Summary of Network Virtualization in Oracle Solaris
With server virtualization becoming more mainstream in the IT industry, the focus is shifting to a deployment model that uses network virtualization to support the sharing of network traffic amongst multiple virtual machines (VMs) or zones. Along with a rise in the adoption of cloud architectures that rely upon virtualization for deploying workloads, network virtualization is playing an even more critical role in the overall network administration strategy in Oracle Solaris.
Virtual environments require a high degree of availability, insulation, performance, and separation. Oracle Solaris provides several features that meet these requirements. Additionally, Oracle Solaris network virtualization features are tightly integrated with other Oracle Solaris features (subsystems). For example, when configuring a zones environment, you can create VNICs (anets) that are automatically configured when the zone boots. For information about working with Oracle Solaris zones, see Introduction to Oracle Solaris 11 Virtual Environments.
Network virtualization is also tightly integrated with Oracle Solaris resource management features, which are used to limit the CPUs in a zones environment. For more information about network virtualization and resource management features in Oracle Solaris, see Managing Network Virtualization and Network Resources in Oracle Solaris 11.3.
For information about Oracle VM, including Oracle VM Server for x86, Oracle VM Server for SPARC (previously called Sun Logical Domains, or LDoms), and Oracle VM Manager, see the documentation at https://www.oracle.com/technetwork/documentation/vm-sparc-194287.html.
Oracle also provides the Oracle Enterprise Manager Ops Center for managing some aspects of network virtualization, for example, the ability to create virtual private networks inside a virtual data center. For more information about Oracle Enterprise Manager Ops Center, refer to Oracle Technical Resources at https://www.oracle.com/technical-resources/.
For more information and examples, see the scenarios that are described in Network Configuration Scenarios.
Network Virtualization Building Blocks
-
VNICs
When a datalink such as a physical NIC or a link aggregation needs to be shared by multiple VMs or zones, you can carve it up into virtual NICs or VNICs. These VNICs appear on the system as any other NIC and are administered exactly the same way as a physical NIC. Each VNIC has its own MAC address that you can configure with additional attributes, such as a VLAN ID, thus enabling the VNIC to be easily integrated into an existing network infrastructure. For higher availability, you can also create VNICs on top of link aggregations, which you can then assign individual bandwidth limits, thereby enabling them to consume just their assigned share of bandwidth. VNICs have a rich set of configurable features. For more information, see Building Virtual Networks in Managing Network Virtualization and Network Resources in Oracle Solaris 11.3.
-
Virtual switching
The Oracle Solaris virtual network stack includes built-in virtual switching capabilities that simulate the capabilities of a physical network switch. You can use virtual switches within a single machine to enable zones and VMs to communicate with each other. Virtual switches are automatically instantiated when multiple VNICs are created on top the same datalink. In addition to being able to create VNICs on top of physical NICs or aggregations, you can also create virtual switches on top of an etherstub. This capability enables you to create fully virtualized networks that are independent of the physical hardware. For more information, see Configuring the Components of a Virtual Network in Managing Network Virtualization and Network Resources in Oracle Solaris 11.3.
-
Elastic Virtual Switch (EVS) feature of Oracle Solaris
The EVS feature is an L2 technology that expands network virtualization capabilities by enabling you to directly manage virtual switches. You can create EVS switches to deploy multiple virtual networks that span multiple hosts, within either a multi-tenant cloud environment or a large deployment. You can also optionally configure an EVS switch with virtual ports, IP subnets, and Service Level Agreements (SLAs). Additionally, you can connect any Oracle Solaris VNIC to an EVS switch or a virtual port. Such VNICs automatically inherit their network configuration from EVS. This capability enables you to more cleanly separate the network configuration from a zone or VM configuration.
You manage and observe EVS switches through a central controller. The elastic virtual switches are then automatically deployed on the various hosts, as needed. Hence, the term elastic is used to describe these switches. The EVS architecture is tightly integrated with various other network virtualization features, including the VXLAN feature. See Chapter 3, Configuring Virtual Networks by Using Virtual Extensible Local Area Networks in Managing Network Virtualization and Network Resources in Oracle Solaris 11.3. Together, you can use these two features to create a large number of virtual networks. Also, because EVS switches are transport-agnostic, you can use them with other types of network fabrics, such as traditional VLANs.
EVS switches are also supported in a zones environment. An anet VNIC resource can connect to an EVS switch by using the appropriate zonecfg properties. See Creating and Using Oracle Solaris Zones and the zonecfg(1M) man page for more information.
For more information about the EVS feature, see Chapter 6, Administering Elastic Virtual Switches in Managing Network Virtualization and Network Resources in Oracle Solaris 11.3.
The EVS feature introduces new administrative commands. For more information, see the evsadm(1M) and evsstat(1M) man pages. See also the dladm(1M) man page.
Network virtualization in Oracle Solaris includes the following key building blocks:
Network Virtualization Strategies
-
Workload consolidation
It is a common practice in large deployments to consolidate multiple workloads onto a single system. This type of workload consolidation is typically accomplished by using virtualization on multiple VMs or zones or by using a combination of both methods. To provide network access to these entities, Oracle Solaris network virtualization features provide a way for the physical NICs that are on a system to be virtualized into multiple VNICs. By virtualizing the physical NICs, you eliminate the need to have separate physical NICs for each VM or zone. The VM or zone shares the physical NIC. As is the case for other virtualized resources, it is important to control the share of the network resources to which each virtual machine is entitled. To accomplish this task, you can configure bandwidth limits on the individual VNICs. Using resource control along with VNICs can further improve the use of resources in a multiple virtual network stack.
-
Private virtual networks
-
Security – Create a private virtual network behind a virtual firewall to better insulate virtual machines from the physical network and also to better insulate the physical network from the virtual network.
-
Testing and simulation – Create a private virtual network within a box to test different features or simulate a feature's behavior under a given network load before actually implementing that new feature or network configuration.
-
Network consolidation – Consolidate multiple hosts, network functions, and various network devices such as routers, firewalls, load balancers, and so on, within a box.
You can also use network virtualization features to build private virtual networks for the following purposes:
-
-
Cloud networking
A cloud architecture is a network administration approach that uses a utility computing model to deploy workloads. In this administrative model, multiple tenants share the same cloud and therefore must be isolated from one another. A cloud architecture is highly dynamic.
Oracle Solaris provides several network virtualization features that are ideal for this type of environment. For example, you could use the EVS feature to build virtual network topologies that span multiple hosts while providing a single point of control and observability.
With EVS, a cloud administrator can easily provision, control, and observe a per-tenant, virtual network. This type of configuration includes the capability for satisfying the most demanding requirements for agility and security in modern cloud environments. For more information about how you would set this type of scenario up, see Setting Up an EVS Virtual Tenant Network.
For background information, see Chapter 5, About Elastic Virtual Switches in Managing Network Virtualization and Network Resources in Oracle Solaris 11.3.
You can deploy Oracle Solaris network virtualization features for the following purposes:
Creating a Highly Available Virtual Network Stack for Cloud Environments
The following figure shows how you might combine multiple network virtualization features, for example, link aggregations, VNICs, VXLANs, and an EVS switch, to provide a highly available and integrated virtual network stack for cloud environments.
In this figure the datalink and network layers of the network protocol stack appear twice. This layering is the result of using VXLANs which provide virtual network segments that are encapsulated within IP packets. The datalink and network layers therefore appear twice in the resulting network stack: once to show the handling of packets at the physical layer and then again to show the encapsulated virtual network traffic within these layers of the stack.
The datalink layer that is shown at the lower level of the figure (just above the hardware layer) is used to connect the host to the physical network through three physical NICs, which are aggregated to provide high availability. The resulting aggregation is configured at the network layer and assigned an IP address (aggr0/v4). The same IP address is then used to encapsulate VXLAN packets which form a virtual network segment. In Oracle Solaris, VXLANs are configured through datalinks and then used through VNICs. These VNICs are then configured with IP addresses from within their zones, as depicted in the datalink and network layers that are shown in the top portion of the figure.
Figure 3 Combining Aggregations With VXLANs, VNICs, and an EVS Switch
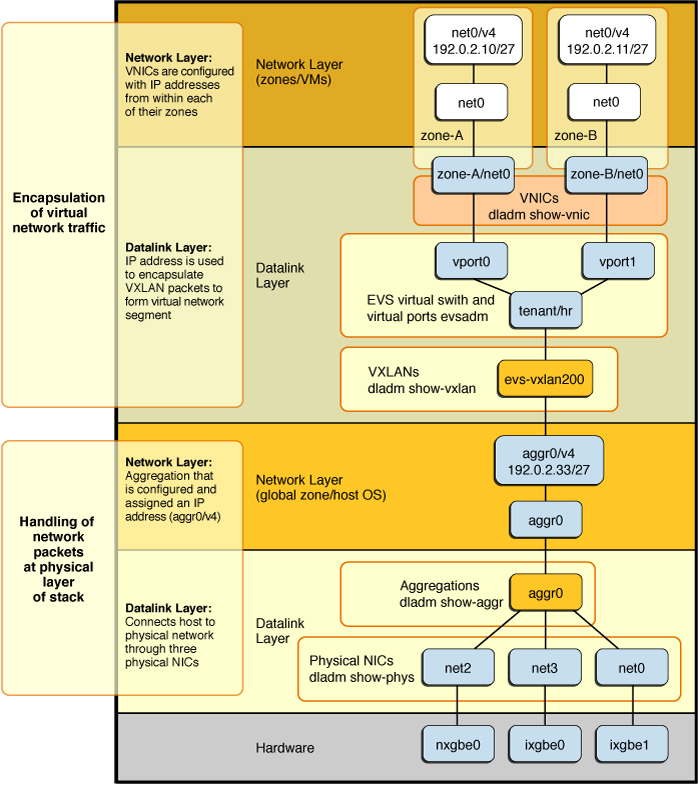
The figure represents the following configuration:
-
Starting from the hardware layer, multiple physical NICs (net0, net2, and net3) are aggregated to form a highly available link aggregation called aggr0.
-
The aggregation is then configured with an IP address, aggr0/v4 (192.0.2.33/27).
-
An EVS virtual switch tenant/hr is created on top of the IP interface aggr0. In this figure, EVS is configured to use a VXLAN.
The new vxlan0 datalink is connected to a virtual L2 network that overlays the IP network.
-
Assuming that EVS assigned the virtual switch a VXLAN ID of 200, EVS automatically creates a VXLAN datalink called evs-vxlan200, which is associated with the tenant/hr virtual switch.
-
The EVS switch has two virtual ports (vport0 and vport1), which are connected to two VNICs that are used by two zones. The VNICs appear in the zone as datalinks named net0 and are visible from the global zone as zone-A/net0 and zone-B/net0.
For some examples of how you would deploy these features, see Network Configuration Scenarios.