1 Introduction to the Connector
Oracle Identity Governance is a centralized identity management solution that provides self-service, compliance, provisioning, and password management services for applications residing on-premises or on the Cloud. Oracle Identity Governance connectors are used to integrate Oracle identity Governance with the external identity-aware applications.
The Siebel Connector lets you create and onboard Siebel applications in Oracle Identity Governance.
Note:
In this guide, the connector that is deployed using the Applications option on the Manage tab of Identity Self Service is referred to as an AOB application.From Oracle Identity Governance release 12.2.1.3.0 onward, connector deployment is handled using the application onboarding capability of Oracle Identity Self Service. This capability lets business users to onboard applications with minimum details and effort. The connectorinstallation package includes a collection of predefined templates (XML files) that contain all the information required for provisioning and reconciling data from a given application or target system. These templates also include basic connectivity and configuration details specific to your target system. The connector uses information from these predefined templates allowing you to onboard your applications quickly and easily using only a single and simplified UI.
Application onboarding is the process of registering or associating an application with Oracle Identity Governance and making that application available for provisioning and reconciliation of user information.
The following topics provide a high-level overview of the connector:
1.1 Certified Components
These are the software components and their versions required for installing and using the Siebel Connector.
Table 1-1 Certified Components
| Item | Requirement |
|---|---|
|
Oracle Identity Governance or Oracle Identity Manager |
You can use one of the following releases of Oracle Identity Governance or Oracle Identity Manager:
|
| Oracle Identity Governance or Oracle Identity Manager JDK | JDK 1.8 and later version |
|
Target Systems |
The target system can be any one of the following:
Note:Siebel Connector needs JDK 1.8 or later as a minimum version to work with Siebel IP 2017, IP 2018, Siebel 19.x, and 20.x, 23.x, 24.x,25.x target systems. For Siebel 26.x target systems, the Siebel Connector requires JDK 21 or later as the minimum version. |
|
Connector Server |
12.2.1.3.1 or 12.2.1.3.0 |
|
Connector Server JDK |
Note: If you are using Siebel Innovation Pack 2017, 2018, Siebel 19.x, 20.x or later see Understanding the JDK Requirement for Siebel IP 2017, Siebel IP 2018, Siebel 19.x, or Siebel 20.x later for information related to JDK requirement. If you are using Siebel 26.x or later see Understanding the JDK Requirement for Siebel 26.x later for information related to JDK requirement. |
|
External code |
Depending on the target system that you use, obtain one of the following dependent libraries from the target system:
|
1.2 Usage Recommendation
If you are using Oracle Identity Governance 12c (12.2.1.3.0) or Oracle Identity Governance 14c (14.1.2.1.0) or later, then use the latest 12.2.1.x version of this connector. Deploy the connector using the Applications option on the Manage tab of Identity Self Service.
1.3 Certified Languages
This release of the connector supports the following languages:
-
Arabic
-
Chinese Simplified
-
Chinese Traditional
-
Czech
-
Danish
-
Dutch
-
English
-
Finnish
-
French
-
French (Canadian)
-
German
-
Greek
-
Hebrew
-
Hungarian
-
Italian
-
Japanese
-
Korean
-
Norwegian
-
Polish
-
Portuguese
-
Portuguese (Brazilian)
-
Romanian
-
Russian
-
Slovak
-
Spanish
-
Swedish
-
Thai
-
Turkish
1.4 Supported Connector Operations
These are the list of operations that the connector supports for your target system.
Table 1-2 Supported Connector Operations
| Operation | Supported |
|---|---|
|
User Management |
|
|
Create user |
Yes |
|
Update user |
Yes |
|
Enable user |
Yes |
|
Disable user |
Yes |
|
Delete user |
Yes |
|
Reset Password |
No |
| Position Grant Management | |
|
Assign and Revoke Position |
Yes |
| Responsibility Grant Management | |
| Assign and Revoke Responsibility | Yes |
1.5 Connector Architecture
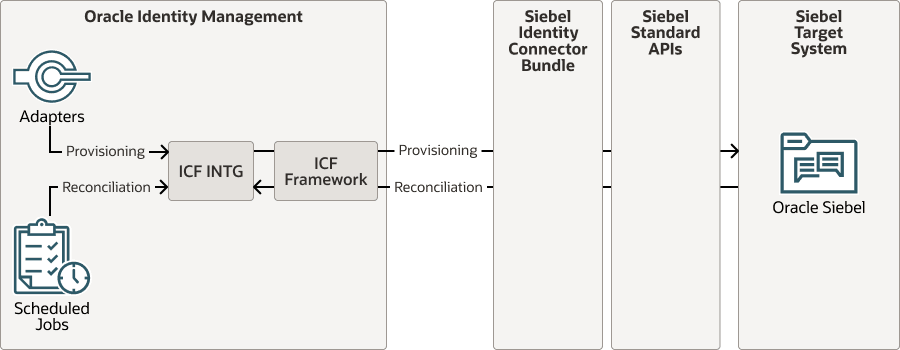
The Siebel is implemented by using the Identity Connector Framework (ICF).
The ICF is a component that is required to use Identity Connector. ICF provides basic reconciliation and provisioning operations that are common to all Oracle Identity Governance connectors. In addition, ICF provides common features that developers would otherwise need to implement on their own, such as, buffering, time outs, and filtering. ICF is distributed together with Oracle Identity Governance. Therefore, you do not need to configure or modify ICF.
Figure 1-1 shows the architecture of the Siebel.
Figure 1-1 Siebel Connector Architecture
The connector is configured to run in one of the following modes:
- Account management
Account management is also known as target resource management. In this mode, the target system is used as a target resource and the connector enables the following operations:
- Provisioning
Provisioning involves creating, updating, or deleting users on the target system through Oracle Identity Governance. During provisioning, the Adapters invoke ICF operation, ICF in turn invokes create operation on the Siebel Identity Connector Bundle and then the bundle calls the target system API (Siebel API) for provisioning operations. The API on the target system accepts provisioning data from the bundle, carries out the required operation on the target system, and returns the response from the target system back to the bundle, which passes it to the adapters.
- Target resource reconciliation
During reconciliation, a scheduled task invokes an ICF operation. ICF in turn invokes a search operation on the Siebel Identity Connector Bundle and then the bundle calls Siebel API for Reconciliation operation. The API extracts user records that match the reconciliation criteria and hands them over through the bundle and ICF back to the scheduled task, which brings the records to Oracle Identity Governance.
Each record fetched from the target system is compared with Siebel resources that are already provisioned to OIM Users. If a match is found, then the update made to the Siebel record from the target system is copied to the Siebel resource in Oracle Identity Governance. If no match is found, then the Name of the record is compared with the User Login of each OIM User. If a match is found, then data in the target system record is used to provision an Siebel resource to the OIM User.
- Provisioning
The Siebel Identity Connector Bundle communicates with the Siebel API using the HTTPS protocol. The Siebel API provides programmatic access to Siebel through Siebel API endpoints. Apps can use the Siebel API to perform create, read, update, and delete (CRUD) operations on directory data and directory objects, such as users, positions, and responsibilities.
See Also:
Understanding the Identity Connector Framework in Oracle Fusion Middleware Developing and Customizing Applications for Oracle Identity Governance for more information about ICF.
1.6 Use Cases Supported by the Connector
The Siebel is used to integrate Oracle Identity Governance with Siebel to ensure that all Siebel accounts are created, updated, and deactivated on an integrated cycle with the rest of the identity-aware applications in your enterprise. The Siebel supports management of identities for Cloud Identity, Synchronized Identity, and Federated Identity models of Siebel. In a typical IT scenario, an organization using Oracle Identity Governance wants to manage accounts, positions, and responsibilities across Siebel Service. The following are some of the most common scenarios in which this connector can be used:
- Siebel User Management:
An organization using Siebel wants to integrate with Oracle Identity Governance to manage identities. The organization wants to manage its user identities by creating them in the target system using Oracle Identity Governance. The organization also wants to synchronize user identity changes performed directly in the target system with Oracle Identity Governance. In such a scenario, a quick and an easy way is to install the Siebel and configure it with your target system by providing connection information.
To create a new user in the target system, fill in and submit the OIM process form to trigger the provisioning operation. The connector executes the CreateOp operation against your target system and the user is created on successful execution of the operation. Similarly, operations like delete and update can be performed.
To search or retrieve the user identities, you must run a scheduled task from Oracle Identity Governance. The connector will run the corresponding SearchOp against the user identities in the target system and fetch all the changes to Oracle Identity Governance
- Siebel Position Management:
An organization has several Siebel positions allowing its users to set up new positions, manage, and delete positions. The organization now wants to know the list of positions that have not been recently accessed or who has no position. In such a scenario, you can use the Siebel to highlight the usage trend for positions. By using the Siebel, you can leverage the reporting capabilities of Oracle Identity Governance to track any operations (such as create, update, delete) performed on positions.
- Siebel Responsibility Management:
In large organizations, it may be necessary for an administrator to designate other employees to act as administrators to serve different functions. For example, you can set responsibilities for your IT staff that can act as support agents to other employees, partners, customers, and vendors. With the Siebel, you can assign or revoke a Siebel responsibility to users as an entitlement, thus facilitating you to leverage the delegated administration capability of Siebel.
1.7 Connector Features
The features of the connector include support for connector server, full reconciliation, limited reconciliation, and reconciliation of deleted account data.
Table 1-3 Supported Connector Features Matrix
| Feature | AOB Application |
|---|---|
| Full reconciliation | Yes |
| Limited reconciliation | Yes |
| Delete reconciliation | Yes |
| Use connector server | Yes |
| Transformation and validation of account data | Yes |
| Perform connector operations in multiple domains | Yes |
| Support for paging | No |
| Test connection | Yes |
| Reset password | No |
| Siebel Position assignment | Yes |
| Siebel Responsibility assignment | Yes |
| User Provisioning | Yes |
1.7.1 User Provisioning
User provisioning involves creating or modifying the account data on the target system through Oracle Identity Governance.
Note:
For more information, see Performing Provisioning Operations.1.7.2 Full Reconciliation
You can perform full reconciliation to bring all existing user data from the target system to Oracle Identity Governance.
After the first full reconciliation run, you can configure your connector if the target system contains an attribute that holds the timestamp at which an object is created or modified.
1.7.3 Limited Reconciliation
You can reconcile records from the target system based on a specified filter criterion. To limit or filter the records that are fetched into Oracle Identity Governance during a reconciliation run, you can specify the subset of added or modified target system records that must be reconciled.
You can set a reconciliation filter as the value of the Custom Recon Query attribute of the user reconciliation scheduled job. The Custom Recon Query attribute helps you to assign filters to the API based on which you get a filtered response from the target system.
For more information, see Performing Limited Reconciliation.
1.7.4 Reconciliation Based on User Type
You can specify the Siebel user type (Employee or User) for which you want to reconcile records from the target system.
See Reconciliation Based on User Type for more information.
1.7.5 Reconciliation of Deleted User Records
You can configure the connector for reconciliation of deleted user records. In target resource mode, if a record is deleted on the target system, then the corresponding Siebel resource is revoked from the OIM User. In trusted source mode, if a record is deleted on the target system, then the corresponding OIM User is deleted.
See Scheduled Job for Reconciliation of Deleted Users Records for more information about scheduled jobs used for reconciling deleted user records.
1.7.6 Support for the Connector Server
Connector Server is one of the features provided by ICF. By using one or more connector servers, the connector architecture permits your application to communicate with externally deployed bundles.
A Java connector server is useful when you do not want to execute a Java connector bundle in the same VM as your application. It can be beneficial to run a Java connector on a different host for performance improvements if the bundle works faster when deployed on the same host as the native managed resource.
See Also:
Using an Identity Connector Server in Oracle Fusion Middleware Developing and Customizing Applications for Oracle Identity Manager for more information about installing and configuring connector server and running the connector server
1.7.7 Transformation and Validation of Account Data
You can configure transformation and validation of account data that is brought into or sent from Oracle Identity Governance during reconciliation and provisioning operations by writing Groovy scripts while creating your application.
For more information, see Validation and Transformation of Provisioning and Reconciliation Attributes in Oracle Fusion Middleware Performing Self Service Tasks with Oracle Identity Governance.
1.7.8 Support for Enabling and Disabling Accounts
Enabling User accounts from Oracle Identity Governance makes the Console and Programmatic Access active in the target system if the enableProgrammaticAccess configuration parameter is set to true. Only the Console access is active if the configuration parameter is set to false.
Disabling user accounts from Oracle Identity Governance makes the Console access and Programmatic Access deactivated in the target system irrespective of the enableProgrammaticAccess configuration parameter value. This disables user accounts in Oracle Identity Governance thereby prohibiting them from performing any operation.
Enabling and disabling Oracle Identity Governance account status during reconciliation operation:
Oracle Identity Governance account status is disabled if both the Console access and Programmatic access are deactivated in the target. If either Console access or Programmatic access is activated, Oracle Identity Governance account status is enabled.