1 Introduction to Oracle Database Vault
Oracle Database Vault enables you to control administrative access to your data.
- What Is Oracle Database Vault?
Oracle Database Vault provides controls to prevent unauthorized privileged users from accessing sensitive data and to prevent unauthorized database changes. - What Privileges Do You Need to Use Oracle Database Vault?
Oracle Database Vault provides database roles that enable different users to perform specific tasks, based on separation-of-duty guidelines. - Components of Oracle Database Vault
Oracle Database Vault has a set of components that include PL/SQL packages and other special tools. - How Oracle Database Vault Addresses Compliance Regulations
One of the biggest side benefits resulting from regulatory compliance has been security awareness. - How Oracle Database Vault Protects Privileged User Accounts
Many security breaches, both external and internal, target privileged users database accounts to steal data from databases. - How Oracle Database Vault Allows for Flexible Security Policies
Oracle Database Vault helps you design flexible security policies for your database. - How Oracle Database Vault Addresses Database Consolidation Concerns
Consolidation and cloud environments reduce cost but can expose sensitive application data to those without a true need-to-know. - How Oracle Database Vault Works in a Multitenant Environment
To provide increased security for consolidation, you can use Oracle Database Vault with Oracle Multitenant.
1.1 What Is Oracle Database Vault?
Oracle Database Vault provides controls to prevent unauthorized privileged users from accessing sensitive data and to prevent unauthorized database changes.
- About Oracle Database Vault
The Oracle Database Vault security controls protect application data from unauthorized access, and helps you to comply with privacy and regulatory requirements. - Controls for Privileged Accounts
Privileged database accounts are one of the most commonly used pathways for gaining access to sensitive applications data in the database. - Controls for Database Configuration
Common audit findings are unauthorized changes to database entitlements and grants of theDBArole to too many users. - Enterprise Applications Protection Policies
Application-specific Oracle Database Vault protection policies and guidelines are available for major enterprise applications. - Run-time Privilege Analysis for Users and Applications
Oracle Database Vault enables you to identify the actual privileges and roles that are used at run-time.
Parent topic: Introduction to Oracle Database Vault
1.1.1 About Oracle Database Vault
The Oracle Database Vault security controls protect application data from unauthorized access, and helps you to comply with privacy and regulatory requirements.
Oracle Database Vault is a licensable option of Oracle Database Enterprise Edition. Its purpose is to mitigate the potential impact of privileged account abuse, misuse, insider and external threats, and human error on your sensitive data.
Privileged accounts can be administrator accounts, such as database administrators, or application administrators, application owners, or data analysts. Most users with these type of accounts have far more privileges and access than they need on a daily basis.
Oracle Database Vault is built into the kernel of the Oracle database and makes decisions after system or object privileges are verified. If the command is authorized by a system or object privilege, then Oracle Database Vault then determines if the command is controlled by an Oracle Database Vault realm or command rule. The realm or command rule controls are determined by you. Oracle Database Vault does not replace your existing existing grants or roles but augments them by allowing you to decide when, where, why, and how object or system privileges or roles are used by the grantee.
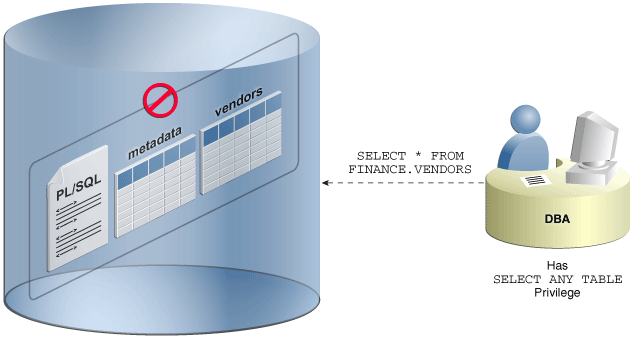
For example, any user who is granted the SELECT ANY TABLE system privilege can use their privilege to query virtually any table in the database, including tables you consider sensitive or important. Oracle Database Vault can restrict the SELECT ANY TABLE system privilege usage on your sensitive tables or other database objects.
Oracle Database Vault helps you increase the security of existing applications through transparent controls that are determined by your requirements.
Parent topic: What Is Oracle Database Vault?
1.1.2 Controls for Privileged Accounts
Privileged database accounts are one of the most commonly used pathways for gaining access to sensitive applications data in the database.
While their broad and unrestricted access facilitates database maintenance, the same access also creates a point of attack for gaining access to large amounts of data. Oracle Database Vault realms around application schemas, sensitive tables, and stored procedures provide controls to prevent privileged accounts from being exploited by intruders and insiders to access sensitive application data.
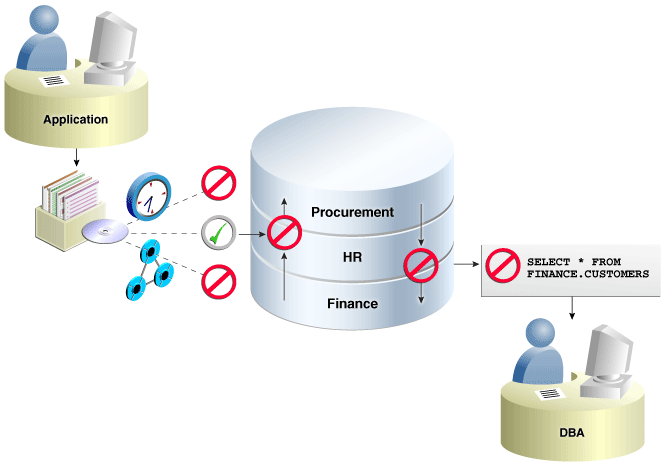
Figure 1-1 Oracle Database Vault Realm Blocking DBA Access to Data
Description of "Figure 1-1 Oracle Database Vault Realm Blocking DBA Access to Data"
Parent topic: What Is Oracle Database Vault?
1.1.3 Controls for Database Configuration
Common audit findings are unauthorized changes to database entitlements and grants of the DBA role to too many users.
Preventing unauthorized changes to production environments is important not only for security, but also for compliance as such changes can weaken security and open doors to intruders, violating privacy and compliance regulations. Oracle Database Vault SQL command rules enable you to control operations inside the database, including commands such as CREATE TABLE, TRUNCATE TABLE, and CREATE USER. Various out-of-the-box factors such as IP address, authentication method, and program name help implement trusted path authorization to deter attacks leveraging stolen passwords. These controls prevent accidental configuration changes and also prevent hackers and malicious insiders from tampering with applications.
The Oracle Database Vault realms with the mandatory mode enables you to seal off access to application objects, even to those with direct object grants, including the object owner. With mandatory realms, you do not need to analyze who has access because this is clear from the list of authorized users. You can enable mandatory realms at runtime and use them in response to a cyber threat, preventing all access until the threat has been analyzed.
Parent topic: What Is Oracle Database Vault?
1.1.4 Enterprise Applications Protection Policies
Application-specific Oracle Database Vault protection policies and guidelines are available for major enterprise applications.
These enterprise applications include Oracle Fusion Applications, Oracle E-Business Suit, Oracle PeopleSoft, Oracle Siebel, Oracle Financial Services (i-Flex), Oracle Primavera, SAP, and Finacle from Infosys.
Parent topic: What Is Oracle Database Vault?
1.1.5 Run-time Privilege Analysis for Users and Applications
Oracle Database Vault enables you to identify the actual privileges and roles that are used at run-time.
The additional unused roles and privileges can then be audited or revoked by the security administrators to reduce the attack surface and implement least privilege model. Privilege analysis can also be used on administrators to help limit the roles and privileges they are granted to fulfill their responsibilities. You do not need to have Oracle Database Vault enabled to perform privilege analysis.
Parent topic: What Is Oracle Database Vault?
1.2 What Privileges Do You Need to Use Oracle Database Vault?
Oracle Database Vault provides database roles that enable different users to perform specific tasks, based on separation-of-duty guidelines.
The most commonly used roles are as follows:
-
DV_OWNERandDV_ADMINenable you to create and manage Database Vault policies. -
DV_ACCTMGRenables you to manage user accounts.
When you register Oracle Database Vault, the DV_OWNER role is granted to a user who must exist before you begin the configuration process, and the DV_ACCTMGR role is granted to a second, optional user, who must also exist before configuration. You can grant the Database Vault roles to other users, but ensure that these users are trusted.
During the registration process, you must create backup accounts for the DV_OWNER and DV_ACCTMGR users. As a best practice, Oracle strongly recommends that you keep and maintain these backup accounts.
Related Topics
Parent topic: Introduction to Oracle Database Vault
1.3 Components of Oracle Database Vault
Oracle Database Vault has a set of components that include PL/SQL packages and other special tools.
- Oracle Database Vault Access Control Components
Oracle Database Vault enables you to create a set of components to manage security for your database instance. - Oracle Enterprise Manager Cloud Control Database Vault Administrator Pages
Oracle Database Vault is pre-installed by default and can be enabled easily. - Oracle Database Vault DVSYS and DVF Schemas
Oracle Database Vault database objects and public functions are stored in theDVSYSandDVFschemas, respectively. - Oracle Database Vault PL/SQL Interfaces and Packages
Oracle Database Vault provides PL/SQL interfaces and packages for security managers or application developers to configure access control policies. - Oracle Database Vault Reporting and Monitoring Tools
You can generate reports on the various activities that Oracle Database Vault monitors.
Parent topic: Introduction to Oracle Database Vault
1.3.1 Oracle Database Vault Access Control Components
Oracle Database Vault enables you to create a set of components to manage security for your database instance.
These components are as follows:
-
Realms. A realm is a protection zone inside the database where database schemas, objects, and roles can be secured. For example, you can secure a set of schemas, objects, and roles that are related to accounting, sales, or human resources. After you have secured these into a realm, you can use the realm to control the use of system and object privileges to specific accounts or roles. This enables you to provide fine-grained access controls for anyone who wants to use these schemas, objects, and roles. Configuring Realms, discusses realms in detail. See also Oracle Database Vault Realm APIs.
-
Command rules. A command rule is a special security policy that you can create to control how users can execute almost any SQL statement, including
SELECT,ALTER SYSTEM, database definition language (DDL), and data manipulation language (DML) statements. Command rules must work with rule sets to determine whether the statement is allowed. Configuring Command Rules, discusses command rules in detail. See also Oracle Database Vault Command Rule APIs. -
Factors. A factor is a named variable or attribute, such as a user location, database IP address, or session user, which Oracle Database Vault can recognize and use as a trusted path. You can use factors in rules to control activities such as authorizing database accounts to connect to the database or the execution of a specific database command to restrict the visibility and manageability of data. Each factor can have one or more identities. An identity is the actual value of a factor. A factor can have several identities depending on the factor retrieval method or its identity mapping logic. Configuring Factors, discusses factors in detail. See also Oracle Database Vault Factor APIs.
-
Rule sets. A rule set is a collection of one or more rules that you can associate with a realm authorization, command rule, factor assignment, or secure application role. The rule set evaluates to true or false based on the evaluation of each rule it contains and the evaluation type (All True or Any True). The rule within a rule set is a PL/SQL expression that evaluates to true or false. You can have the same rule in multiple rule sets. Configuring Rule Sets, discusses rule sets in detail. See also Oracle Database Vault Rule Set APIs.
-
Secure application roles. A secure application role is a special Oracle Database role that can be enabled based on the evaluation of an Oracle Database Vault rule set. Configuring Secure Application Roles for Oracle Database Vault, discusses secure application roles in detail. See also Oracle Database Vault Secure Application Role APIs.
To augment these components, Oracle Database Vault provides a set of PL/SQL interfaces and packages. Oracle Database Vault PL/SQL Interfaces and Packages provides an overview.
In addition to these components, you can analyze the privilege use of your users. Performing Privilege Analysis to Find Privilege Use describes how to use privilege analysis.
In general, the first step you take is to create a realm composed of the database schemas or database objects that you want to secure. You can further secure the realm by creating rules, command rules, factors, identities, rule sets, and secure application roles. In addition, you can run reports on the activities these components monitor and protect. Getting Started with Oracle Database Vault, provides a simple tutorial that will familiarize you with basic Oracle Database Vault functionality. Later chapters provide more advanced tutorials. Oracle Database Vault Reports, provides more information about how you can run reports to check the configuration and other activities that Oracle Database Vault performs.
Parent topic: Components of Oracle Database Vault
1.3.2 Oracle Enterprise Manager Cloud Control Database Vault Administrator Pages
Oracle Database Vault is pre-installed by default and can be enabled easily.
Oracle Database Vault administration is fully integrated with Oracle Enterprise Manager Cloud Control, providing security administrators with a streamlined and centralized interface to manage Oracle Database Vault.
In Oracle Enterprise Manager Cloud Control, you can access the Oracle Database Vault Administrator pages if you prefer to use a graphical user interface to configure Database Vault policies, and view Database Vault alerts and reports. Oracle Database Vault Administrator provides an extensive collection of security-related reports that assist in understanding the baseline security configuration. These reports also help point out deviations from this baseline.
Getting Started with Oracle Database Vault through DBA Operations in an Oracle Database Vault Environment explain how to use the Oracle Database Vault Administrator pages to configure access control policy defined in realms, command rules, factors, rule sets, secure application roles, and how to integrate Oracle Database Vault with other Oracle products. Monitoring Oracle Database Vault explains how to use these pages to monitor Database Vault activity, and Oracle Database Vault Reports, explains Oracle Database Vault reporting.
Parent topic: Components of Oracle Database Vault
1.3.3 Oracle Database Vault DVSYS and DVF Schemas
Oracle Database Vault database objects and public functions are stored in the DVSYS and DVF schemas, respectively.
Oracle Database Vault provides a schema, DVSYS, which stores the database objects needed to process Oracle data for Oracle Database Vault. This schema contains the roles, views, accounts, functions, and other database objects that Oracle Database Vault uses. The DVF schema contains public functions to retrieve (at run time) the factor values set in the Oracle Database Vault access control configuration. Both of these schemas are authenticated as schema only accounts. These accounts are locked by default and should remain locked unless directed otherwise by Oracle Support.
Related Topics
Parent topic: Components of Oracle Database Vault
1.3.4 Oracle Database Vault PL/SQL Interfaces and Packages
Oracle Database Vault provides PL/SQL interfaces and packages for security managers or application developers to configure access control policies.
The PL/SQL procedures and functions allow the general database account to operate within the boundaries of access control policy in the context of a given database session.
See Oracle Database Vault Realm APIs through Oracle Database Vault API Reference for more information.
Parent topic: Components of Oracle Database Vault
1.3.5 Oracle Database Vault Reporting and Monitoring Tools
You can generate reports on the various activities that Oracle Database Vault monitors.
In addition, you can monitor policy changes, security violation attempts, and database configuration and structural changes.
Related Topics
Parent topic: Components of Oracle Database Vault
1.4 How Oracle Database Vault Addresses Compliance Regulations
One of the biggest side benefits resulting from regulatory compliance has been security awareness.
Historically, the focus of the information technology (IT) department has been on high availability and performance. The focus on regulatory compliance has required everyone to take a step back and look at their IT infrastructure, databases, and applications from a security angle. Common questions include:
-
Where is the sensitive information stored?
-
Who has access to this information?
Regulations such as the Sarbanes-Oxley Act, Health Insurance Portability and Accountability Act (HIPAA), International Convergence of Capital Measurement and Capital Standards: a Revised Framework (Basel II), Japan Privacy Law, Payment Card Industry Data Security Standard (PCI DSS), and the European Union Directive on Privacy and Electronic Communications have common themes that include internal controls, separation of duty, and access control.
While most changes required by regulations such as Sarbanes-Oxley and HIPAA are procedural in nature, the remainder may require technology investments. A common security requirement found in regulations is stringent internal controls. The degree to which Oracle Database Vault helps an organization achieve compliance varies with the regulation. In general, Oracle Database Vault realms, command rules, factors and separation of duty features, help reduce the overall security risks that regulation provisions worldwide address.
Table 1-1 lists regulations that address potential security threats.
Table 1-1 Regulations That Address Potential Security Threats
| Regulation | Potential Security Threat |
|---|---|
|
Sarbanes-Oxley Section 302 |
Unauthorized changes to data |
|
Sarbanes-Oxley Section 404 |
Modification to data, unauthorized access |
|
Sarbanes-Oxley Section 409 |
Denial of service, unauthorized access |
|
Gramm-Leach-Bliley |
Unauthorized access, modification, or disclosure |
|
Health Insurance Portability and Accountability Act (HIPAA) 164.306 |
Unauthorized access to data |
|
HIPAA 164.312 |
Unauthorized access to data |
|
Basel II – Internal Risk Management |
Unauthorized access to data |
|
CFR Part 11 |
Unauthorized access to data |
|
Japan Privacy Law |
Unauthorized access to data |
|
EU Directive on Privacy and Electronic Communications |
Unauthorized access to data |
|
Payment Card Industry Data Security Standard (PCI DSS) |
Unauthorized changes to data |
Parent topic: Introduction to Oracle Database Vault
1.5 How Oracle Database Vault Protects Privileged User Accounts
Many security breaches, both external and internal, target privileged users database accounts to steal data from databases.
Oracle Database Vault protects against compromised privilege user account attacks by using realms, factors, and command rules. Combined, these provide powerful security tools to help secure access to databases, applications, and sensitive information. You can combine rules and factors to control the conditions under which commands in the database are allowed to execute, and to control access to data protected by a realm. For example, you can create rules and factors to control access to data based on IP addresses, the time of day, and specific programs. These can limit access to only those connections that pass these conditions. This can prevent unauthorized access to application data and access to the database by unauthorized applications.
Oracle Database Vault provides built-in factors that you can use in combination with rules to control access to the database, realm-protected applications, and commands within the database.
You can associate rules and factors with many SQL statements in the database to provide stronger internal controls within the database. You can customize these to meet the operational policies for your site. For example, you could define a rule to limit execution of the ALTER SYSTEM statement to a specific IP address and host name.
Parent topic: Introduction to Oracle Database Vault
1.6 How Oracle Database Vault Allows for Flexible Security Policies
Oracle Database Vault helps you design flexible security policies for your database.
For example, any database user who has the DBA role can make modifications to basic parameters in a database. Suppose an inexperienced administrator who has system privileges decides to start a new redo log file but does not realize that doing so at a particular time may cause problems for the database. With Oracle Database Vault, you can create a command rule to prevent this user from making such modifications by limiting his or her usage of the ALTER SYSTEM SWITCH LOGFILE statement. Furthermore, you can attach rule sets to the command rule to restrict activity further, such as limiting the statement's execution in the following ways:
-
By time (for example, only during 4 p.m. and 5 p.m. on Friday afternoons)
-
By local access only, that is, not remotely
-
By IP address (for example, allowing the action to only a specified range of IP addresses)
You can customize Oracle Database Vault separation of duties to fit the requirements of business of any size. For example, large customers with dedicated IT staff and some out sourced back end operations can further fine tune separation of duties to control what out sourced database administrators can do. For smaller organizations with some users handling multiple responsibilities, separation of duties can be tuned down and these users can create separate dedicated accounts for each responsibility. This helps such users keep track of all actions made and prevents intruders from exploiting compromised privileged database accounts to steal sensitive data. In addition, it helps auditors verify compliance.
Parent topic: Introduction to Oracle Database Vault
1.7 How Oracle Database Vault Addresses Database Consolidation Concerns
Consolidation and cloud environments reduce cost but can expose sensitive application data to those without a true need-to-know.
Data from one country may be hosted in an entirely different country, but access to that data must be restricted based on regulations of the country to which the data belongs. Oracle Database Vault controls provide increased security for these environments by preventing database administrators from accessing the applications data. In addition, controls can be used to help block application bypass and enforce a trusted-path from the application tier to the application data.
Oracle Database Vault provides four distinct separation of duty controls for security administration:
-
Day-to-day database administrator tasks using the default Oracle Database
DBArole -
Security administrator tasks using the
DV_OWNERandDV_ADMINroles -
Account administrator tasks using the
DV_ACCTMGRrole -
Grants of roles and privileges by a named trusted user
Oracle Database Vault separation of duty controls can be customized and organizations with limited resources can assign multiple Oracle Database Vault responsibilities to the same administrator, but using separate accounts for each separation-of-duty role to minimize damage to the database if any one account is stolen and leveraged.
Oracle customers today still have hundreds and even thousands of databases distributed throughout the enterprise and around the world. However, for database consolidation as a cost-saving strategy in the coming years to be effective, the physical security provided by the distributed database architecture must be available in the consolidated environment. Oracle Database Vault addresses the primary security concerns of database consolidation.
Figure 1-2 illustrates how Oracle Database Vault addresses the following database security concerns:
-
Administrative privileged account access to application data: In this case, Oracle Database Vault prevents the database administrator from accessing the schemas that are protected by the Finance realm. Although the database administrator is the most powerful and trusted user, this administrator does not need access to application data residing within the database.
-
Separation of duties for application data access: In this case, the HR realm owner, created in Oracle Database Vault, has access to the HR realm schemas.
Database consolidation can result in multiple powerful user accounts residing in a single database. This means that in addition to the overall database administrator, individual application schema owners also may have powerful privileges. Revoking some privileges may adversely affect existing applications. Using Oracle Database Vault realms, you can enforce access to applications through a trusted path, preventing database users who have not been specifically authorized access from using powerful privileges to look at other application data. For example, a database administrator who has the SELECT ANY TABLE system privilege can be prevented from using that privilege to view other application data residing in the same database.
Parent topic: Introduction to Oracle Database Vault
1.8 How Oracle Database Vault Works in a Multitenant Environment
To provide increased security for consolidation, you can use Oracle Database Vault with Oracle Multitenant.
Oracle Database Vault can prevent privileged user access inside a pluggable database (PDB) and between the PDB and the common privileged user at the container database. Each PDB has its own Database Vault metadata, such as realms, rule sets, command rules, default policies (such as default realms), and so on. In addition, the objects within the DVSYS and DVF schemas are automatically available to any child PDBs. Both schemas are common user schemas.
You can configure common realms in the application root only, but you can create common rule sets and command rules in either the application root or the CDB root. A common command rule in the application root applies to its associated PDBs, and common command rules in the CDB root apply to all PDBs in the CDB environment. The ability to create common realms and command rules enables you to create policies that use a shared set of realms, rule sets, or command rules throughout the CDB environments, rather than having to create these same components for every PDB in the multitenant environment.
You can create individual local policies for each PDB. When you use Database Vault to protect an object, Database Vault subjects common privileges for common objects to the same enforcement rules as local system privileges.
When you configure a PDB that has Database Vault enabled, the DVSYS schema is a common user schema that is stored in the root. This means that all the objects within the DVSYS schema (tables, data dictionary views, user accounts, PL/SQL packages, default policies, and so on) are subject to the common privileges available for this schema. In other words, you can create realms, factors, and so on in the root to protect the schema in the root. Ensure that you configure Database Vault in the root first, before you configure it in the associated PDBs.
When you enable Oracle Database Vault in the CDB root, you can choose either regular mode or strict mode. The settings propagate throughout the CDB based on the setting you choose. For example, suppose a CDB contains both Database Vault-enabled PDBs and PDBs in which Database Vault is not enabled. If you enable Database Vault using regular mode, then both types of PDBs continue to function normally. If you enable Database Vault using strict mode, then the Database Vault-disabled PDBs operate in restricted mode. If you want to run DBMS_MACADM.ENABLE_DV in an application container, then you must run it in the application container outside of application actions.
Figure 1-3 illustrates how the database in regular mode allows different access for common and local database administrators depending if Database Vault is enabled. In this scenario, neither the common user nor the local users have access to the realms in PDB1 and PDB2. Both the common user and the PDB3 local user have access to the Custom App application in PDB3, where Database Vault is not enabled.
Figure 1-3 Oracle Database Vault in a Multitenant Environment with Regular Mode
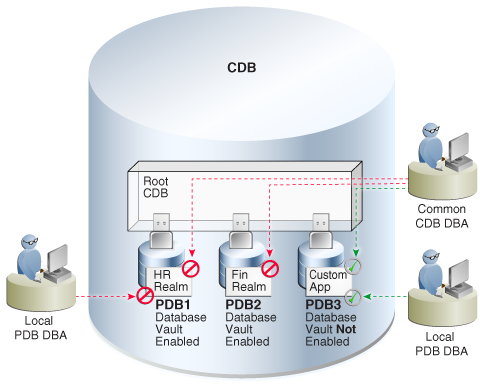
Description of "Figure 1-3 Oracle Database Vault in a Multitenant Environment with Regular Mode"