guides.
2.4.3 System Requirements for Oracle Audit Vault and Database Firewall
Read about the Oracle AVDF hardware and software requirements.
For hardware and software requirements, see Oracle Audit Vault and Database Firewall Installation Guide.
2.4.4 Supported Targets for Oracle Audit Vault and Database Firewall
Learn about Oracle Audit Vault and Database Firewall targets.
A target is a database or non-database product that you secure using either the Audit Vault Agent, the Database Firewall, or both. If the target, whether or not it is a database, is supported by the Audit Vault Agent, then you can deploy the Agent on that target's host computer and collect audit data from the internal audit tables and operating system audit files. If the target is a database, then you can monitor or block its incoming SQL traffic with Database Firewall.
Oracle Audit Vault and Database Firewall supports various target products out of the box in the form of built-in plug-ins.
See Also:
-
Plug-In Reference for detailed information on each plug-in.
-
Table C-1 for supported target products and versions.
-
Table C-22 for the data collected and platforms supported for each audit trail type.
-
Configuring Quick JSON Target Type to Collect Audit Data from MongoDB
-
Oracle Audit Vault and Database Firewall Developer's Guide for information on creating custom plug-ins to capture audit trails from more target types using the Oracle AVDF SDK.
2.4.5 Oracle Audit Vault and Database Firewall Administrative Features
You can use Oracle Audit Vault and Database Firewall administrative features to manage targets and their hosts, firewalls, and other features.
You can use Oracle Audit Vault and Database Firewall administrative features to configure and manage the following:
-
Targets
-
Database Firewalls
-
High Availability
-
Third party integrations
-
Audit Vault Agent deployment
-
Audit trail collection
-
Audit data lifecycle, archiving, and purging
-
Microsoft Active Directory or OpenLDAP
2.4.6 Oracle Audit Vault and Database Firewall Auditing Features
Learn about Oracle Audit Vault and Database Firewall auditing features.
Oracle Audit Vault and Database Firewall auditing features enable you to configure and manage the following:
-
Firewall policies
-
Audit policies for Oracle Database
-
Reports and report schedules
-
Entitlement auditing for Oracle Database
-
Stored procedure auditing
-
Alerts and e-mail notifications
- Security assessment and drift management
See Also:
Oracle Audit Vault and Database Firewall Auditor's Guide for detailed information about these auditing features
2.4.7 Integrating Oracle Audit Vault and Database Firewall with Oracle Key Vault
You can integrate Oracle Audit Vault and Database Firewall with Oracle Key Vault.
Oracle Key Vault events are collected by Oracle Audit Vault and Database Firewall.
See Oracle Key Vault Administrator's Guide for instructions about integrating Oracle Key Vault with Oracle Audit Vault and Database Firewall
2.5 Separation of Duties
Oracle Audit Vault and Database Firewall offers multiple roles as part of the separation of duties between auditors and administrators.
To provide greater security, the Oracle Audit Vault and Database Firewall administrator and auditor roles have different user interfaces, and different user accounts. This separation of interfaces and accounts ensures that there is a separation of duties between these two roles. In addition to these Oracle Audit Vault and Database Firewall user accounts, you can also set up user accounts on your targets as necessary to access targets for collecting audit data. This is needed by the Audit Vault Agent for connecting to the target and collecting the audit data from the audit trails. Oracle Audit Vault and Database Firewall provides scripts to set up these user accounts on database targets, and guidance for other types of targets.
The following table shows the user accounts in Oracle Audit Vault and Database Firewall.
Table 2-1 Oracle Audit Vault and Database Firewall User Accounts
| Account | Description |
|---|---|
|
Super Administrator |
Super administrators configure and maintain the Oracle Audit Vault and Database Firewall system, including Audit Vault Server settings such as network settings, high availability, data retention policies, etc. The super administrator can create other administrators or super administrators, and has access to all targets. The super administrator can also grant access to specific targets to other administrators. |
|
Administrator |
The administrator can perform a subset of the system configuration tasks that a super administrator can, such as registering hosts and targets, running archive jobs, etc. Administrators can also manage targets for which they have been granted access by a super administrator. An administrator cannot create another administrator. This can be performed by a super administrator only. |
|
Super Auditor |
The super auditor can create firewall policies, provision audit policies for Oracle Database targets, and specify settings for target such as whether to enable stored procedure auditing. Super auditors also generate reports, and create alerts and notifications. The super auditor can access all targets, create auditor or super auditor users, and grant access to specific targets to those users. |
|
Auditor |
Auditors can perform all the functions of super auditors, but only for the targets to which they have access. |
Additional accounts are provided for diagnostics and used under the guidance of Oracle Support.
2.6 Understanding the Administrator's Role
Oracle AVDF administrators can configure system settings, create connections and targets, deploy agents, configure audit trails, and more.
Oracle AVDF Administrator Tasks
As an Oracle Audit Vault and Database Firewall administrator, your tasks include:
- Configuring the system settings on Audit Vault Server.
- Configuring connections to host computers on which you deployed Audit Vault Agent. This is usually the same computer as your targets.
- Creating targets on Audit Vault Server for each database or operating system that you are monitoring.
- Deploying and activating Audit Vault Agent on target host computers.
- Configuring audit trails for targets that Audit Vault Agent monitors.
- Configuring Database Firewall on your network.
- Creating Database Firewall monitoring points for targets.
- Backing up and archiving audit and configuration data.
- Creating administrative users and managing access (super administrator only).
- Configuring Microsoft Active Directory or OpenLDAP.
- Creating high availability for Audit Vault Server.
Administrator Roles in Oracle AVDF
There are two Oracle AVDF administrator roles with different target access levels:
-
Super Administrator - This role can create other administrators or super administrators, has access to all targets, and grants access to specific targets and groups to an administrator.
-
Administrator - Administrators can only see data for targets to which they have been granted access by a super administrator.
2.7 Planning Your Oracle Audit Vault and Database Firewall System Configuration
Learn about planning your system configuration for Oracle AVDF.
2.7.1 Guidance for Planning Your Oracle Audit Vault and Database Firewall Configuration
Learn about the steps for planning your Oracle Audit Vault and Database Firewall configuration.
The steps in this section summarize the planning steps with links to specific instructions in this user guide.
See Also:
Oracle Audit Vault and Database Firewall Concepts Guide for guidance on planning deployments of Oracle Audit Vault Server, Oracle Audit Vault Agent, and Oracle Database Firewall.
2.7.2 Step 1: Plan Your Oracle Audit Vault Server Configuration
Plan your Oracle Audit Vault Server configuration.
In this step, plan whether to configure a resilient pair of servers, whether to change the network configuration settings that were made during the installation, and how to configure optional services.
See Also:
-
Configuring Audit Vault Server for information on the Oracle Audit Vault Server configuration settings.
-
High Availability in Oracle AVDF for information about setting up resilient pairs of Oracle Audit Vault Servers.
-
Integrating Oracle Audit Vault and Database Firewall with Microsoft Active Directory or OpenLDAP for authenticating users connecting to the Audit Vault Server console.
2.7.3 Step 2: Plan Your Oracle Database Firewall Configuration
Learn how to plan your Oracle Database Firewall configuration.
If you are using Oracle Database Firewall, then plan how many you need, which target databases they will protect, where to place them in the network, whether they will be for monitoring only or for monitoring and blocking mode, and whether to configure a resilient pair of firewalls. Also plan whether to change the Oracle Database Firewall network configuration that was specified during installation.
Following are the list of activities you would like to review:
-
Overview of Oracle Database Firewall Deployment for information on different deployment types available.
-
Configuring Database Firewall for information about the Oracle Database Firewall configuration settings.
-
High Availability in Oracle AVDF for information on setting up resilient pairs of firewalls.
2.7.4 Step 3: Plan Your Oracle Audit Vault Agent Deployments
If you're deploying the Audit Vault Agent, determine the targets for which you want to collect audit data and identify their host computers.
You register these hosts with Oracle Audit Vault and Database Firewall (Oracle AVDF) and deploy the Audit Vault Agent on each of them. Then you register each target in the Audit Vault Server.
Note:
Starting in Oracle AVDF 20.9, you can use agentless collection instead of the Audit Vault Agent for up to 20 Oracle Database table audit trails. Starting in Oracle AVDF 20.10, you can also use agentless collection for Microsoft SQL Server directory audit trails for.sqlaudit and .xel (extended events). The
total number of audit trails for agentless collection should not exceed 20. See Adding Audit Trails with Agentless
Collection.
2.7.5 Step 4: Plan Your Audit Trail Configurations
If you're deploying the Audit Vault Agent or using agentless collection (Oracle AVDF 20.9 and later) to collect audit data, then you need to configure audit trails.
Use these guidelines to plan audit trail configurations for the targets from which you want to extract audit data. The type of audit trail that you select depends on the target type, and in the case of an Oracle Database target, the type of auditing that you've enabled in Oracle Database.
To plan the target audit trail configuration:
2.7.6 Step 5: Plan for High Availability
Learn how to plan for high availability.
In this step, consider the high availability options that are outlined in "High Availability in Oracle AVDF".
2.7.7 Step 6: Plan User Accounts and Access Rights
Learn how to plan your user accounts and their access rights.
As a super administrator, you can create other super administrators and administrators. Super administrators can see and modify any target. Administrators have access to the targets that you enable them to access. In this step, determine how many super administrators and administrators you create accounts for, and to which targets the administrators will have access.
See Also:
2.8 Summary of Configuration Steps
Learn about the Oracle AVDF configuration steps.
With Oracle AVDF, you can deploy Oracle Audit Vault Agent, Oracle Database Firewall, or both. This section suggests the high-level steps for configuring Oracle AVDF when you are:
2.8.1 Configuring Oracle Audit Vault and Database Firewall and Deploying the Agent
Use this procedure to configure Oracle Audit Vault and Database Firewall (Oracle AVDF) and deploy the Audit Vault Agent or configure agentless collection (Oracle AVDF 20.9 and later).
After you configure the system as an administrator, the Oracle AVDF auditor creates and provisions audit policies for targets and generates various reports.
2.8.2 Configuring Oracle Audit Vault and Database Firewall and Deploying Oracle Database Firewall
Configure and deploy Oracle Audit Vault and Database Firewall to enable you to create firewall policies and assign them to the targets.
After configuring the system as administrator, the Oracle Audit Vault and Database Firewall auditor creates firewall policies and assigns them to the targets. Your role and tasks as an auditor are described in Oracle Audit Vault and Database Firewall Auditor's Guide.
2.9 Using Audit Vault Server Console
Learn how to log in and use Audit Vault Server console.
2.9.1 Log in to Audit Vault Server Console
Learn how to log in to Audit Vault Server console.
When you first log in after installing Audit Vault Server:
- you must set up a password for root user
- create a super administrator or super auditor
See Also:
Oracle Audit Vault and Database Firewall Installation Guide for information on post-installation tasks.
To log in to Oracle Audit Vault Server Console:
2.9.2 Log in to Database Firewall Console
Learn how to log in to Database Firewall Console.
Starting with Oracle Audit Vault and Database Firewall release
20.1.0.0.0, you can perform Database Firewall related tasks on
the Audit Vault Server console.
- Log in to Audit Vault Server console.
- Click the Database Firewalls tab on the main page.
As administrator, use the Database Firewalls tab in the Audit Vault Server console to configure the network, services, and system settings for Database Firewall. You can also use the console to identify the Audit Vault Server that manages each firewall instance, to configure network traffic sources, monitor, and block threats to your target databases.
See Also:
Configuring Database Firewall for detailed information on configuring the Database Firewall using the Audit Vault Server console.
2.9.3 Understanding the Tabs and Menus in Audit Vault Server Console
Audit Vault Server Console tabs and menus enable you to see statuses for Agents, audit trails, targets, and more.
Oracle Audit Vault Server Console includes the following six tabs:
-
Home - Displays a dashboard showing high-level information and status for:
- System Alerts
- Targets
- Audit Collection
- Database Firewall Monitoring
- Collection summary
- Jobs summary
- Data Retention summary
- System overview
-
Targets - Provides menus for registering targets, managing target groups, managing access rights, and monitoring audit trails.
-
Agents - Provides menus for registering, deploying, activating, and managing Audit Vault Agents.
-
Database Firewalls - Provides menus for registering Database Firewalls in Audit Vault Server, for creating resilient firewall pairs for high availability, managing, and monitoring.
- Data Retention - Provides menus for viewing details of online and archived data, viewing and creating archiving policies, assigning archive policies to targets, and viewing and creating remote archiving locations.
-
Settings - Provides menus for managing security, storage, archiving, users, certificates, password, and system settings. From here, you can also download the AVCLI command line utility.
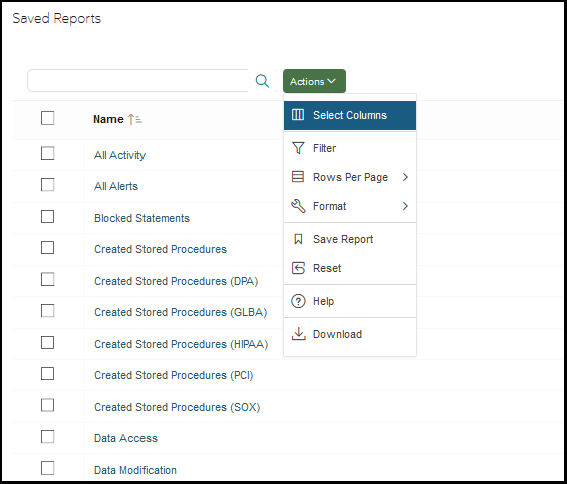
2.9.4 Working with Lists of Objects in the Audit Vault Server Console
Learn how to work with lists of objects in the Audit Vault Server console.
In the Audit Vault Server console, you can view lists of objects such as users, monitoring points, and so on. You can also filter and customize the lists of objects using the Actions menu and other filters. This section provides a summary of how you can create custom views of lists of objects. For more detailed information, see the Reports chapter of Oracle Audit Vault and Database Firewall Auditor's Guide.
To filter and control the display of lists of objects in the Audit Vault Server console:
2.10 Using the Audit Vault Command Line Interface
Learn about using the Audit Vault Command Line Interface (AVCLI).
You can download AVCLI and use it as an alternative to Audit Vault Server Console for:
- configuring and managing Oracle Audit Vault and Database Firewall
- creating Database Firewall monitoring points
- managing audit trails
- registering hosts and performing other Agent related tasks
- configuring both database and non database targets for Audit Vault Server
- managing archive locations
See Also:
-
Downloading and Using the AVCLI Command Line Interface for information on downloading and using AVCLI
-
AVCLI Commands Reference for details of available commands and syntax
2.11 Using the Oracle Audit Vault and Oracle Database Firewall Enterprise Manager Plug-In
Learn about using the Oracle Audit Vault and Database Firewall Enterprise Manager plug-in.
With Oracle Enterprise Manager Cloud Control you can install the Oracle Audit Vault and Database Firewall plug-in. Use this plug-in to manage and monitor Oracle Audit Vault and Database Firewall through Oracle Enterprise Manager.
You can perform the following tasks:
-
View Audit Vault and Database Firewall topologies
-
Monitor the availability and performance of Oracle Audit Vault components
-
Provision Oracle Audit Vault Agent on targets
-
Initialize and integrate Oracle Audit Vault and Database Firewall with targets including Oracle Database, hosts, and audit trails for hosts as well as Oracle Database.
-
Perform discovery of sensitive columns on targets
-
Monitor targets
Using Oracle Enterprise Manager Audit Vault and Database Firewall plug-in, the following components can be managed to perform certain operations:
| Components | Operations Performed |
|---|---|
|
Database Firewall |
|
|
Audit Vault Agent |
|
|
Monitoring Point |
|
|
Audit Trail |
|
|
Target |
|
Related Topics
See Also:
Refer to MOS note (Doc ID 2855345.1) for more information to manually deploy Oracle Enterprise Manager 13.x Agent on Audit Vault Server using the pull method.2.12 Logging In to Oracle AVDF Appliances Through SSH
When installing or administering Oracle Audit Vault and Database Firewall (Oracle AVDF), you sometimes need to log in to the Audit Vault Server or Database Firewall appliance through SSH.
-
Log in to the appliance through SSH as the
supportuser.The
supportuser is set up during the post-installation process. See Post-Install Configuration Tasks.Note:
If you're using the Oracle Cloud Infrastructure (OCI) marketplace image, connect through SSH as theOPCuser.ssh support@<appliance_ip_address> -
Switch to the
rootuser.su - rootNote:
If you're using the OCI marketplace image, use thesudo su -command.
Caution:
Logging in asroot during install or upgrade uses tmux, a terminal
multiplexer, to display persistent information. A user with access to these screens
can create new root shells. If you plan to leave the session unattended, Oracle
recommends disconnecting from the blue screen by using the CTRL-b d
command. To reconnect, log in as root once more.