About the Trusted Network
Data is properly labeled in network communications.
Mandatory access control (MAC) rules are enforced when data is sent or received across a local network and when file systems are mounted.
MAC rules are enforced when data is routed to distant networks.
MAC rules are enforced when data is routed to zones.
Trusted Extensions assigns security attributes to zones, hosts, and networks. These attributes ensure that the following security features are enforced on the network:
In Trusted Extensions, network packets are protected by MAC. Labels are used for MAC decisions. Data is labeled explicitly or implicitly with a sensitivity label. A label has an ID field, a classification or "level" field, and a compartment or "category" field. Data must pass an accreditation check. This check determines if the label is well-formed, and if the label lies within the accreditation range of the receiving host. Well-formed packets that are within the receiving host's accreditation range are granted access.
IP packets that are exchanged between trusted systems can be labeled. A label on a packet serves to classify, segregate, and route IP packets. Routing decisions compare the sensitivity label of the data with the label of the destination.
For IPv4 packets, Trusted Extensions supports Commercial IP Security Option (CIPSO) labels.
For IPv6 packets, Trusted Extensions supports Common Architecture Label IPv6 Security Option (CALIPSO) labels.
If you must interoperate with systems on an IPv6 CIPSO network, see How to Configure an IPv6 CIPSO Network in Trusted Extensions.
Trusted Extensions supports labels on IPv4 and IPv6 packets.
Typically on a trusted network, the label is generated by a sending host and processed by the receiving host. However, a trusted router can also add or strip labels while forwarding packets in a trusted network. A sensitivity label is mapped to a CALIPSO or CIPSO label before transmission. This label is embedded in the IP packet, which is then a labeled packet. Typically, a packet sender and the packet's receiver operate at the same label.
Trusted networking software ensures that the Trusted Extensions security policy is enforced even when the subjects (processes) and objects (data) are located on different hosts. Trusted Extensions networking preserves MAC across distributed applications.
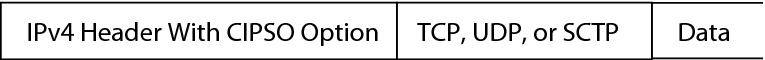
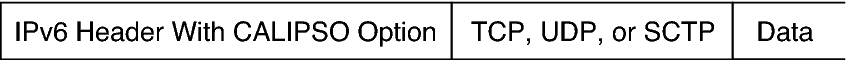
Trusted Extensions Data Packets
Trusted Extensions data packets include a label option. The CIPSO data packets are sent over IPv4 networks. The CALIPSO packets are sent over IPv6 networks.
In the standard IPv4 format, the IPv4 header with options is followed by a TCP, UDP, or SCTP header, and then the actual data. The Trusted Extensions version of an IPv4 packet uses the CIPSO option in the IP header for the security attributes.
In the standard IPv6 format, an IPv6 header with options is followed by a TCP, UDP, or SCTP header and then the actual data. The Trusted Extensions version of an IPv6 packet uses the CALIPSO option in the IP header for security attributes.
Trusted Extensions Multicast Packets
Trusted Extensions can add labels to multicast packets within a LAN. This feature enables you to send labeled multicast packets to CIPSO or CALIPSO systems that operate at the same label or within the label range of the multicast packets. On a heterogeneous LAN, that is, a LAN with both labeled and unlabeled hosts, multicast cannot verify the membership of a multicast group.
Caution - Do not send labeled multicast packets on a heterogeneous LAN. Leakage of labeled information could occur. |
Trusted Network Communications
Trusted Extensions supports labeled and unlabeled hosts on a trusted network. The txzonemgr GUI and the tncfg command are used to configure the network.
Other hosts that are running Trusted Extensions
Hosts that are running operating systems that do not recognize security attributes, but do support TCP/IP, such as Oracle Solaris systems, other UNIX systems, Microsoft Windows, and Macintosh OS systems
Hosts that are running other trusted operating systems that recognize CIPSO labels for IPv4 packets and CALIPSO labels for IPv6 packets
Systems that run Trusted Extensions software support network communications between Trusted Extensions systems and any of the following types of hosts:
Trusted Extensions adds commands and provides a GUI to administer trusted networking. Trusted Extensions also adds options to the Oracle Solaris network commands. For a description of these commands, see Network Commands in Trusted Extensions.
The interfaces manage three Trusted Extensions network configuration databases, tnzonecfg, tnrhdb, and tnrhtp. For details, see Network Configuration Databases in Trusted Extensions.
Trusted Extensions adds the tnrhtp and tnrhdb databases to the properties of the naming service switch SMF service, svc:/system/name-service/switch.
Initial Configuration of Trusted Extensions describes how to define zones and hosts when you configure the network. For additional procedures, see Managing Networks in Trusted Extensions.
Trusted Extensions extends the IKE configuration file, /etc/inet/ike/config. For more information, see Administration of Labeled IPsec and the ike.config(5) man page
As in the Oracle Solaris OS, Trusted Extensions network communications and services can be managed by a naming service. Trusted Extensions adds the following interfaces to Oracle Solaris network interfaces:
Network Commands in Trusted Extensions
tncfg – This command creates, modifies, and displays the configuration of your Trusted Extensions network. The tncfg -t command is used to view, create, or modify a specified security template. The tncfg -z command is used to view or modify the network properties of a specified zone. For details, see the tncfg(8) man page.
tnchkdb – This command is used to verify the correctness of the trusted network databases. The tnchkdb command is called whenever you change a security template (tnrhtp), a security template assignment (tnrhdb), or the configuration of a zone (tnzonecfg) by using the txzonemgr or the tncfg command. For details, see the tnchkdb(8) man page.
tnctl – This command can be used to update the trusted network information in the kernel. tnctl is also a system service. A restart with the command svcadm restart /network/tnctl refreshes the kernel cache from the trusted network databases on the local system. For details, see the tnctl(8) man page.
tnd – This daemon pulls tnrhdb and tnrhtp information from the LDAP directory and local files. The order of search is dictated by the name-service/switch SMF service. The tnd daemon is started at boot time by the svc:/network/tnd service. This service is dependent on the svc:/network/ldap/client.
In an LDAP network, the tnd command also can be used for debugging and for changing the polling interval. For details, see the tnd(8) man page.
tninfo – This command displays the details of the current state of the trusted network kernel cache. The output can be filtered by host name, zone, or security template. For details, see the tninfo(8) man page.
Trusted Extensions adds the following commands to administer trusted networking:
ipadm – The –all-zones address property makes the specified interface available to every zone on the system. The appropriate zone to deliver data to is determined by the label that is associated with the data. For details, see the ipadm(8) man page.
netstat – The –R option extends Oracle Solaris netstat usage to display Trusted Extensions-specific information, such as security attributes for multilevel sockets and routing table entries. The extended security attributes include the label of the peer, and whether the socket is specific to a zone, or available to several zones. For details, see the netstat(8) man page.
route – The –secattr option extends Oracle Solaris route usage to display the security attributes of the route. The value of the option has the following format:
min_sl=label,max_sl=label,doi=integer,cipso
The cipso keyword is optional and set by default. For details, see the route(8) man page.
snoop – As in Oracle Solaris, the –v option to this command can be used to display the IP headers in detail. In Trusted Extensions, the headers contain label information.
ipseckey – In Trusted Extensions, the following extensions are available to label IPsec-protected packets: label label, outer-label label, and implicit-label label. For details, see the ipseckey(8) man page.
Trusted Extensions adds options to the following Oracle Solaris network commands:
Network Configuration Databases in Trusted Extensions
tnzonecfg – This local database stores zone attributes that are security-related. The tncfg command is the interface to access and modify this database.
The attributes for each zone specify the zone label and the zone's access to single-level and multilevel ports. Another attribute handles responses to control messages, such as ping. The labels for zones are defined in the label_encodings file. For more information, see the label_encodings(5) man page. For a discussion of multilevel ports, see Zones and Multilevel Ports.
tnrhtp – This database stores templates that describe the security attributes of hosts and gateways. The tncfg command is the interface to access and modify this database.
Hosts and gateways use the attributes of the destination host and next-hop gateway to enforce MAC when sending traffic. When receiving traffic, hosts and gateways use the attributes of the sender. However, when an adaptive host is the sender, the receiving network interface assigns its default label to the incoming packets. For details of the security attributes, see Network Security Attributes in Trusted Extensions.
tnrhdb – This database holds the IP addresses and ranges of IP addresses that correspond to all hosts that are allowed to communicate with this system. The tncfg command is the interface to access and modify this database.
Each host or range of IP addresses is assigned a security template from the tnrhtp database. The attributes in the template define the attributes of the assigned host.
Trusted Extensions loads three network configuration databases into the kernel. These databases are used in accreditation checks as data is transmitted from host to host.
Trusted Network Security Attributes
Network administration in Trusted Extensions is based on security templates. A security template describes a set of hosts that have identical protocols and security attributes.
Security attributes are administratively assigned to remote systems, both hosts and routers, by means of templates. The security administrator administers templates and assigns them to remote systems. If a remote system is not assigned a template, no communications are allowed with that system.
One of four host types: unlabeled, cipso, adaptive, or netif. The protocol that is used for network communications is determined by the host type of the template. See Host Type and Template Name in Security Templates.
A set of security attributes that are applied to each host type.
Every template is named and includes the following:
For more detail, see Network Security Attributes in Trusted Extensions.