Overview of VXLANs
In a cloud environment, systems might be located in different Layer 2 networks. For example, a cloud might span systems that are in different geographical locations. In such cases, creating virtual machines (VMs) or tenants over a Layer 2 network restricts the number of systems that you can use for provisioning these VMs. You can use systems in different Layer 2 networks for provisioning VMs. However, as the migration between different systems is restricted to the same Layer 2 network, the utilization of the physical resource is not optimized.
VXLAN is a Layer 2 technology that enables you to create a Layer 2 network on top of a Layer 3 network, thereby providing further network isolation. VXLAN provides a virtual Layer 2 network that stretches over multiple physical Layer 2 networks. Therefore, provisioning resources in a cloud environment is not restricted to a single physical Layer 2 network. Systems can be a part of a VXLAN network as long as they are connected by IPv4 or IPv6 networks.
You can use the VXLAN technology with the Elastic Virtual Switch (EVS) feature of Oracle Solaris to create a large number of virtual networks. For information about how to use VXLAN with the EVS feature to create a virtual network, see Use Case: Configuring an Elastic Virtual Switch for a Tenant. For more information, see About Elastic Virtual Switches and Administering Elastic Virtual Switches.
VXLAN provides isolated Layer 2 segment that is identified by the VXLAN segment ID or VXLAN network identifier (VNI). All VMs in the same VXLAN segment belong to the same virtual Layer 2 broadcast domain.
Communication in VXLANs is similar to that in isolated VLANs. Hence, only VMs that are in the same VXLAN segment can talk to each other. VMs that are not in the same VXLAN segment cannot communicate with each other.
Advantages of Using VXLANs
VXLAN provides the following advantages:
-
Increases scalability in virtualized cloud environments as the VXLAN ID is 24 bits, which enables you to create up to 16 million isolated networks. This overcomes the limitation of VLANs having the 12 bits VLAN ID, which enables you to create a maximum of 4094 isolated networks.
-
Enables you to use the Layer 3 features of the underlying network.
-
The virtual Layer 2 network is abstracted from the underlying physical network. As a result, the virtual network is not visible to the physical network and provides the following benefits:
-
Removes the need to have additional physical infrastructure. For example, the forwarding table of the external switch does not grow with the increase in the VMs behind the physical port on the server.
-
Reduces the scope of MAC address duplication to VMs that exists in the same VXLAN segment. The MAC address can overlap when the addresses are not a part of the same VXLAN segment.
In a VXLAN, only the MAC address of the datalink that belong to the same VXLAN segment or VNI must be unique. This is similar to a VLAN where the VLAN ID and the MAC address must have a unique combination.
-
VXLAN Naming Convention
In Oracle Solaris, a VXLAN endpoint is represented by a VXLAN datalink. This VXLAN datalink is associated with an IP address (IPv4 or IPv6) and a VXLAN network identifier (VNI). Even though multiple VXLAN datalinks can use the same IP address, the combination of the IP address and VNI must be unique. You can configure a VXLAN datalink with an optional multicast address, which is used for discovering the peer VXLAN endpoints on the same VNI and also to implement broadcast within a VXLAN segment. VXLAN datalinks in the same VNI must be configured with the same multicast address. For more information about the requirements of a VXLAN, see Planning a VXLAN Configuration.
Every VXLAN datalink is associated with a VXLAN segment ID, or a VNI. The convention for naming VXLAN datalinks is same as the convention that is used for links or VLANs. For information about providing valid datalink names, see Rules for Valid Link Names in Configuring and Managing Network Components in Oracle Solaris 11.3.
VXLAN Topology
VXLAN enables you to organize systems on a Layer 3 network within their own VXLAN segments.
The following figure illustrates a VXLAN network that is configured over multiple physical servers.
Figure 8 VXLAN Topology
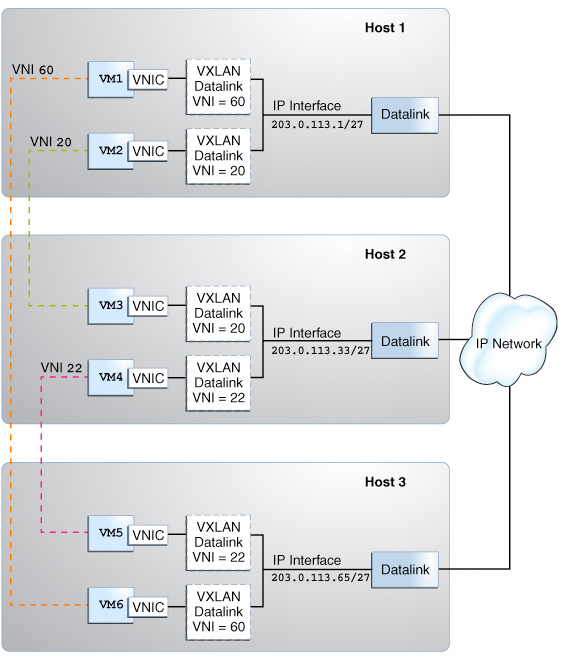
The figure shows three virtualized hosts attached to an IP network infrastructure. There are three VXLAN overlay networks identified by the VXLAN segment IDs or VNIs, 60, 20, and 22. The VMs VM1 and VM6 are on the overlay network identified by the VNI 60, the VMs VM2 and VM3 are on the overlay network identified by the VNI 20, and the VMs VM4 and VM5 are on the overlay network identified by the VNI 22.
Using VXLAN With Zones
You can assign VNICs that are created over VXLAN datalinks to zones. VXLAN datalinks are created by specifying a VNI and these VXLAN datalinks belong to the VXLAN segment that is identified by that VNI. For example, if you specify the VNI as 20 when you create the VXLAN datalink, then that datalink belongs to the VXLAN segment identified by the VNI 20. VNICs that are created over VXLAN datalinks are a part of the VXLAN segment.
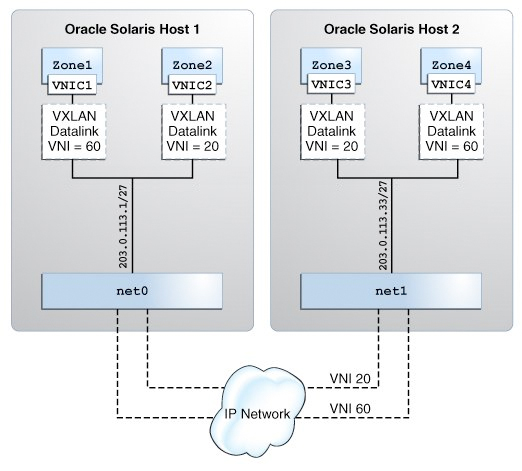
The following figure shows two virtualized Oracle Solaris hosts attached to an IP network infrastructure with two VXLAN overlay networks identified by the VNIs, 20 and 60.
Figure 9 VXLAN With Zones
-
Create a VNIC over a VXLAN and assign the VNIC to the zone. For more information, see Configuring a VXLAN.
-
Assign the VXLAN as the underlying link for the zone's anet (VNIC) resource. For more information, see Assigning a VXLAN to a Zone.
You can create zones that are a part of a VXLAN segment in the following ways:
In any case, the VNIC that is created in a zone is a part of a VXLAN segment identified by the underlying VXLAN datalink. For more information about zones, see Introduction to Oracle Solaris 11 Virtual Environments.
Assigning VNICs to VXLAN links is similar to creating a VLAN link and assigning it to a zone. For more information about creating a VLAN and assigning it to a zone, see How to Configure a VLAN in Managing Network Datalinks in Oracle Solaris 11.3.