Overview of the EVS Feature
-
Maintain multiple systems hosting several virtual machines (VMs) and manage their MAC and IP addresses.
-
Administer different virtualization technologies such as VLANs and VXLANs.
-
Ensure the internal and external connectivity of the VMs and at the same time provide isolation among virtual networks' tenants.
-
Implement and enforce service-level agreements (SLAs).
Today's data centers or multitenant cloud environments present challenging tasks to administrators such as the following:
In Oracle Solaris, EVS works with other technologies to meet these requirements. Through the EVS, system administrators can manage multiple systems through a single virtual switch.
About Virtual Switches
The virtual switch is an entity that facilitates communication between virtual machines. In Oracle Solaris, a virtual switch is implicitly created when you create a VNIC over a datalink The virtual switch loops traffic between VMs within the physical machine and does not send this traffic out on the wire. To communicate with each other, VMs must be on the same Layer 2 segment. See Virtual Switch.
Beginning with Oracle Solaris 11.2, virtual switches are managed by EVS. As a network component, EVS can be configured with virtual ports, IP addresses and other properties to maintain and improve network operations. However, EVS does not replace the implicit virtual switch in previous Oracle Solaris releases.
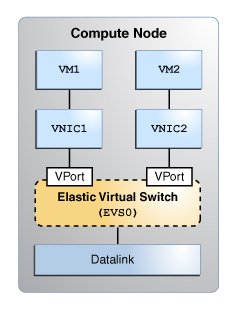
The following figure shows the elastic virtual switch EVS0 in a single compute node.
Figure 16 Elastic Virtual Switch in a Compute Node
The Oracle Solaris Elastic Virtual Switch
EVS is a virtual switch that spans one or more compute nodes and their VMs, hence its 'elastic' character. Through the switch, VMs connect to one another from anywhere in the network.
Note - In EVS, VMs specifically refer to Oracle Solaris Zones and Oracle Solaris Kernel Zones.
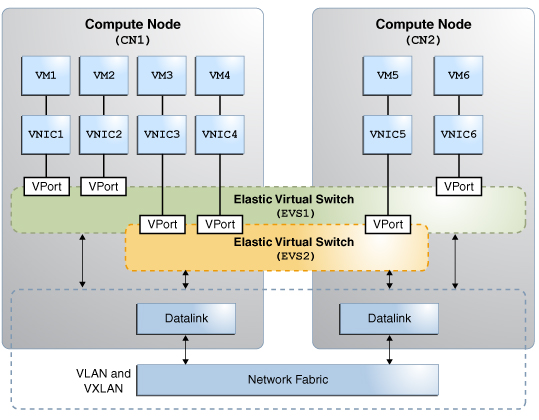
An EVS represents an isolated L2 segment. The isolation is implemented as a flat (untagged) network, a VLAN or a VXLAN. VLANs and VXLANs are used in an EVS setup that involves multiple nodes and network segments. A flat network suffices if the VM instances are on the same segment in the same node.
The following figure shows two elastic virtual switches (EVS1 and EVS2) that span two compute nodes. Each node connects to the same network fabric through their datalinks. In the context of the cloud, datalinks are also called uplink ports.
VNICs connect to their switches through virtual ports. Through the switches, VMs can communicate with one another.
Figure 17 Elastic Virtual Switches Between Compute Nodes
Elastic Virtual Switch Resources
An elastic virtual switch is associated with both an IP network and a virtual port. These two resources and the EVS together are associated with a Universal Unique Identifiers (UUID). A UUID is automatically generated by the EVS controller when you create an elastic virtual switch or its resources.
IP Network
The IP network or a subnet, represents a block of IPv4 or IPv6 addresses with a default router for the block. You can associate only one subnet to an elastic virtual switch. All VMs that connect to the elastic virtual switch through a virtual port are assigned an IP address from the subnet. However, if preferred, you can manually assign an IP address to a VM's virtual port through one of the port's properties.
Virtual Port
A virtual port represents the point of attachment between the VNIC and an elastic virtual switch. When a VNIC connects to a virtual port, the VNIC inherits the network configuration parameters that the port encapsulates, such as the following:
-
SLA parameters such as maximum bandwidth, class of service, and priority
-
MAC address
-
IP address
When you create a port, a randomly generated MAC address and the next available IP address from the associated subnet are assigned to the port. However, if preferred, you can specify the IP address and the MAC address through the port's properties.
You do not always need to add a virtual port to an elastic virtual switch. When a VNIC is created, you can specify only the name of the elastic virtual switch to which the VNIC must connect. In such cases, the EVS controller generates a system virtual port. These virtual ports follow the naming convention sys-vportname, for example, sys-vport0. The system virtual port inherits the elastic virtual switch properties.
The following table shows the port properties.
|
About EVS Tenants
The elastic virtual switches and their resources are logically grouped together. Each logical group is called a tenant. The defined resources for the elastic virtual switch within a tenant are not visible outside that tenant's namespace. The tenant acts as a container to hold all the tenant's resources together.
If you do not specify a tenant, a default tenant sys0global is created and all the EVS operations occur in this namespace.